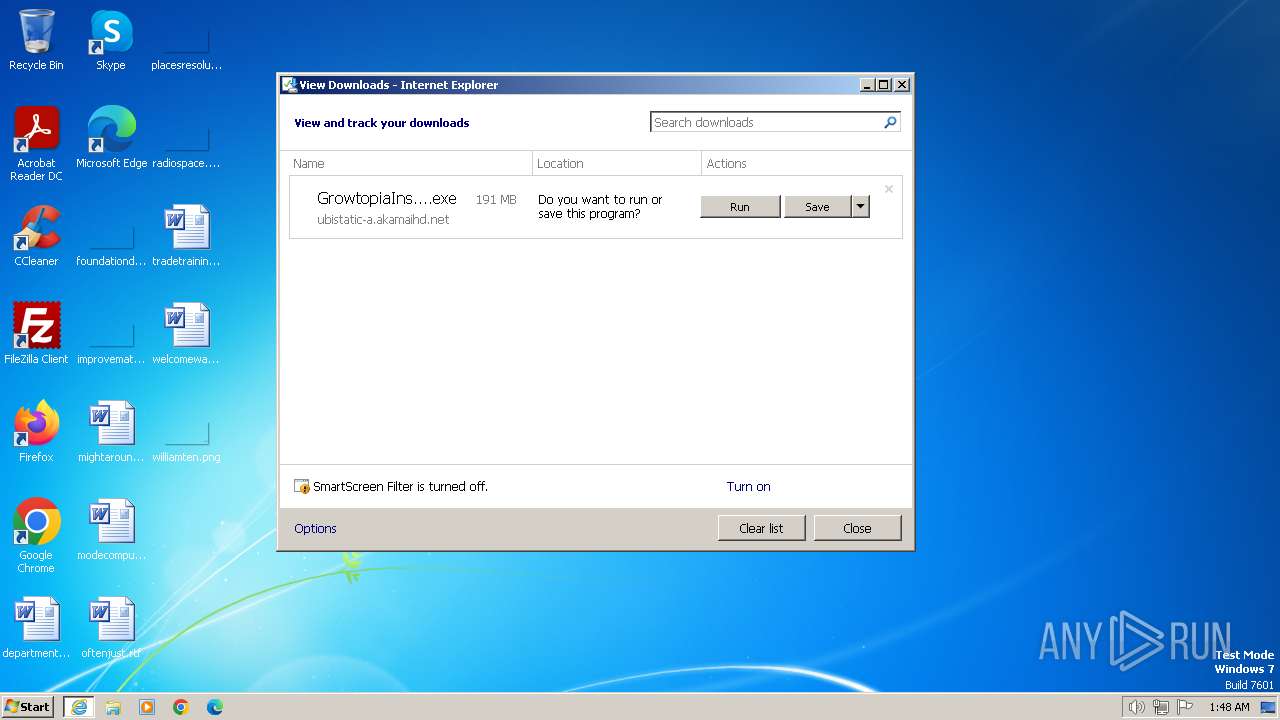
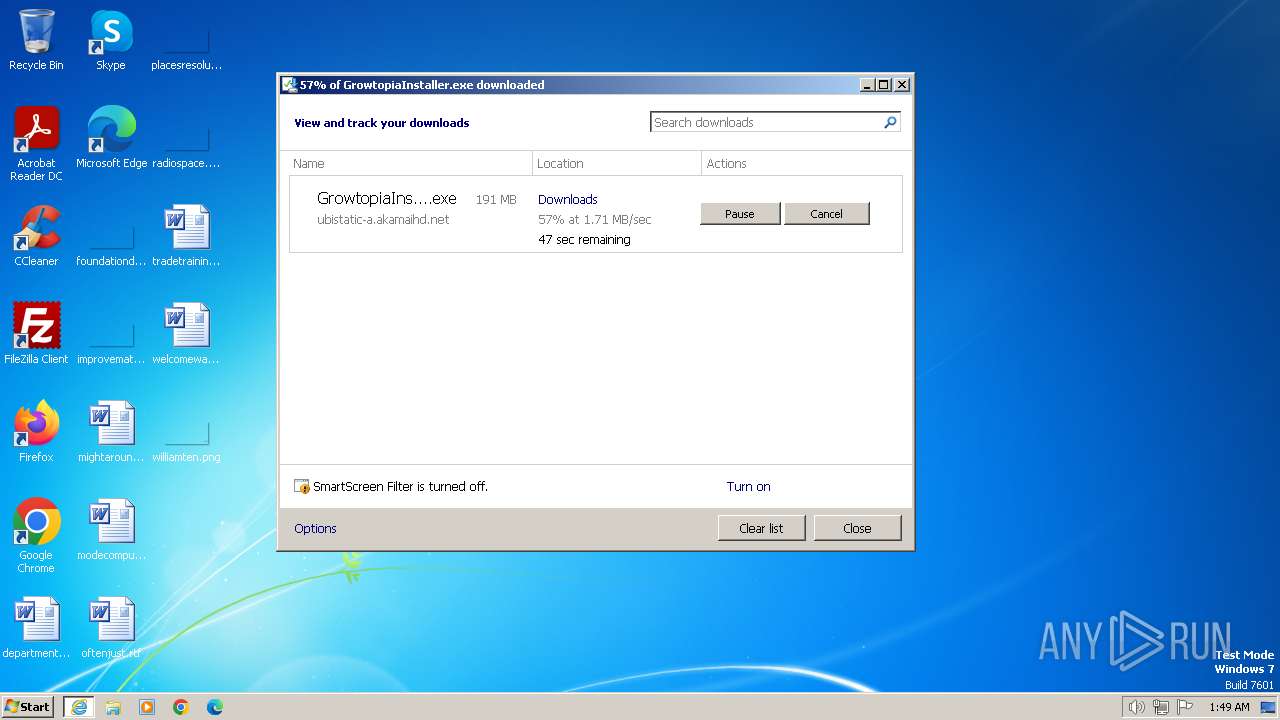
| URL: | https://ubistatic-a.akamaihd.net/0098/594764/GrowtopiaInstaller.exe |
| Full analysis: | https://app.any.run/tasks/e0cf05e3-3536-4aee-8b7e-e7e12e308084 |
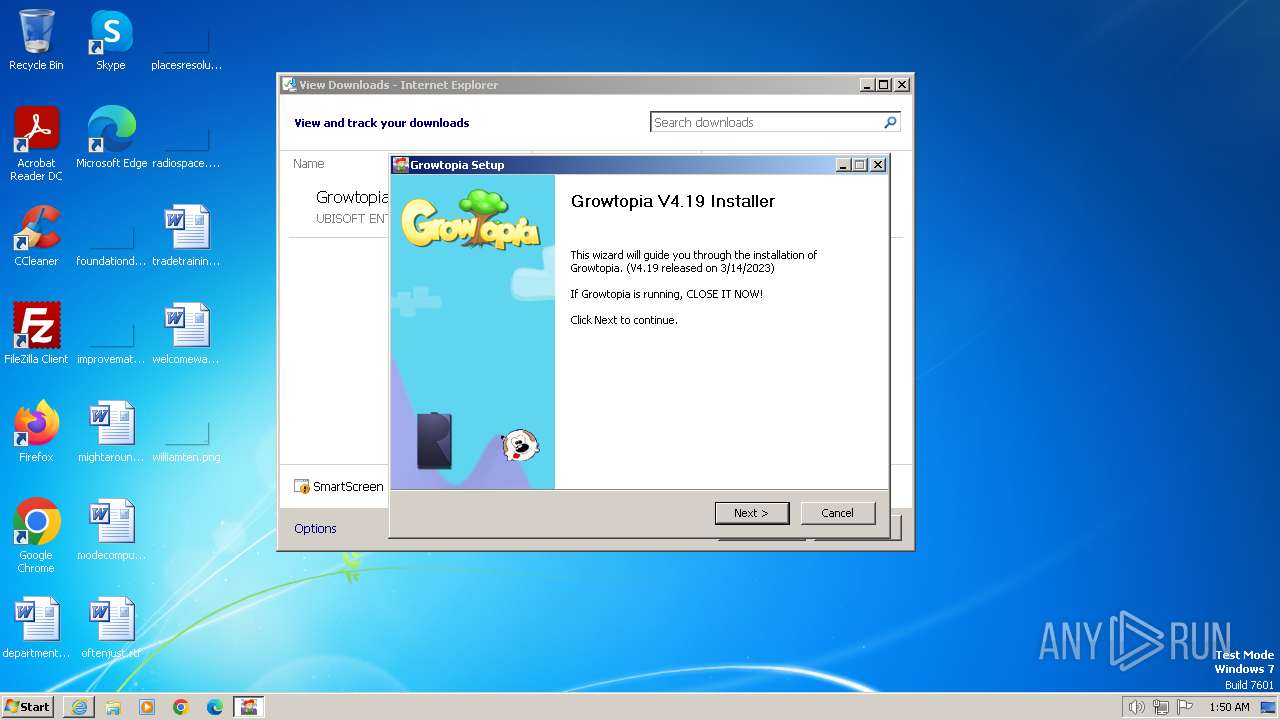
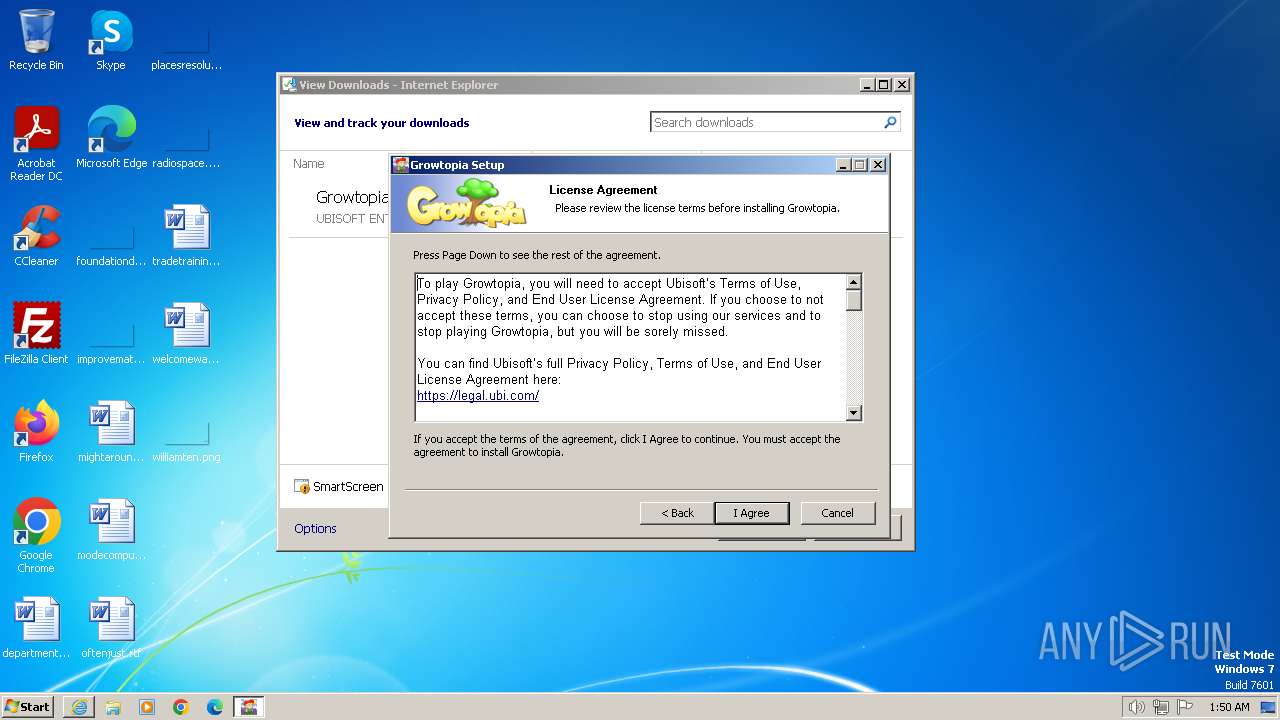
| Verdict: | Malicious activity |
| Analysis date: | January 25, 2024, 01:48:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6189DC9026CBA9B506F6E88C368D831C |
| SHA1: | 6DCD9B2FBAAEB078DB64109E9C718DC6D8E195F0 |
| SHA256: | 60175D1EFB2FB3D0F5A5A91EF2D89D60F74B36500501A16BADA0300EEF5EAB50 |
| SSDEEP: | 3:N8BW9ELhSKQcqLKSszqDgXLNn:2SLDtsu8XLN |
MALICIOUS
Drops the executable file immediately after the start
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
SUSPICIOUS
The process creates files with name similar to system file names
- GrowtopiaInstaller.exe (PID: 2072)
Malware-specific behavior (creating "System.dll" in Temp)
- GrowtopiaInstaller.exe (PID: 2072)
Executable content was dropped or overwritten
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
Process drops legitimate windows executable
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
Searches for installed software
- vc_redist.x86.exe (PID: 2876)
INFO
Drops the executable file immediately after the start
- iexplore.exe (PID: 2584)
The process uses the downloaded file
- iexplore.exe (PID: 2580)
Application launched itself
- iexplore.exe (PID: 2580)
Checks supported languages
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
Reads the computer name
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
Create files in a temporary directory
- GrowtopiaInstaller.exe (PID: 2072)
- vc_redist.x86.exe (PID: 2876)
Executable content was dropped or overwritten
- iexplore.exe (PID: 2584)
Creates files or folders in the user directory
- GrowtopiaInstaller.exe (PID: 2072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2072 | "C:\Users\admin\Downloads\GrowtopiaInstaller.exe" | C:\Users\admin\Downloads\GrowtopiaInstaller.exe | iexplore.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2580 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ubistatic-a.akamaihd.net/0098/594764/GrowtopiaInstaller.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2580 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
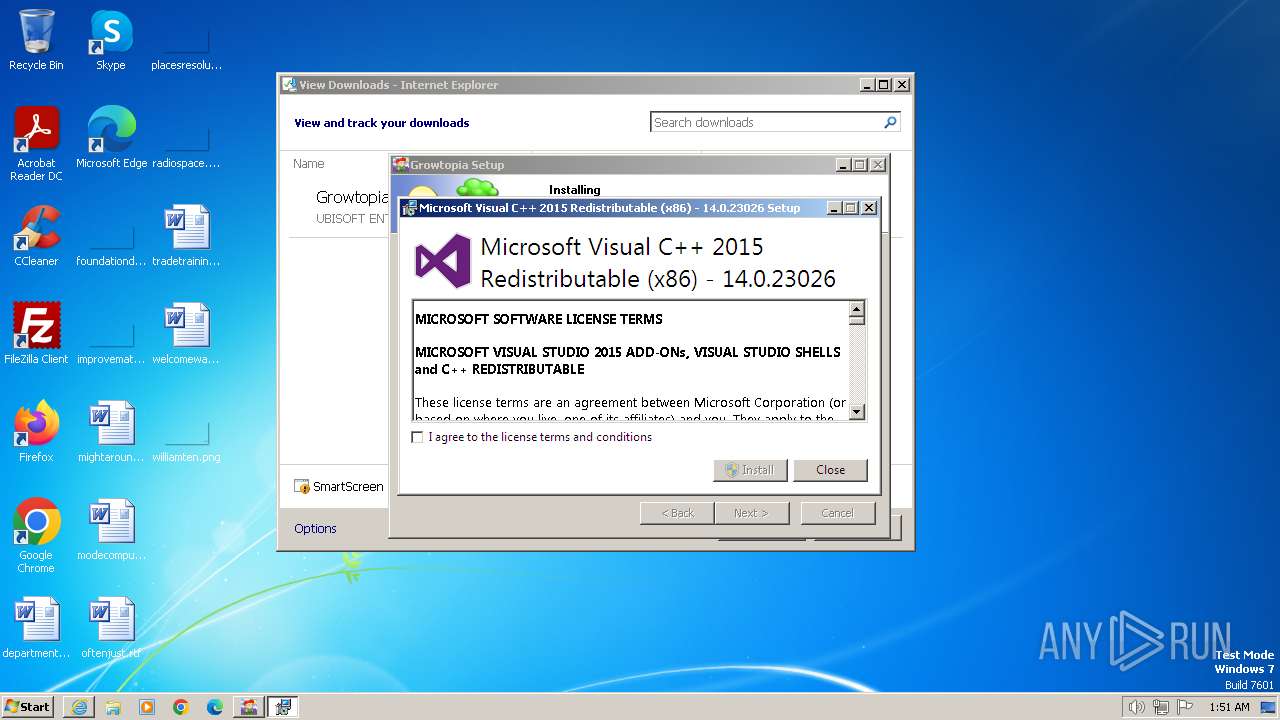
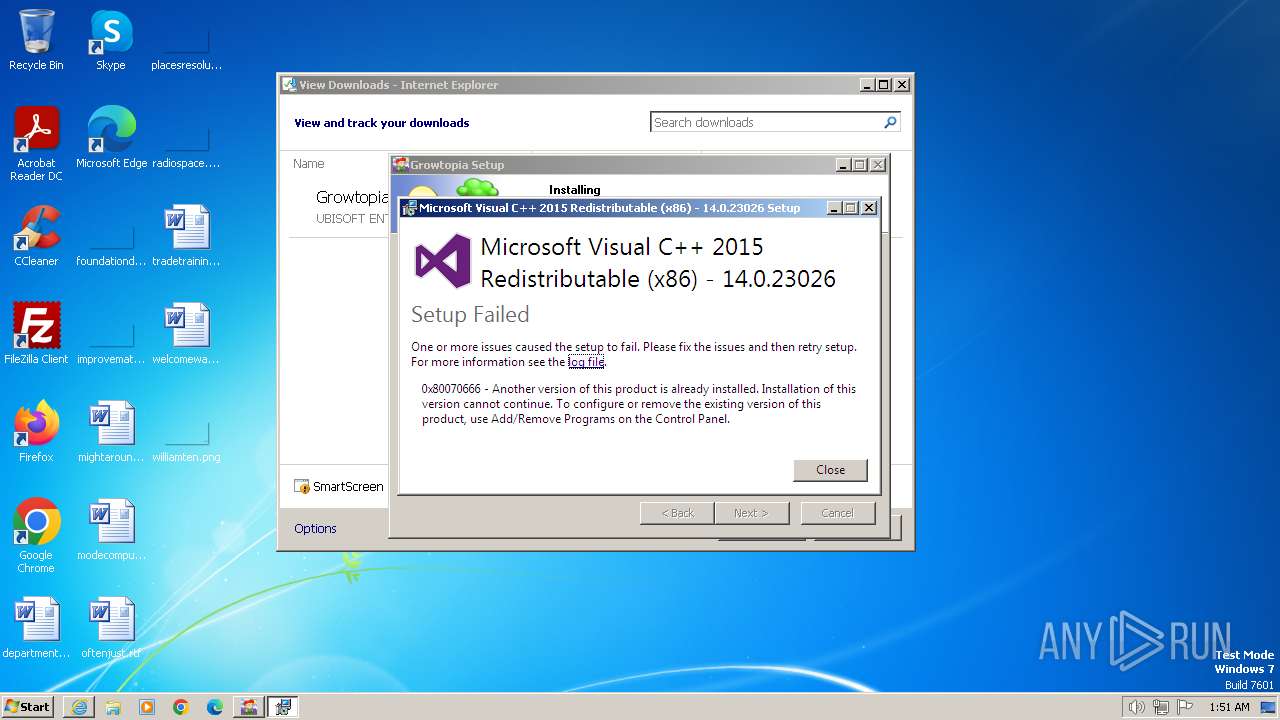
| 2876 | C:\Users\admin\AppData\Local\Growtopia\vc_redist.x86.exe | C:\Users\admin\AppData\Local\Growtopia\vc_redist.x86.exe | GrowtopiaInstaller.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2015 Redistributable (x86) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
Total events
17 333
Read events
17 253
Write events
73
Delete events
7
Modification events
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2580) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
16
Suspicious files
2 022
Text files
56
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:3147E46BEFAB72365C32AF5B9E8DA516 | SHA256:B0EEA0AD65F4045A92447BBC75350B8595952333C77EF8656F54BD0E05D17EFF | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:A586B98571FAA4BB65F51FDD89ADF1E5 | SHA256:04CF55C2EB64AA426650F21FE794690FEFACF160EBB926DA489FB8AB1FEE48BE | |||
| 2584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\GrowtopiaInstaller[1].exe | executable | |
MD5:775B50F06FD5991B5A3F4A478CF2133F | SHA256:E5C72B7A1654959E7E4C9084C289FAB24183CA65510561780582798ED5C20EF4 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ND4HRMA4.txt | text | |
MD5:A37A24B8FE22010AFEA8BF5EFD23FE7B | SHA256:2963C9CD329B323D8D87F26B33CC74650A44BA9E6778BB2CE0CEC619830E42E3 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\KALW4PZR.txt | text | |
MD5:550918BAE26D636C7FA89FAD4BF76638 | SHA256:0A80BD34026F75316B079BD6877AFAAA64E80F9A0BC705FD0156E92D8D79B29F | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\D8TM3T0Z.txt | text | |
MD5:CBCAA2902A3D61D2BF59A75809A1BDD0 | SHA256:9BFBF2417872EA3B050E7DCF27FDE0A36EC56A43A476C9D9CABC913595318B6E | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\M2B00KI3.txt | text | |
MD5:8340B4FE93D4C1F777B270B2EB5CD446 | SHA256:7A635EED7410D87B1AF9EBFF2B83F348CF2C1EE925B8393CE4CB036907071F66 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:6C9B222CD1E44E41AD93BA8D2FCB6512 | SHA256:4D9577E0B9CDB6FD342F66ED39177A482FA460DA255F954DCD6A32B88385727D | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 2580 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\versionlist.xml | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
20
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2584 | iexplore.exe | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?d66bcfdf10b71413 | unknown | — | — | unknown |
2584 | iexplore.exe | GET | 304 | 23.53.40.49:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?098bd4f8ce551810 | unknown | — | — | unknown |
1080 | svchost.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?89bca2e7018c82c0 | unknown | compressed | 65.2 Kb | unknown |
2584 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?1b8fee253118cbef | unknown | compressed | 65.2 Kb | unknown |
2580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | unknown | binary | 471 b | unknown |
2580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
2580 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2584 | iexplore.exe | 23.48.23.24:443 | ubistatic-a.akamaihd.net | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2584 | iexplore.exe | 23.53.40.49:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
2584 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2580 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2580 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2580 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ubistatic-a.akamaihd.net |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
dns.msftncsi.com |
| shared |