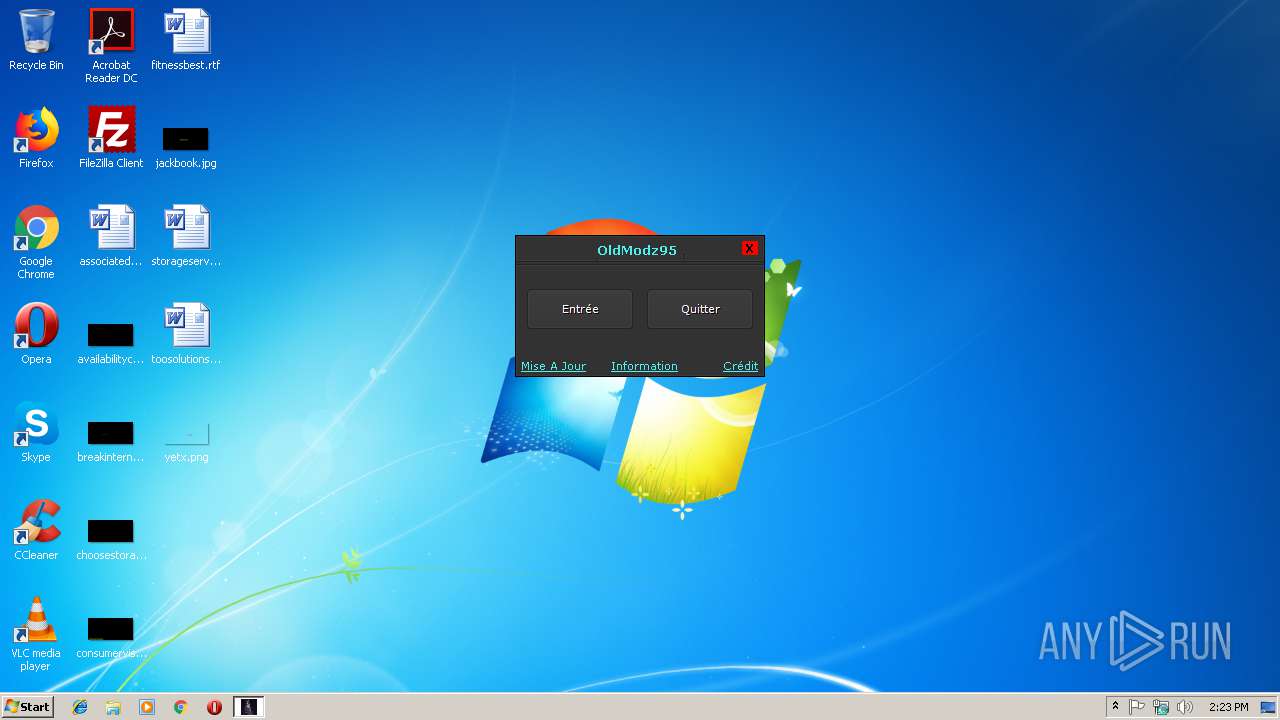
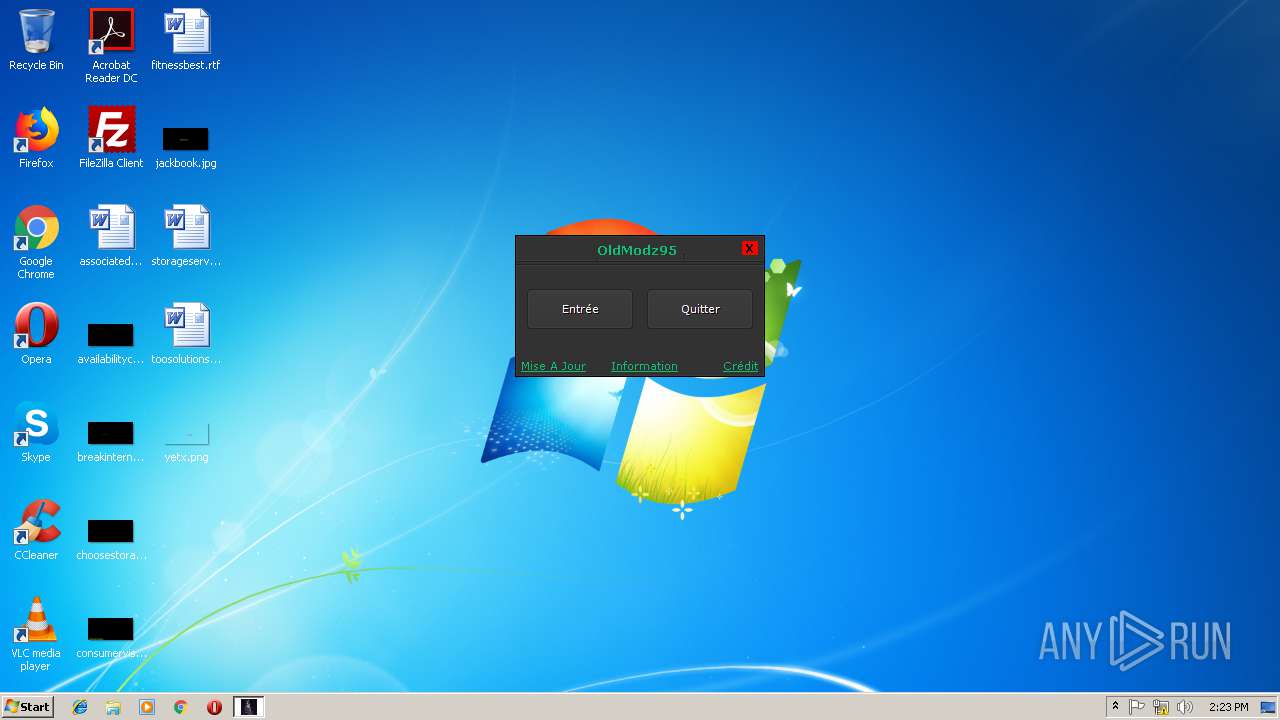
| File name: | Installeur Outil Tool-By OldModz95.exe |
| Full analysis: | https://app.any.run/tasks/be5c7acb-94d4-4f7e-8ce6-db400323e75e |
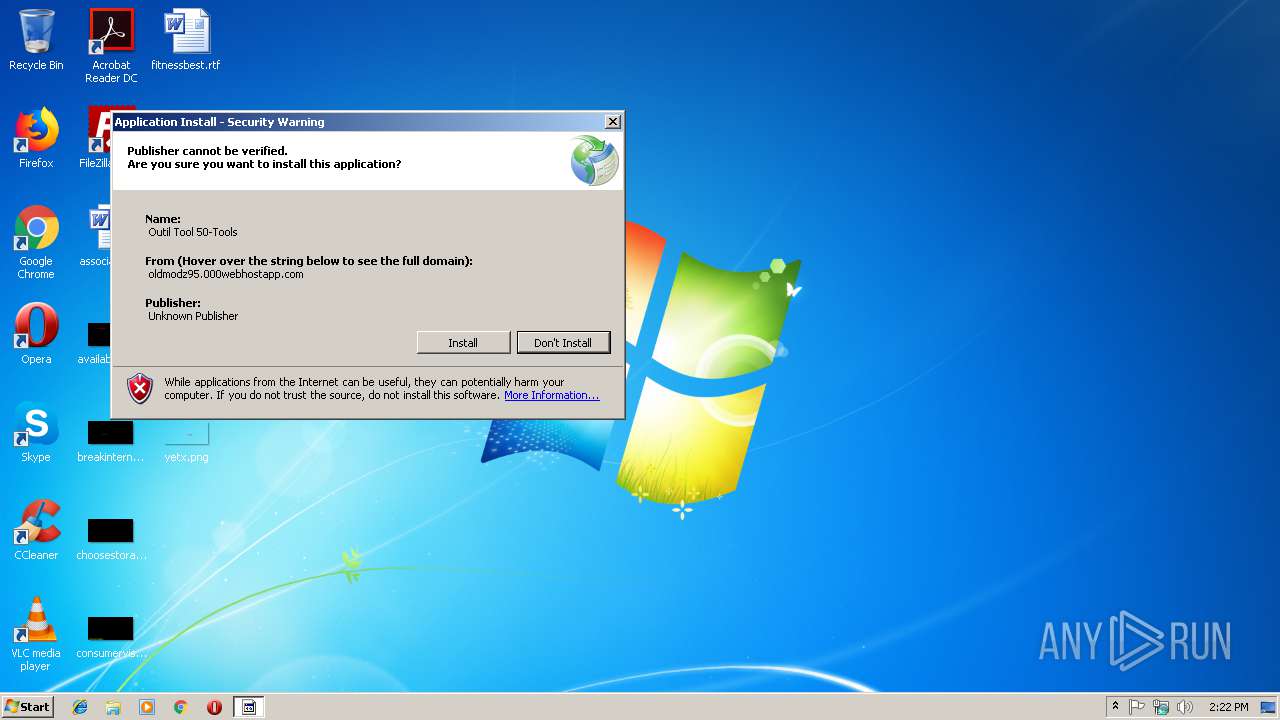
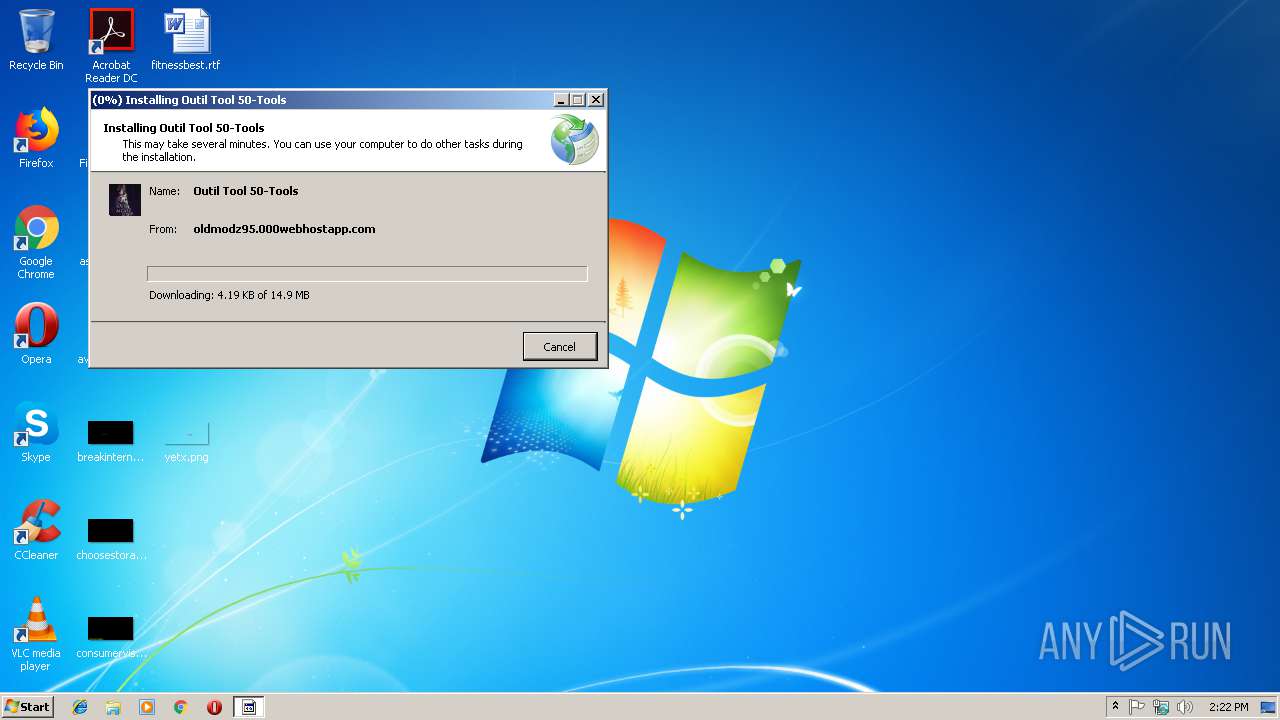
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 14:22:10 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3938C0DC3556283398951572B20E82E3 |
| SHA1: | 888B2F79D1B03EDBED78B064CFB31F1E2CB2F752 |
| SHA256: | 600E7E660ED1C3DFFD0D7F3919FDAA6FE123BACD937E345A9BFA2B40D8D9CBE0 |
| SSDEEP: | 6144:hDRMxppSSVridF55EGOaJhaQXgFIaUHQWWiNLsqEIvooEE0WgpgKSHhDGntOTbDa:hDGxppI1wQwFXQWiN61u4l |
MALICIOUS
Application was dropped or rewritten from another process
- Outil Tool 50-Tools.exe (PID: 4084)
SUSPICIOUS
Reads Environment values
- dfsvc.exe (PID: 2340)
Creates files in the user directory
- dfsvc.exe (PID: 2340)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 2340)
Reads internet explorer settings
- dfsvc.exe (PID: 2340)
Reads Internet Cache Settings
- dfsvc.exe (PID: 2340)
Creates a software uninstall entry
- dfsvc.exe (PID: 2340)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:10:05 06:40:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 331264 |
| InitializedDataSize: | 93184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2fafd |
| OSVersion: | 5.1 |
| ImageVersion: | 10 |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.0.21005.1 |
| ProductVersionNumber: | 12.0.21005.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 12.0.21005.1 built by: REL |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | setup.exe |
| ProductName: | - |
| ProductVersion: | 12.0.21005.1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Oct-2013 04:40:50 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | - |
| FileDescription: | Setup |
| FileVersion: | 12.0.21005.1 built by: REL |
| InternalName: | setup.exe |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | setup.exe |
| ProductName: | - |
| ProductVersion: | 12.0.21005.1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Oct-2013 04:40:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00050DC8 | 0x00050E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37701 |
.data | 0x00052000 | 0x0000460C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79845 |
.idata | 0x00057000 | 0x000014A4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.33464 |
.rsrc | 0x00059000 | 0x0000FC14 | 0x0000FE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.11358 |
.reloc | 0x00069000 | 0x00003608 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.54791 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22003 | 1286 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.01125 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.66147 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 1.69902 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.52655 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 3.83804 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.22476 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 2.497 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 1.78194 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 1.0882 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
ADVAPI32.dll (delay-loaded) |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
Secur32.dll |
USER32.dll |
WININET.dll |
msi.dll |
ole32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
_DecodePointerInternal@4 | 1 | 0x0001CE3B |
_EncodePointerInternal@4 | 2 | 0x0001CE56 |
Total processes
33
Monitored processes
3
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\dfsvc.exe | Installeur Outil Tool-By OldModz95.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: ClickOnce Exit code: 0 Version: 4.6.1055.0 built by: NETFXREL2 Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\AppData\Local\Temp\Installeur Outil Tool-By OldModz95.exe" | C:\Users\admin\AppData\Local\Temp\Installeur Outil Tool-By OldModz95.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Exit code: 0 Version: 12.0.21005.1 built by: REL Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\AppData\Local\Apps\2.0\0A08PBNE.TKL\9E98N8NL.T0Z\outi..tion_fa263e38441e67fd_0001.0000_29c9243928679f81\Outil Tool 50-Tools.exe" | C:\Users\admin\AppData\Local\Apps\2.0\0A08PBNE.TKL\9E98N8NL.T0Z\outi..tion_fa263e38441e67fd_0001.0000_29c9243928679f81\Outil Tool 50-Tools.exe | — | dfsvc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Outil Tool Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
308
Read events
165
Write events
135
Delete events
8
Modification events
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3492) Installeur Outil Tool-By OldModz95.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Installeur Outil Tool-By OldModz95_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
8
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\CabA915.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\TarA916.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\CabA927.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\TarA928.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\CabA9B6.tmp | — | |
MD5:— | SHA256:— | |||
| 3492 | Installeur Outil Tool-By OldModz95.exe | C:\Users\admin\AppData\Local\Temp\TarA9B7.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\CabB0D5.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\TarB0D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\2766V9YP.H9Y\903B75KP.LK4\Outil Tool 50-Tools.exe | — | |
MD5:— | SHA256:— | |||
| 2340 | dfsvc.exe | C:\Users\admin\AppData\Local\Temp\Deployment\2766V9YP.H9Y\903B75KP.LK4\Outil Tool 50-Tools.exe.genman | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
2
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3492 | Installeur Outil Tool-By OldModz95.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
3492 | Installeur Outil Tool-By OldModz95.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3492 | Installeur Outil Tool-By OldModz95.exe | 145.14.145.43:443 | oldmodz95.000webhostapp.com | Hostinger International Limited | US | shared |
2340 | dfsvc.exe | 145.14.145.43:443 | oldmodz95.000webhostapp.com | Hostinger International Limited | US | shared |
3492 | Installeur Outil Tool-By OldModz95.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
oldmodz95.000webhostapp.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | Not Suspicious Traffic | ET INFO Observed Free Hosting Domain (*.000webhostapp .com in DNS Lookup) |
3492 | Installeur Outil Tool-By OldModz95.exe | A Network Trojan was detected | SC BACKDOOR TeleRAT webhook using attempt |
3492 | Installeur Outil Tool-By OldModz95.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
2340 | dfsvc.exe | A Network Trojan was detected | SC BACKDOOR TeleRAT webhook using attempt |
2340 | dfsvc.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
2340 | dfsvc.exe | A Network Trojan was detected | SC BACKDOOR TeleRAT webhook using attempt |
2340 | dfsvc.exe | Not Suspicious Traffic | ET INFO Observed SSL Cert for Free Hosting Domain (*.000webhostapp .com) |
Process | Message |
|---|---|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status originated: -1073741811
*** Source File: d:\iso_whid\x86fre\base\isolation\hier_hierarchy.cpp, line 230
|
dfsvc.exe |
*** Status Originated: -1073741772
*** Source File: d:\iso_whid\x86fre\base\isolation\win32\isoreg_direct.cpp, line 1127
|