| File name: | phobos |
| Full analysis: | https://app.any.run/tasks/b9a403ad-ba2a-4126-ab7b-9a0d35941609 |
| Verdict: | Malicious activity |
| Analysis date: | November 03, 2024, 04:26:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | C1826AC82ABF9C6D49C3BFF9F8CBB31C |
| SHA1: | 0C15D09F8AF3E0850C97B8AECE22E351229AB6BD |
| SHA256: | 5FF273F03E88A8B0A1F58C85DFA28FEE6F44766EB09D53C421EB770D6B965E43 |
| SSDEEP: | 1536:NFu+gD5S4h4UZPaf2vpmbl4aXmI7ufDg6ALj2TC2OgVSKV4:NFIxuEaev4bl4i7zclOISW4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks for external IP
- svchost.exe (PID: 2172)
- phobos.exe (PID: 6024)
Executes application which crashes
- phobos.exe (PID: 6024)
INFO
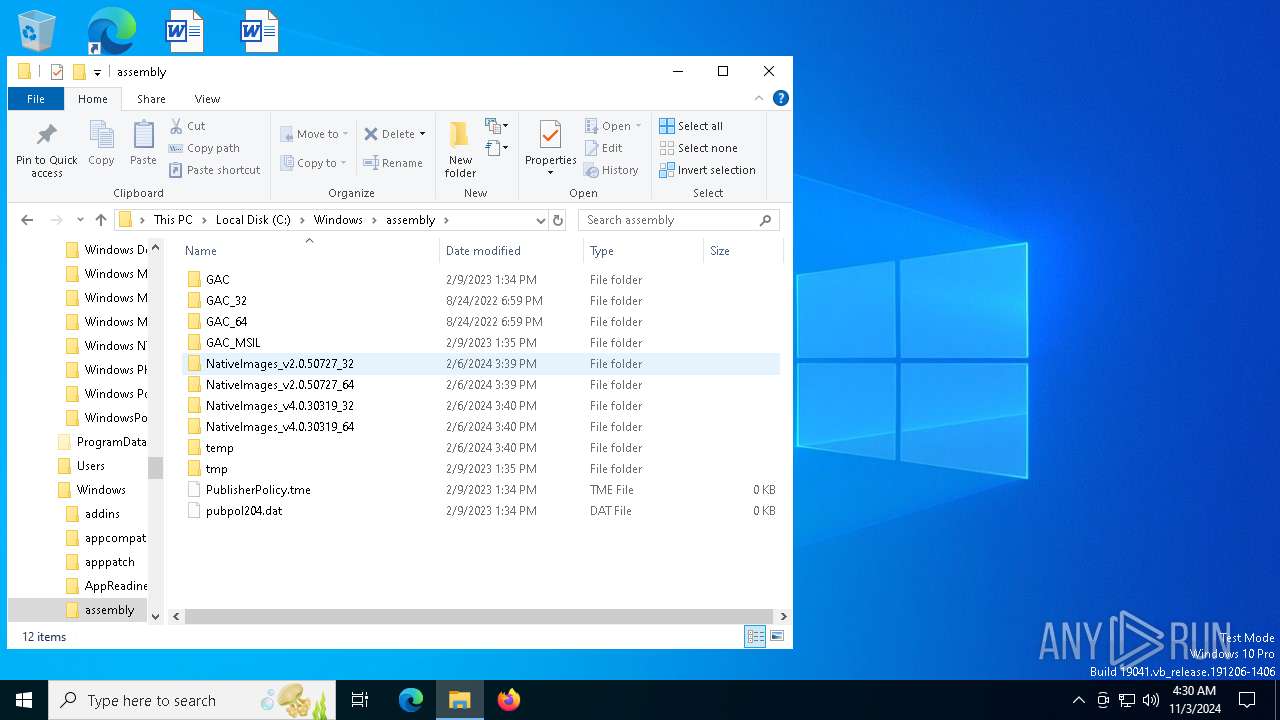
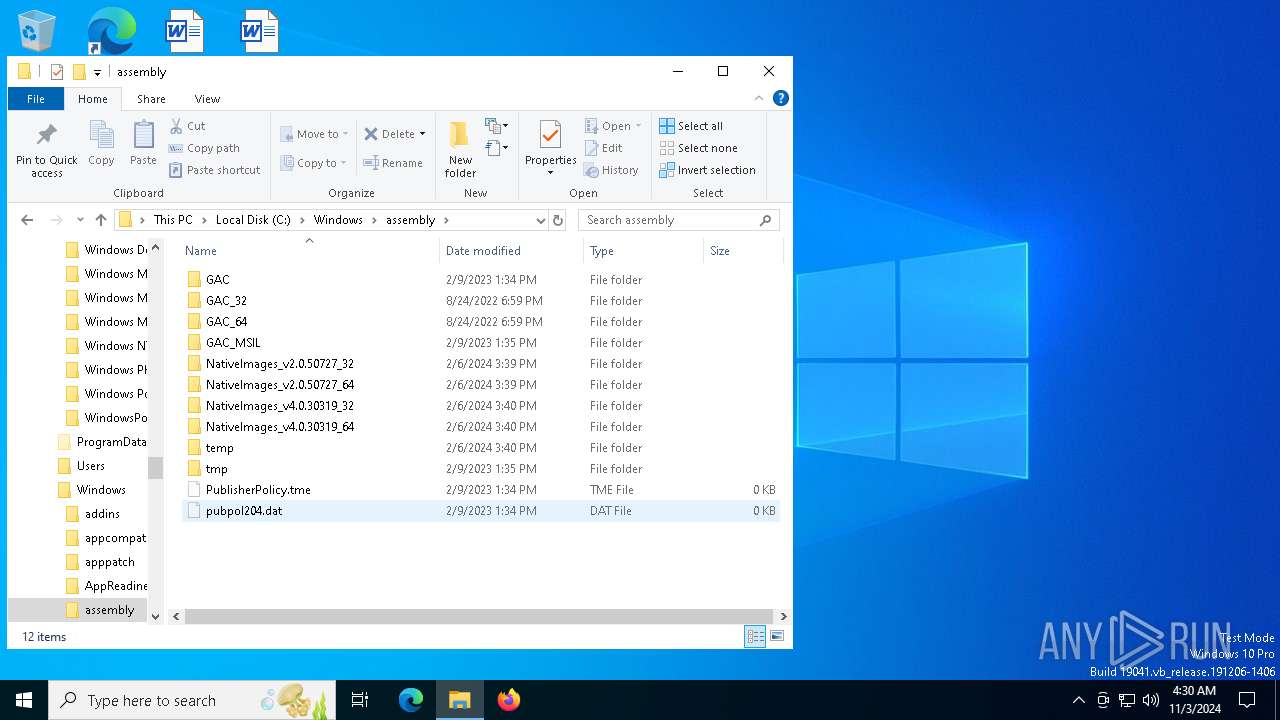
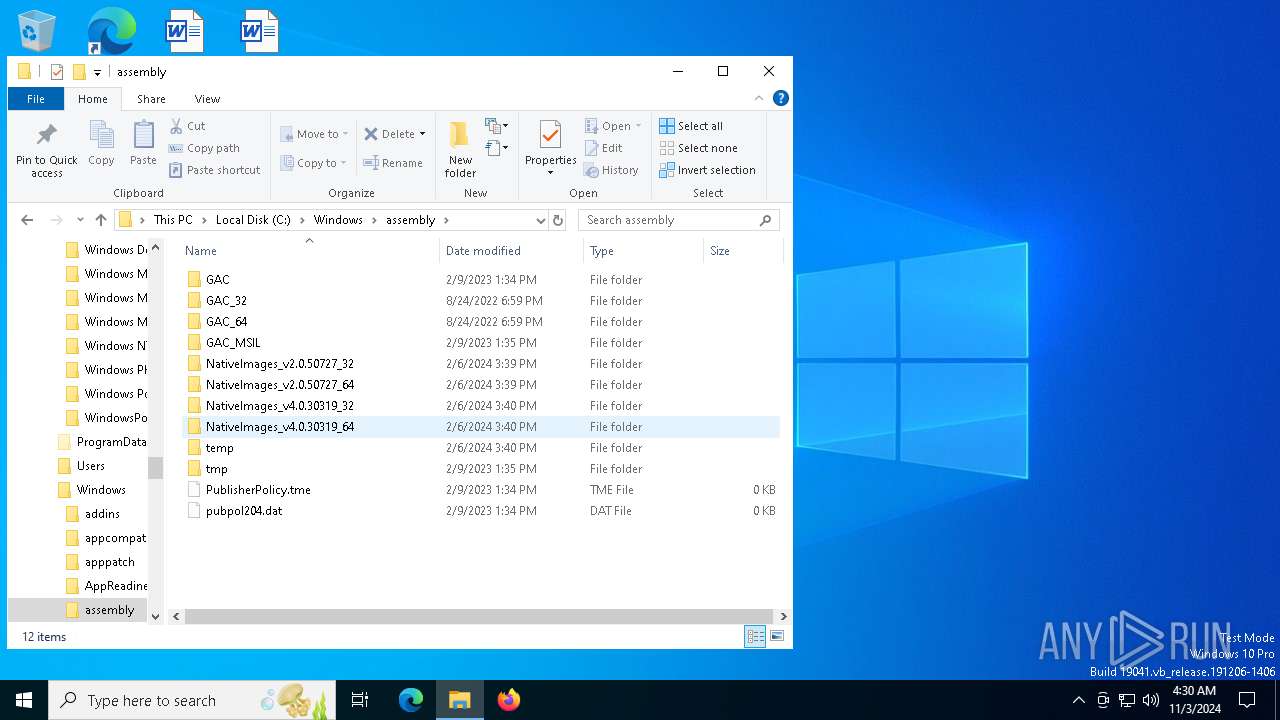
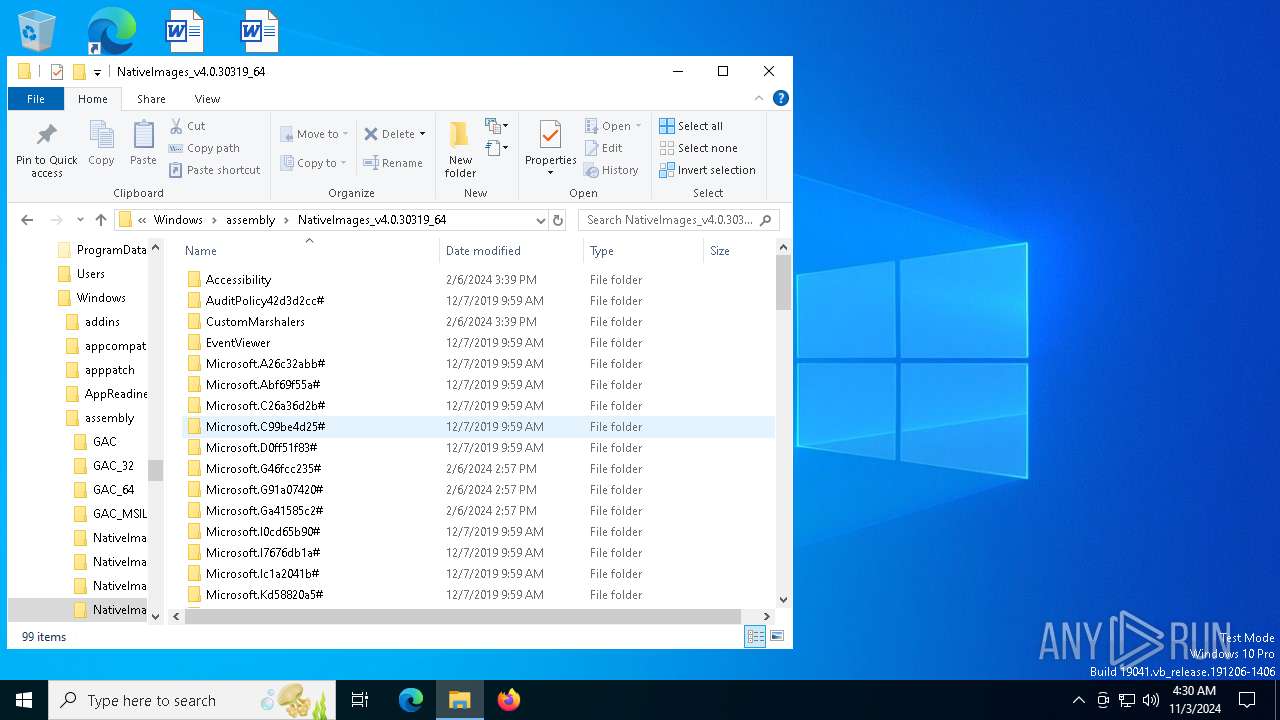
Disables trace logs
- phobos.exe (PID: 6024)
Creates files or folders in the user directory
- WerFault.exe (PID: 6912)
Reads the software policy settings
- slui.exe (PID: 5944)
- WerFault.exe (PID: 6912)
- slui.exe (PID: 4828)
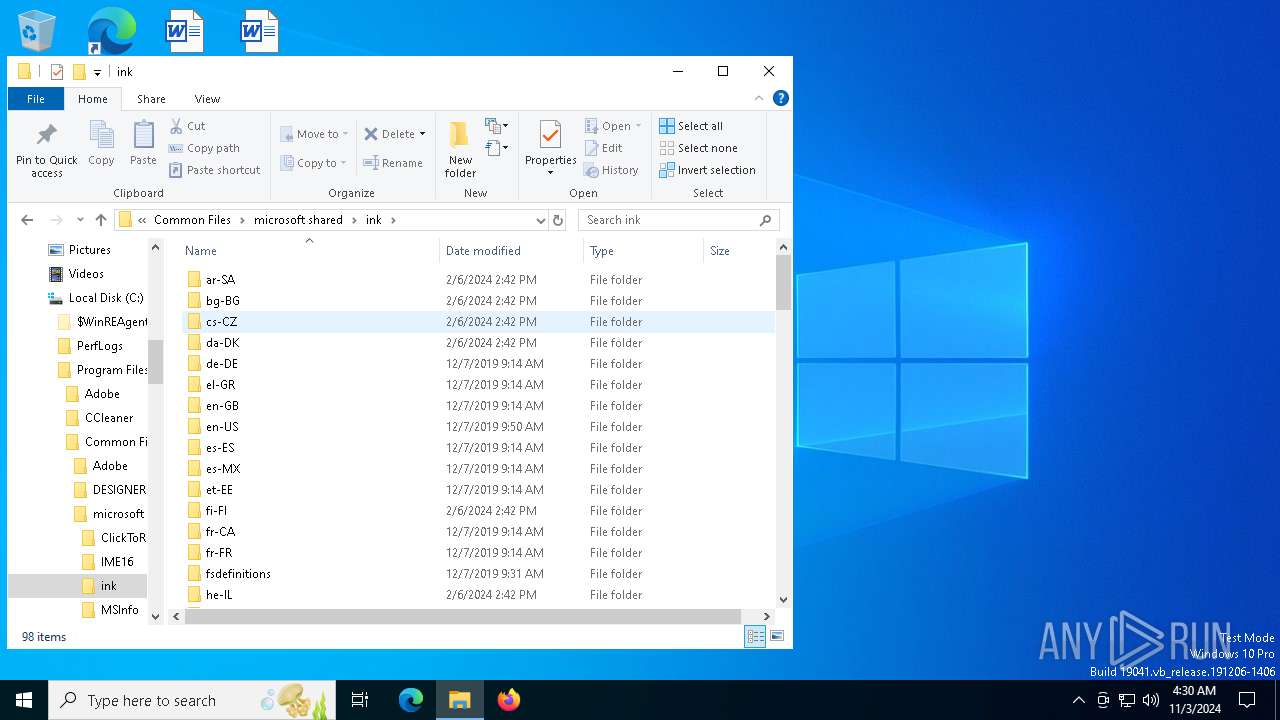
Checks supported languages
- phobos.exe (PID: 6024)
Reads the machine GUID from the registry
- phobos.exe (PID: 6024)
Reads Environment values
- phobos.exe (PID: 6024)
Reads the computer name
- phobos.exe (PID: 6024)
Sends debugging messages
- phobos.exe (PID: 6024)
Checks proxy server information
- slui.exe (PID: 5944)
- WerFault.exe (PID: 6912)
- phobos.exe (PID: 6024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (56.7) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21.3) |
| .scr | | | Windows screen saver (10.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:02:25 22:53:40+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 84992 |
| InitializedDataSize: | 2048 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16a7e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.12.0.20 |
| ProductVersionNumber: | 2.12.0.20 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
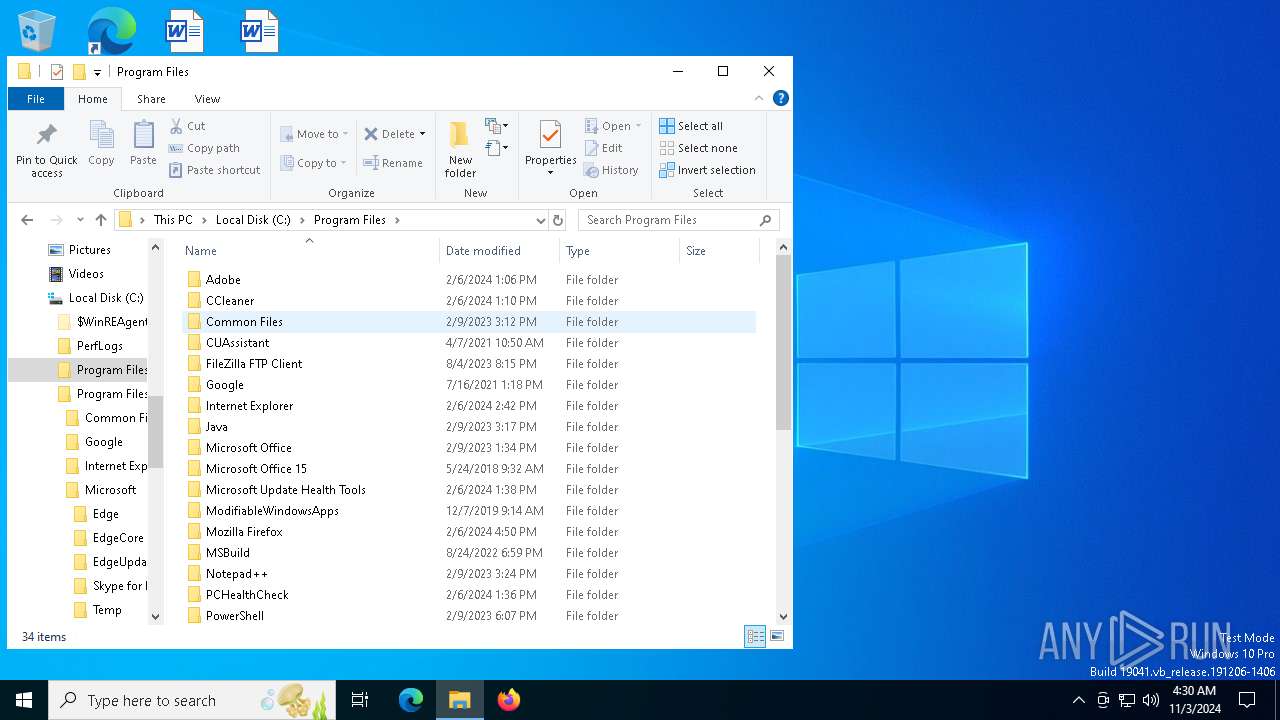
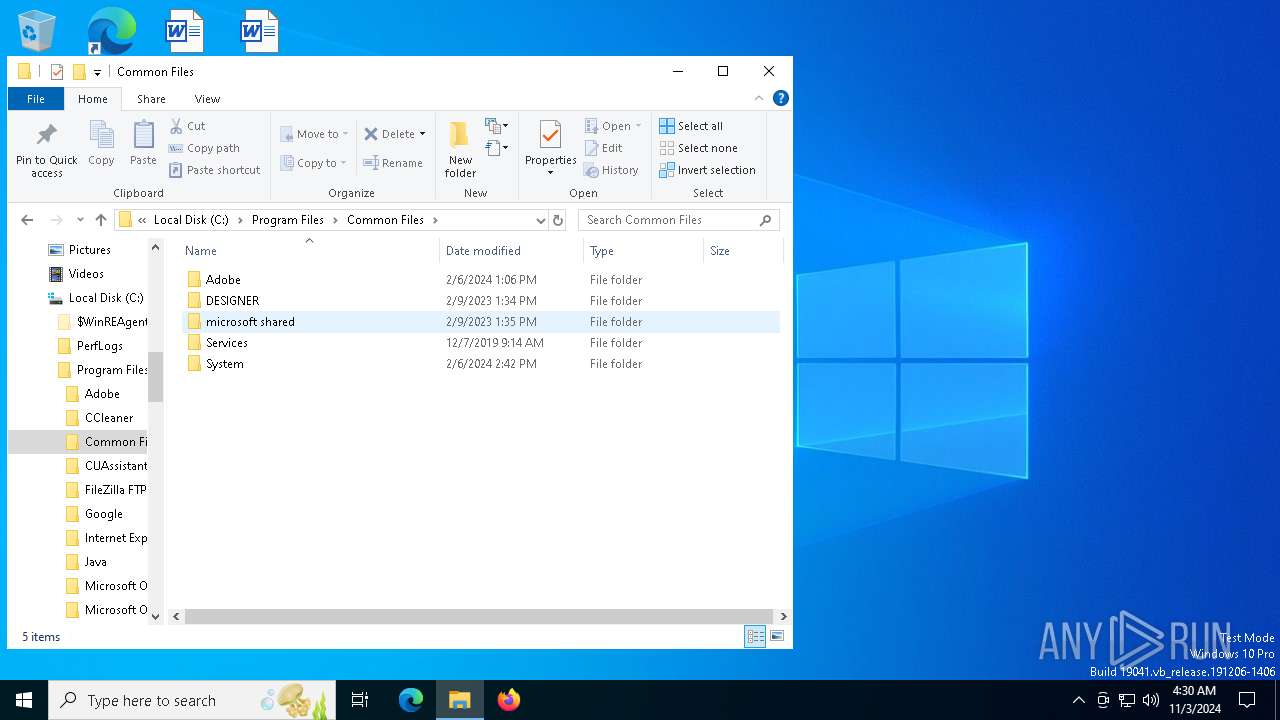
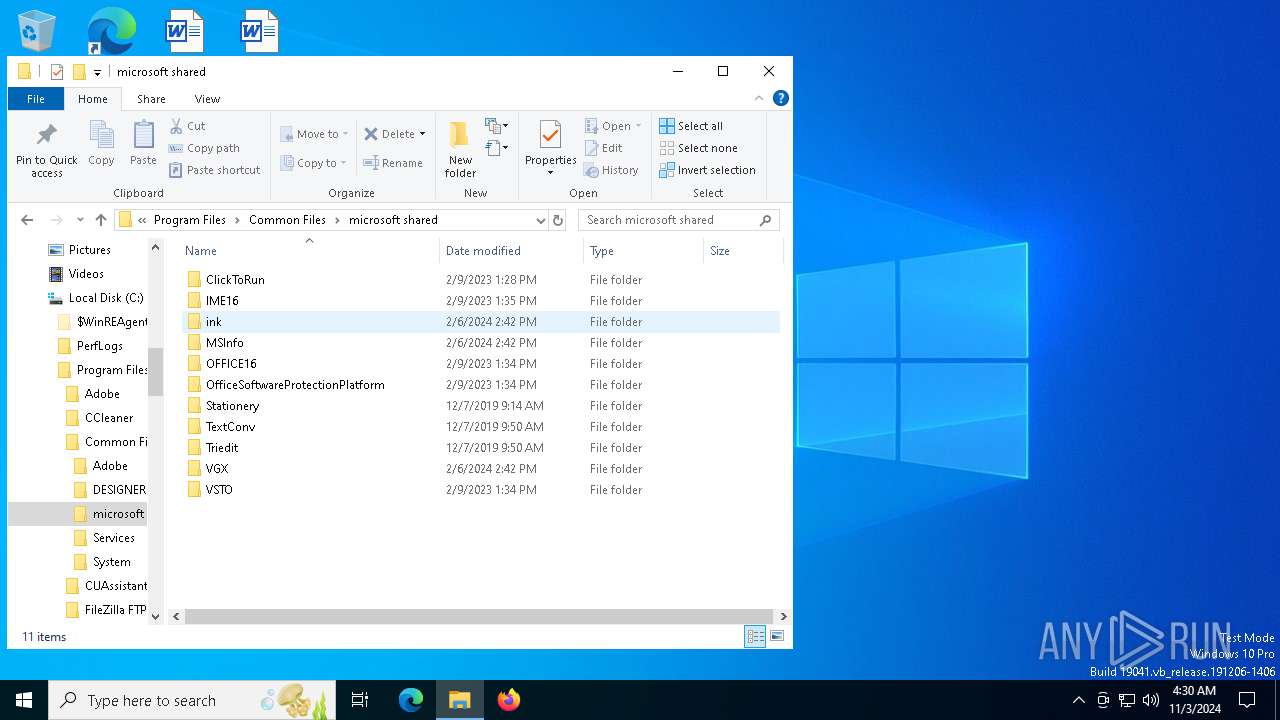
| CompanyName: | Adobe Inc. |
| FileDescription: | Adobe Installer |
| FileVersion: | 2.12.0.20 |
| InternalName: | xWmDDA.exe |
| LegalCopyright: | © 2015-2023 Adobe. All rights reserved. |
| OriginalFileName: | xWmDDA.exe |
| ProductName: | Adobe Installer |
| ProductVersion: | 2.12.0.20 |
| AssemblyVersion: | 2.12.0.20 |
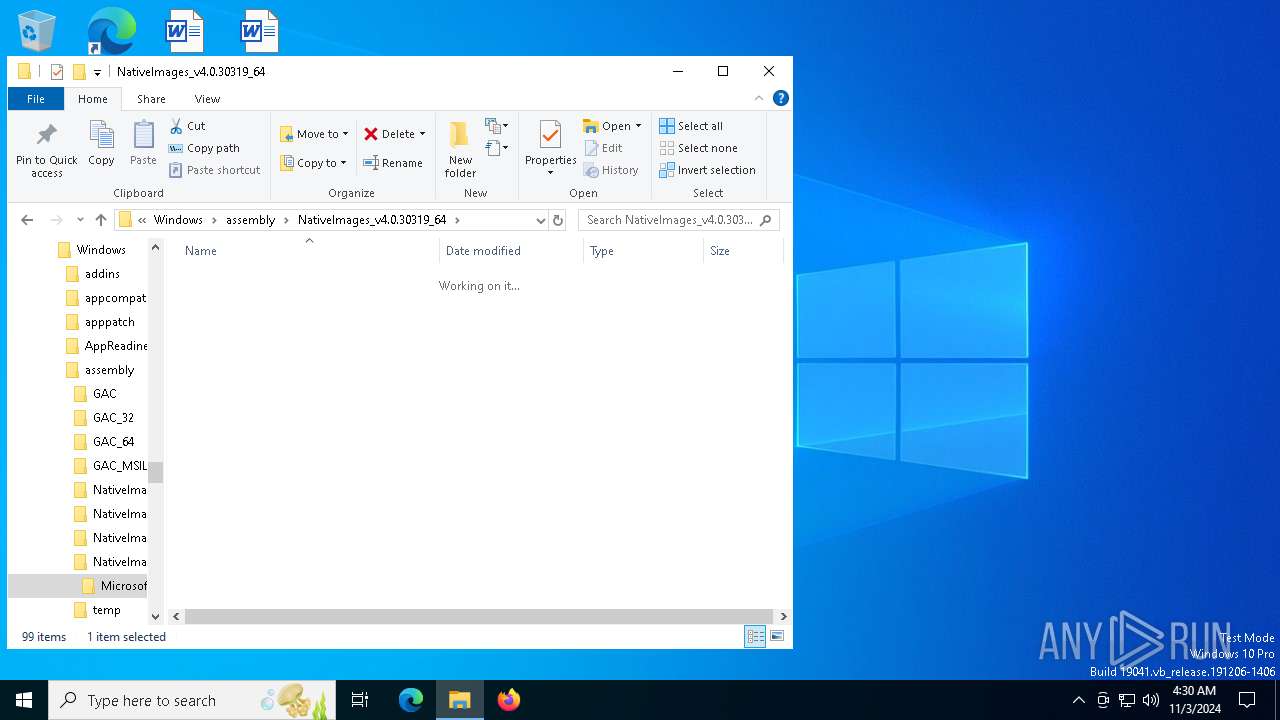
Total processes
144
Monitored processes
7
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4828 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5944 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
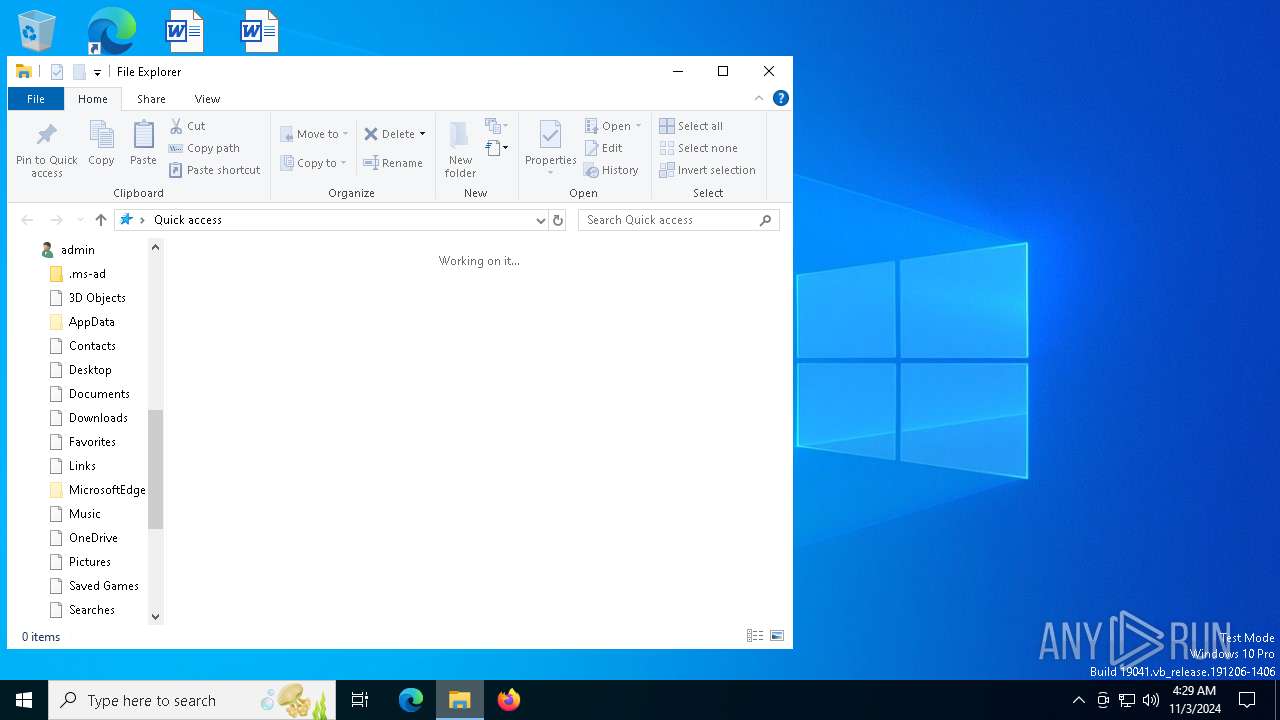
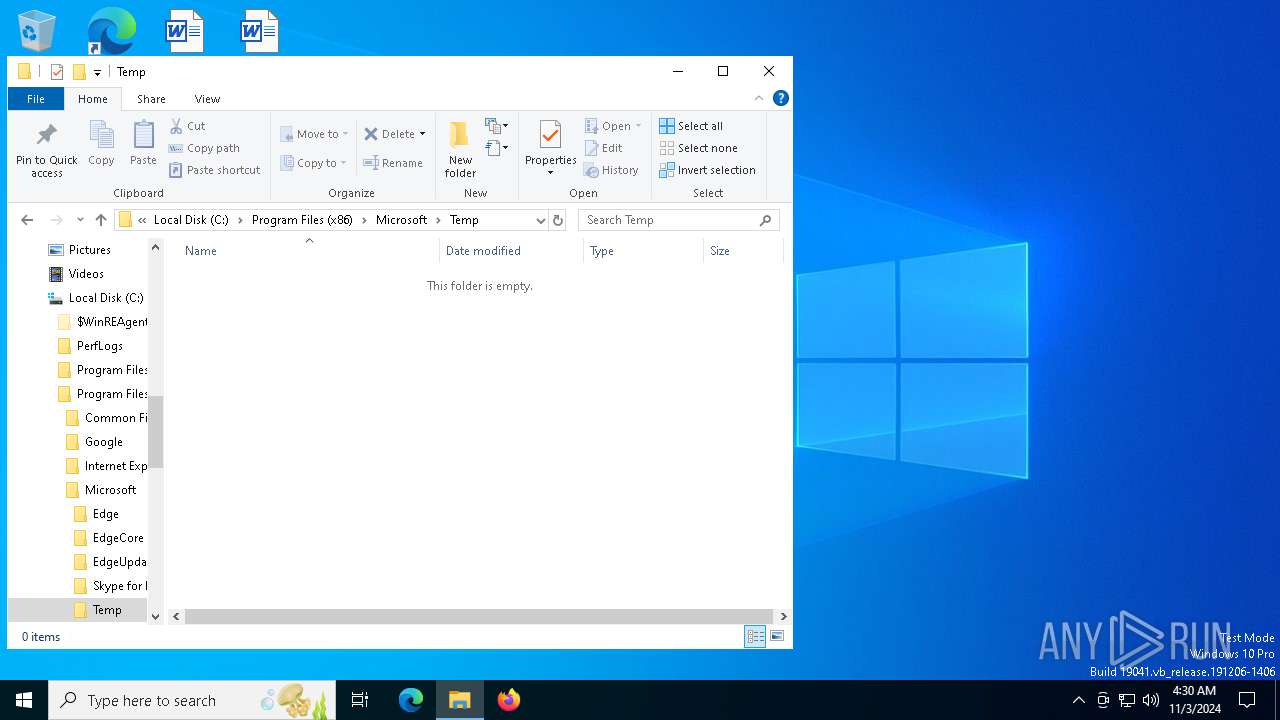
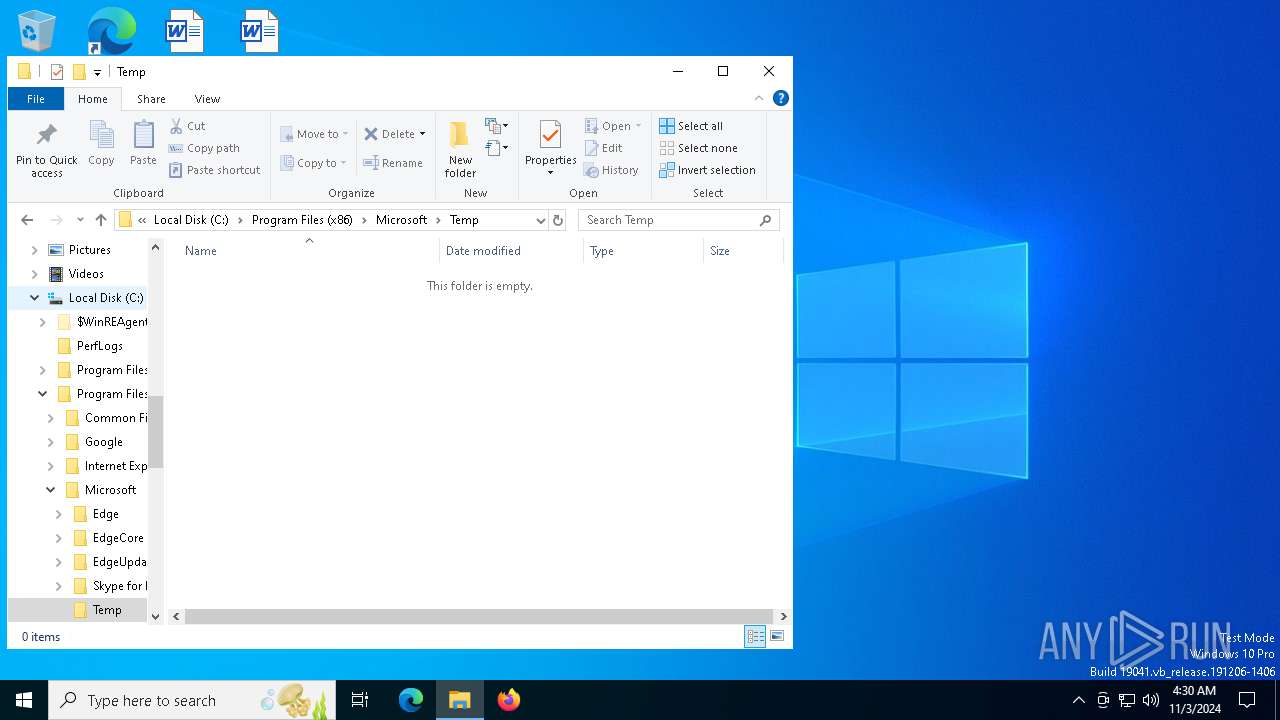
| 6024 | "C:\Users\admin\AppData\Local\Temp\phobos.exe" | C:\Users\admin\AppData\Local\Temp\phobos.exe | explorer.exe | ||||||||||||
User: admin Company: Adobe Inc. Integrity Level: MEDIUM Description: Adobe Installer Exit code: 2148734499 Version: 2.12.0.20 Modules
| |||||||||||||||
| 6912 | C:\WINDOWS\system32\WerFault.exe -u -p 6024 -s 1836 | C:\Windows\System32\WerFault.exe | phobos.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 388
Read events
5 374
Write events
14
Delete events
0
Modification events
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6024) phobos.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\phobos_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
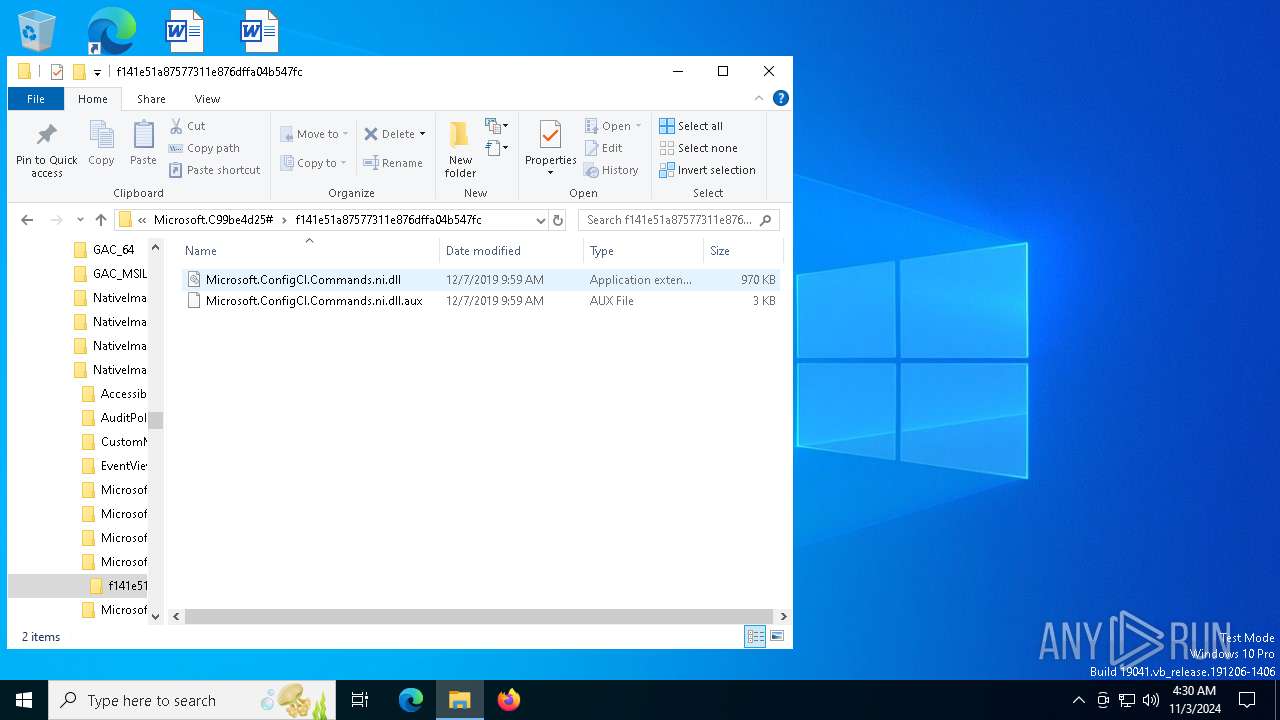
Executable files
0
Suspicious files
5
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
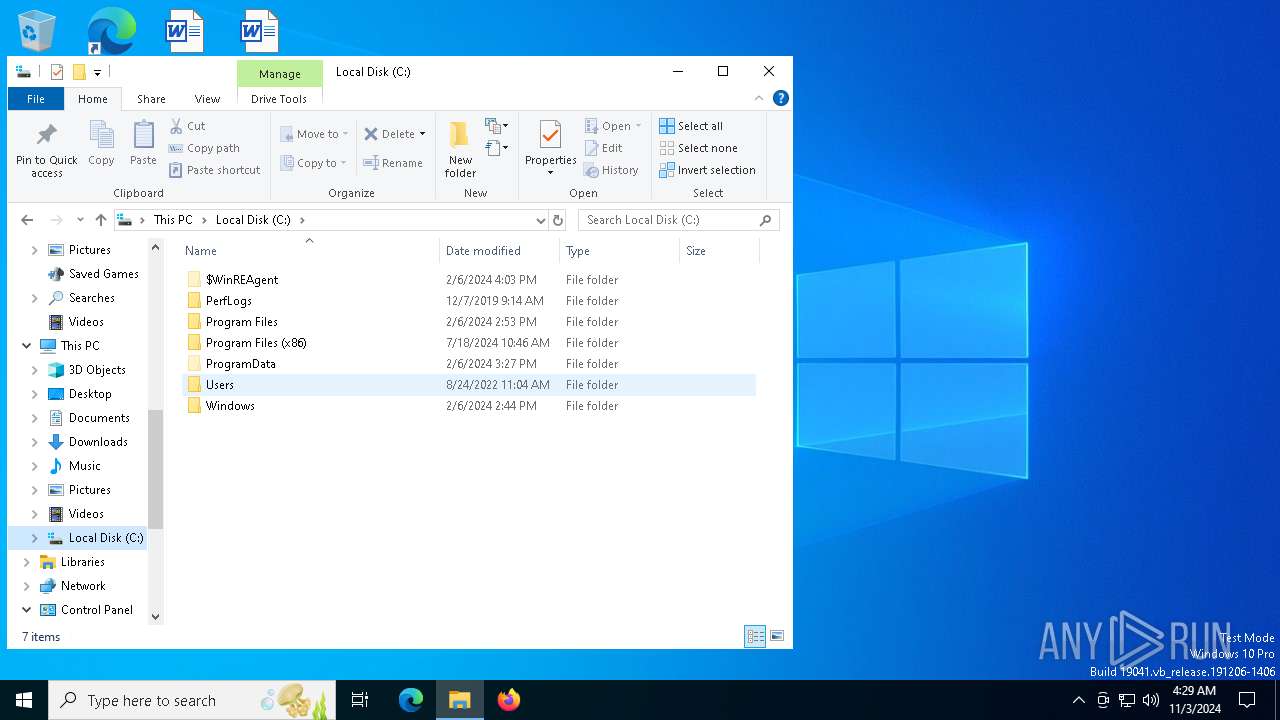
| 6912 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportArchive\AppCrash_phobos.exe_39a2c863e148557aaa7cfdf2e3e0aaeec993eb68_de925953_c82ad395-54b9-45ce-9fa3-416ebad5b06e\Report.wer | — | |
MD5:— | SHA256:— | |||
| 6912 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\phobos.exe.6024.dmp | — | |
MD5:— | SHA256:— | |||
| 6912 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\21253908F3CB05D51B1C2DA8B681A785 | der | |
MD5:1B7FD5177461034E4086724C5845E927 | SHA256:065AF18C229898A1C2A8D989911ADCD9B1E2AB14B1953EBF8EAF34AE37EA1627 | |||
| 6912 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCC33.tmp.WERInternalMetadata.xml | xml | |
MD5:0E367487D79DA81BF4A26A203B807915 | SHA256:799686CA3E558CD3F5C33F53C17C0DED71EACBAEFB006EA4E088B174D275C8C0 | |||
| 6912 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCC53.tmp.xml | xml | |
MD5:8D2C2582E93E49E458929F6D2CA28E16 | SHA256:9E8F1A7CDE94C0163A7BC320B490DD96DEC3A2C76B753D8D00C354EA8D1A77FC | |||
| 6912 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\37C951188967C8EB88D99893D9D191FE | der | |
MD5:F0CF5B1794ECA7CD73F9C020DAAB8EF2 | SHA256:2AF00EDCE7EF3266897E52DC81E8DE3B7A079028C0F1F96EAFF9E38AD342F617 | |||
| 6912 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:7A0A822649515900499854D72886461C | SHA256:1CFBA9C021BBE5410DBCA1443083C767536236116A7B828778A9A5D252D69522 | |||
| 6912 | WerFault.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\21253908F3CB05D51B1C2DA8B681A785 | binary | |
MD5:C0887BCD126140F82E01DE7869EC58B9 | SHA256:0555C9BBBF4FABBF72ADBD1324C4843CFA85DE9CED9AEA4442110BCC4EA0DBE4 | |||
| 6912 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERCA3E.tmp.dmp | binary | |
MD5:7B34965218312B229CF2AB22DA4A11BF | SHA256:09FBC2155C062C82BF9E924D87C3870BBE087659A1A65661B193BA6D8FF3362F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
47
DNS requests
22
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6912 | WerFault.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
6024 | phobos.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | US | text | 5 b | shared |
6912 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
2076 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6944 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
6944 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
4208 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
7092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
7092 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1764 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5488 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4360 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6024 | phobos.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | shared |
6912 | WerFault.exe | 20.189.173.22:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6912 | WerFault.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
ip-api.com |
| shared |
watson.events.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
th.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6024 | phobos.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6024 | phobos.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
Process | Message |
|---|---|
phobos.exe | CLR: Managed code called FailFast without specifying a reason.
|