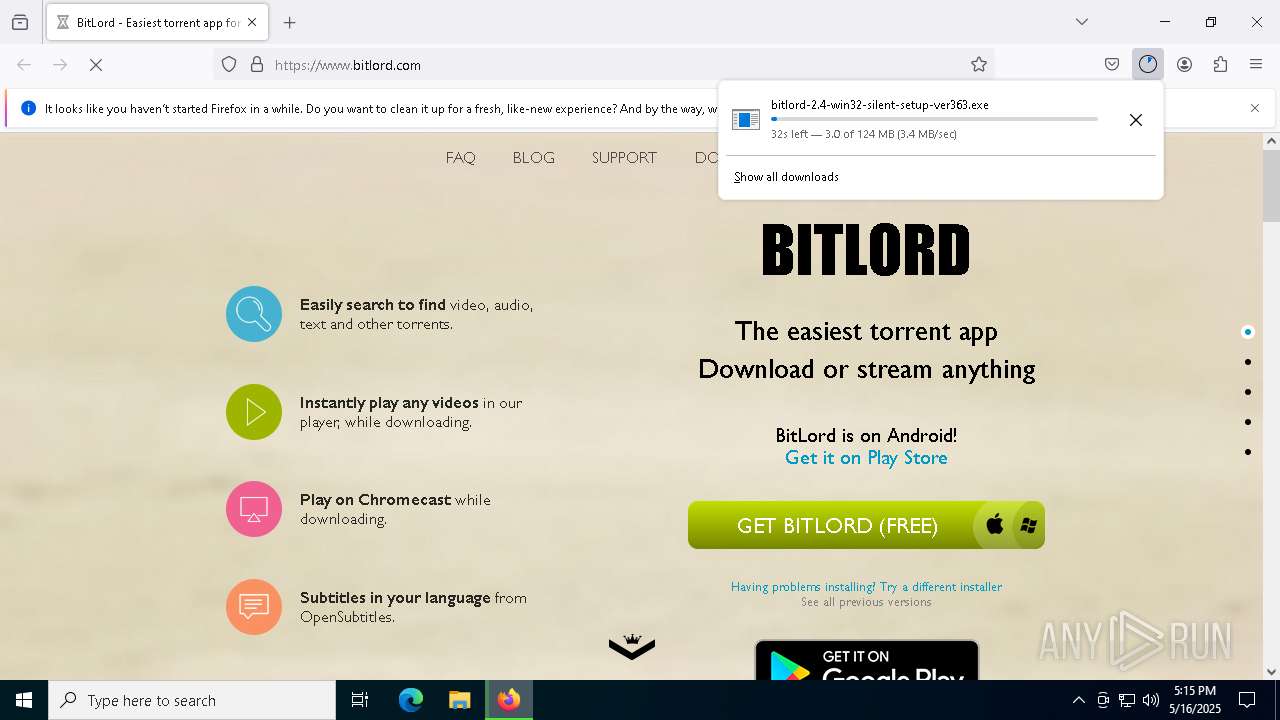
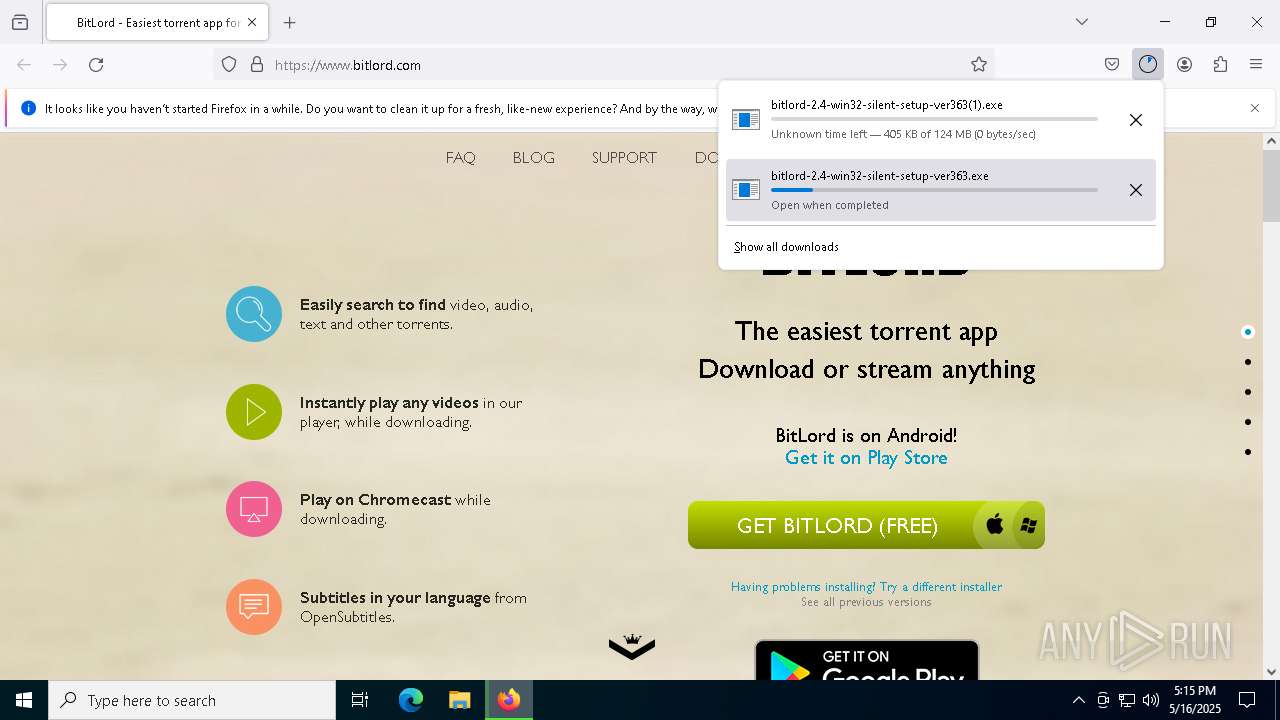
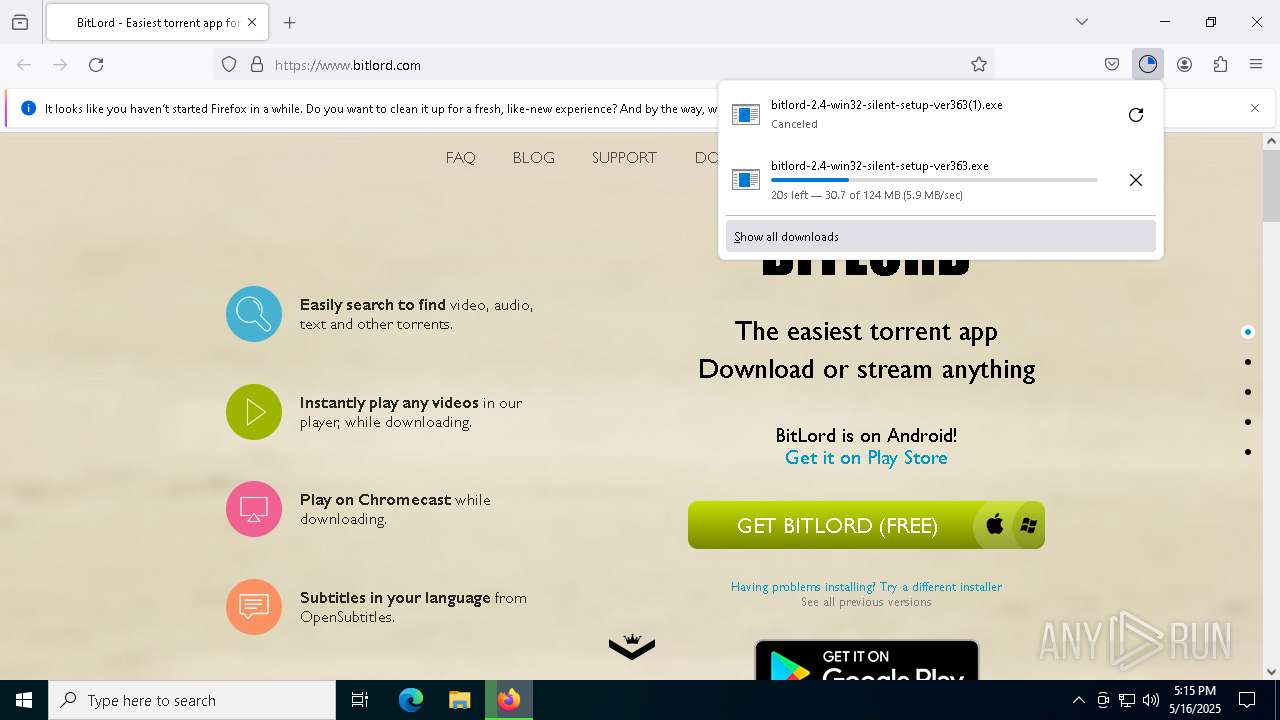
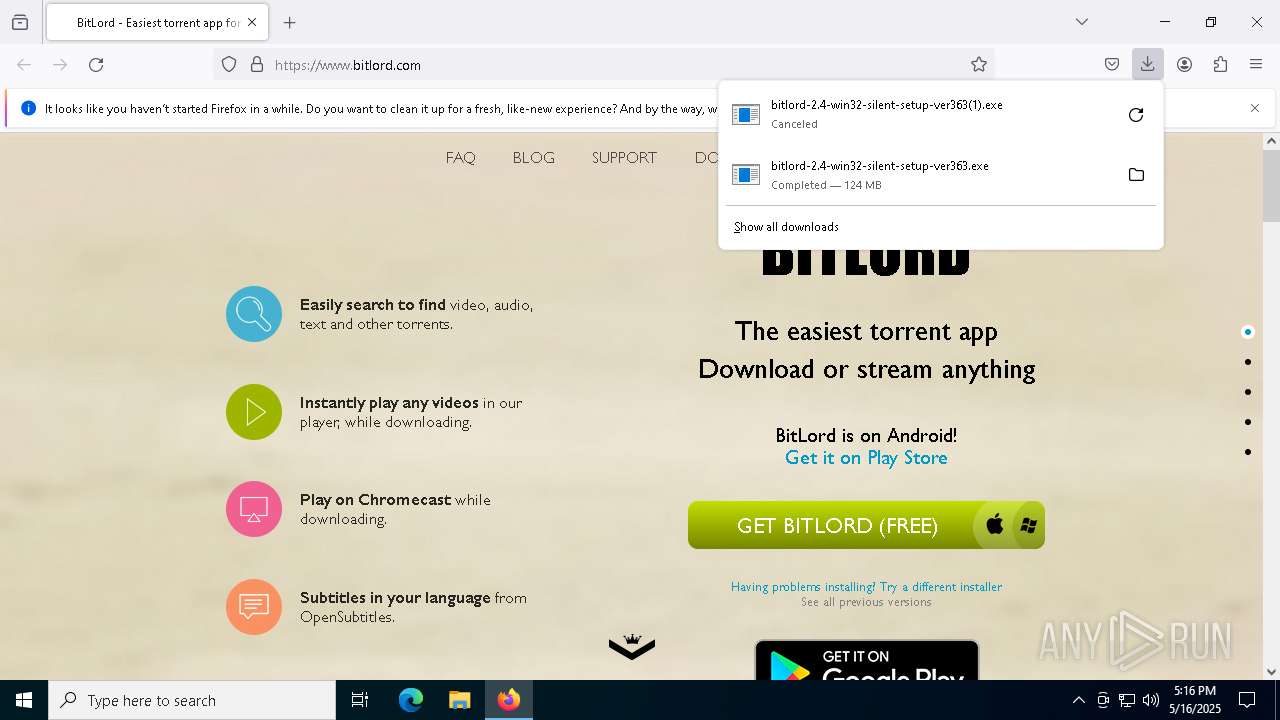
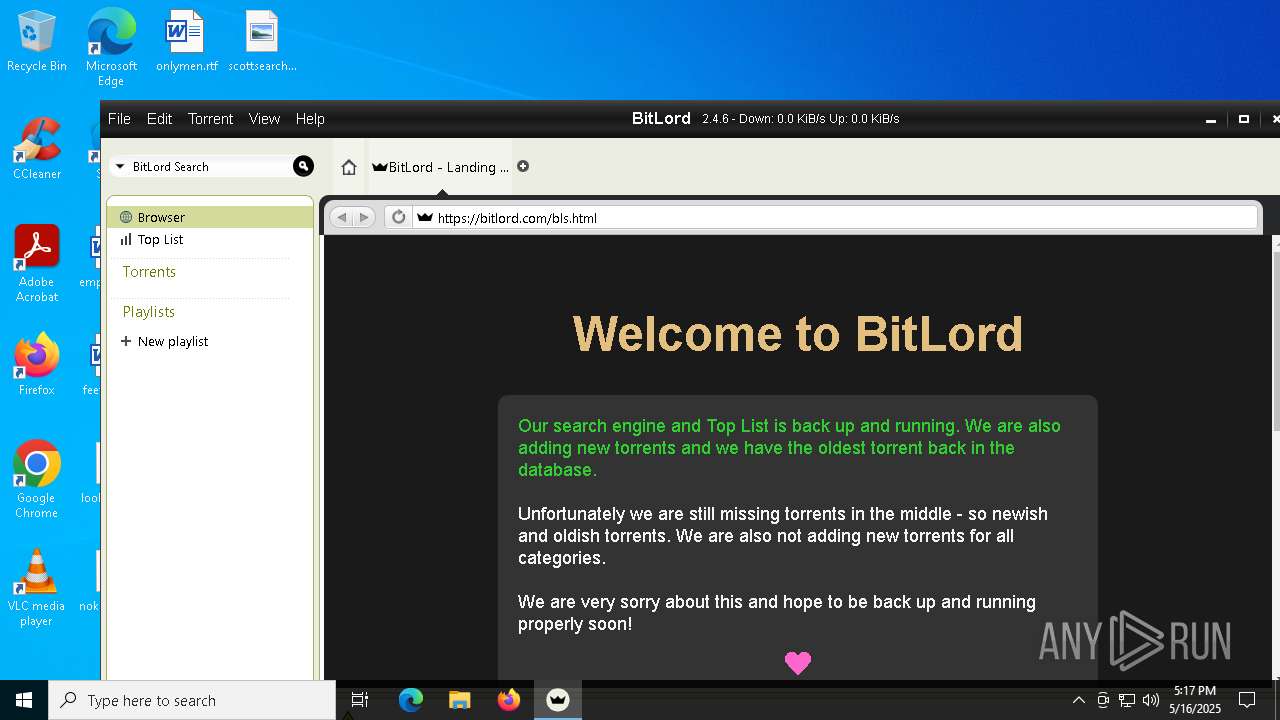
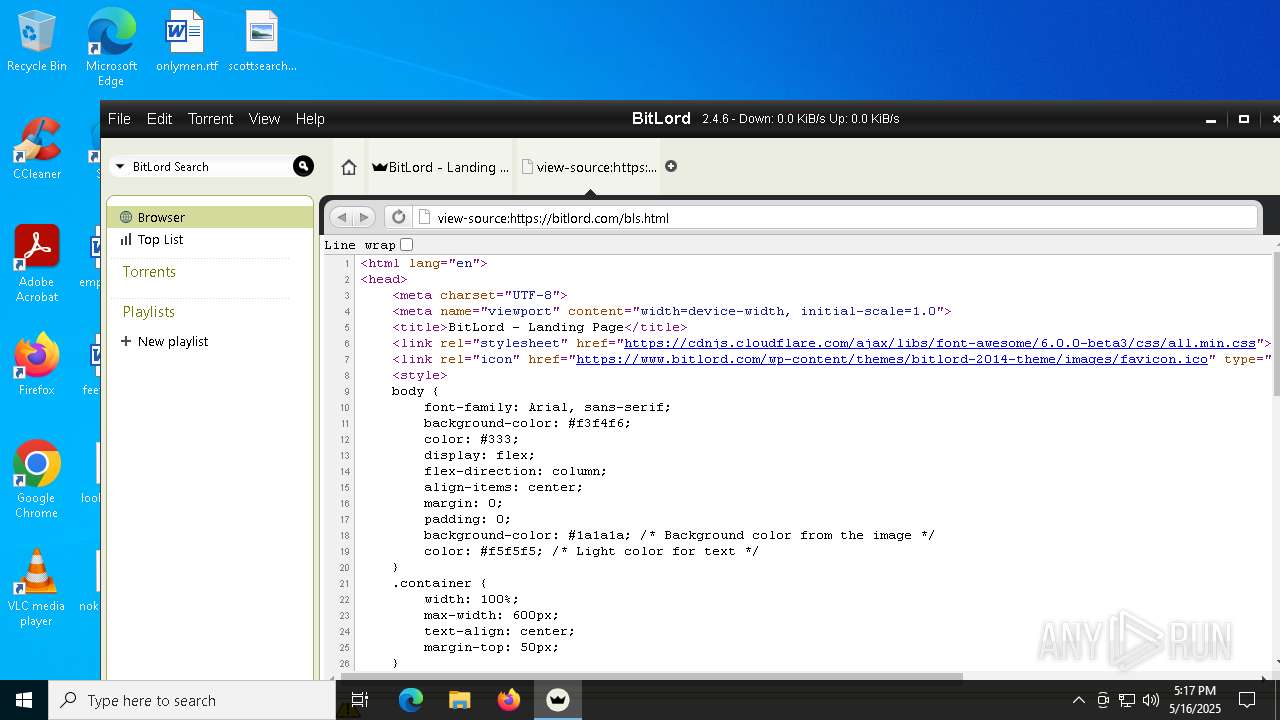
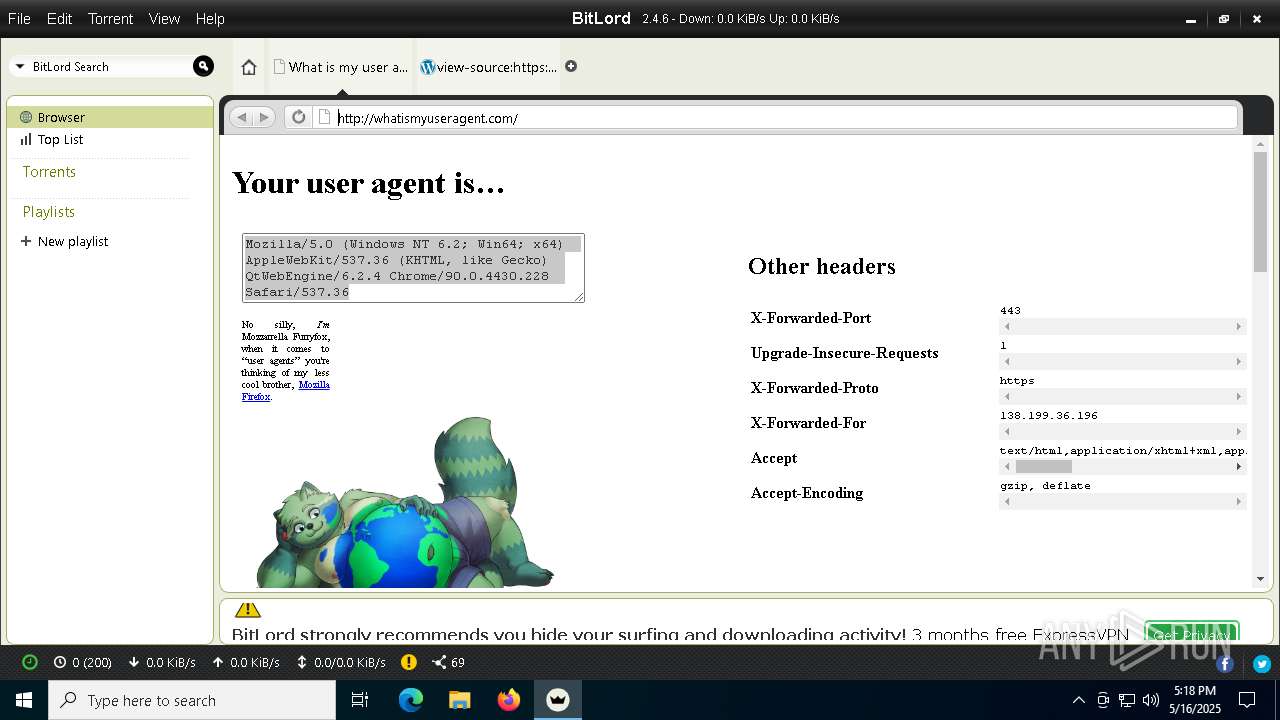
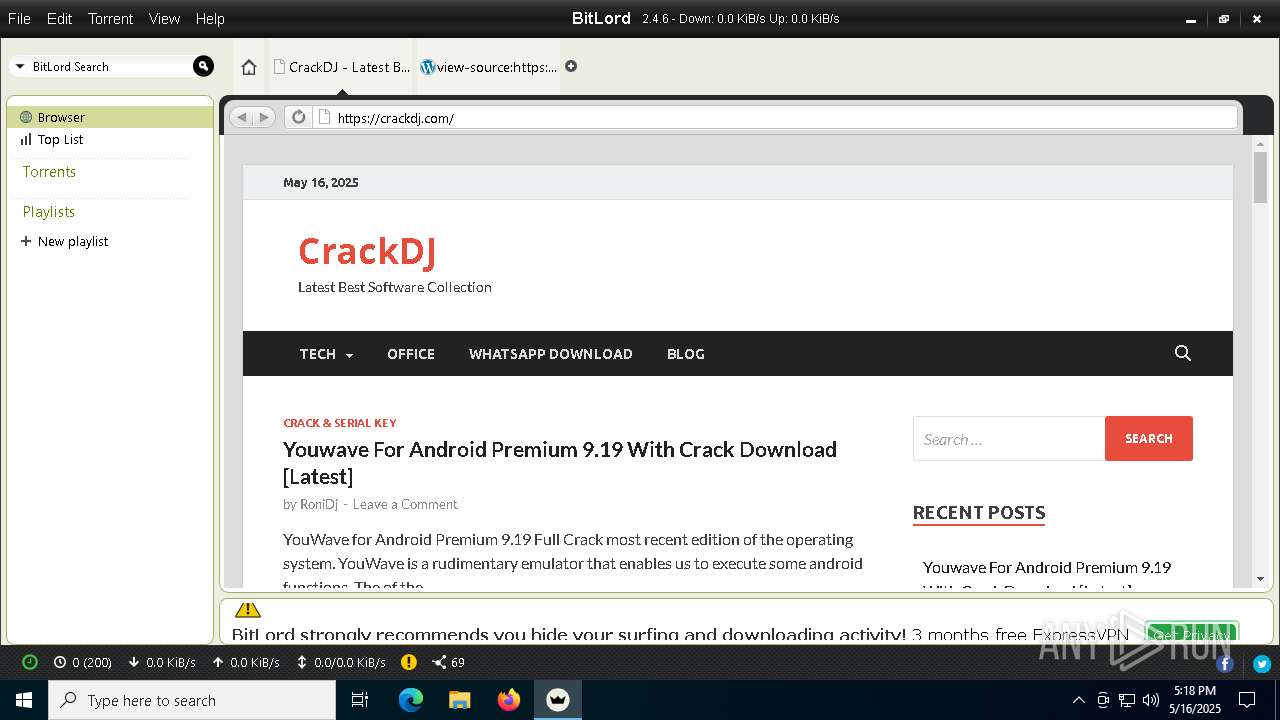
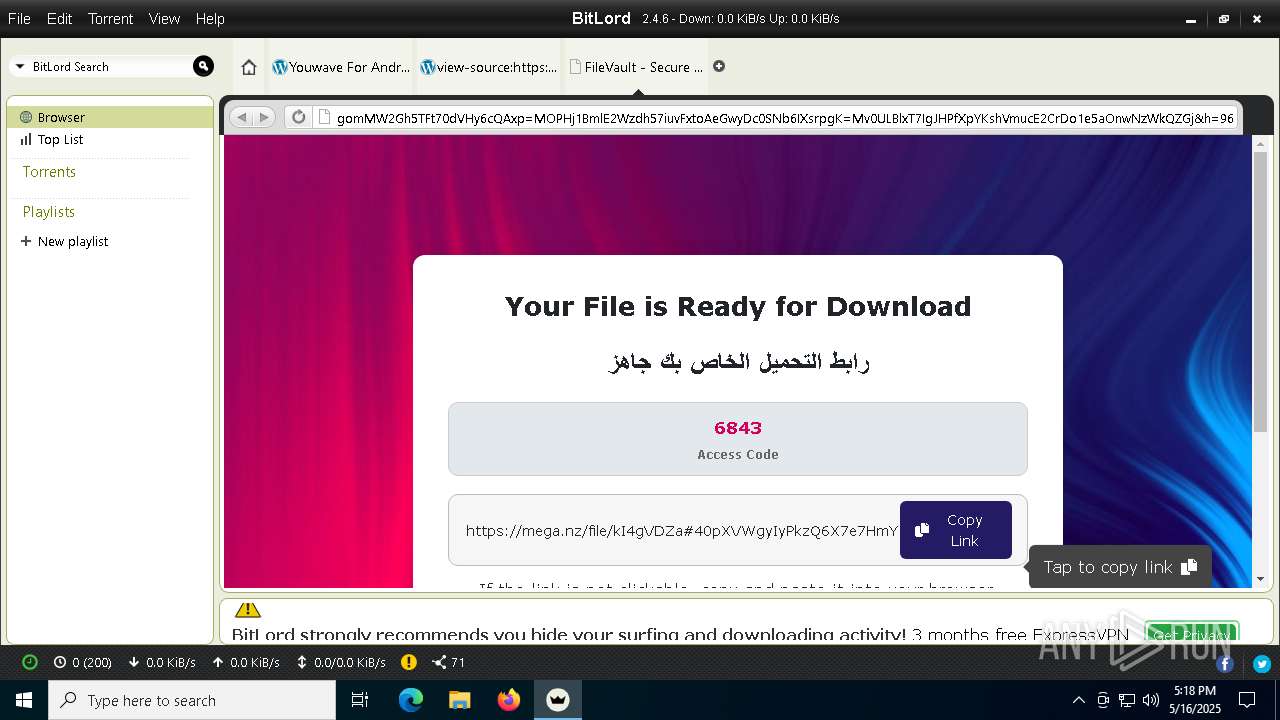
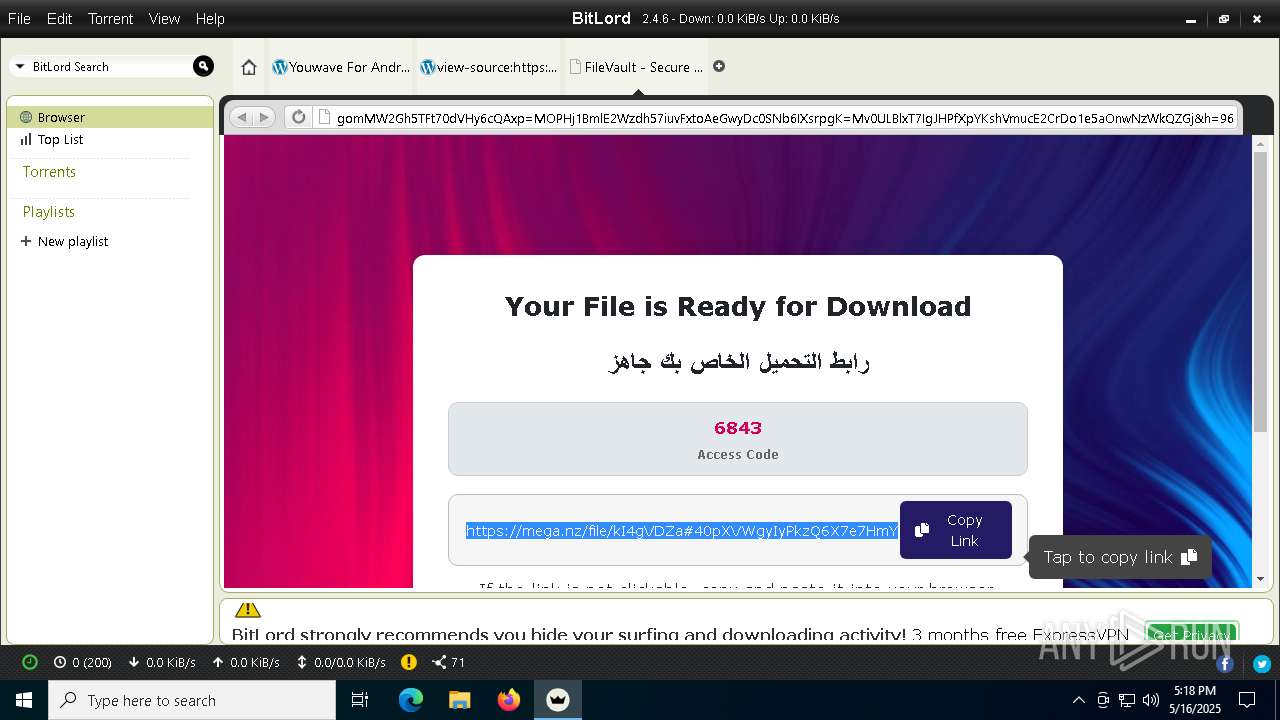
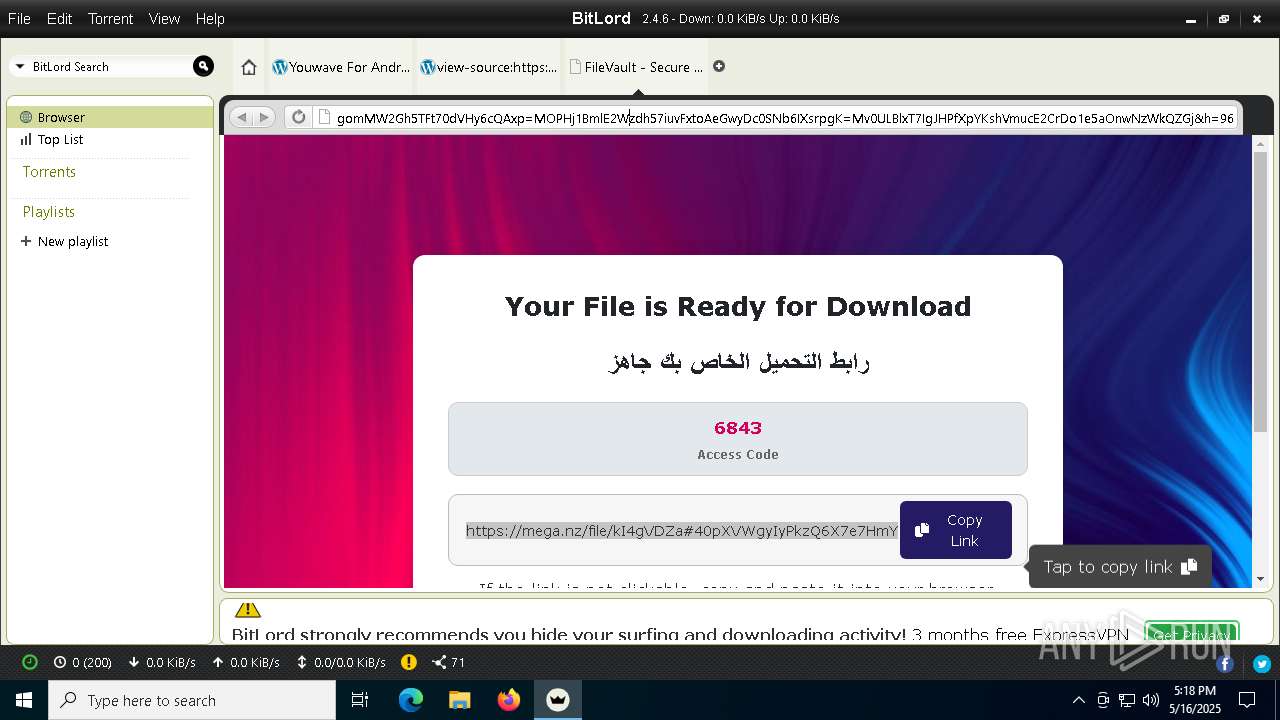
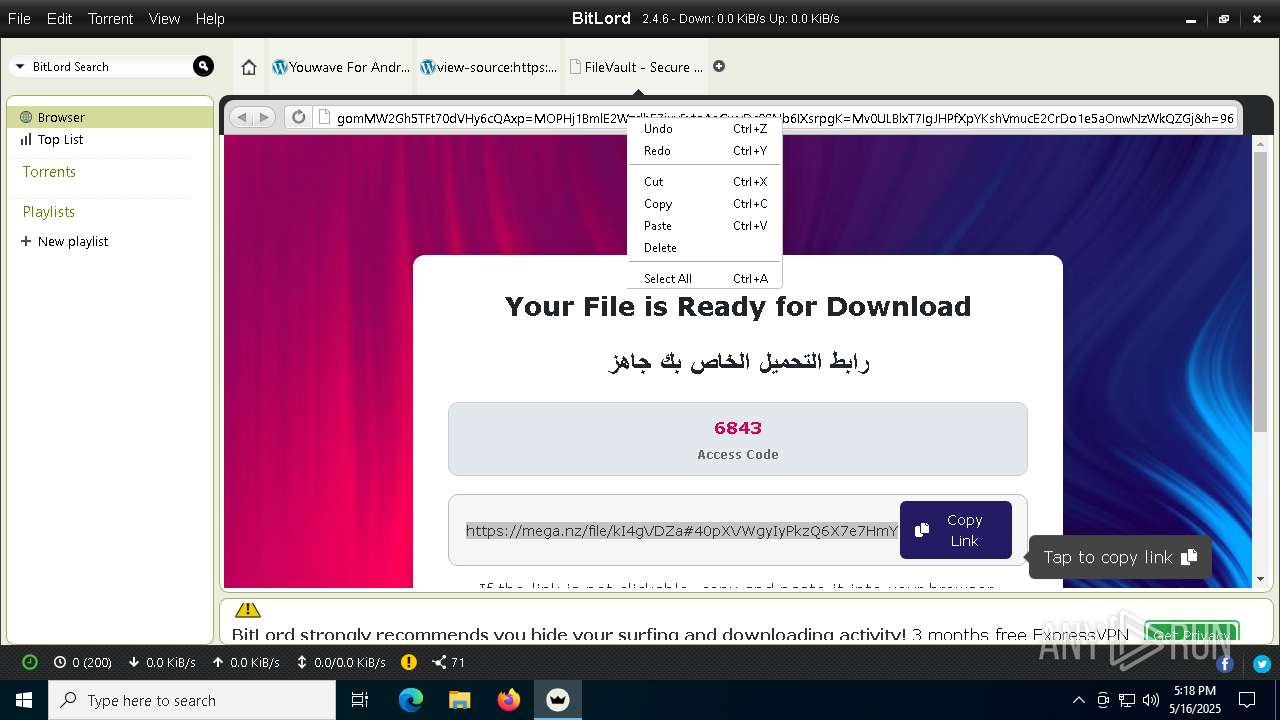
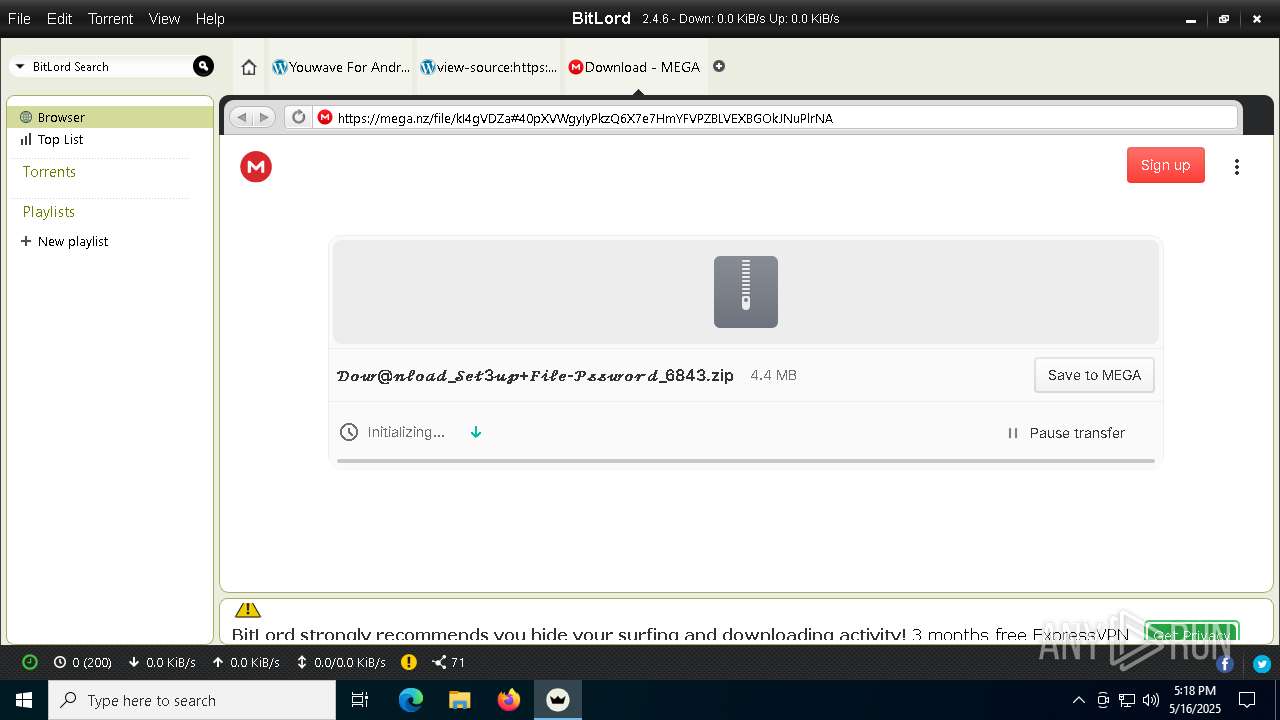
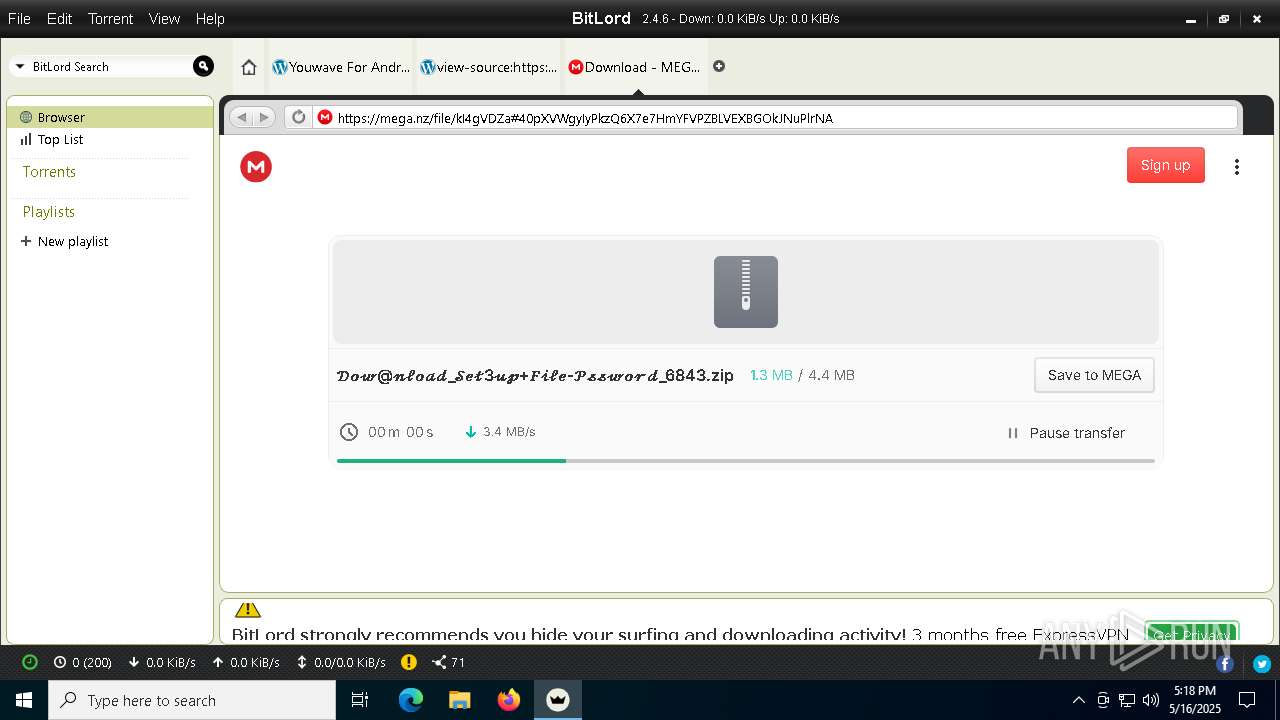
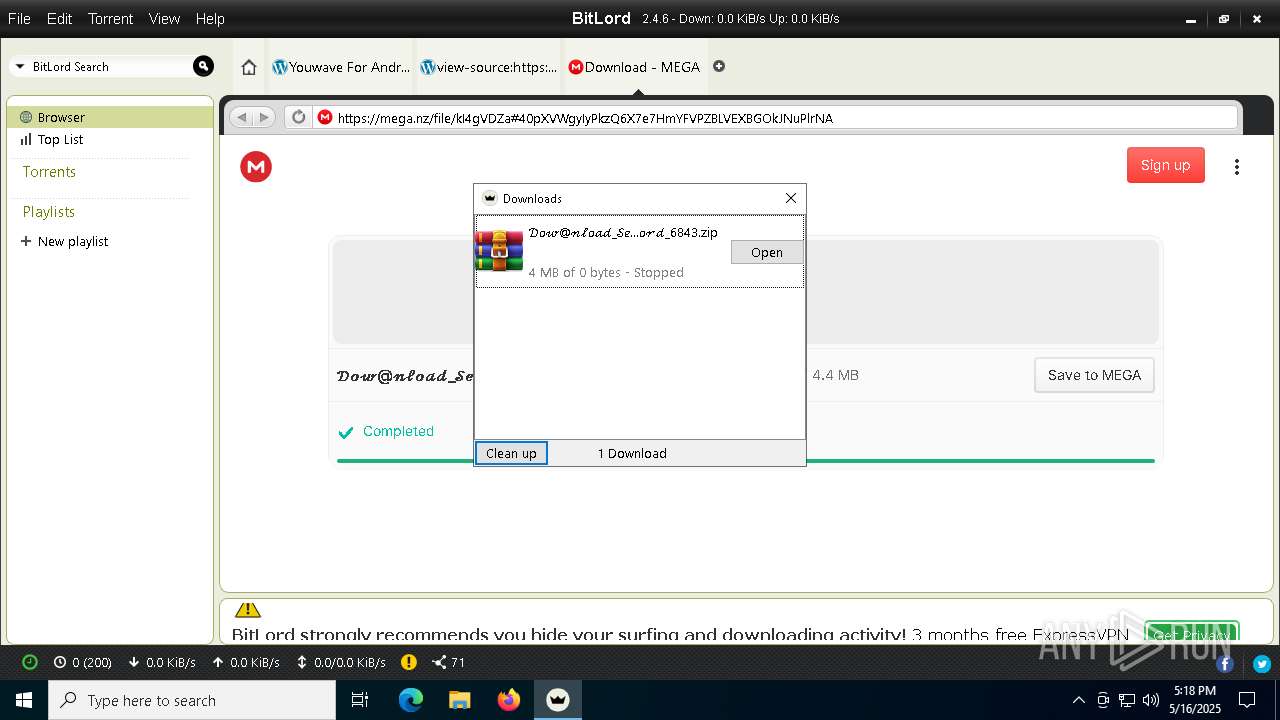
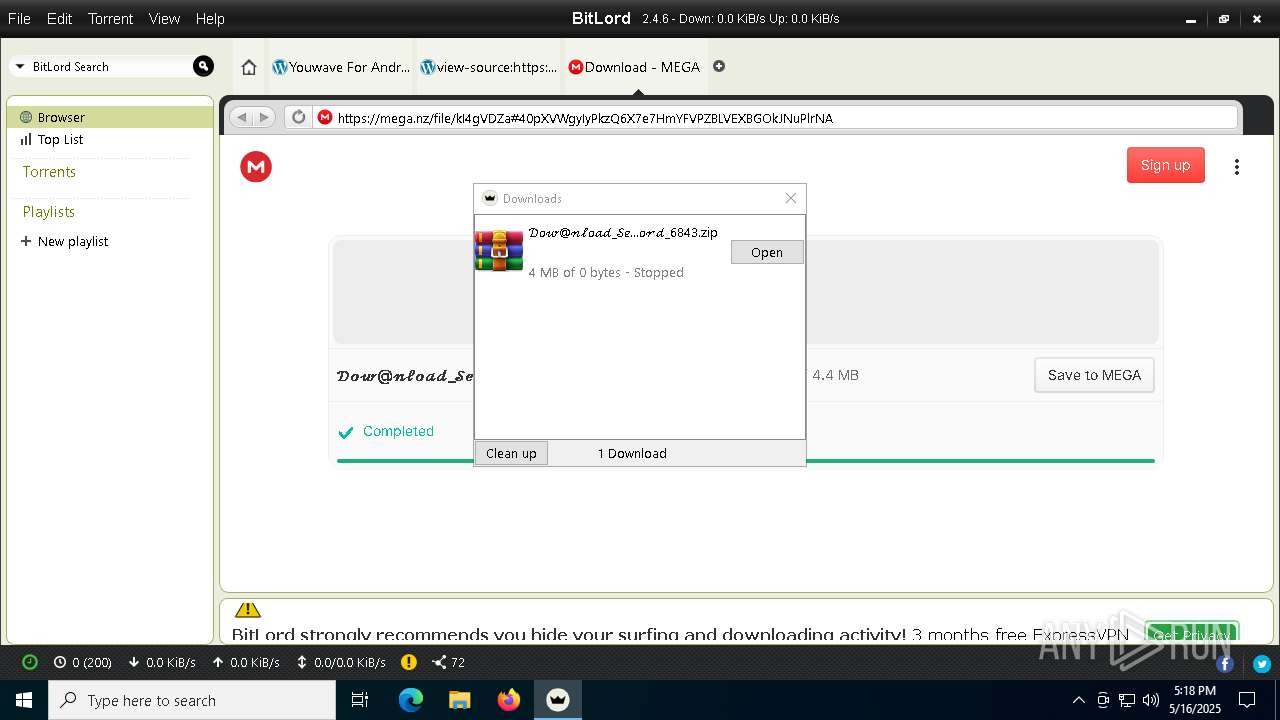
| URL: | https://www.bitlord.com/ |
| Full analysis: | https://app.any.run/tasks/e86415fe-3807-4df9-a77b-d2d15b4e26e0 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 17:15:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C4F50D69E5DB49B18C18598A5B044FC3 |
| SHA1: | 97814A838D7B7C1E252ABCC595046192DFD2ACD6 |
| SHA256: | 5F74DEC3D695BC98BC2821889A0FF7667FBF0B1F34F5506D3DE5FEE7D38161C6 |
| SSDEEP: | 3:N8DSLsk9KK:2OLsk9R |
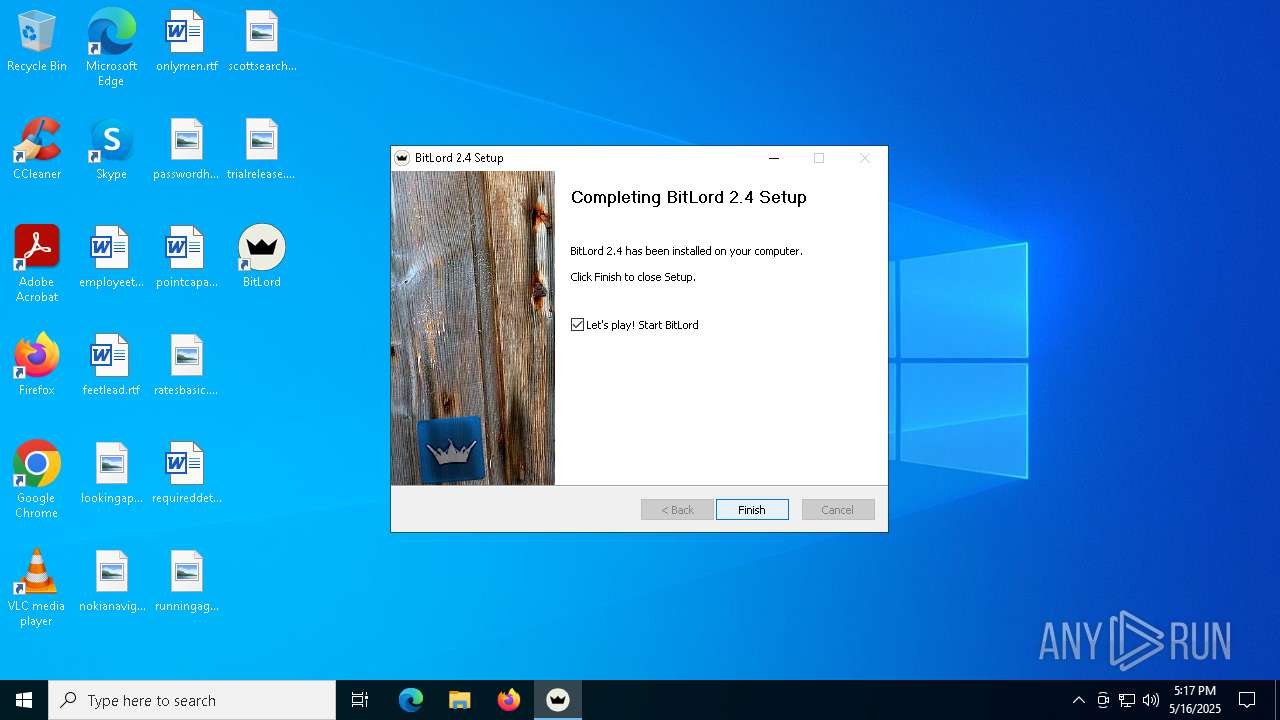
MALICIOUS
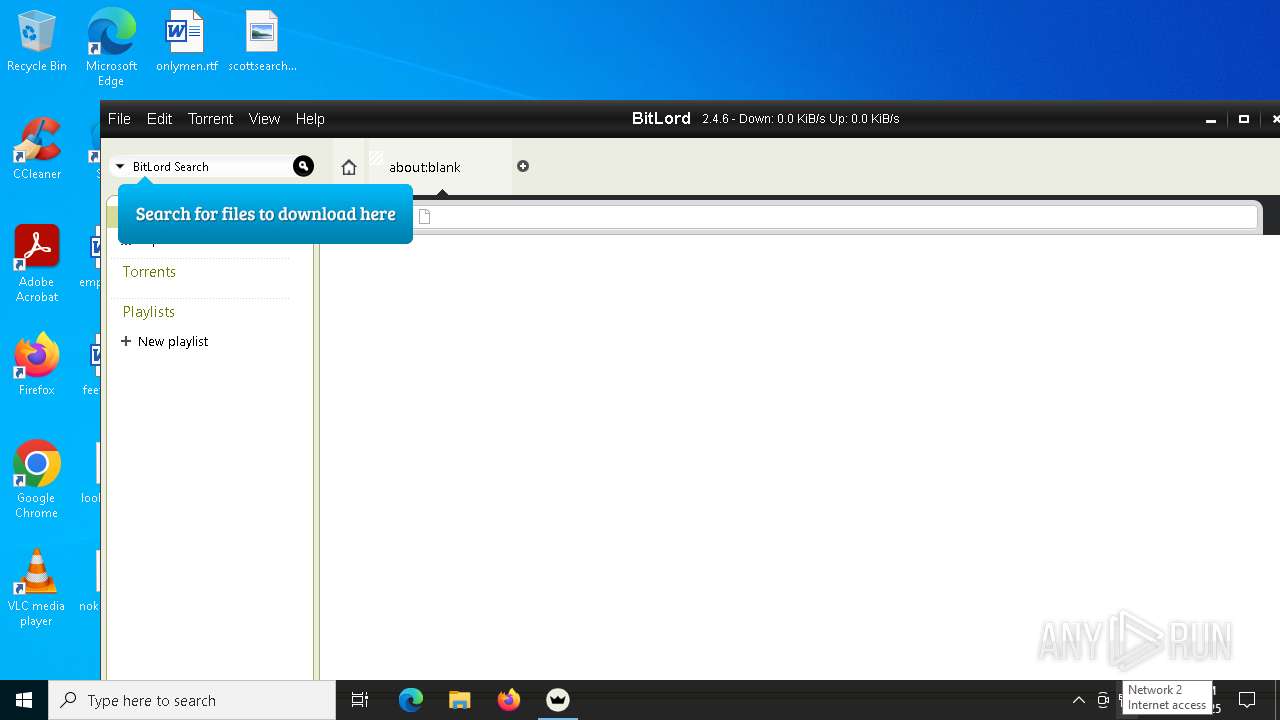
BITTORRENT has been detected (SURICATA)
- BitLord.exe (PID: 872)
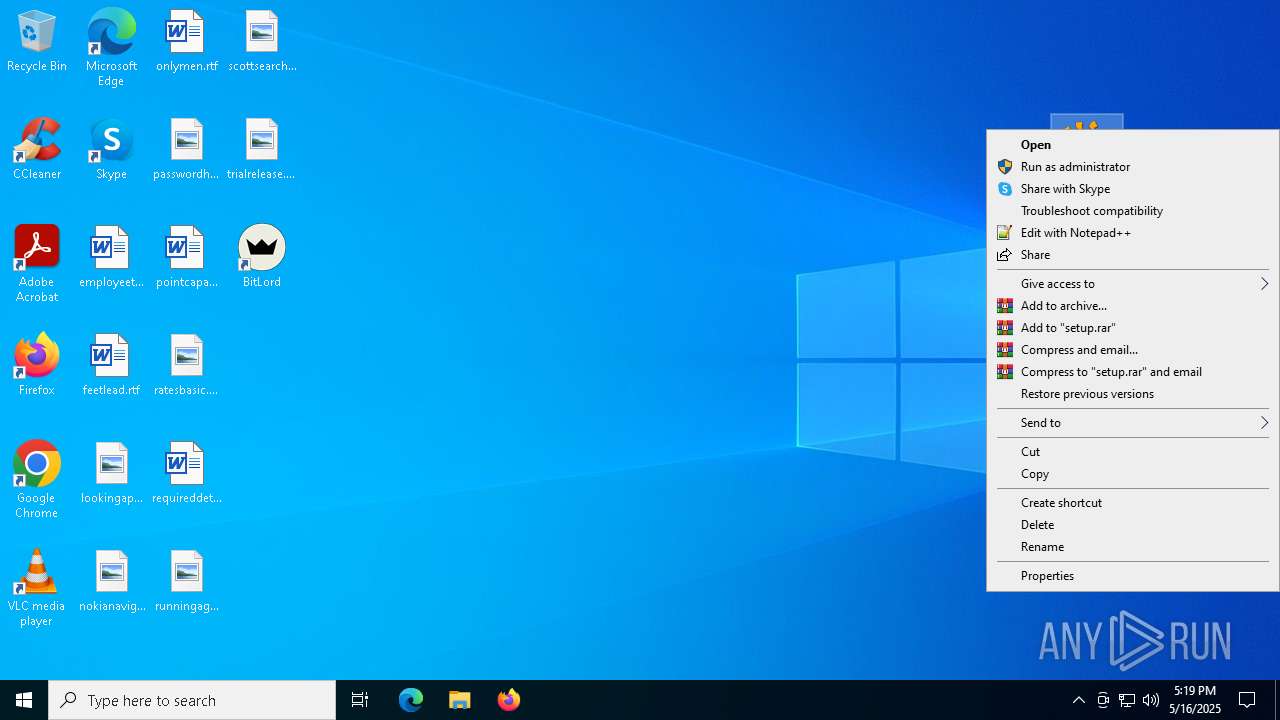
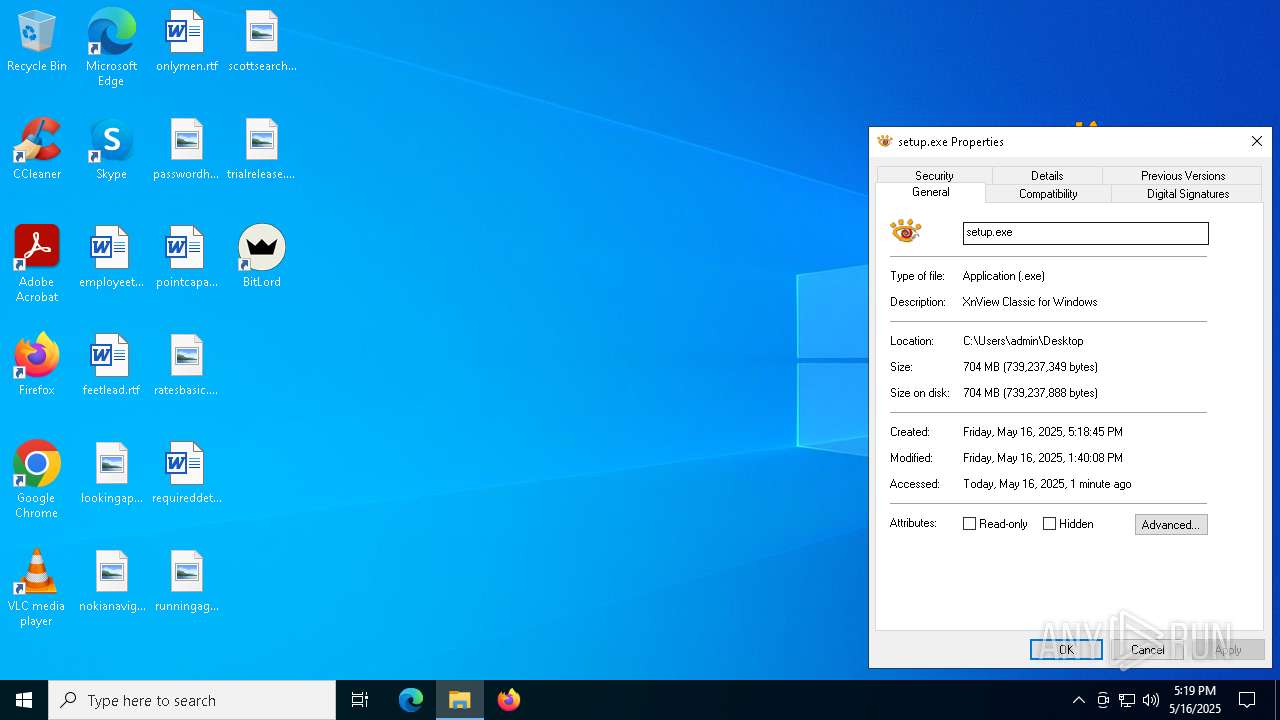
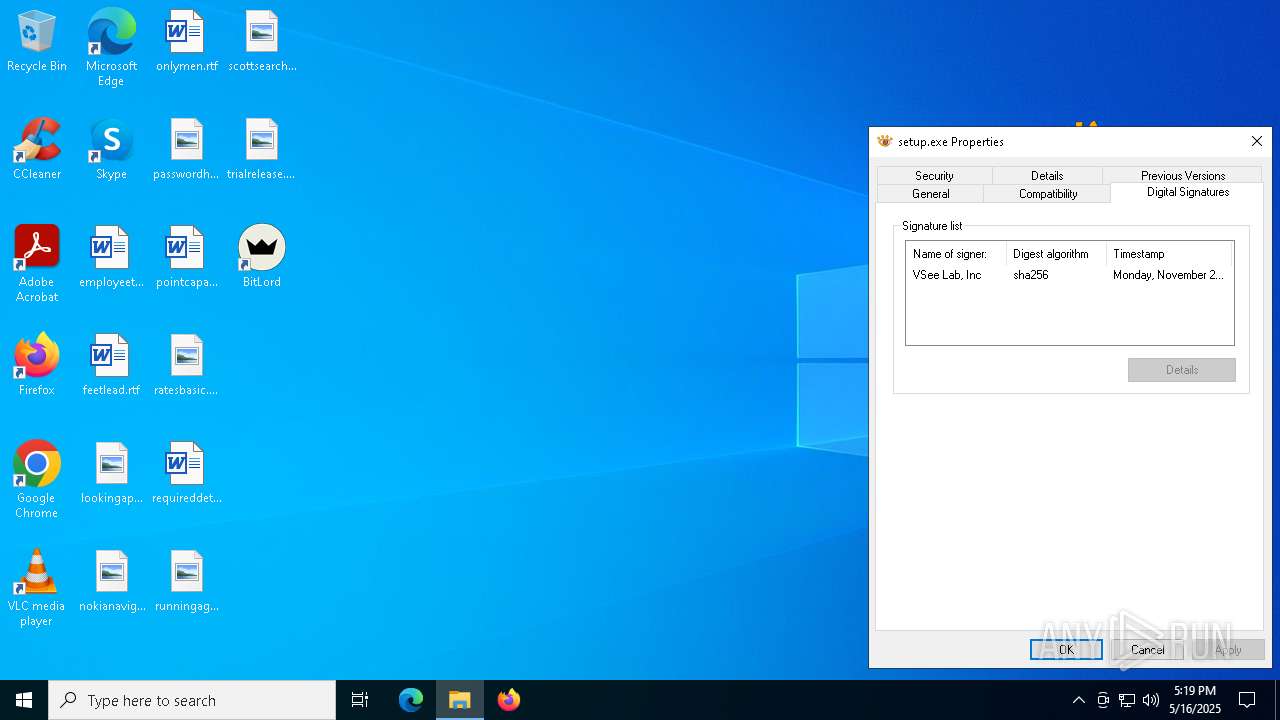
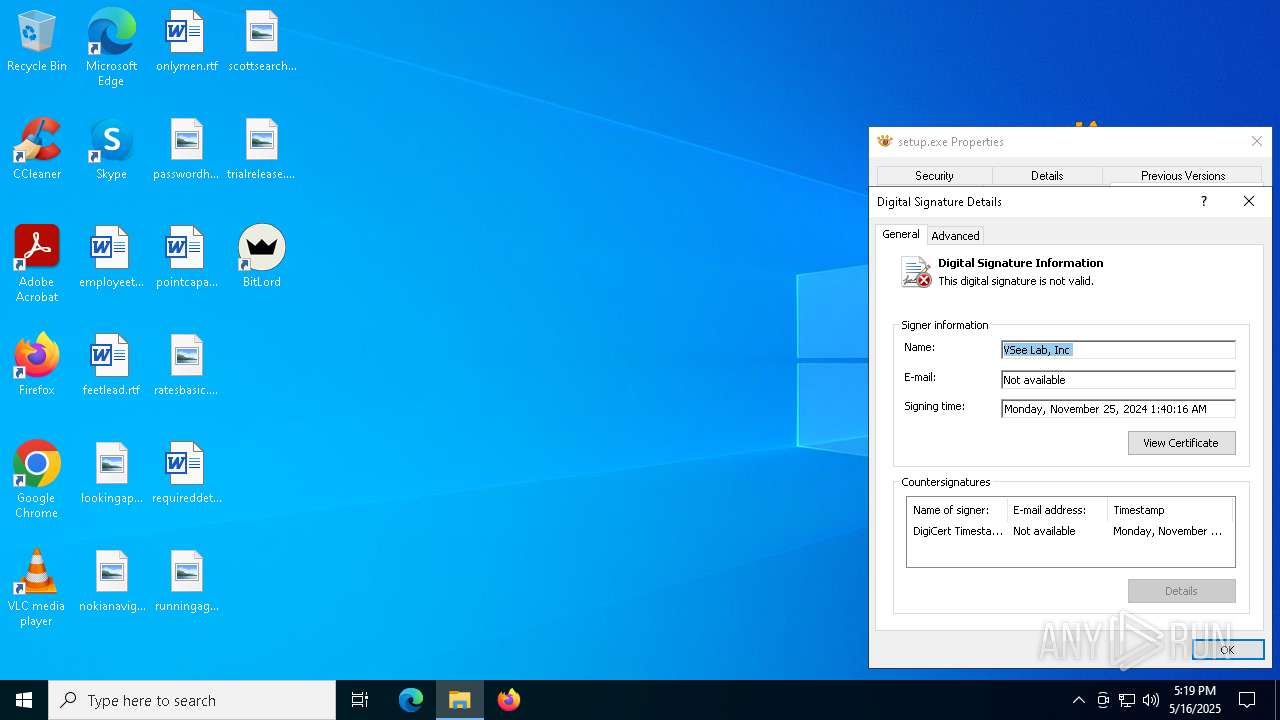
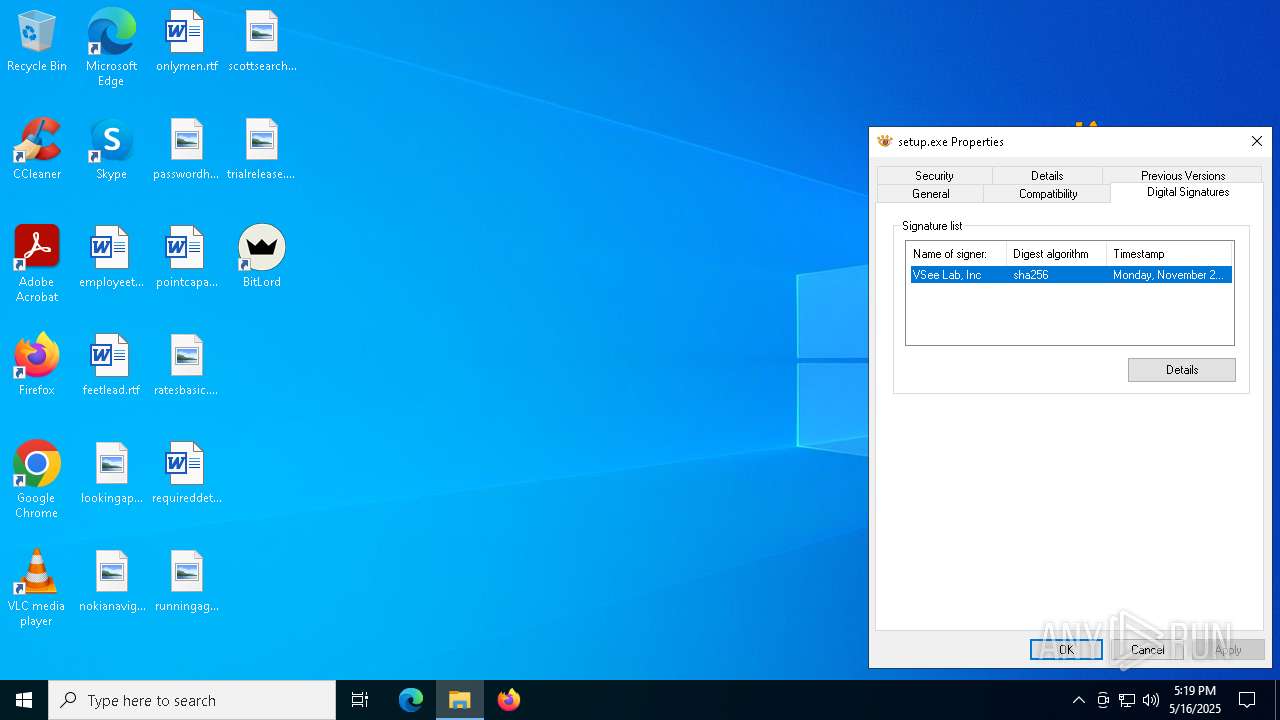
Executing a file with an untrusted certificate
- setup.exe (PID: 2772)
- hjksfyc.exe (PID: 7220)
- DistriCompiler89.exe (PID: 4180)
- DistriCompiler89.exe (PID: 6404)
- VirtuServer128.exe (PID: 8144)
- DistriCompiler89.exe (PID: 2852)
Known privilege escalation attack
- dllhost.exe (PID: 7448)
SUSPICIOUS
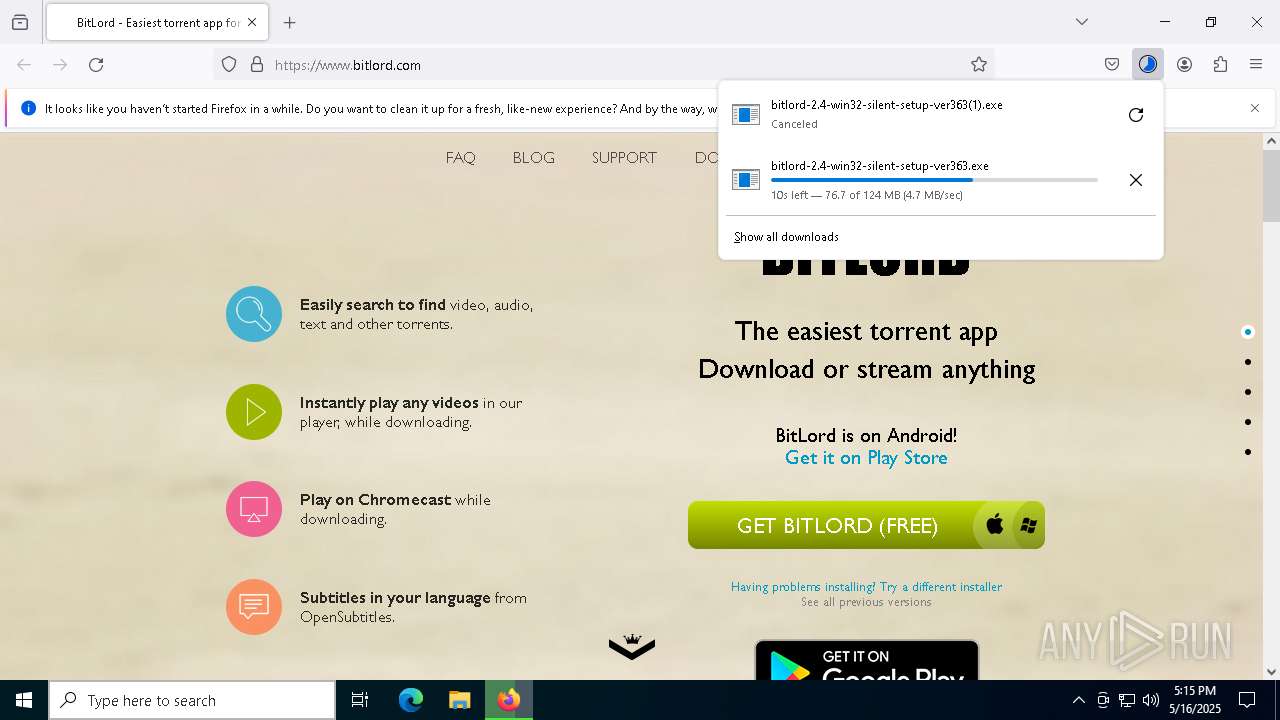
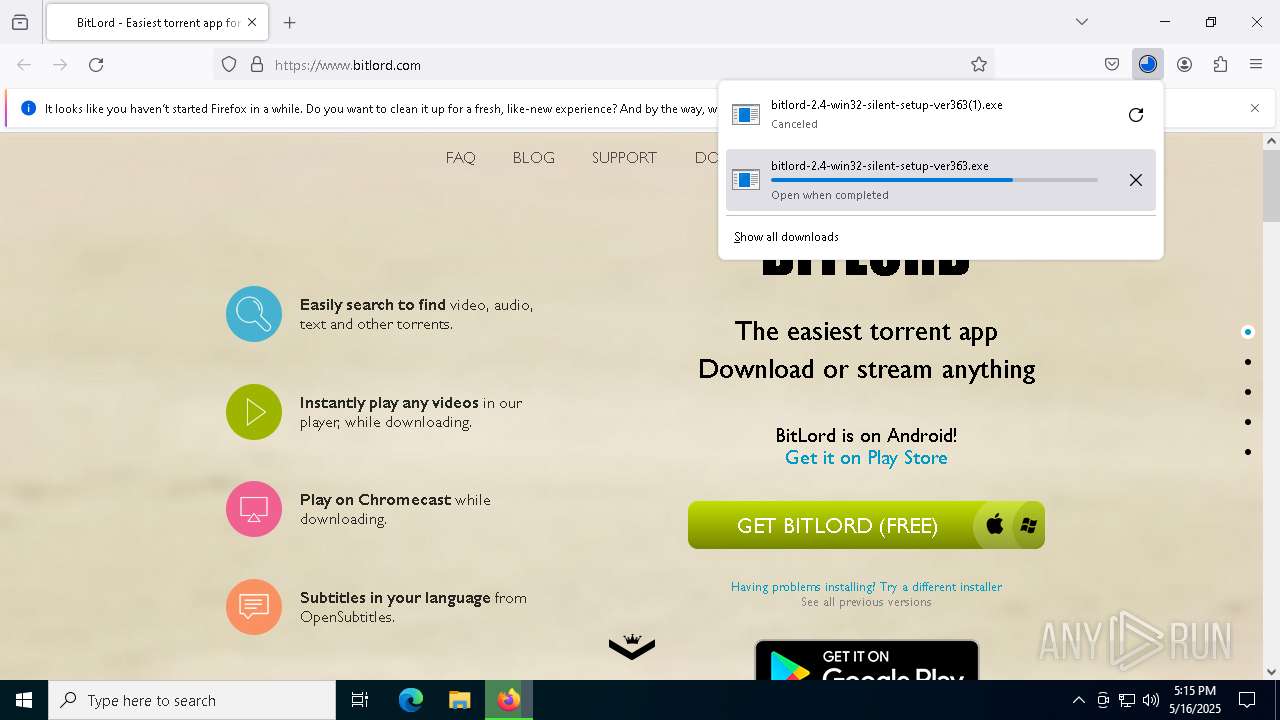
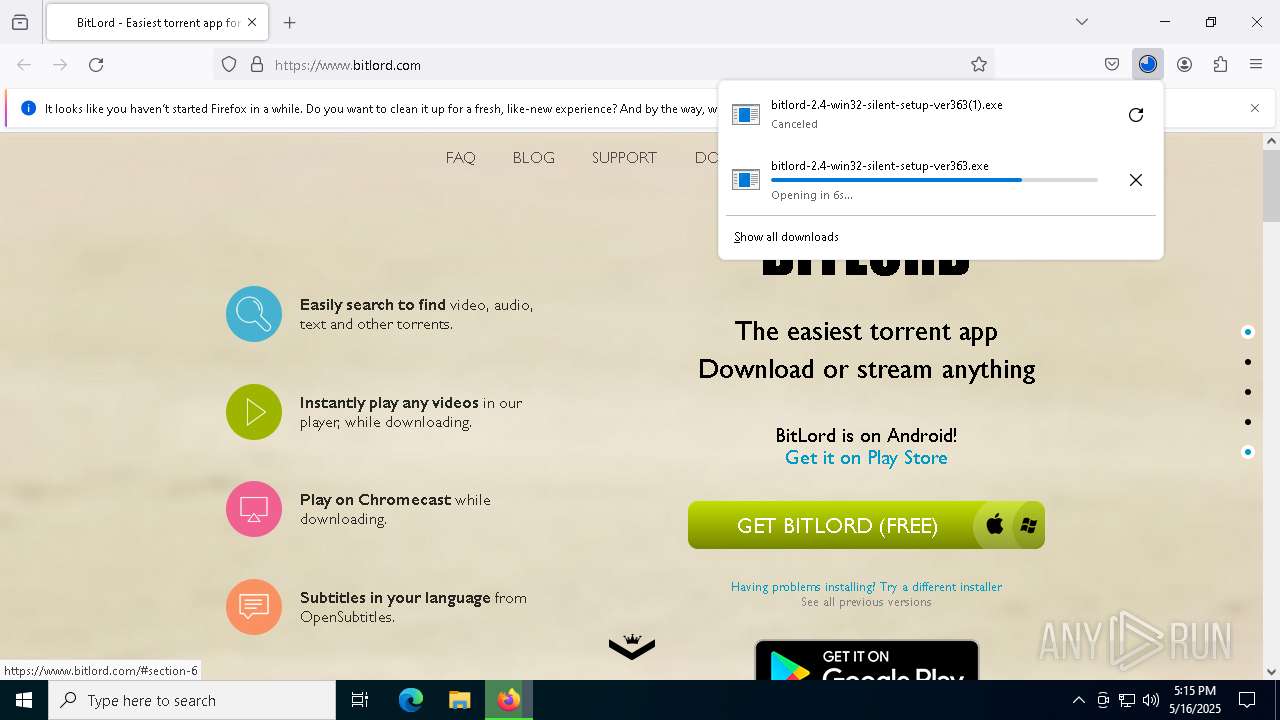
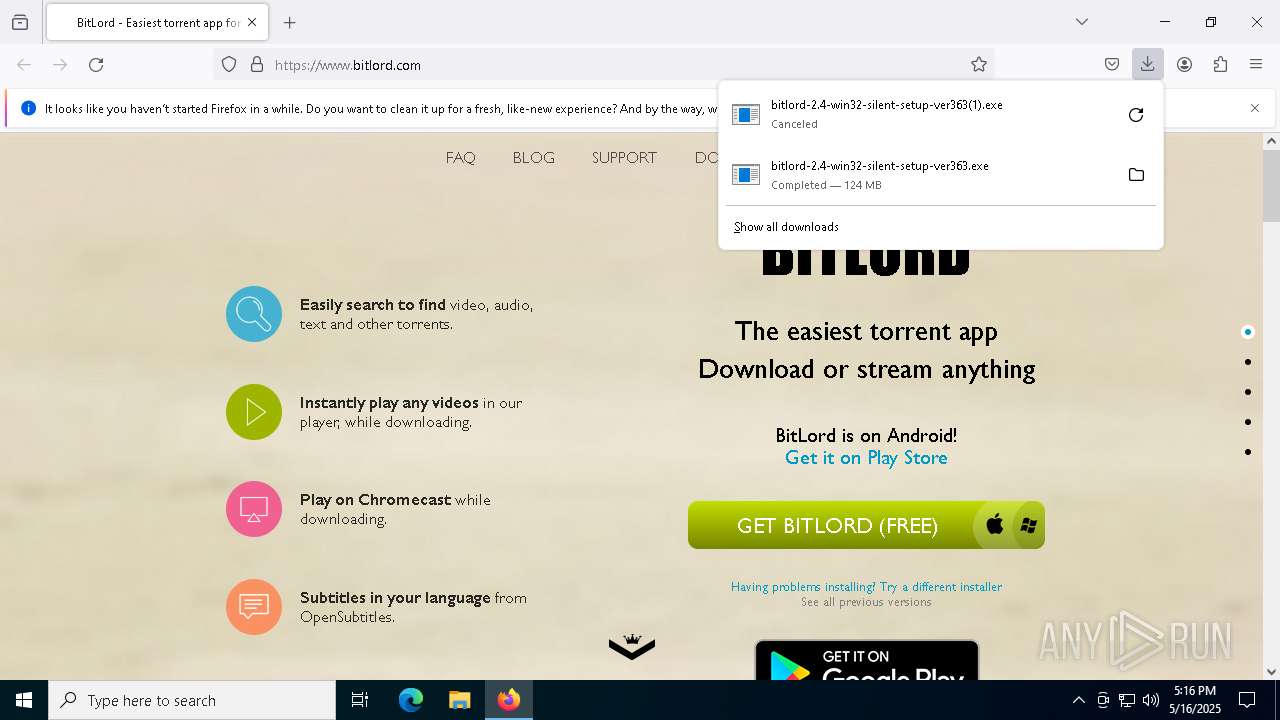
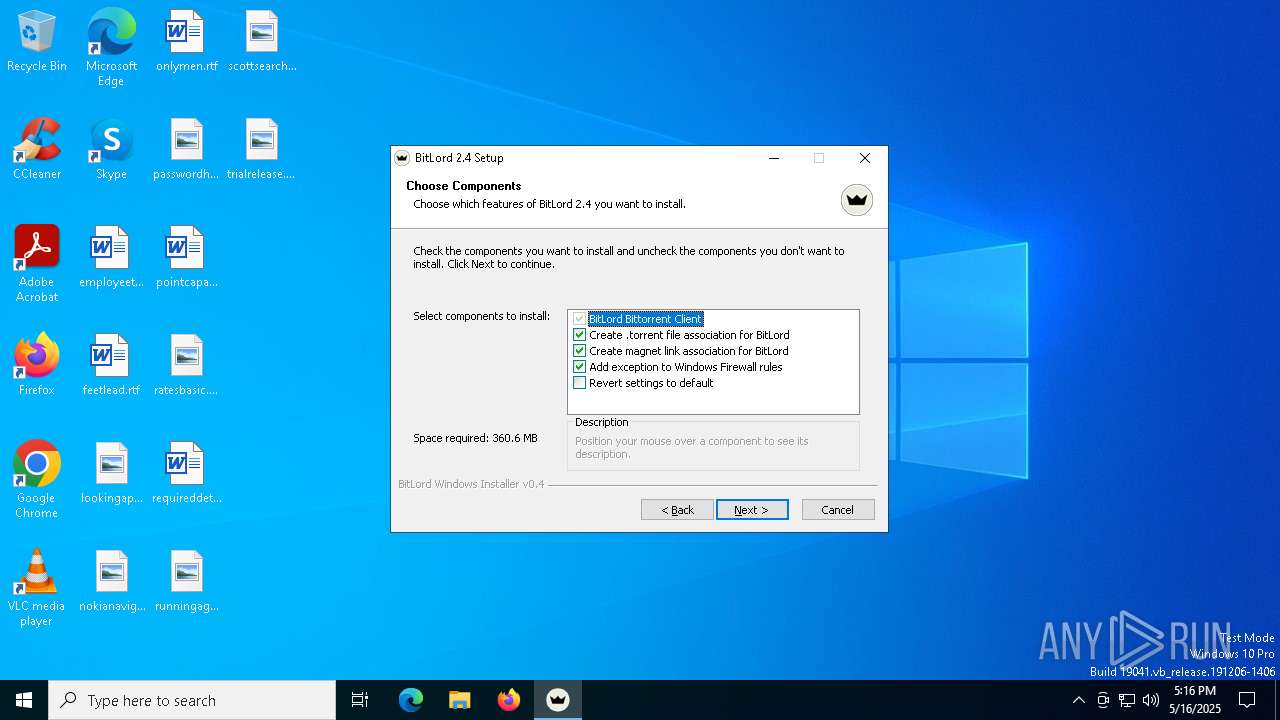
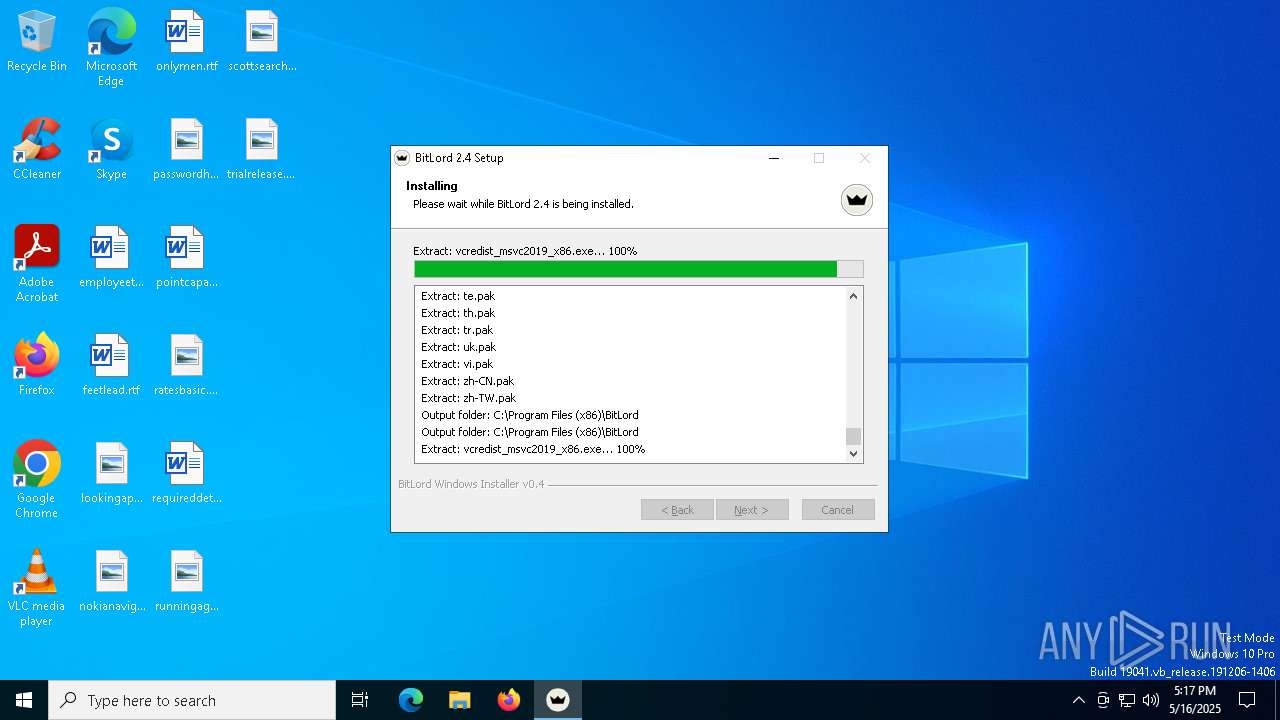
Malware-specific behavior (creating "System.dll" in Temp)
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
The process creates files with name similar to system file names
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
There is functionality for taking screenshot (YARA)
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- BitLord.exe (PID: 872)
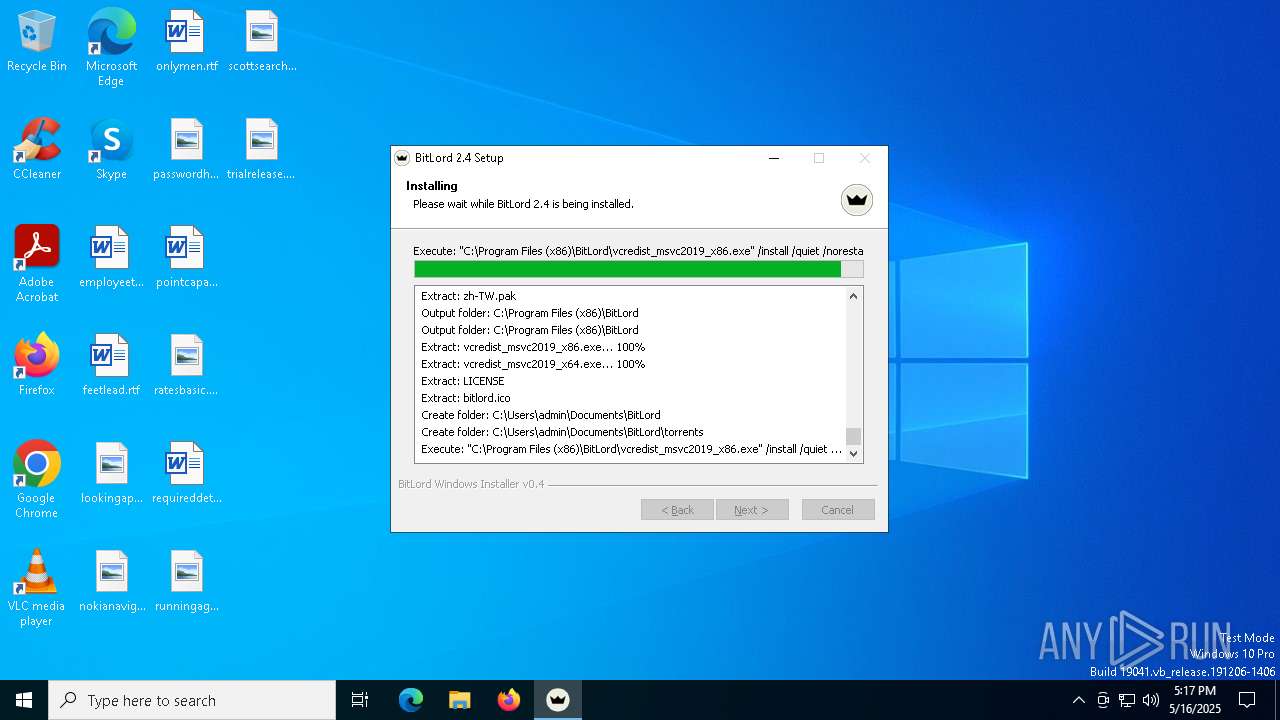
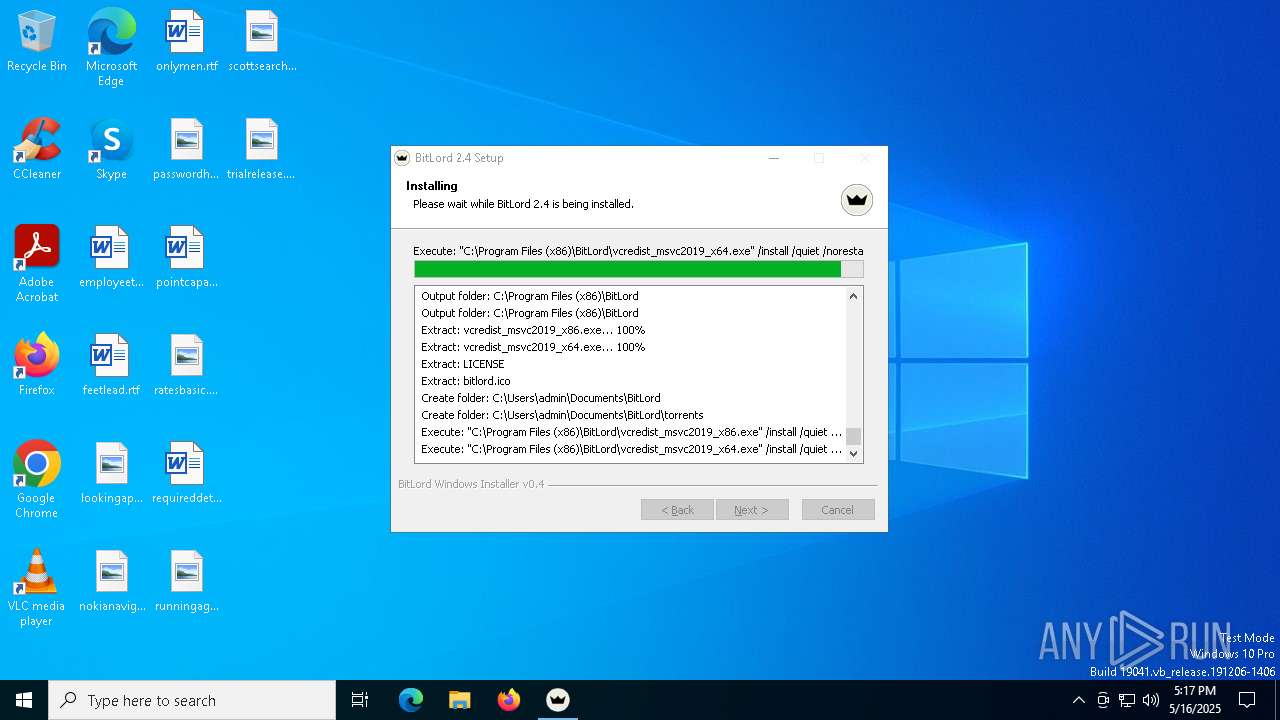
Executable content was dropped or overwritten
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x86.exe (PID: 4756)
- vcredist_msvc2019_x64.exe (PID: 7684)
- vcredist_msvc2019_x86.exe (PID: 904)
- vcredist_msvc2019_x64.exe (PID: 2552)
- hjksfyc.exe (PID: 7220)
- setup.exe (PID: 2772)
- DistriCompiler89.exe (PID: 4180)
- DistriCompiler89.exe (PID: 2852)
- DistriCompiler89.exe (PID: 6404)
Process drops legitimate windows executable
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x64.exe (PID: 7684)
- vcredist_msvc2019_x86.exe (PID: 904)
Searches for installed software
- vcredist_msvc2019_x86.exe (PID: 4756)
- vcredist_msvc2019_x64.exe (PID: 2552)
Starts a Microsoft application from unusual location
- vcredist_msvc2019_x64.exe (PID: 2552)
- vcredist_msvc2019_x86.exe (PID: 4756)
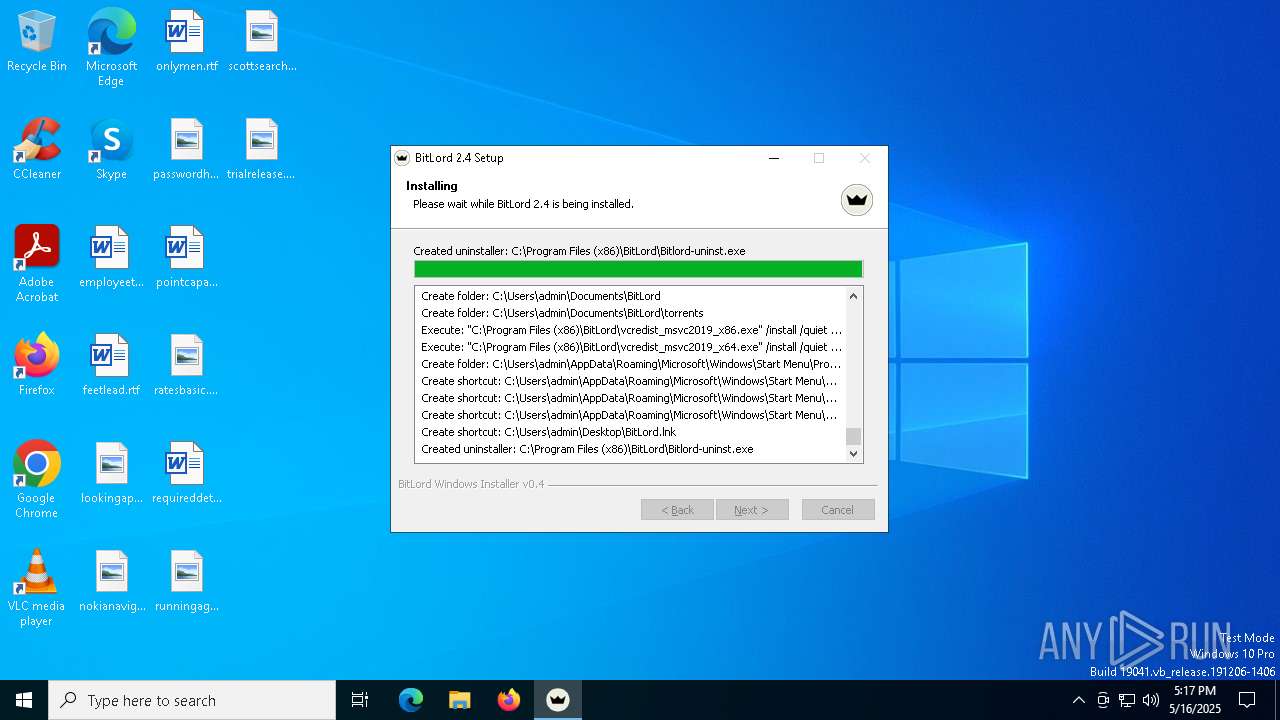
Creates a software uninstall entry
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
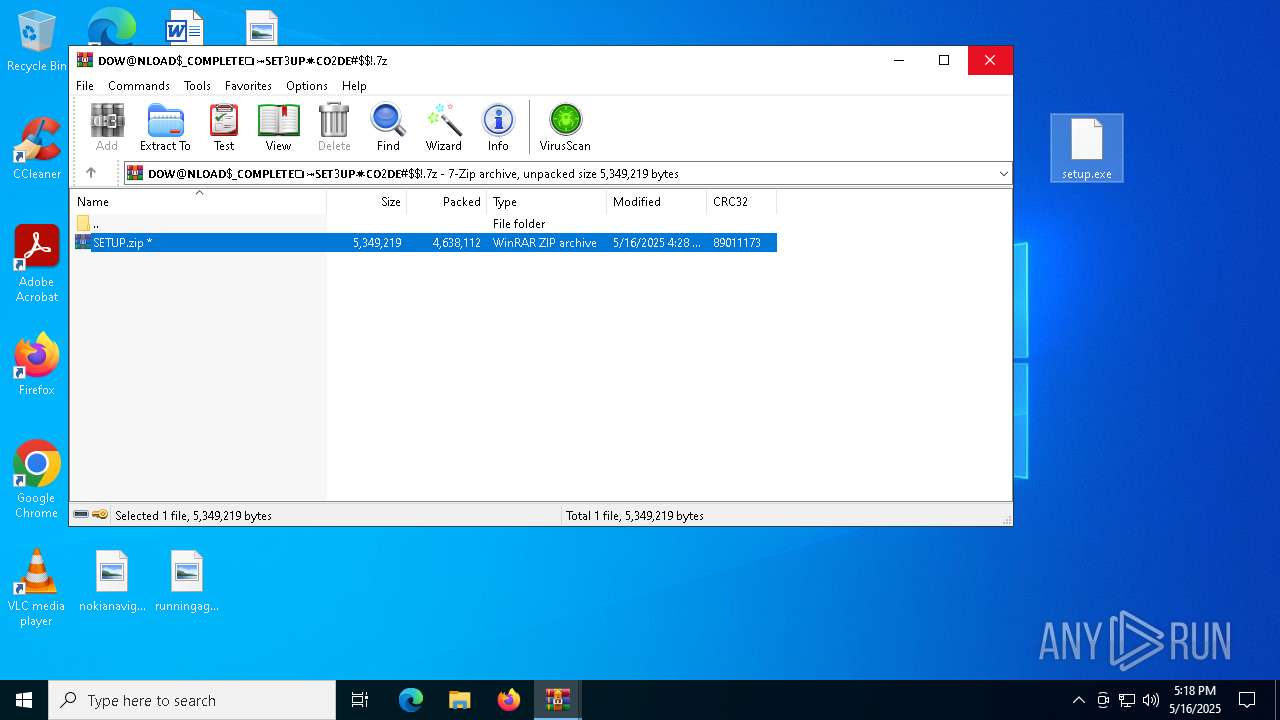
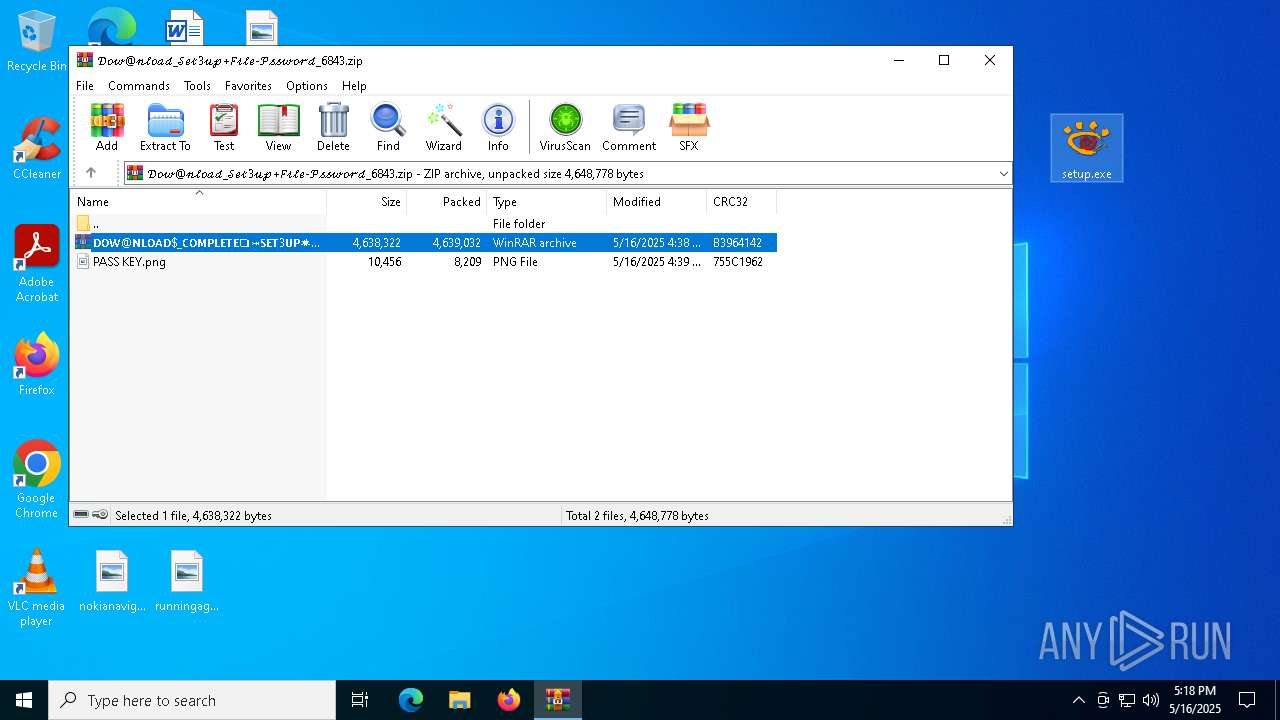
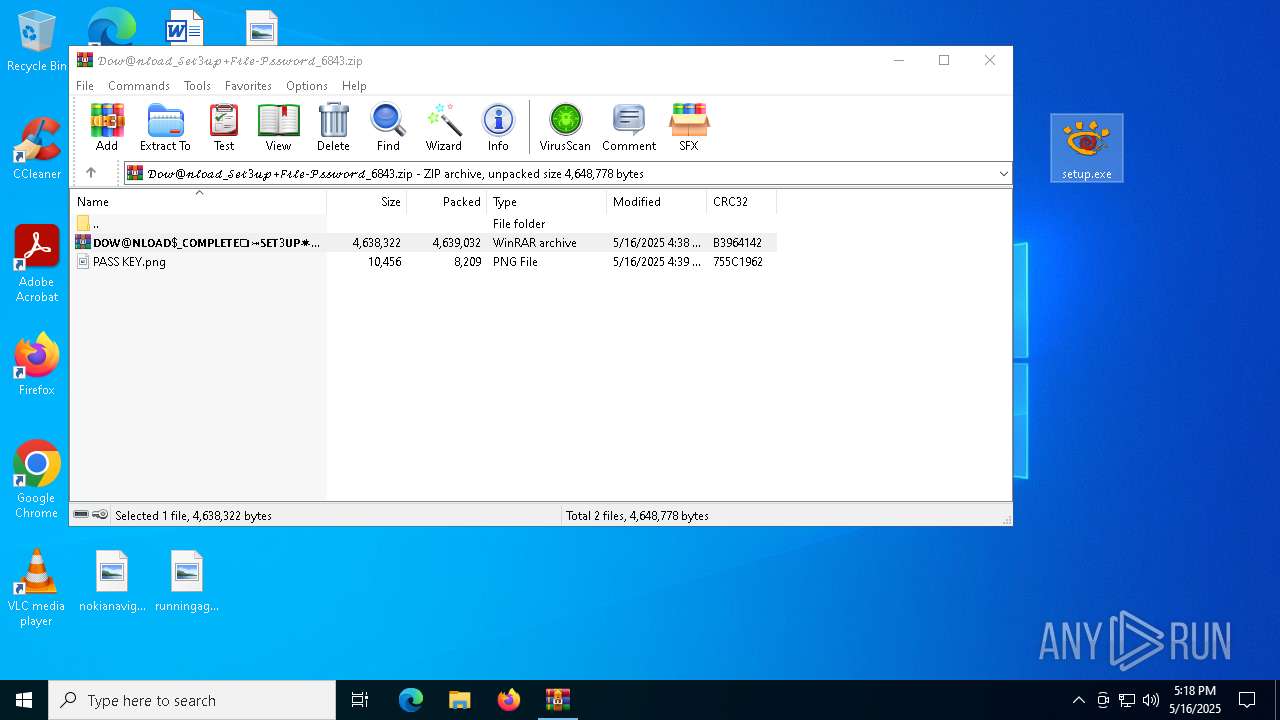
Application launched itself
- WinRAR.exe (PID: 7280)
- WinRAR.exe (PID: 5188)
Adds/modifies Windows certificates
- BitLord.exe (PID: 872)
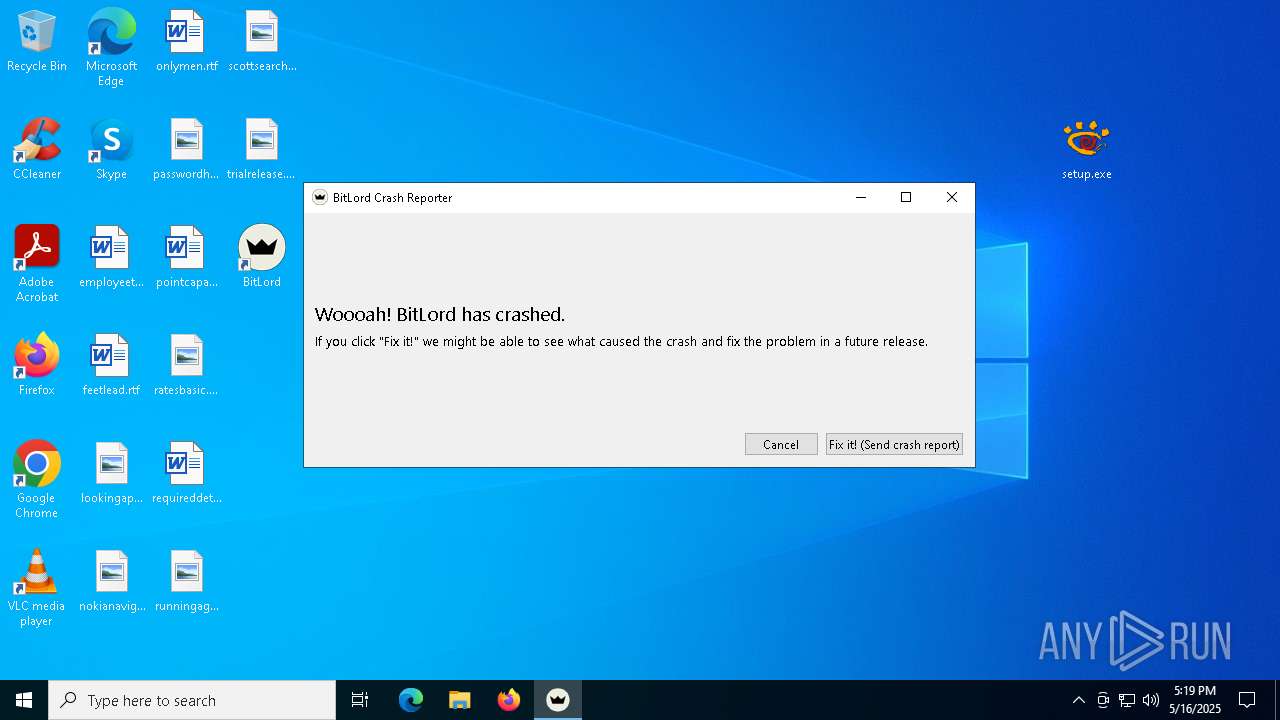
Executes application which crashes
- BitLord.exe (PID: 872)
Potential Corporate Privacy Violation
- setup.exe (PID: 2772)
Starts itself from another location
- DistriCompiler89.exe (PID: 4180)
Drops 7-zip archiver for unpacking
- DistriCompiler89.exe (PID: 2852)
INFO
Checks supported languages
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x86.exe (PID: 904)
- vcredist_msvc2019_x64.exe (PID: 7684)
- vcredist_msvc2019_x86.exe (PID: 4756)
- vcredist_msvc2019_x64.exe (PID: 2552)
- BitLord.exe (PID: 872)
- QtWebEngineProcess.exe (PID: 7884)
- QtWebEngineProcess.exe (PID: 7944)
Application launched itself
- firefox.exe (PID: 7400)
- firefox.exe (PID: 7380)
Executable content was dropped or overwritten
- firefox.exe (PID: 7400)
The sample compiled with english language support
- firefox.exe (PID: 7400)
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x86.exe (PID: 4756)
- vcredist_msvc2019_x64.exe (PID: 7684)
- vcredist_msvc2019_x86.exe (PID: 904)
- vcredist_msvc2019_x64.exe (PID: 2552)
- DistriCompiler89.exe (PID: 2852)
- DistriCompiler89.exe (PID: 6404)
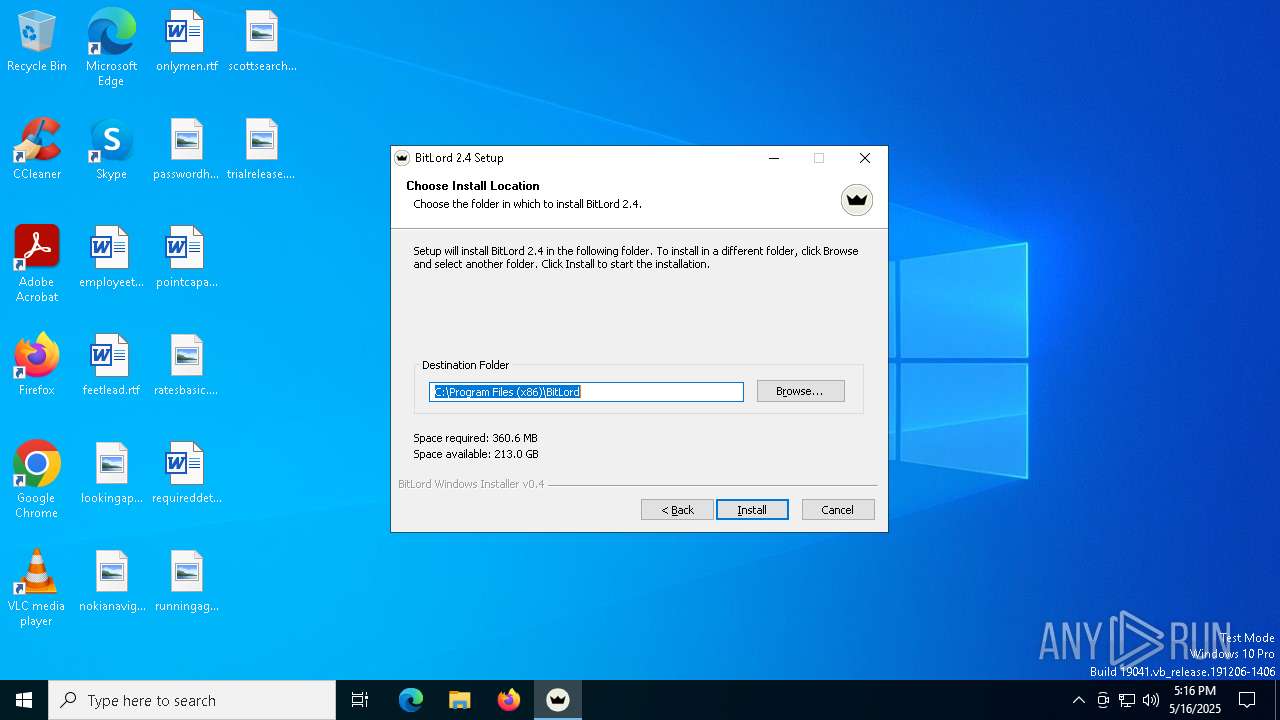
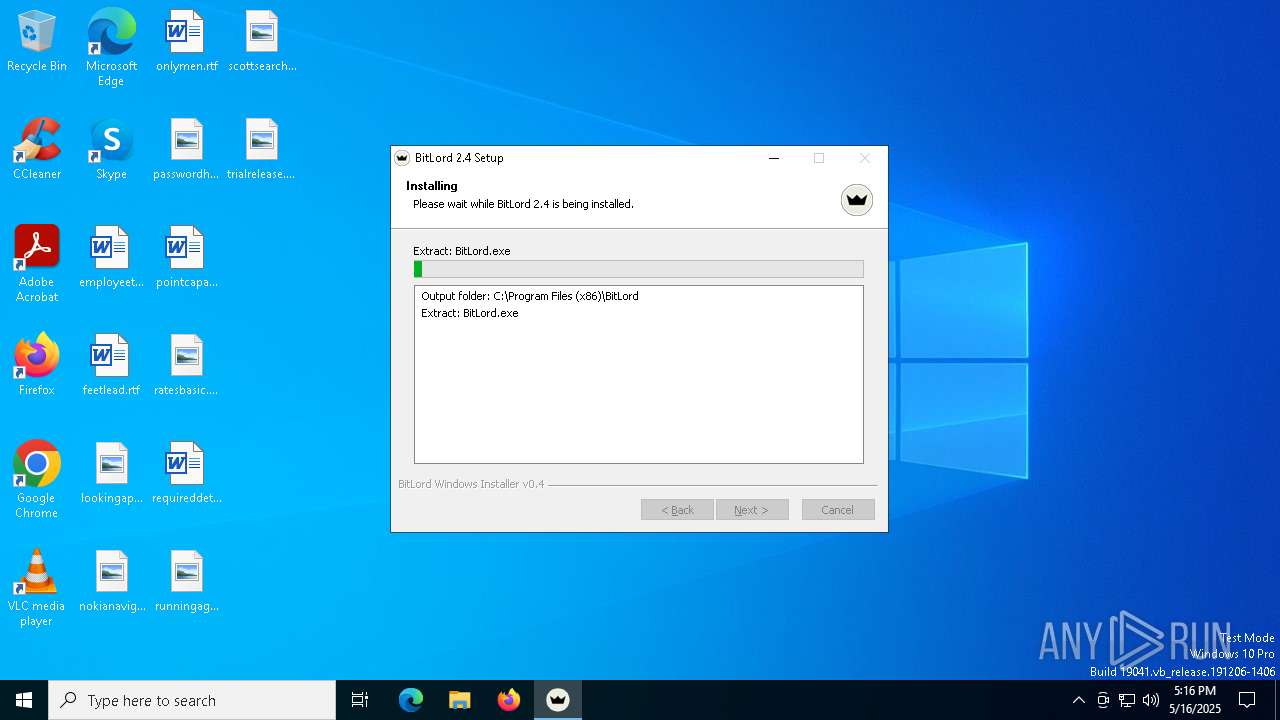
Creates files in the program directory
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
Reads the computer name
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x86.exe (PID: 4756)
- BitLord.exe (PID: 872)
- QtWebEngineProcess.exe (PID: 7884)
- vcredist_msvc2019_x64.exe (PID: 2552)
- QtWebEngineProcess.exe (PID: 7944)
Create files in a temporary directory
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- vcredist_msvc2019_x86.exe (PID: 4756)
- BitLord.exe (PID: 872)
- vcredist_msvc2019_x64.exe (PID: 2552)
Reads the software policy settings
- slui.exe (PID: 672)
- BitLord.exe (PID: 872)
Creates files or folders in the user directory
- bitlord-2.4-win32-silent-setup-ver363.exe (PID: 6708)
- explorer.exe (PID: 5492)
- BitLord.exe (PID: 872)
Qt framework related mutex has been found
- BitLord.exe (PID: 872)
Reads the machine GUID from the registry
- BitLord.exe (PID: 872)
Checks proxy server information
- BitLord.exe (PID: 872)
Process checks computer location settings
- BitLord.exe (PID: 872)
- QtWebEngineProcess.exe (PID: 7944)
- QtWebEngineProcess.exe (PID: 7884)
The process uses Lua
- BitLord.exe (PID: 872)
Executes as Windows Service
- elevation_service.exe (PID: 7664)
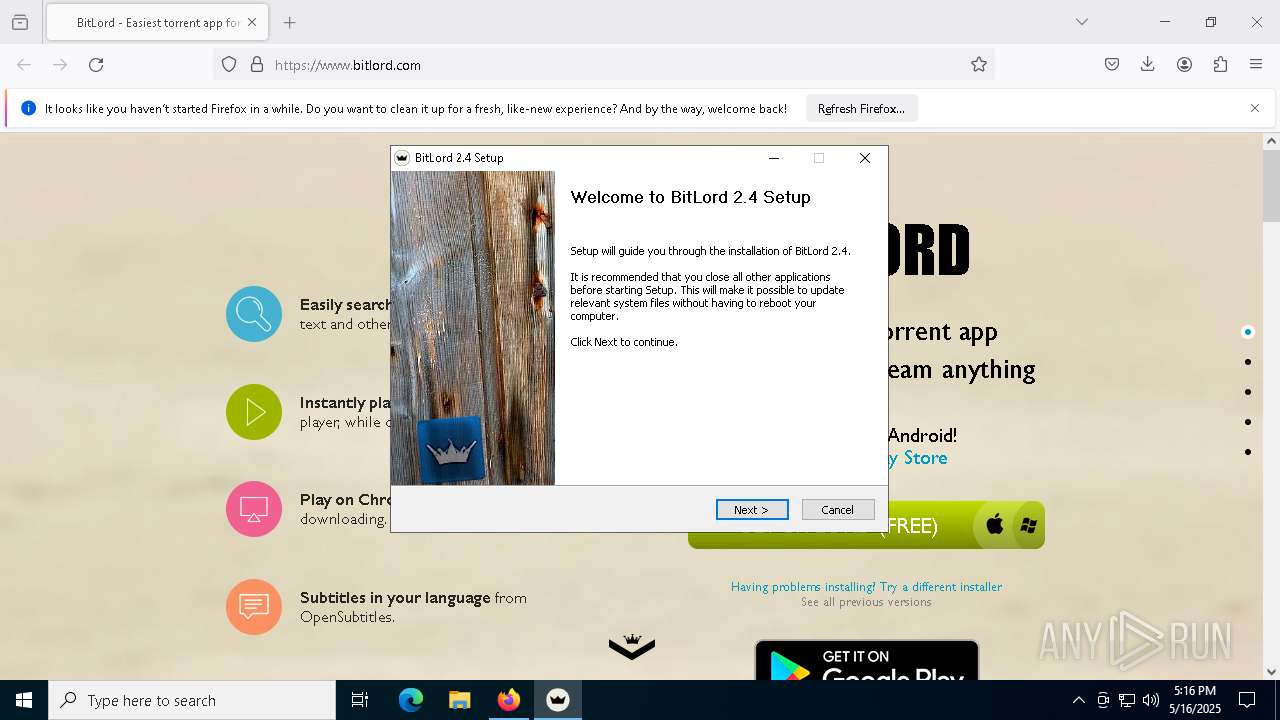
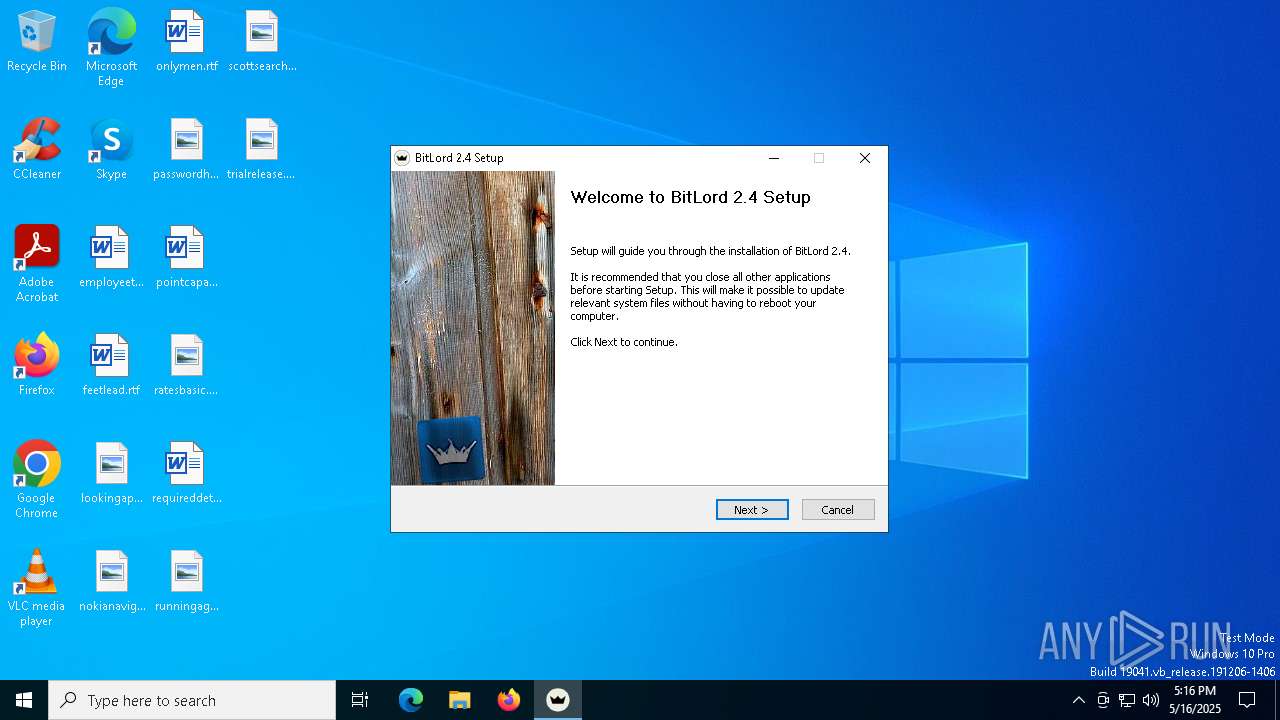
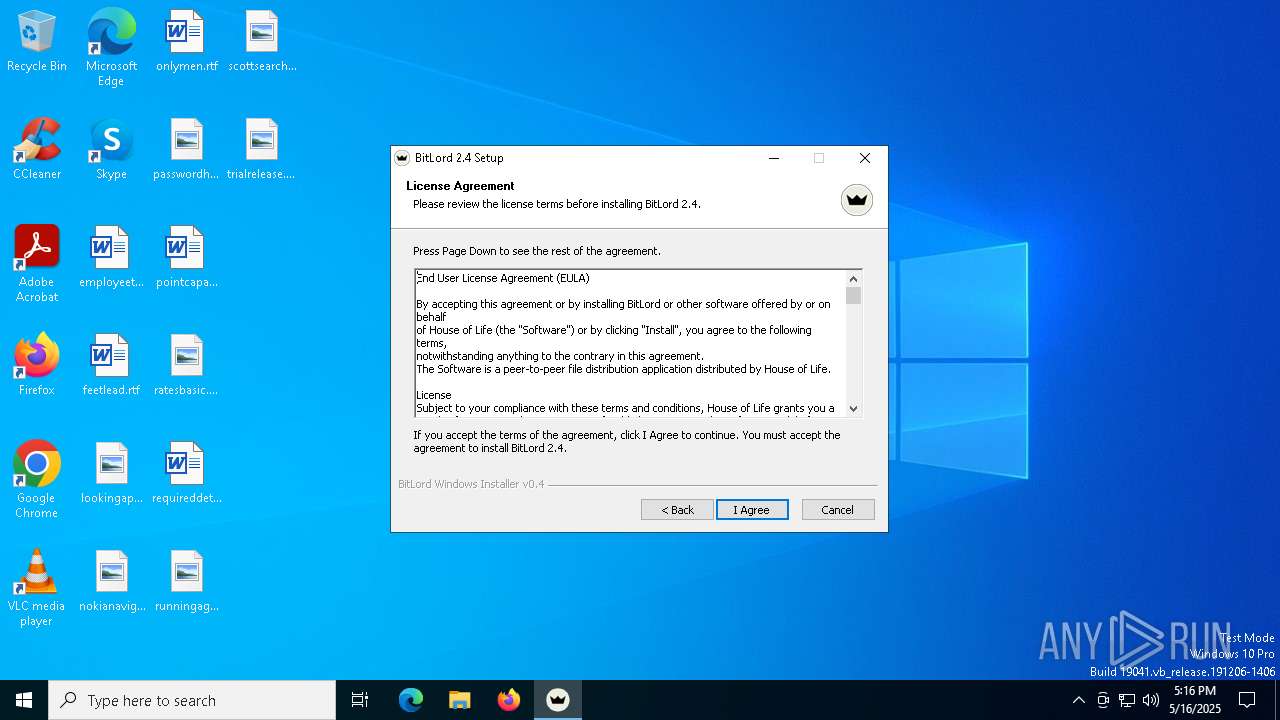
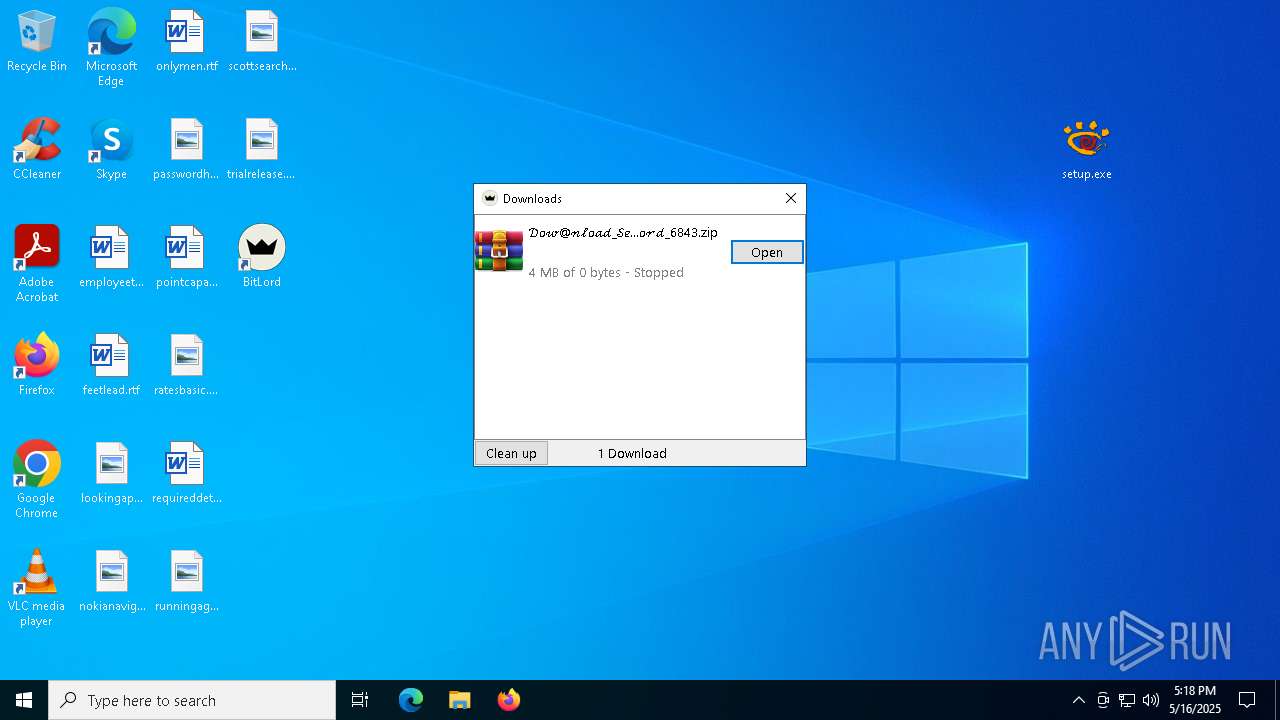
Manual execution by a user
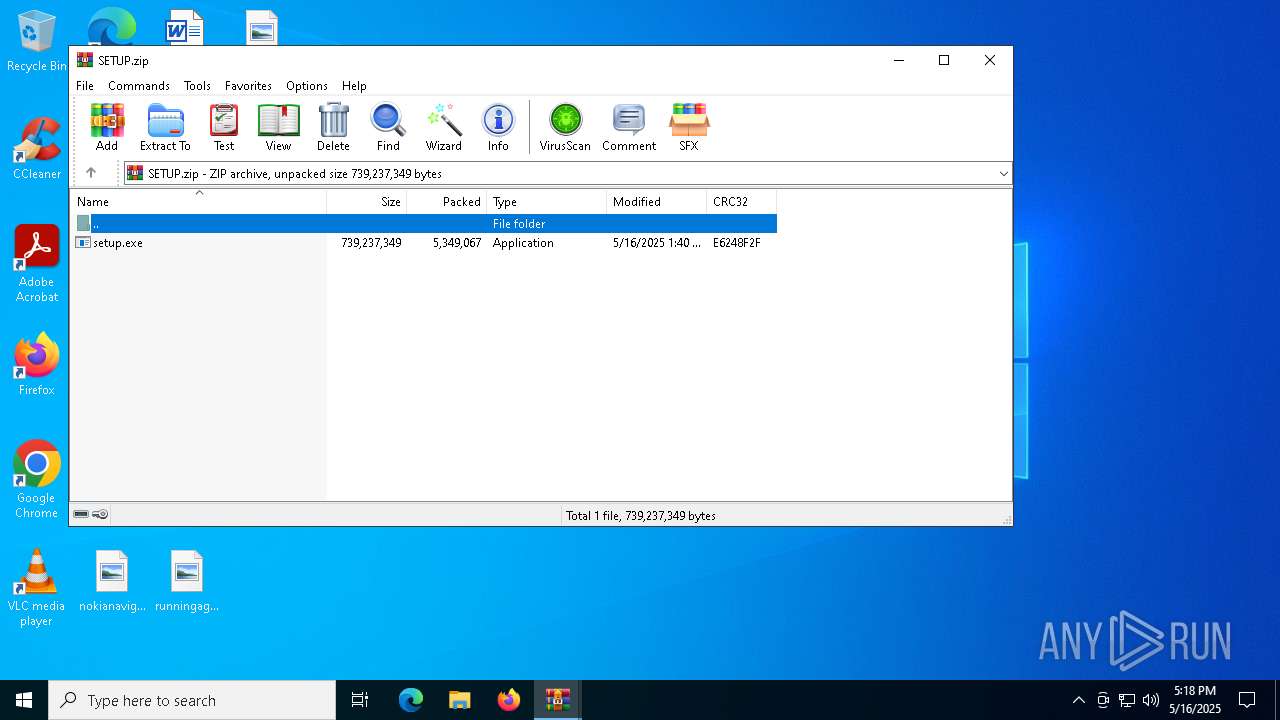
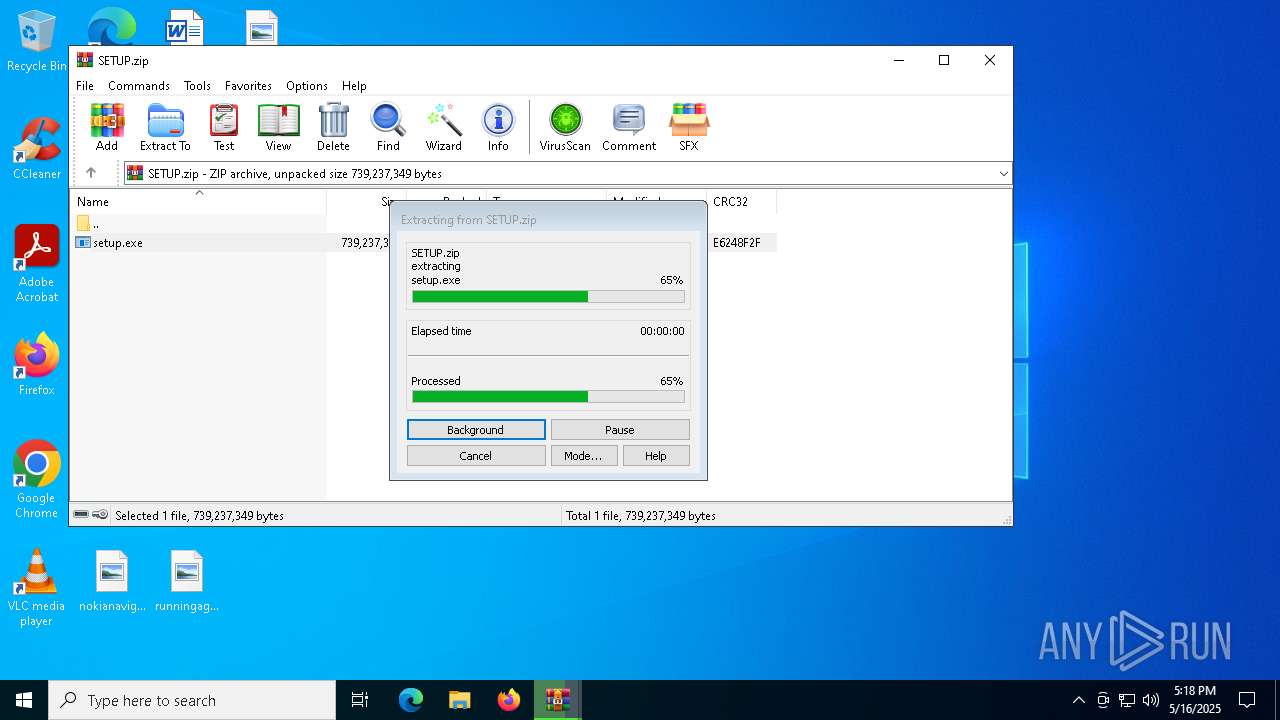
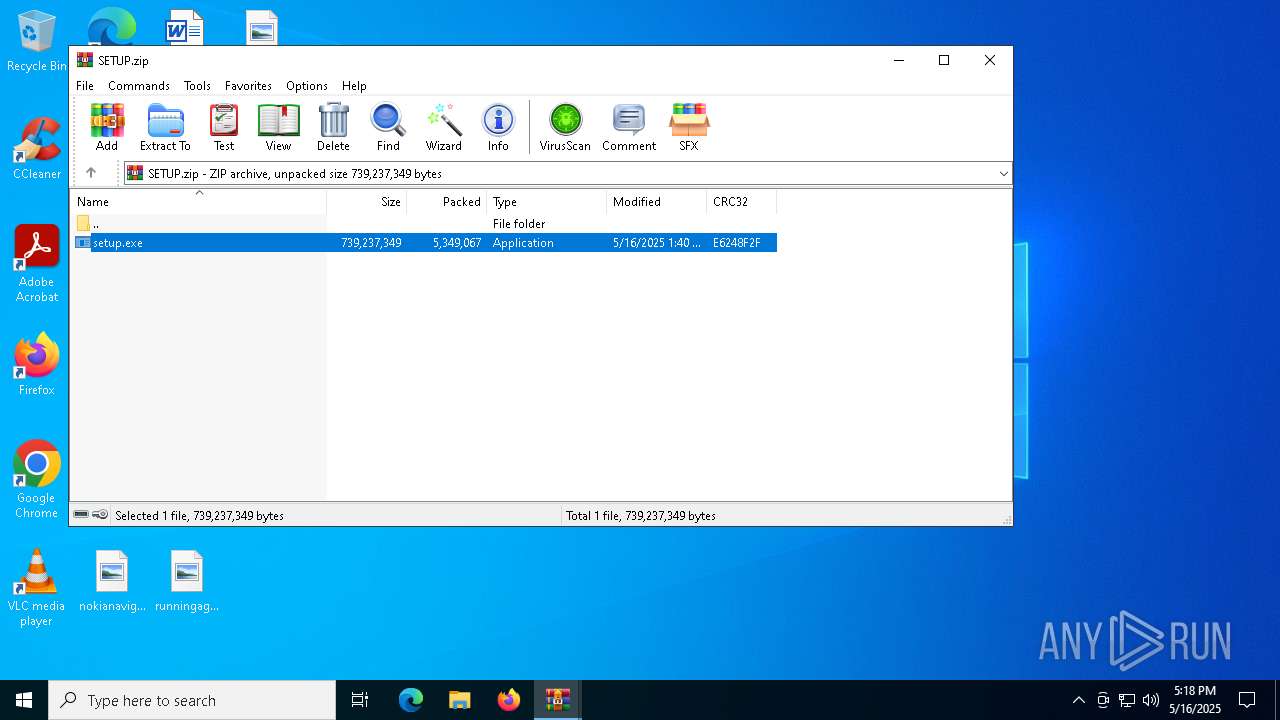
- setup.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
197
Monitored processes
57
Malicious processes
8
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 672 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7za.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files (x86)\BitLord\Bitlord.exe" | C:\Program Files (x86)\BitLord\BitLord.exe | bitlord-2.4-win32-silent-setup-ver363.exe | ||||||||||||
User: admin Company: House of Life Integrity Level: HIGH Description: BitLord Exit code: 3221227010 Version: 2.4.6-363 Modules
| |||||||||||||||
| 904 | "C:\Program Files (x86)\BitLord\vcredist_msvc2019_x86.exe" /install /quiet /norestart | C:\Program Files (x86)\BitLord\vcredist_msvc2019_x86.exe | bitlord-2.4-win32-silent-setup-ver363.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x86) - 14.24.28127 Exit code: 1638 Version: 14.24.28127.4 Modules
| |||||||||||||||
| 1180 | "C:\ProgramData\Iaclientv2\7za.exe" "C:\ProgramData\Iaclientv2\7za.exe" a -t7z "C:\Users\admin\AppData\Roaming\app.7z" C: | C:\ProgramData\Iaclientv2\7za.exe | — | DistriCompiler89.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Standalone Console Version: 18.05 | |||||||||||||||
| 1628 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2552 | "C:\WINDOWS\Temp\{23AB9EFD-5E71-467D-8C49-0765B19D7FBB}\.cr\vcredist_msvc2019_x64.exe" -burn.clean.room="C:\Program Files (x86)\BitLord\vcredist_msvc2019_x64.exe" -burn.filehandle.attached=560 -burn.filehandle.self=668 /install /quiet /norestart | C:\Windows\Temp\{23AB9EFD-5E71-467D-8C49-0765B19D7FBB}\.cr\vcredist_msvc2019_x64.exe | vcredist_msvc2019_x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015-2019 Redistributable (x64) - 14.24.28127 Exit code: 1638 Version: 14.24.28127.4 Modules
| |||||||||||||||
| 2656 | "C:\Program Files (x86)\BitLord\QtWebEngineProcess.exe" --type=renderer --disable-speech-api --enable-threaded-compositing --enable-features=NetworkServiceInProcess,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,InstalledApp,PictureInPicture,WebOTP,WebPayments,WebUSB --disable-gpu-compositing --lang=en --webengine-schemes=qrc:sV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=2988 /prefetch:1 | C:\Program Files (x86)\BitLord\QtWebEngineProcess.exe | — | BitLord.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: LOW Description: Qt QtWebEngineProcess Exit code: 0 Version: 6.2.4.0 Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\Desktop\setup.exe" | C:\Users\admin\Desktop\setup.exe | explorer.exe | ||||||||||||
User: admin Company: XnView, http://www.xnview.com Integrity Level: MEDIUM Description: XnView Classic for Windows Exit code: 0 Version: 2.52.0 Modules
| |||||||||||||||
| 2852 | C:\ProgramData\Iaclientv2\DistriCompiler89.exe | C:\ProgramData\Iaclientv2\DistriCompiler89.exe | DistriCompiler89.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
48 817
Read events
48 545
Write events
247
Delete events
25
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040264 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppBadgeUpdated |
| Operation: | write | Name: | 308046B0AF4A39CB |
Value: 21 | |||
| (PID) Process: | (7400) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (7400) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000070270 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:0000000000040264 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6708) bitlord-2.4-win32-silent-setup-ver363.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BitLord |
| Operation: | write | Name: | DisplayName |
Value: BitLord 2.4 | |||
| (PID) Process: | (6708) bitlord-2.4-win32-silent-setup-ver363.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BitLord |
| Operation: | write | Name: | DisplayVersion |
Value: 2.4.6-363 | |||
| (PID) Process: | (6708) bitlord-2.4-win32-silent-setup-ver363.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BitLord |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files (x86)\BitLord\Bitlord-uninst.exe | |||
| (PID) Process: | (6708) bitlord-2.4-win32-silent-setup-ver363.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\BitLord |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files (x86)\BitLord\bitlord.ico | |||
Executable files
450
Suspicious files
420
Text files
122
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7400 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:2C99A16AED3906D92FFE3EF1808E2753 | SHA256:08412578CC3BB4922388F8FF8C23962F616B69A1588DA720ADE429129C73C452 | |||
| 7400 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
32
DNS requests
103
Threats
22
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.158:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7400 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://o.pki.goog/s/wr3/FIY | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
7400 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
7400 | firefox.exe | POST | 200 | 142.250.185.67:80 | http://o.pki.goog/we2 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7400 | firefox.exe | 172.67.212.154:443 | www.bitlord.com | CLOUDFLARENET | US | whitelisted |
7400 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
7400 | firefox.exe | 34.36.137.203:443 | contile.services.mozilla.com | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
7400 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | unknown |
7400 | firefox.exe | 142.250.185.138:443 | safebrowsing.googleapis.com | — | — | unknown |
7400 | firefox.exe | 142.250.185.67:80 | o.pki.goog | GOOGLE | US | unknown |
7400 | firefox.exe | 184.24.77.62:80 | r11.o.lencr.org | Akamai International B.V. | DE | unknown |
7400 | firefox.exe | 34.107.243.93:443 | push.services.mozilla.com | GOOGLE | US | unknown |
7400 | firefox.exe | 34.107.152.202:443 | firefox-settings-attachments.cdn.mozilla.net | GOOGLE | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
www.bitlord.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |