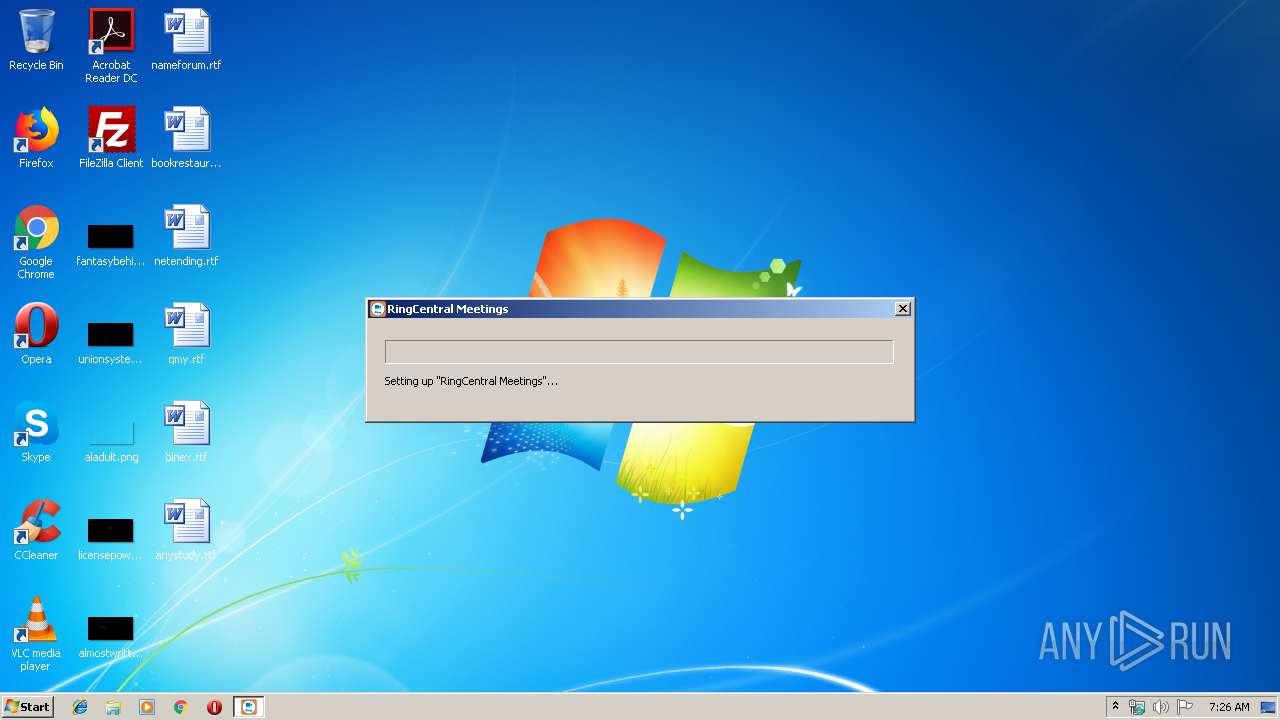
| File name: | RingCentral_launcher.exe |
| Full analysis: | https://app.any.run/tasks/ec3473b8-3483-471c-9f11-8c9806fb0128 |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 07:26:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D7D5A68DDBEF9BDDAA73BE467183C14 |
| SHA1: | F7C0AA4FBFE9FBE7236DF2562879FF0E6D434BB2 |
| SHA256: | 5FF07113B7970582D12086AA07F6B591636DA96C4D7D09B466DCC0B9C22C1BB7 |
| SSDEEP: | 3072:Smwq0BS3gMNeKflHm5Sw68I+hyWExG1sa0azty/ON0Oh/JYWJK9dYWSkJiDvtpXa:Oq8S3wKflFvQyw1NtfDkEDH1g |
MALICIOUS
Application was dropped or rewritten from another process
- Installer.exe (PID: 2948)
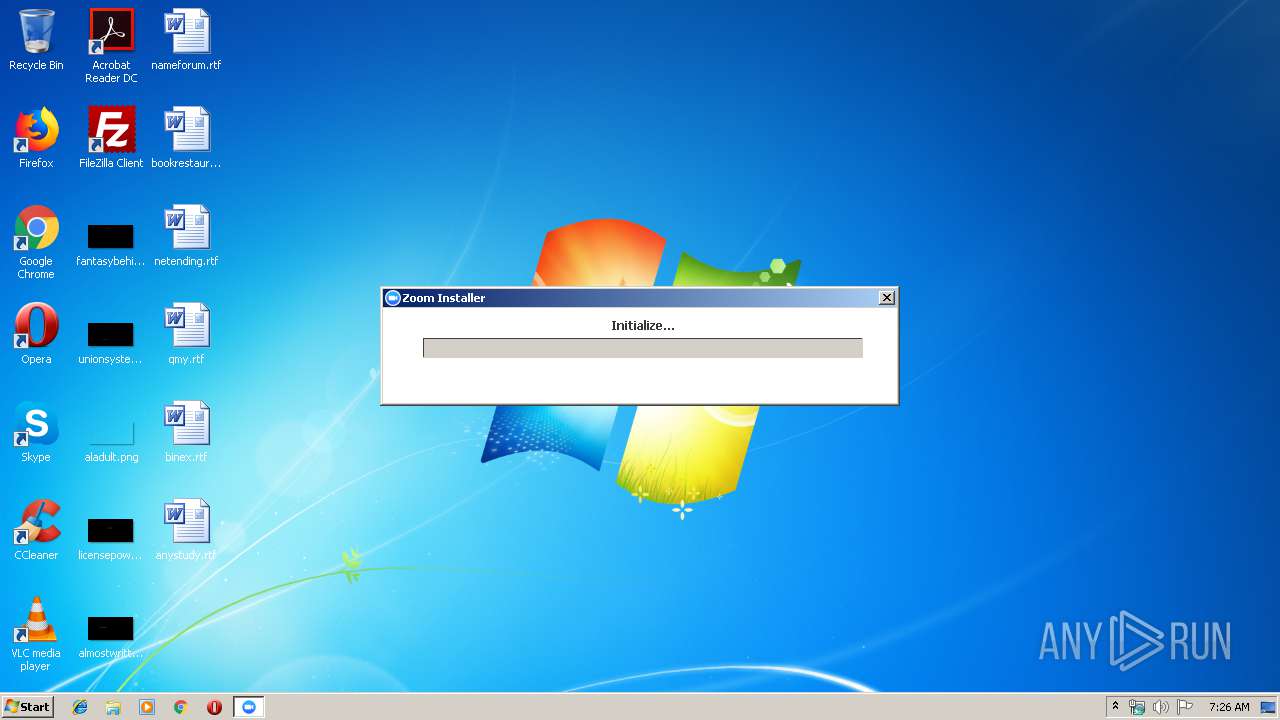
- Zoom.exe (PID: 3432)
- Zoom.exe (PID: 2780)
Loads dropped or rewritten executable
- Installer.exe (PID: 2948)
- Zoom.exe (PID: 3432)
- Zoom.exe (PID: 2780)
SUSPICIOUS
Creates files in the user directory
- RingCentral_launcher.exe (PID: 1052)
- Zoom.exe (PID: 3432)
- Zoom.exe (PID: 2780)
- Installer.exe (PID: 2948)
Executable content was dropped or overwritten
- RingCentral_launcher.exe (PID: 1052)
- Installer.exe (PID: 2948)
Creates a software uninstall entry
- Installer.exe (PID: 2948)
Changes IE settings (feature browser emulation)
- Installer.exe (PID: 2948)
Modifies the open verb of a shell class
- Installer.exe (PID: 2948)
Application launched itself
- Zoom.exe (PID: 3432)
INFO
Dropped object may contain Bitcoin addresses
- Installer.exe (PID: 2948)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:21 06:07:28+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 85504 |
| InitializedDataSize: | 182784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x94b4 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.3.15457.1221 |
| ProductVersionNumber: | 6.3.15457.1221 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | RingCentral Meetings |
| CompanyName: | Zoom Video Communications, Inc. and RingCentral Inc. |
| FileDescription: | RingCentral Meetings |
| FileVersion: | 6,3,15457,1221 |
| InternalName: | RingCentral Meetings |
| LegalCopyright: | Copyright ©2012-2017 Zoom Video Communications, Inc. and RingCentral Inc. All rights reserved. |
| LegalTrademarks: | RingCentral Meetings |
| OriginalFileName: | RingCentral Meetings |
| ProductName: | RingCentral Meetings |
| ProductVersion: | 6,3,15457,1221 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2018 05:07:28 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | RingCentral Meetings |
| CompanyName: | Zoom Video Communications, Inc. and RingCentral Inc. |
| FileDescription: | RingCentral Meetings |
| FileVersion: | 6,3,15457,1221 |
| InternalName: | RingCentral Meetings |
| LegalCopyright: | Copyright ©2012-2017 Zoom Video Communications, Inc. and RingCentral Inc. All rights reserved. |
| LegalTrademarks: | RingCentral Meetings |
| OriginalFilename: | RingCentral Meetings |
| ProductName: | RingCentral Meetings |
| ProductVersion: | 6,3,15457,1221 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2018 05:07:28 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014D73 | 0x00014E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54496 |
.rdata | 0x00016000 | 0x00004494 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.37155 |
.data | 0x0001B000 | 0x00003F6C | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.90845 |
.rsrc | 0x0001F000 | 0x00023F84 | 0x00024000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.86733 |
.reloc | 0x00043000 | 0x00001FC8 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 4.39066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.0784 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 4.42725 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.14677 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 4.94867 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.53663 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.29912 | 100 | Latin 1 / Western European | English - United States | RT_STRING |
8 | 2.21706 | 84 | Latin 1 / Western European | English - United States | RT_STRING |
9 | 2.77292 | 238 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.98834 | 462 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
WININET.dll |
Total processes
33
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1052 | "C:\Users\admin\AppData\Local\Temp\RingCentral_launcher.exe" | C:\Users\admin\AppData\Local\Temp\RingCentral_launcher.exe | explorer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. and RingCentral Inc. Integrity Level: MEDIUM Description: RingCentral Meetings Exit code: 0 Version: 6,3,15457,1221 Modules
| |||||||||||||||
| 2780 | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe --action=preload --runaszvideo=TRUE | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Zoom.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 4,3,46560,0311 Modules
| |||||||||||||||
| 2948 | "C:\Users\admin\AppData\Roaming\RingCentralMeetings\ZoomDownload\Installer.exe" C:\Users\admin\AppData\Roaming\RingCentralMeetings\ZoomDownload\Installer.exe --cid= --conf.no= --zc= --pwd= --pk= --tk= --browser= --sid= --stype= --token= --uid= --uname= --rtoken= --action=launch | C:\Users\admin\AppData\Roaming\RingCentralMeetings\ZoomDownload\Installer.exe | RingCentral_launcher.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Installer Exit code: 0 Version: 4,3,46560,0311 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe" C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe --url=zoomlaunch://win.launch?action=launch& | C:\Users\admin\AppData\Roaming\Zoom\bin\Zoom.exe | Installer.exe | ||||||||||||
User: admin Company: Zoom Video Communications, Inc. Integrity Level: MEDIUM Description: Zoom Meetings Exit code: 0 Version: 4,3,46560,0311 Modules
| |||||||||||||||
Total events
1 248
Read events
1 136
Write events
112
Delete events
0
Modification events
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1052) RingCentral_launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\RingCentral_launcher_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
84
Suspicious files
24
Text files
12
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1052 | RingCentral_launcher.exe | C:\Users\admin\AppData\Roaming\RingCentralMeetings\ZoomDownload\Zoom.msi | — | |
MD5:— | SHA256:— | |||
| 1052 | RingCentral_launcher.exe | C:\Users\admin\AppData\Roaming\RingCentralMeetings\ZoomDownload\Installer.exe | executable | |
MD5:— | SHA256:— | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\leave.pcm | binary | |
MD5:— | SHA256:— | |||
| 1052 | RingCentral_launcher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@zoom[1].txt | text | |
MD5:— | SHA256:— | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\duilib_license.txt | text | |
MD5:7FAEC2006BB231D14B794A9F31769448 | SHA256:7ED2ACCA31A243BA107D8C12FDDECD52462FD326D3D2C73B04D4CF10C76765FF | |||
| 1052 | RingCentral_launcher.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\IETldCache\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\dingdong.pcm | binary | |
MD5:6634B90AC989DC297DA9F37CE3F656AC | SHA256:80A9A24A19C9749F7D76D2E3A37587A19AC812659DE2E76B50B08F5F293884CD | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\directui_license.txt | text | |
MD5:AB54B14548A4CC76DD7C27414D971111 | SHA256:6033476BE3D1D41166B65984E2BE94C87AC98DCE55BFEC887E932B696E859295 | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\record_start.pcm | binary | |
MD5:AB8A5F2981E225D3EDAACB520083835A | SHA256:193C4FFEA3DE04802E97E9E62FCD8533D8CA53E7306BA113A2234959B5262EB4 | |||
| 2948 | Installer.exe | C:\Users\admin\AppData\Roaming\Zoom\zoom_install_src\CptControl.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
3
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1052 | RingCentral_launcher.exe | GET | 301 | 52.202.62.235:80 | http://www.zoom.us/client/latest/Installer.exe | US | html | 177 b | whitelisted |
1052 | RingCentral_launcher.exe | GET | 301 | 52.202.62.235:80 | http://www.zoom.us/client/latest/Zoom.msi | US | html | 177 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1052 | RingCentral_launcher.exe | 52.202.62.235:80 | www.zoom.us | Amazon.com, Inc. | US | suspicious |
1052 | RingCentral_launcher.exe | 52.202.62.235:443 | www.zoom.us | Amazon.com, Inc. | US | suspicious |
3432 | Zoom.exe | 52.202.62.235:443 | www.zoom.us | Amazon.com, Inc. | US | suspicious |
1052 | RingCentral_launcher.exe | 52.85.188.14:443 | d11yldzmag5yn.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.zoom.us |
| whitelisted |
d11yldzmag5yn.cloudfront.net |
| whitelisted |
zoom.us |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | RingCentral_launcher.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
1052 | RingCentral_launcher.exe | A Network Trojan was detected | ET POLICY User-Agent (Launcher) |
Process | Message |
|---|---|
RingCentral_launcher.exe | WinMain start, lpCmdLine is: |
RingCentral_launcher.exe | WinMain start, parameter is: |
RingCentral_launcher.exe | installer.exe=Installer.exe&package.name=Zoom.msi&package.version=latest&package.size=4980k&downloadRoot=http://www.zoom.us/client |
RingCentral_launcher.exe | CZpDownloadMgr::FindParam |
RingCentral_launcher.exe | installer.exe |
RingCentral_launcher.exe | Installer.exe |
RingCentral_launcher.exe | CZpDownloadMgr::FindParam |
RingCentral_launcher.exe | package.name |
RingCentral_launcher.exe | Zoom.msi |
RingCentral_launcher.exe | CZpDownloadMgr::FindParam |