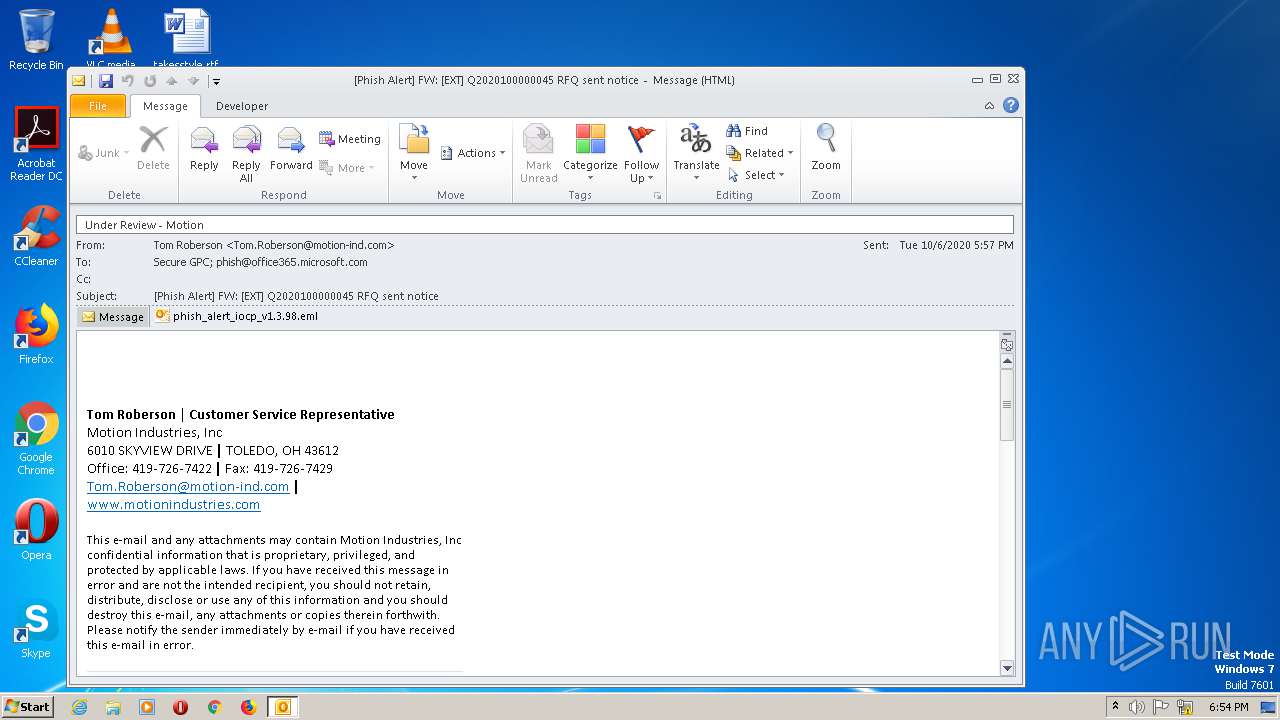
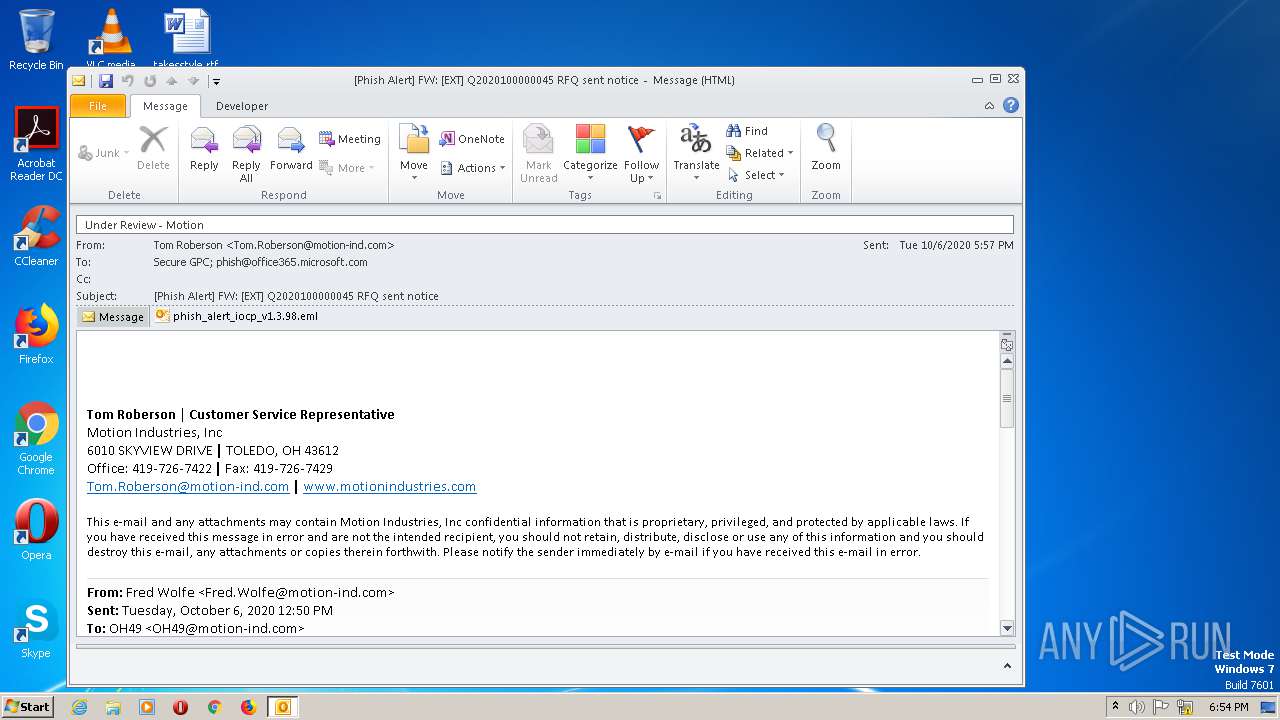
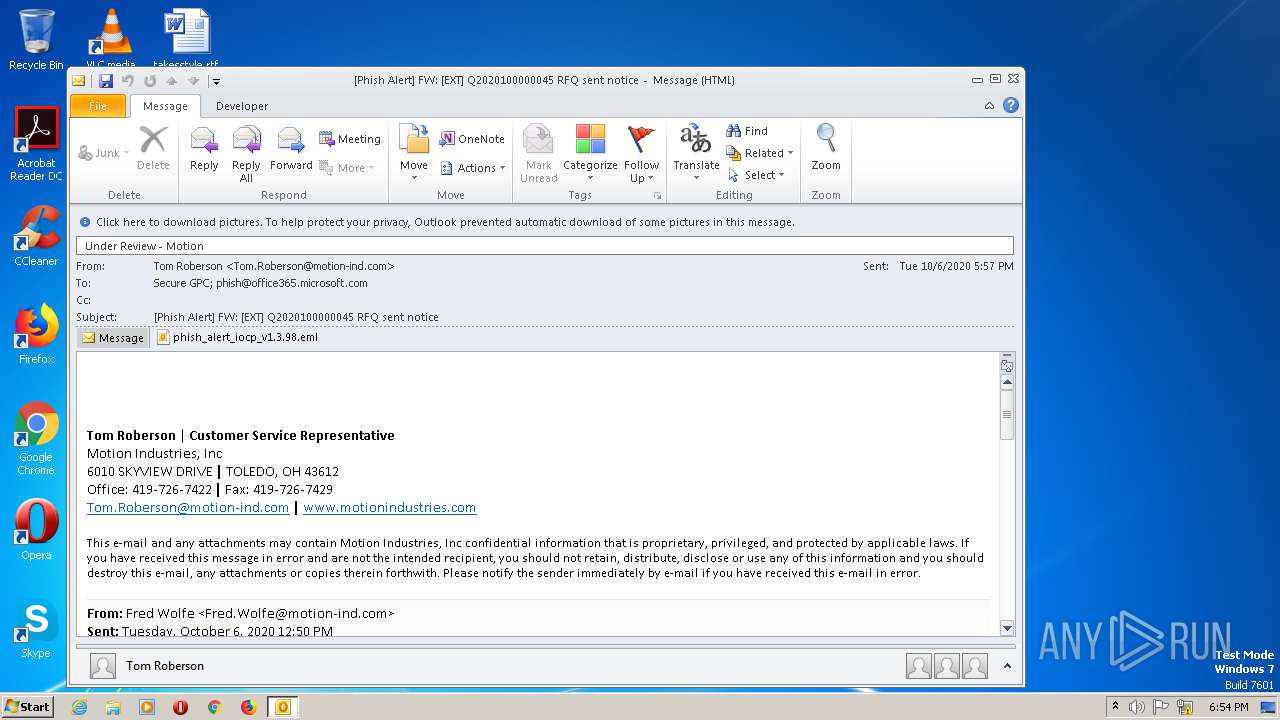
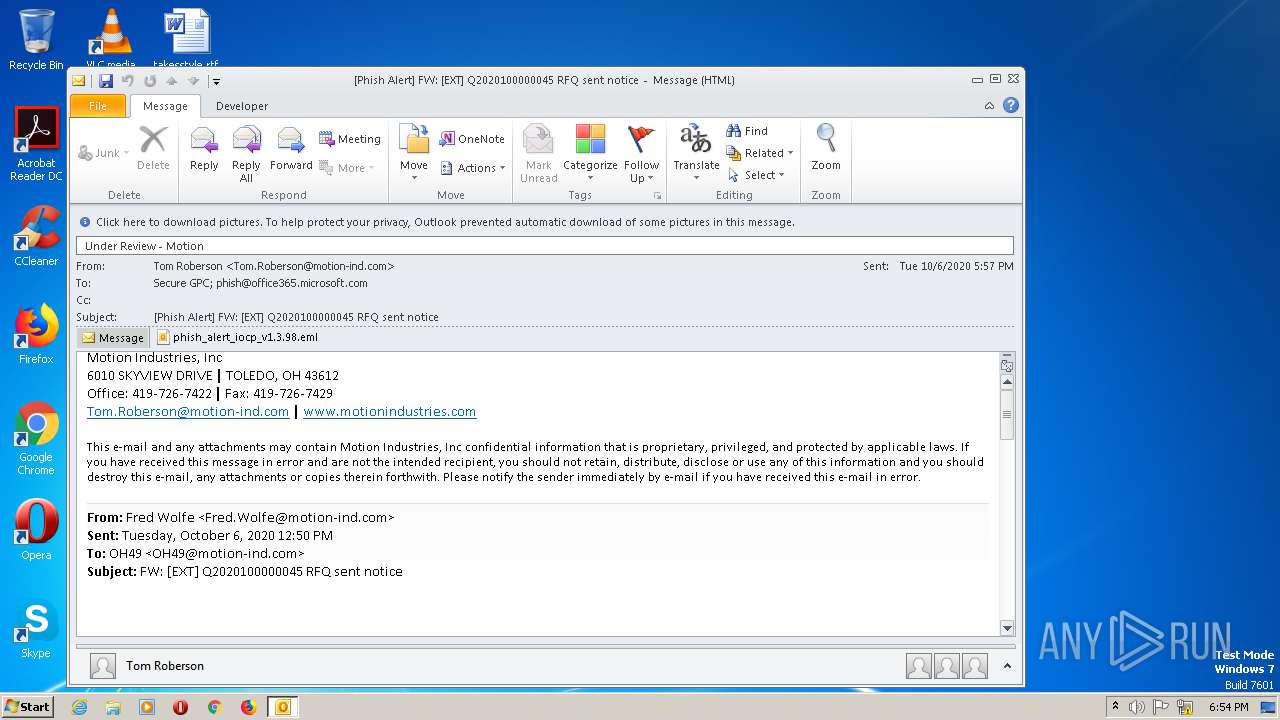
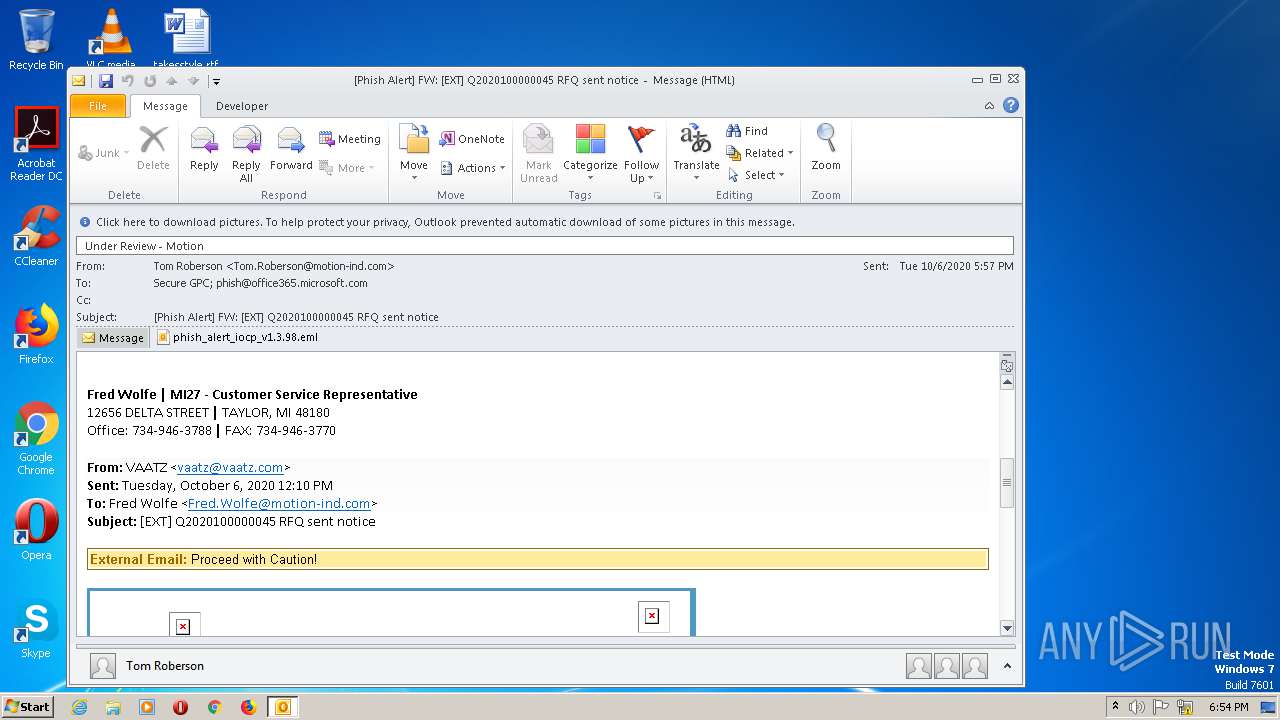
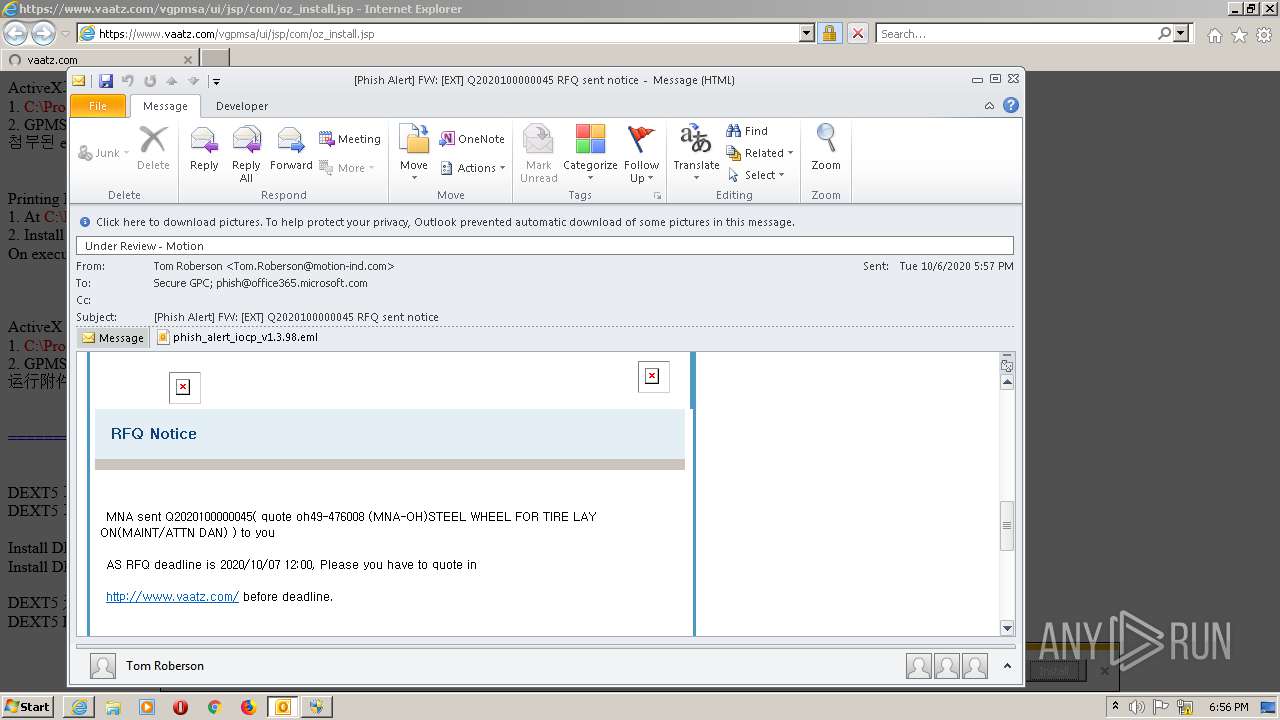
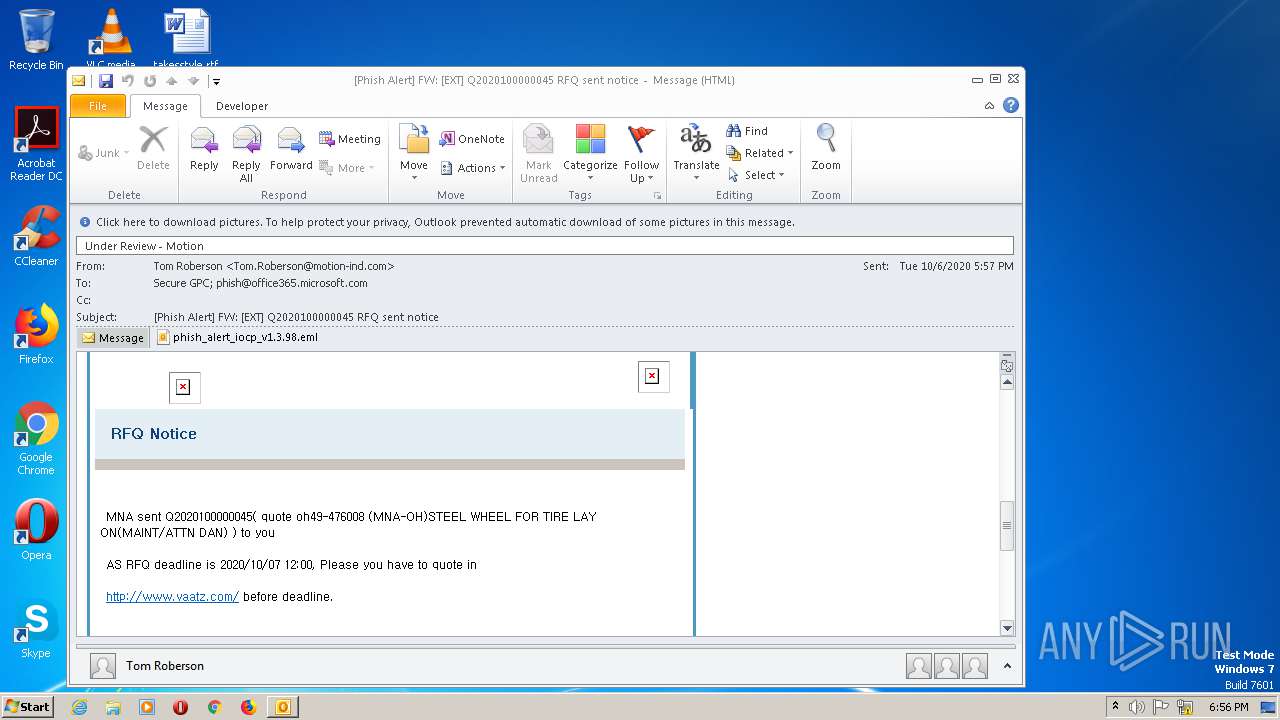
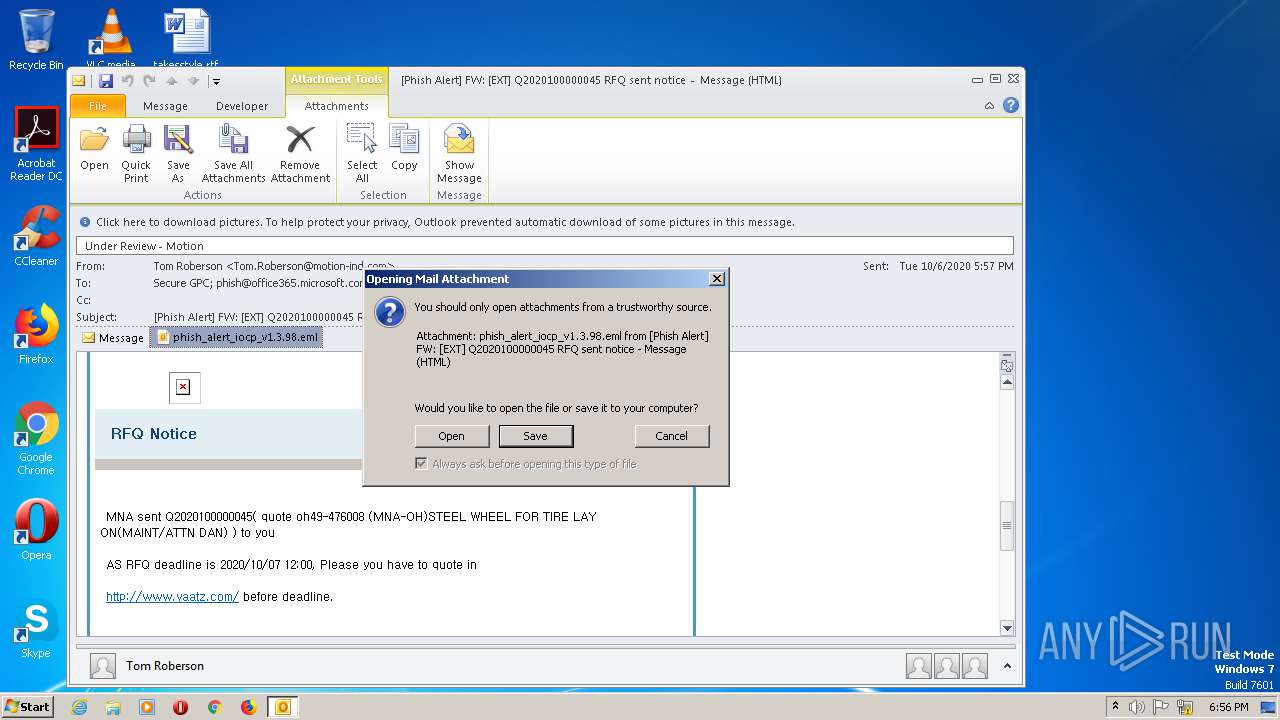
| File name: | Phish Alert FW EXT Q2020100000045 RFQ sent notice.msg |
| Full analysis: | https://app.any.run/tasks/681f8849-5d74-496f-b759-ab1bc26c5ea0 |
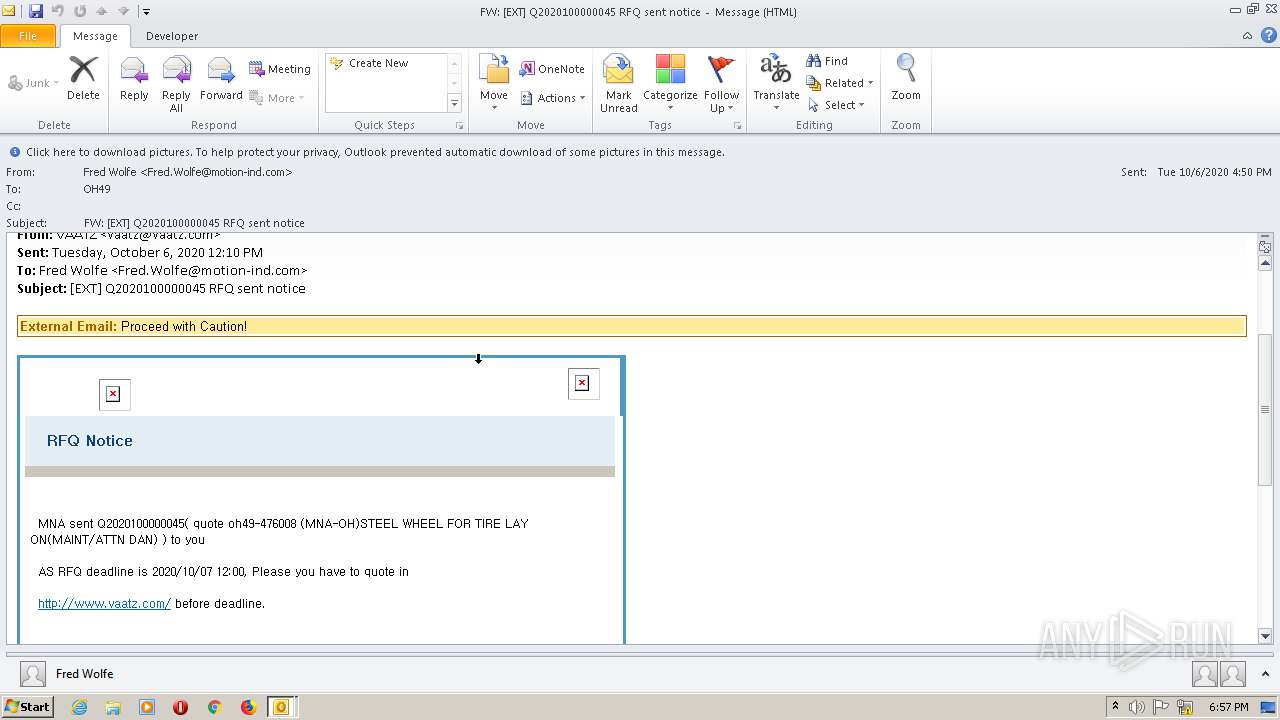
| Verdict: | Malicious activity |
| Analysis date: | October 06, 2020, 18:54:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 6A20A836ED87F4996C191D02FC7E15AA |
| SHA1: | 92E60A8194180F5E6E8CDA8F3FC6739CCC76459E |
| SHA256: | 600E95C6C6E64D53BC863F5F86D1B89BA480B3BB7AF2872F60698B8DF651AB30 |
| SSDEEP: | 1536:ZYi3gaqnWQ2QSf7eojHc0iSWZjZ3YjW5NRTdBQspAZ0Npmi:ZQ2Bj3HpiZZoCNyZ0jmi |
MALICIOUS
Changes settings of System certificates
- IEInstal.exe (PID: 2668)
- IEInstal.exe (PID: 932)
Loads dropped or rewritten executable
- IEInstal.exe (PID: 2668)
- DllHost.exe (PID: 2432)
- IEXPLORE.EXE (PID: 2816)
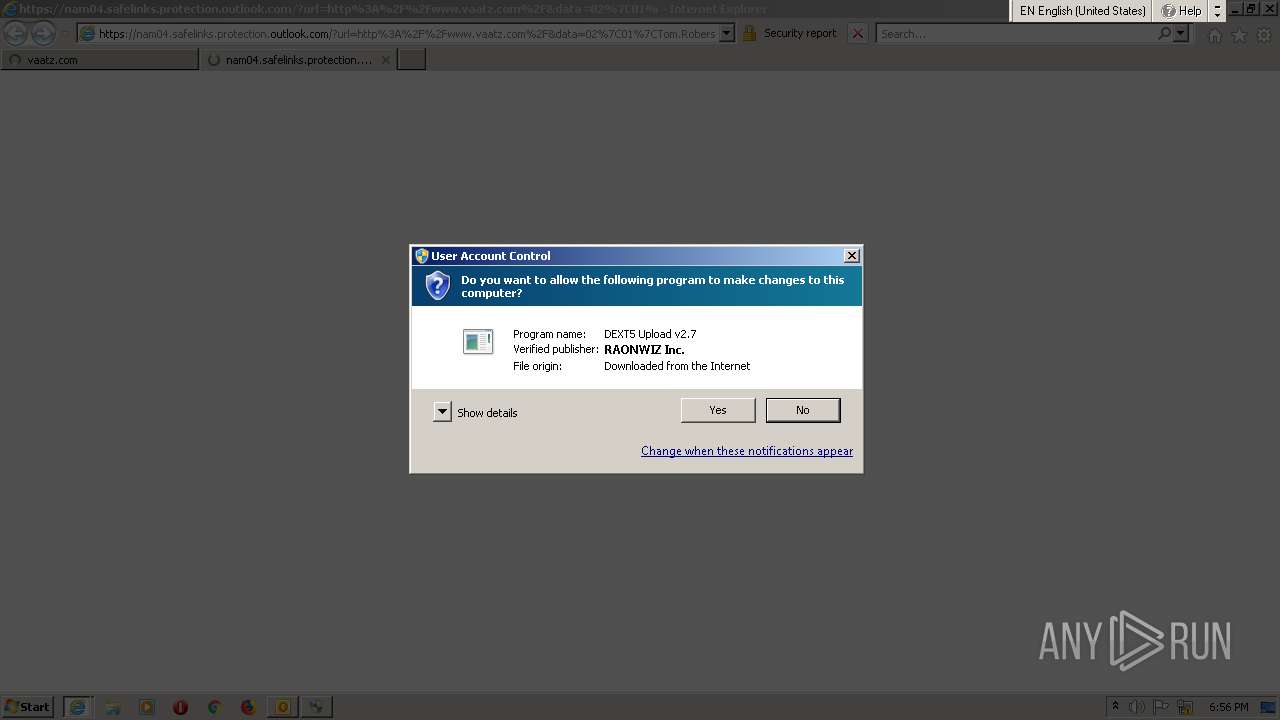
Application was dropped or rewritten from another process
- dext5upload.exe (PID: 2028)
Changes internet zones settings
- dext5upload.exe (PID: 2028)
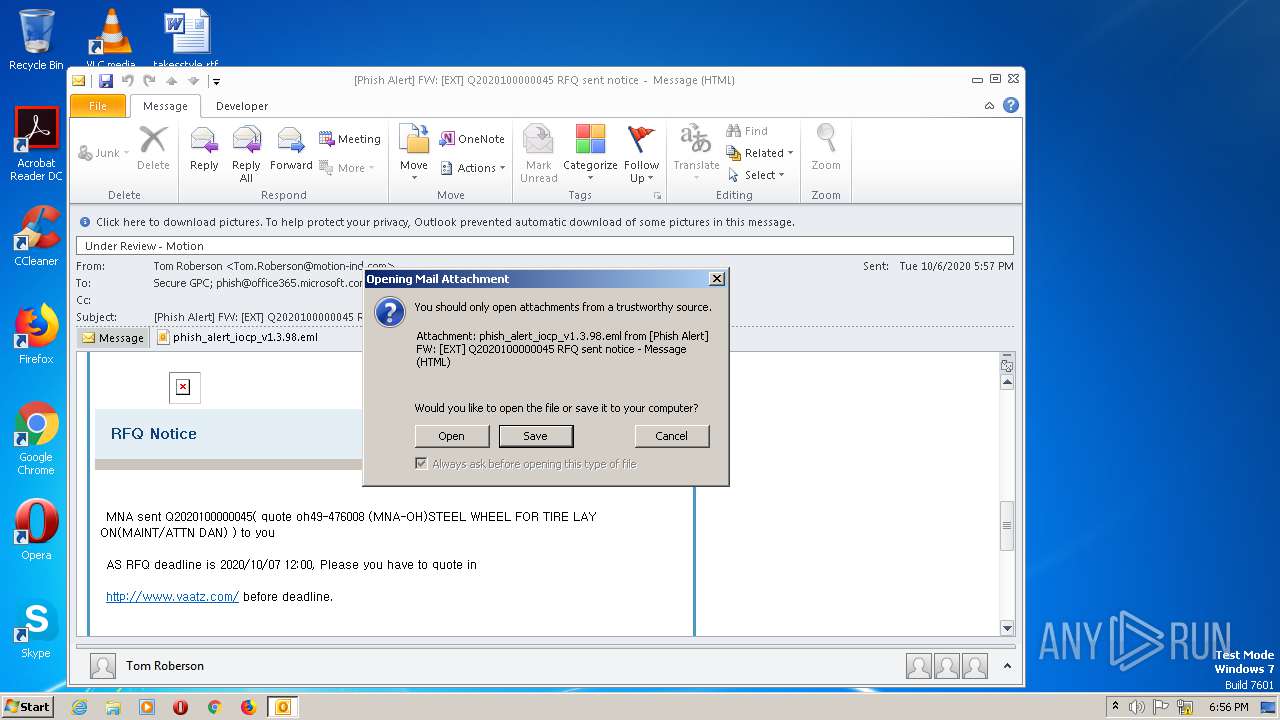
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 604)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 604)
Adds / modifies Windows certificates
- IEInstal.exe (PID: 2668)
- IEInstal.exe (PID: 932)
Executable content was dropped or overwritten
- IEInstal.exe (PID: 2668)
- DllHost.exe (PID: 2432)
- dext5upload.exe (PID: 2028)
- IEInstal.exe (PID: 932)
Removes files from Windows directory
- IEInstal.exe (PID: 2668)
- IEInstal.exe (PID: 932)
Executed via COM
- IEInstal.exe (PID: 2668)
- DllHost.exe (PID: 2432)
- IEInstal.exe (PID: 932)
Creates files in the Windows directory
- IEInstal.exe (PID: 2668)
- dext5upload.exe (PID: 2028)
- IEInstal.exe (PID: 932)
Creates COM task schedule object
- IEInstal.exe (PID: 2668)
- DllHost.exe (PID: 2432)
Creates files in the program directory
- DllHost.exe (PID: 2432)
Modifies the open verb of a shell class
- DllHost.exe (PID: 2432)
Changes IE settings (feature browser emulation)
- dext5upload.exe (PID: 2028)
Starts itself from another location
- OUTLOOK.EXE (PID: 604)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 604)
INFO
Creates files in the user directory
- IEXPLORE.EXE (PID: 2816)
- iexplore.exe (PID: 2536)
Reads the machine GUID from the registry
- iexplore.exe (PID: 2536)
- OUTLOOK.EXE (PID: 604)
Reads internet explorer settings
- IEXPLORE.EXE (PID: 2816)
- IEXPLORE.EXE (PID: 1788)
Changes settings of System certificates
- iexplore.exe (PID: 2536)
Reads settings of System Certificates
- IEXPLORE.EXE (PID: 2816)
- iexplore.exe (PID: 2536)
- IEXPLORE.EXE (PID: 1788)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 604)
- OUTLOOK.EXE (PID: 2124)
Changes internet zones settings
- iexplore.exe (PID: 2536)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 604)
- iexplore.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
53
Monitored processes
9
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
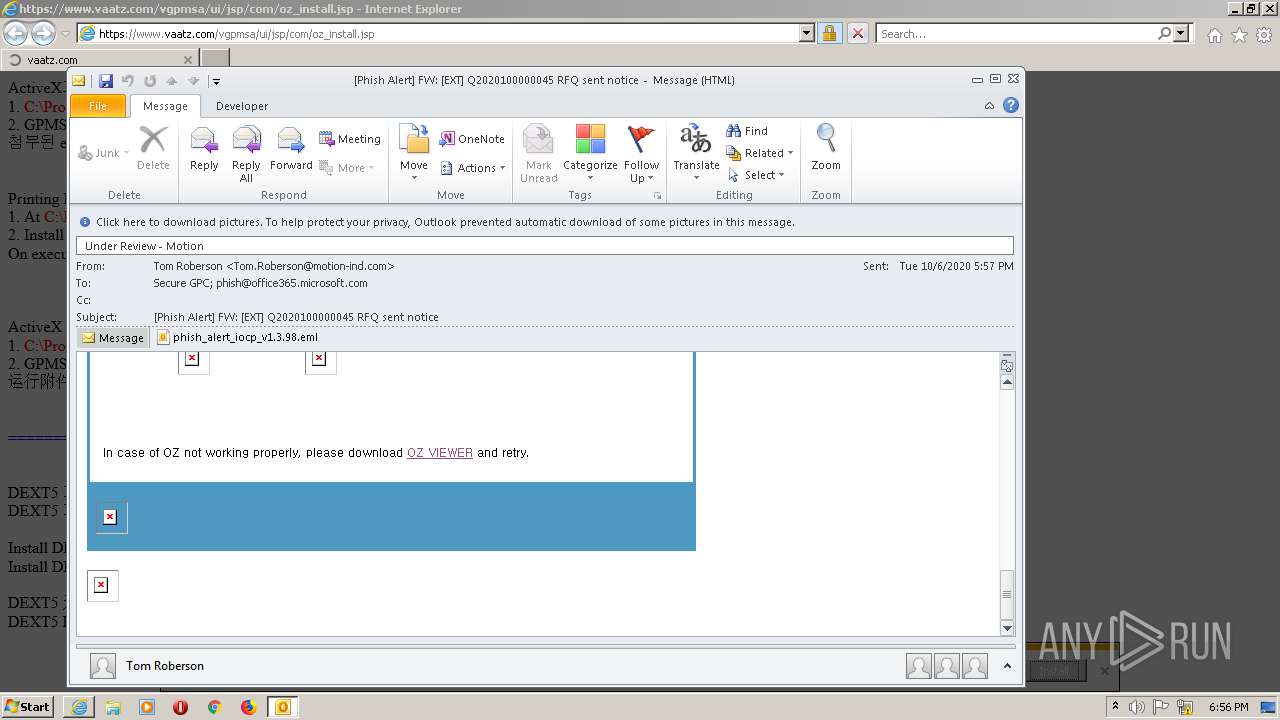
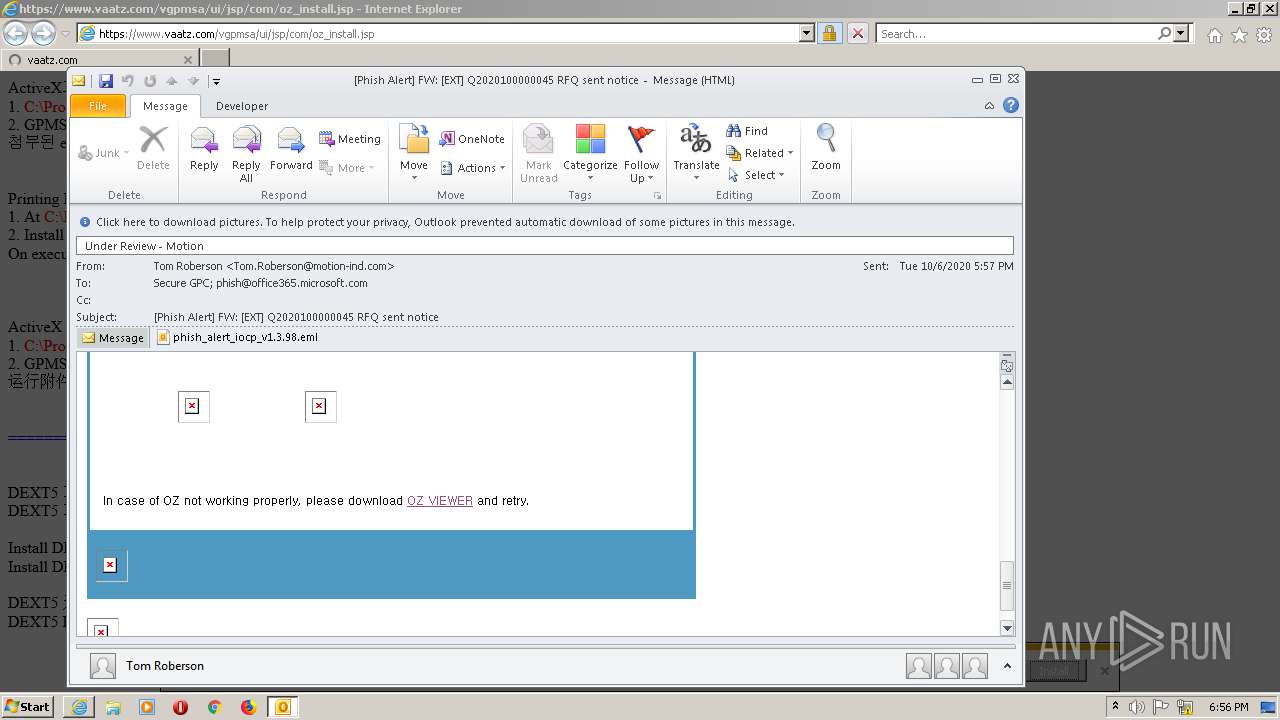
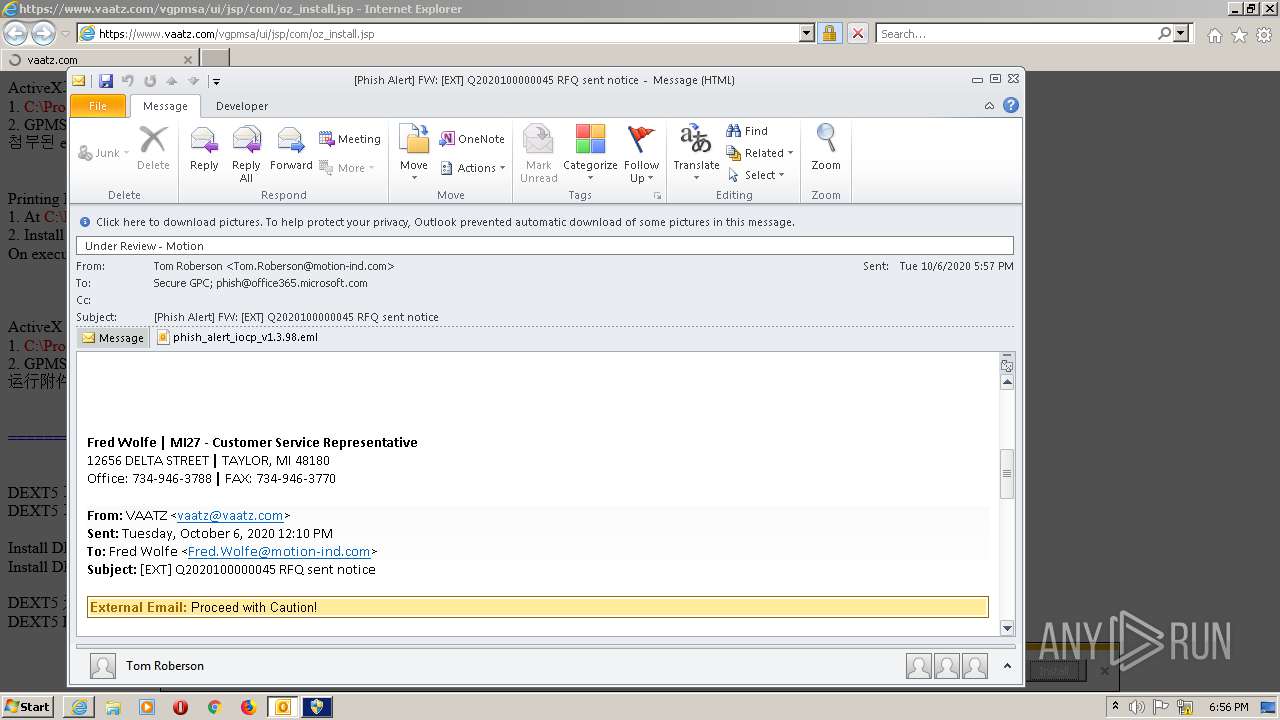
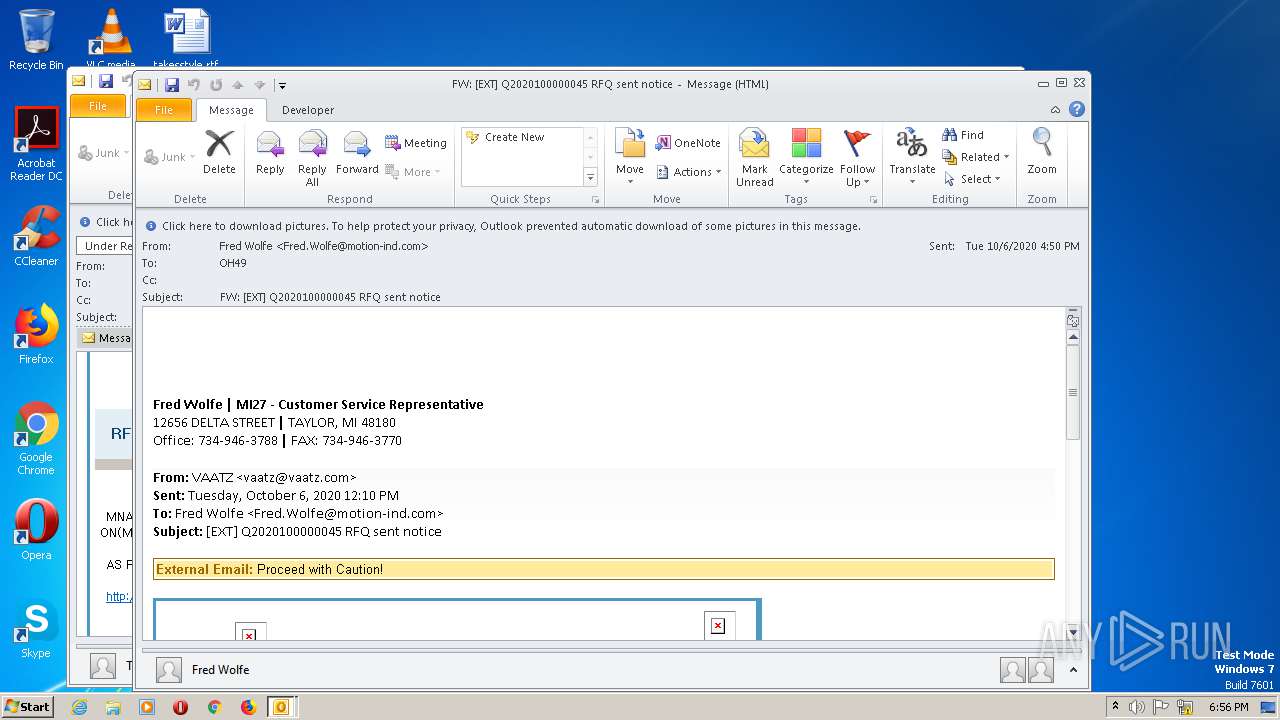
| 604 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Downloads\Phish Alert FW EXT Q2020100000045 RFQ sent notice.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.4760.1000 Modules
| |||||||||||||||
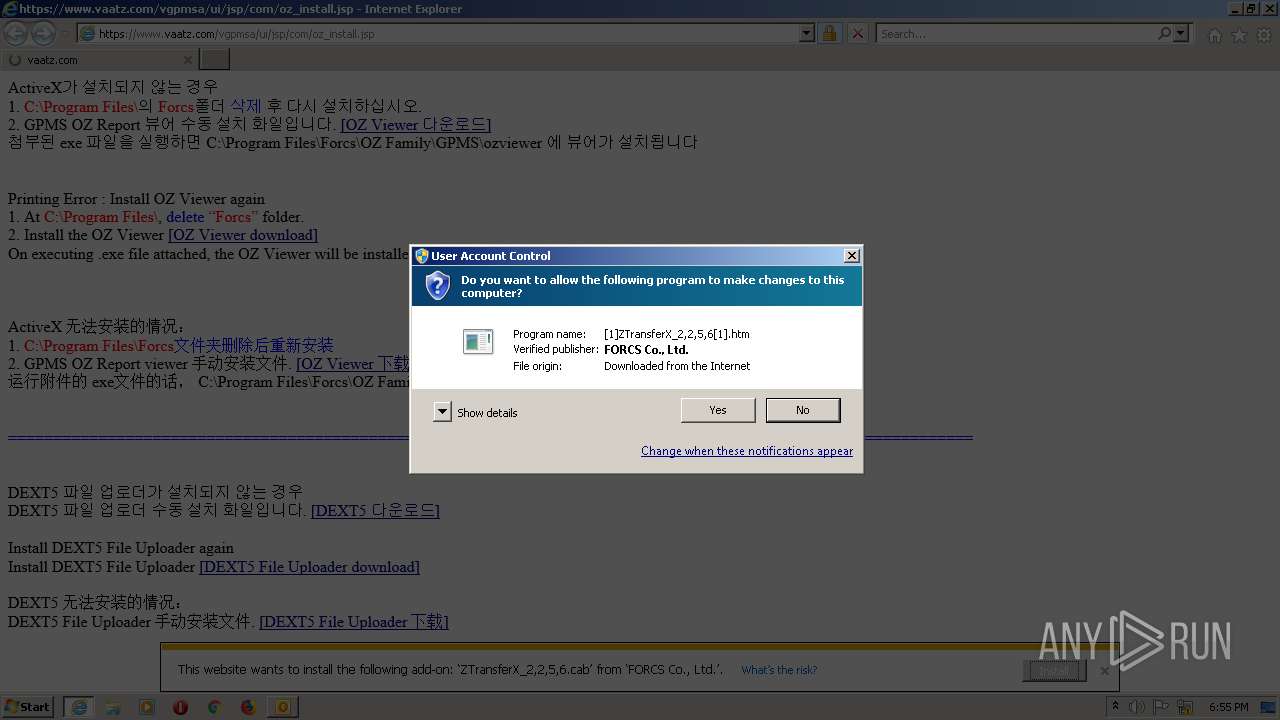
| 932 | "C:\Program Files (x86)\Internet Explorer\IEInstal.exe" -Embedding | C:\Program Files (x86)\Internet Explorer\IEInstal.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Add-on Installer Exit code: 2147942402 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1788 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2536 CREDAT:857364 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2028 | C:\Users\admin\AppData\Local\Temp\IDC2.tmp\dext5upload.exe | C:\Users\admin\AppData\Local\Temp\IDC2.tmp\dext5upload.exe | IEInstal.exe | ||||||||||||
User: admin Company: RAONWiZ Inc. Integrity Level: HIGH Description: DEXT5 Hybrid 50 Exit code: 0 Version: 5.0.0.111 Modules
| |||||||||||||||
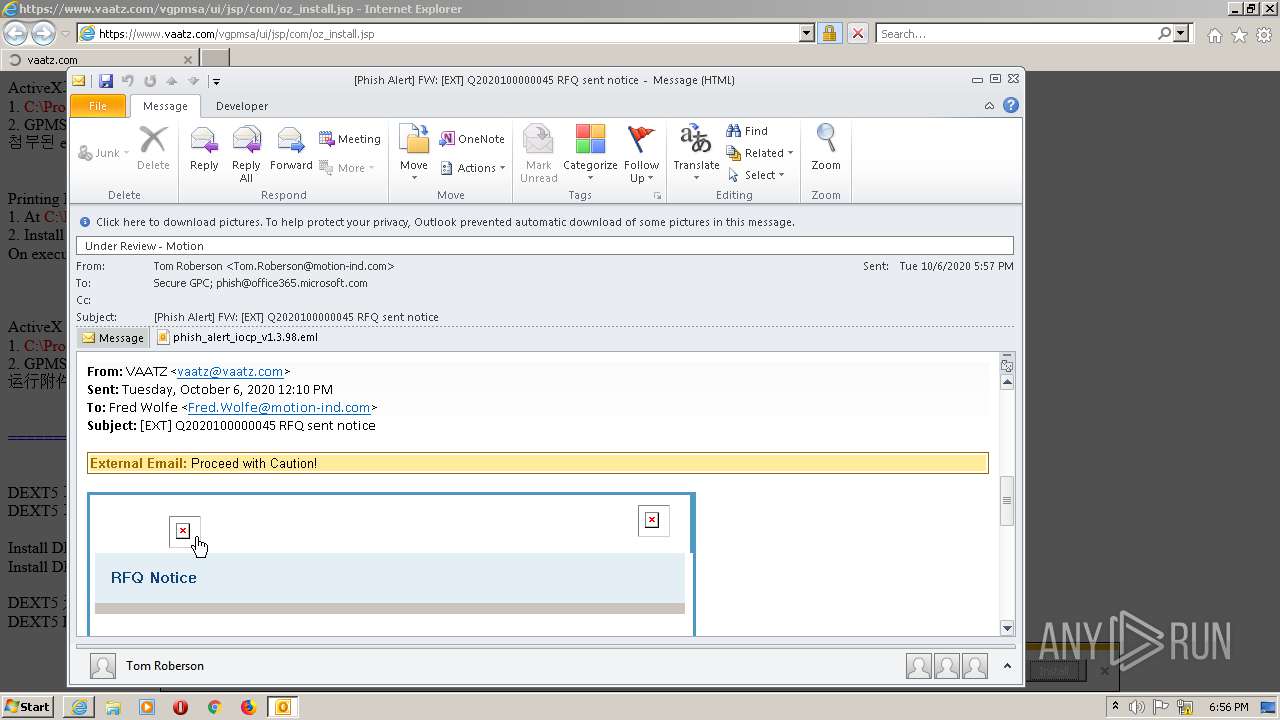
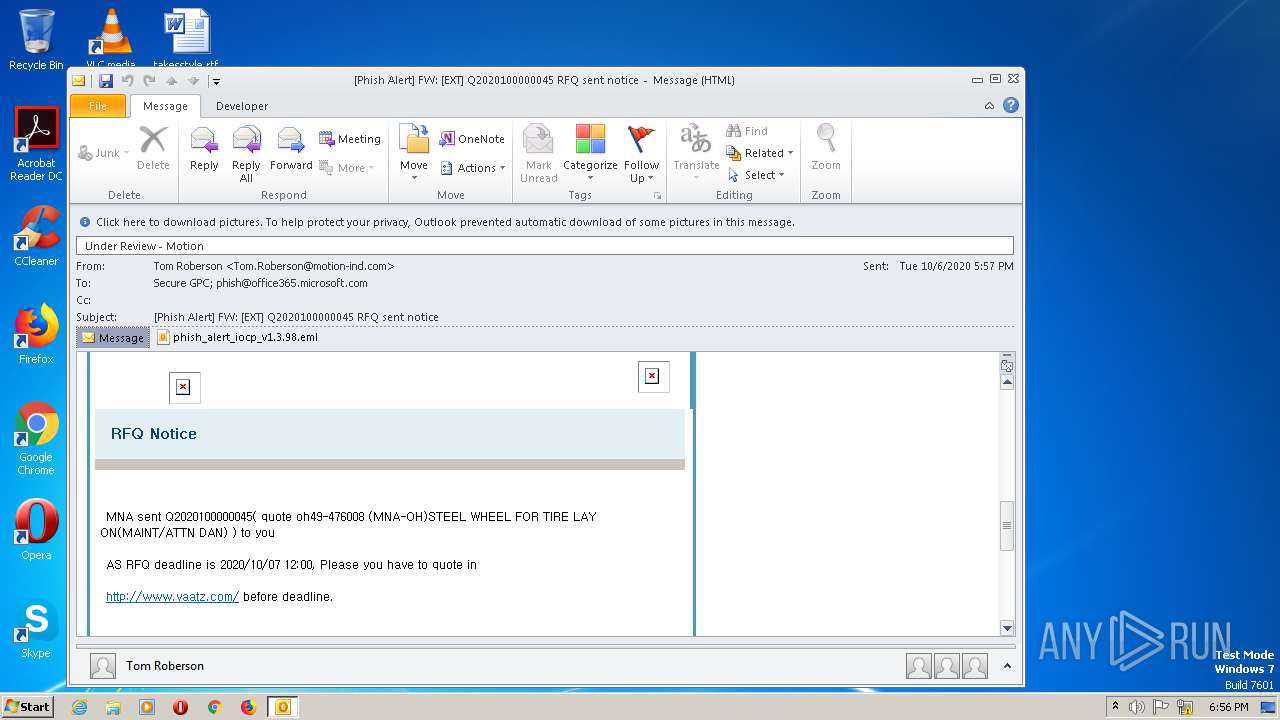
| 2124 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\XD1OXQRQ\phish_alert_iocp_v1 3 98.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.4760.1000 Modules
| |||||||||||||||
| 2432 | C:\Windows\SysWOW64\DllHost.exe /Processid:{B152CEE4-4106-4E81-A288-69097069B582} | C:\Windows\SysWOW64\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
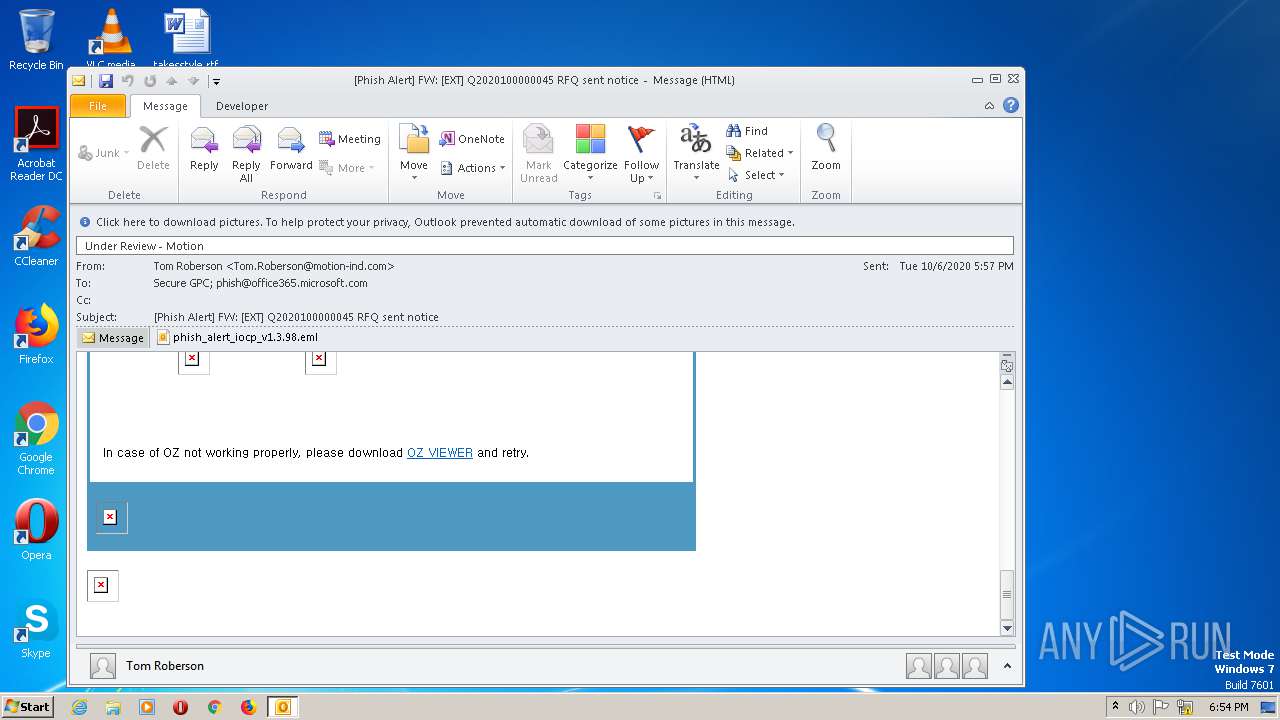
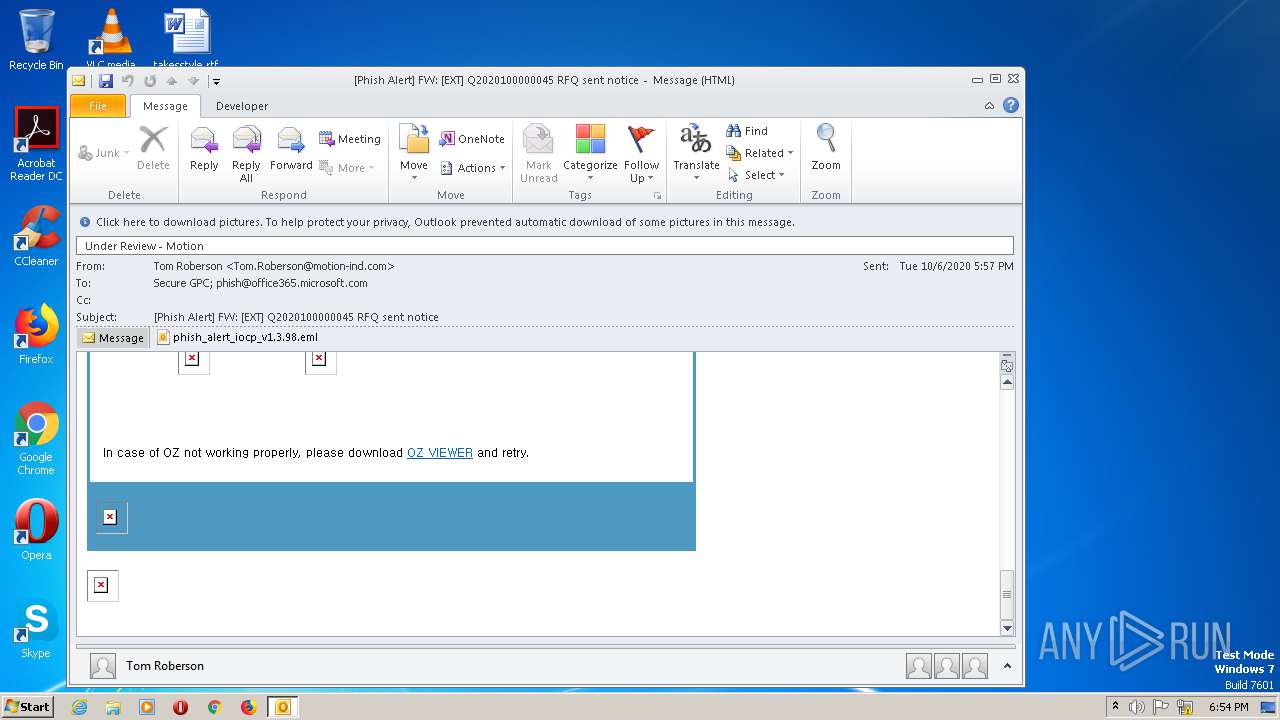
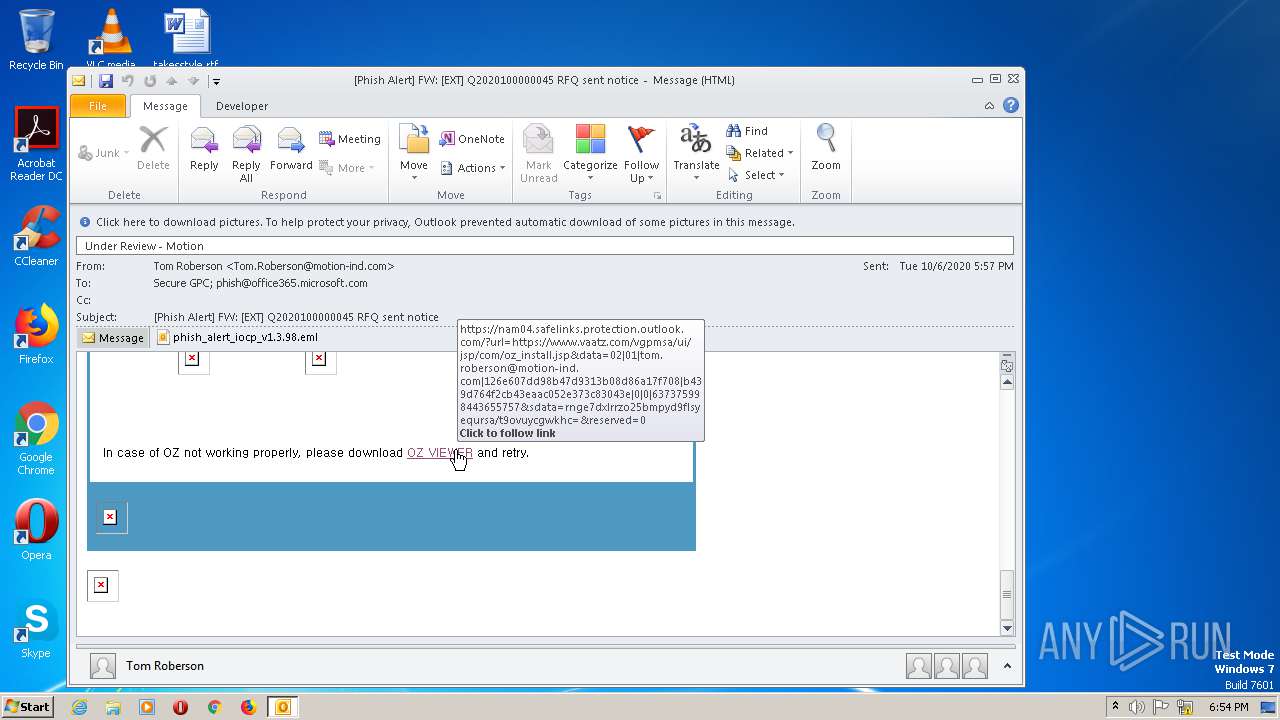
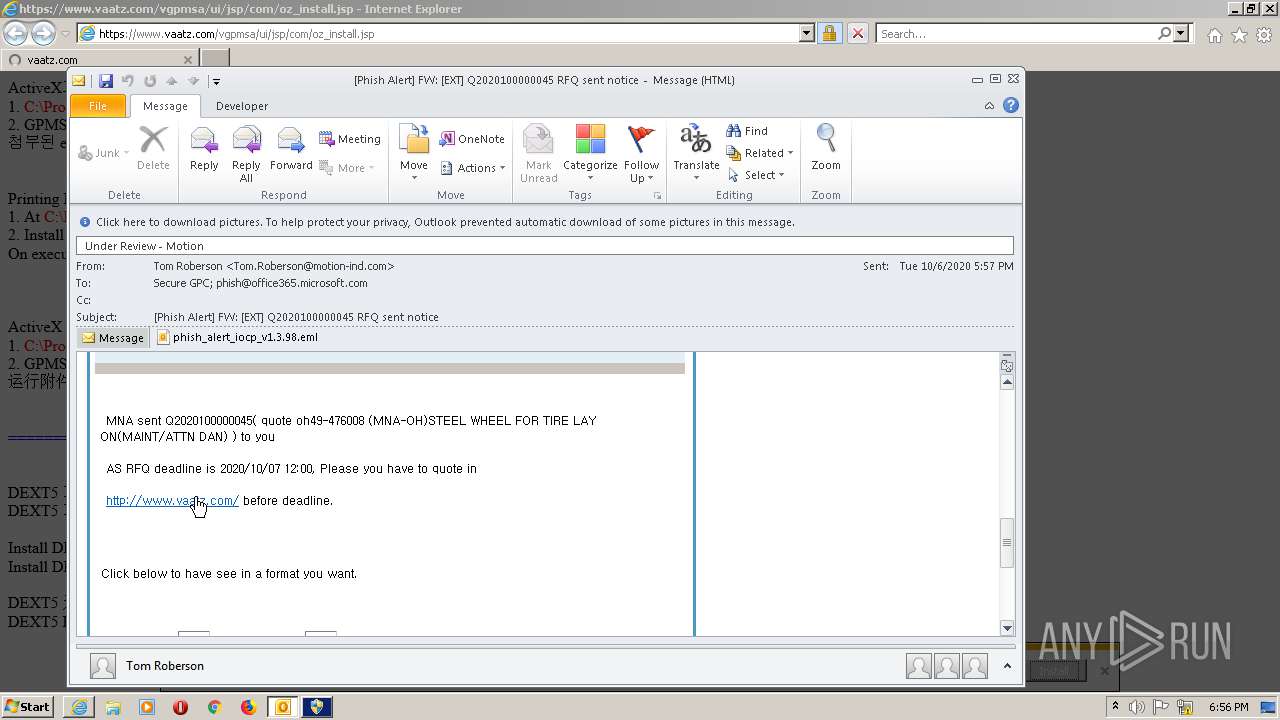
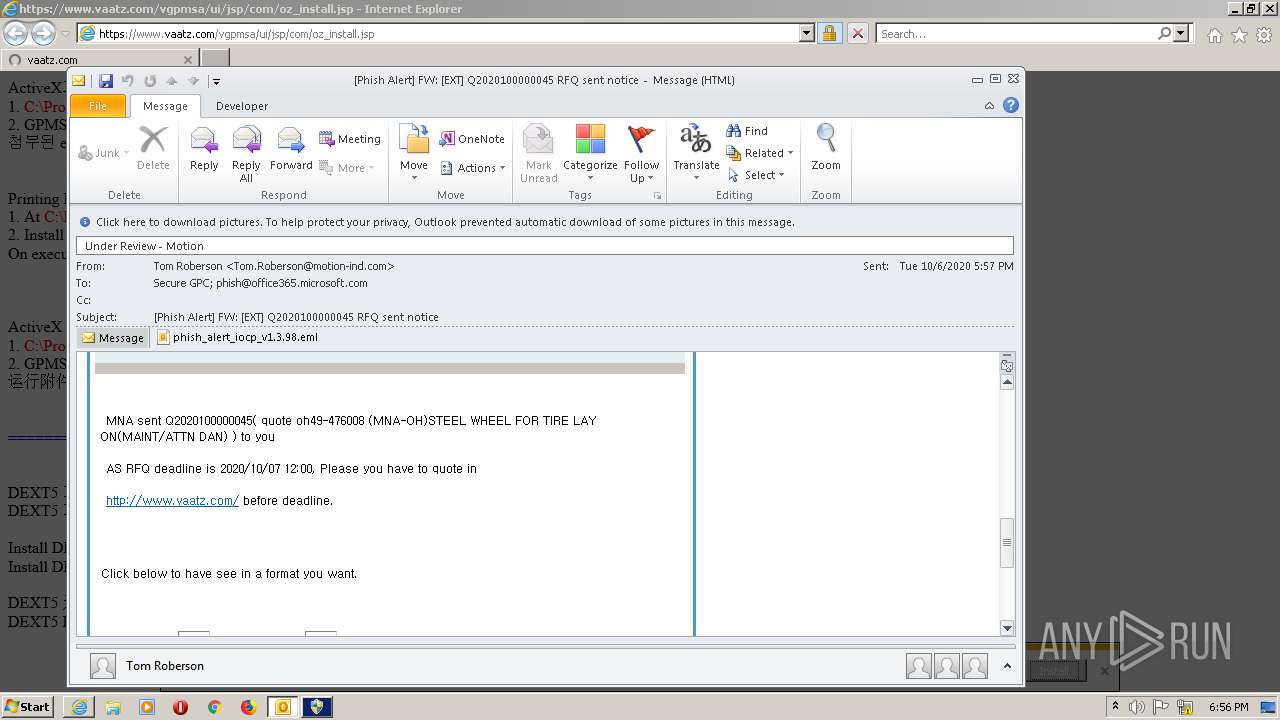
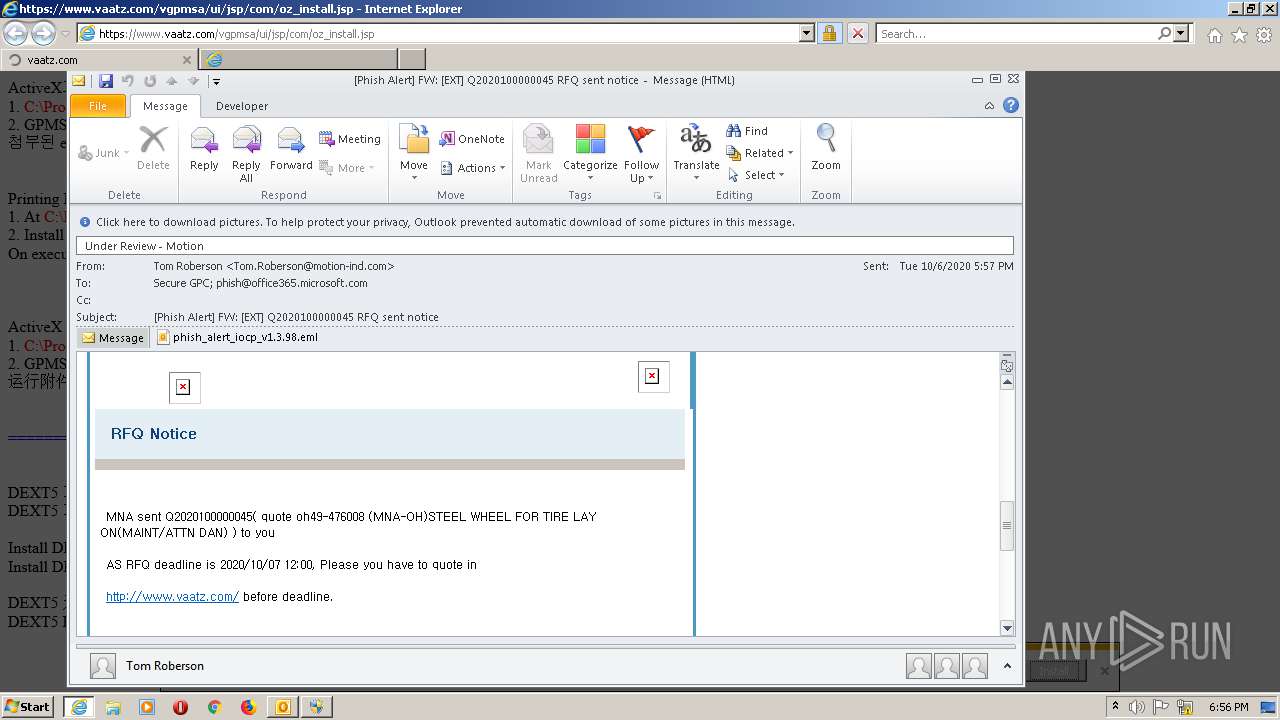
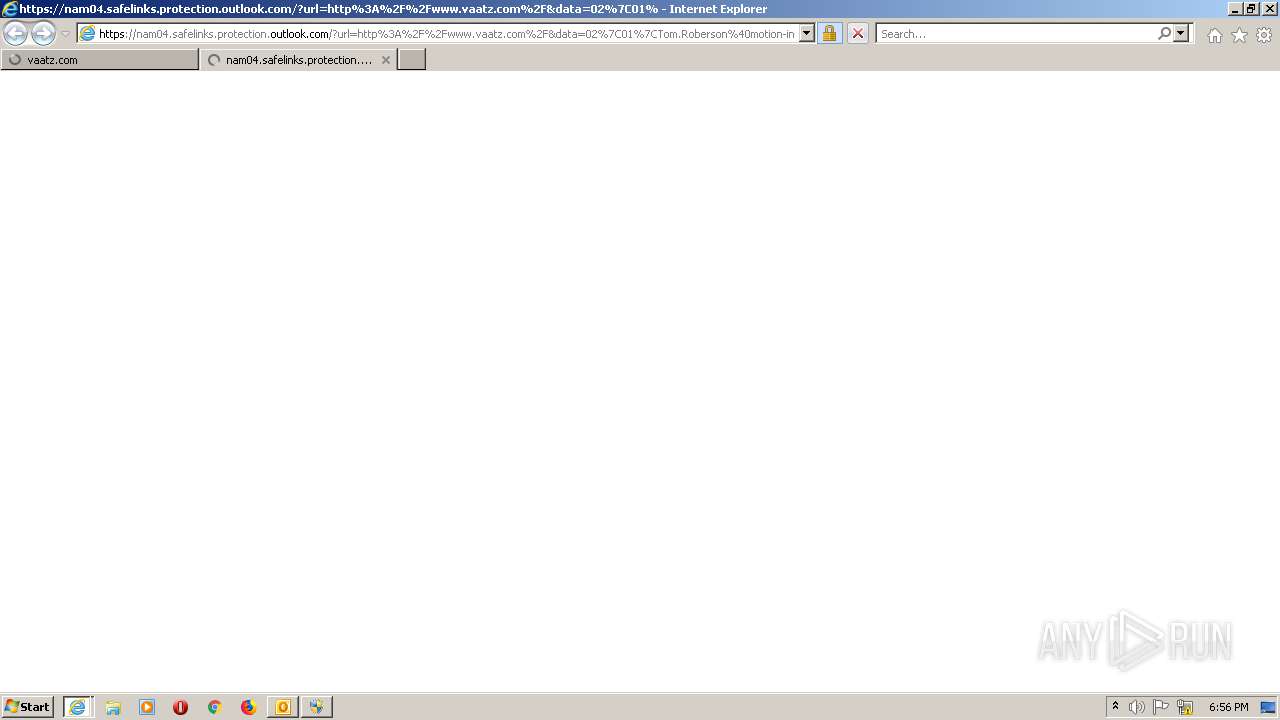
| 2536 | "C:\Program Files\Internet Explorer\iexplore.exe" https://nam04.safelinks.protection.outlook.com/?url=https%3A%2F%2Fwww.vaatz.com%2Fvgpmsa%2Fui%2Fjsp%2Fcom%2Foz_install.jsp&data=02%7C01%7CTom.Roberson%40motion-ind.com%7C126e607dd98b47d9313b08d86a17f708%7Cb439d764f2cb43eaac052e373c83043e%7C0%7C0%7C637375998443655757&sdata=rNGE7DxlRrzo25bmpyd9flSYEquRSA%2Ft9ovUyCgwKhc%3D&reserved=0 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2668 | "C:\Program Files (x86)\Internet Explorer\IEInstal.exe" -Embedding | C:\Program Files (x86)\Internet Explorer\IEInstal.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Add-on Installer Exit code: 2147942402 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2816 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:2536 CREDAT:267521 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
4 660
Read events
3 055
Write events
1 581
Delete events
24
Modification events
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (604) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
29
Suspicious files
18
Text files
284
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 604 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRED54.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 604 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 604 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8DBUF92Y.txt | text | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YQPEPCE1\0YML1RSR.HTM | html | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UJFUX3OG\oz_install[1].htm | html | |
MD5:— | SHA256:— | |||
| 2668 | IEInstal.exe | C:\Windows\Downloaded Program Files\SET91D1.tmp | — | |
MD5:— | SHA256:— | |||
| 2816 | IEXPLORE.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\ZOYIQ18X\oz_install[1].htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
174
TCP/UDP connections
40
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
604 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2536 | iexplore.exe | GET | 304 | 152.199.19.161:443 | https://iecvlist.microsoft.com/ie11blocklist/1401746408/versionlistWin7.xml | US | — | — | whitelisted |
2536 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://r20swj13mr.microsoft.com/ieblocklist/v1/urlblocklist.bin | US | — | — | whitelisted |
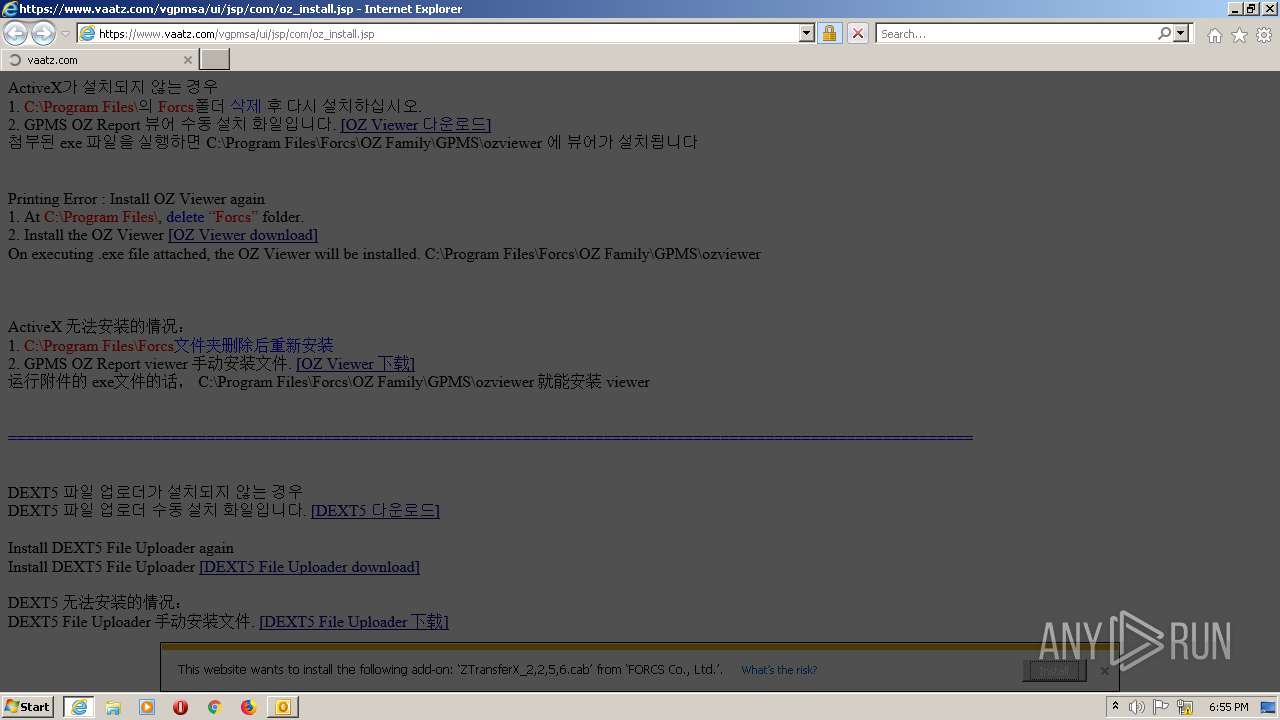
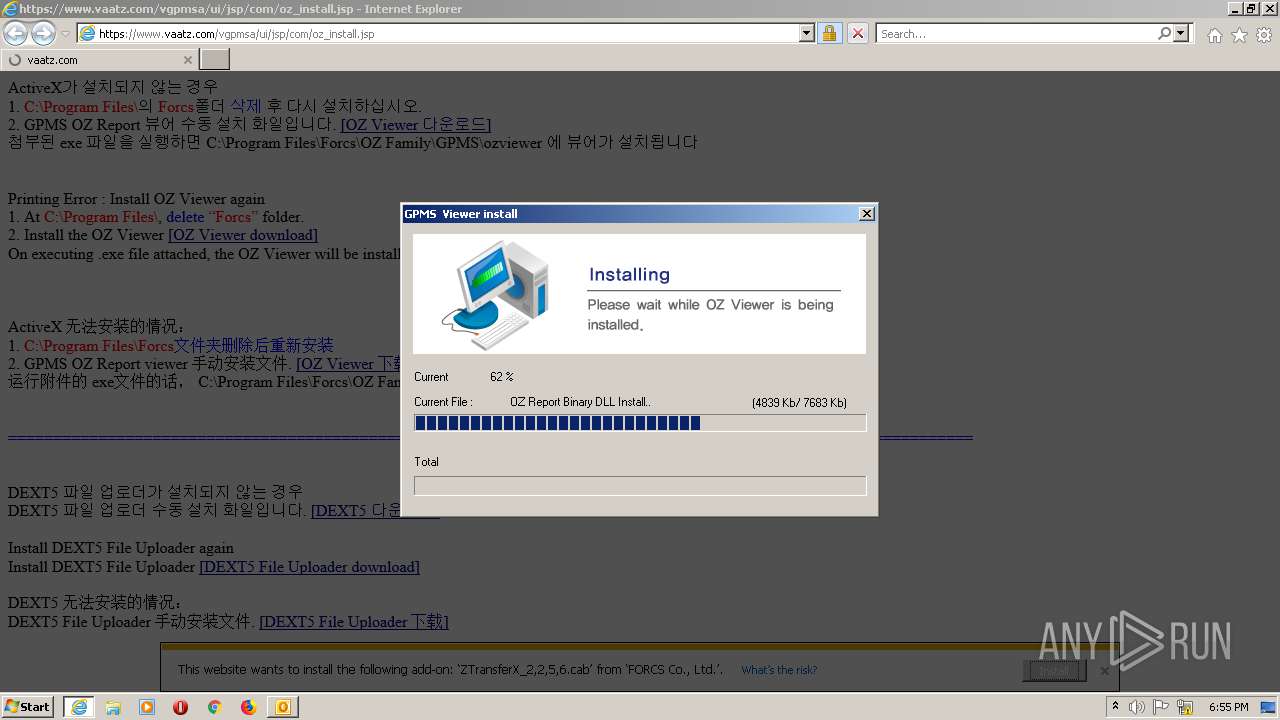
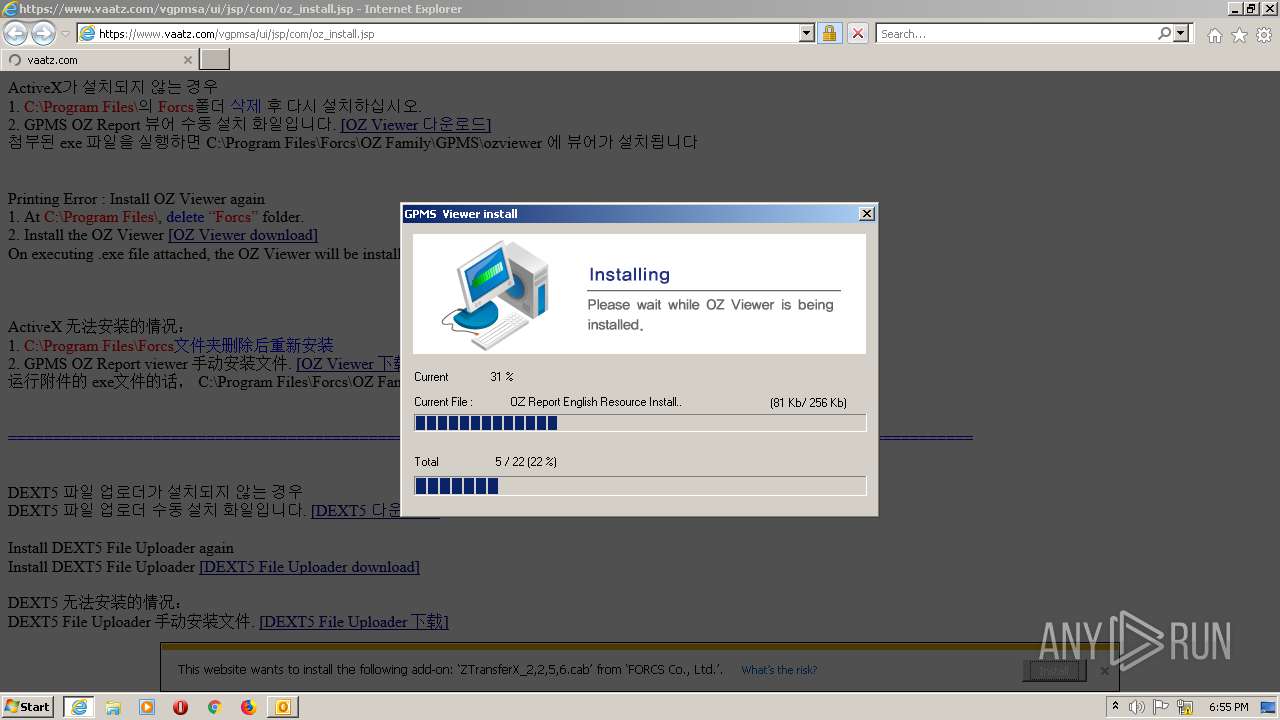
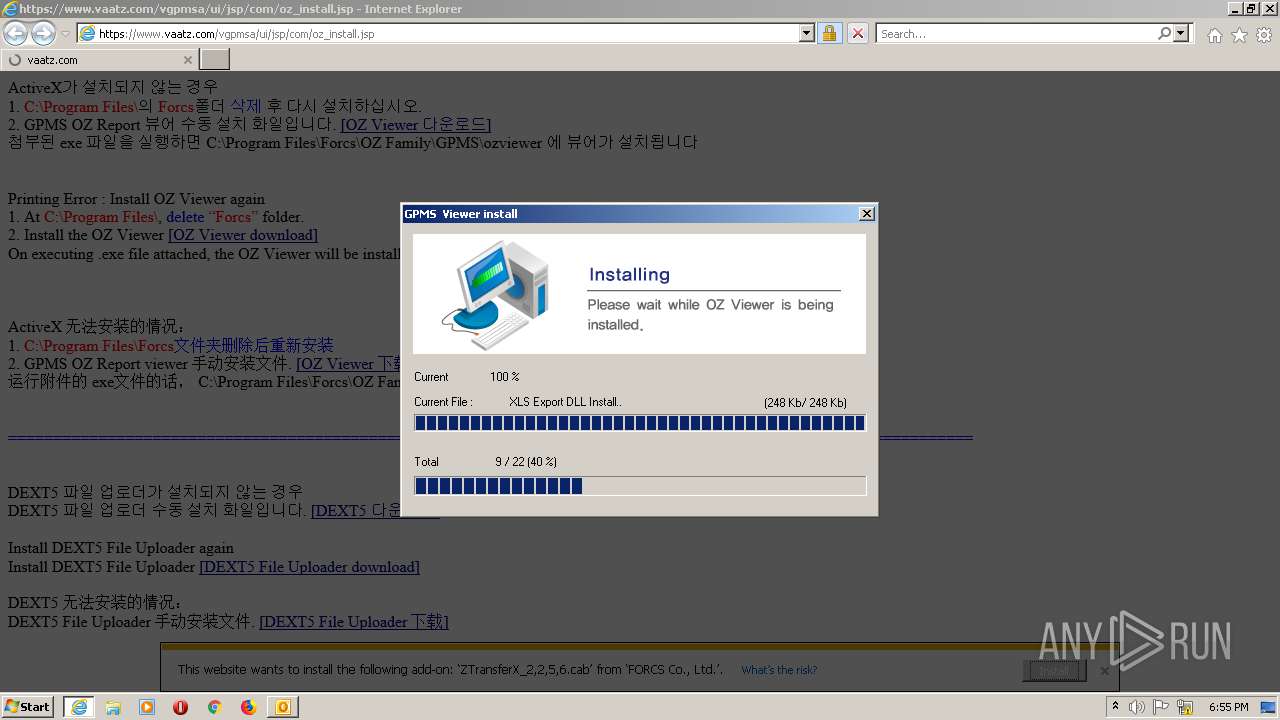
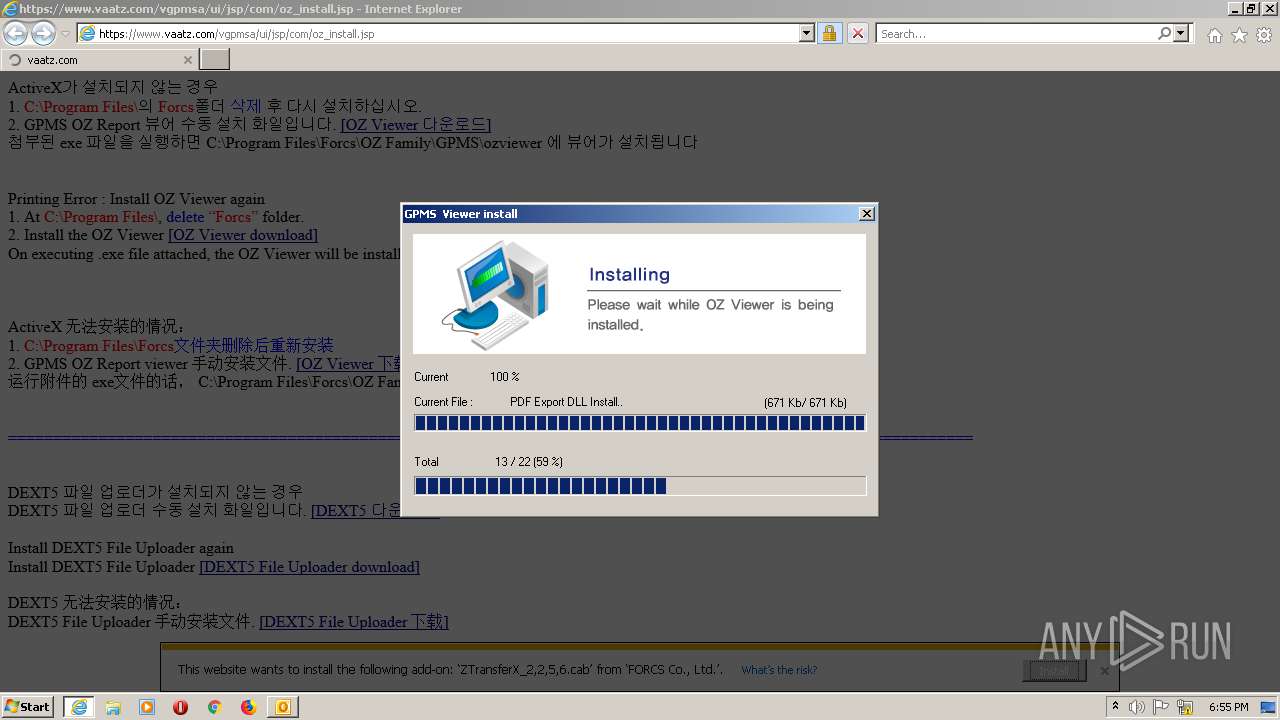
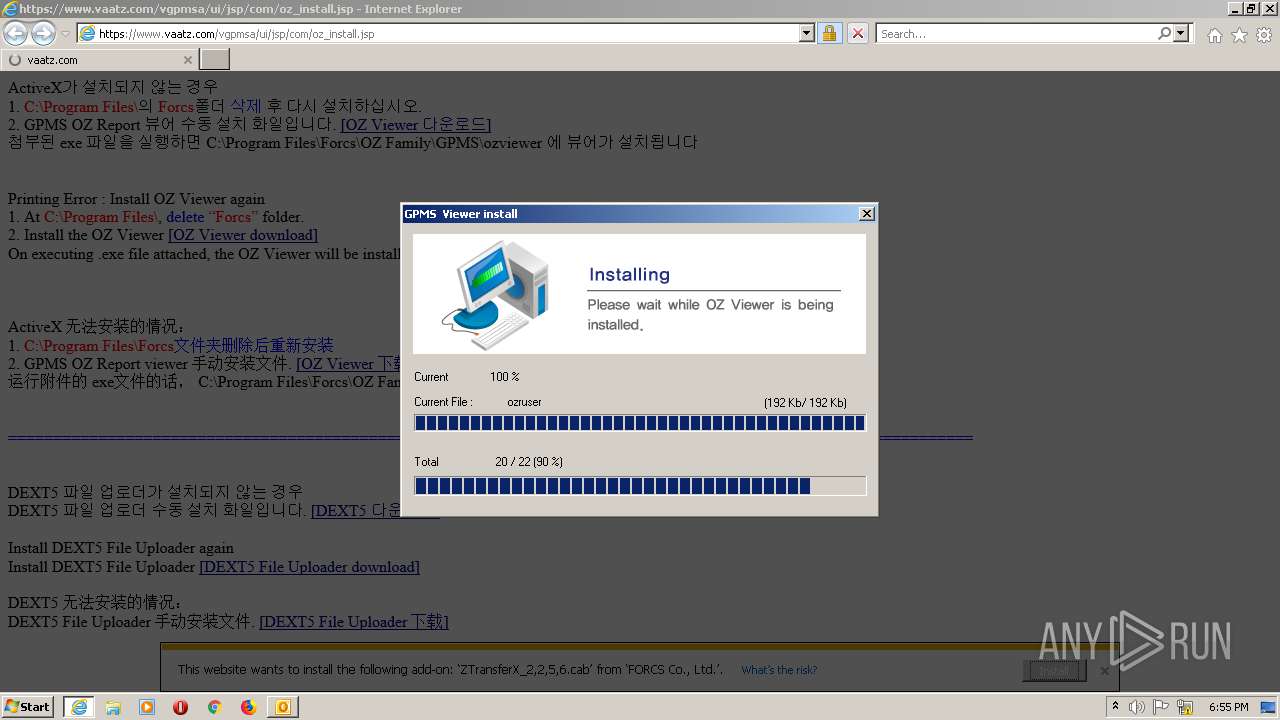
2816 | IEXPLORE.EXE | GET | 200 | 211.252.133.188:443 | https://api.vaatz.com/oz/ozrviewer/ZTransferX_2,2,5,6.cab | KR | compressed | 679 Kb | unknown |
2816 | IEXPLORE.EXE | GET | 200 | 211.252.134.107:443 | https://sol.vaatz.com/vaatzfile/dext5/plugin/dext5.cab | KR | compressed | 2.78 Mb | unknown |
2816 | IEXPLORE.EXE | GET | 200 | 211.252.133.188:443 | https://api.vaatz.com/oz/ozrviewer/ZTransferX_2,2,5,6.cab | KR | compressed | 679 Kb | unknown |
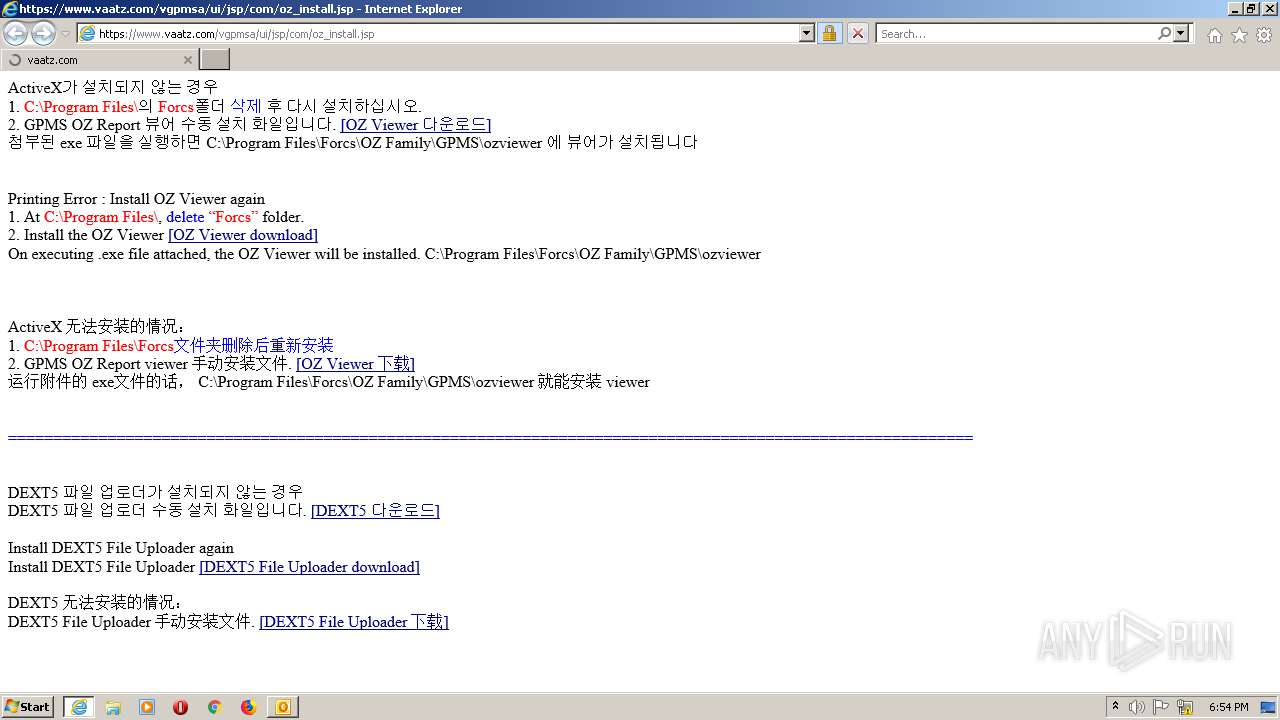
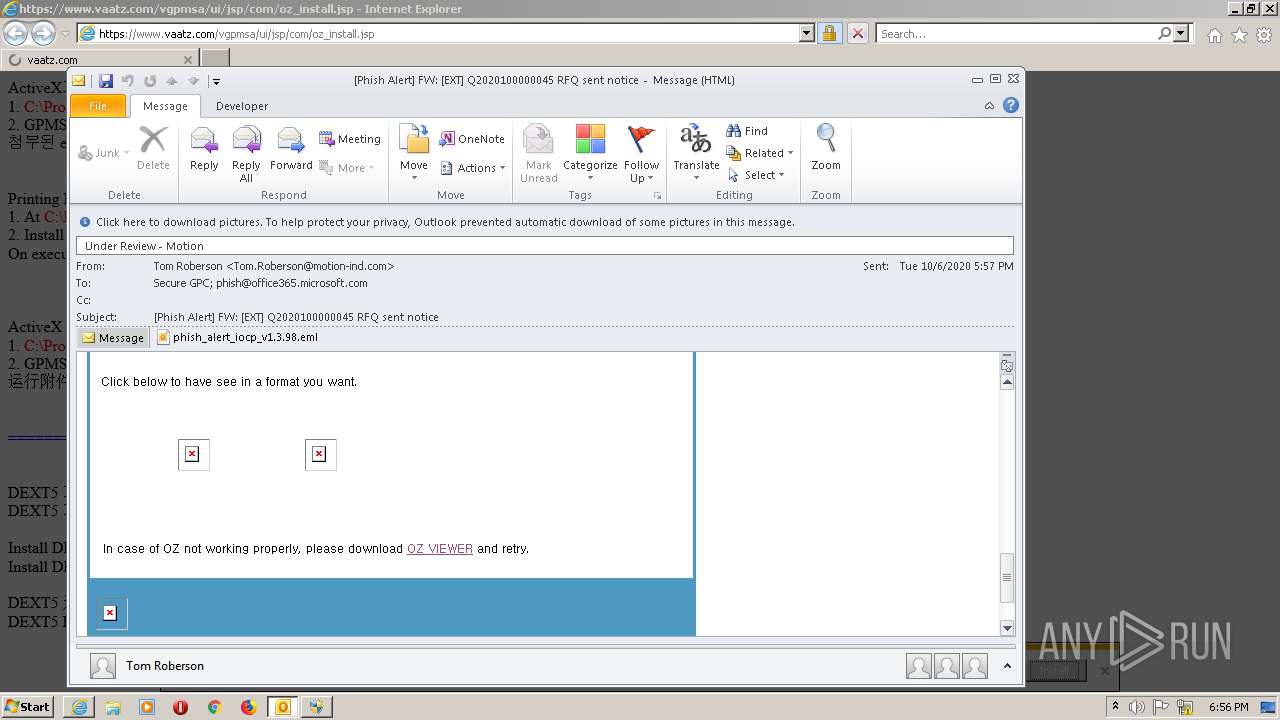
2816 | IEXPLORE.EXE | GET | 200 | 211.252.134.67:443 | https://www.vaatz.com/vgpmsa/ui/jsp/com/oz_install.jsp | KR | html | 3.83 Kb | unknown |
2816 | IEXPLORE.EXE | GET | 200 | 211.252.134.67:443 | https://www.vaatz.com/vgpmsa/ui/jsp/com/oz_install.jsp | KR | html | 3.83 Kb | unknown |
2536 | iexplore.exe | GET | 200 | 152.199.19.161:443 | https://iecvlist.microsoft.com/IE11/1479242656000/iecompatviewlist.xml | US | xml | 344 Kb | whitelisted |
2816 | IEXPLORE.EXE | GET | 200 | 211.252.133.188:443 | https://api.vaatz.com/oz/ozrviewer/ozrviewer.zip | KR | compressed | 7.33 Mb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
604 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2816 | IEXPLORE.EXE | 211.252.134.67:443 | www.vaatz.com | AutoEverSystems Corp. | KR | unknown |
2536 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2816 | IEXPLORE.EXE | 211.252.133.188:443 | api.vaatz.com | AutoEverSystems Corp. | KR | unknown |
2816 | IEXPLORE.EXE | 211.252.134.107:443 | sol.vaatz.com | AutoEverSystems Corp. | KR | unknown |
2536 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2536 | iexplore.exe | 104.108.39.131:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
2536 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2536 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
1788 | IEXPLORE.EXE | 211.252.134.67:443 | www.vaatz.com | AutoEverSystems Corp. | KR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
nam04.safelinks.protection.outlook.com |
| whitelisted |
www.vaatz.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
api.vaatz.com |
| unknown |
sol.vaatz.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |