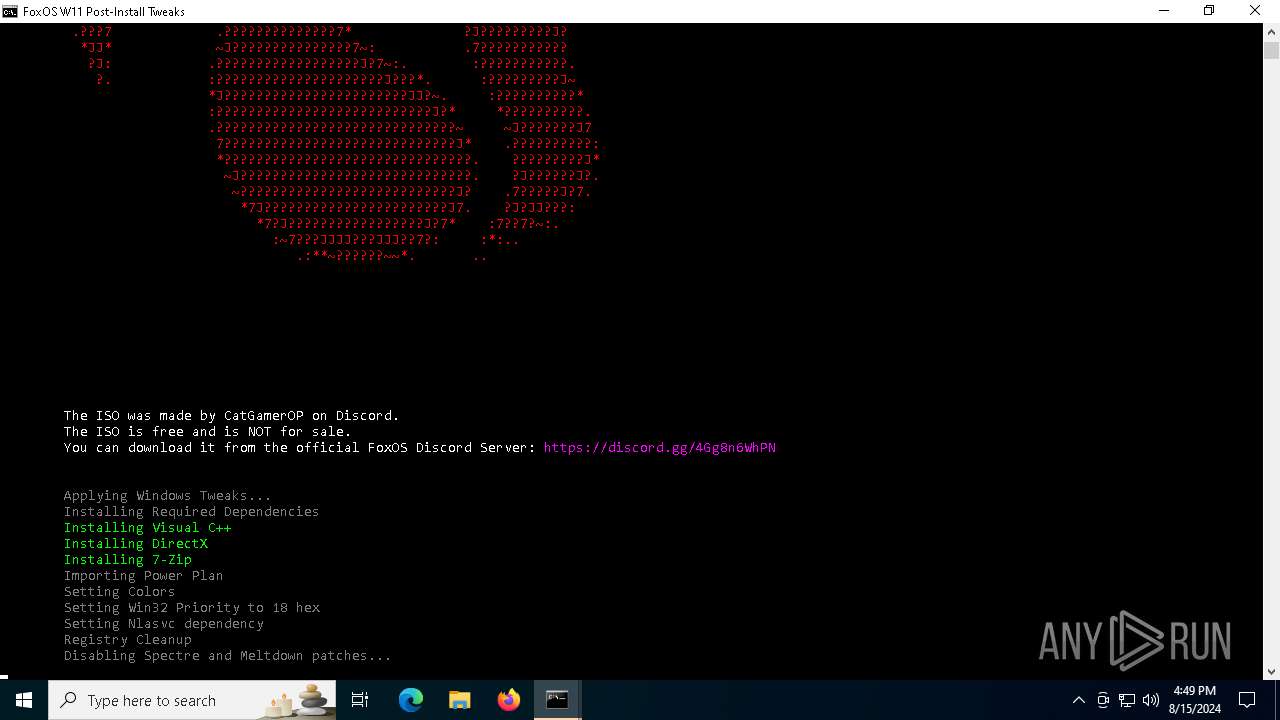
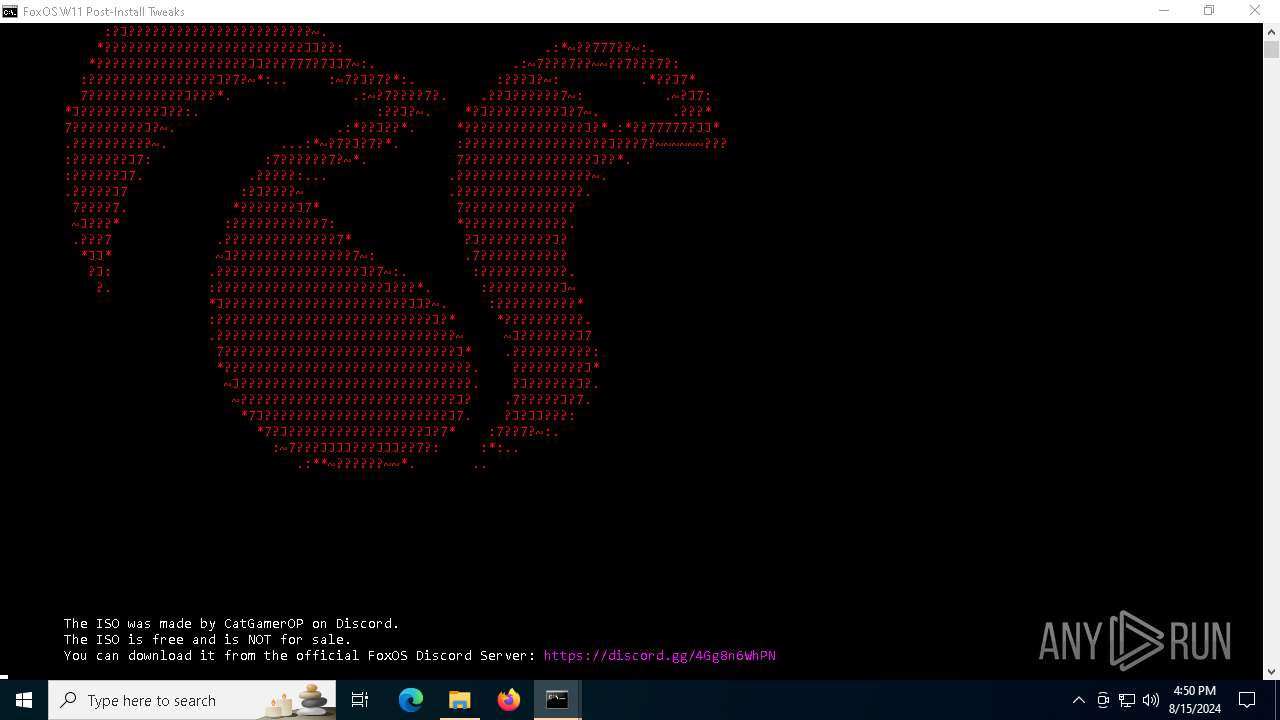
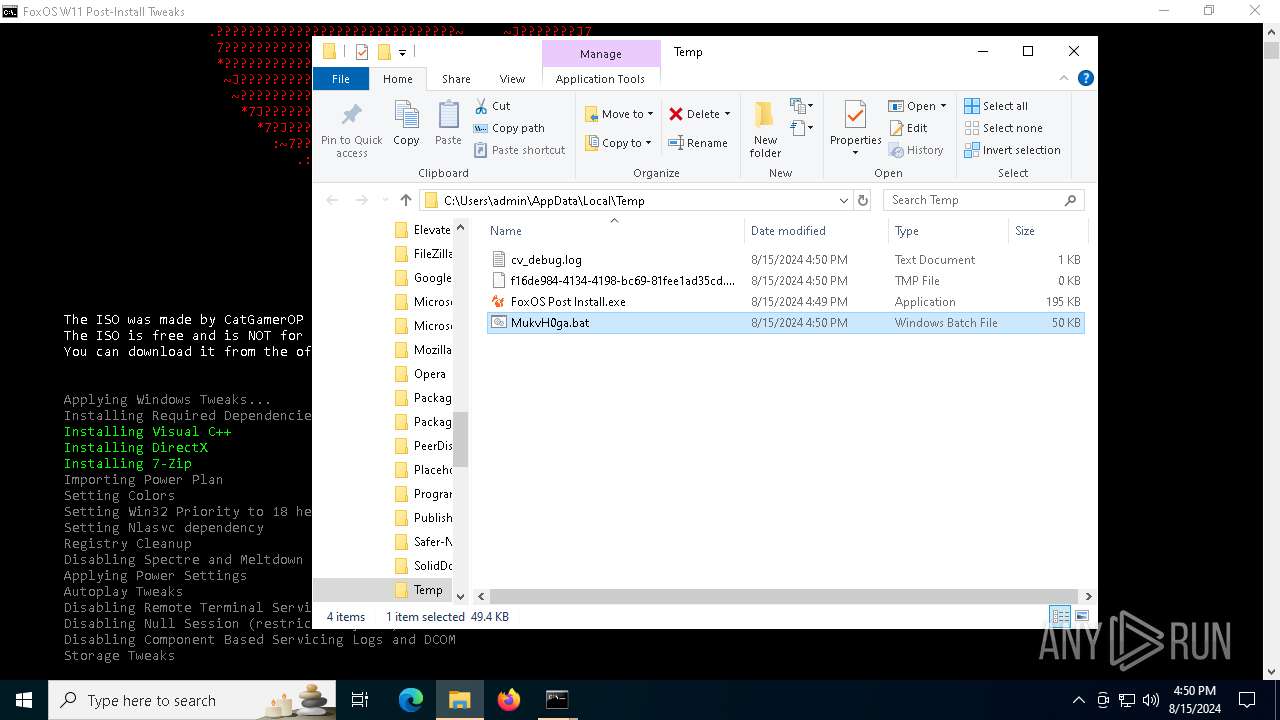
| File name: | FoxOS Post Install.exe |
| Full analysis: | https://app.any.run/tasks/ecb9496a-4ba7-402f-b972-66ea34a72da4 |
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2024, 16:49:03 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | E07A79DFB6409358299B6952600F2552 |
| SHA1: | B73413C974AC6A74B04954FCED09648A2B4DA5A3 |
| SHA256: | 5F69BC66B594F45ABD8C36F4B32CCD4C27B5E3D909927C61E4D0BB29553D8E92 |
| SSDEEP: | 768:SJFmbYc2FNAQBA9WFydBmu0zbbj0mxds+sY3z:SJFmyNAQBCyLj0m51 |
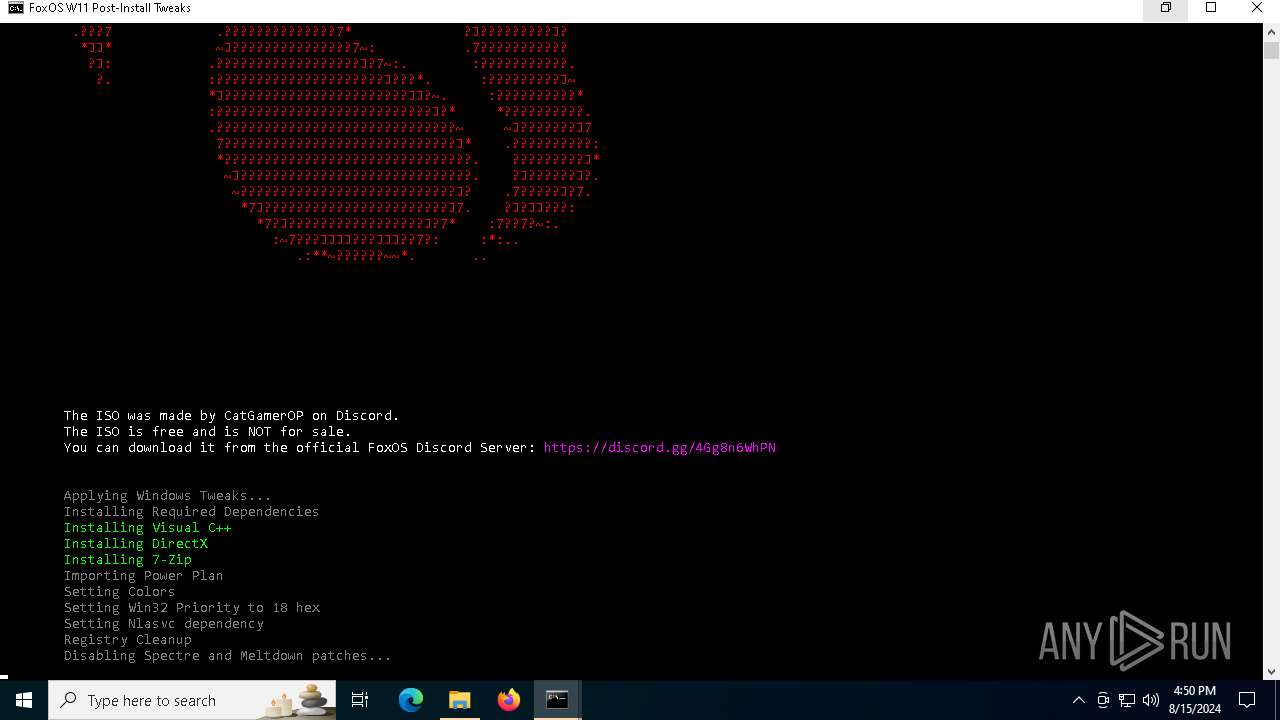
MALICIOUS
Using BCDEDIT.EXE to modify recovery options
- cmd.exe (PID: 7736)
Changes powershell execution policy (Unrestricted)
- cmd.exe (PID: 7736)
SUSPICIOUS
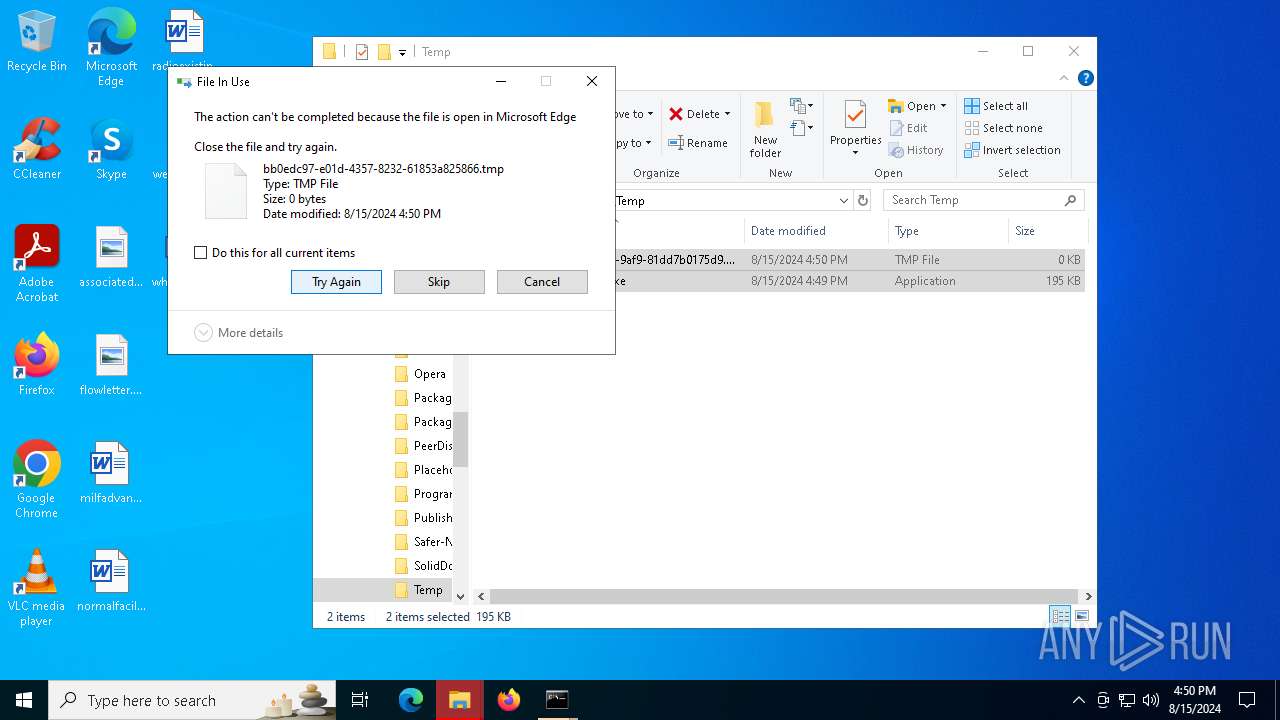
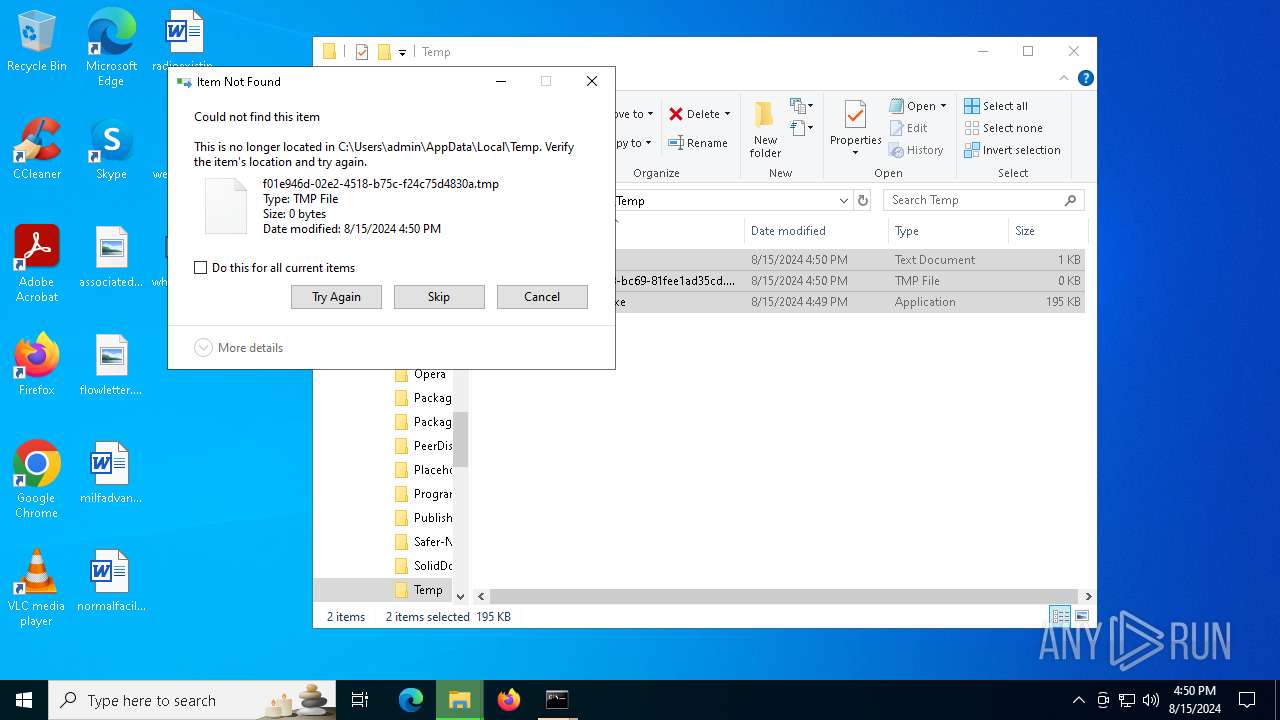
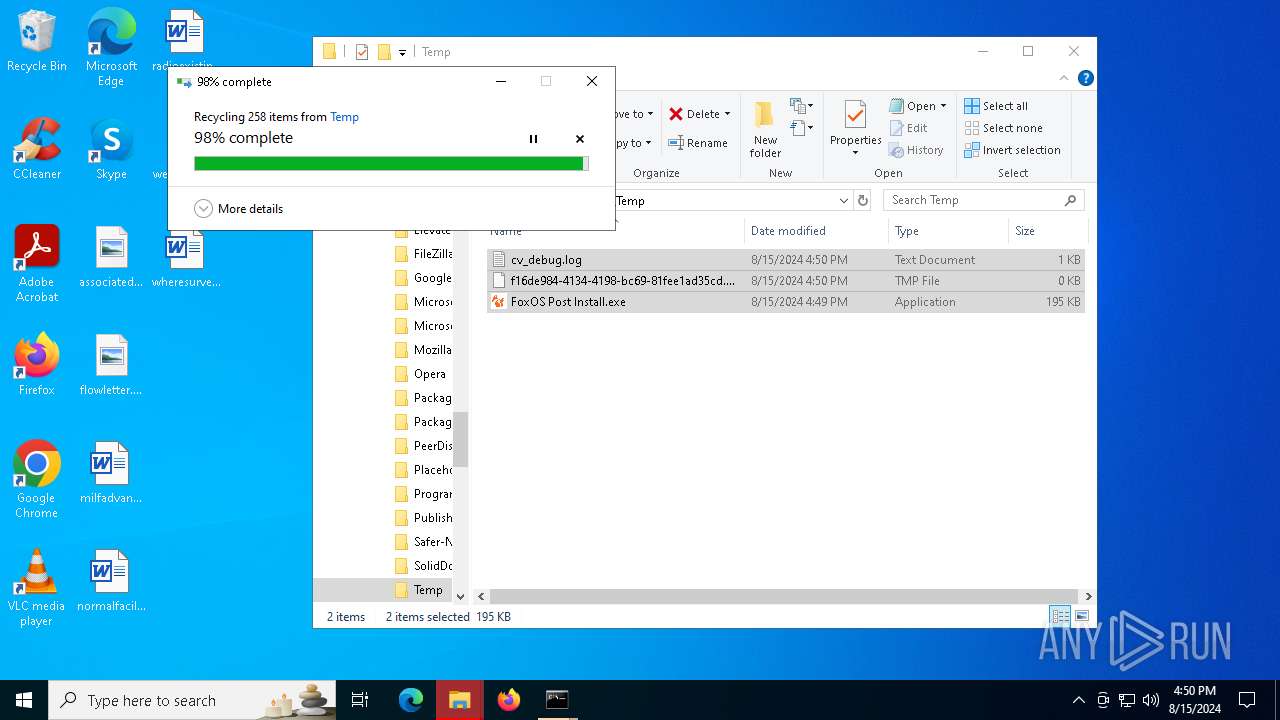
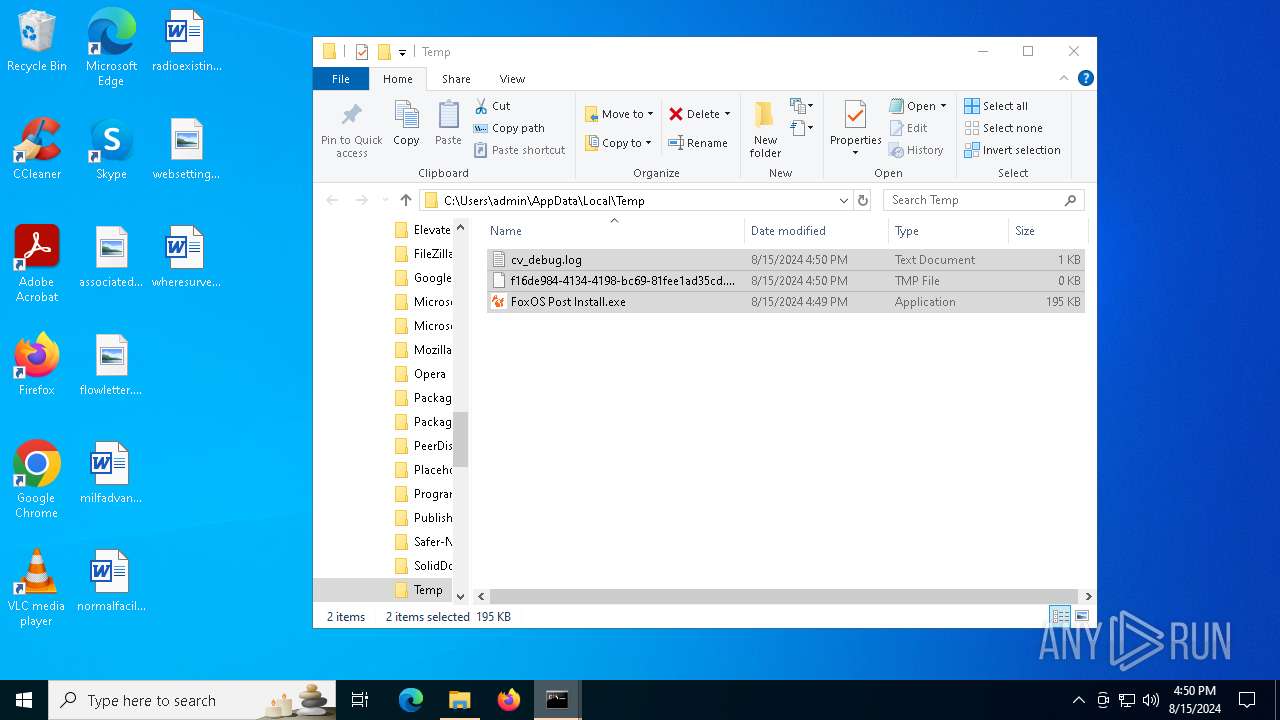
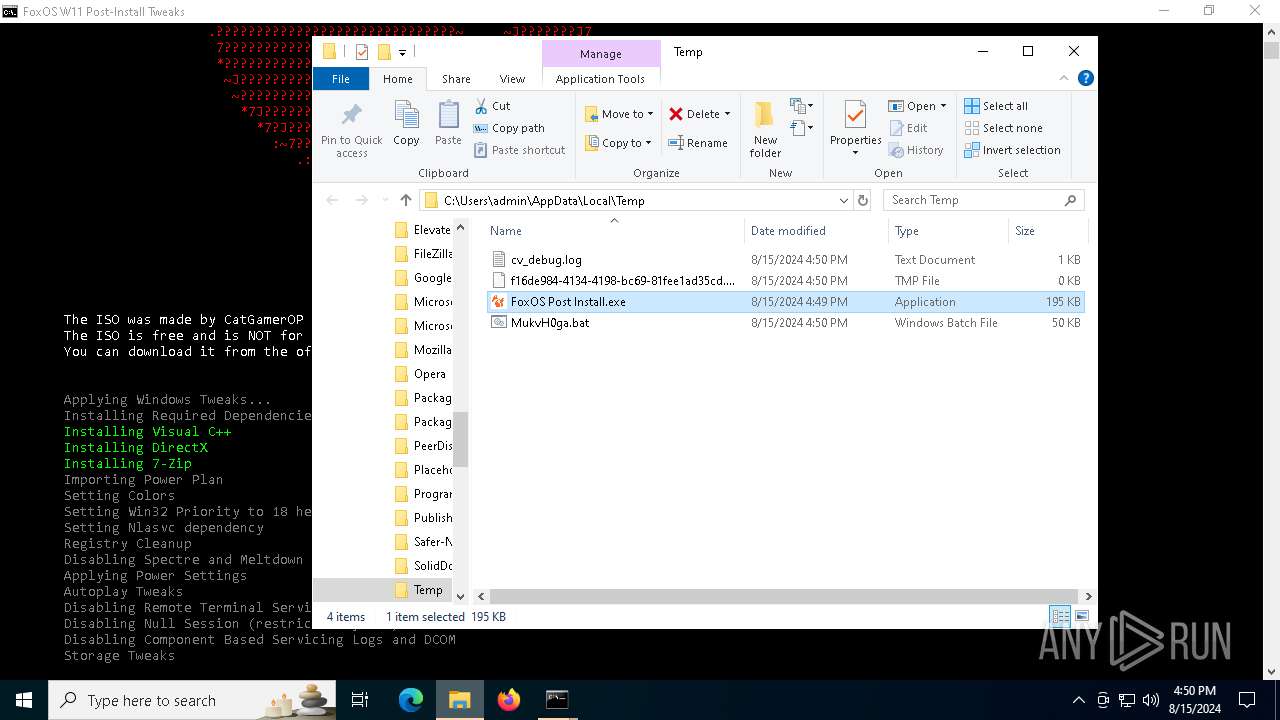
Drops the executable file immediately after the start
- FoxOS Post Install.exe (PID: 6296)
Reads security settings of Internet Explorer
- FoxOS Post Install.exe (PID: 6296)
- ShellExperienceHost.exe (PID: 6000)
- FoxOS Post Install.exe (PID: 2136)
Reads the date of Windows installation
- FoxOS Post Install.exe (PID: 6296)
- FoxOS Post Install.exe (PID: 2136)
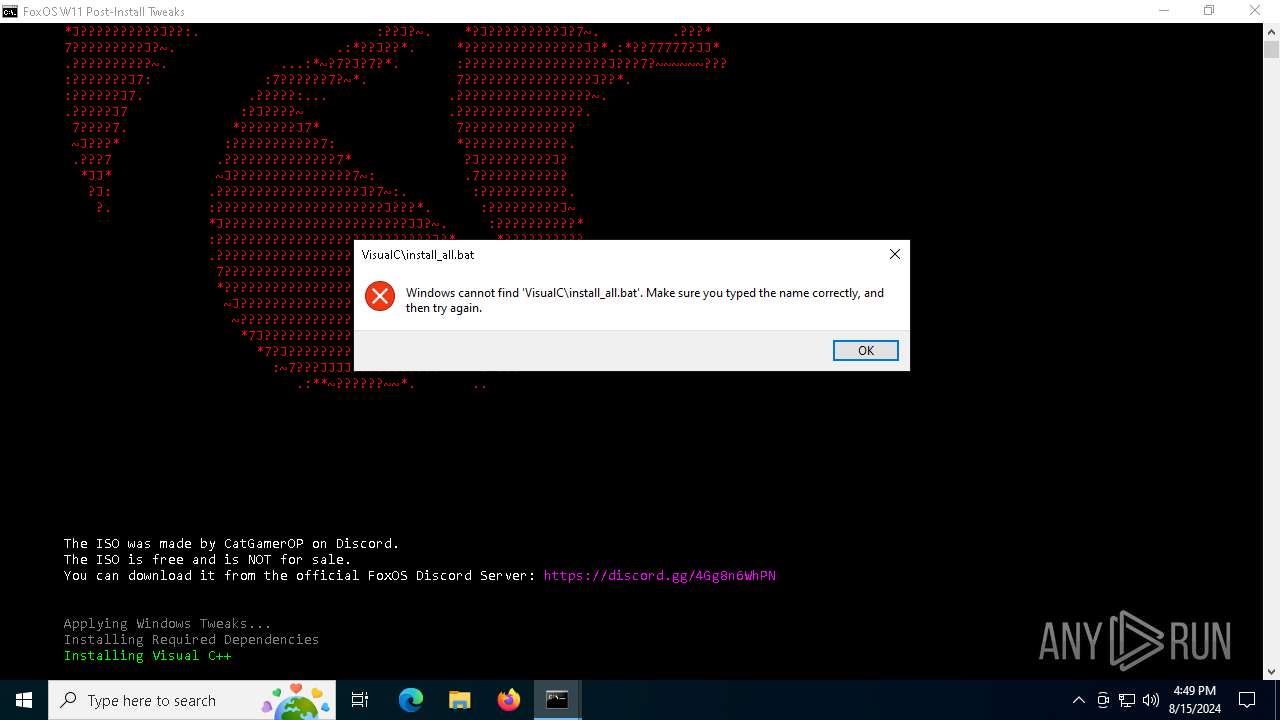
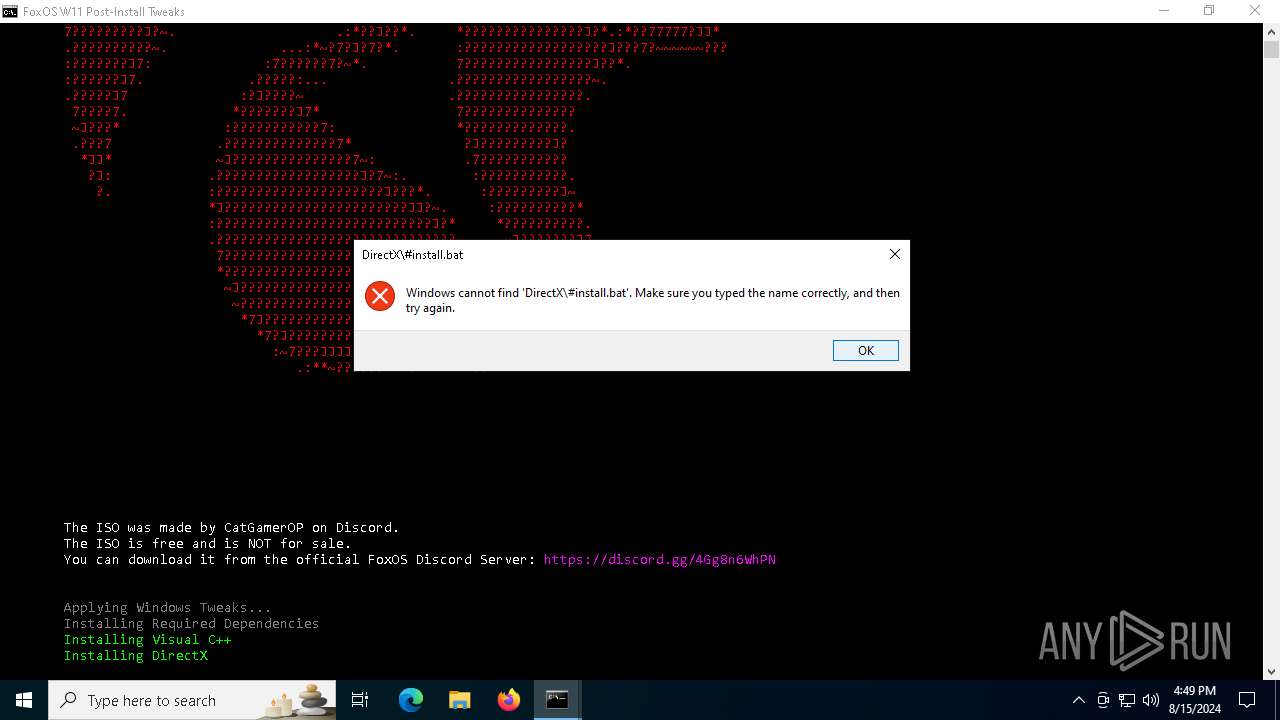
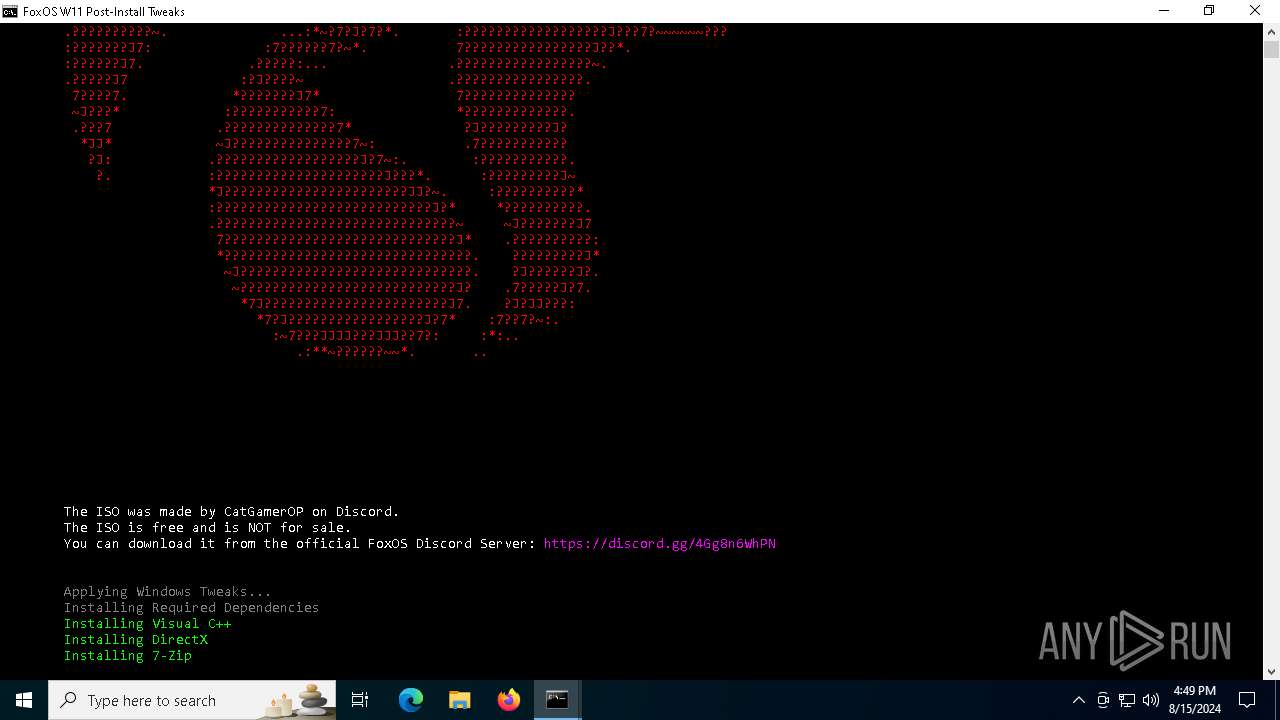
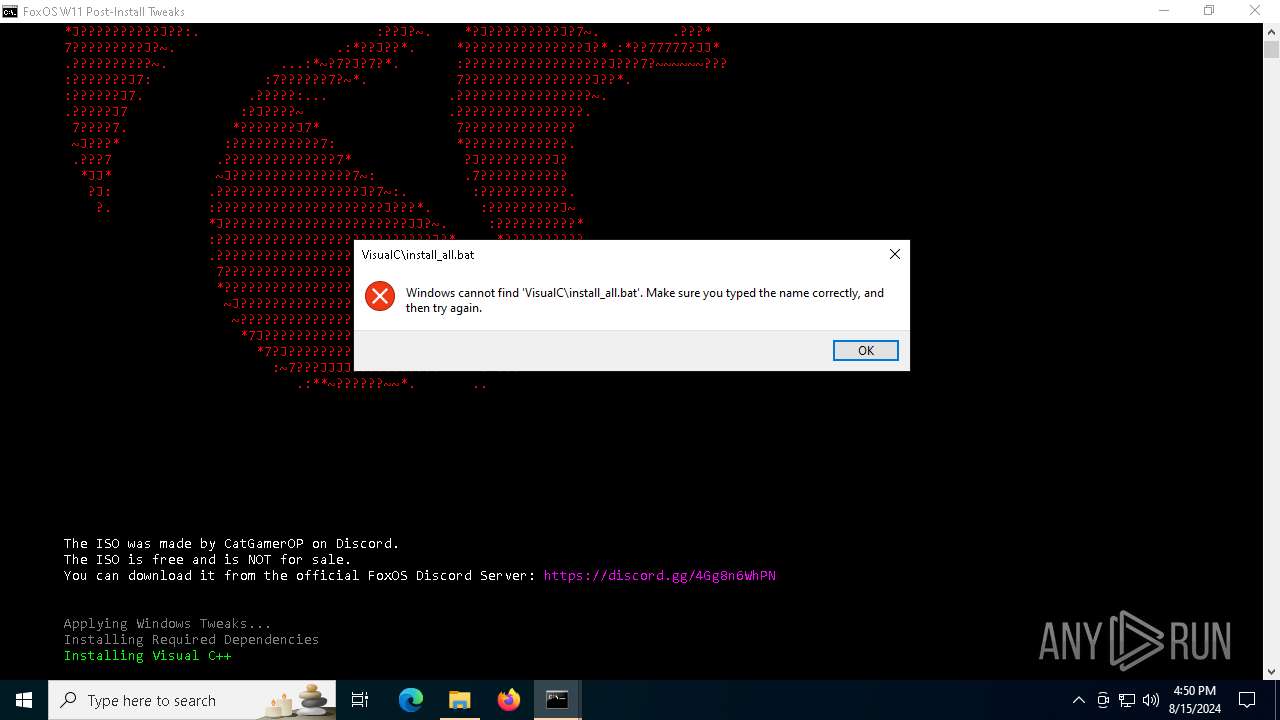
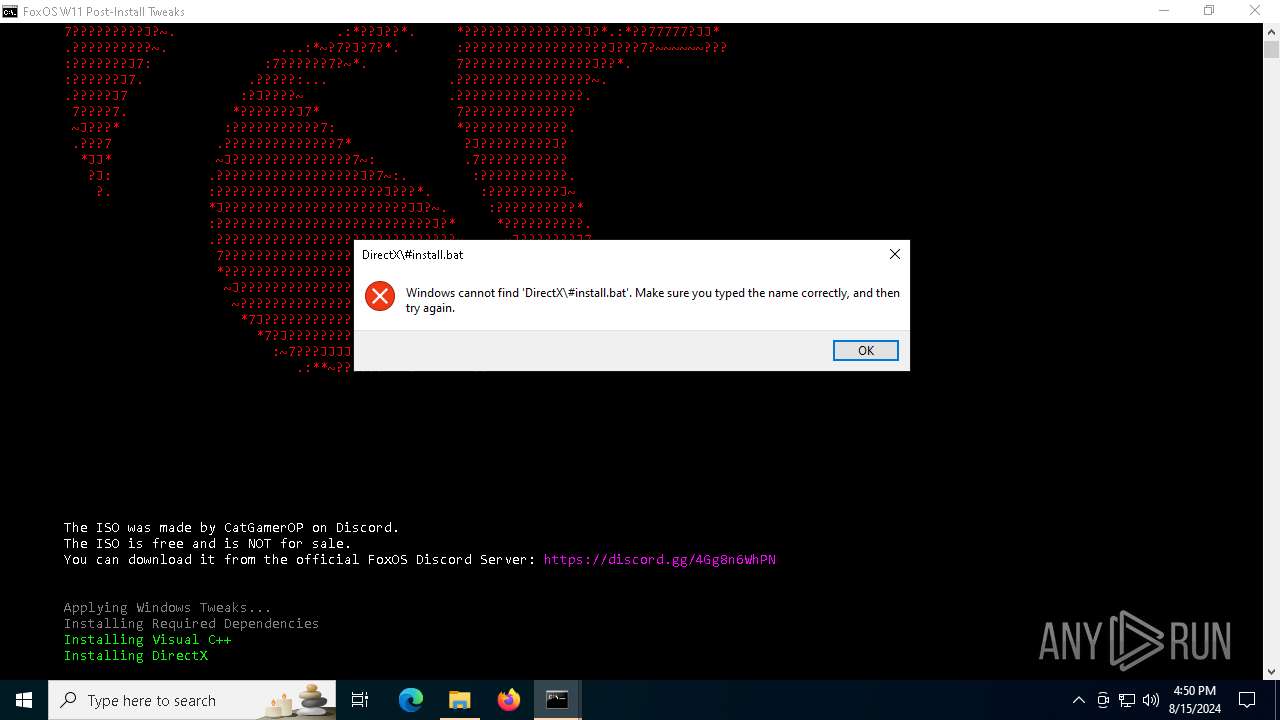
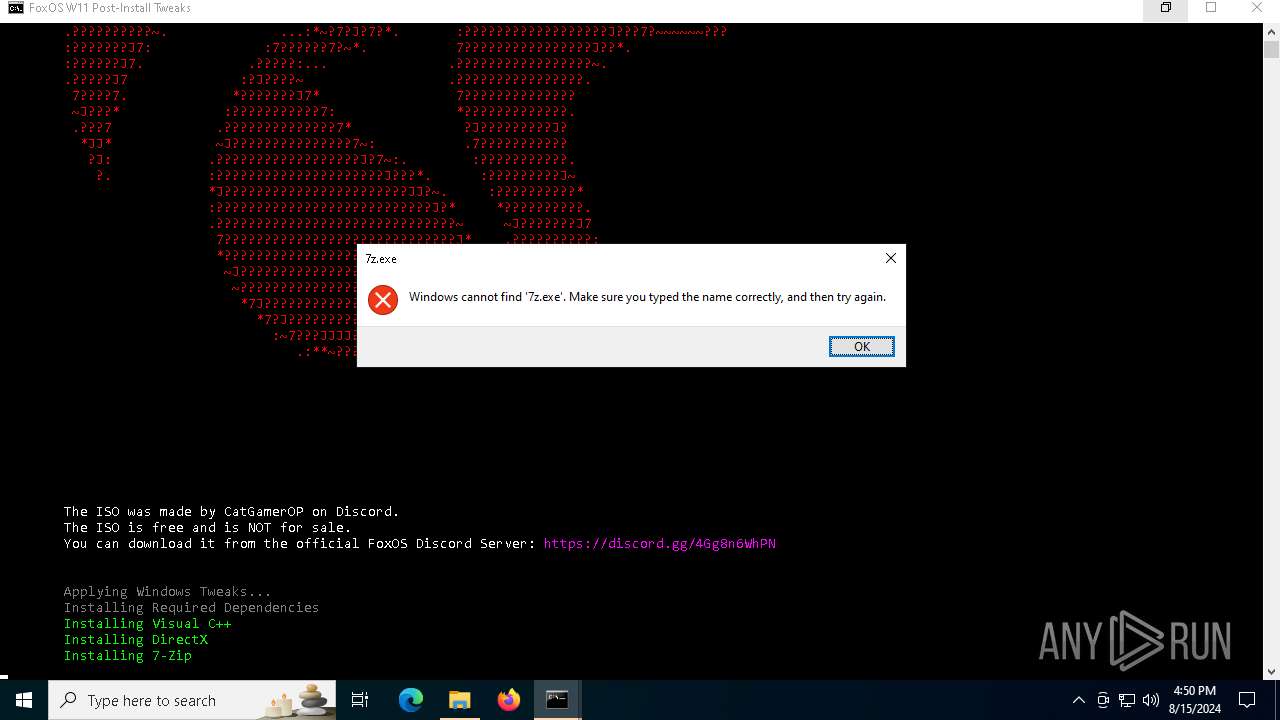
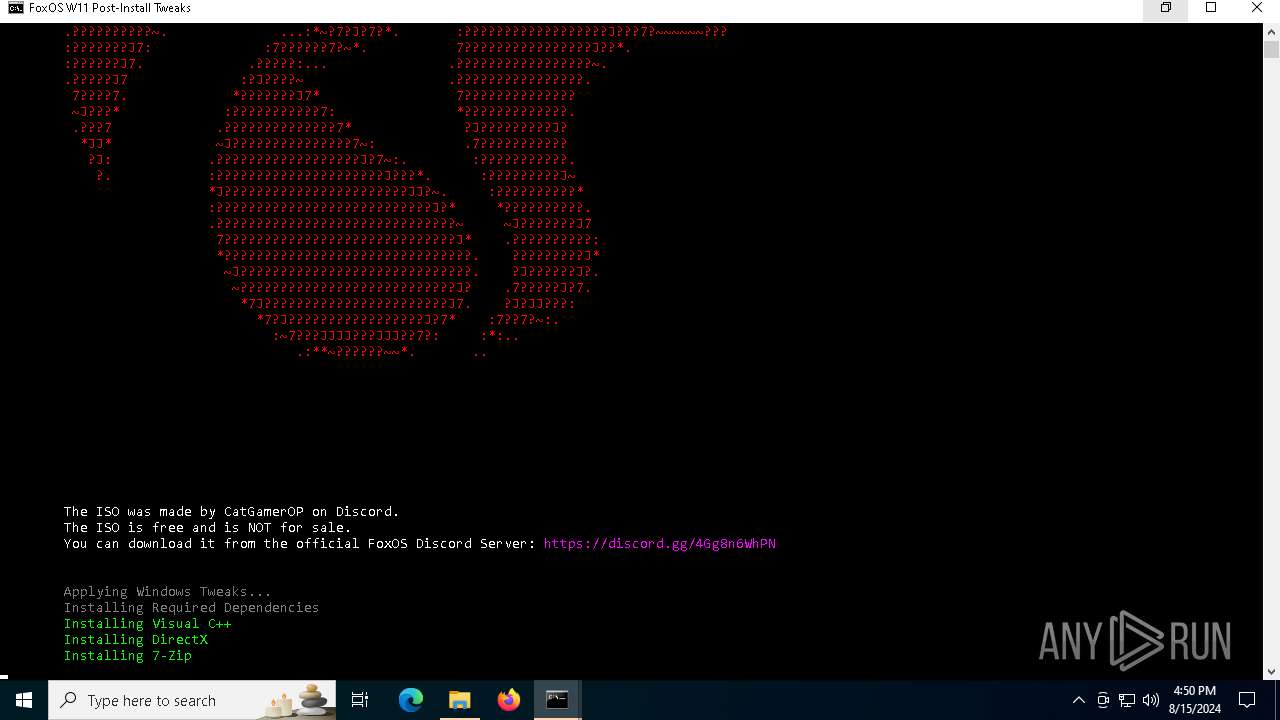
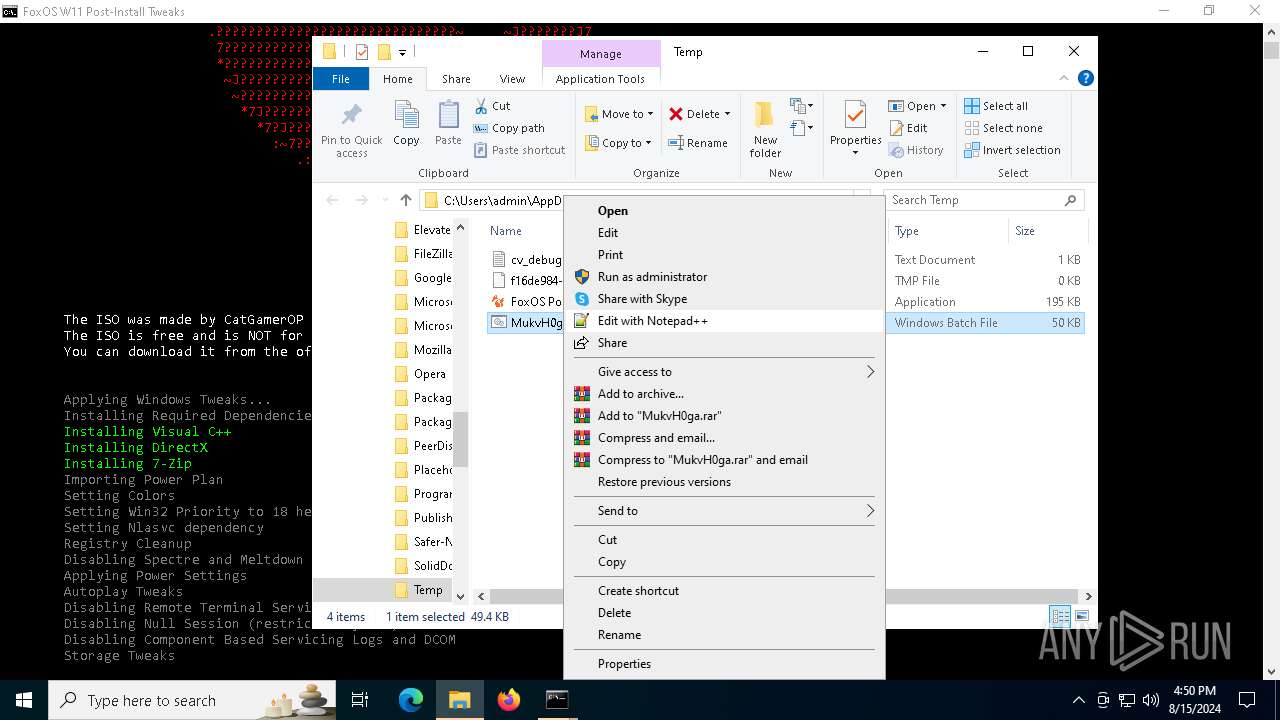
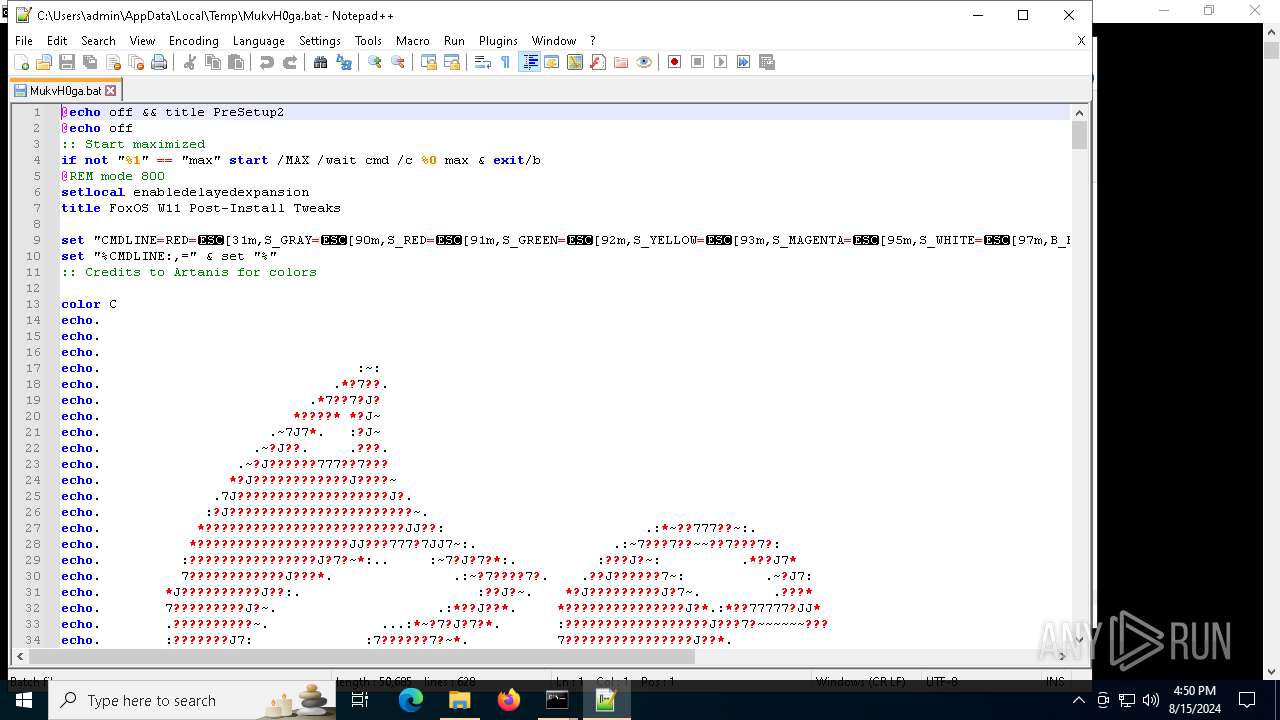
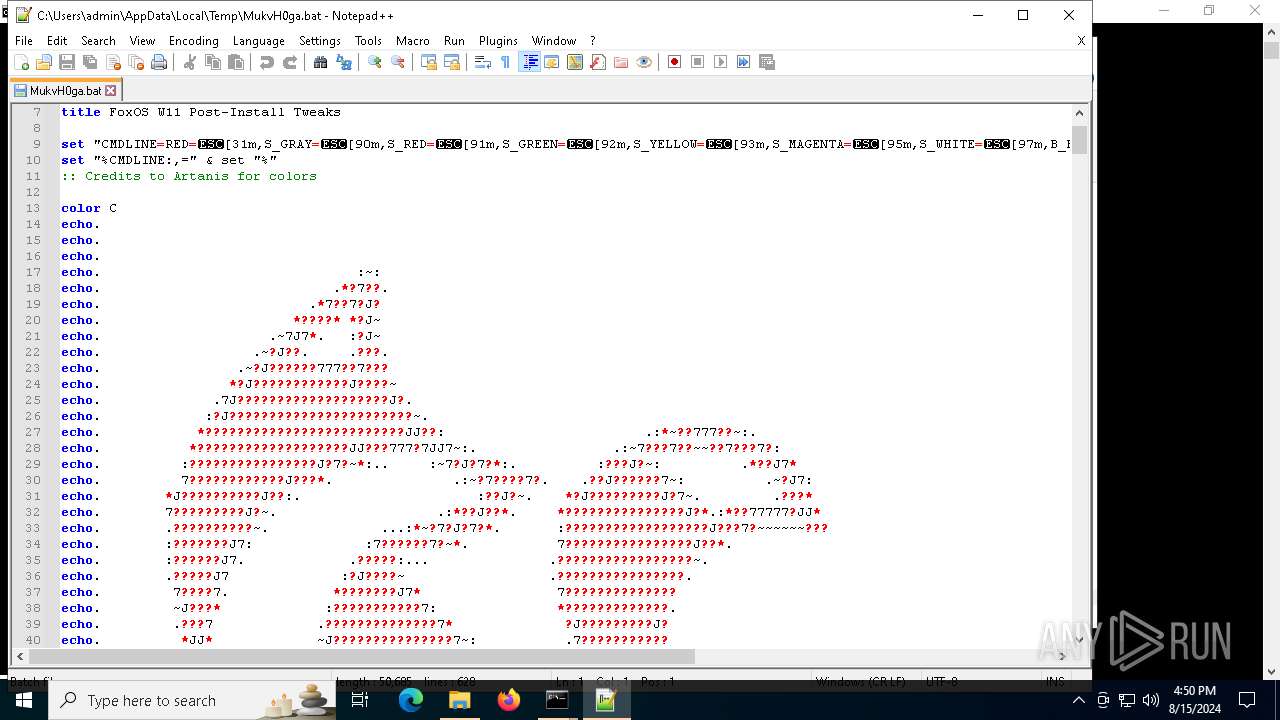
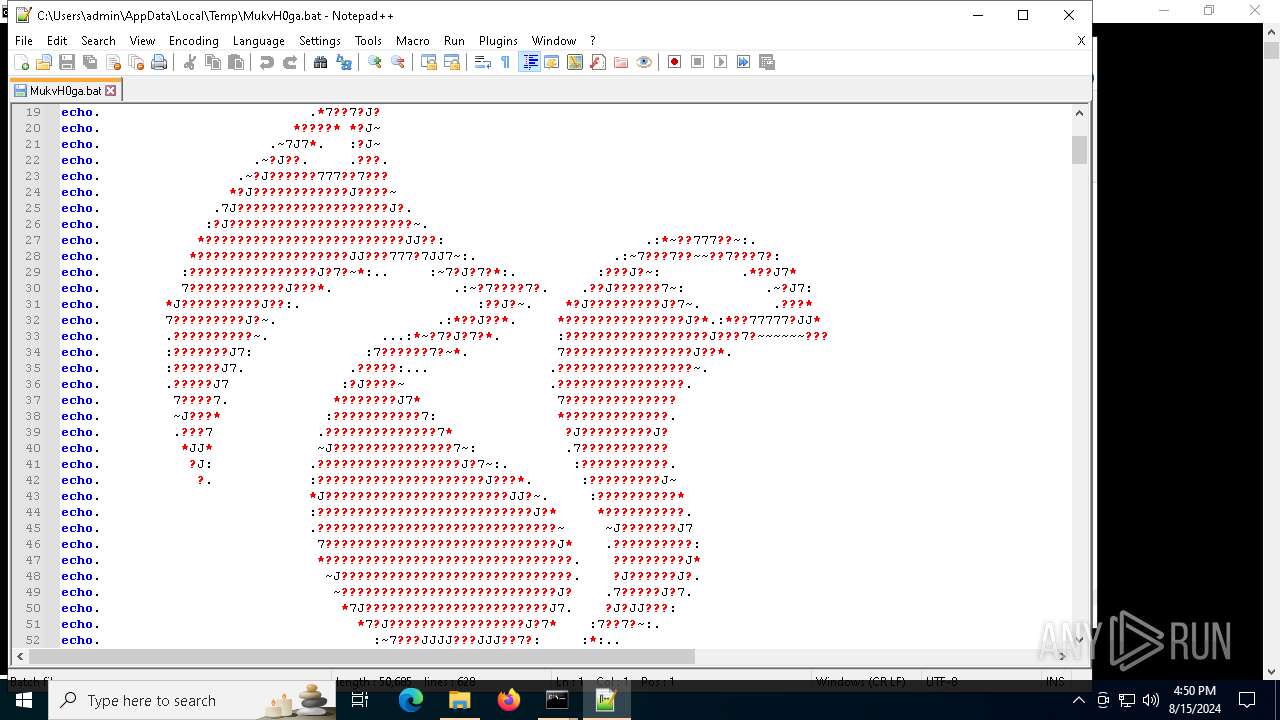
Executing commands from a ".bat" file
- FoxOS Post Install.exe (PID: 6296)
- cmd.exe (PID: 6396)
- FoxOS Post Install.exe (PID: 2136)
- cmd.exe (PID: 7012)
Application launched itself
- cmd.exe (PID: 6396)
- cmd.exe (PID: 7012)
- cmd.exe (PID: 7736)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6396)
- FoxOS Post Install.exe (PID: 6296)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 7012)
- FoxOS Post Install.exe (PID: 2136)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7736)
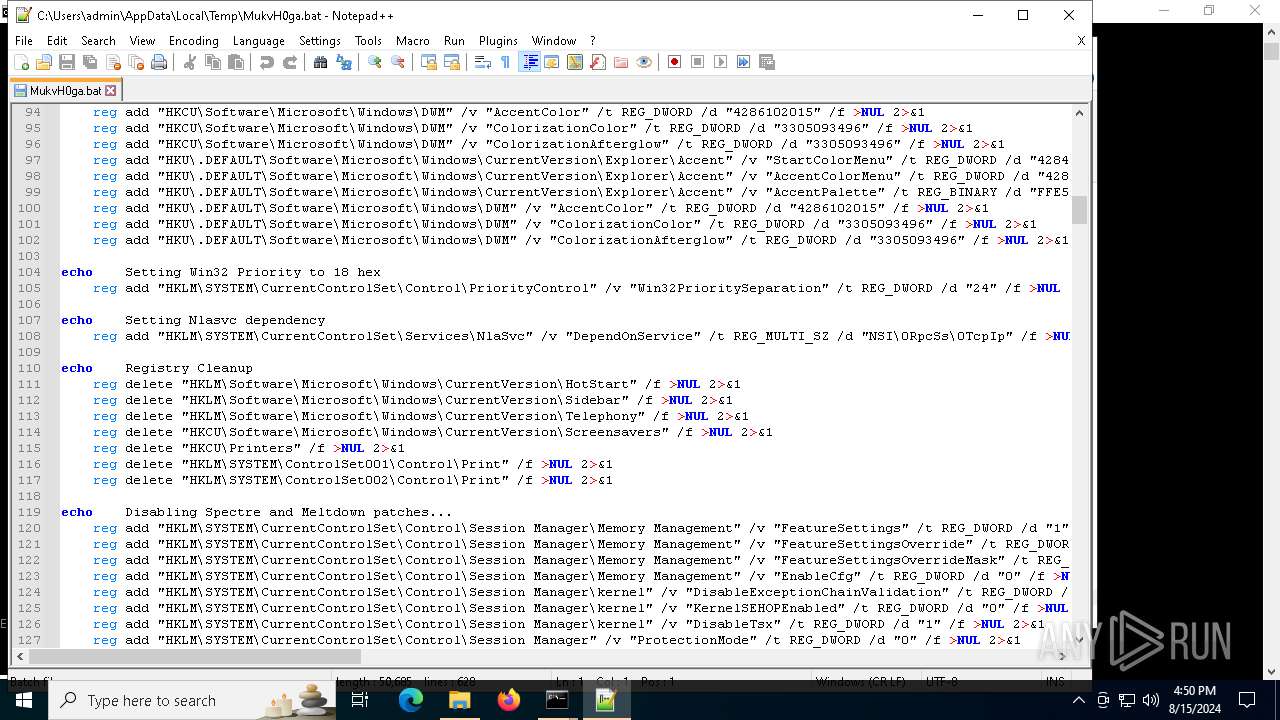
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6476)
- cmd.exe (PID: 5196)
- cmd.exe (PID: 6944)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 7736)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 4232)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 5092)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7736)
The process executes via Task Scheduler
- default-browser-agent.exe (PID: 2132)
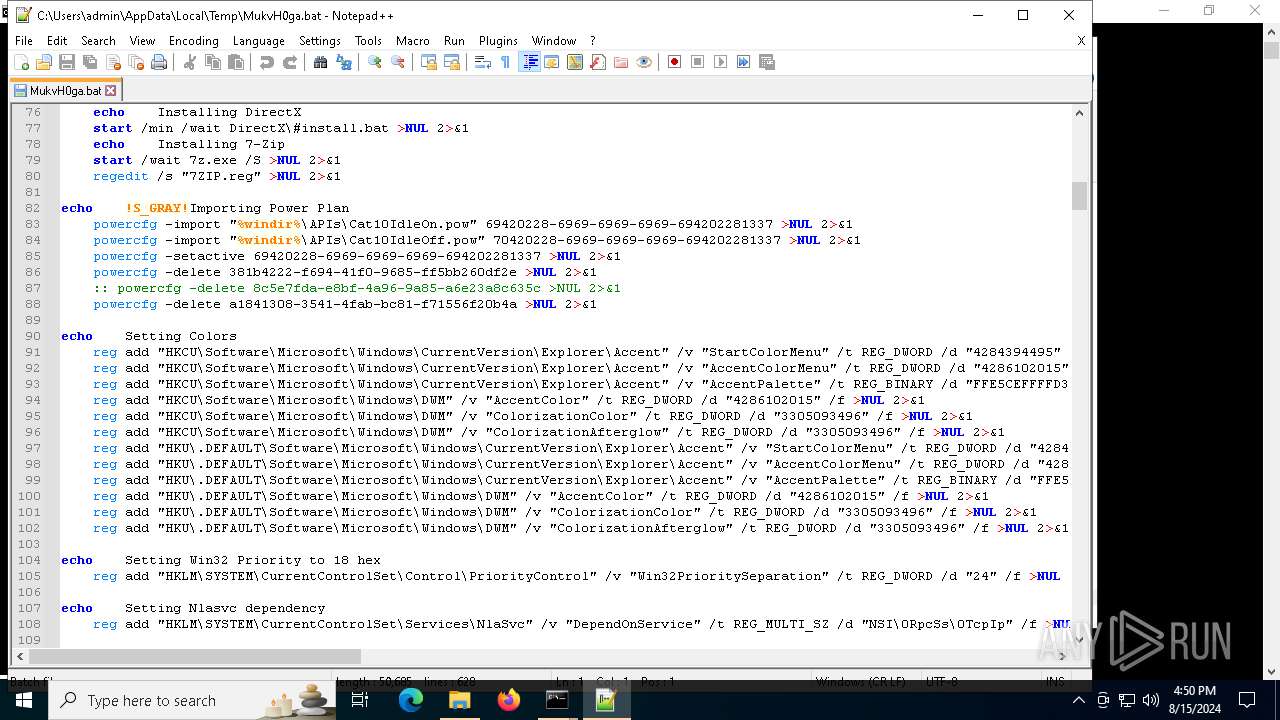
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 6476)
- cmd.exe (PID: 7736)
Loads DLL from Mozilla Firefox
- default-browser-agent.exe (PID: 2132)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5196)
- cmd.exe (PID: 6944)
- cmd.exe (PID: 6684)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7492)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 3684)
- cmd.exe (PID: 3140)
- cmd.exe (PID: 7768)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 6444)
- cmd.exe (PID: 6344)
- cmd.exe (PID: 5292)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 7224)
- cmd.exe (PID: 4232)
- cmd.exe (PID: 7472)
- cmd.exe (PID: 4708)
- cmd.exe (PID: 5472)
- cmd.exe (PID: 5092)
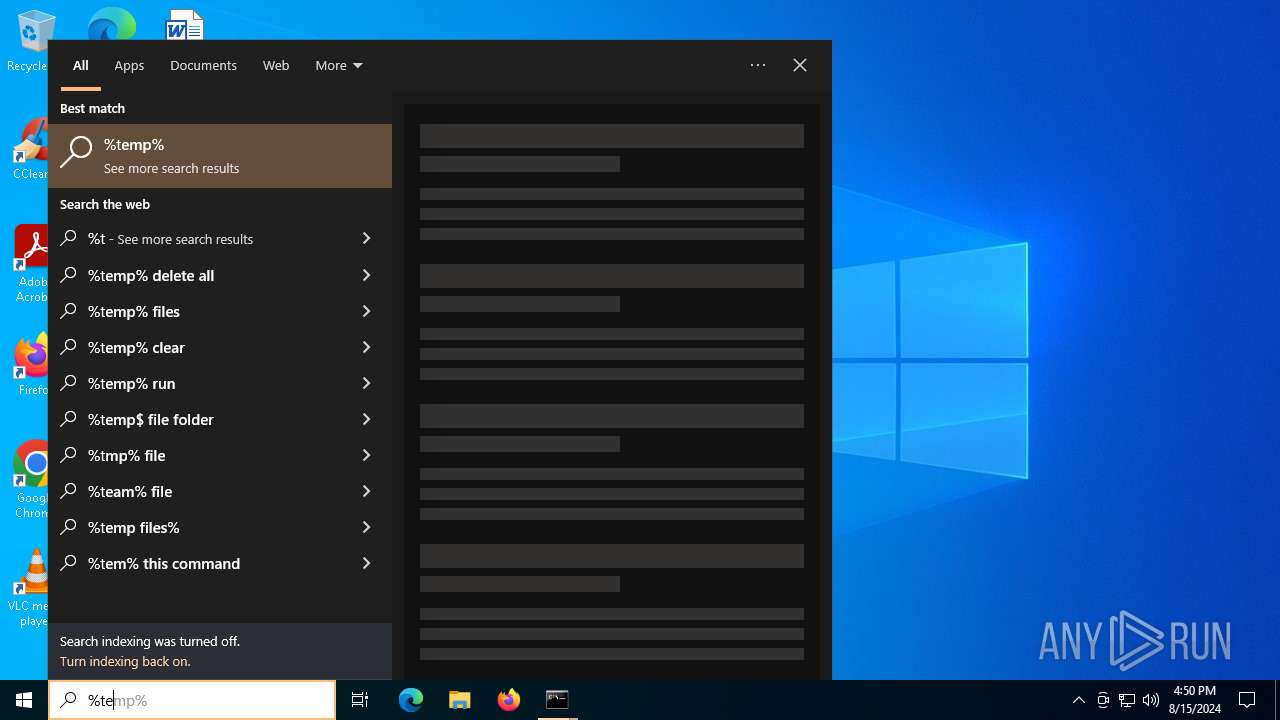
Read disk information to detect sandboxing environments
- reg.exe (PID: 3660)
- reg.exe (PID: 6956)
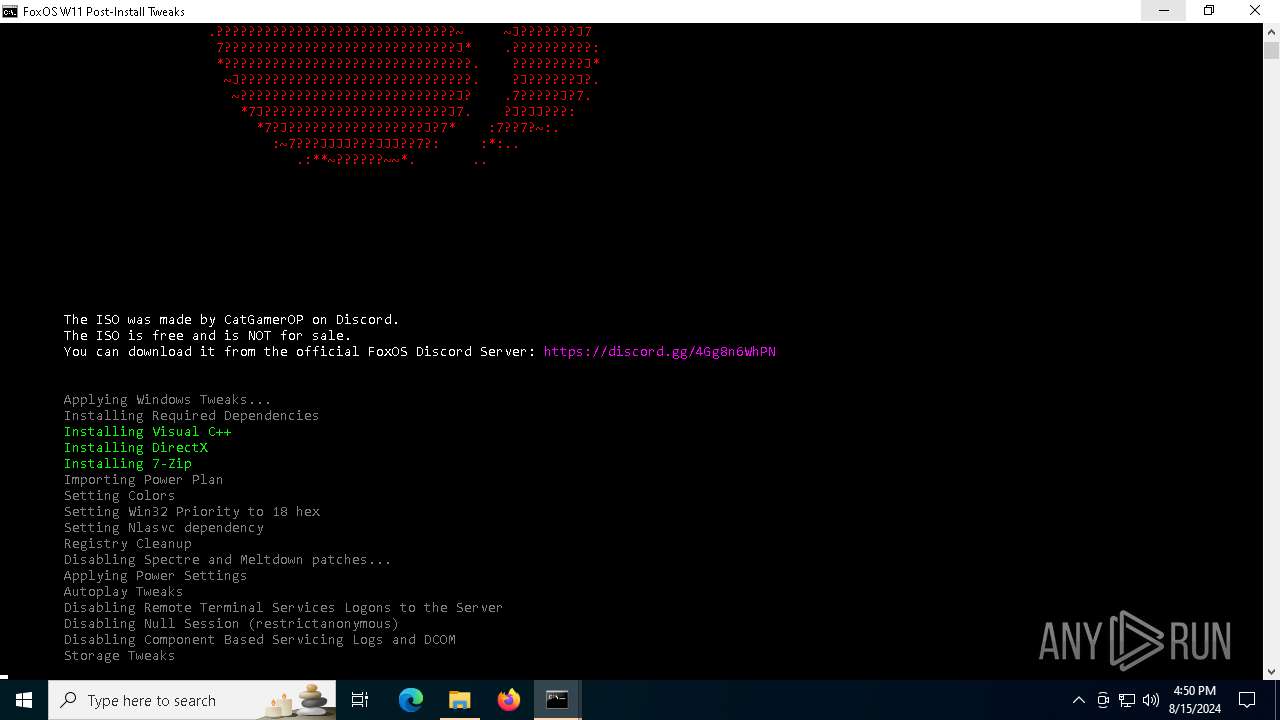
Changes the desktop background image
- reg.exe (PID: 7232)
Uses WMIC.EXE
- cmd.exe (PID: 6884)
- cmd.exe (PID: 7440)
- cmd.exe (PID: 7472)
Process uses powershell cmdlet to discover network configuration
- cmd.exe (PID: 7736)
Starts SC.EXE for service management
- cmd.exe (PID: 7736)
Modifies existing scheduled task
- schtasks.exe (PID: 7384)
- schtasks.exe (PID: 6964)
- schtasks.exe (PID: 6912)
- schtasks.exe (PID: 5196)
- schtasks.exe (PID: 6340)
- schtasks.exe (PID: 6916)
- schtasks.exe (PID: 3684)
- schtasks.exe (PID: 7544)
- schtasks.exe (PID: 4484)
- schtasks.exe (PID: 7008)
- schtasks.exe (PID: 7768)
- schtasks.exe (PID: 6368)
- schtasks.exe (PID: 6372)
- schtasks.exe (PID: 6524)
- schtasks.exe (PID: 7624)
- schtasks.exe (PID: 6476)
- schtasks.exe (PID: 7616)
- schtasks.exe (PID: 2132)
- schtasks.exe (PID: 8008)
- schtasks.exe (PID: 7300)
- schtasks.exe (PID: 1432)
- schtasks.exe (PID: 4280)
- schtasks.exe (PID: 7120)
- schtasks.exe (PID: 7004)
- schtasks.exe (PID: 7092)
- schtasks.exe (PID: 6616)
- schtasks.exe (PID: 6956)
- schtasks.exe (PID: 6824)
- schtasks.exe (PID: 8032)
- schtasks.exe (PID: 6568)
- schtasks.exe (PID: 7596)
- schtasks.exe (PID: 7512)
- schtasks.exe (PID: 8064)
- schtasks.exe (PID: 7404)
- schtasks.exe (PID: 3476)
- schtasks.exe (PID: 7244)
- schtasks.exe (PID: 6880)
- schtasks.exe (PID: 5600)
- schtasks.exe (PID: 7508)
- schtasks.exe (PID: 1292)
- schtasks.exe (PID: 6988)
- schtasks.exe (PID: 5920)
- schtasks.exe (PID: 6232)
- schtasks.exe (PID: 232)
- schtasks.exe (PID: 904)
- schtasks.exe (PID: 1020)
- schtasks.exe (PID: 7356)
- schtasks.exe (PID: 7208)
- schtasks.exe (PID: 5944)
- schtasks.exe (PID: 2088)
- schtasks.exe (PID: 1920)
- schtasks.exe (PID: 4692)
- schtasks.exe (PID: 6640)
- schtasks.exe (PID: 7700)
- schtasks.exe (PID: 3876)
- schtasks.exe (PID: 6016)
- schtasks.exe (PID: 1492)
- schtasks.exe (PID: 6172)
- schtasks.exe (PID: 4024)
- schtasks.exe (PID: 4016)
- schtasks.exe (PID: 6976)
- schtasks.exe (PID: 5504)
- schtasks.exe (PID: 5196)
- schtasks.exe (PID: 6980)
- schtasks.exe (PID: 7108)
- schtasks.exe (PID: 7472)
- schtasks.exe (PID: 3880)
- schtasks.exe (PID: 7768)
- schtasks.exe (PID: 1964)
- schtasks.exe (PID: 6440)
- schtasks.exe (PID: 6376)
- schtasks.exe (PID: 6368)
- schtasks.exe (PID: 2248)
- schtasks.exe (PID: 7616)
- schtasks.exe (PID: 6476)
- schtasks.exe (PID: 7624)
- schtasks.exe (PID: 5060)
- schtasks.exe (PID: 5408)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 1060)
- schtasks.exe (PID: 4080)
- schtasks.exe (PID: 7484)
- schtasks.exe (PID: 7584)
Uses NETSH.EXE to change the status of the firewall
- cmd.exe (PID: 7736)
Found IP address in command line
- powershell.exe (PID: 6936)
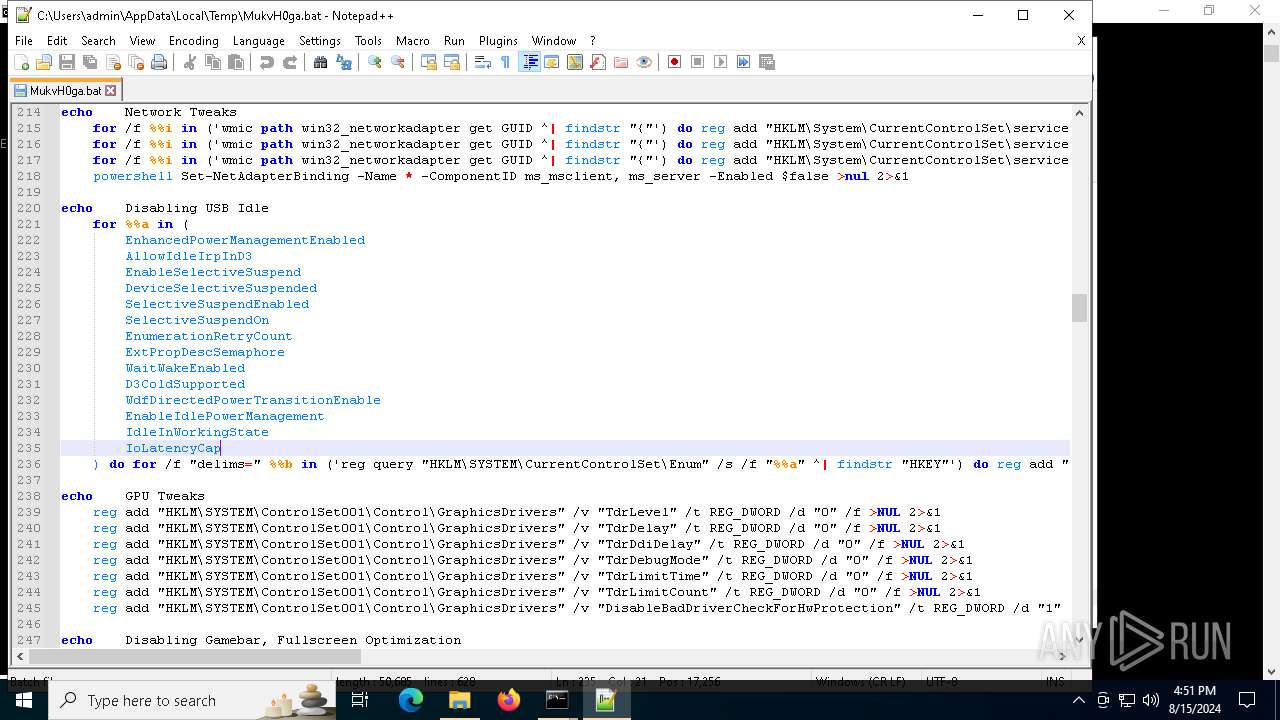
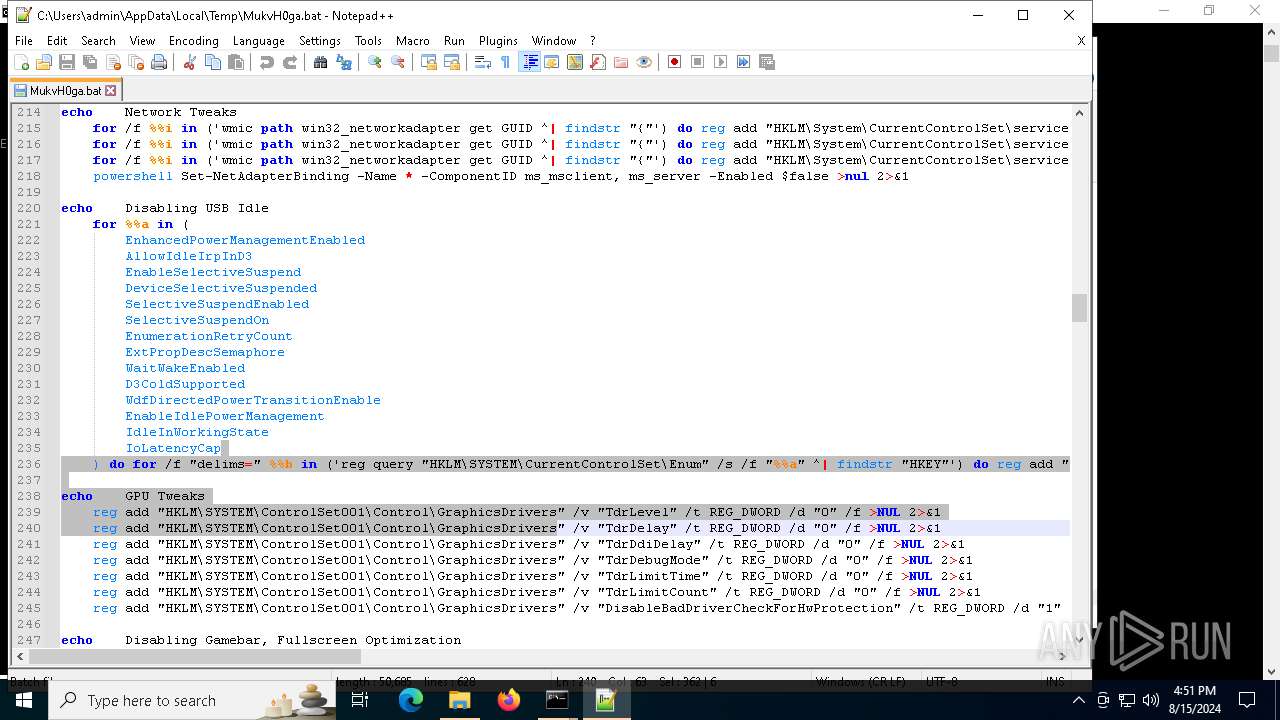
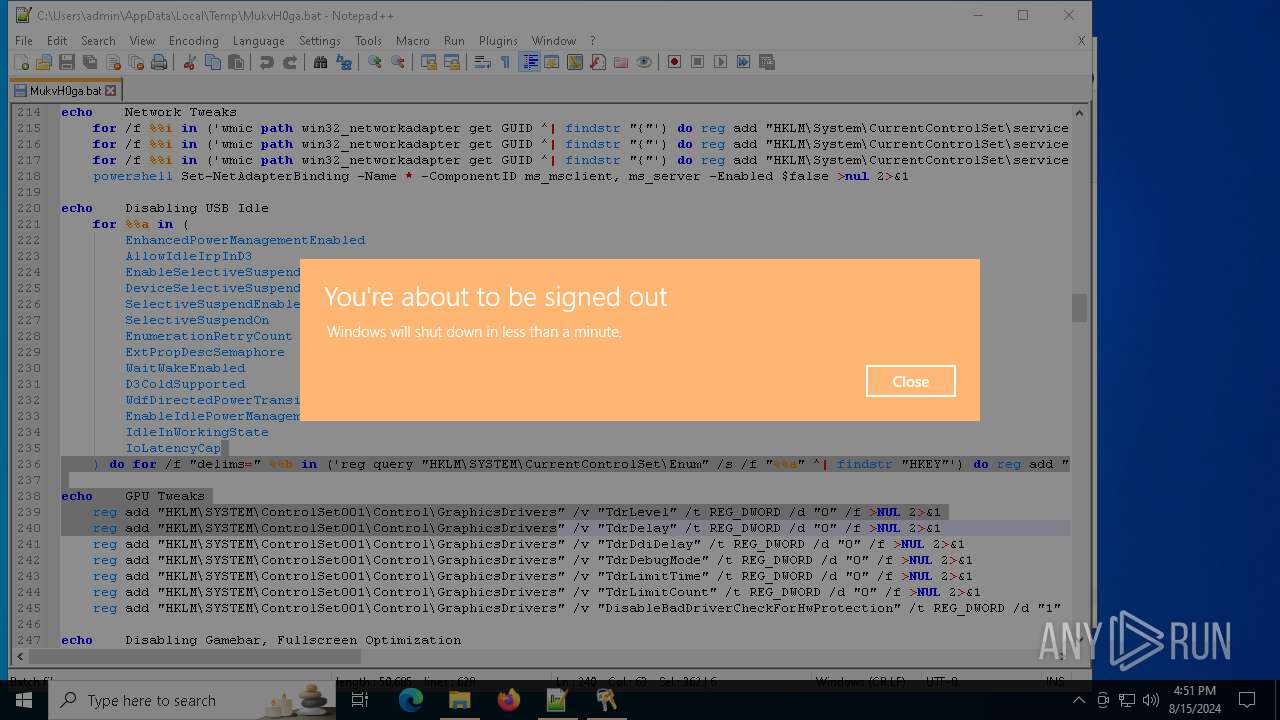
The system shut down or reboot
- cmd.exe (PID: 7736)
INFO
Process checks computer location settings
- FoxOS Post Install.exe (PID: 6296)
- FoxOS Post Install.exe (PID: 2136)
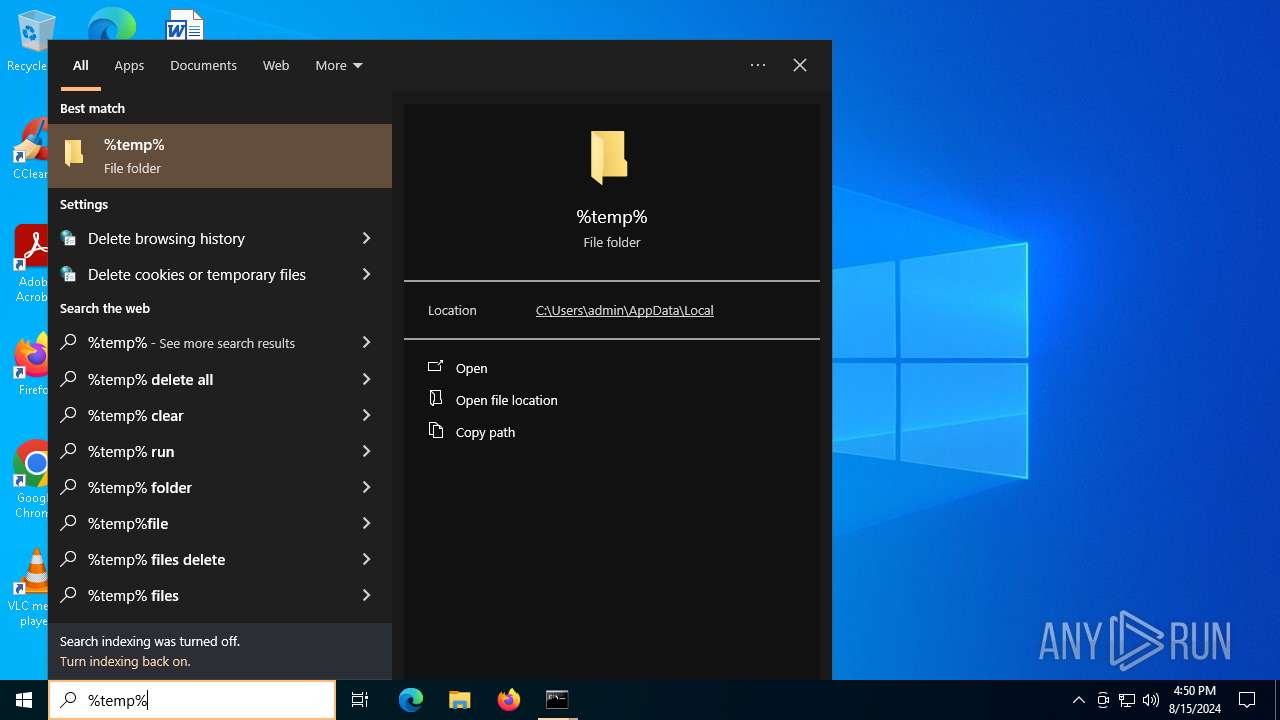
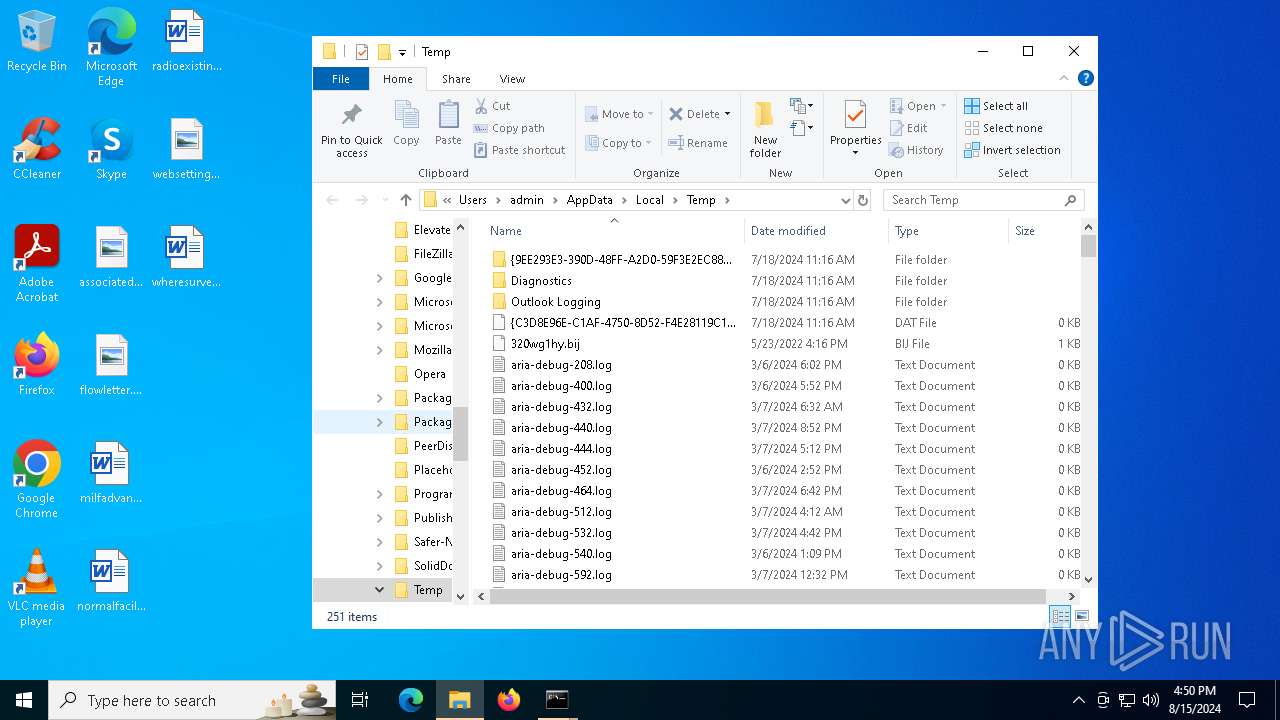
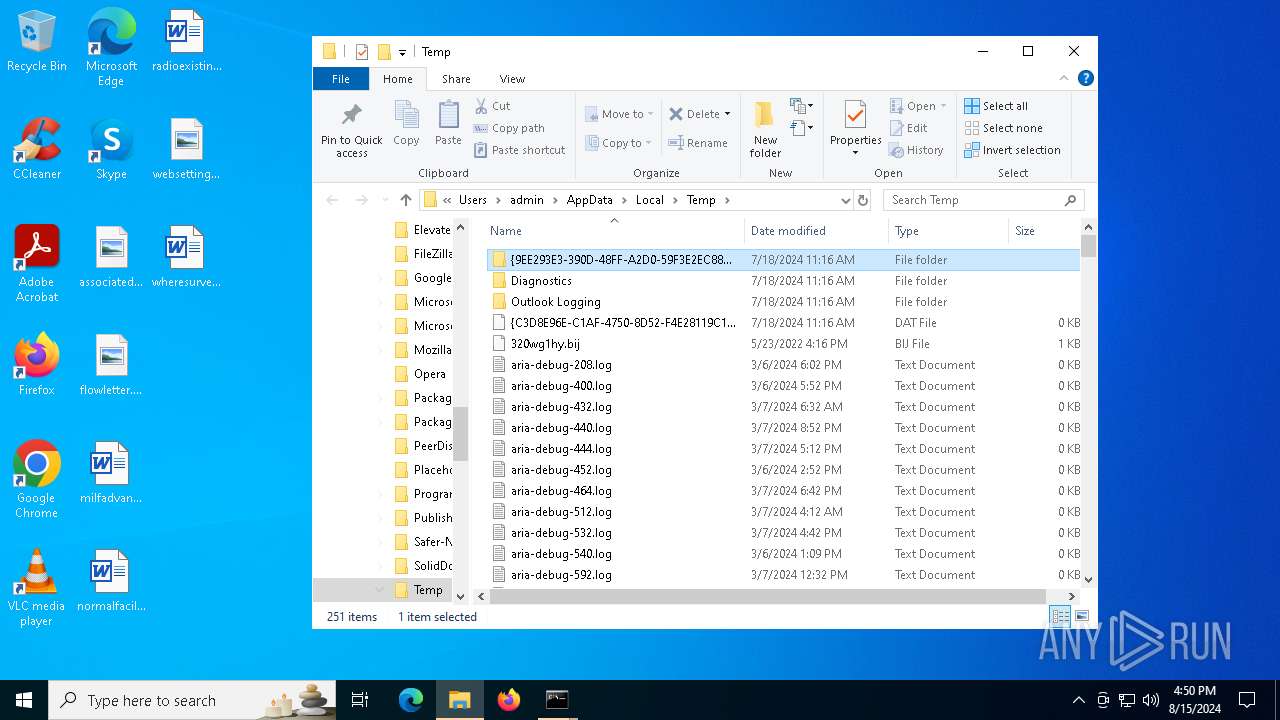
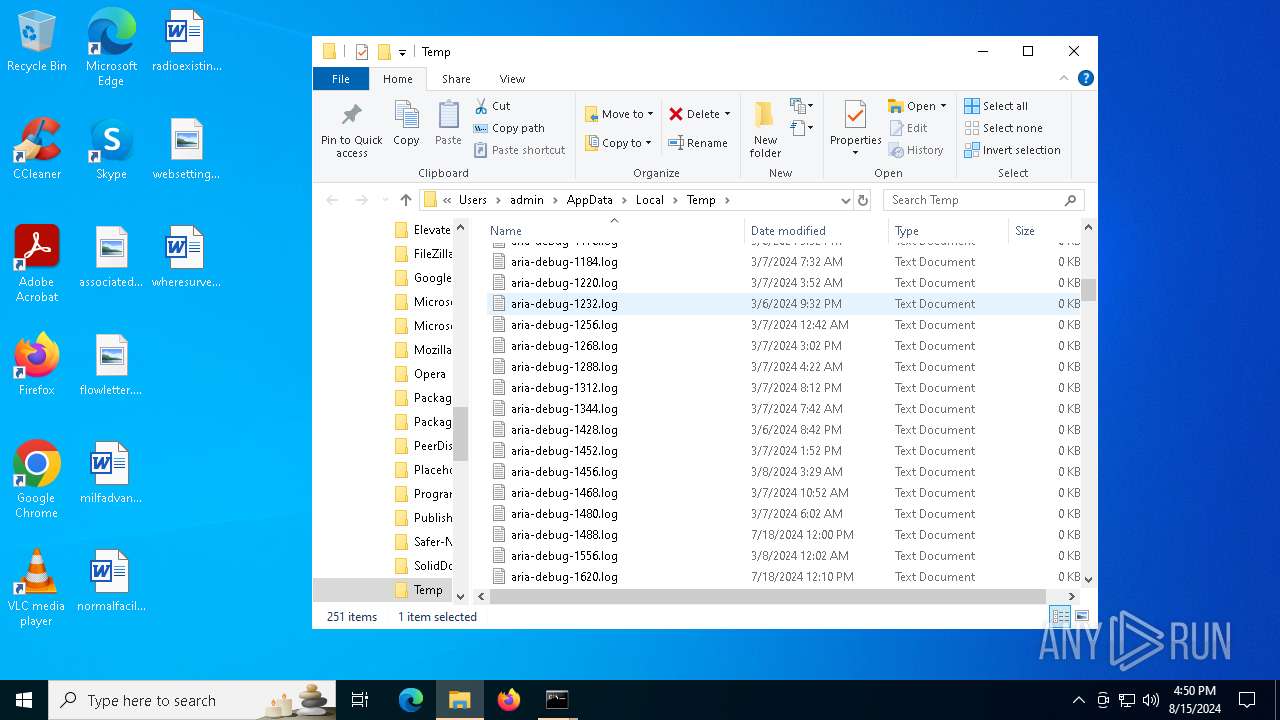
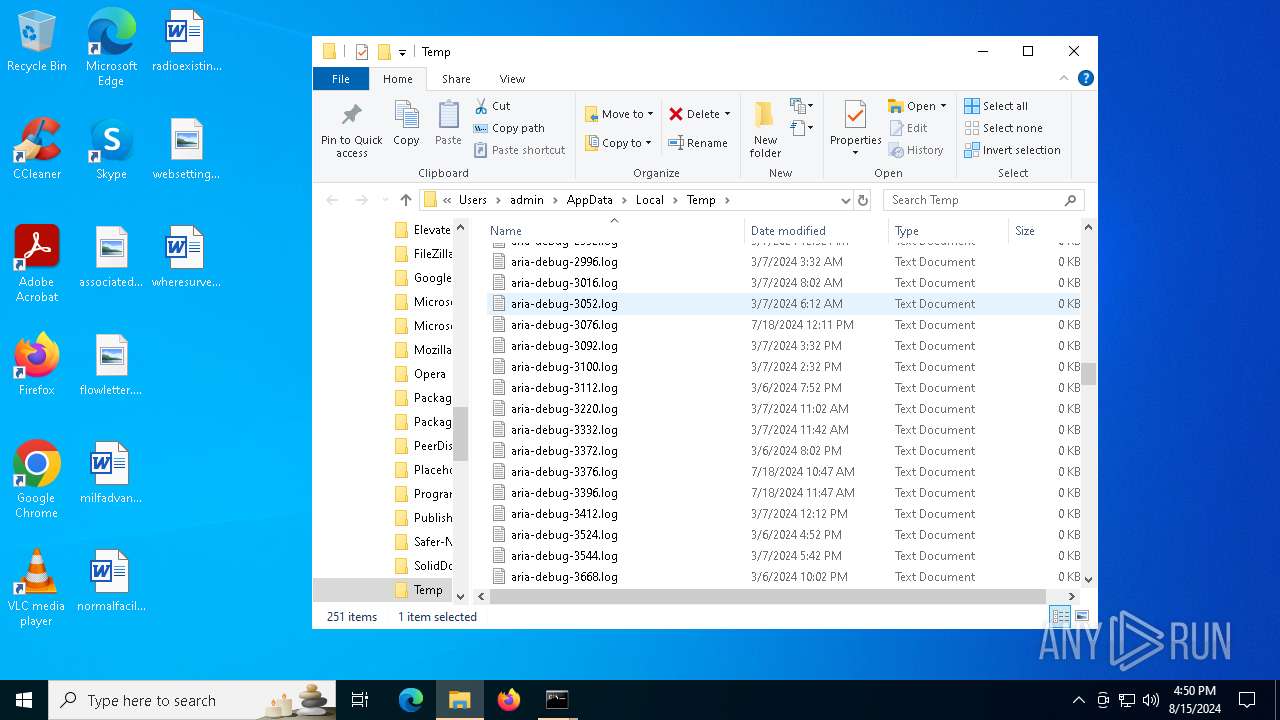
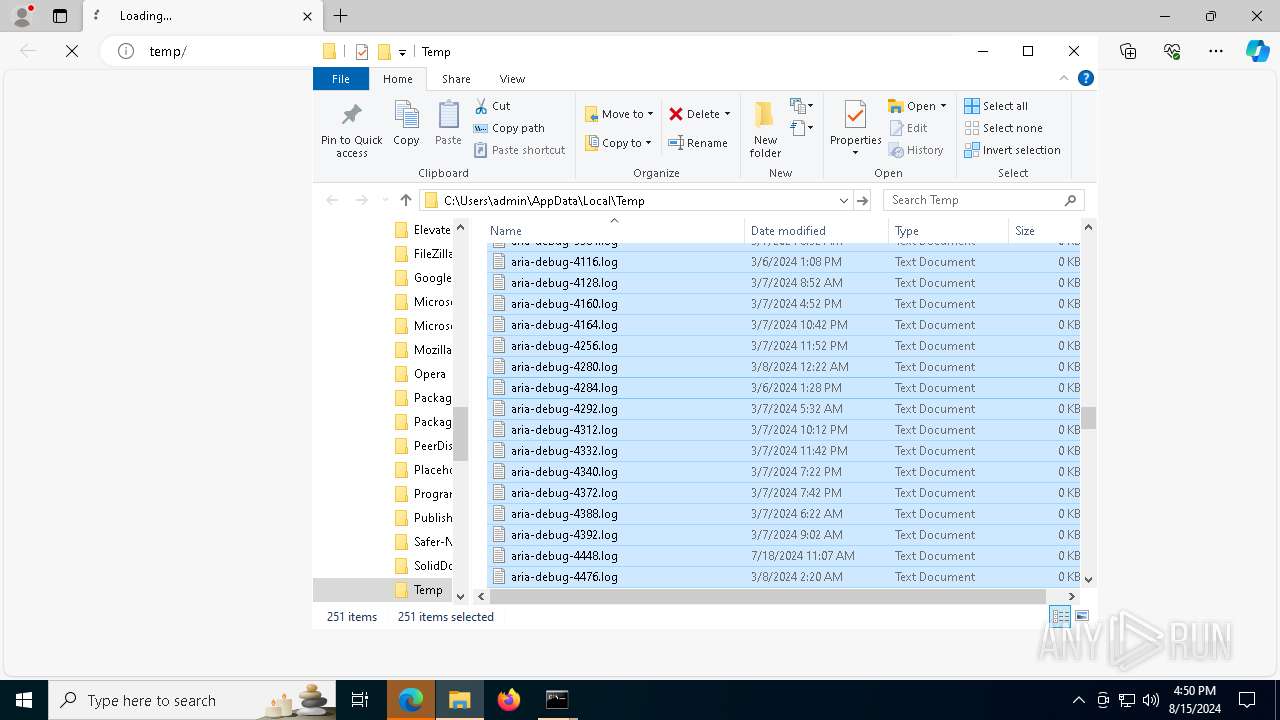
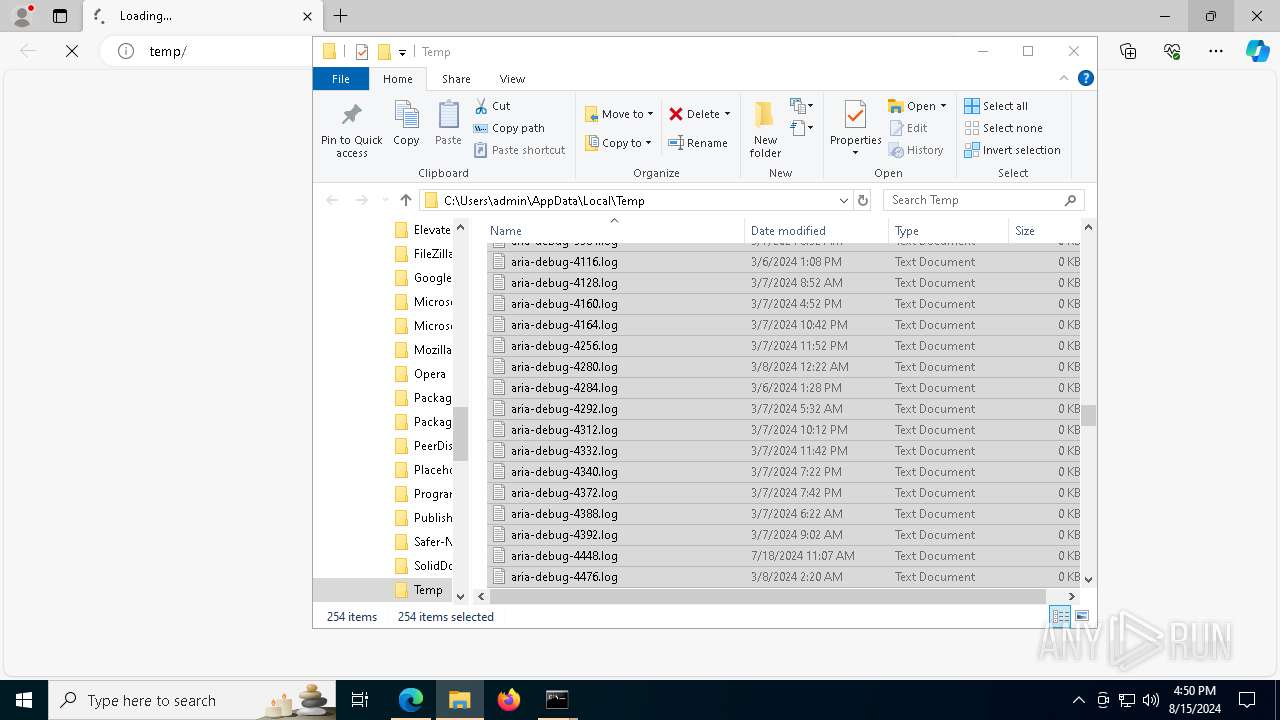
Create files in a temporary directory
- FoxOS Post Install.exe (PID: 6296)
- FoxOS Post Install.exe (PID: 2136)
Checks supported languages
- FoxOS Post Install.exe (PID: 6296)
- default-browser-agent.exe (PID: 2132)
- TextInputHost.exe (PID: 7052)
- ShellExperienceHost.exe (PID: 6000)
- identity_helper.exe (PID: 7544)
- FoxOS Post Install.exe (PID: 2136)
Reads the computer name
- FoxOS Post Install.exe (PID: 6296)
- TextInputHost.exe (PID: 7052)
- identity_helper.exe (PID: 7544)
- ShellExperienceHost.exe (PID: 6000)
- FoxOS Post Install.exe (PID: 2136)
Application launched itself
- firefox.exe (PID: 1536)
- msedge.exe (PID: 2872)
- msedge.exe (PID: 7720)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7720)
- msedge.exe (PID: 2872)
Manual execution by a user
- msedge.exe (PID: 2872)
- FoxOS Post Install.exe (PID: 2136)
- notepad++.exe (PID: 5552)
Reads Environment values
- identity_helper.exe (PID: 7544)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 6028)
- WMIC.exe (PID: 2388)
- WMIC.exe (PID: 1248)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3996)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3996)
- powershell.exe (PID: 6936)
- powershell.exe (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:07:31 10:44:32+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 103936 |
| InitializedDataSize: | 95232 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1b5ee |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | |
| FileVersion: | 0.0.0.0 |
| InternalName: | PreSetup2.exe |
| LegalCopyright: | |
| OriginalFileName: | PreSetup2.exe |
| ProductVersion: | 0.0.0.0 |
| AssemblyVersion: | 0.0.0.0 |
Total processes
723
Monitored processes
574
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | reg delete "HKLM\Software\Microsoft\Windows\CurrentVersion\Telephony" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | reg add "HKLM\SYSTEM\CurrentControlSet\Control\Lsa" /v RestrictAnonymousSAM /t REG_DWORD /d 1 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | Auditpol /set /subcategory:"Security State Change" /success:disable /failure:enable | C:\Windows\System32\auditpol.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Audit Policy Program Exit code: 1314 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 232 | schtasks /change /tn "\Microsoft\Windows\AppxDeploymentClient\Pre-staged app cleanup" /disable | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Explorer\VisualEffects" /v "VisualFXSetting" /t REG_DWORD /d "3" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | reg delete "HKLM\SYSTEM\ControlSet001\Control\Print" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 360 | reg add "HKCU\SOFTWARE\Classes.png" /ve /t REG_SZ /d "PhotoViewer.FileAssoc.Tiff" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 460 | bcdedit /set allowedinmemorysettings 0 | C:\Windows\System32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 752 | reg add "HKLM\SYSTEM\CurrentControlSet\Control\Lsa" /v "disabledomaincreds" /t REG_DWORD /d "1" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
193 104
Read events
192 729
Write events
229
Delete events
146
Modification events
| (PID) Process: | (6296) FoxOS Post Install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6296) FoxOS Post Install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6296) FoxOS Post Install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6296) FoxOS Post Install.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6476) cmd.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3c\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\ndfapi.dll,-40001 |
Value: Windows Network Diagnostics | |||
| (PID) Process: | (6476) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6476) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6476) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6476) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6292) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Accent |
| Operation: | write | Name: | StartColorMenu |
Value: | |||
Executable files
0
Suspicious files
84
Text files
93
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFf5c21.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFf5c30.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6296 | FoxOS Post Install.exe | C:\Users\admin\AppData\Local\Temp\lAw24lsm.bat | text | |
MD5:46DC84028C06836A09663289DF01181B | SHA256:E26F28D0115C4C3F0E89C421431C88FB498BA9A7BE191D077A3A431960A5F5B4 | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFf5c30.TMP | — | |
MD5:— | SHA256:— | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1236 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Background Tasks Profiles\93u99co2.MozillaBackgroundTask-308046B0AF4A39CB-defaultagent\datareporting\glean\db\data.safe.tmp | dbf | |
MD5:63B1BB87284EFE954E1C3AE390E7EE44 | SHA256:B017EE25A7F5C09EB4BF359CA721D67E6E9D9F95F8CE6F741D47F33BDE6EF73A | |||
| 1928 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_l3mqcixr.vga.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFf5c40.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
81
DNS requests
49
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1664 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1664 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6952 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4208 | svchost.exe | HEAD | 200 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1724112530&P2=404&P3=2&P4=VzFG1OzNMJGZ9yUDO%2b%2b80TTwHKUwekBtim7StmnEfDsDoNdxADfedyewI1aL%2bNr9SI9J97T6u2SbBM0aSv0EEA%3d%3d | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
7004 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1724112530&P2=404&P3=2&P4=VzFG1OzNMJGZ9yUDO%2b%2b80TTwHKUwekBtim7StmnEfDsDoNdxADfedyewI1aL%2bNr9SI9J97T6u2SbBM0aSv0EEA%3d%3d | unknown | — | — | whitelisted |
4208 | svchost.exe | GET | 206 | 152.199.19.161:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/8f2381c2-652d-48a2-86f6-19cb7757f5dc?P1=1724112530&P2=404&P3=2&P4=VzFG1OzNMJGZ9yUDO%2b%2b80TTwHKUwekBtim7StmnEfDsDoNdxADfedyewI1aL%2bNr9SI9J97T6u2SbBM0aSv0EEA%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4280 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4424 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5336 | SearchApp.exe | 23.36.162.68:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1664 | svchost.exe | 40.126.31.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1664 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|
regedit.exe | REGEDIT: CreateFile failed, GetLastError() = 2
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|