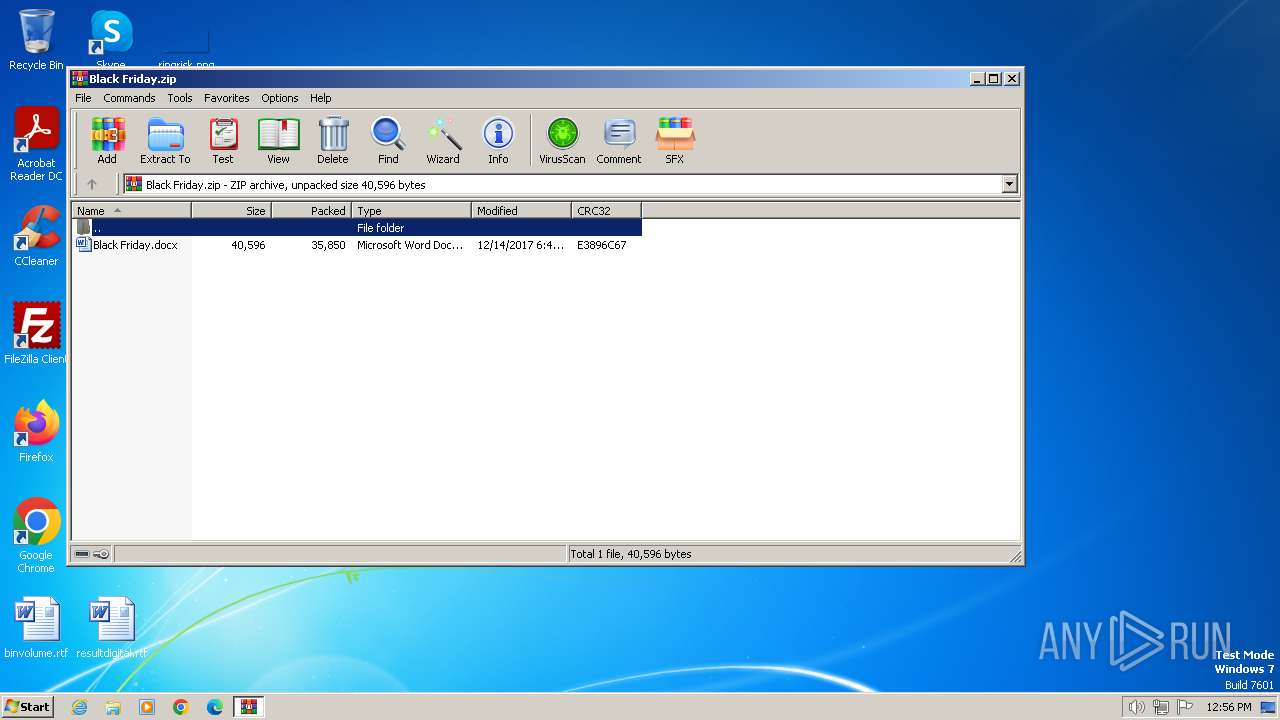
| File name: | Black Friday.zip |
| Full analysis: | https://app.any.run/tasks/811559a6-46ea-46e1-89a8-448ee55b7a5a |
| Verdict: | Malicious activity |
| Analysis date: | April 18, 2024, 11:56:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F75DD471FC651508B5785569FB39E0CB |
| SHA1: | 07C8D46F2FF4756FEB68C95F5F87A62AC98DC72F |
| SHA256: | 5FD4B1EF7A3069C8AE76B83F220E0BEFF5B2B7F939357656F4B198ED02CD850C |
| SSDEEP: | 768:7vdUBbCbWNCFD862PZjLHOGmuF27l8343uLCaOzcQQU/Rvk1Obt:7vdP0a462RPHR9F2J8I3SzOgQQUtZbt |
MALICIOUS
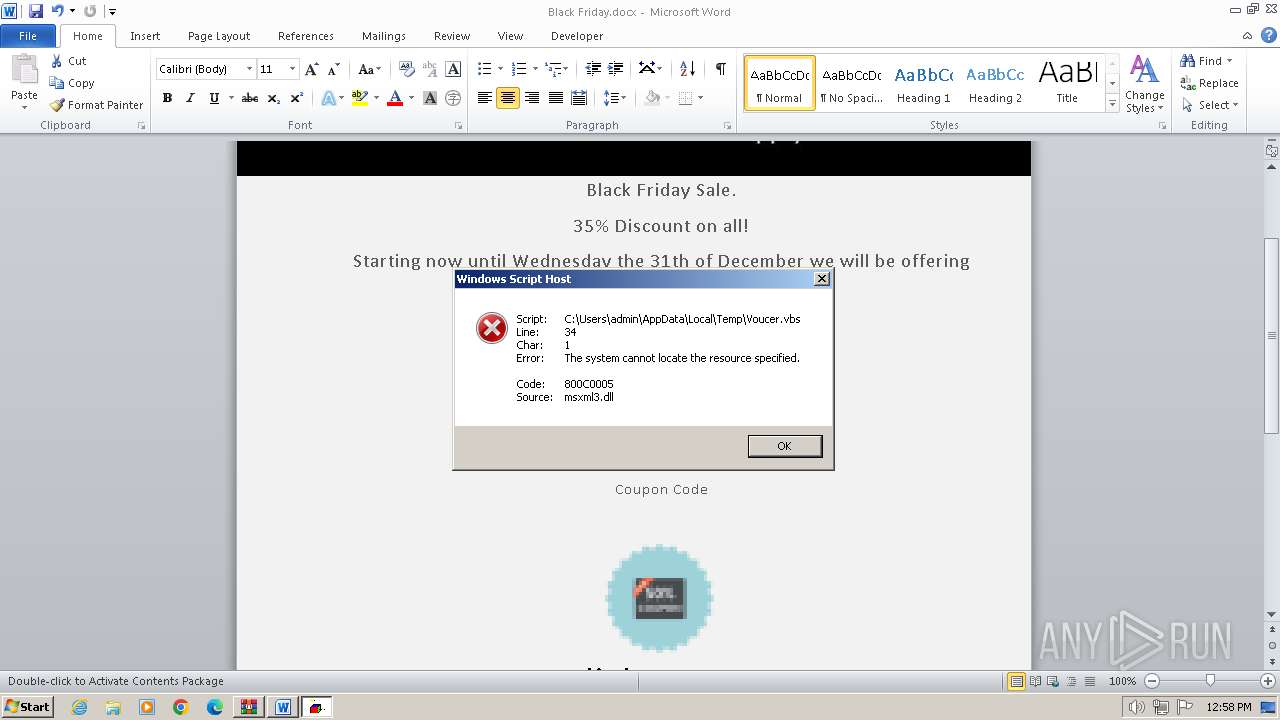
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Accesses environment variables (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Gets %appdata% folder path (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
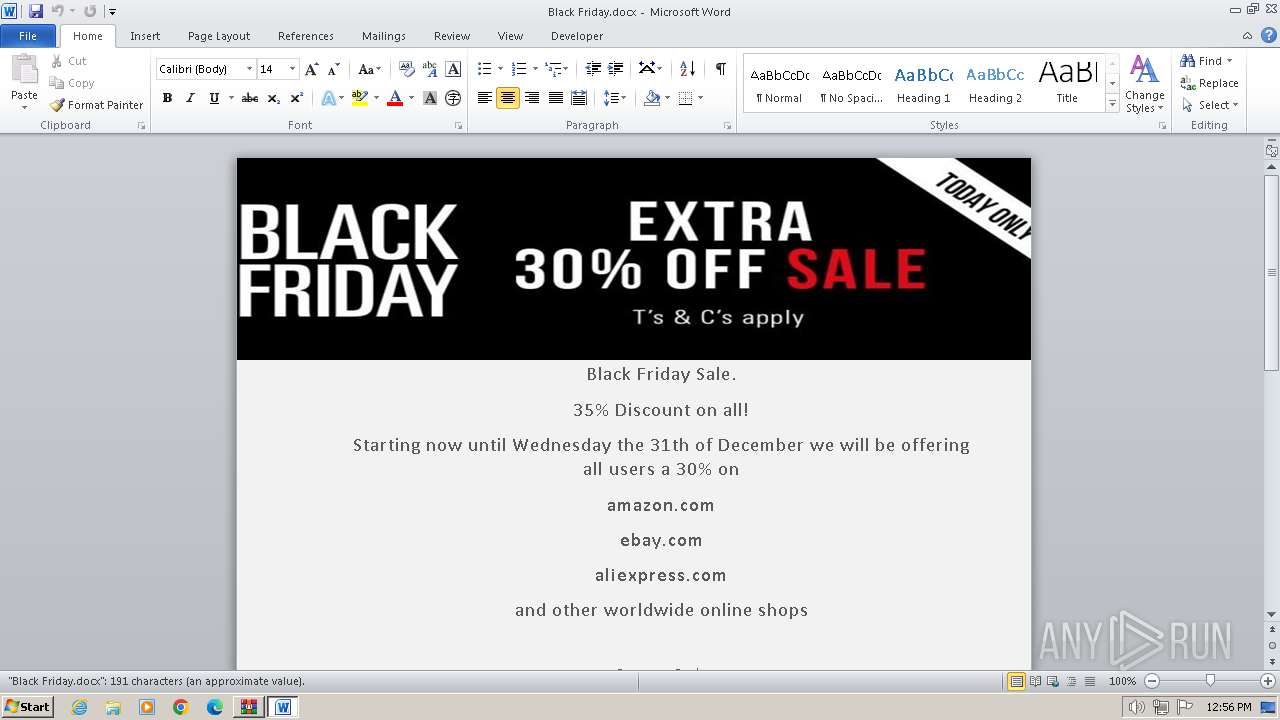
Unusual execution from MS Office
- WINWORD.EXE (PID: 3248)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Modifies registry startup key (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Unusual connection from system programs
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
SUSPICIOUS
Non-standard symbols in registry
- WINWORD.EXE (PID: 3248)
Accesses ComputerSystem(Win32_ComputerSystem) via WMI (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
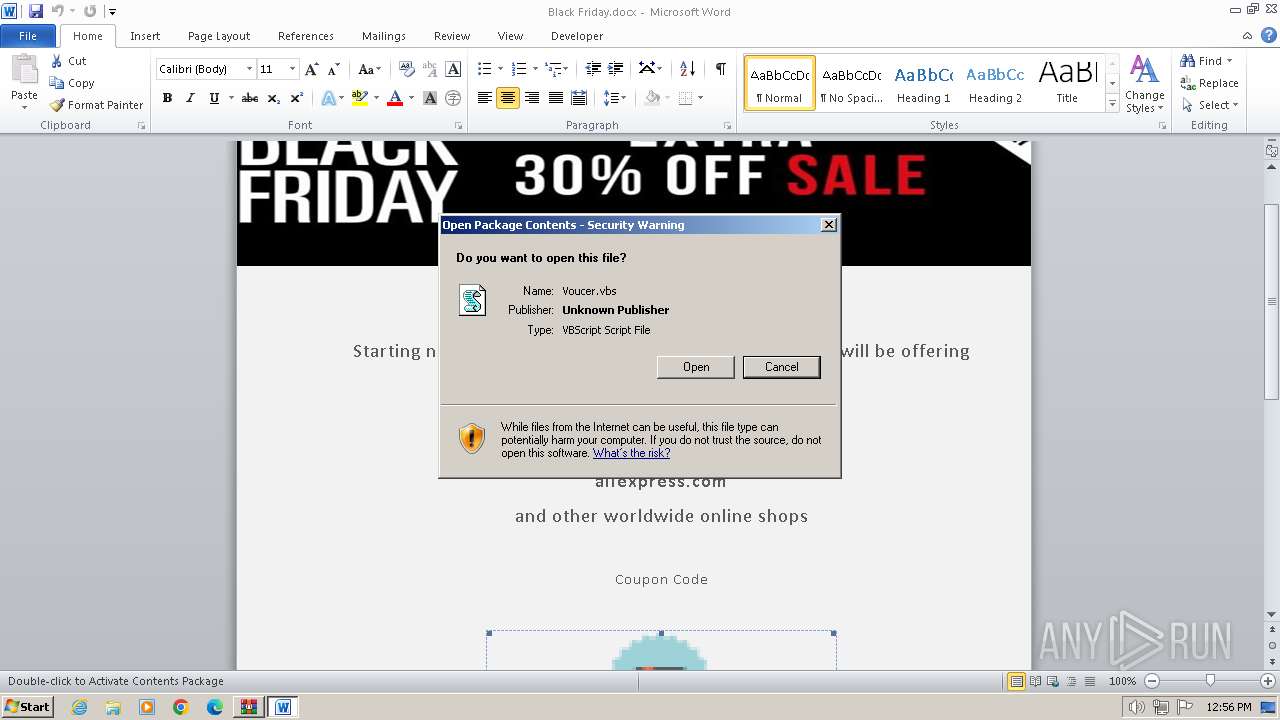
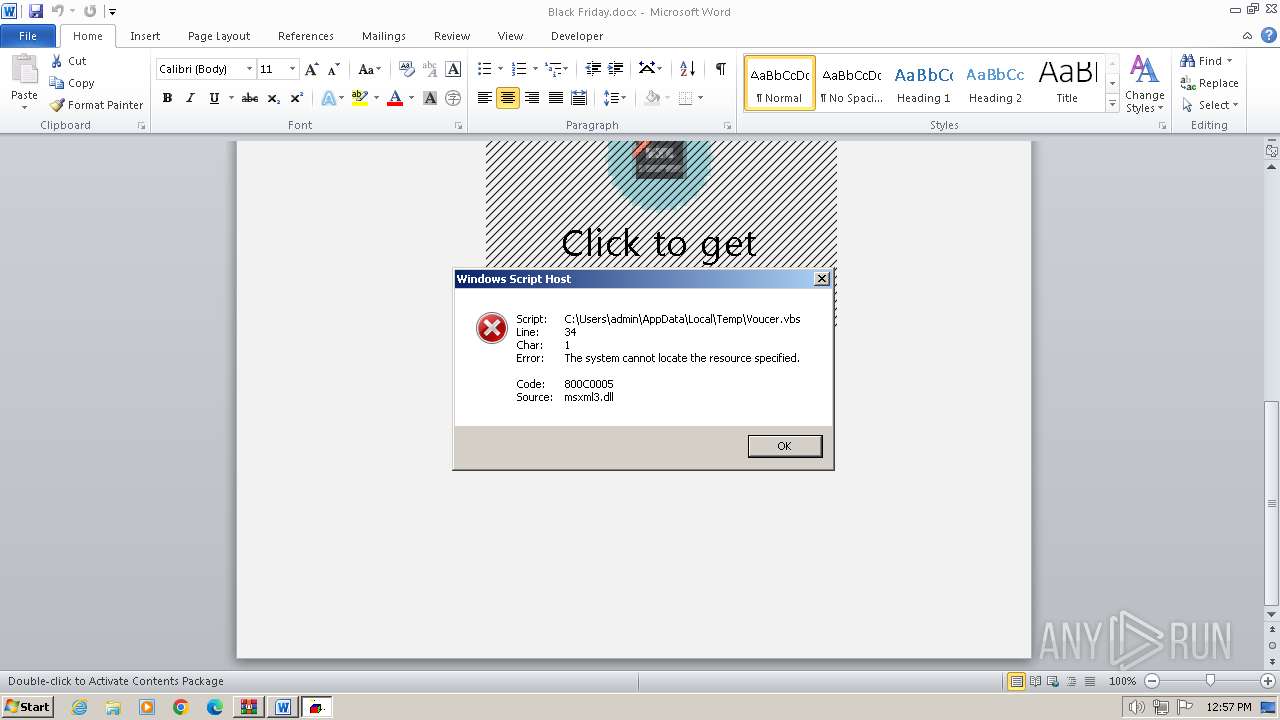
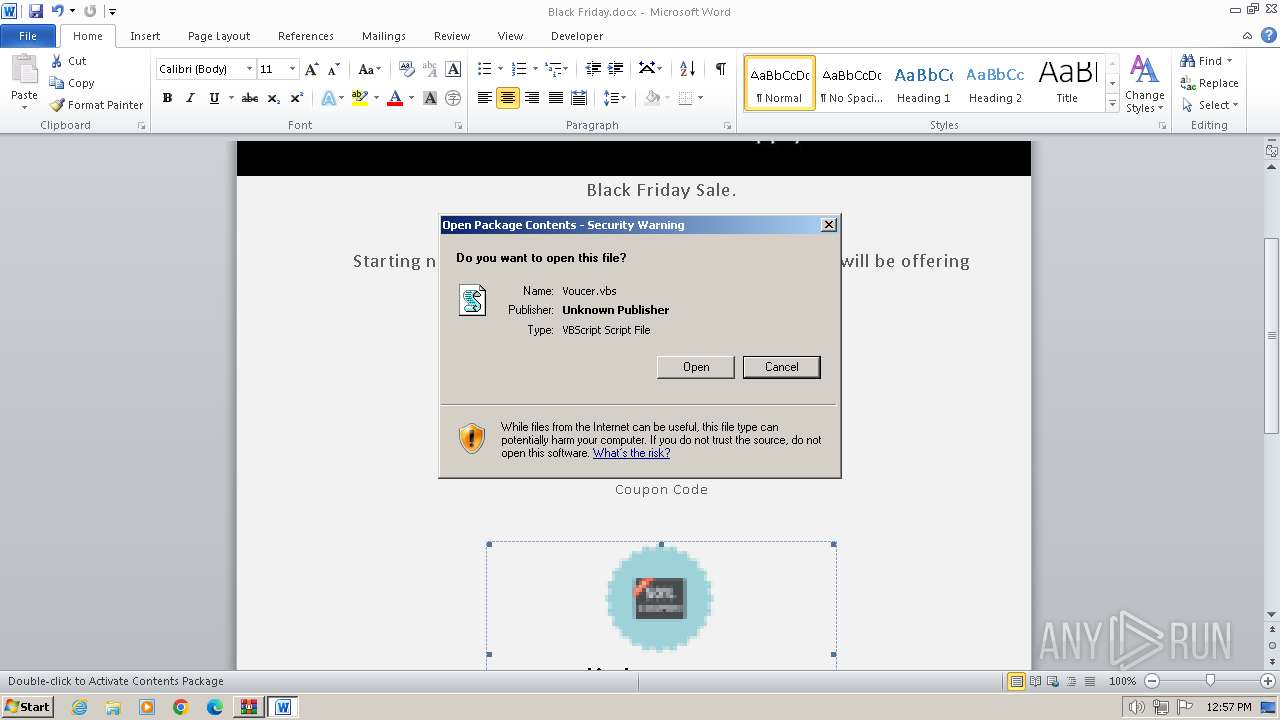
The process executes VB scripts
- WINWORD.EXE (PID: 3248)
Reads the Internet Settings
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Runs shell command (SCRIPT)
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 668)
The process uses the downloaded file
- WINWORD.EXE (PID: 3248)
Checks proxy server information
- wscript.exe (PID: 3244)
- wscript.exe (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2017:12:14 18:48:30 |
| ZipCRC: | 0xe3896c67 |
| ZipCompressedSize: | 35850 |
| ZipUncompressedSize: | 40596 |
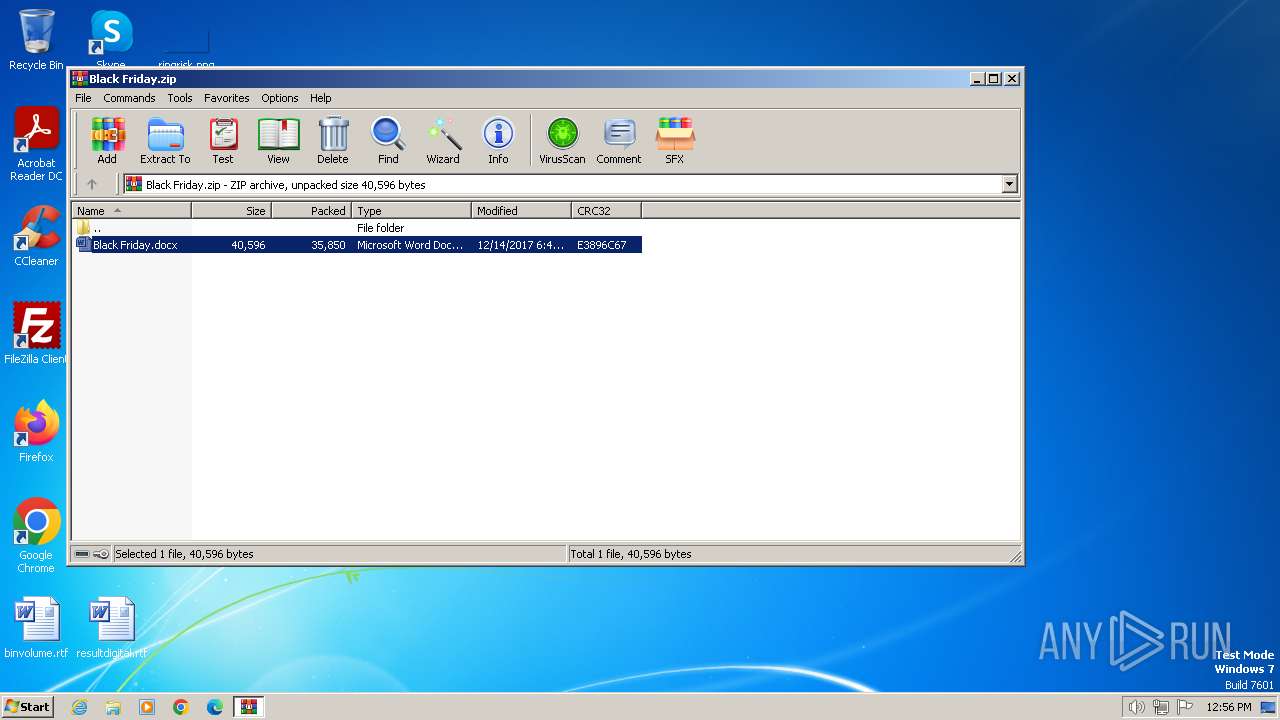
| ZipFileName: | Black Friday.docx |
Total processes
45
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Black Friday.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2172 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Voucer.vbs" | C:\Windows\System32\wscript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\schtasks.exe" /create /tn Cclenears /SC HOURLY /MO 3 /tr "C:\Users\admin\AppData\Roaming\sys.exe" | C:\Windows\System32\schtasks.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3244 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Voucer.vbs" | C:\Windows\System32\wscript.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa668.20370\Black Friday.docx" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3564 | "C:\Windows\System32\schtasks.exe" /create /tn Cclenears /SC HOURLY /MO 3 /tr "C:\Users\admin\AppData\Roaming\sys.exe" | C:\Windows\System32\schtasks.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 154
Read events
14 264
Write events
632
Delete events
258
Modification events
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Black Friday.zip | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (668) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
0
Suspicious files
3
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR141C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Voucer.vbs:Zone.Identifier | — | |
MD5:FBCCF14D504B7B2DBCB5A5BDA75BD93B | SHA256:EACD09517CE90D34BA562171D15AC40D302F0E691B439F91BE1B6406E25F5913 | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:01382D8CD815C969E64D2EFE288CA2A2 | SHA256:0F79E5435496DD8C28ADE1E8351940934FB5BCB09CBF6BB13DFA1E534C849097 | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Voucer.vbs | text | |
MD5:BBB378AEC999760C29F973B32B252534 | SHA256:F67A2DE79ED8B4DA056619DC29E16824478EE028EFB86F53AAA94536F77EF742 | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryPB0416.lex | — | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa668.20370\Black Friday.docx | document | |
MD5:D2C54126B71A2439DFC384930580786C | SHA256:A7447DB99BA60C2F7BFD9E9BCFADFB05A4FC0EA214450B76EA85D386DB1F727B | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\UProof\ExcludeDictionaryEN0409.lex | — | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A737D620.emf | emf | |
MD5:FB813ED34231B6DE535CB1D3222B5656 | SHA256:A98E291138500445FC9829AA24AE87F1EDF056947321F7023F7B67F924F049F4 | |||
| 3248 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIa668.20370\~$ack Friday.docx | pgc | |
MD5:4FC503FA31B7FDC3CD9D446BB917B0C4 | SHA256:2DA665C53B8CDB1DD674864B14E6FD8ECDBFBECBEF0CEEA90192E666B60A4661 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
1
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3244 | wscript.exe | 49.13.77.253:443 | forum.cryptopia.gdn | Hetzner Online GmbH | DE | unknown |
2172 | wscript.exe | 49.13.77.253:443 | forum.cryptopia.gdn | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
forum.cryptopia.gdn |
| unknown |
dns.msftncsi.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gdn Domain |