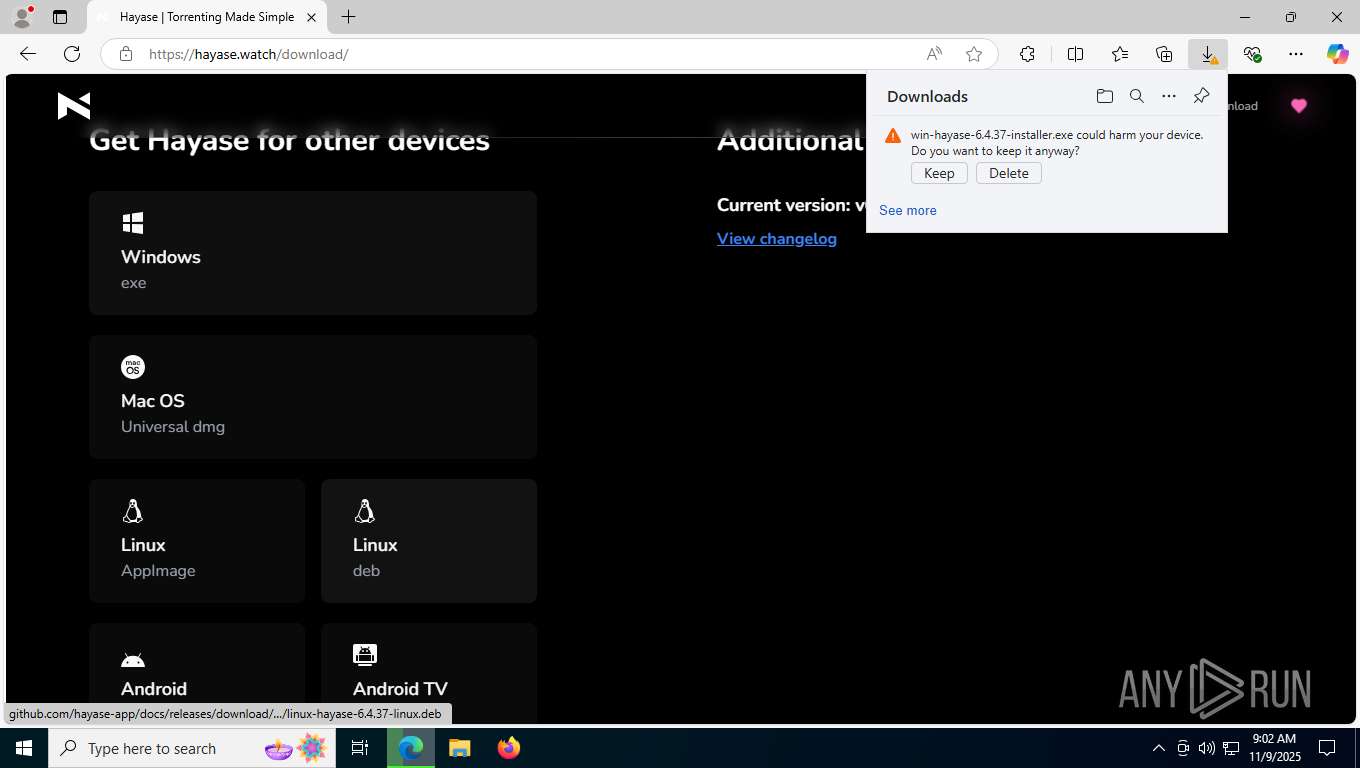
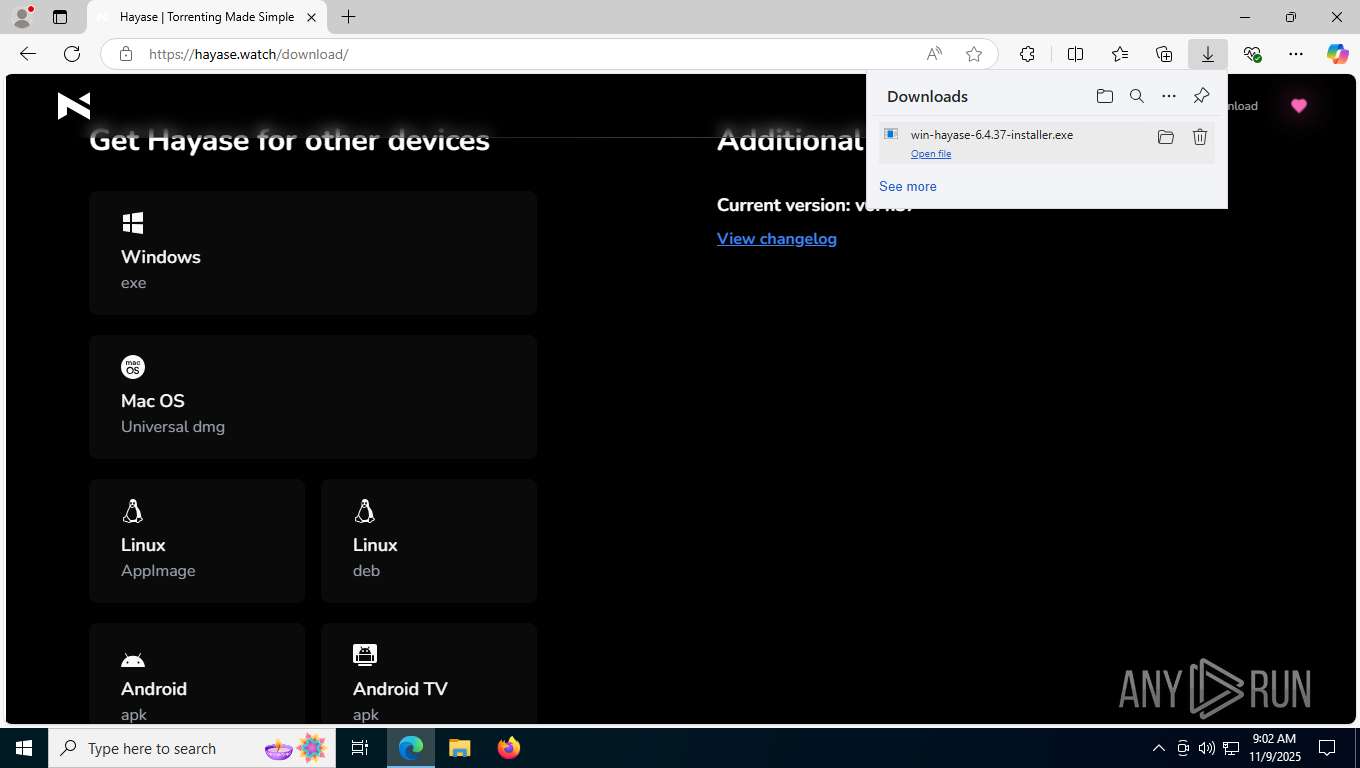
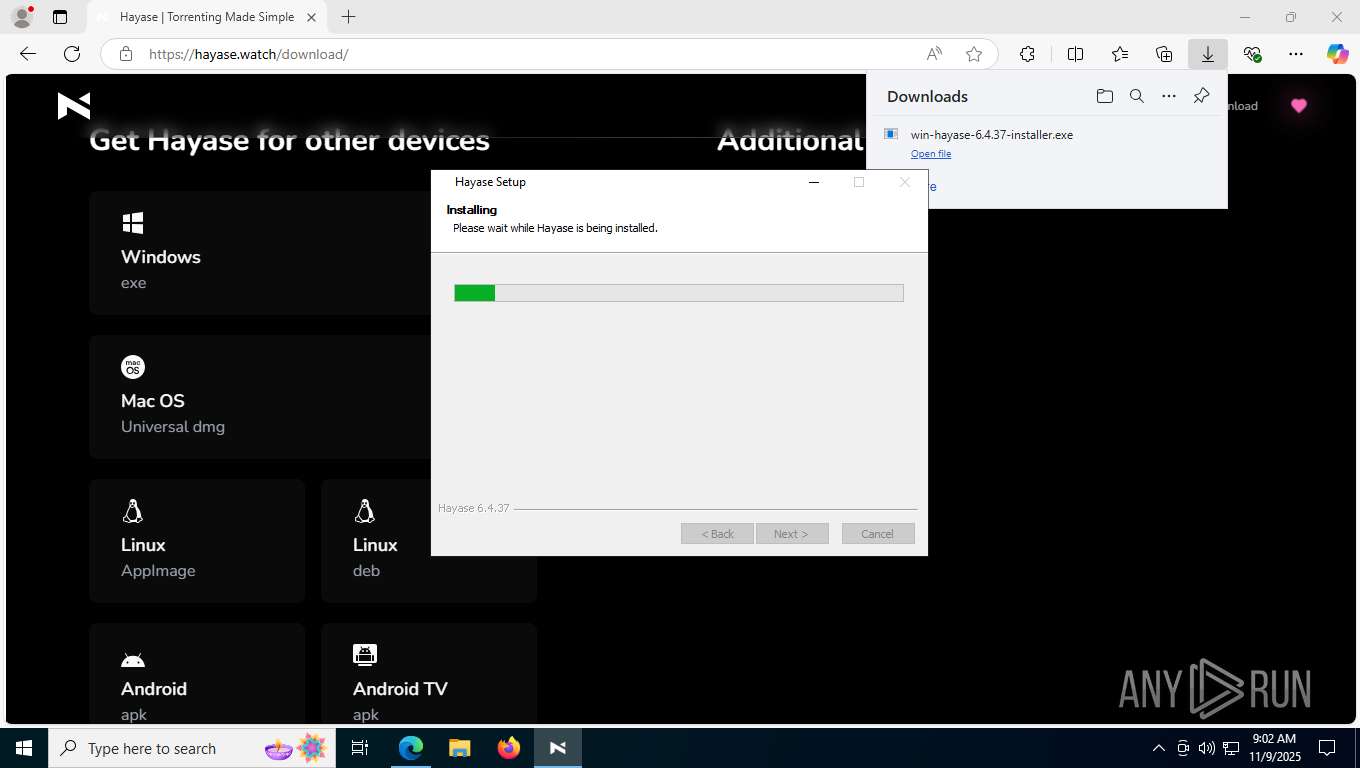
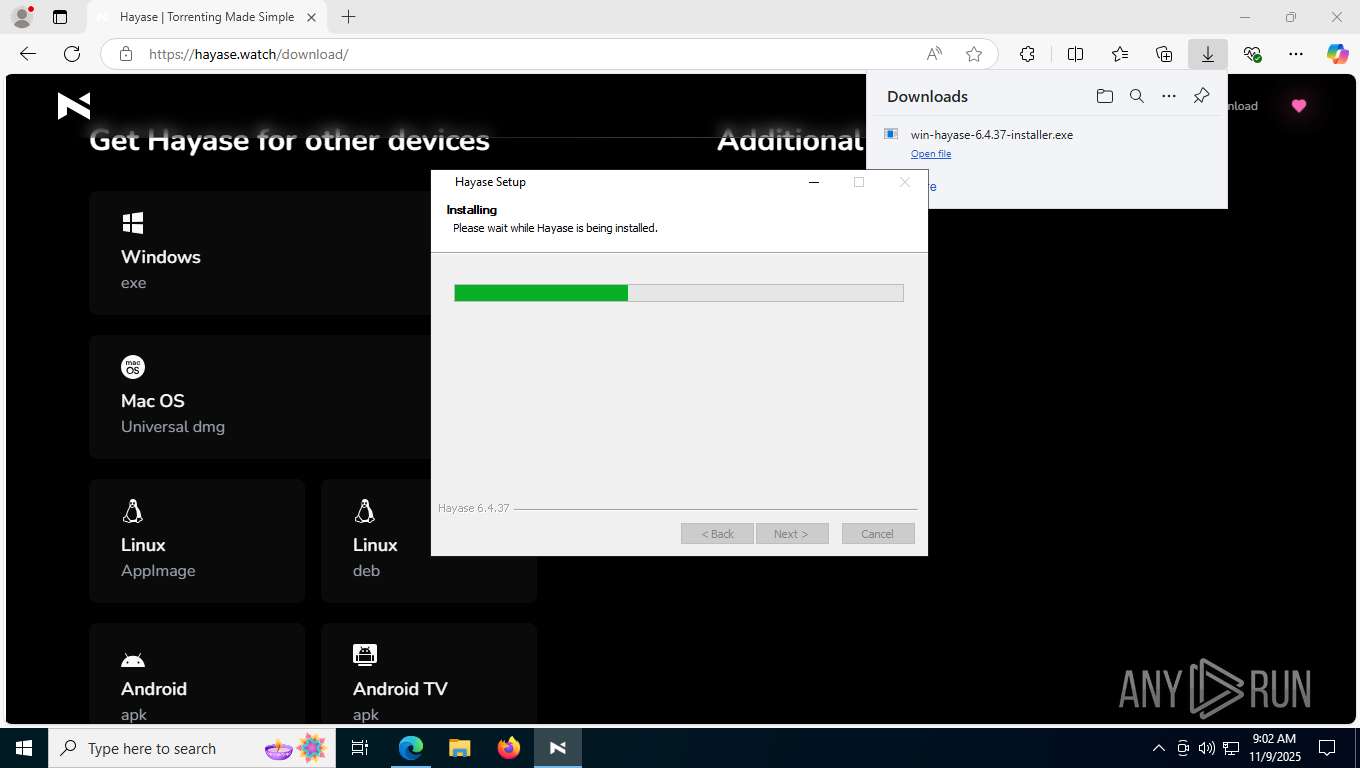
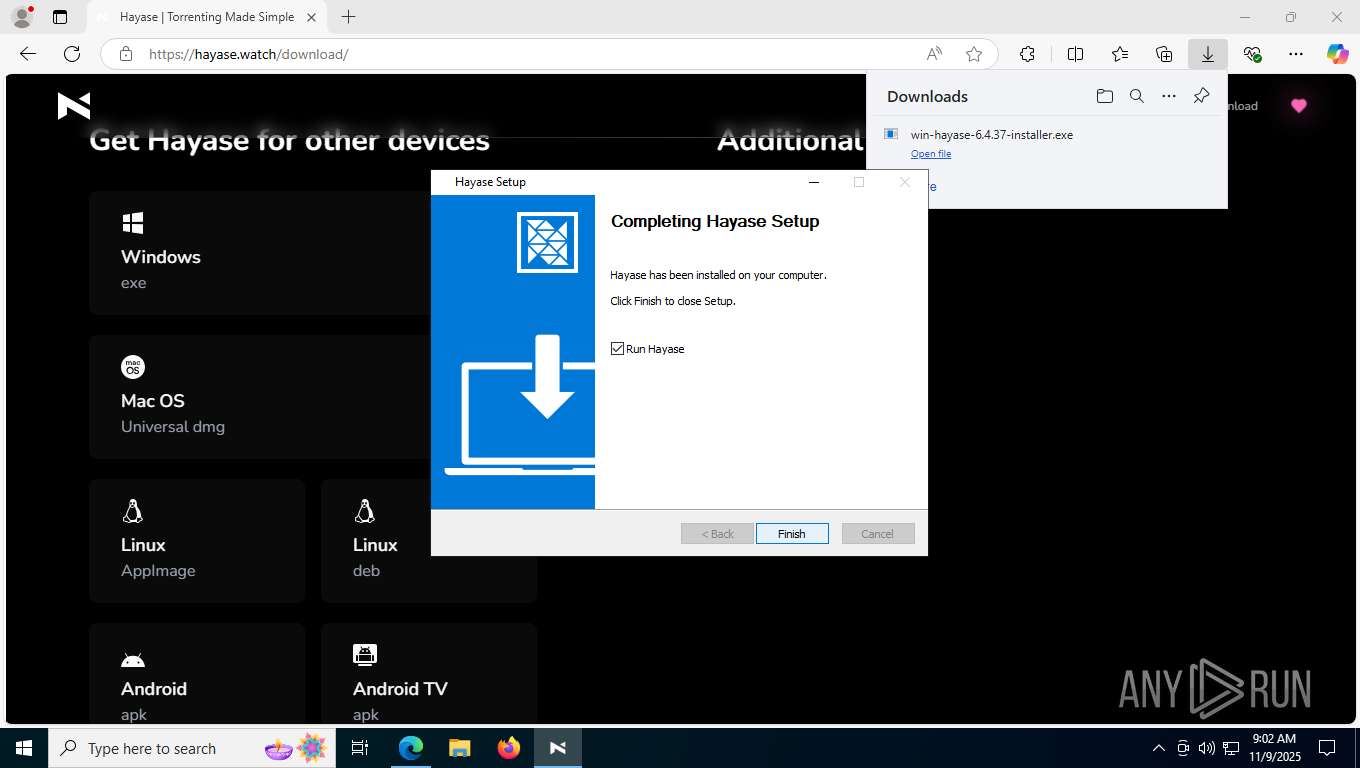
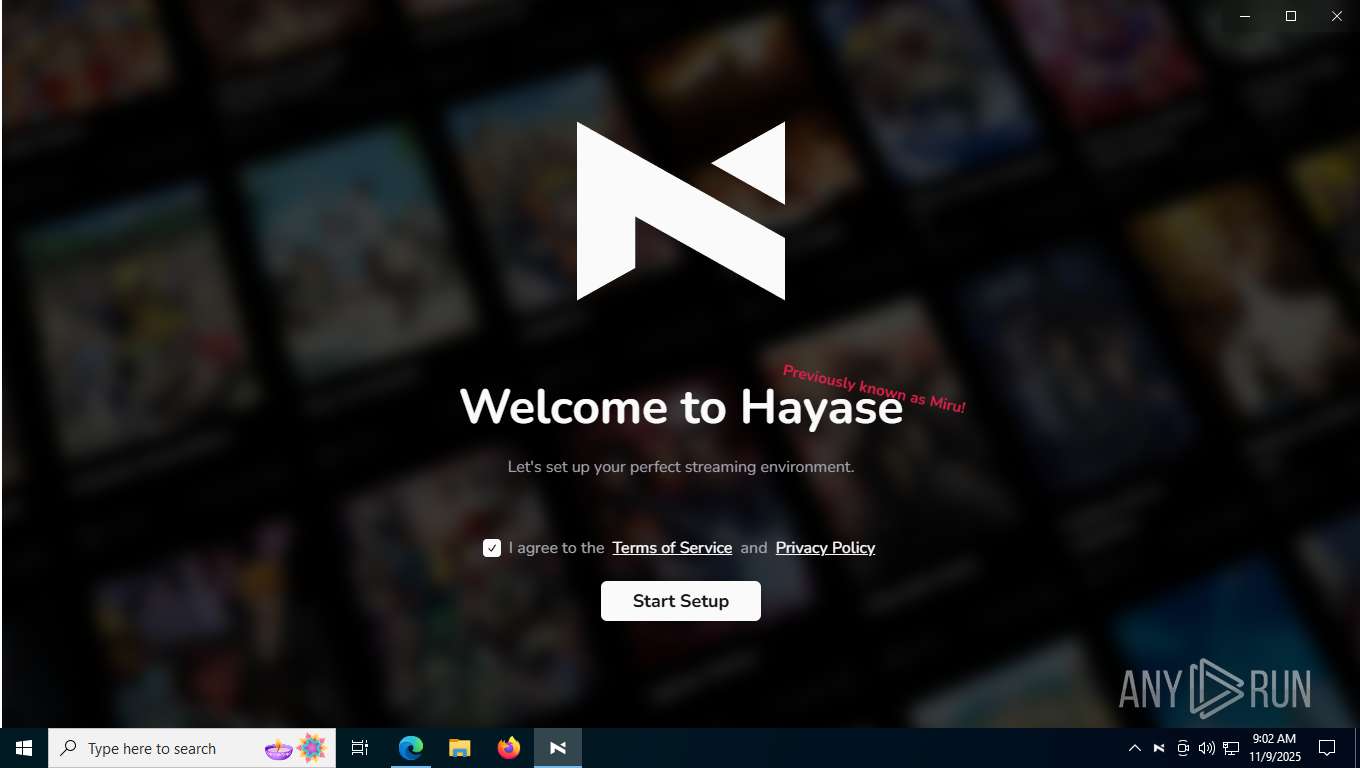
| URL: | https://hayase.watch/ |
| Full analysis: | https://app.any.run/tasks/a39df03c-d327-423f-9dca-d81a918a75e7 |
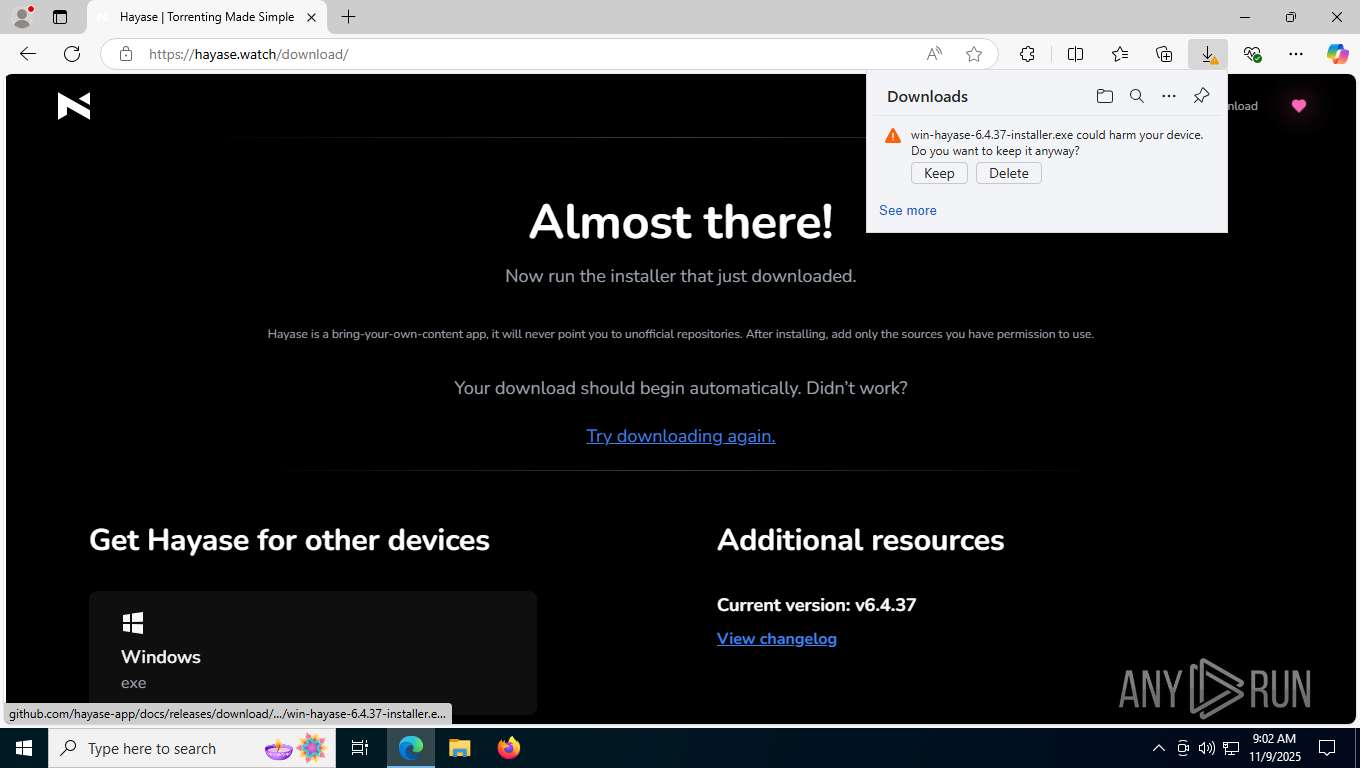
| Verdict: | Malicious activity |
| Analysis date: | November 09, 2025, 09:02:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D54AA83125AF60BCC4B99570BA0760D1 |
| SHA1: | 66417321CD2212AC0366E333F32D2DAE29530A0F |
| SHA256: | 5FC20CD7C1BA9AE3A33C49CBAA6244DB1780EDD9E8310EC0365AA0CDEA379E6F |
| SSDEEP: | 3:N841Wu3RB:241rn |
MALICIOUS
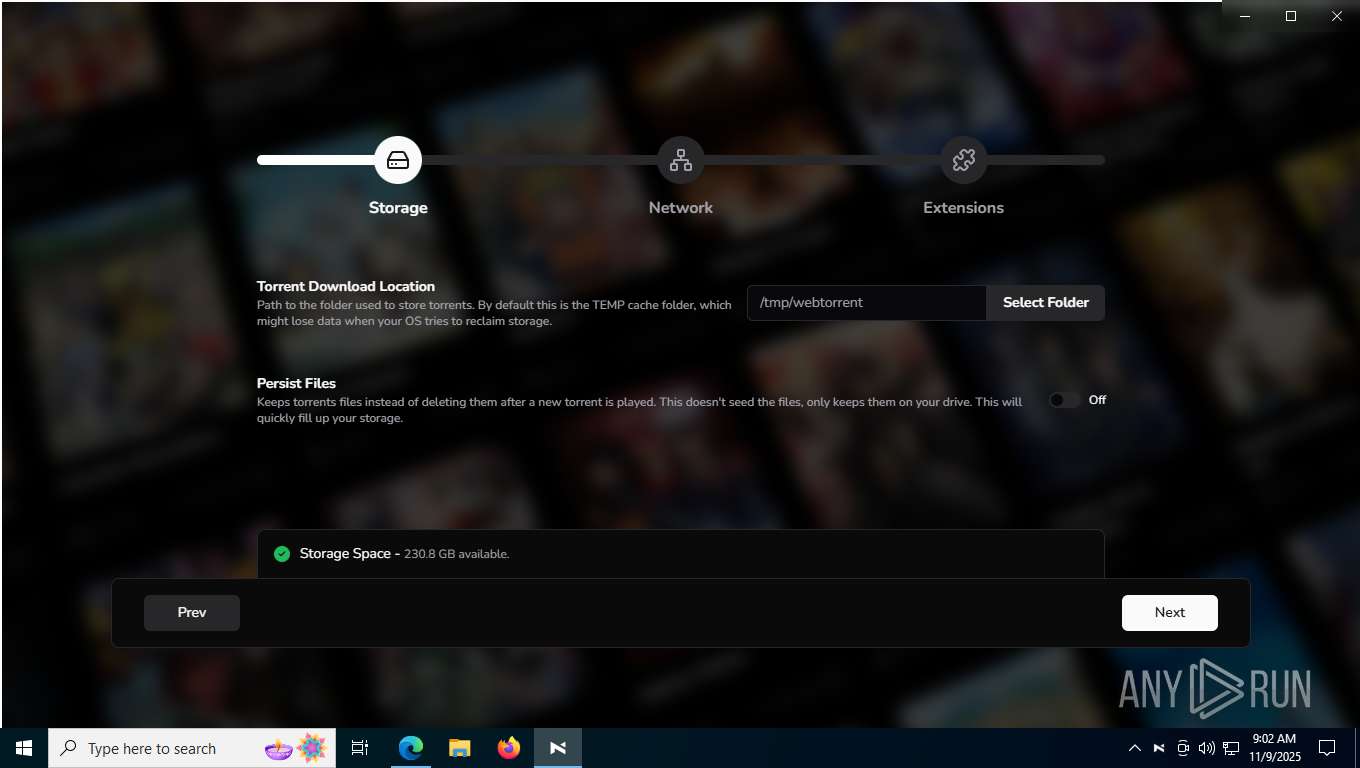
BITTORRENT has been detected (SURICATA)
- Hayase.exe (PID: 7144)
SUSPICIOUS
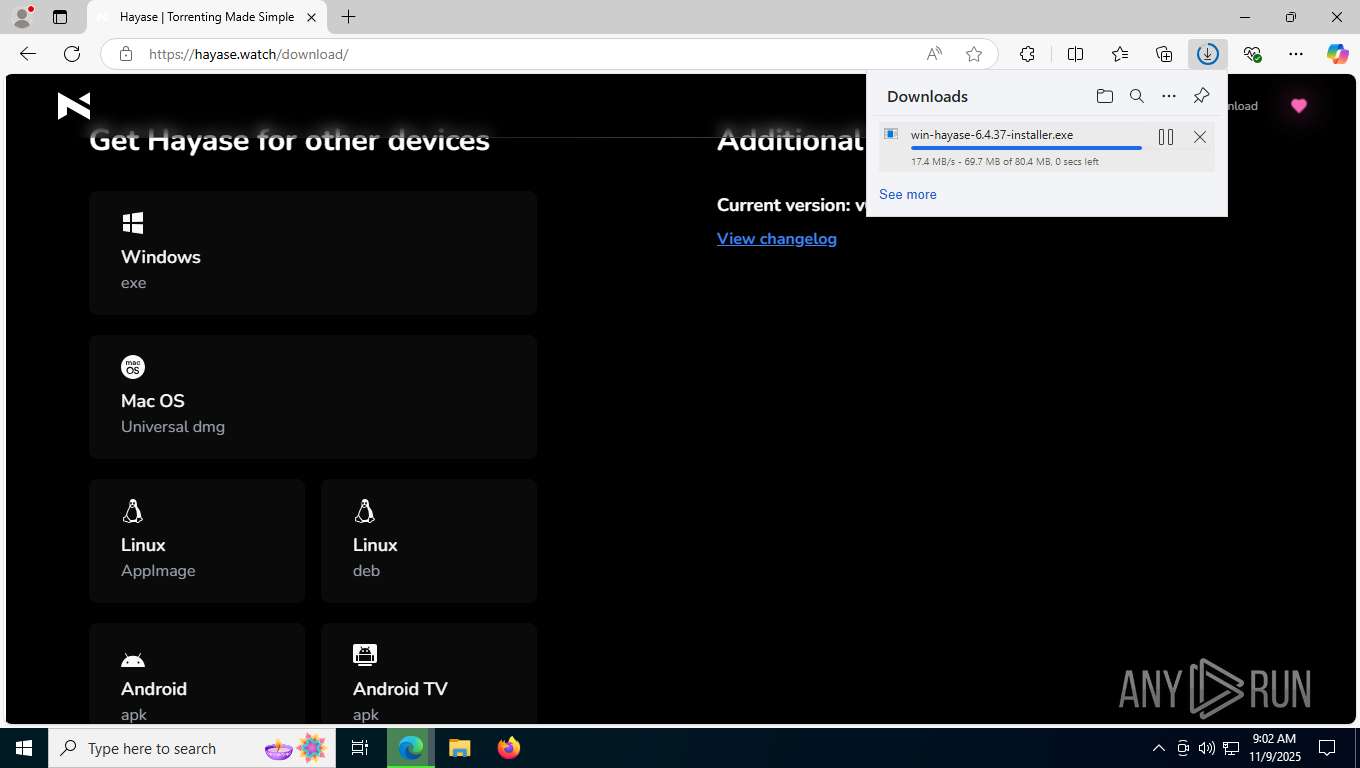
The process creates files with name similar to system file names
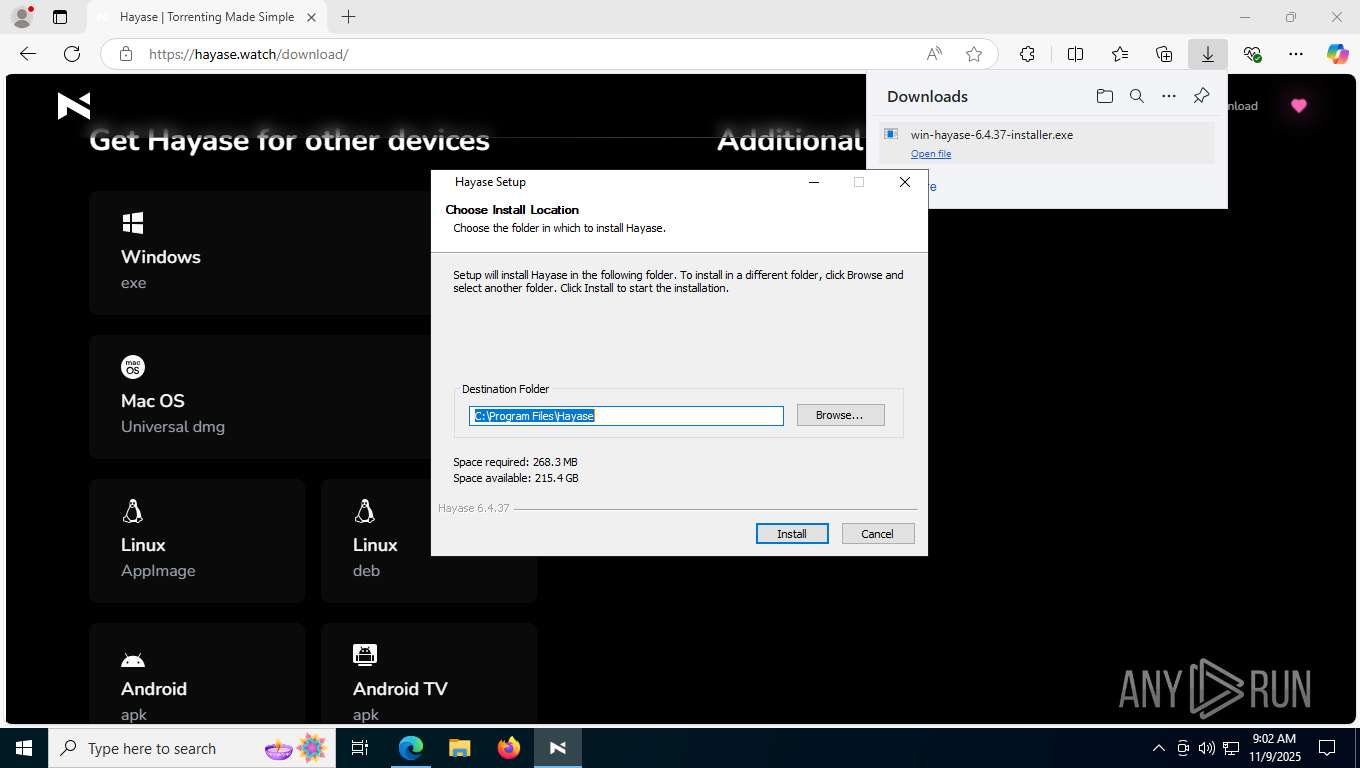
- win-hayase-6.4.37-installer.exe (PID: 8896)
- win-hayase-6.4.37-installer.exe (PID: 8936)
Executable content was dropped or overwritten
- win-hayase-6.4.37-installer.exe (PID: 8896)
- win-hayase-6.4.37-installer.exe (PID: 8936)
Malware-specific behavior (creating "System.dll" in Temp)
- win-hayase-6.4.37-installer.exe (PID: 8896)
- win-hayase-6.4.37-installer.exe (PID: 8936)
Drops 7-zip archiver for unpacking
- win-hayase-6.4.37-installer.exe (PID: 8896)
Process drops legitimate windows executable
- win-hayase-6.4.37-installer.exe (PID: 8896)
Application launched itself
- Hayase.exe (PID: 8332)
Reads security settings of Internet Explorer
- win-hayase-6.4.37-installer.exe (PID: 8896)
- Hayase.exe (PID: 8332)
Potential Corporate Privacy Violation
- Hayase.exe (PID: 7144)
Uses WMIC.EXE to obtain network information
- Hayase.exe (PID: 7144)
Uses WMIC.EXE
- Hayase.exe (PID: 7144)
INFO
Application launched itself
- msedge.exe (PID: 7344)
Checks supported languages
- win-hayase-6.4.37-installer.exe (PID: 8896)
- identity_helper.exe (PID: 480)
- win-hayase-6.4.37-installer.exe (PID: 8936)
- Hayase.exe (PID: 4324)
- Hayase.exe (PID: 7144)
- Hayase.exe (PID: 8412)
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 8696)
Reads Environment values
- identity_helper.exe (PID: 480)
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 7144)
Reads the computer name
- identity_helper.exe (PID: 480)
- win-hayase-6.4.37-installer.exe (PID: 8896)
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 4324)
- Hayase.exe (PID: 8412)
- Hayase.exe (PID: 7144)
Executable content was dropped or overwritten
- msedge.exe (PID: 7344)
Create files in a temporary directory
- win-hayase-6.4.37-installer.exe (PID: 8896)
- win-hayase-6.4.37-installer.exe (PID: 8936)
- Hayase.exe (PID: 8332)
Creates files in the program directory
- win-hayase-6.4.37-installer.exe (PID: 8896)
The sample compiled with english language support
- win-hayase-6.4.37-installer.exe (PID: 8896)
Creates files or folders in the user directory
- win-hayase-6.4.37-installer.exe (PID: 8896)
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 8412)
Creates a software uninstall entry
- win-hayase-6.4.37-installer.exe (PID: 8896)
Manual execution by a user
- Hayase.exe (PID: 8332)
Process checks computer location settings
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 7144)
- Hayase.exe (PID: 8696)
Checks proxy server information
- Hayase.exe (PID: 8332)
Reads product name
- Hayase.exe (PID: 8332)
- Hayase.exe (PID: 7144)
Reads the machine GUID from the registry
- Hayase.exe (PID: 8332)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 8792)
- WMIC.exe (PID: 2308)
- WMIC.exe (PID: 1844)
- WMIC.exe (PID: 8824)
Drops encrypted JS script (Microsoft Script Encoder)
- Hayase.exe (PID: 7144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
47
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6368,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=6396 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5716,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=5792 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_xpay_wallet.mojom.EdgeXPayWalletService --lang=en-US --service-sandbox-type=utility --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5512,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=5520 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1844 | wmic path Win32_NetworkAdapterConfiguration where IPEnabled=true get DefaultIPGateway,GatewayCostMetric,IPConnectionMetric,Index /format:table | C:\Windows\System32\wbem\WMIC.exe | — | Hayase.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5584,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=5444 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2052 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2308 | wmic path Win32_NetworkAdapter where Index=10 get NetConnectionID,MACAddress /format:table | C:\Windows\System32\wbem\WMIC.exe | — | Hayase.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2768 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6368,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=6396 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2792 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=4260,i,6529727373814690588,4202711830997446090,262144 --variations-seed-version --mojo-platform-channel-handle=3920 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
6 124
Read events
6 093
Write events
13
Delete events
18
Modification events
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Hayase | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | ShortcutName |
Value: Hayase | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | DisplayName |
Value: Hayase | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Hayase\Uninstall Hayase.exe" /allusers | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Program Files\Hayase\Uninstall Hayase.exe" /allusers /S | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | DisplayVersion |
Value: 6.4.37 | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Hayase\Hayase.exe,0 | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | Publisher |
Value: ThaUnknown_ | |||
| (PID) Process: | (8896) win-hayase-6.4.37-installer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\dfa2ed72-71bd-56ef-a676-b435325e7bc6 |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
Executable files
41
Suspicious files
619
Text files
87
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF161ed7.TMP | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF161ee7.TMP | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF161ef6.TMP | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF161ef6.TMP | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF161ef6.TMP | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
289
DNS requests
93
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7688 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:nAyXV-b7vqZNMr-tIgh1KhXO9zuIvl7AhdjqmRoV5r0&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
2800 | svchost.exe | GET | 200 | 95.101.35.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6776 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2716 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | NL | binary | 813 b | whitelisted |
2716 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | NL | binary | 401 b | whitelisted |
2716 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2800 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6048 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.204.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
7688 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7688 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7688 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7688 | msedge.exe | 104.21.85.40:443 | hayase.watch | CLOUDFLARENET | — | unknown |
7688 | msedge.exe | 2.16.204.153:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
hayase.watch |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.youtube-nocookie.com |
| whitelisted |
i.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
7144 | Hayase.exe | Misc activity | INFO [ANY.RUN] P2P BitTorrent Protocol |
7144 | Hayase.exe | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT nodes reply |
2276 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a .tk domain - Likely Hostile |
7144 | Hayase.exe | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
8412 | Hayase.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
8412 | Hayase.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |