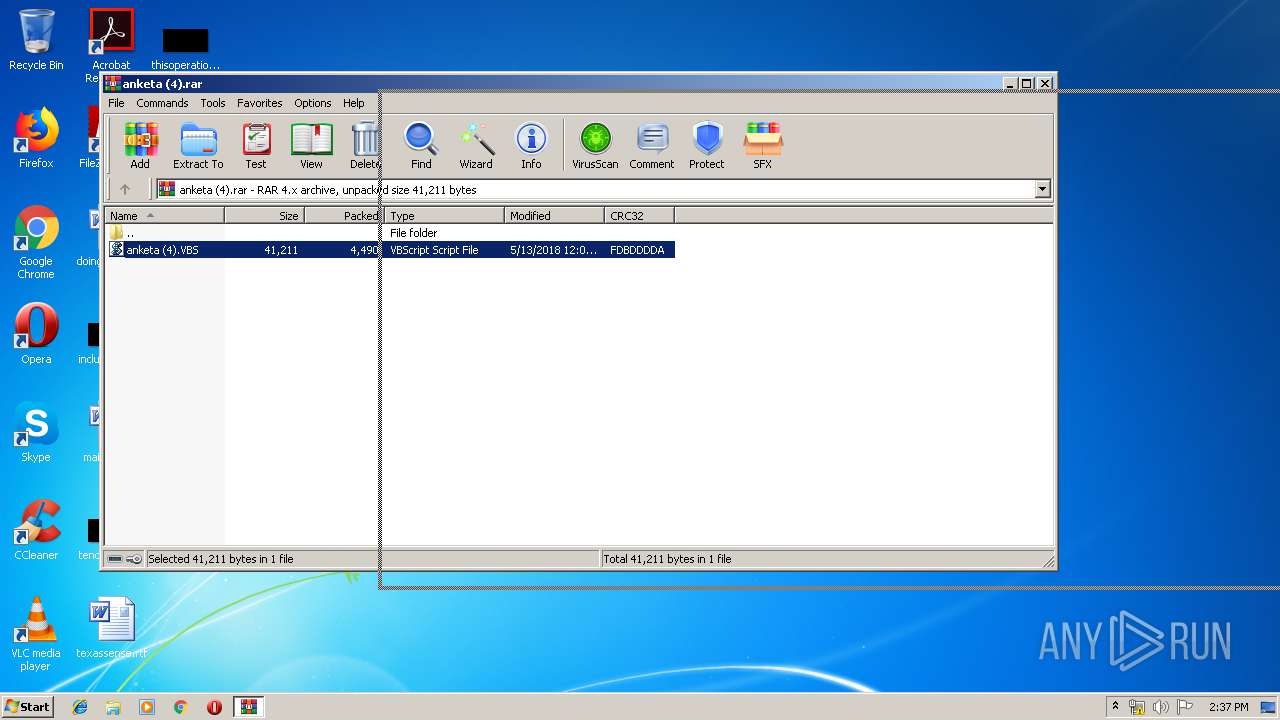
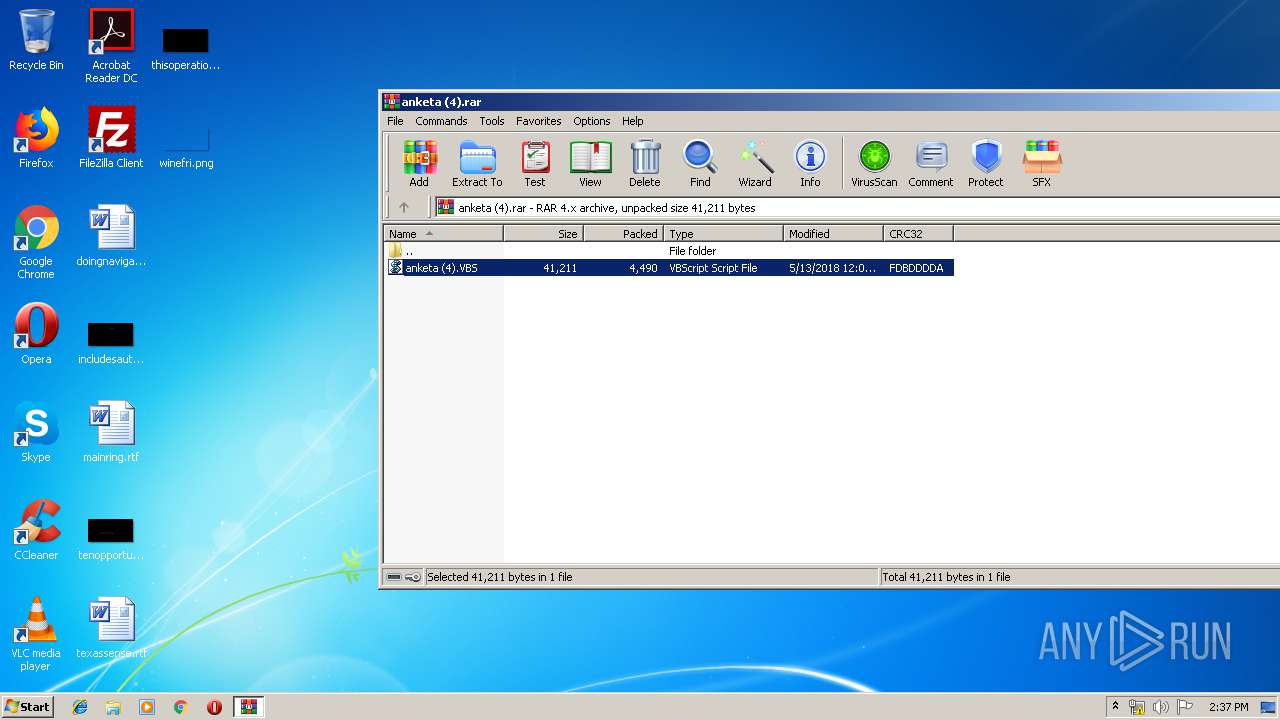
| File name: | anketa (4).rar |
| Full analysis: | https://app.any.run/tasks/8695a3b3-7280-49df-8161-b7b97a2f75ca |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 13:36:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
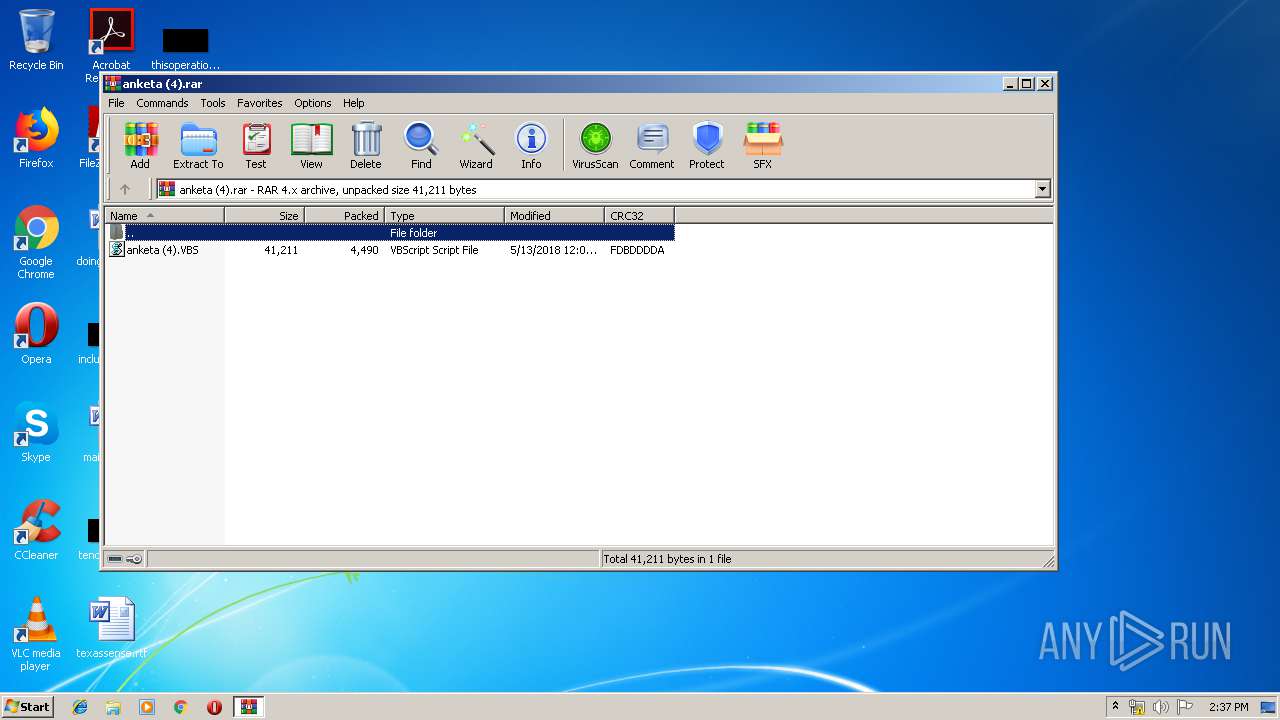
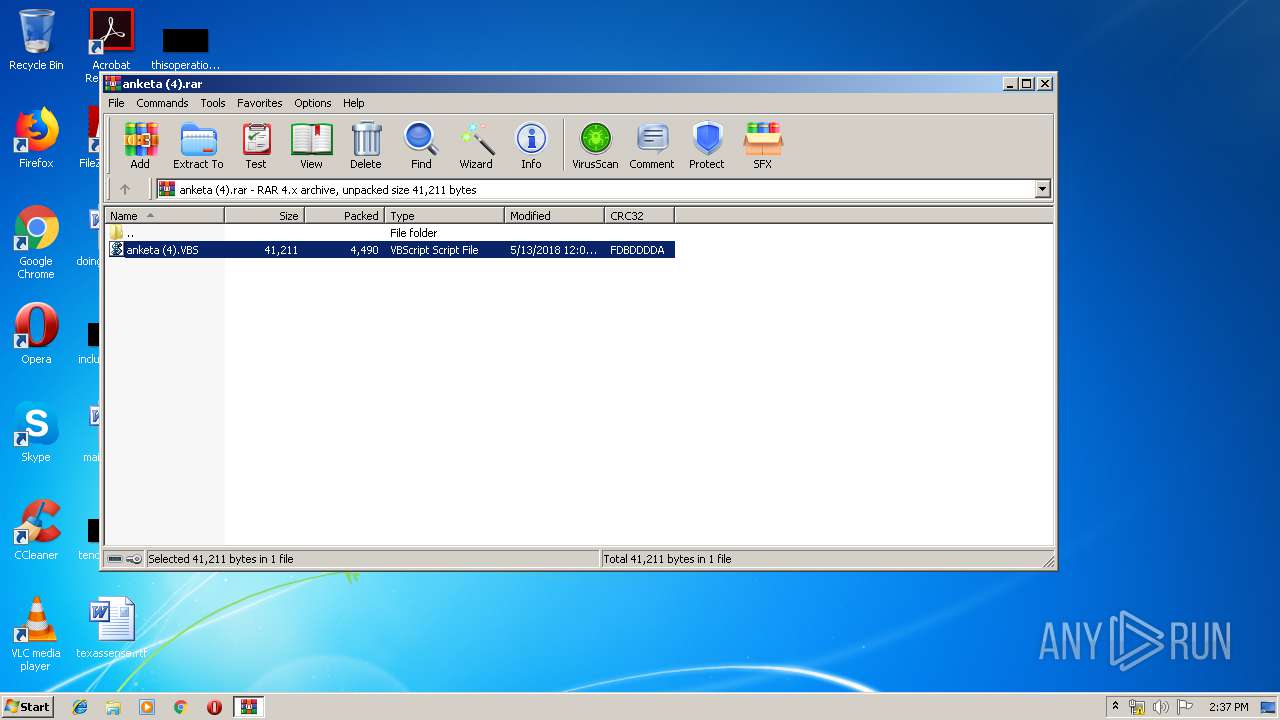
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | E6749813F96ADE4A17781BB8C44B89DE |
| SHA1: | B3BE0244EE7DA6B6A80731DD40769C4722A74FB9 |
| SHA256: | 600EB581FCFFF2267AA676104E373ACCEF1F403CDCA3A378DD87B9F820019206 |
| SSDEEP: | 96:FTqXG5YYBtgpSBZDX0JnEo3cjRXTTIVv4N4ea7elHBEd/FbxbFpa:FTPYYXgw7DEJR+RyvM4ehqd/7bFpa |
MALICIOUS
Changes the autorun value in the registry
- powershell.exe (PID: 2156)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 1484)
- powershell.exe (PID: 2156)
- powershell.exe (PID: 3300)
Starts NET.EXE for network exploration
- cmd.exe (PID: 3196)
Executes scripts
- WinRAR.exe (PID: 2180)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 2488)
Executes PowerShell scripts
- WScript.exe (PID: 2488)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 4052)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 4530 |
|---|---|
| UncompressedSize: | 41211 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2018:05:13 12:02:24 |
| PackingMethod: | Normal |
| ArchivedFileName: | anketa (4).VBS |
Total processes
49
Monitored processes
11
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 536 | systeminfo | C:\Windows\system32\systeminfo.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Displays system information Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | "C:\Windows\System32\cmd.exe" /C nslookup e > ~tmp_ns.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1484 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command Copy-Item -Path "C:\Users\admin\AppData\Local\Temp\Rar$DIa2180.43424\anketa (4).VBS" -Destination "C:\Users\admin\AppData\Roaming\ptWTRrRKFOYCDFjQeQKMeVTwr.vbs" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command New-ItemProperty -Path HKCU:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run -Name ARSv5 -PropertyType String -Value C:\Users\admin\AppData\Roaming\ptWTRrRKFOYCDFjQeQKMeVTwr.vbs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\anketa (4).rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2488 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2180.43424\anketa (4).VBS" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3196 | "C:\Windows\System32\cmd.exe" /C net view> ~tmp_nv.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3300 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command New-ItemProperty -Path HKLM:\SOFTWARE\Microsoft\Windows\CurrentVersion\Run -Name ARSv5 -PropertyType String -Value C:\Users\admin\AppData\Roaming\ptWTRrRKFOYCDFjQeQKMeVTwr.vbs | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | net view | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Windows\System32\cmd.exe" /C systeminfo > ~tmp_si.txt | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 081
Read events
879
Write events
202
Delete events
0
Modification events
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\anketa (4).rar | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4802 |
Value: VBScript Script File | |||
| (PID) Process: | (2180) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1484 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\A9VSRCY3HI6Y9LFYT5E9.temp | — | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LQMYG31X4UHQ4KDFLVQJ.temp | — | |
MD5:— | SHA256:— | |||
| 3300 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\23VTVW06AQET09U7Q3DH.temp | — | |
MD5:— | SHA256:— | |||
| 1484 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFe919d.TMP | binary | |
MD5:— | SHA256:— | |||
| 2180 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2180.43424\anketa (4).VBS | text | |
MD5:— | SHA256:— | |||
| 1484 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4052 | cmd.exe | C:\Users\admin\AppData\Local\Temp\~tmp_si.txt | text | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2156 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFedec3.TMP | binary | |
MD5:— | SHA256:— | |||
| 3300 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFee27c.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
12
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
cloud-protection-service.bid |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
e |
| unknown |