| File name: | http://ciscobinary.openh264.org/openh264-win32-2e1774ab6dc6c43debb0b5b628bdf122a391d521.zip |
| Full analysis: | https://app.any.run/tasks/7cab4b61-8fdd-4fcf-9930-63ea93009935 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2022, 16:54:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 29DDFD36F79EAAE39627110A00FF8370 |
| SHA1: | F5A0D4EB07B0E6813E64F07C99478B823EEDB82D |
| SHA256: | 600552DE4DE554364152ED426D02264E97D76AE1F33AFB1D845A0D25E5E5BA33 |
| SSDEEP: | 12288:E9FVnFrhwA7XATekr8IlK1uR/JRtPX/pPPWAyXKh10e+m:EJhv7XAT3r8IlK1uRvdRPPWAZWNm |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 2612)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3540)
- Explorer.EXE (PID: 1080)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2612)
Reads the computer name
- WinRAR.exe (PID: 2612)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2612)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2612)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2612)
INFO
Checks supported languages
- rundll32.exe (PID: 2460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
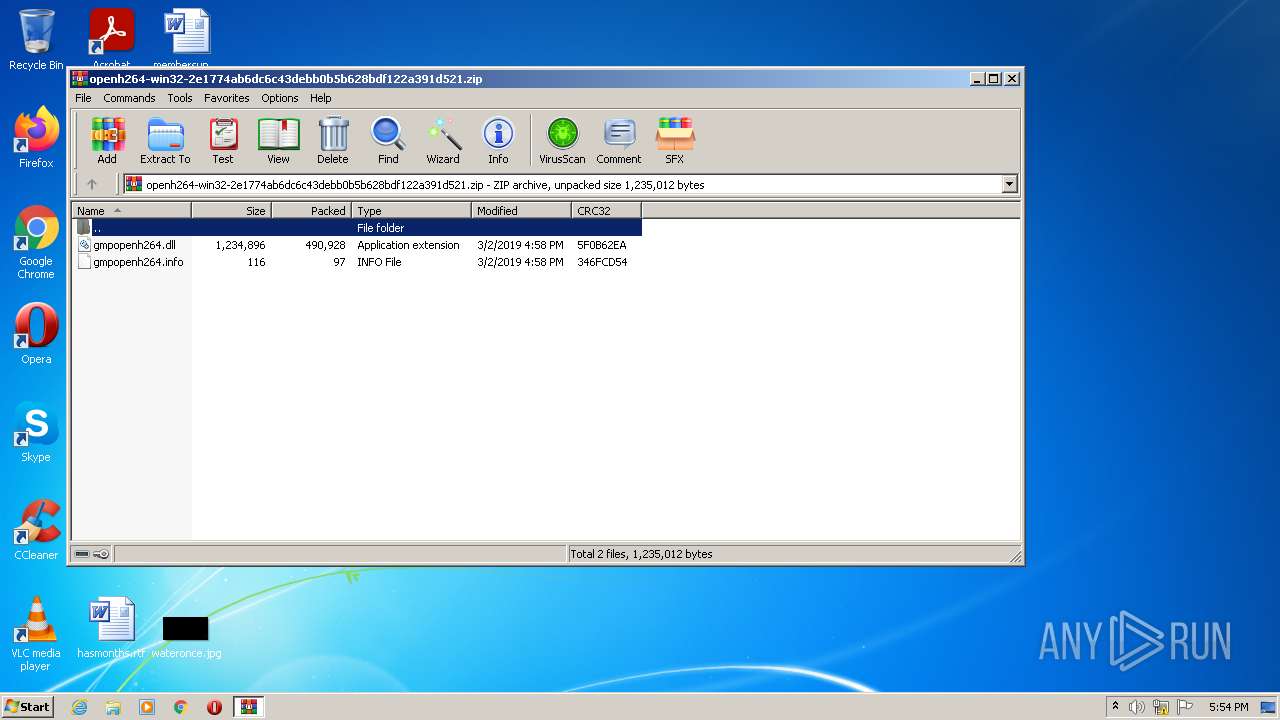
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
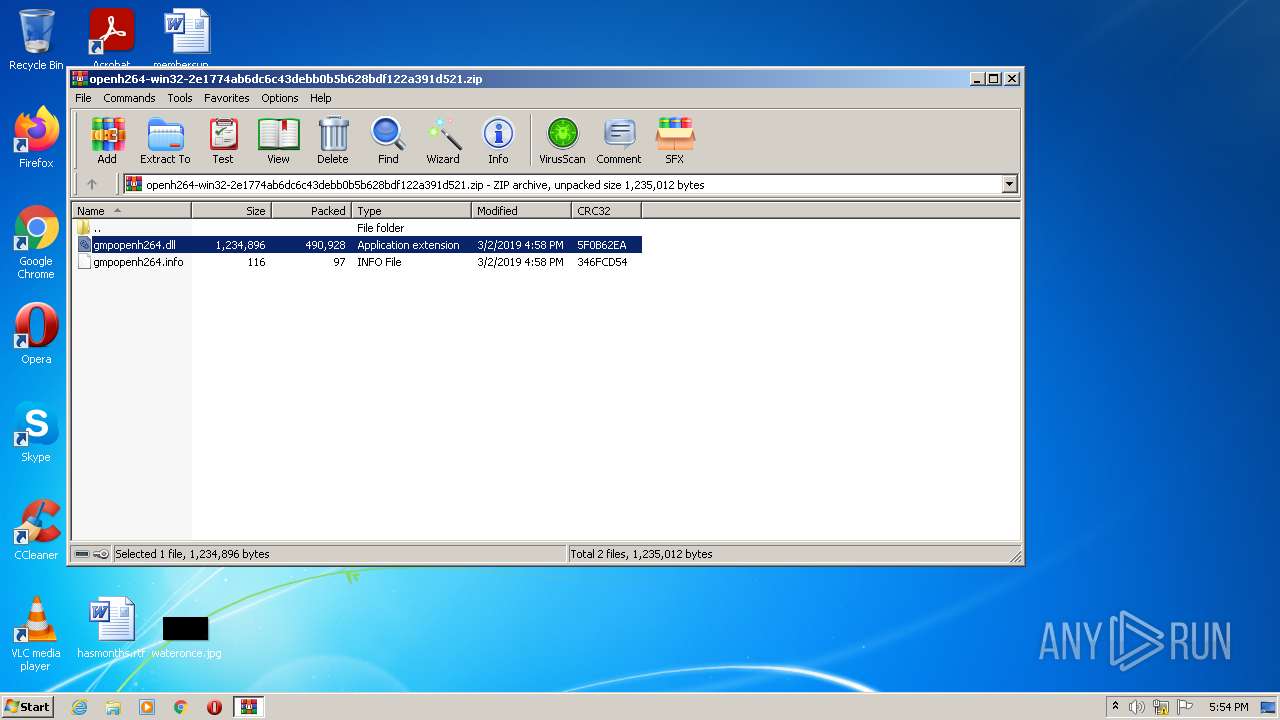
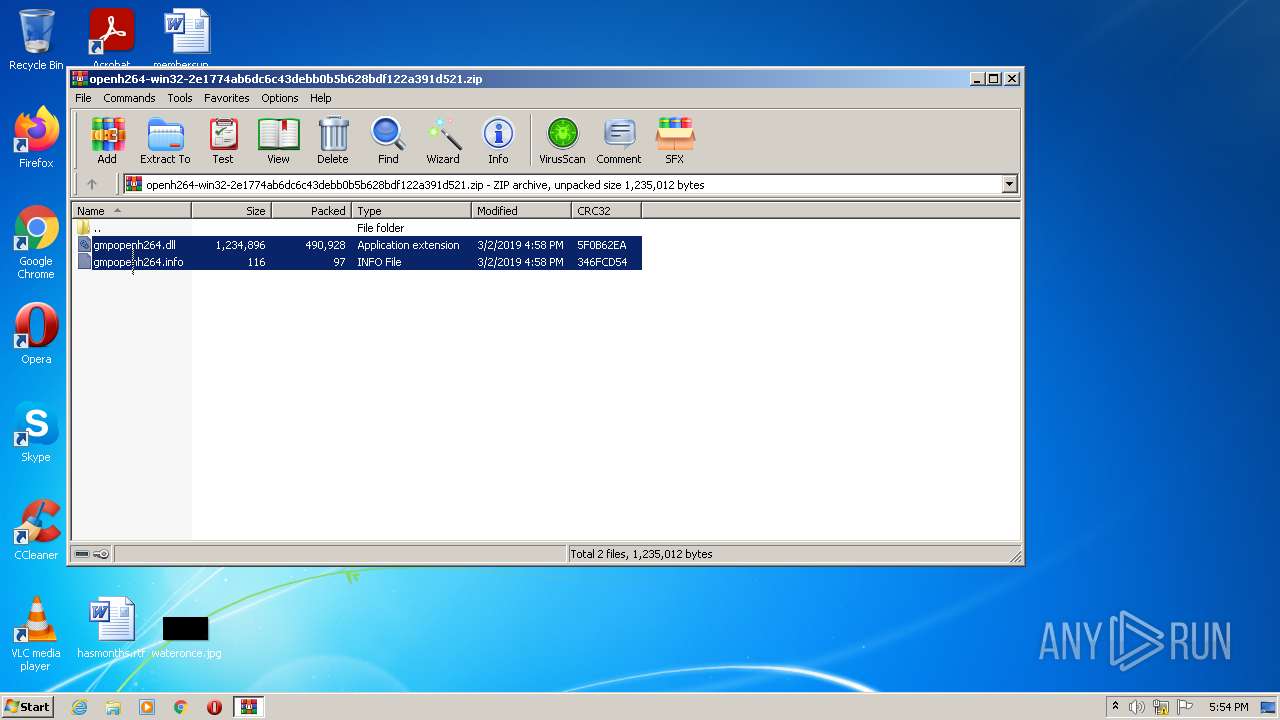
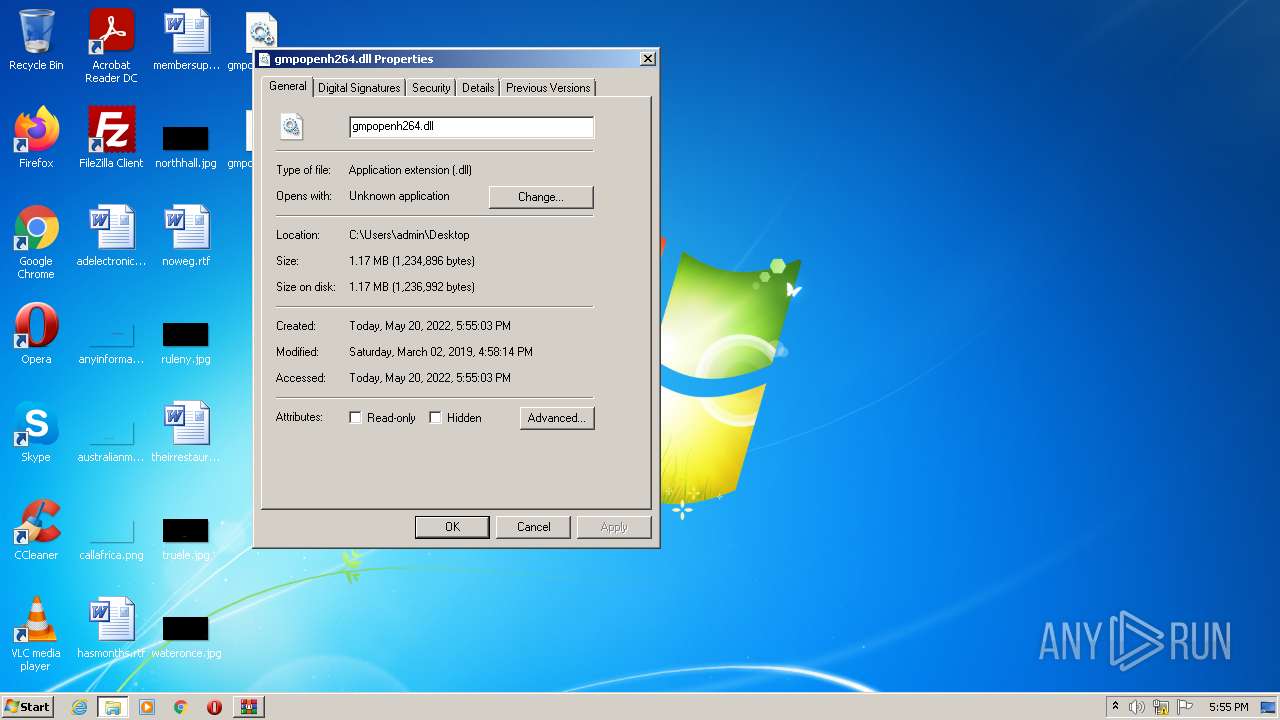
| ZipFileName: | gmpopenh264.dll |
|---|---|
| ZipUncompressedSize: | 1234896 |
| ZipCompressedSize: | 490928 |
| ZipCRC: | 0x5f0b62ea |
| ZipModifyDate: | 2019:03:02 16:58:07 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
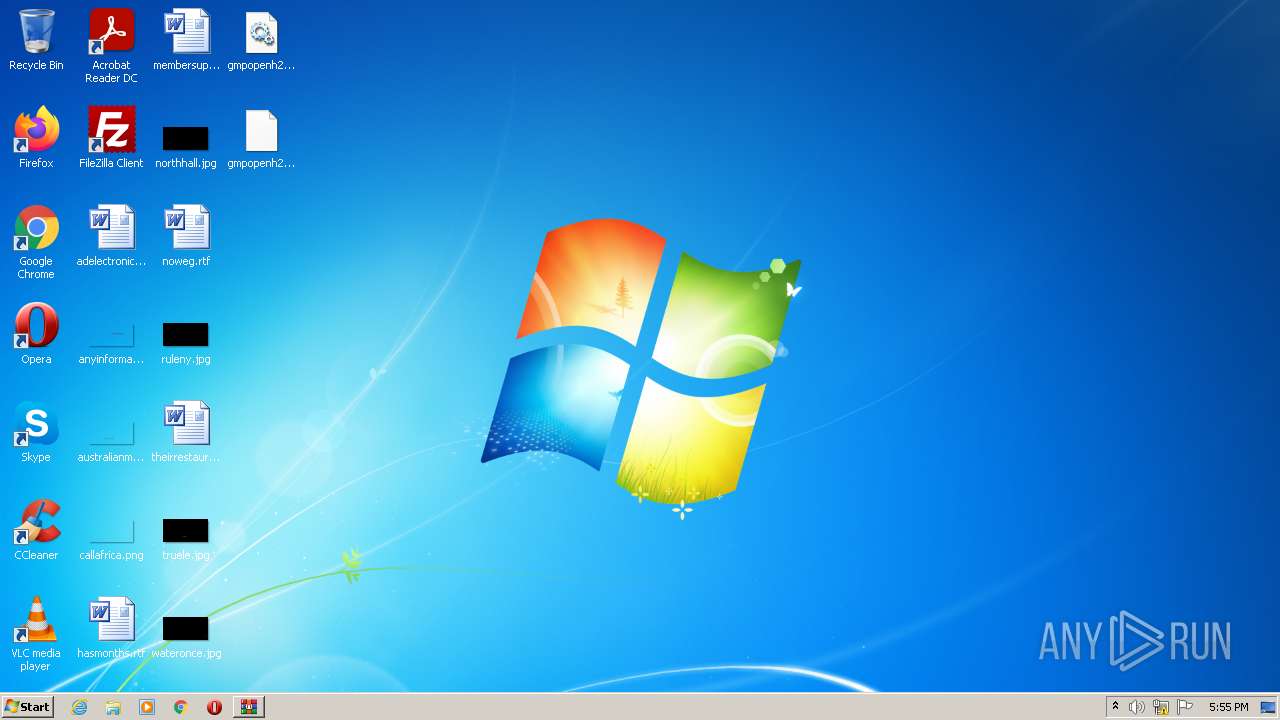
| 1080 | C:\Windows\Explorer.EXE | C:\Windows\Explorer.EXE | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
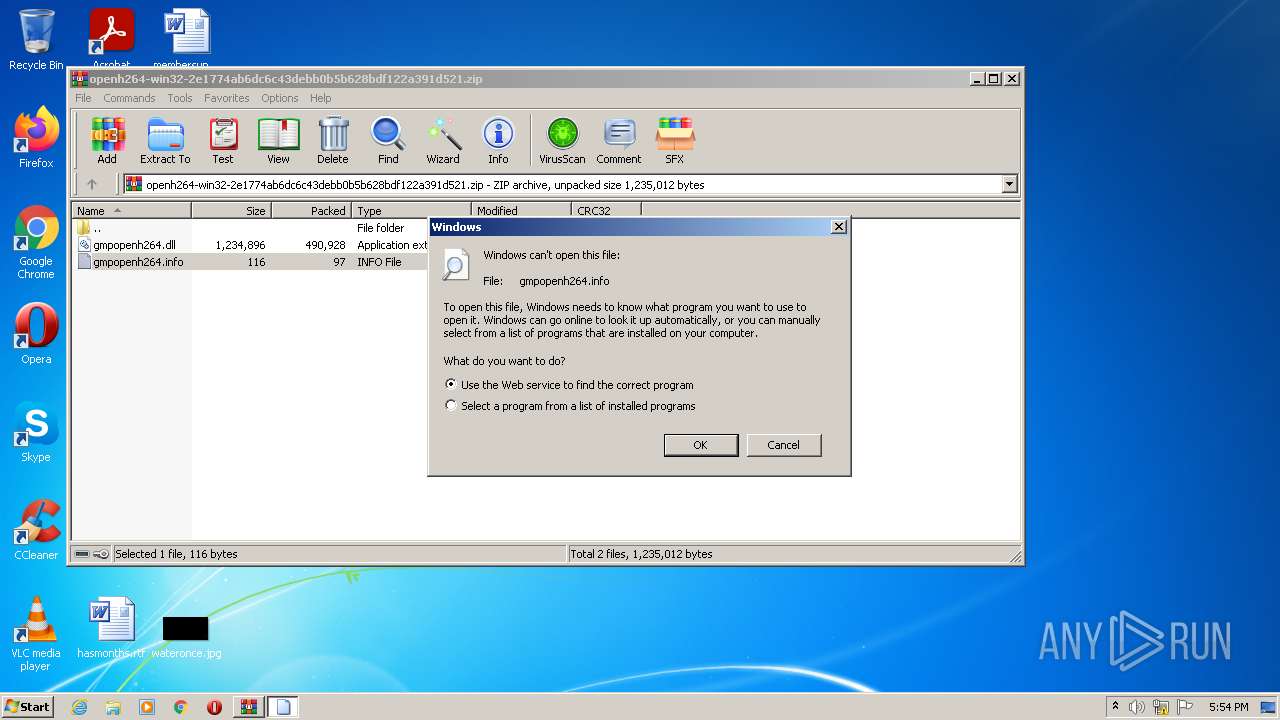
| 2460 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa2612.33196\gmpopenh264.info | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
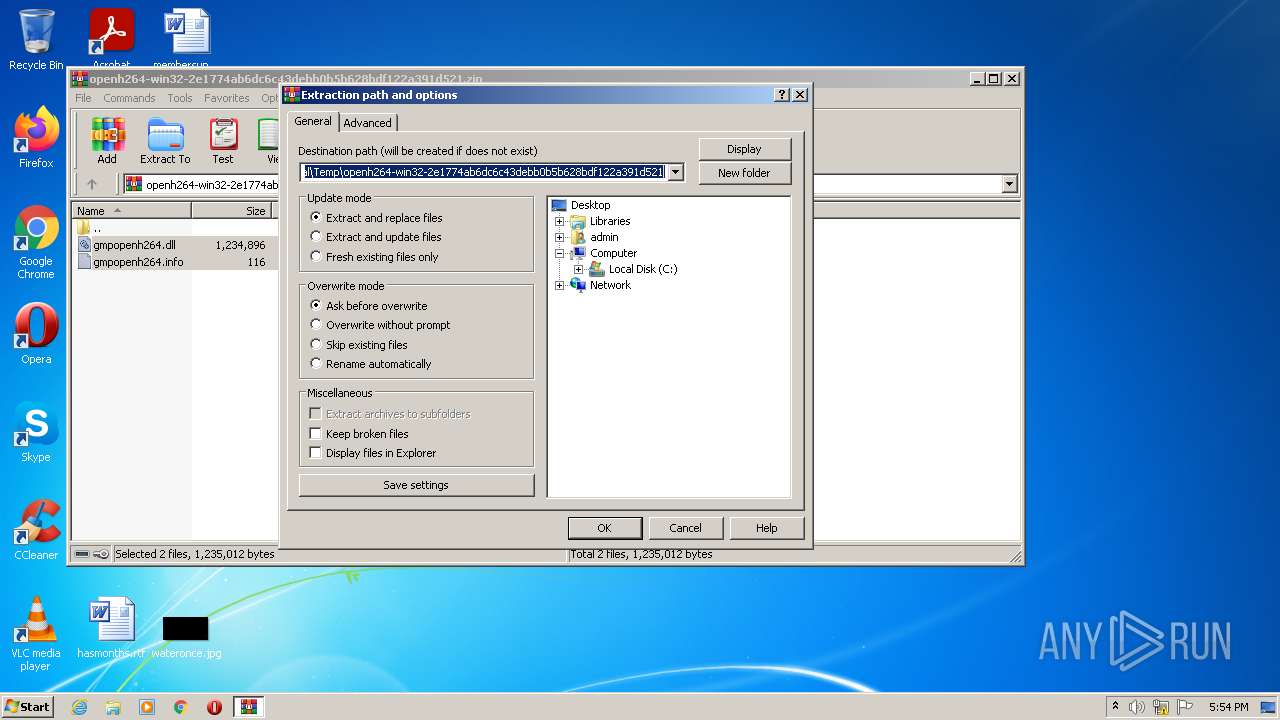
| 2612 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\openh264-win32-2e1774ab6dc6c43debb0b5b628bdf122a391d521.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3540 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe3_ Global\UsGthrCtrlFltPipeMssGthrPipe3 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
Total events
2 241
Read events
2 185
Write events
56
Delete events
0
Modification events
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\openh264-win32-2e1774ab6dc6c43debb0b5b628bdf122a391d521.zip | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2612) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
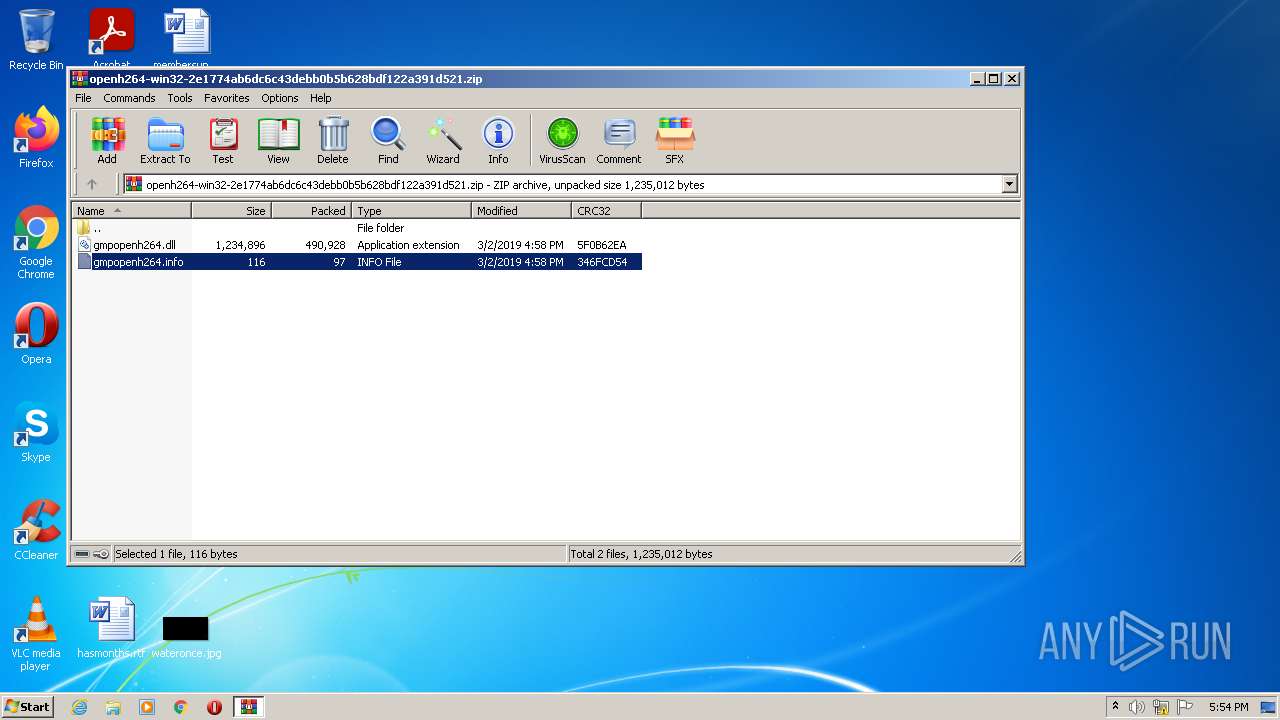
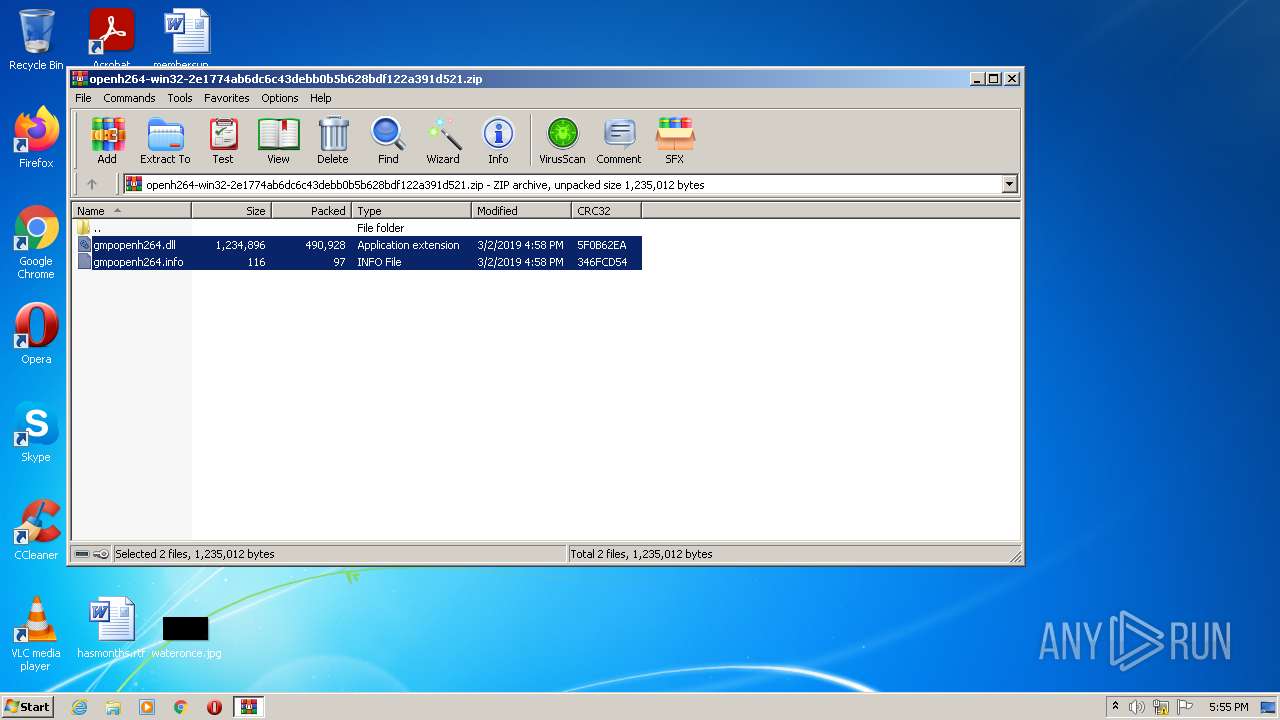
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2612.33196\gmpopenh264.info | text | |
MD5:3D33CDC0B3D281E67DD52E14435DD04F | SHA256:F526E9F98841D987606EFEAFF7F3E017BA9FD516C4BE83890C7F9A093EA4C47B | |||
| 2612 | WinRAR.exe | C:\Users\admin\Desktop\gmpopenh264.info | text | |
MD5:3D33CDC0B3D281E67DD52E14435DD04F | SHA256:F526E9F98841D987606EFEAFF7F3E017BA9FD516C4BE83890C7F9A093EA4C47B | |||
| 2612 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2612.32329\gmpopenh264.dll | executable | |
MD5:D23F706F2EACC190F2D4B75B041670D5 | SHA256:CED08CE5BC45DBE505FA94B3A4268C0830CCDA016A23C0ACB16DD7268CFA7A65 | |||
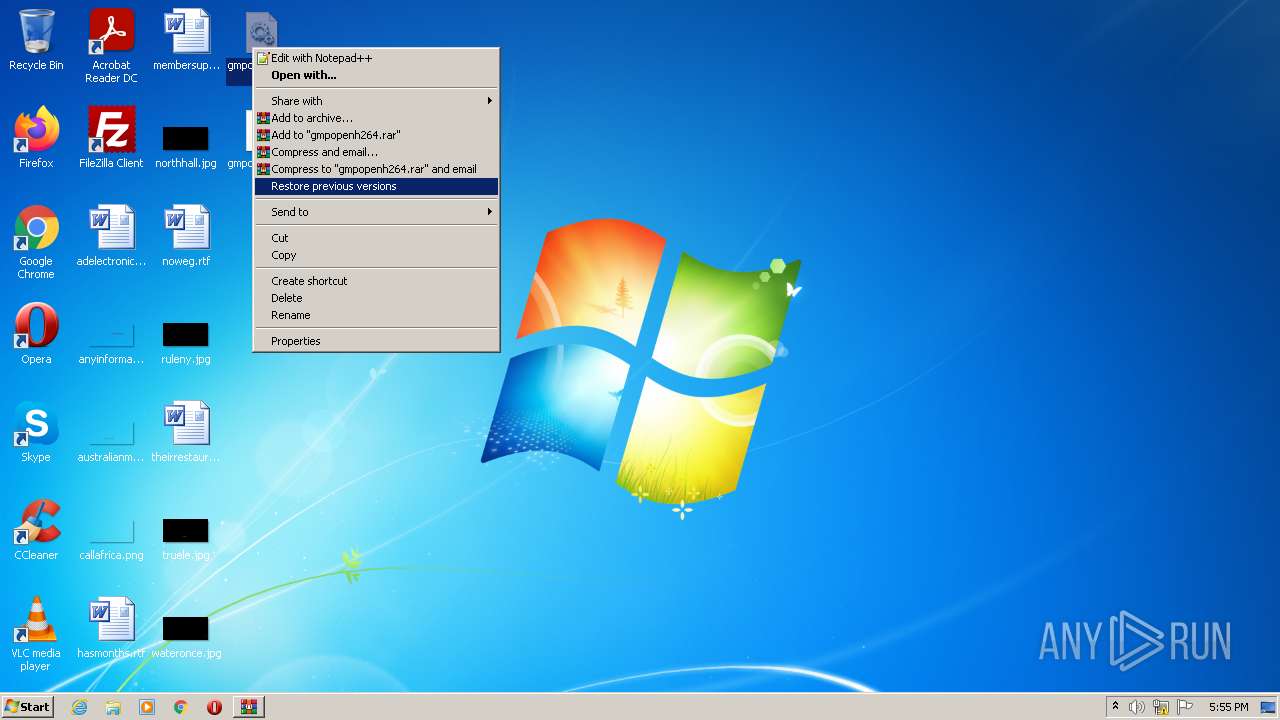
| 2612 | WinRAR.exe | C:\Users\admin\Desktop\gmpopenh264.dll | executable | |
MD5:D23F706F2EACC190F2D4B75B041670D5 | SHA256:CED08CE5BC45DBE505FA94B3A4268C0830CCDA016A23C0ACB16DD7268CFA7A65 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report