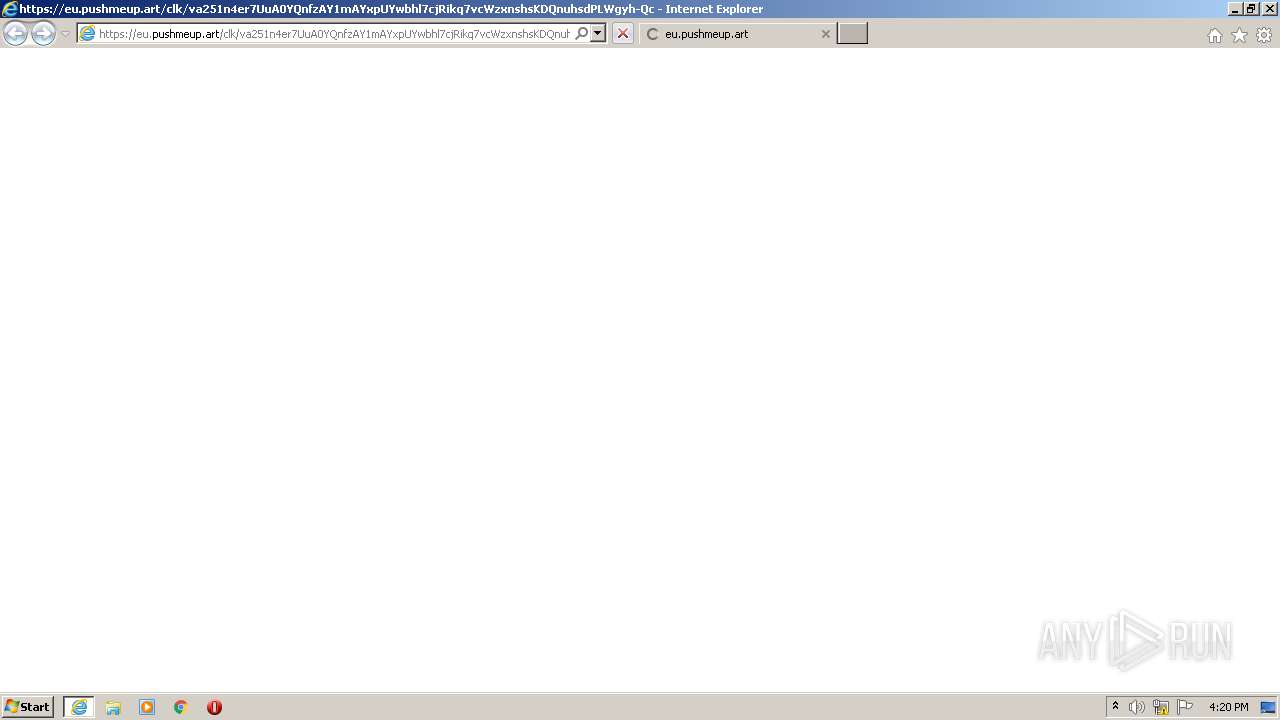
| URL: | https://eu.pushmeup.art/clk/va251n4er7UuA0YQnfzAY1mAYxpUYwbhl7cjRikq7vcWzxnshsKDQnuhsdPLWgyh-QcjxIHDc4waOh8DN9ksFYW3fvnE7CReHO0fTsZlN9jW3gyOYwV-VwXEizbF15BmsgX_gq_a1TDoPtv0BugDzXYV2X26T2yWmq2XzS2g8_pyV9hLXV7irBt_ZQ3Hizef-pZRbmBDnoBrMbqapEzL_kXMy1hUcTwXtElH4i2EBCYNO-gZR_i5HXITXkrrpp07N3S64SoW4z66r3RugIJPB5Rt-ECjZ4eN8KO8L59v6DG7C_IHLiuh4fP4WHRwvxdGg5gBR5bf2jdIMwpZcj606XsMyvTCOI737loZ-fXm15fiOre88qjkKcmZbXcpNYjQn3Yp-5WpvFWZz4BZqljwgOlbWwWawLsyz_uGxeI8DdxDOmlyjExMCRXiPoV2A1lV1hBUltylx8O9G0LSp6wxW4yGrsMfsQqk7AH2H-vNxORdlTcJPjvIMY8za5r786d22-FKrxzpRk62EH3nu9U9cRJJs4XPxjx7-A9qE18tjZEBfdRlZw_16rDSm02JfVRFLoesZ7GxybVjEQ-yU1Iv8i8W-55l7XvYi77a18V3U0yzw3yEmjgDKIOVGBg1HW_lhHQRLvXQf8BAsgOLeyuMkwDB3ZN4P4_V4Fb37v5fo1aO2jlWjDus6v5_oxQSwx7iDBUJ5nI8LM41vpW_A5IkSAkjblZGO-xkxnBksP2krLBhium2tz3hRBsTCYu3dhR994gnLe1vrDy0vO-4z4Dh86JRqdJgZW3kgss8aqI8j5cD2jgF-ta-I0LAIvXGQWDIyorpNaMkji6j3DSFcM1TzQ |
| Full analysis: | https://app.any.run/tasks/4c2852e2-a822-4739-8d2d-6038afd1246c |
| Verdict: | Malicious activity |
| Analysis date: | May 12, 2021, 15:19:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D59586AE1942B02A3B6061ACDDC263B9 |
| SHA1: | 7EECB312444360D8D7F84B590F0ADE2A9A7471C2 |
| SHA256: | 5FCCAAA25A895D037602A39C7717A3A4CBAB8EE098846CFEB6D9ED94E0281E17 |
| SSDEEP: | 24:25uE/M5uNN0Wt/3w3XR6rUBQonPK5MdFIQP13:ECuNuWl3Wh33PqM3IS13 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 1736)
Creates files in the user directory
- iexplore.exe (PID: 3504)
Reads internet explorer settings
- iexplore.exe (PID: 3504)
Changes internet zones settings
- iexplore.exe (PID: 1736)
Reads settings of System Certificates
- iexplore.exe (PID: 3504)
- iexplore.exe (PID: 1736)
Changes settings of System certificates
- iexplore.exe (PID: 1736)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1736 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://eu.pushmeup.art/clk/va251n4er7UuA0YQnfzAY1mAYxpUYwbhl7cjRikq7vcWzxnshsKDQnuhsdPLWgyh-QcjxIHDc4waOh8DN9ksFYW3fvnE7CReHO0fTsZlN9jW3gyOYwV-VwXEizbF15BmsgX_gq_a1TDoPtv0BugDzXYV2X26T2yWmq2XzS2g8_pyV9hLXV7irBt_ZQ3Hizef-pZRbmBDnoBrMbqapEzL_kXMy1hUcTwXtElH4i2EBCYNO-gZR_i5HXITXkrrpp07N3S64SoW4z66r3RugIJPB5Rt-ECjZ4eN8KO8L59v6DG7C_IHLiuh4fP4WHRwvxdGg5gBR5bf2jdIMwpZcj606XsMyvTCOI737loZ-fXm15fiOre88qjkKcmZbXcpNYjQn3Yp-5WpvFWZz4BZqljwgOlbWwWawLsyz_uGxeI8DdxDOmlyjExMCRXiPoV2A1lV1hBUltylx8O9G0LSp6wxW4yGrsMfsQqk7AH2H-vNxORdlTcJPjvIMY8za5r786d22-FKrxzpRk62EH3nu9U9cRJJs4XPxjx7-A9qE18tjZEBfdRlZw_16rDSm02JfVRFLoesZ7GxybVjEQ-yU1Iv8i8W-55l7XvYi77a18V3U0yzw3yEmjgDKIOVGBg1HW_lhHQRLvXQf8BAsgOLeyuMkwDB3ZN4P4_V4Fb37v5fo1aO2jlWjDus6v5_oxQSwx7iDBUJ5nI8LM41vpW_A5IkSAkjblZGO-xkxnBksP2krLBhium2tz3hRBsTCYu3dhR994gnLe1vrDy0vO-4z4Dh86JRqdJgZW3kgss8aqI8j5cD2jgF-ta-I0LAIvXGQWDIyorpNaMkji6j3DSFcM1TzQ" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3504 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1736 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
775
Read events
683
Write events
88
Delete events
4
Modification events
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1736) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {85E05605-B335-11EB-818E-1203334A04AF} |
Value: 0 | |||
Executable files
0
Suspicious files
17
Text files
13
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1D88.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1D89.tmp | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BEU4BAEC.txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\XVN3CZZ3.txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BB30QIUP.txt | — | |
MD5:— | SHA256:— | |||
| 3504 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8INJ6NK5.txt | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2ECF.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab2ECE.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2ED0.tmp | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar2ED1.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
31
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | iexplore.exe | GET | 200 | 88.221.223.40:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMSbkwAFL1M8t4qtA6N%2FWwoSw%3D%3D | unknown | der | 503 b | shared |
3504 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3504 | iexplore.exe | GET | 200 | 88.221.223.40:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRqDIm3sMJ%2BjazfhY0RTa%2BTBw%3D%3D | unknown | der | 503 b | shared |
3504 | iexplore.exe | GET | 200 | 88.221.223.58:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
3504 | iexplore.exe | GET | 200 | 88.221.223.58:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
1736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3504 | iexplore.exe | GET | 200 | 88.221.223.35:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgRqDIm3sMJ%2BjazfhY0RTa%2BTBw%3D%3D | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1736 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
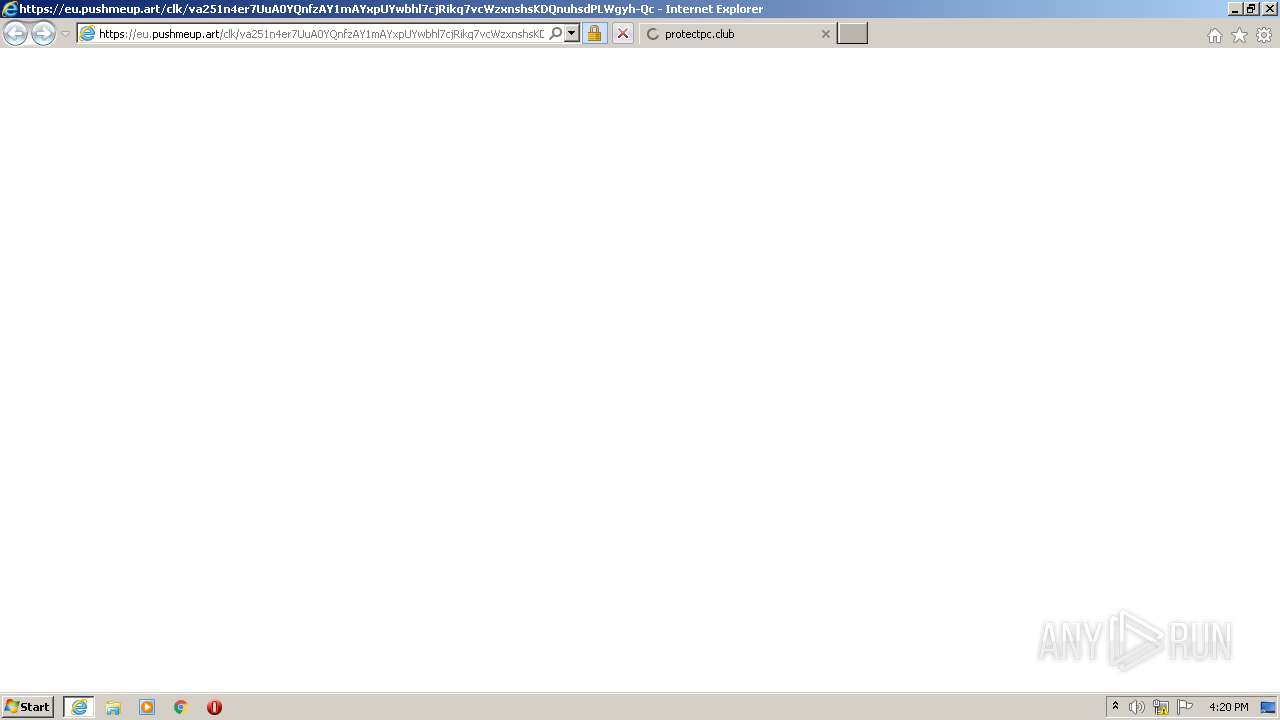
3504 | iexplore.exe | 161.35.211.77:443 | protectpc.club | — | US | suspicious |
3504 | iexplore.exe | 18.195.128.171:443 | t.avroute01.com | Amazon.com, Inc. | DE | suspicious |
3504 | iexplore.exe | 139.45.197.238:443 | nougacoush.com | — | US | malicious |
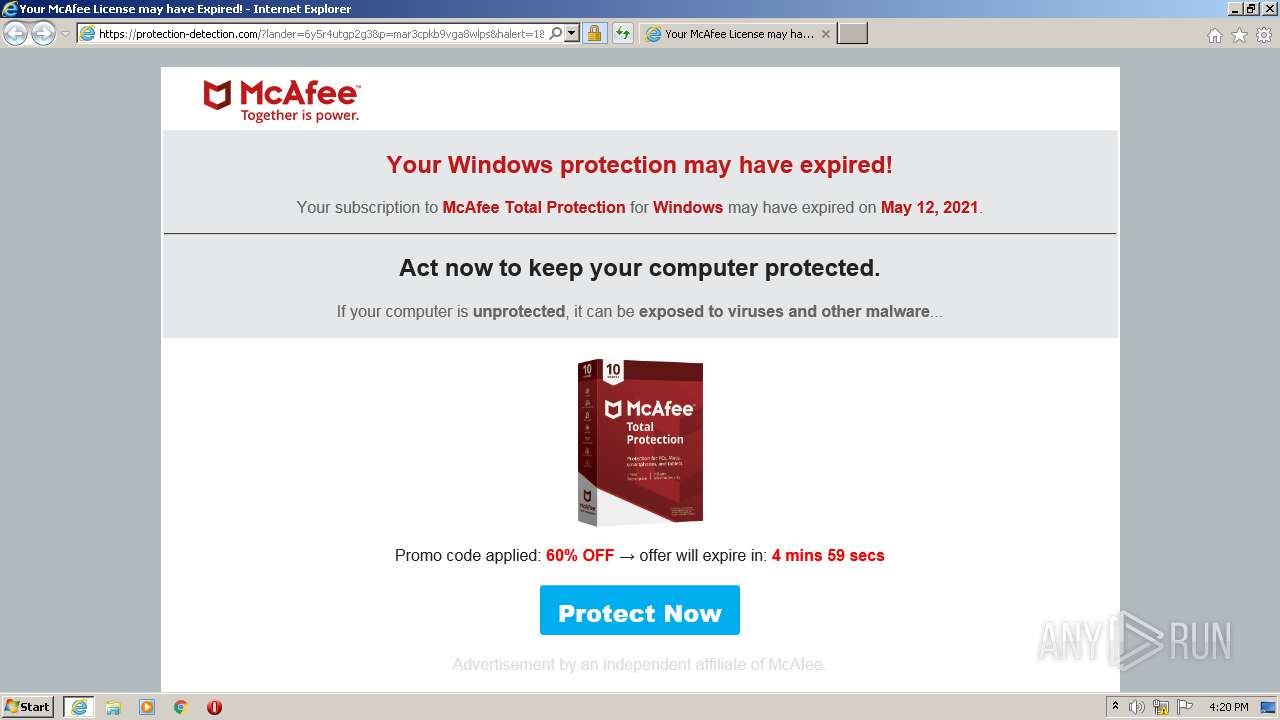
3504 | iexplore.exe | 104.21.35.157:443 | protection-detection.com | Cloudflare Inc | US | unknown |
3504 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3504 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
1736 | iexplore.exe | 104.21.35.157:443 | protection-detection.com | Cloudflare Inc | US | unknown |
3504 | iexplore.exe | 88.221.223.58:80 | crl.identrust.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
eu.pushmeup.art |
| suspicious |
crl.identrust.com |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
protectpc.club |
| suspicious |
nougacoush.com |
| malicious |
t.avroute01.com |
| suspicious |
protection-detection.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |