| File name: | virus.cmd |
| Full analysis: | https://app.any.run/tasks/f9b3a698-3c52-4491-beb8-2cd308e01760 |
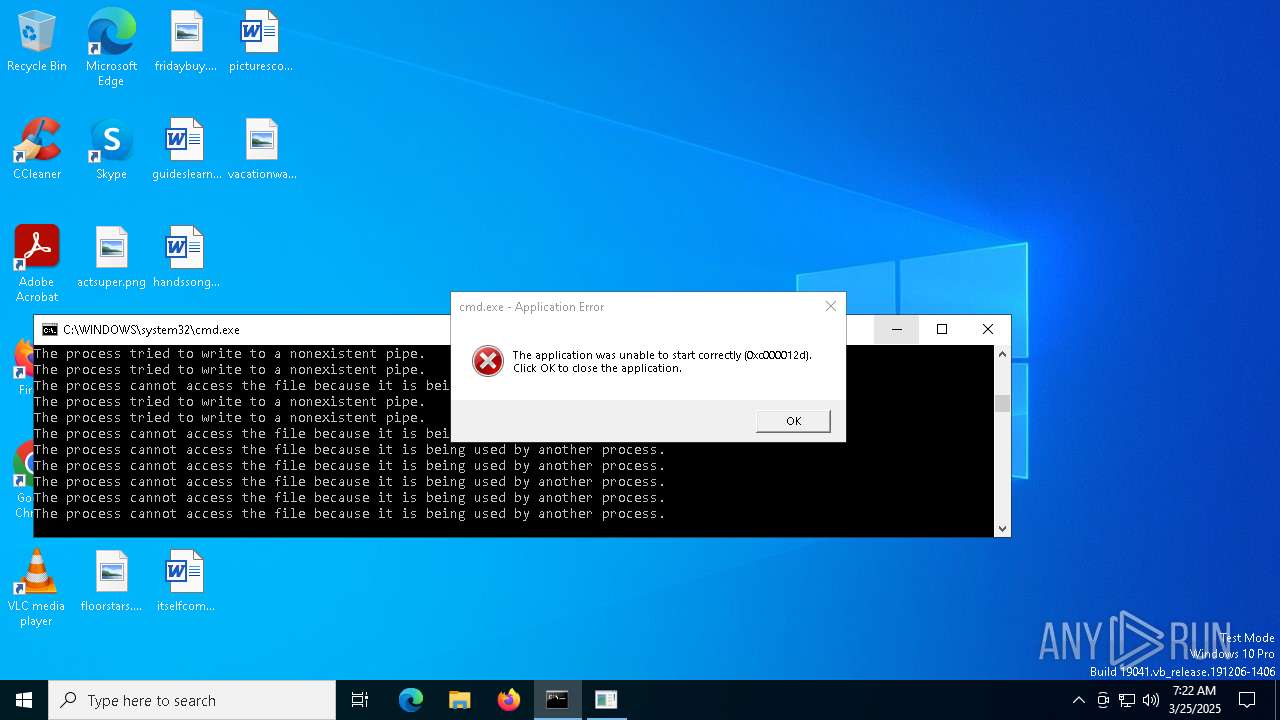
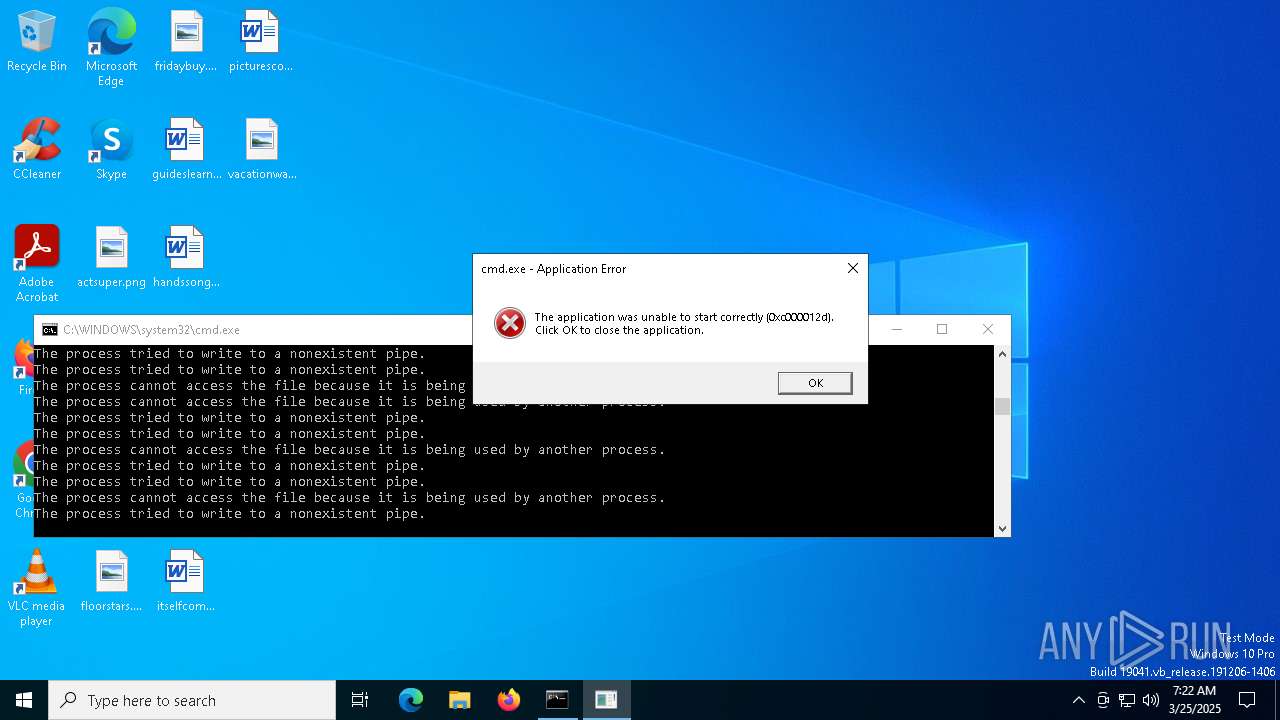
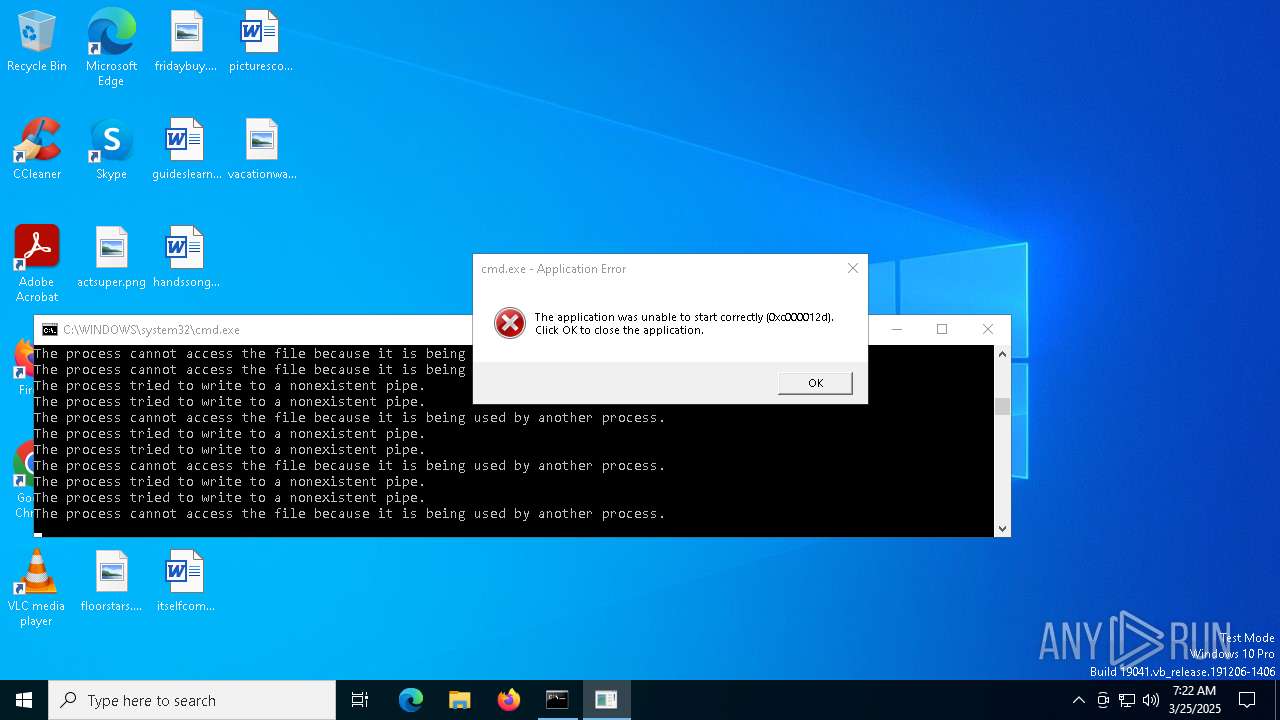
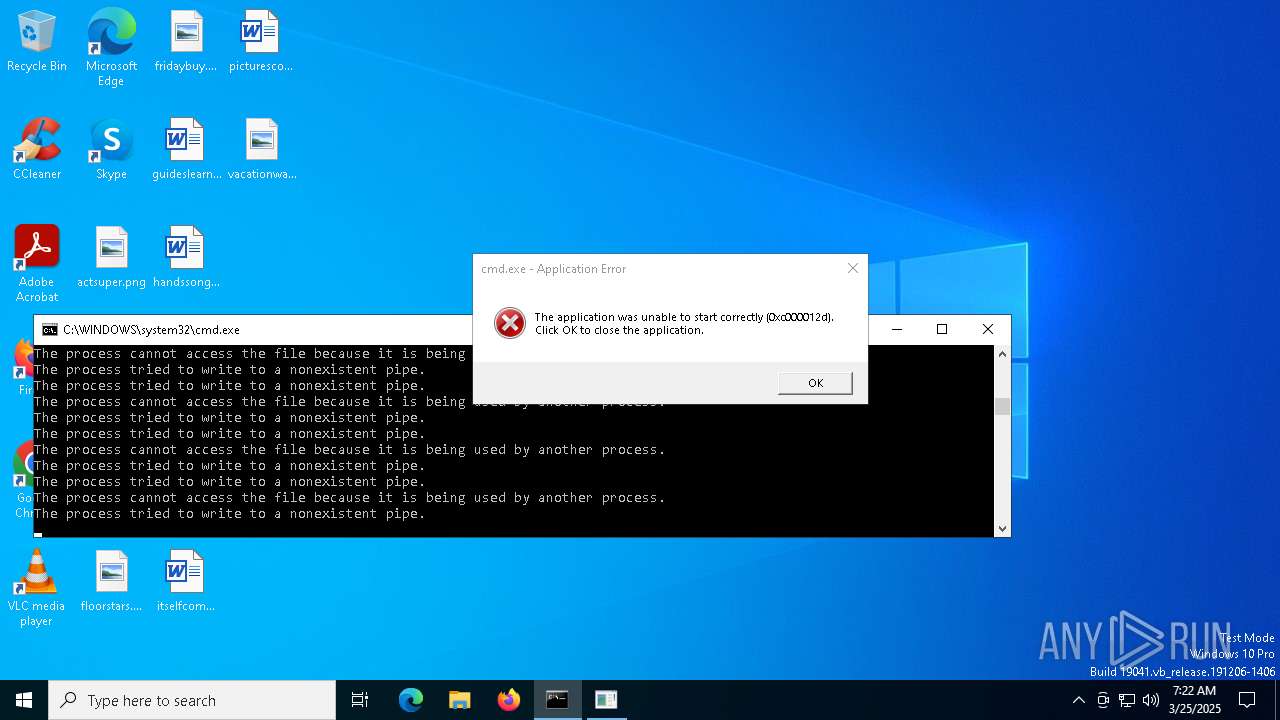
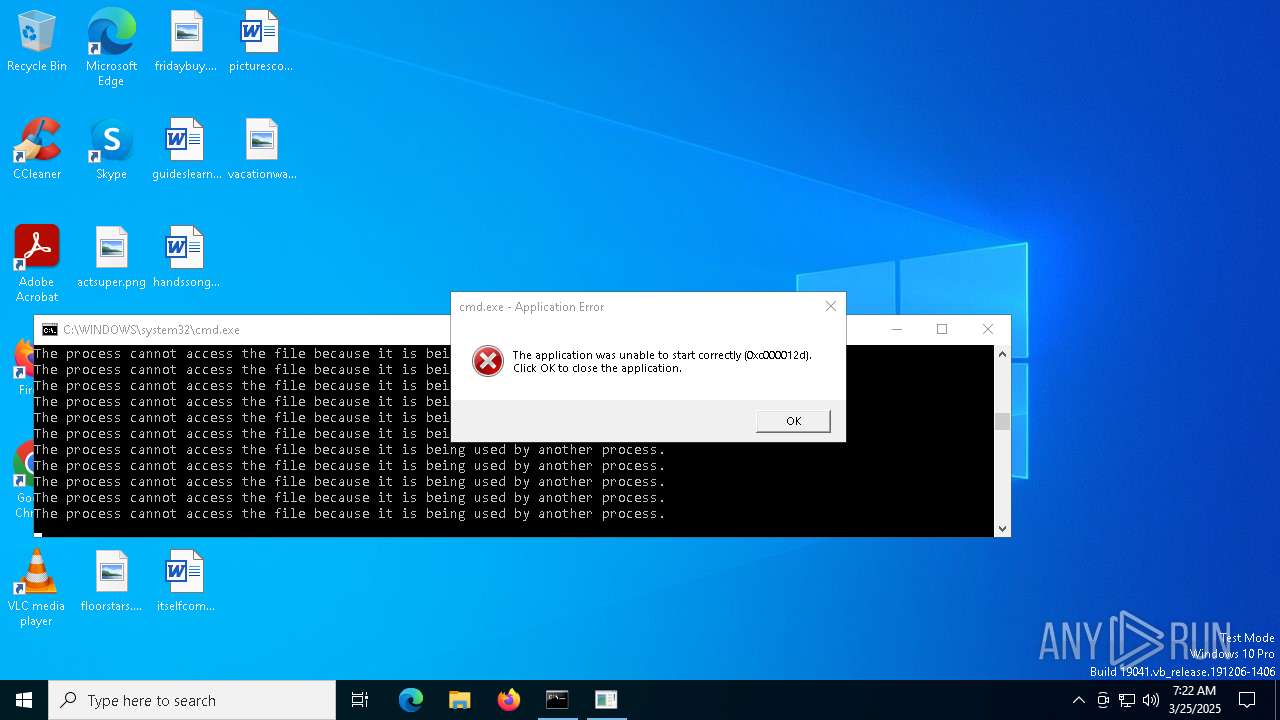
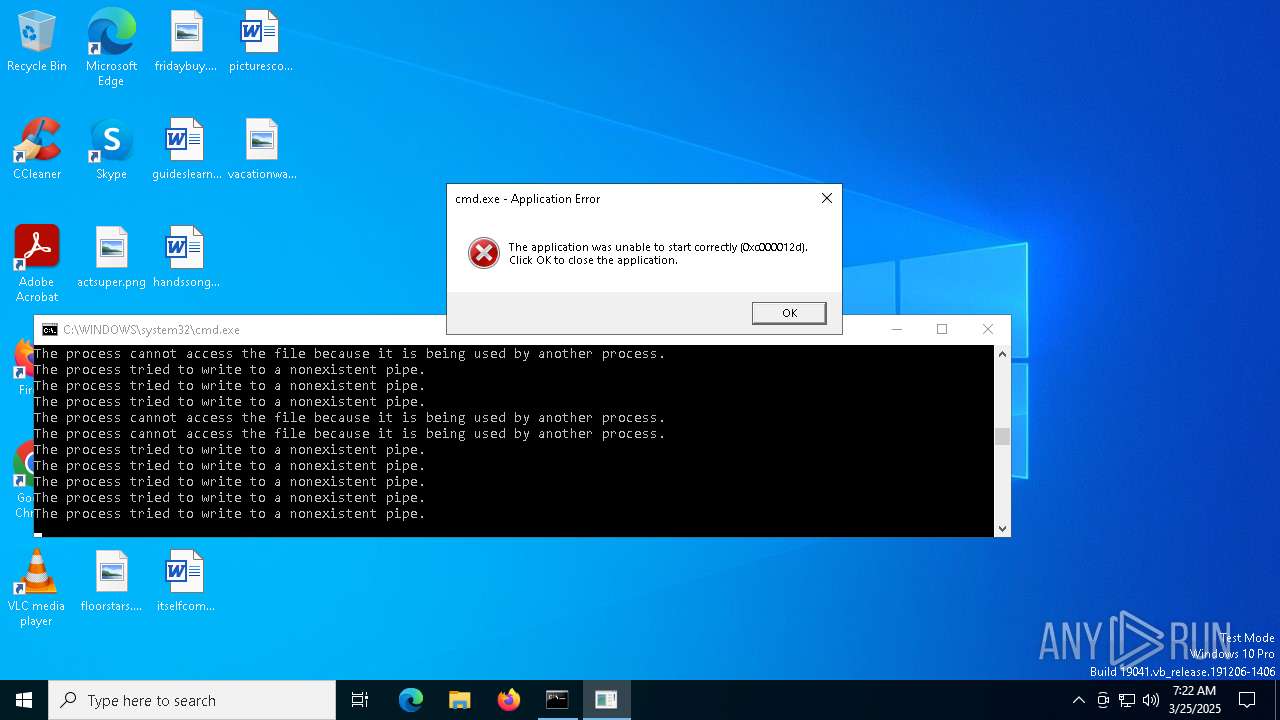
| Verdict: | Malicious activity |
| Analysis date: | March 25, 2025, 07:21:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | ECAF9F3A441016633B93999461D6A7A5 |
| SHA1: | 9B1DAA93512628917DC751FA8D295476CB01D1DC |
| SHA256: | 5F8F6472D06E271BC55707DAA3D39E4A5E68B927DBFB1427D250BA1993AC4302 |
| SSDEEP: | 3:oGNVRgBAf+v:oa4Af+v |
MALICIOUS
No malicious indicators.SUSPICIOUS
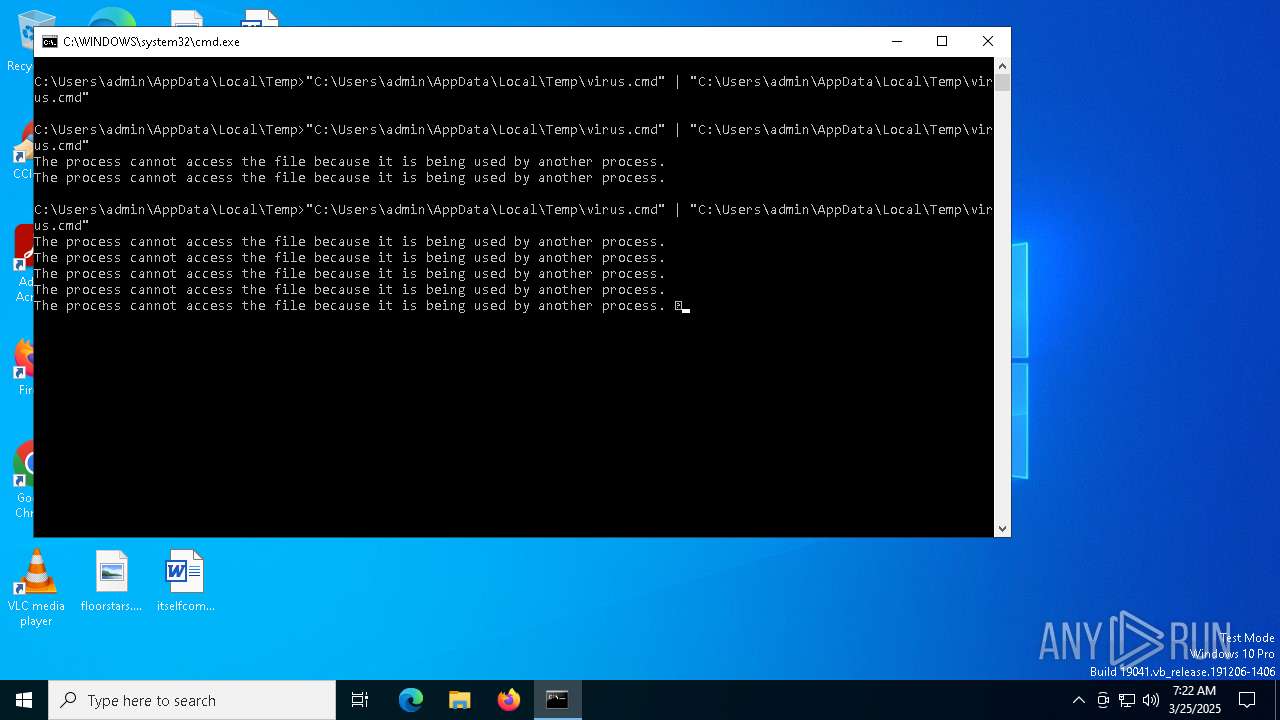
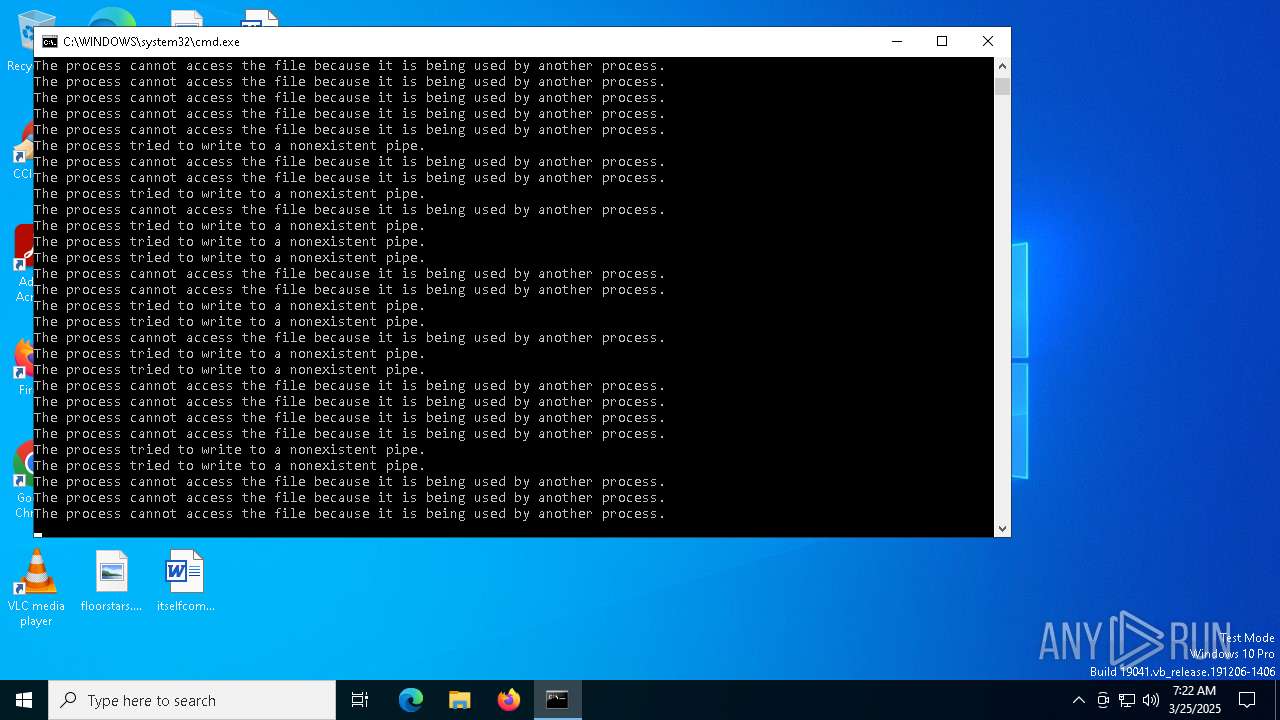
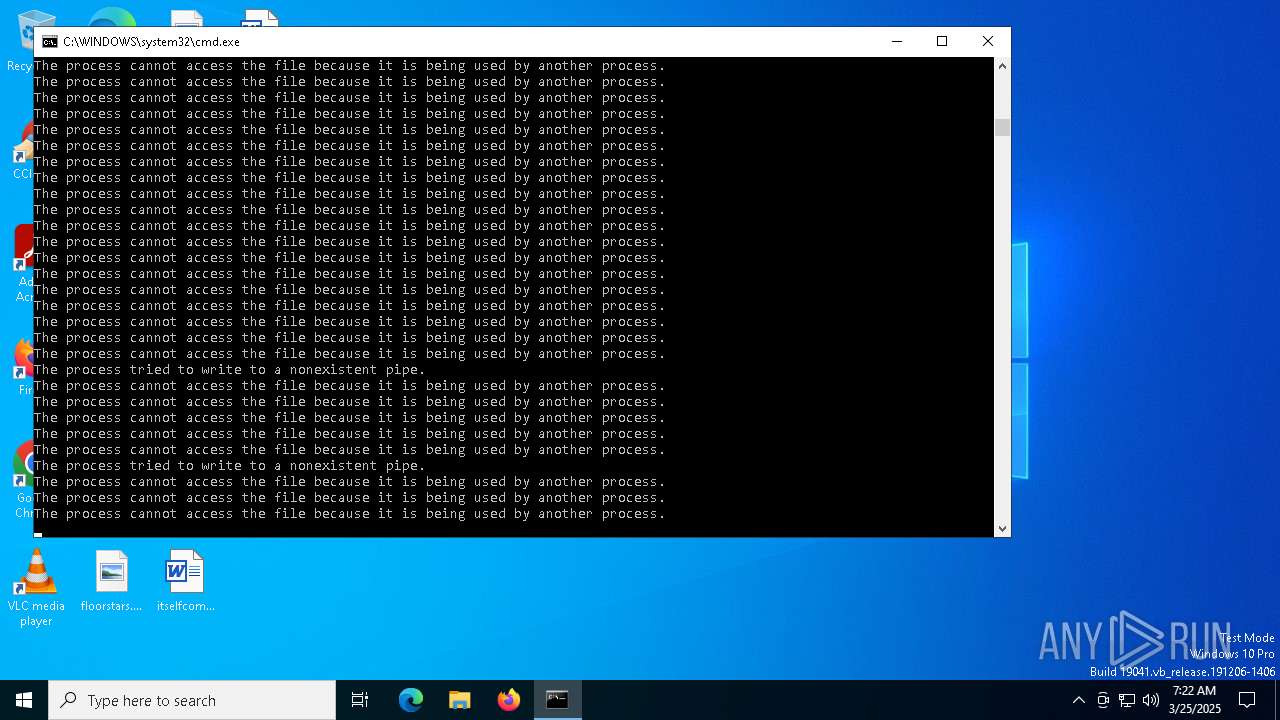
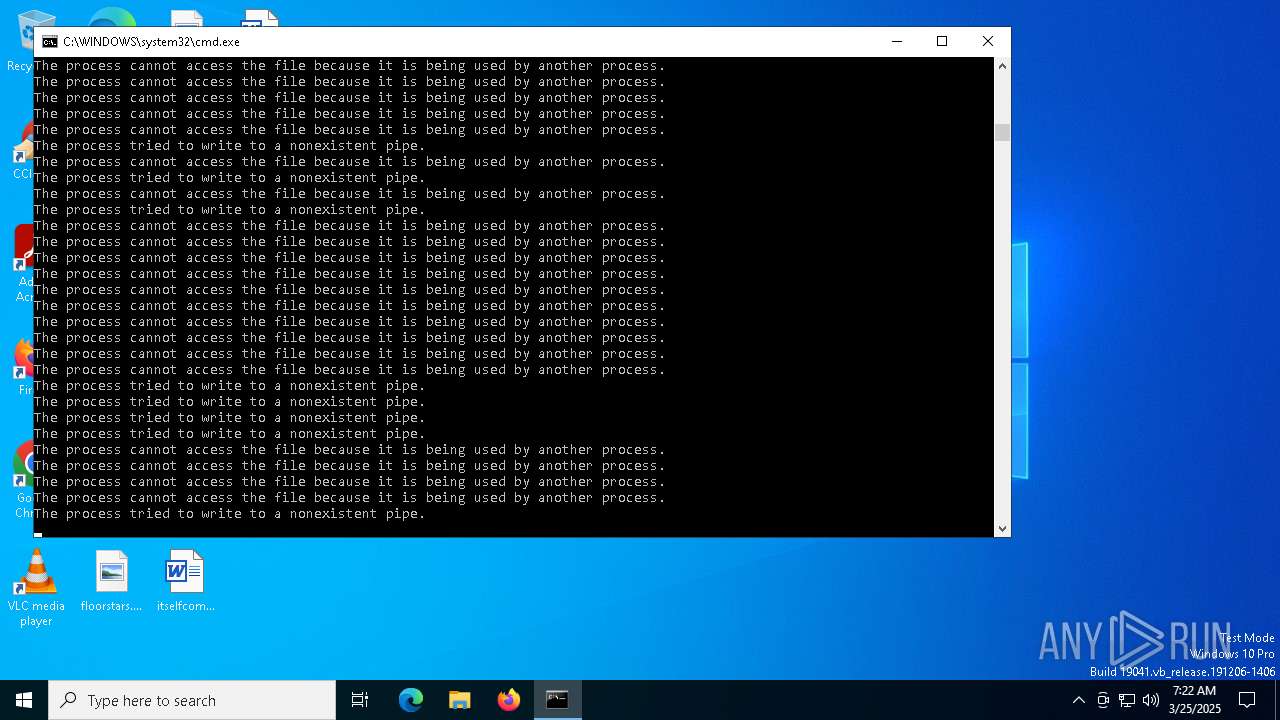
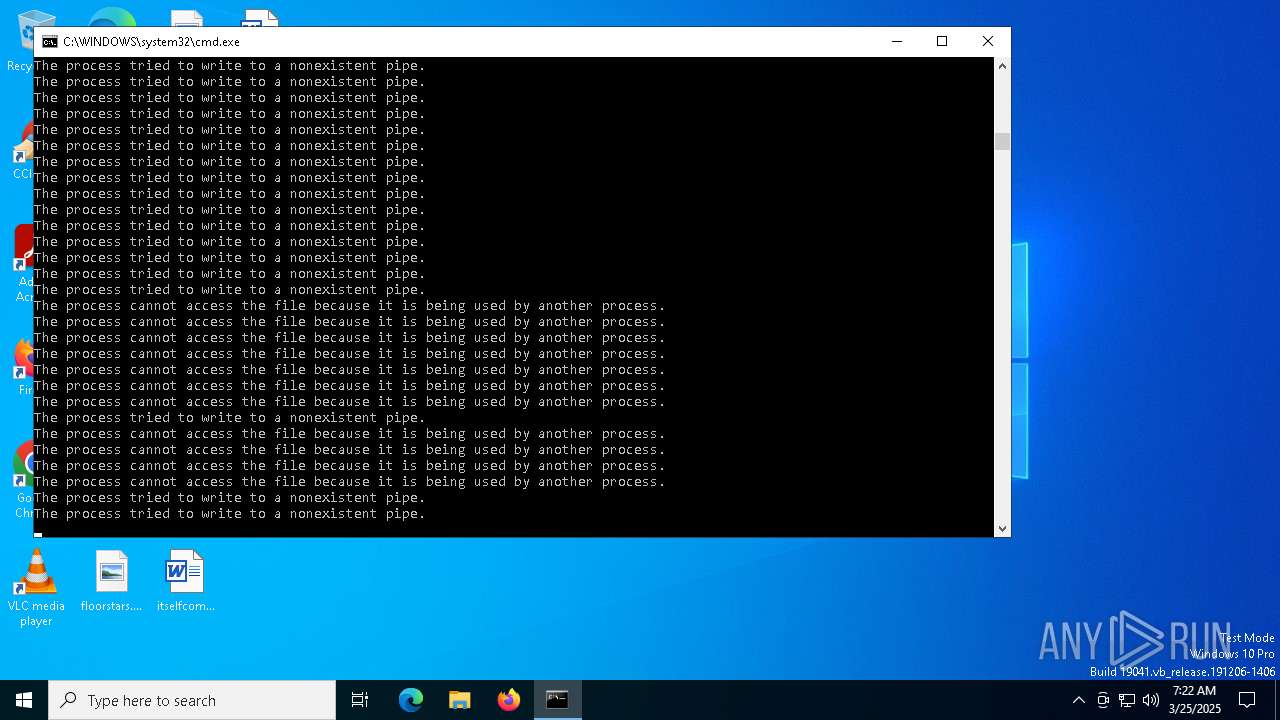
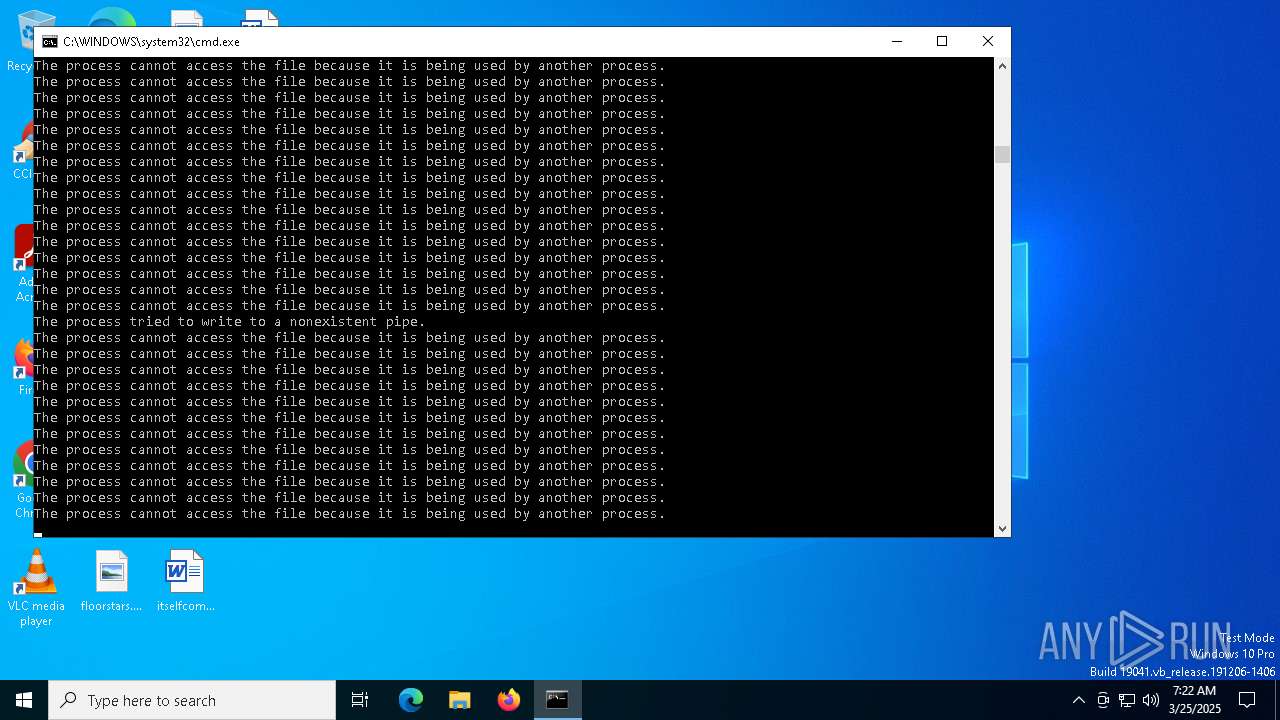
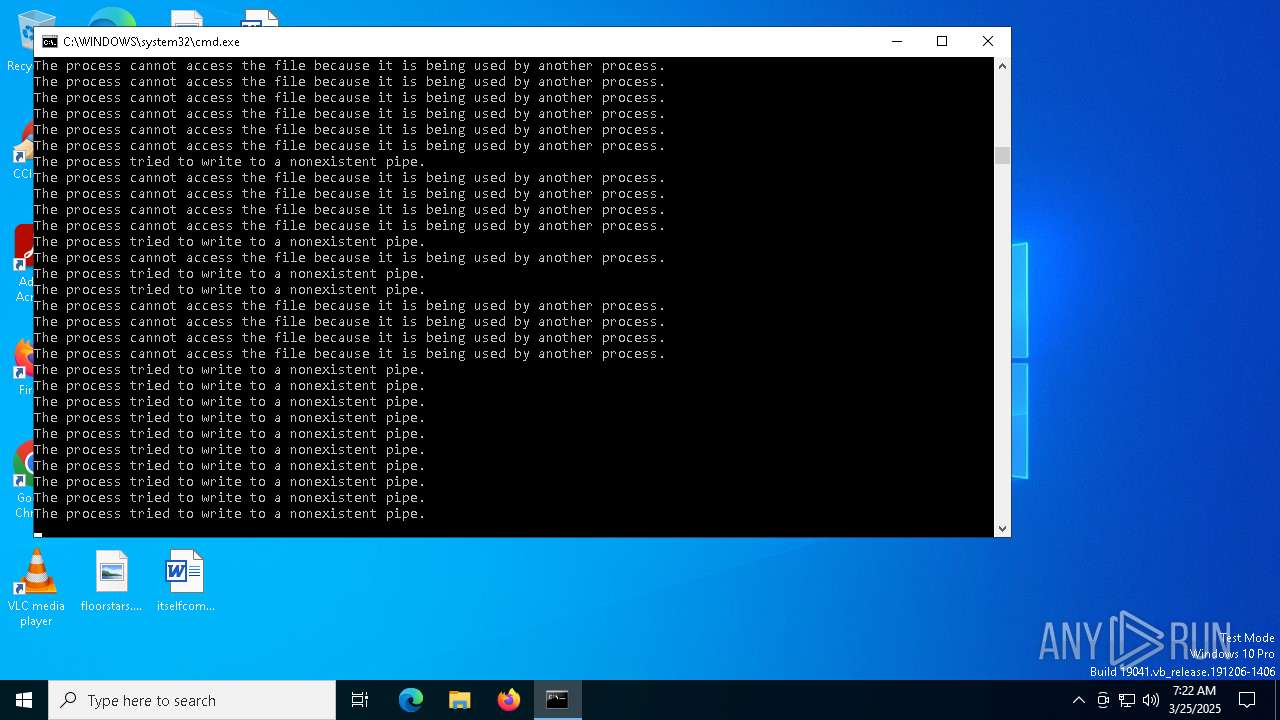
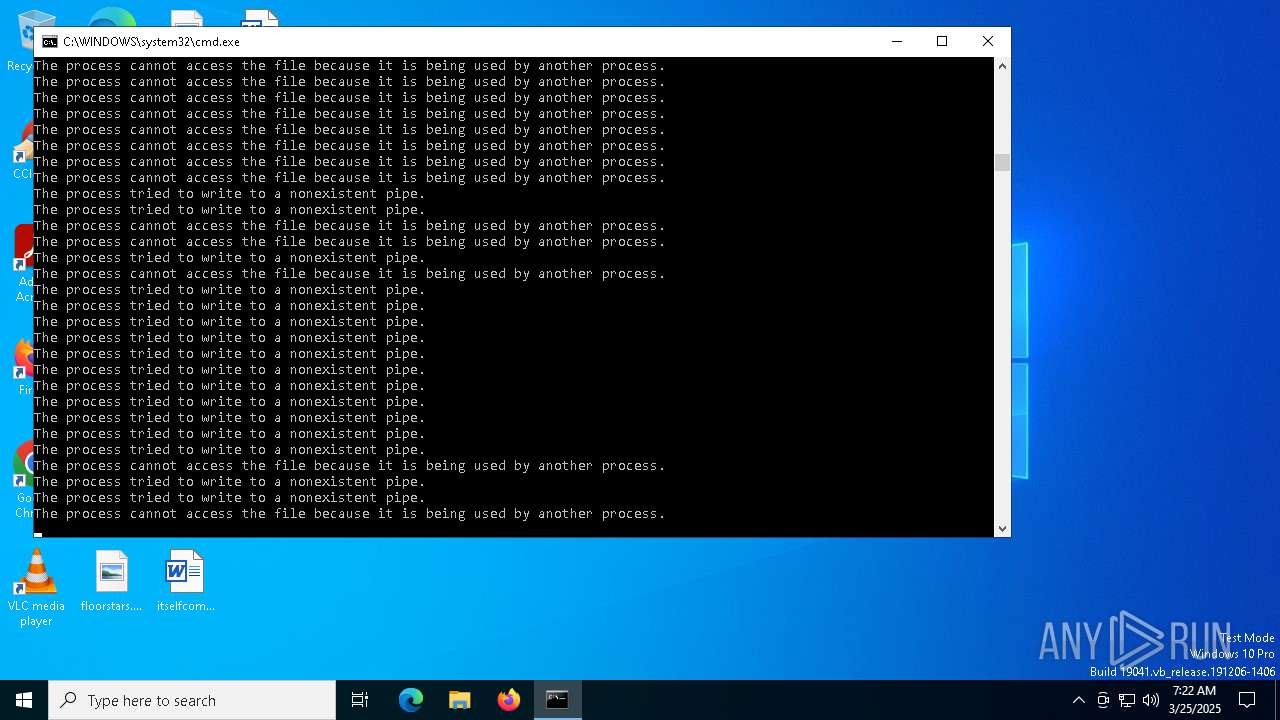
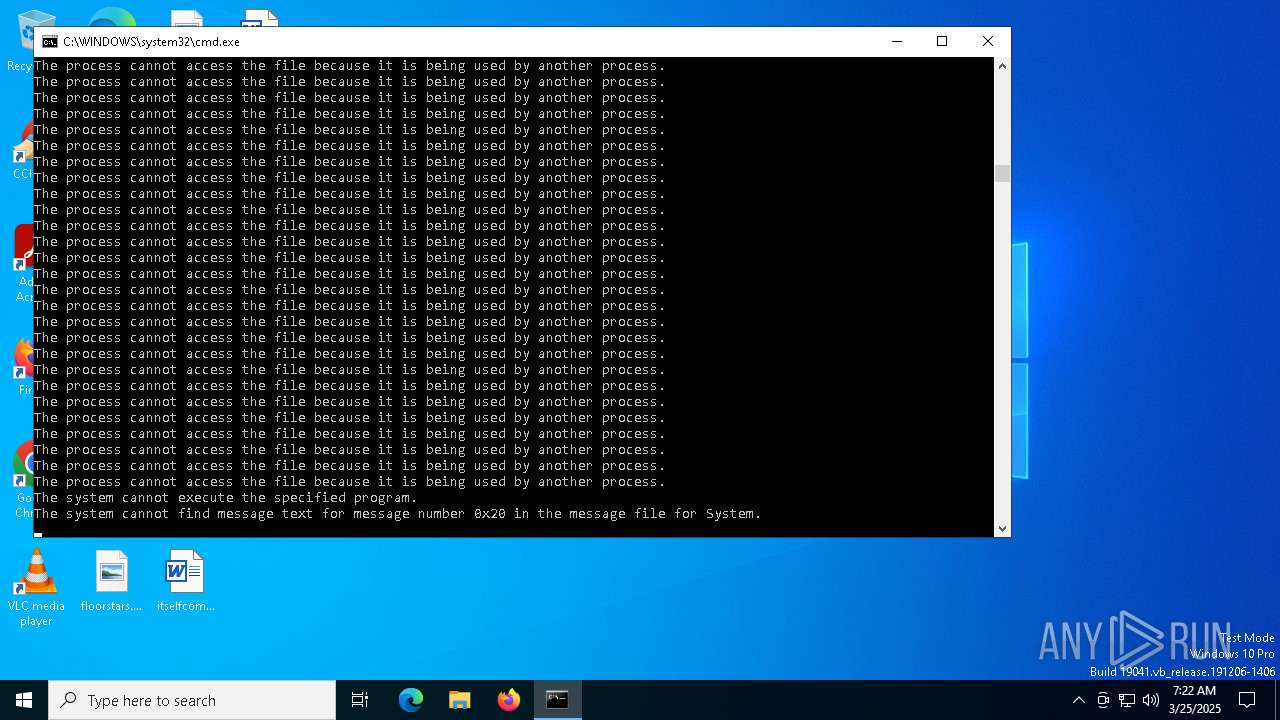
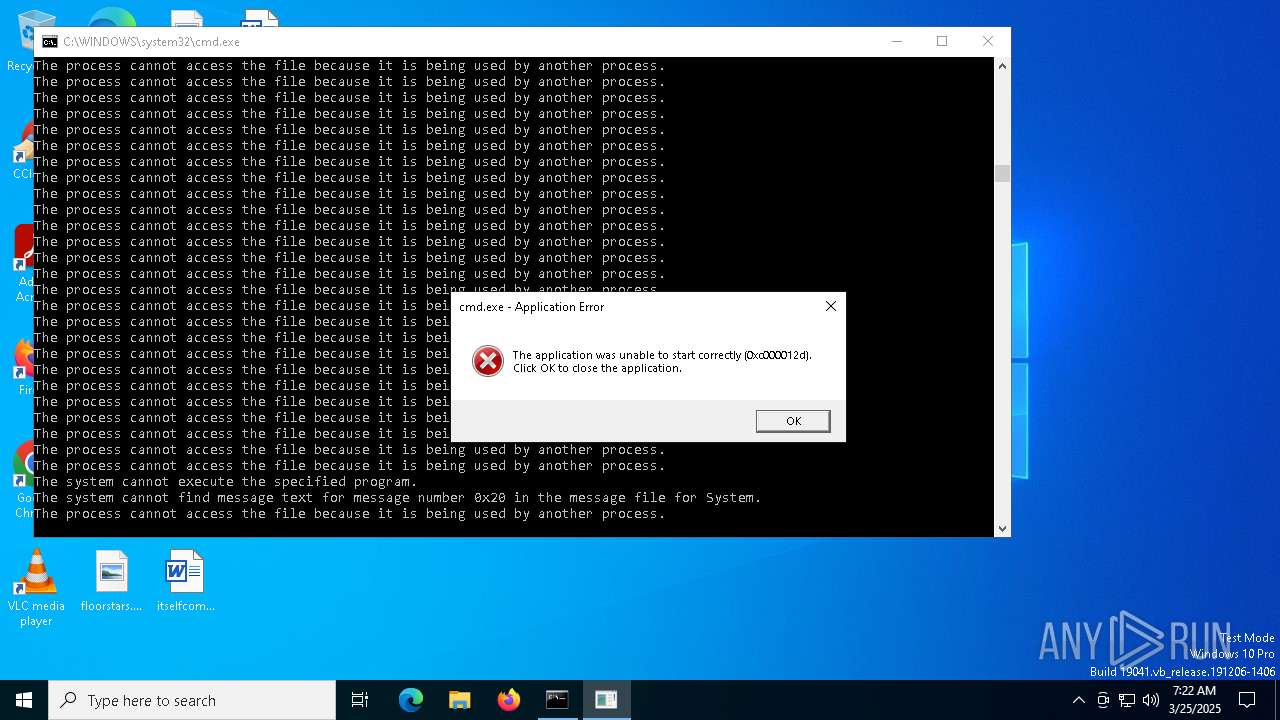
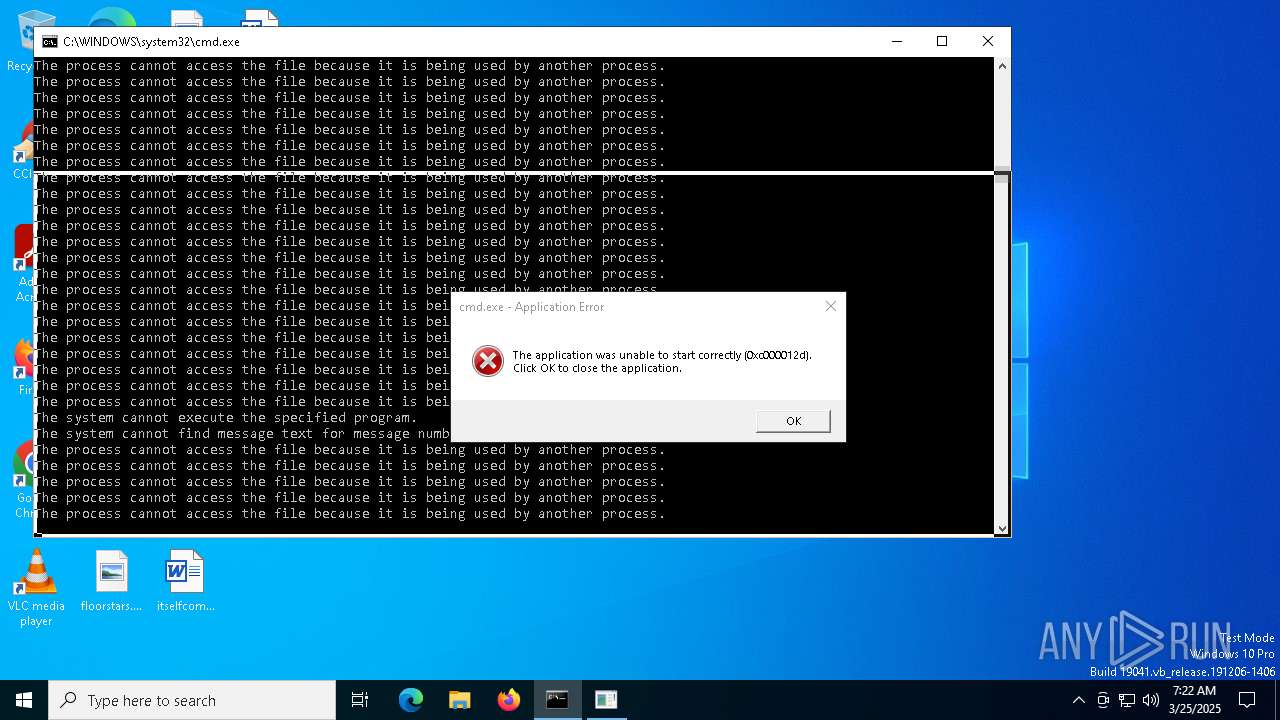
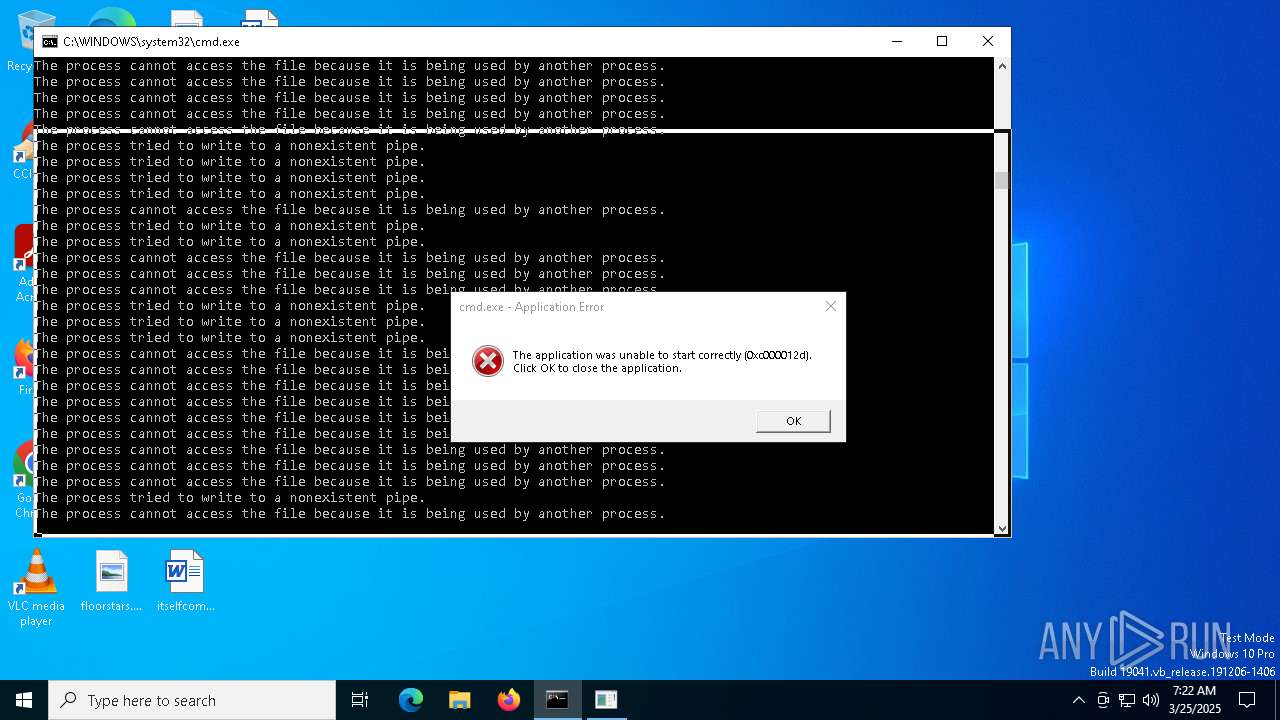
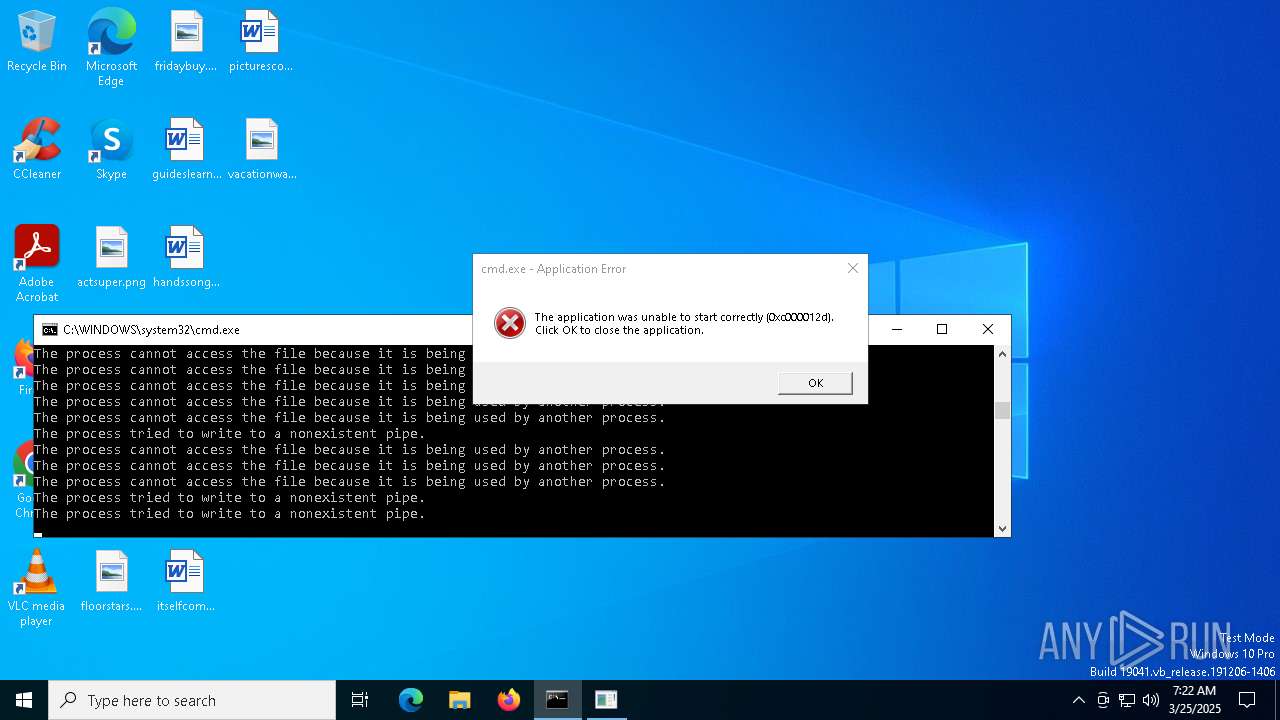
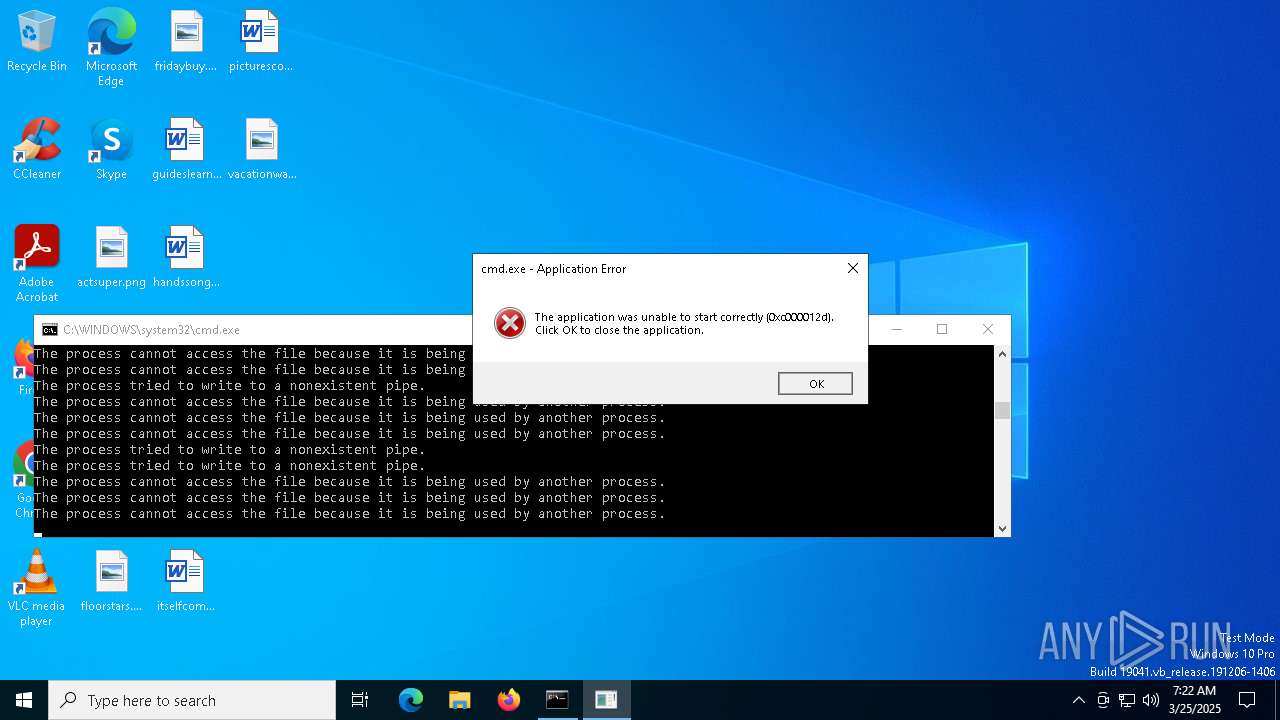
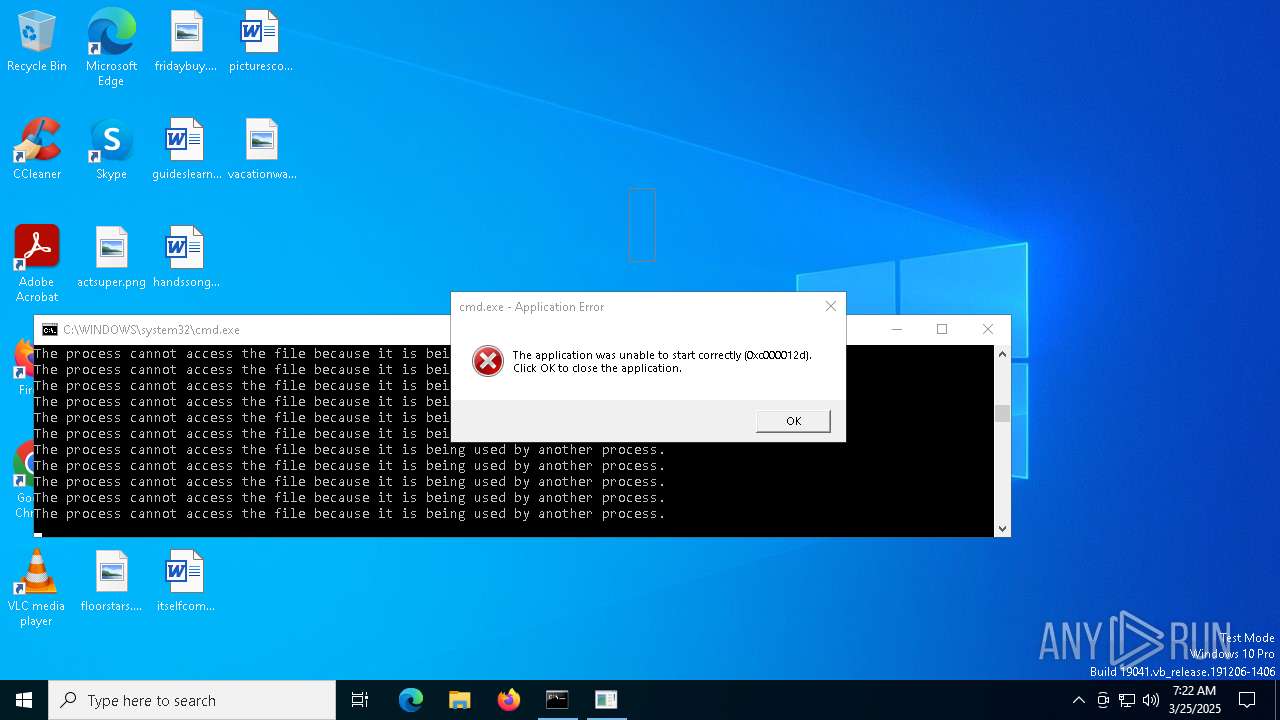
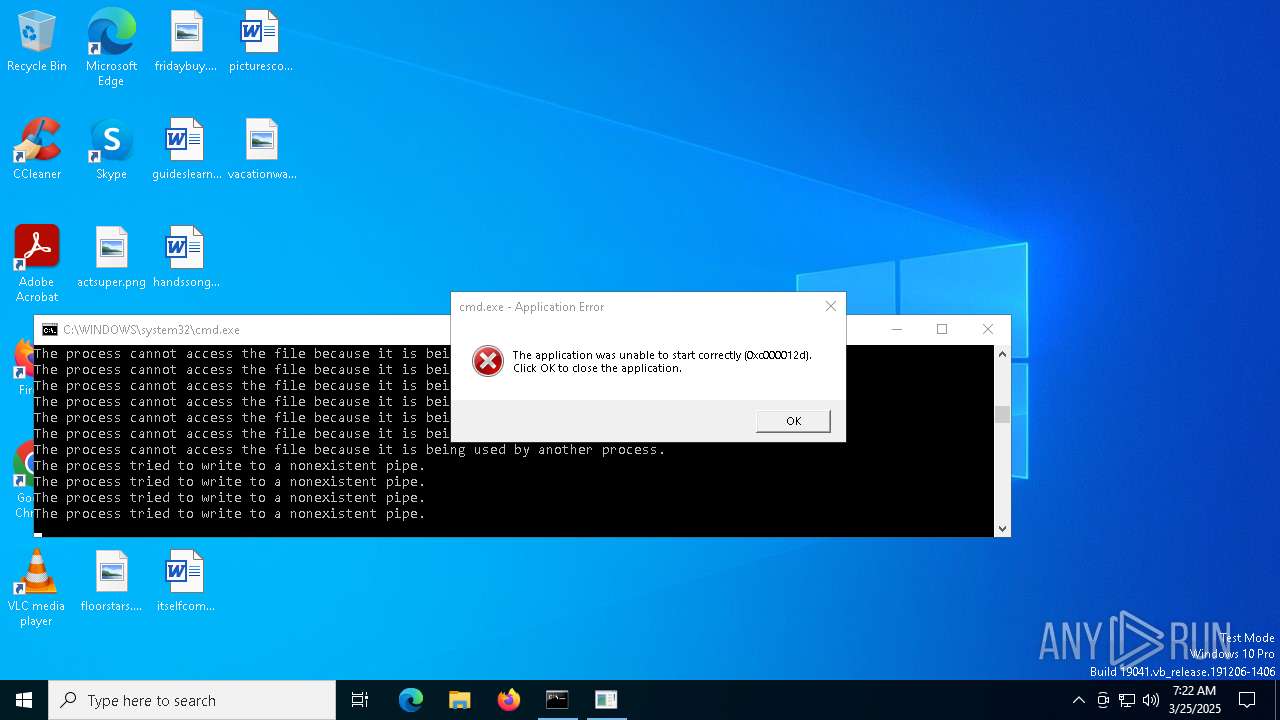
Executing commands from ".cmd" file
- cmd.exe (PID: 6620)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7808)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8412)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8316)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 8700)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8672)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8952)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 9428)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 9052)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 9176)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 9640)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 9996)
- cmd.exe (PID: 9272)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 9532)
- cmd.exe (PID: 9632)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 9376)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 9408)
- cmd.exe (PID: 8436)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 9932)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 9520)
- cmd.exe (PID: 9852)
- cmd.exe (PID: 9648)
- cmd.exe (PID: 9232)
- cmd.exe (PID: 10100)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 9400)
- cmd.exe (PID: 9756)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 9596)
- cmd.exe (PID: 9768)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 10244)
- cmd.exe (PID: 9616)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 9680)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 8480)
- cmd.exe (PID: 10284)
- cmd.exe (PID: 10660)
- cmd.exe (PID: 10492)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 10652)
- cmd.exe (PID: 10600)
- cmd.exe (PID: 9116)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 11320)
- cmd.exe (PID: 11860)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 10260)
- cmd.exe (PID: 10644)
- cmd.exe (PID: 11108)
- cmd.exe (PID: 10276)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 10740)
- cmd.exe (PID: 11512)
- cmd.exe (PID: 10720)
- cmd.exe (PID: 12352)
- cmd.exe (PID: 10924)
- cmd.exe (PID: 11548)
- cmd.exe (PID: 9816)
- cmd.exe (PID: 11768)
- cmd.exe (PID: 11532)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 11400)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 13504)
- cmd.exe (PID: 10536)
- cmd.exe (PID: 9624)
- cmd.exe (PID: 11504)
- cmd.exe (PID: 12992)
- cmd.exe (PID: 13196)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 13640)
- cmd.exe (PID: 10016)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 13540)
- cmd.exe (PID: 12968)
- cmd.exe (PID: 13088)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 13520)
- cmd.exe (PID: 12752)
- cmd.exe (PID: 12784)
- cmd.exe (PID: 14476)
- cmd.exe (PID: 11592)
- cmd.exe (PID: 14760)
- cmd.exe (PID: 15184)
- cmd.exe (PID: 10748)
- cmd.exe (PID: 12928)
- cmd.exe (PID: 13160)
- cmd.exe (PID: 11284)
- cmd.exe (PID: 12304)
- cmd.exe (PID: 15032)
- cmd.exe (PID: 15476)
- cmd.exe (PID: 13860)
- cmd.exe (PID: 15240)
- cmd.exe (PID: 14996)
- cmd.exe (PID: 15396)
- cmd.exe (PID: 15228)
- cmd.exe (PID: 12532)
- cmd.exe (PID: 13000)
- cmd.exe (PID: 12368)
- cmd.exe (PID: 12240)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 12524)
- cmd.exe (PID: 13260)
- cmd.exe (PID: 12844)
- cmd.exe (PID: 11872)
- cmd.exe (PID: 10828)
- cmd.exe (PID: 9808)
- cmd.exe (PID: 16516)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 16156)
- cmd.exe (PID: 14416)
- cmd.exe (PID: 12908)
- cmd.exe (PID: 13632)
- cmd.exe (PID: 17380)
- cmd.exe (PID: 12764)
- cmd.exe (PID: 13572)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 13580)
- cmd.exe (PID: 18192)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 17016)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 14636)
- cmd.exe (PID: 14644)
- cmd.exe (PID: 15860)
- cmd.exe (PID: 12688)
- cmd.exe (PID: 14988)
- cmd.exe (PID: 14752)
- cmd.exe (PID: 12560)
- cmd.exe (PID: 13380)
- cmd.exe (PID: 13788)
- cmd.exe (PID: 15948)
- cmd.exe (PID: 17396)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 11352)
- cmd.exe (PID: 15924)
- cmd.exe (PID: 11644)
- cmd.exe (PID: 15932)
- cmd.exe (PID: 16472)
- cmd.exe (PID: 17612)
- cmd.exe (PID: 16604)
- cmd.exe (PID: 18620)
- cmd.exe (PID: 18172)
- cmd.exe (PID: 18284)
- cmd.exe (PID: 18160)
- cmd.exe (PID: 12824)
- cmd.exe (PID: 13180)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 17876)
- cmd.exe (PID: 18772)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 19012)
- cmd.exe (PID: 13732)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 15256)
- cmd.exe (PID: 14512)
- cmd.exe (PID: 15712)
- cmd.exe (PID: 18116)
- cmd.exe (PID: 18748)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 19508)
- cmd.exe (PID: 21152)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 20236)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 21028)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 22276)
- cmd.exe (PID: 21908)
- cmd.exe (PID: 22348)
- cmd.exe (PID: 17672)
- cmd.exe (PID: 20280)
- cmd.exe (PID: 22512)
- cmd.exe (PID: 24456)
- cmd.exe (PID: 18460)
- cmd.exe (PID: 12272)
- cmd.exe (PID: 22436)
- cmd.exe (PID: 24468)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 25568)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 19352)
- cmd.exe (PID: 25316)
- cmd.exe (PID: 13612)
- cmd.exe (PID: 25716)
- cmd.exe (PID: 28552)
- cmd.exe (PID: 25148)
- cmd.exe (PID: 25308)
- cmd.exe (PID: 27108)
- cmd.exe (PID: 24952)
- cmd.exe (PID: 24072)
- cmd.exe (PID: 15344)
- cmd.exe (PID: 25792)
- cmd.exe (PID: 26188)
- cmd.exe (PID: 28544)
- cmd.exe (PID: 29136)
- cmd.exe (PID: 26956)
- cmd.exe (PID: 26076)
- cmd.exe (PID: 29908)
- cmd.exe (PID: 19868)
- cmd.exe (PID: 19460)
- cmd.exe (PID: 33144)
- cmd.exe (PID: 20756)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 24772)
- cmd.exe (PID: 27704)
- cmd.exe (PID: 11628)
- cmd.exe (PID: 22252)
- cmd.exe (PID: 31404)
- cmd.exe (PID: 26728)
- cmd.exe (PID: 29828)
- cmd.exe (PID: 27532)
- cmd.exe (PID: 30732)
- cmd.exe (PID: 37320)
- cmd.exe (PID: 37792)
- cmd.exe (PID: 22732)
- cmd.exe (PID: 19800)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 22616)
- cmd.exe (PID: 21560)
- cmd.exe (PID: 16596)
- cmd.exe (PID: 19388)
- cmd.exe (PID: 21280)
- cmd.exe (PID: 20884)
- cmd.exe (PID: 22332)
- cmd.exe (PID: 20300)
- cmd.exe (PID: 39752)
- cmd.exe (PID: 24472)
- cmd.exe (PID: 36172)
- cmd.exe (PID: 21068)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 35960)
- cmd.exe (PID: 41024)
- cmd.exe (PID: 37760)
- cmd.exe (PID: 36484)
- cmd.exe (PID: 31156)
- cmd.exe (PID: 37632)
- cmd.exe (PID: 35992)
- cmd.exe (PID: 39920)
- cmd.exe (PID: 39760)
- cmd.exe (PID: 28772)
- cmd.exe (PID: 13876)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 10092)
- cmd.exe (PID: 42104)
- cmd.exe (PID: 24512)
- cmd.exe (PID: 20636)
- cmd.exe (PID: 30300)
- cmd.exe (PID: 27904)
- cmd.exe (PID: 24040)
- cmd.exe (PID: 10732)
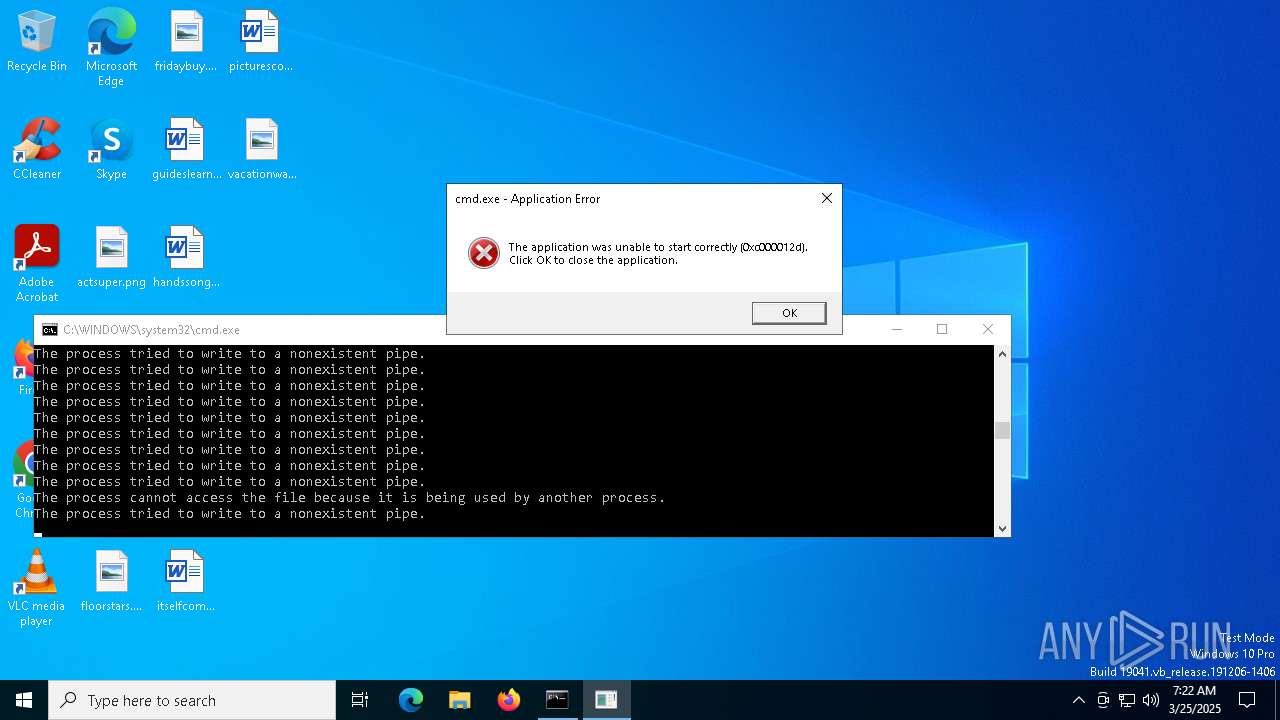
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6620)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 864)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 5956)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7808)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8412)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8700)
- cmd.exe (PID: 8316)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 8952)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8672)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 9052)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 9428)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 9176)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 9640)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 9996)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 9272)
- cmd.exe (PID: 9376)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 9532)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 9408)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 8436)
- cmd.exe (PID: 9632)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 9932)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 9520)
- cmd.exe (PID: 9852)
- cmd.exe (PID: 9648)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 10100)
- cmd.exe (PID: 9400)
- cmd.exe (PID: 9756)
- cmd.exe (PID: 9232)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 9768)
- cmd.exe (PID: 9596)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 10244)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 9616)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 9680)
- cmd.exe (PID: 10284)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 10492)
- cmd.exe (PID: 8480)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 10652)
- cmd.exe (PID: 10660)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 10600)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 11320)
- cmd.exe (PID: 9116)
- cmd.exe (PID: 11860)
- cmd.exe (PID: 11108)
- cmd.exe (PID: 10260)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 10644)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 11512)
- cmd.exe (PID: 10276)
- cmd.exe (PID: 12352)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 10740)
- cmd.exe (PID: 10720)
- cmd.exe (PID: 11532)
- cmd.exe (PID: 10924)
- cmd.exe (PID: 11548)
- cmd.exe (PID: 9816)
- cmd.exe (PID: 11768)
- cmd.exe (PID: 11400)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 10536)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 9624)
- cmd.exe (PID: 10016)
- cmd.exe (PID: 13196)
- cmd.exe (PID: 11504)
- cmd.exe (PID: 13504)
- cmd.exe (PID: 12992)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 12968)
- cmd.exe (PID: 13640)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 13540)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 13520)
- cmd.exe (PID: 12752)
- cmd.exe (PID: 12784)
- cmd.exe (PID: 13088)
- cmd.exe (PID: 14476)
- cmd.exe (PID: 14760)
- cmd.exe (PID: 15184)
- cmd.exe (PID: 10748)
- cmd.exe (PID: 13160)
- cmd.exe (PID: 12928)
- cmd.exe (PID: 11592)
- cmd.exe (PID: 15476)
- cmd.exe (PID: 14996)
- cmd.exe (PID: 11284)
- cmd.exe (PID: 12304)
- cmd.exe (PID: 13860)
- cmd.exe (PID: 15032)
- cmd.exe (PID: 15228)
- cmd.exe (PID: 15240)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 15396)
- cmd.exe (PID: 12532)
- cmd.exe (PID: 12240)
- cmd.exe (PID: 12368)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 12524)
- cmd.exe (PID: 13000)
- cmd.exe (PID: 12844)
- cmd.exe (PID: 11872)
- cmd.exe (PID: 9808)
- cmd.exe (PID: 13260)
- cmd.exe (PID: 12908)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 16516)
- cmd.exe (PID: 10828)
- cmd.exe (PID: 16156)
- cmd.exe (PID: 14416)
- cmd.exe (PID: 13572)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 17380)
- cmd.exe (PID: 12764)
- cmd.exe (PID: 13580)
- cmd.exe (PID: 18192)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 12688)
- cmd.exe (PID: 13632)
- cmd.exe (PID: 17016)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 14988)
- cmd.exe (PID: 14636)
- cmd.exe (PID: 14644)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 15948)
- cmd.exe (PID: 13380)
- cmd.exe (PID: 12560)
- cmd.exe (PID: 13788)
- cmd.exe (PID: 15860)
- cmd.exe (PID: 14752)
- cmd.exe (PID: 17396)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 11352)
- cmd.exe (PID: 15924)
- cmd.exe (PID: 10732)
- cmd.exe (PID: 11644)
- cmd.exe (PID: 15932)
- cmd.exe (PID: 17612)
- cmd.exe (PID: 16604)
- cmd.exe (PID: 16472)
- cmd.exe (PID: 18284)
- cmd.exe (PID: 18620)
- cmd.exe (PID: 18160)
- cmd.exe (PID: 18172)
- cmd.exe (PID: 13180)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 12824)
- cmd.exe (PID: 17876)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 13732)
- cmd.exe (PID: 18772)
- cmd.exe (PID: 15256)
- cmd.exe (PID: 19012)
- cmd.exe (PID: 14512)
- cmd.exe (PID: 15712)
- cmd.exe (PID: 18116)
- cmd.exe (PID: 18748)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 21028)
- cmd.exe (PID: 19508)
- cmd.exe (PID: 21152)
- cmd.exe (PID: 20236)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 22276)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 22348)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 17672)
- cmd.exe (PID: 20280)
- cmd.exe (PID: 21908)
- cmd.exe (PID: 22512)
- cmd.exe (PID: 24456)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 12272)
- cmd.exe (PID: 18460)
- cmd.exe (PID: 22436)
- cmd.exe (PID: 24468)
- cmd.exe (PID: 25316)
- cmd.exe (PID: 13612)
- cmd.exe (PID: 25568)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 19352)
- cmd.exe (PID: 25148)
- cmd.exe (PID: 25792)
- cmd.exe (PID: 27108)
- cmd.exe (PID: 25716)
- cmd.exe (PID: 28552)
- cmd.exe (PID: 25308)
- cmd.exe (PID: 24072)
- cmd.exe (PID: 15344)
- cmd.exe (PID: 26188)
- cmd.exe (PID: 24952)
- cmd.exe (PID: 29136)
- cmd.exe (PID: 26076)
- cmd.exe (PID: 28544)
- cmd.exe (PID: 26956)
- cmd.exe (PID: 19460)
- cmd.exe (PID: 29908)
- cmd.exe (PID: 20756)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 19868)
- cmd.exe (PID: 24772)
- cmd.exe (PID: 22252)
- cmd.exe (PID: 27704)
- cmd.exe (PID: 33144)
- cmd.exe (PID: 11628)
- cmd.exe (PID: 26728)
- cmd.exe (PID: 19800)
- cmd.exe (PID: 29828)
- cmd.exe (PID: 31404)
- cmd.exe (PID: 27532)
- cmd.exe (PID: 37320)
- cmd.exe (PID: 22732)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 30732)
- cmd.exe (PID: 37792)
- cmd.exe (PID: 21560)
- cmd.exe (PID: 20300)
- cmd.exe (PID: 16596)
- cmd.exe (PID: 19388)
- cmd.exe (PID: 22616)
- cmd.exe (PID: 22332)
- cmd.exe (PID: 20884)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 21280)
- cmd.exe (PID: 35960)
- cmd.exe (PID: 39752)
- cmd.exe (PID: 36172)
- cmd.exe (PID: 21068)
- cmd.exe (PID: 24472)
- cmd.exe (PID: 31156)
- cmd.exe (PID: 37632)
- cmd.exe (PID: 41024)
- cmd.exe (PID: 37760)
- cmd.exe (PID: 36484)
- cmd.exe (PID: 13876)
- cmd.exe (PID: 39920)
- cmd.exe (PID: 35992)
- cmd.exe (PID: 39760)
- cmd.exe (PID: 28772)
- cmd.exe (PID: 10092)
- cmd.exe (PID: 20636)
- cmd.exe (PID: 42104)
- cmd.exe (PID: 24512)
- cmd.exe (PID: 30300)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 24040)
- cmd.exe (PID: 27904)
Application launched itself
- cmd.exe (PID: 5956)
- cmd.exe (PID: 6620)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 4776)
- cmd.exe (PID: 7204)
- cmd.exe (PID: 864)
- cmd.exe (PID: 7212)
- cmd.exe (PID: 2140)
- cmd.exe (PID: 7256)
- cmd.exe (PID: 7296)
- cmd.exe (PID: 7240)
- cmd.exe (PID: 7372)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7304)
- cmd.exe (PID: 7264)
- cmd.exe (PID: 7400)
- cmd.exe (PID: 7316)
- cmd.exe (PID: 7504)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 7432)
- cmd.exe (PID: 7388)
- cmd.exe (PID: 7384)
- cmd.exe (PID: 7612)
- cmd.exe (PID: 7328)
- cmd.exe (PID: 7596)
- cmd.exe (PID: 7644)
- cmd.exe (PID: 7496)
- cmd.exe (PID: 7808)
- cmd.exe (PID: 7424)
- cmd.exe (PID: 7784)
- cmd.exe (PID: 7772)
- cmd.exe (PID: 7620)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7604)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7728)
- cmd.exe (PID: 7416)
- cmd.exe (PID: 8008)
- cmd.exe (PID: 8056)
- cmd.exe (PID: 7584)
- cmd.exe (PID: 7888)
- cmd.exe (PID: 7896)
- cmd.exe (PID: 8324)
- cmd.exe (PID: 7652)
- cmd.exe (PID: 7868)
- cmd.exe (PID: 8036)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7764)
- cmd.exe (PID: 7832)
- cmd.exe (PID: 7972)
- cmd.exe (PID: 7824)
- cmd.exe (PID: 8460)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 7816)
- cmd.exe (PID: 7956)
- cmd.exe (PID: 7996)
- cmd.exe (PID: 7980)
- cmd.exe (PID: 8800)
- cmd.exe (PID: 8232)
- cmd.exe (PID: 7752)
- cmd.exe (PID: 8244)
- cmd.exe (PID: 8604)
- cmd.exe (PID: 8412)
- cmd.exe (PID: 8680)
- cmd.exe (PID: 8596)
- cmd.exe (PID: 8832)
- cmd.exe (PID: 8208)
- cmd.exe (PID: 8620)
- cmd.exe (PID: 8488)
- cmd.exe (PID: 8316)
- cmd.exe (PID: 8692)
- cmd.exe (PID: 8260)
- cmd.exe (PID: 8700)
- cmd.exe (PID: 8788)
- cmd.exe (PID: 9204)
- cmd.exe (PID: 8828)
- cmd.exe (PID: 8372)
- cmd.exe (PID: 8524)
- cmd.exe (PID: 8504)
- cmd.exe (PID: 9188)
- cmd.exe (PID: 8672)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7368)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 7928)
- cmd.exe (PID: 8088)
- cmd.exe (PID: 8952)
- cmd.exe (PID: 9428)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 8020)
- cmd.exe (PID: 8916)
- cmd.exe (PID: 8736)
- cmd.exe (PID: 9052)
- cmd.exe (PID: 9176)
- cmd.exe (PID: 8368)
- cmd.exe (PID: 8224)
- cmd.exe (PID: 9324)
- cmd.exe (PID: 8468)
- cmd.exe (PID: 9004)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 7608)
- cmd.exe (PID: 7848)
- cmd.exe (PID: 9640)
- cmd.exe (PID: 9340)
- cmd.exe (PID: 9996)
- cmd.exe (PID: 8588)
- cmd.exe (PID: 9272)
- cmd.exe (PID: 8908)
- cmd.exe (PID: 9912)
- cmd.exe (PID: 9632)
- cmd.exe (PID: 9532)
- cmd.exe (PID: 8768)
- cmd.exe (PID: 9376)
- cmd.exe (PID: 9688)
- cmd.exe (PID: 8436)
- cmd.exe (PID: 8444)
- cmd.exe (PID: 9932)
- cmd.exe (PID: 9316)
- cmd.exe (PID: 9408)
- cmd.exe (PID: 8872)
- cmd.exe (PID: 9436)
- cmd.exe (PID: 9420)
- cmd.exe (PID: 8048)
- cmd.exe (PID: 9384)
- cmd.exe (PID: 9520)
- cmd.exe (PID: 9852)
- cmd.exe (PID: 9648)
- cmd.exe (PID: 9232)
- cmd.exe (PID: 10100)
- cmd.exe (PID: 8380)
- cmd.exe (PID: 8004)
- cmd.exe (PID: 9400)
- cmd.exe (PID: 9756)
- cmd.exe (PID: 9768)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 8756)
- cmd.exe (PID: 10244)
- cmd.exe (PID: 9616)
- cmd.exe (PID: 9596)
- cmd.exe (PID: 10284)
- cmd.exe (PID: 8160)
- cmd.exe (PID: 9680)
- cmd.exe (PID: 8516)
- cmd.exe (PID: 9784)
- cmd.exe (PID: 8448)
- cmd.exe (PID: 10652)
- cmd.exe (PID: 10660)
- cmd.exe (PID: 10492)
- cmd.exe (PID: 9868)
- cmd.exe (PID: 8480)
- cmd.exe (PID: 11564)
- cmd.exe (PID: 9116)
- cmd.exe (PID: 10600)
- cmd.exe (PID: 11320)
- cmd.exe (PID: 10856)
- cmd.exe (PID: 11860)
- cmd.exe (PID: 11512)
- cmd.exe (PID: 10644)
- cmd.exe (PID: 8168)
- cmd.exe (PID: 11108)
- cmd.exe (PID: 10740)
- cmd.exe (PID: 10260)
- cmd.exe (PID: 11648)
- cmd.exe (PID: 9816)
- cmd.exe (PID: 12352)
- cmd.exe (PID: 10720)
- cmd.exe (PID: 11532)
- cmd.exe (PID: 10924)
- cmd.exe (PID: 10276)
- cmd.exe (PID: 11548)
- cmd.exe (PID: 10536)
- cmd.exe (PID: 11768)
- cmd.exe (PID: 9300)
- cmd.exe (PID: 11400)
- cmd.exe (PID: 8084)
- cmd.exe (PID: 12992)
- cmd.exe (PID: 9624)
- cmd.exe (PID: 13196)
- cmd.exe (PID: 10016)
- cmd.exe (PID: 11504)
- cmd.exe (PID: 10036)
- cmd.exe (PID: 13504)
- cmd.exe (PID: 13540)
- cmd.exe (PID: 12968)
- cmd.exe (PID: 13640)
- cmd.exe (PID: 12752)
- cmd.exe (PID: 13828)
- cmd.exe (PID: 12784)
- cmd.exe (PID: 13088)
- cmd.exe (PID: 12928)
- cmd.exe (PID: 7712)
- cmd.exe (PID: 13520)
- cmd.exe (PID: 14476)
- cmd.exe (PID: 14760)
- cmd.exe (PID: 10748)
- cmd.exe (PID: 15184)
- cmd.exe (PID: 13160)
- cmd.exe (PID: 11592)
- cmd.exe (PID: 12304)
- cmd.exe (PID: 11284)
- cmd.exe (PID: 13860)
- cmd.exe (PID: 15032)
- cmd.exe (PID: 15476)
- cmd.exe (PID: 15228)
- cmd.exe (PID: 12532)
- cmd.exe (PID: 15240)
- cmd.exe (PID: 14996)
- cmd.exe (PID: 12592)
- cmd.exe (PID: 15396)
- cmd.exe (PID: 12524)
- cmd.exe (PID: 13000)
- cmd.exe (PID: 12240)
- cmd.exe (PID: 11408)
- cmd.exe (PID: 12368)
- cmd.exe (PID: 12844)
- cmd.exe (PID: 11872)
- cmd.exe (PID: 10828)
- cmd.exe (PID: 9808)
- cmd.exe (PID: 13260)
- cmd.exe (PID: 12908)
- cmd.exe (PID: 16516)
- cmd.exe (PID: 16156)
- cmd.exe (PID: 14416)
- cmd.exe (PID: 17016)
- cmd.exe (PID: 13632)
- cmd.exe (PID: 17380)
- cmd.exe (PID: 12764)
- cmd.exe (PID: 6048)
- cmd.exe (PID: 13572)
- cmd.exe (PID: 6148)
- cmd.exe (PID: 18192)
- cmd.exe (PID: 12016)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 13580)
- cmd.exe (PID: 15148)
- cmd.exe (PID: 14644)
- cmd.exe (PID: 15860)
- cmd.exe (PID: 12688)
- cmd.exe (PID: 14988)
- cmd.exe (PID: 14636)
- cmd.exe (PID: 12560)
- cmd.exe (PID: 13380)
- cmd.exe (PID: 15948)
- cmd.exe (PID: 14752)
- cmd.exe (PID: 13788)
- cmd.exe (PID: 11352)
- cmd.exe (PID: 11644)
- cmd.exe (PID: 15924)
- cmd.exe (PID: 16604)
- cmd.exe (PID: 10732)
- cmd.exe (PID: 6872)
- cmd.exe (PID: 17396)
- cmd.exe (PID: 16472)
- cmd.exe (PID: 15932)
- cmd.exe (PID: 15256)
- cmd.exe (PID: 17612)
- cmd.exe (PID: 18620)
- cmd.exe (PID: 12824)
- cmd.exe (PID: 18160)
- cmd.exe (PID: 18172)
- cmd.exe (PID: 18284)
- cmd.exe (PID: 17608)
- cmd.exe (PID: 17876)
- cmd.exe (PID: 13180)
- cmd.exe (PID: 18116)
- cmd.exe (PID: 4844)
- cmd.exe (PID: 13732)
- cmd.exe (PID: 18772)
- cmd.exe (PID: 6272)
- cmd.exe (PID: 19012)
- cmd.exe (PID: 18748)
- cmd.exe (PID: 19056)
- cmd.exe (PID: 14512)
- cmd.exe (PID: 15712)
- cmd.exe (PID: 20236)
- cmd.exe (PID: 21152)
- cmd.exe (PID: 19508)
- cmd.exe (PID: 8864)
- cmd.exe (PID: 21028)
- cmd.exe (PID: 21908)
- cmd.exe (PID: 22276)
- cmd.exe (PID: 5324)
- cmd.exe (PID: 22348)
- cmd.exe (PID: 22504)
- cmd.exe (PID: 17672)
- cmd.exe (PID: 20280)
- cmd.exe (PID: 18460)
- cmd.exe (PID: 22512)
- cmd.exe (PID: 24456)
- cmd.exe (PID: 6516)
- cmd.exe (PID: 12272)
- cmd.exe (PID: 22436)
- cmd.exe (PID: 24468)
- cmd.exe (PID: 19448)
- cmd.exe (PID: 25316)
- cmd.exe (PID: 13612)
- cmd.exe (PID: 25568)
- cmd.exe (PID: 25148)
- cmd.exe (PID: 19352)
- cmd.exe (PID: 27108)
- cmd.exe (PID: 28552)
- cmd.exe (PID: 25792)
- cmd.exe (PID: 25308)
- cmd.exe (PID: 25716)
- cmd.exe (PID: 24952)
- cmd.exe (PID: 26076)
- cmd.exe (PID: 15344)
- cmd.exe (PID: 26188)
- cmd.exe (PID: 24072)
- cmd.exe (PID: 29136)
- cmd.exe (PID: 26956)
- cmd.exe (PID: 28544)
- cmd.exe (PID: 6572)
- cmd.exe (PID: 19868)
- cmd.exe (PID: 19460)
- cmd.exe (PID: 29908)
- cmd.exe (PID: 20756)
- cmd.exe (PID: 22252)
- cmd.exe (PID: 27704)
- cmd.exe (PID: 33144)
- cmd.exe (PID: 11628)
- cmd.exe (PID: 24772)
- cmd.exe (PID: 26728)
- cmd.exe (PID: 19800)
- cmd.exe (PID: 29828)
- cmd.exe (PID: 31404)
- cmd.exe (PID: 27532)
- cmd.exe (PID: 37320)
- cmd.exe (PID: 37792)
- cmd.exe (PID: 1272)
- cmd.exe (PID: 30732)
- cmd.exe (PID: 21560)
- cmd.exe (PID: 16596)
- cmd.exe (PID: 22732)
- cmd.exe (PID: 19388)
- cmd.exe (PID: 22616)
- cmd.exe (PID: 21280)
- cmd.exe (PID: 36172)
- cmd.exe (PID: 20300)
- cmd.exe (PID: 22332)
- cmd.exe (PID: 18204)
- cmd.exe (PID: 20884)
- cmd.exe (PID: 24472)
- cmd.exe (PID: 39752)
- cmd.exe (PID: 21068)
- cmd.exe (PID: 35960)
- cmd.exe (PID: 31156)
- cmd.exe (PID: 37632)
- cmd.exe (PID: 36484)
- cmd.exe (PID: 41024)
- cmd.exe (PID: 37760)
- cmd.exe (PID: 28772)
- cmd.exe (PID: 13876)
- cmd.exe (PID: 39920)
- cmd.exe (PID: 35992)
- cmd.exe (PID: 39760)
- cmd.exe (PID: 10092)
- cmd.exe (PID: 42104)
- cmd.exe (PID: 20636)
- cmd.exe (PID: 24512)
- cmd.exe (PID: 30300)
- cmd.exe (PID: 3124)
- cmd.exe (PID: 24040)
- cmd.exe (PID: 27904)
INFO
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 25096)
- BackgroundTransferHost.exe (PID: 32016)
- BackgroundTransferHost.exe (PID: 21032)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
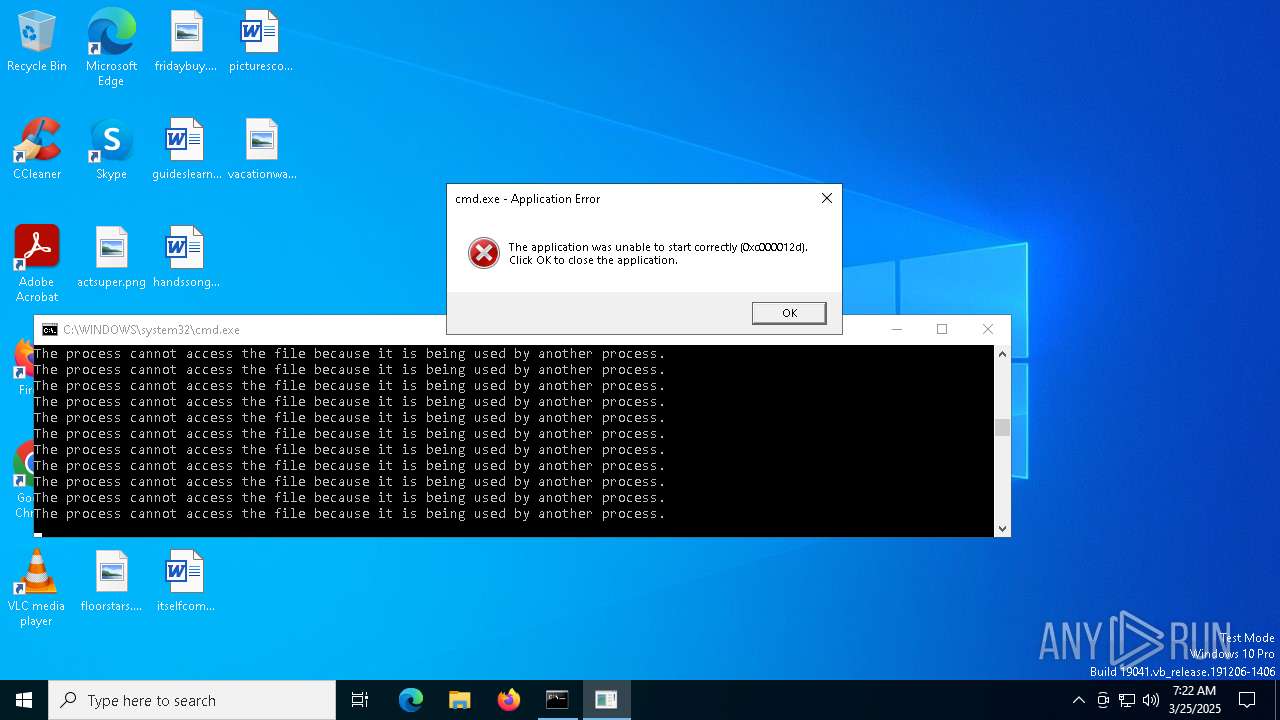
Total processes
3 486
Monitored processes
719
Malicious processes
252
Suspicious processes
116
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 864 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1272 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2140 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2384 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2432 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3124 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\system32\cmd.exe /S /D /c" "C:\Users\admin\AppData\Local\Temp\virus.cmd"" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
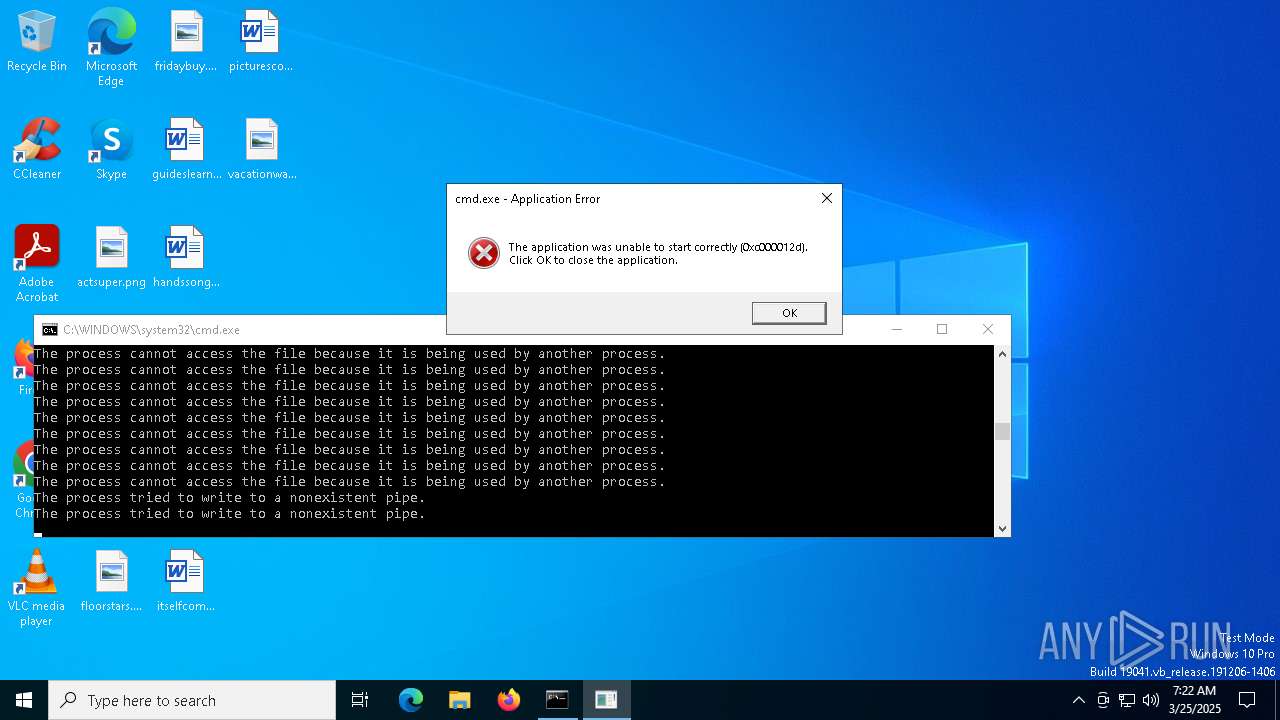
Total events
9 222
Read events
9 207
Write events
15
Delete events
0
Modification events
| (PID) Process: | (25096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (25096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (25096) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (32016) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (32016) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (32016) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (20848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (20848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (20848) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (33216) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
5
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7ef66b03-14e8-4ea6-bfce-4762e4082d4b.down_data | — | |
MD5:— | SHA256:— | |||
| 6620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\$_.cmd | text | |
MD5:0D6A9714884A0FEED715A4E6FFDC14AF | SHA256:6FBB0BE8E6644B0057A42083DCA5E78A95C799E81DE8AABF942A3A40C7C81E3D | |||
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7C6F750F08023F724A77DB26C694D94E | SHA256:ACE5B347DEEFD49A053CD61EED29F73CF4A6B3F85426592DC8E1B43396EA74FF | |||
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:4872BABAF39AA62B8D32695EBB7E9173 | SHA256:2EE85DF86EE29BBEB3DCA81AA29B6DE204F605A2769B84C728A329178A2D0999 | |||
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\7ef66b03-14e8-4ea6-bfce-4762e4082d4b.34a6bb0c-47b1-4726-a68d-a82a201696e4.down_meta | binary | |
MD5:0430492BCF37A6654B62AADEDC4CC2EF | SHA256:E07FD1C178619C279BF51AC4E756A6072515D33C091E51F925DEE41314F6D176 | |||
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\50ec1b39-b7be-41ce-8106-7ab79b85c446.34a6bb0c-47b1-4726-a68d-a82a201696e4.down_meta | binary | |
MD5:0430492BCF37A6654B62AADEDC4CC2EF | SHA256:E07FD1C178619C279BF51AC4E756A6072515D33C091E51F925DEE41314F6D176 | |||
| 32016 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\50ec1b39-b7be-41ce-8106-7ab79b85c446.up_meta_secure | binary | |
MD5:6DE3FA673DBE7E02355DF9D674737669 | SHA256:7391F523189605B63F528CC7C83074FF93BAA1A818850F2C3ED27EA3C51ACC14 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
23
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
13096 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
27676 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
27676 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
32016 | BackgroundTransferHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5176 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
6544 | svchost.exe | 40.126.31.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3216 | svchost.exe | 20.198.162.76:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | SG | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |