| File name: | Boom3D.msi |
| Full analysis: | https://app.any.run/tasks/2576a6ed-a01e-4911-9f4e-654a6ec03263 |
| Verdict: | Malicious activity |
| Analysis date: | October 16, 2024, 14:30:42 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-msi |
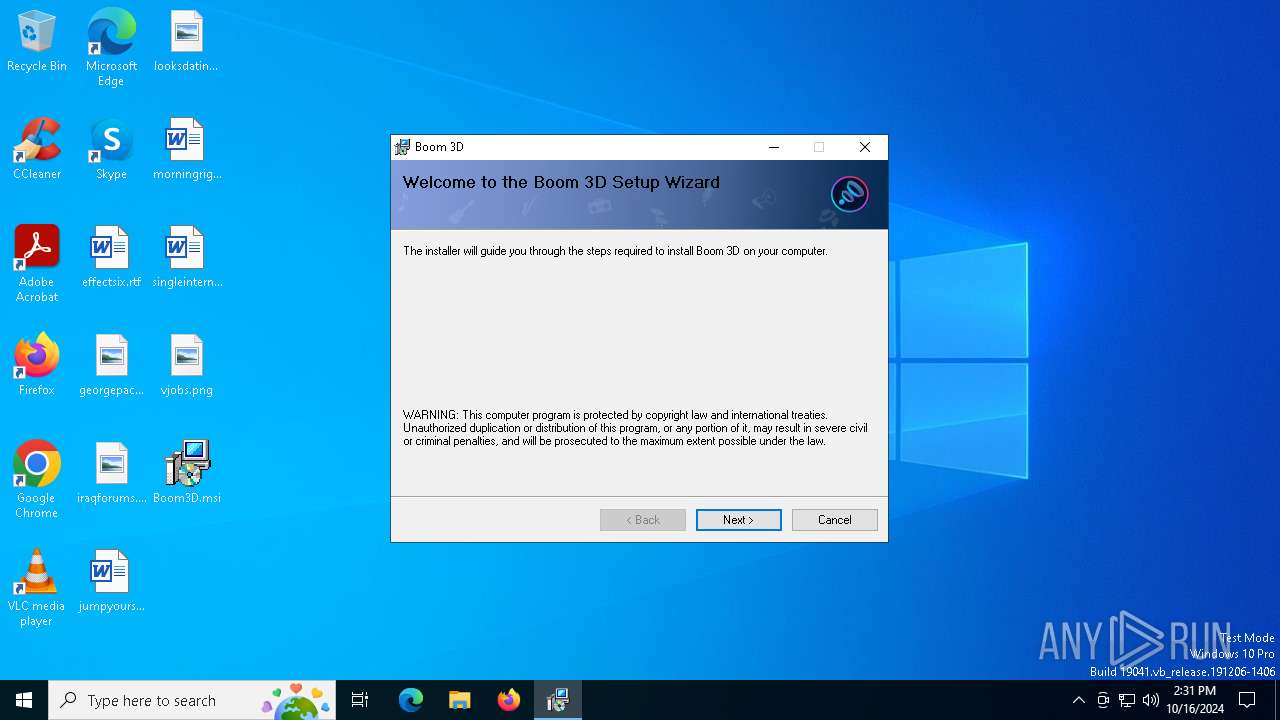
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 07:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: x64;0, Number of Pages: 200, Revision Number: {1531349A-BADF-4044-98AA-8687822F2A75}, Title: Boom 3D, Author: Global Delight, Keywords: Boom, Number of Words: 2, Last Saved Time/Date: Wed Mar 6 06:07:26 2024, Last Printed: Wed Mar 6 06:07:26 2024 |
| MD5: | B1EF831952205F5C6B9DC1D1369221DC |
| SHA1: | 6927C76EF7860C5F483D8B211D73EB11C13F7945 |
| SHA256: | 5FC768D5C1C611C39EEAE7BDE3D05B322FF37FC87272A634B4BBCFEDF2C496EB |
| SSDEEP: | 393216:56U1IvEFG1PQ0WDMBfQCzPDgDY+Pr5gSg90d79NP78pVWNU1RsG0If3uDt/iVlem:5LrYfQq7g977t86Nu0c+DNib |
MALICIOUS
No malicious indicators.SUSPICIOUS
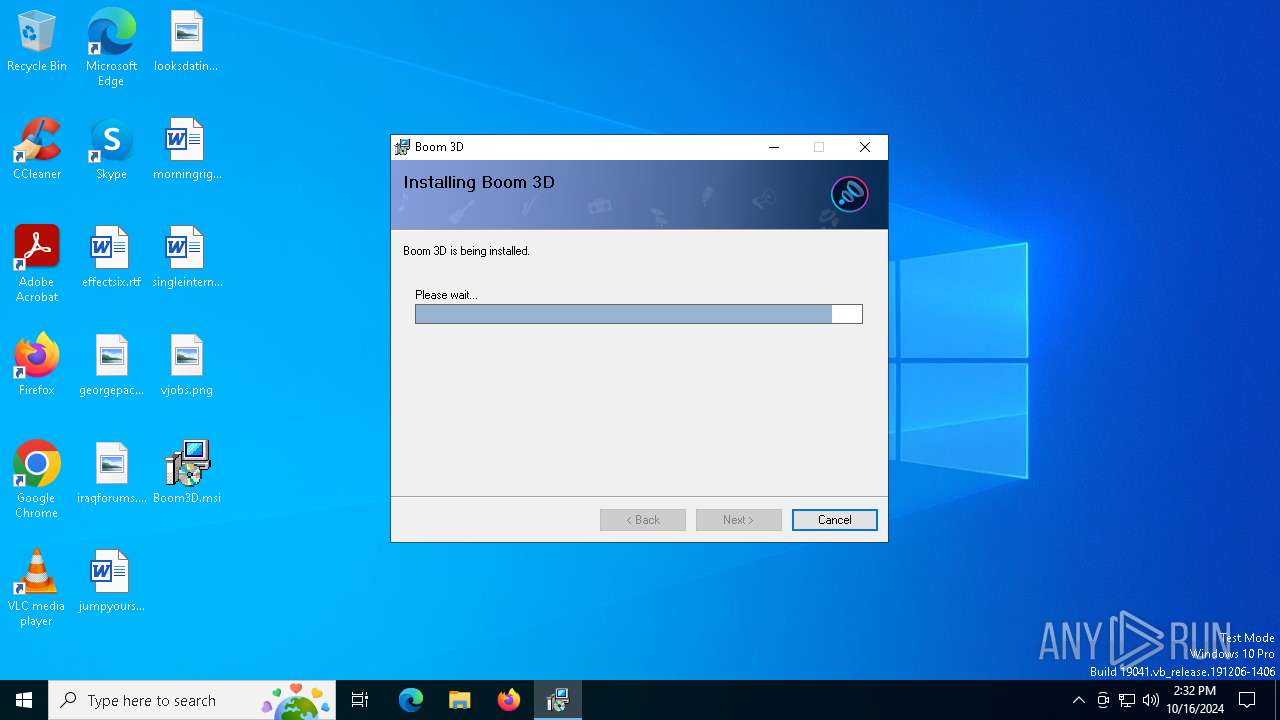
Process drops legitimate windows executable
- msiexec.exe (PID: 5356)
- msiexec.exe (PID: 7160)
Executes as Windows Service
- VSSVC.exe (PID: 6164)
The process drops C-runtime libraries
- msiexec.exe (PID: 7160)
Executable content was dropped or overwritten
- drvinst.exe (PID: 6420)
- drvinst.exe (PID: 4548)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 7160)
- drvinst.exe (PID: 6420)
- drvinst.exe (PID: 4548)
INFO
Reads the software policy settings
- msiexec.exe (PID: 5356)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5356)
Creates files or folders in the user directory
- msiexec.exe (PID: 5356)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5356)
- msiexec.exe (PID: 7160)
Checks proxy server information
- msiexec.exe (PID: 5356)
Manages system restore points
- SrTasks.exe (PID: 5372)
Application launched itself
- msiexec.exe (PID: 7160)
- msedge.exe (PID: 6820)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | x64;0 |
| Pages: | 200 |
| RevisionNumber: | {1531349A-BADF-4044-98AA-8687822F2A75} |
| Title: | Boom 3D |
| Subject: | - |
| Author: | Global Delight |
| Keywords: | Boom |
| Comments: | - |
| Words: | 2 |
| ModifyDate: | 2024:03:06 06:07:26 |
| LastPrinted: | 2024:03:06 06:07:26 |
Total processes
156
Monitored processes
34
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | C:\Windows\System32\MsiExec.exe -Embedding DC467C945A1215DC70DAF3F44F867A0C E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1172 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2368 --field-trial-handle=2372,i,4130840516954828194,9084604367969474869,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
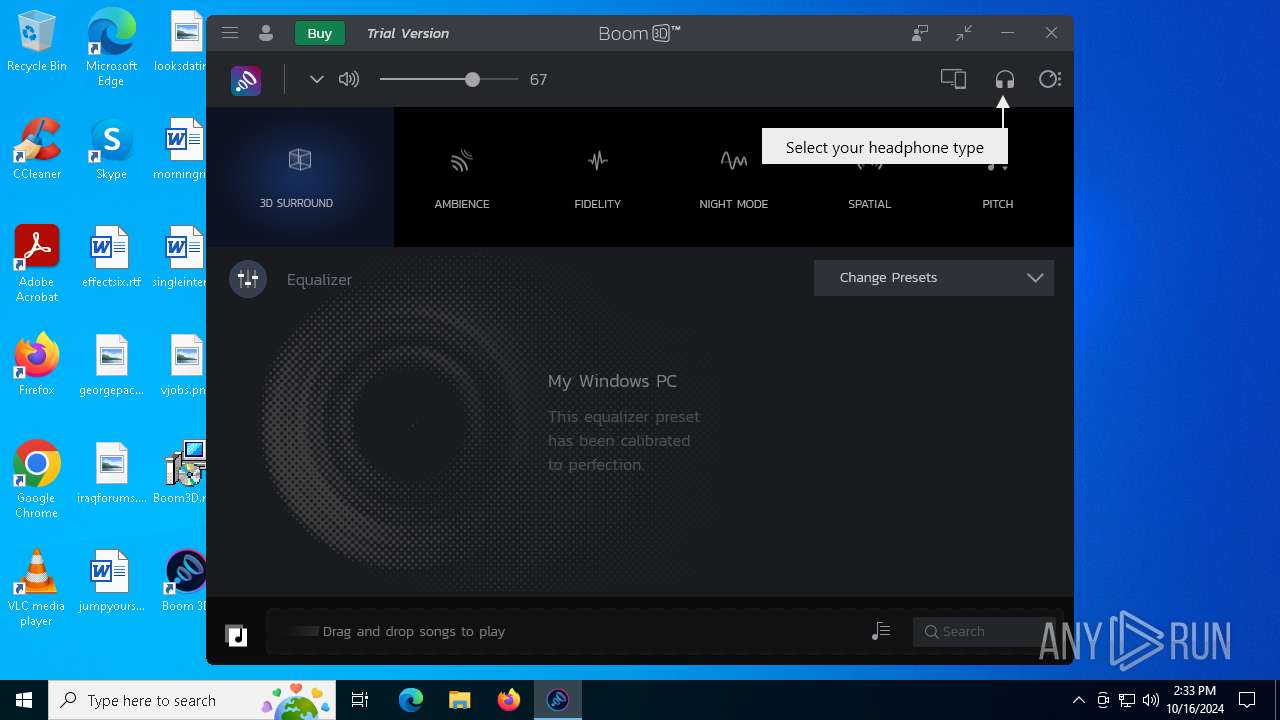
| 3604 | "C:\Program Files\Global Delight\Boom 3D\Boom3D.exe" | C:\Program Files\Global Delight\Boom 3D\Boom3D.exe | — | msiexec.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Version: 1.6.0.0 | |||||||||||||||
| 3832 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2776 --field-trial-handle=2372,i,4130840516954828194,9084604367969474869,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 3952 | C:\Windows\syswow64\MsiExec.exe -Embedding EB9723F7E3BA38045124C92B4869BA7E | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4548 | DrvInst.exe "2" "211" "ROOT\MEDIA\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:ed86ca111108b3f4:BOOMVAD_SA:16.51.4.105:root\gdpl_boom," "449733023" "00000000000001E8" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
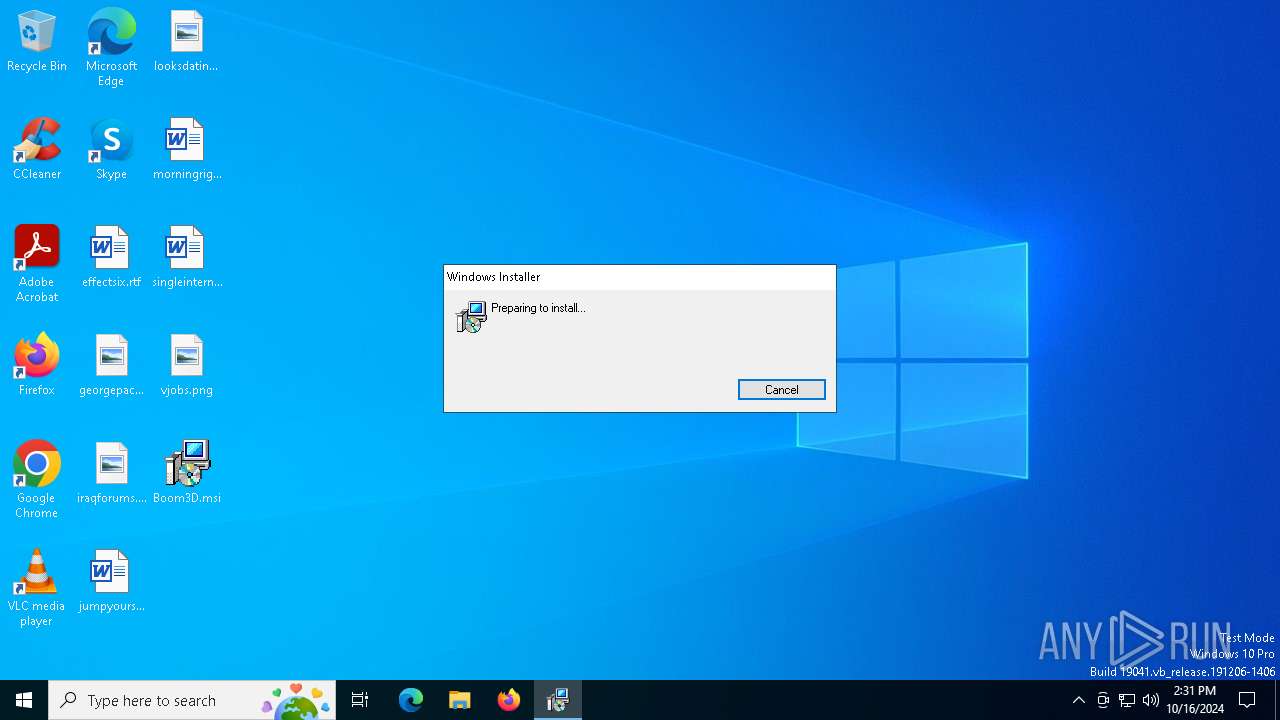
| 5356 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\Desktop\Boom3D.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5372 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5588 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2380 --field-trial-handle=2372,i,4130840516954828194,9084604367969474869,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
| 5944 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3680 --field-trial-handle=2372,i,4130840516954828194,9084604367969474869,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | |||||||||||||||
Total events
10 491
Read events
9 730
Write events
752
Delete events
9
Modification events
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000008E77611CD81FDB01F81B000020180000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 48000000000000008E77611CD81FDB01F81B000020180000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000593A201DD81FDB01F81B000020180000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000593A201DD81FDB01F81B000020180000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000EB9E221DD81FDB01F81B000020180000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000009CB9291DD81FDB01F81B000020180000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000007408A01ED81FDB01F81B000020180000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7160) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B26BA21ED81FDB01F81B0000D8180000E8030000010000000000000000000000B8A3A011E31BDF47841ED4961FE4CEA000000000000000000000000000000000 | |||
| (PID) Process: | (6164) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000F25FAE1ED81FDB011418000038050000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
524
Suspicious files
175
Text files
70
Unknown types
23
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7160 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7160 | msiexec.exe | C:\Windows\Installer\9aa5d.msi | — | |
MD5:— | SHA256:— | |||
| 5356 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\18E6B4A57A6BC7EC9B861CDF2D6D0D02_EF52C1EC85F21F31CC0157A5C8803013 | binary | |
MD5:C956D5825FCA2C5294AA5C2F2391F020 | SHA256:6201A65BF489CE193600546458A343931E3B08CBF1E7020161A4934BDEAE6F01 | |||
| 7160 | msiexec.exe | C:\Program Files\Global Delight\Boom 3D\System.Security.Cryptography.Xml.dll | executable | |
MD5:2B6DC8A1092CF5D0986E41BD348FA664 | SHA256:96F00150F91D1C9FAFBDED91141FE3A743AFDE13AC5158D26CA4FDBED0AA4F04 | |||
| 7160 | msiexec.exe | C:\Program Files\Global Delight\Boom 3D\System.Reflection.TypeExtensions.dll | executable | |
MD5:CDB9345E660EB8F1F2AF43ECD036EAD0 | SHA256:0E4FB580B585EEEE5B5320355DB8C4272C50D7BB020A78732EA00B27D893BEFF | |||
| 5356 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | der | |
MD5:675E7618F1C62BD4FF0ECAF828FC8275 | SHA256:699187D2804D97607F91CEBAB92A517607F5506E0732A0EF4B19EC8606D51624 | |||
| 7160 | msiexec.exe | C:\Windows\Temp\~DF6A11A26BA4BD0CD3.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 7160 | msiexec.exe | C:\Windows\Installer\MSIAF8E.tmp | executable | |
MD5:B77A2A2768B9CC78A71BBFFB9812B978 | SHA256:F74C97B1A53541B059D3BFAFE41A79005CE5065F8210D7DE9F1B600DC4E28AA0 | |||
| 7160 | msiexec.exe | C:\Windows\Installer\MSIB413.tmp | binary | |
MD5:AFD6885D5BFA31088614C7605F5BCE1F | SHA256:F2A7C87B986D44217F53E1C8E13BECC8267BBBA6FD111169E628C48377477666 | |||
| 7160 | msiexec.exe | C:\Program Files\Global Delight\Boom 3D\de\PresentationCore.resources.dll | executable | |
MD5:D67E49077E2E97F74BFE5DAABB11EDAE | SHA256:77AD96D0490ED939549742C3C2F75F0CA6C87B55D0F068792EB3671AFF31A83E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
31
DNS requests
163
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6944 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6944 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5356 | msiexec.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
5356 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCECxuvV2pAFA7XfjTGAz9Bxg%3D | unknown | — | — | whitelisted |
5356 | msiexec.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
— | — | POST | — | 3.232.43.106:443 | https://countly.globaldelight.net/i?app_key=5821cdb3c6c1257bdc9c1507dcd6006c8d85d2c0&device_id=525400852E0F&t=0&sdk_name=csharp-netstd&sdk_version=23.02.0×tamp=1729089161390&dow=3&hour=14&tz=0&begin_session=1&metrics=%7B%0D%0A%20%20%22_os%22:%20%22Windows%2010%22,%0D%0A%20%20%22_os_version%22:%20%2210.0.19045.0%22,%0D%0A%20%20%22_app_version%22:%20%221.6.0%22,%0D%0A%20%20%22_locale%22:%20%22en-US%22%0D%0A%7D | unknown | — | — | unknown |
— | — | GET | 200 | 2.16.164.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl%20 | unknown | — | — | whitelisted |
— | — | POST | — | 3.232.43.106:443 | https://countly.globaldelight.net/i?app_key=5821cdb3c6c1257bdc9c1507dcd6006c8d85d2c0&device_id=525400852E0F&events=%5B%7B%22key%22%3A%22Welcome%20Screen%22%2C%22count%22%3A1%2C%22timestamp%22%3A1729089161831%7D%2C%7B%22key%22%3A%22Onboarding%3A%20Continue%22%2C%22count%22%3A1%2C%22timestamp%22%3A1729089165166%7D%2C%7B%22key%22%3A%22Onboarding%20Screen%22%2C%22count%22%3A1%2C%22timestamp%22%3A1729089165518%7D%2C%7B%22key%22%3A%22First%20Launch%22%2C%22count%22%3A1%2C%22timestamp%22%3A1729089168442%7D%2C%7B%22key%22%3A%22Onboarding%3A%20Start%20Boomin%22%2C%22count%22%3A1%2C%22timestamp%22%3A1729089220478%7D%5D&sdk_version=23.02.0&sdk_name=csharp-netstd&hour=14&dow=3&tz=0×tamp=1729089220480&t=0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6944 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6944 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
5356 | msiexec.exe | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
5356 | msiexec.exe | 104.18.38.233:80 | ocsp.comodoca.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
countly.globaldelight.net |
| unknown |
gdapi.globaldelight.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
— | — | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |