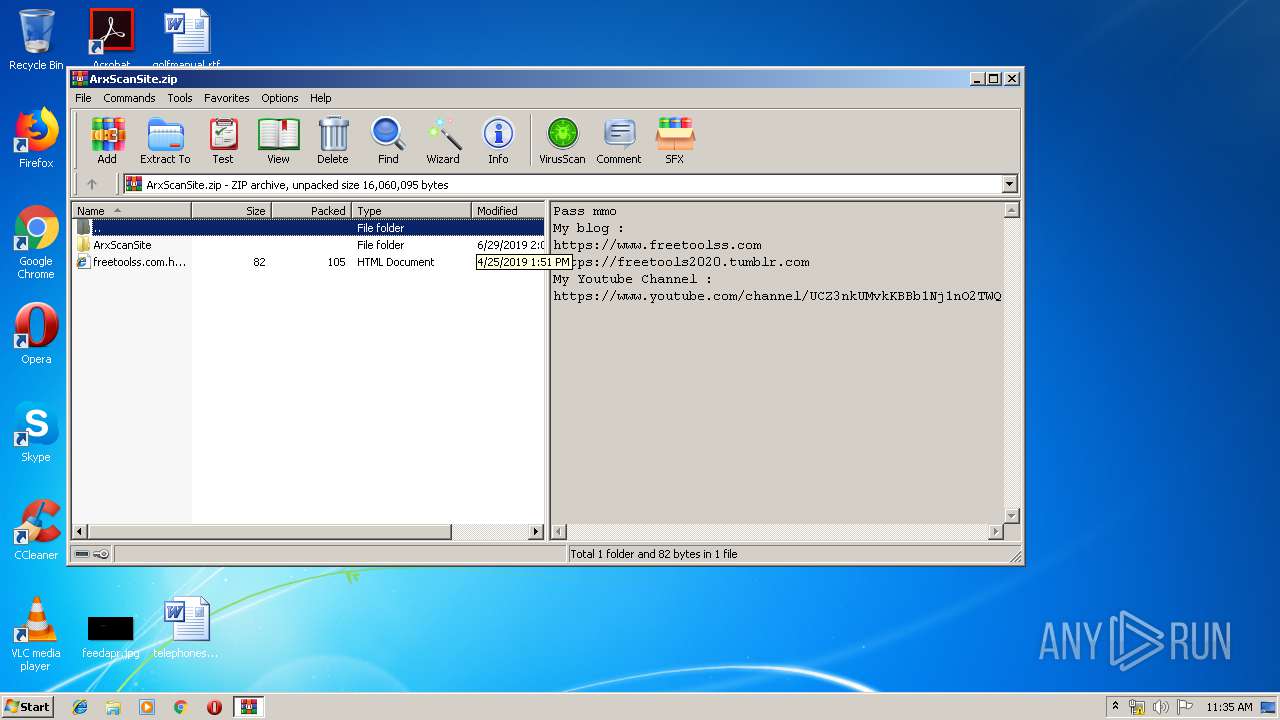
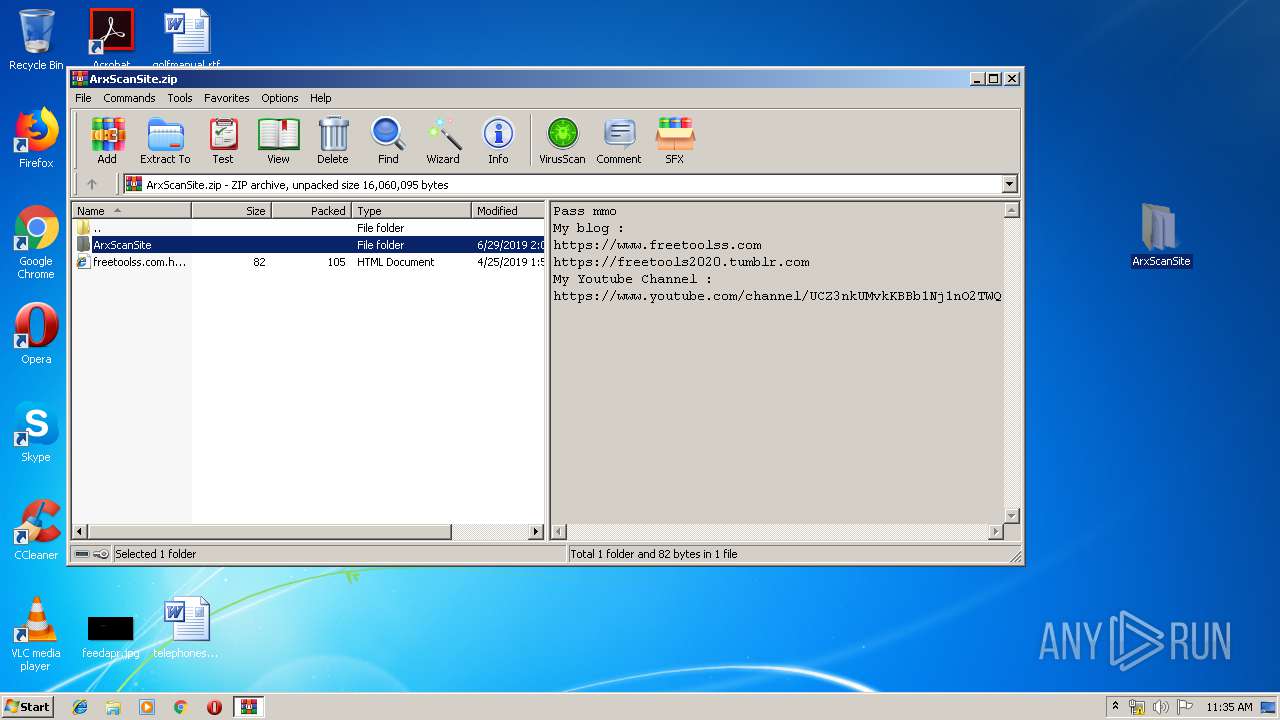
| File name: | ArxScanSite.zip |
| Full analysis: | https://app.any.run/tasks/8578fbd4-c793-4646-9dd3-dbb46bec1e22 |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 10:34:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 1E8E00A90551C88F0373C233FBA4A7E1 |
| SHA1: | 530EF2F1445D75DBD4511E530B34951EF4992CFA |
| SHA256: | 5F7793F0A1699872609B9F4FEDF7F8949A2794BD994D1325068E07ABC83AA9B0 |
| SSDEEP: | 196608:jsjTp4a66Xr7O/6f6OtHlwWGqo/brgwQrn75W:jKjXrnyOtFwvzV |
MALICIOUS
Application was dropped or rewritten from another process
- ArxScanSite.exe (PID: 1228)
- TempSetup.exe (PID: 2400)
- ~ArxScanSite.exe (PID: 3124)
- svchost.exe (PID: 2568)
- svchost.exe (PID: 2996)
Changes the autorun value in the registry
- TempSetup.exe (PID: 2400)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3468)
- ArxScanSite.exe (PID: 1228)
- TempSetup.exe (PID: 2400)
- svchost.exe (PID: 2568)
Creates executable files which already exist in Windows
- TempSetup.exe (PID: 2400)
- svchost.exe (PID: 2568)
Creates files in the user directory
- TempSetup.exe (PID: 2400)
- svchost.exe (PID: 2568)
- svchost.exe (PID: 2996)
INFO
Manual execution by user
- ArxScanSite.exe (PID: 1228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:06:29 20:04:09 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ArxScanSite/ |
Total processes
39
Monitored processes
6
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
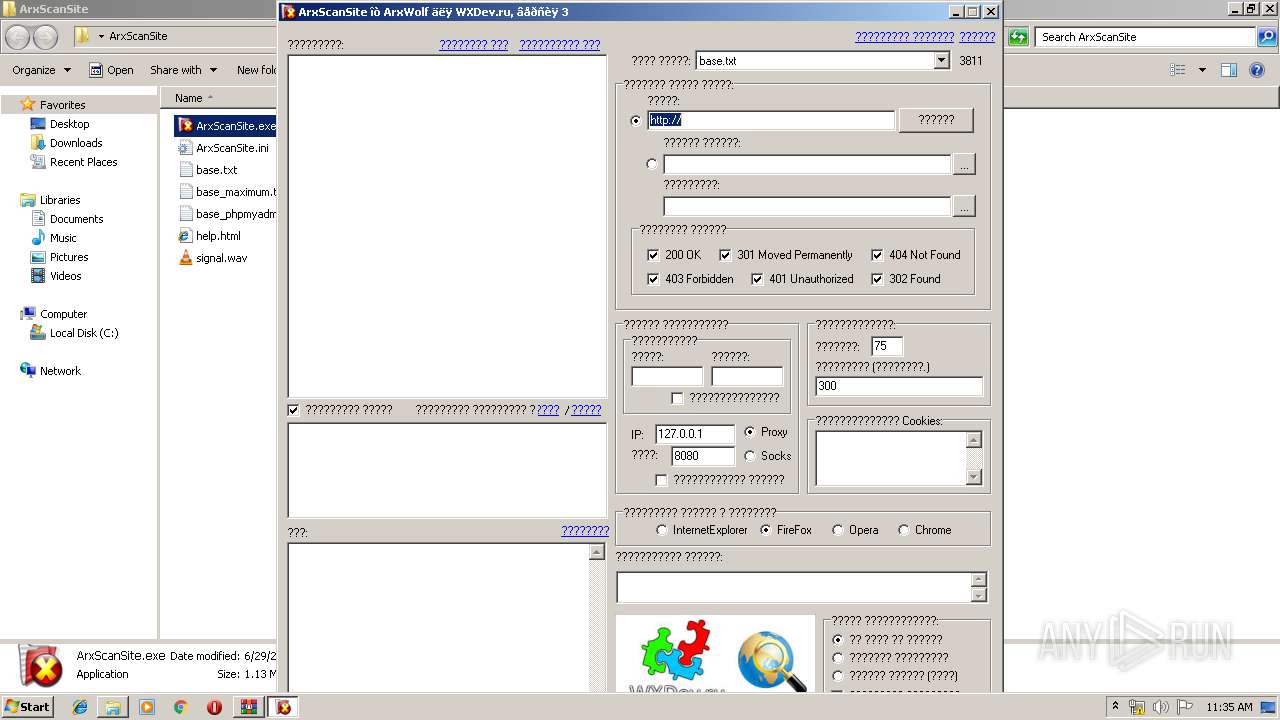
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | "C:\Users\admin\Desktop\ArxScanSite\ArxScanSite.exe" | C:\Users\admin\Desktop\ArxScanSite\ArxScanSite.exe | explorer.exe | ||||||||||||
User: admin Company: ArxWolf Integrity Level: MEDIUM Description: Сканер директорий и файлов на сайте Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
| 2400 | "C:\Users\admin\AppData\Local\TempSetup.exe" | C:\Users\admin\AppData\Local\TempSetup.exe | ArxScanSite.exe | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: MEDIUM Description: hkcmd Module Exit code: 0 Version: 8.1.1.7800 Modules
| |||||||||||||||
| 2568 | "C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\8.1.1.7800\svchost.exe" | C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\8.1.1.7800\svchost.exe | TempSetup.exe | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\8.1.7601.17587\svchost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\8.1.7601.17587\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 8.1.1.7900 Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\Desktop\ArxScanSite\~ArxScanSite.exe" | C:\Users\admin\Desktop\ArxScanSite\~ArxScanSite.exe | — | ArxScanSite.exe | |||||||||||
User: admin Company: ArxWolf Integrity Level: MEDIUM Description: Сканер директорий и файлов на сайте Exit code: 0 Version: 3.0.0.0 Modules
| |||||||||||||||
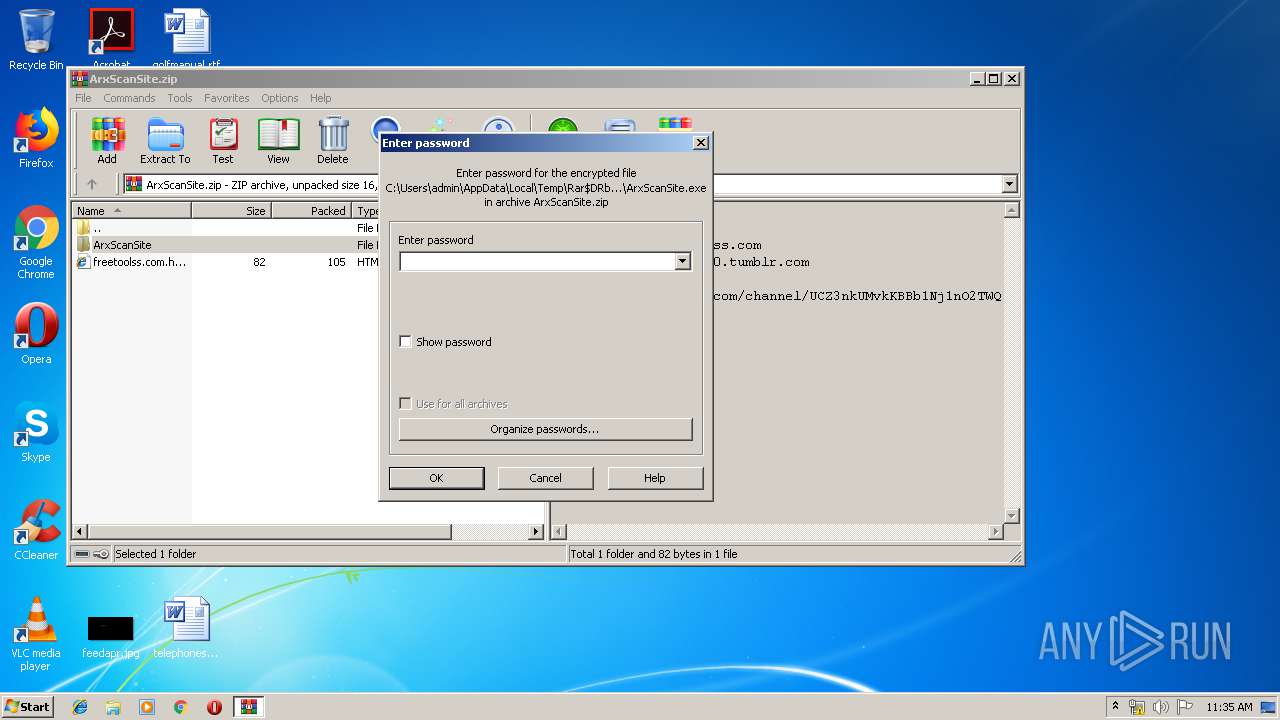
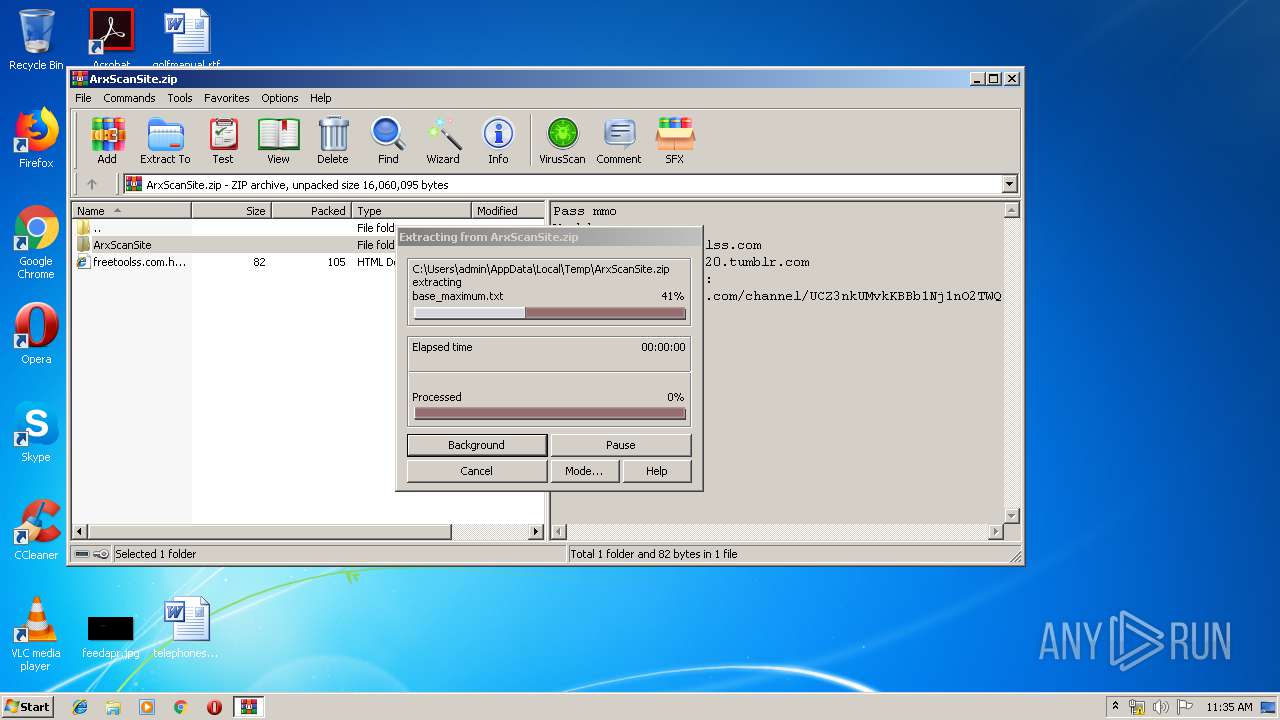
| 3468 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\ArxScanSite.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 740
Read events
1 648
Write events
92
Delete events
0
Modification events
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\ArxScanSite.zip | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
| (PID) Process: | (3468) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
5
Suspicious files
1
Text files
2
Unknown types
0
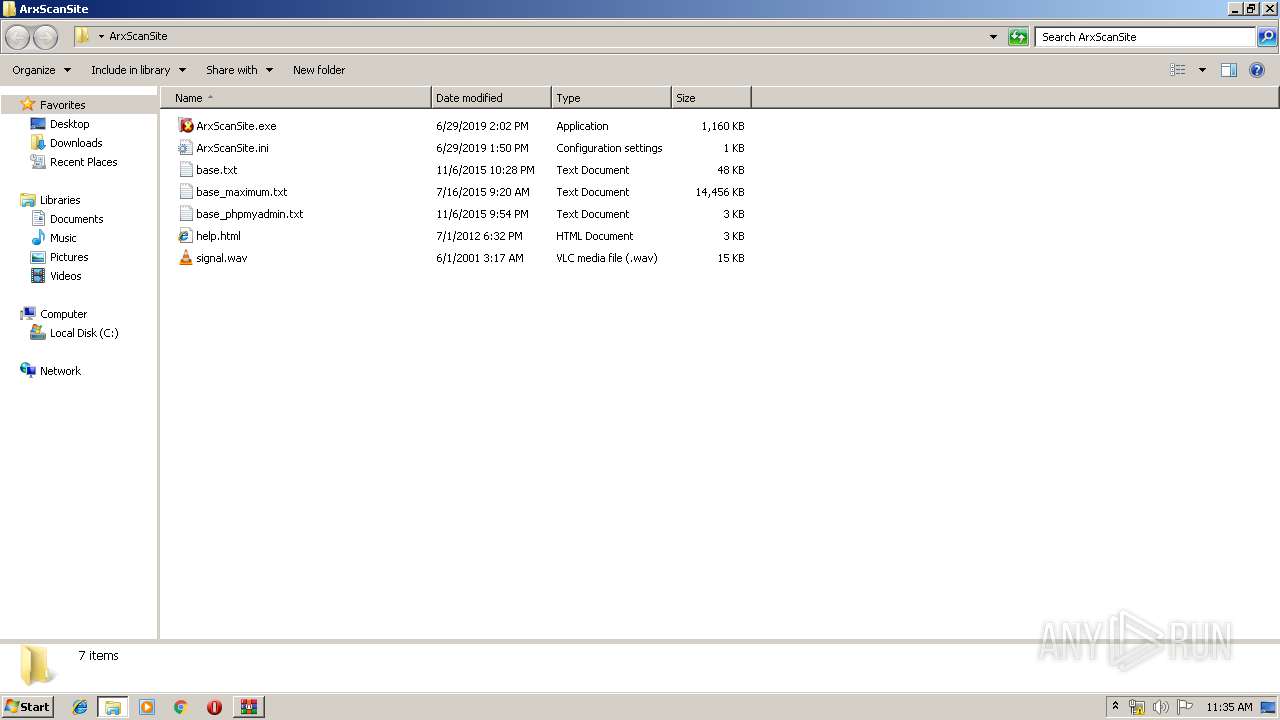
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\base_maximum.txt | — | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\base_phpmyadmin.txt | — | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\help.html | — | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\signal.wav | — | |
MD5:— | SHA256:— | |||
| 2400 | TempSetup.exe | C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\8.1.1.7800\server.zip | — | |
MD5:— | SHA256:— | |||
| 2568 | svchost.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\ArxScanSite.ini | text | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\base.txt | text | |
MD5:— | SHA256:— | |||
| 3468 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3468.21969\ArxScanSite\ArxScanSite.exe | executable | |
MD5:— | SHA256:— | |||
| 1228 | ArxScanSite.exe | C:\Users\admin\Desktop\ArxScanSite\~ArxScanSite.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2996 | svchost.exe | GET | 200 | 160.153.51.197:80 | http://capeturk.com/1/explorer.txt | US | text | 100 b | whitelisted |
2996 | svchost.exe | GET | 404 | 5.134.12.131:80 | http://www.spencerbuley.com/wp-content/cache/nextend/web/n2/1/explorer.zip | GB | html | 24.5 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2996 | svchost.exe | 160.153.51.197:80 | capeturk.com | GoDaddy.com, LLC | US | unknown |
2996 | svchost.exe | 5.134.12.131:80 | www.spencerbuley.com | UKDedicated LTD | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wxdev.ru |
| unknown |
capeturk.com |
| whitelisted |
www.spencerbuley.com |
| malicious |