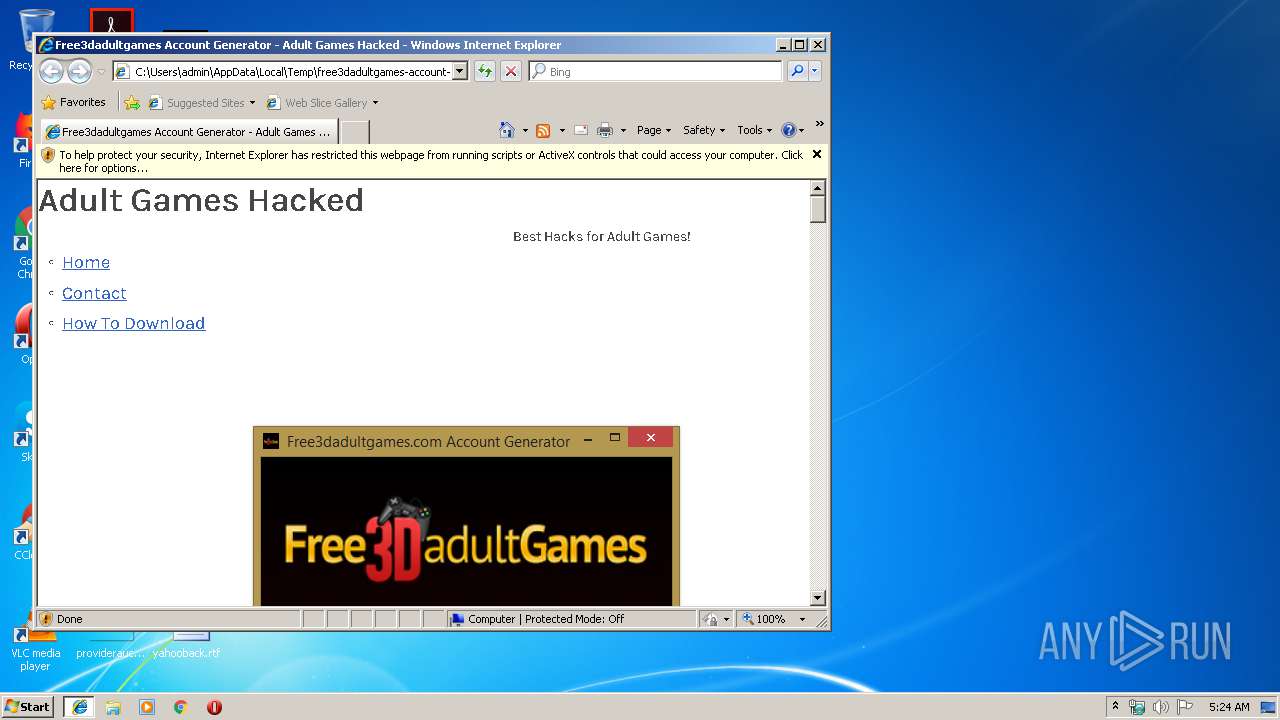
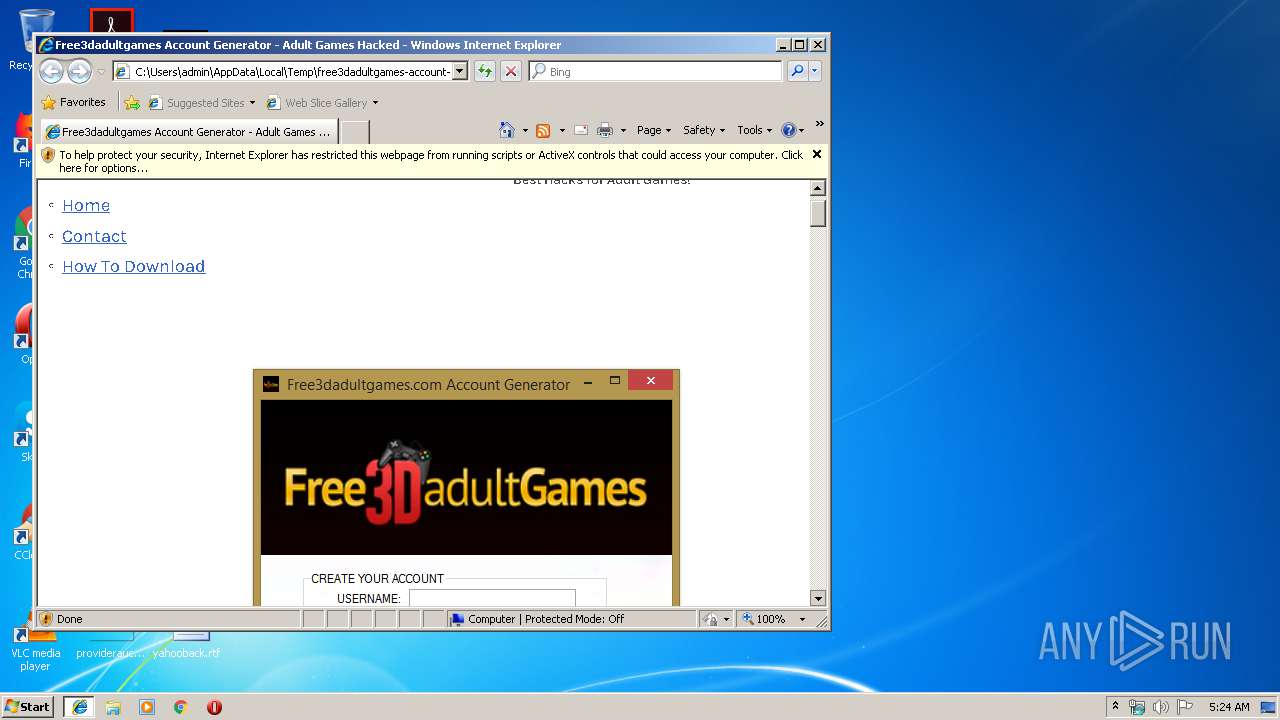
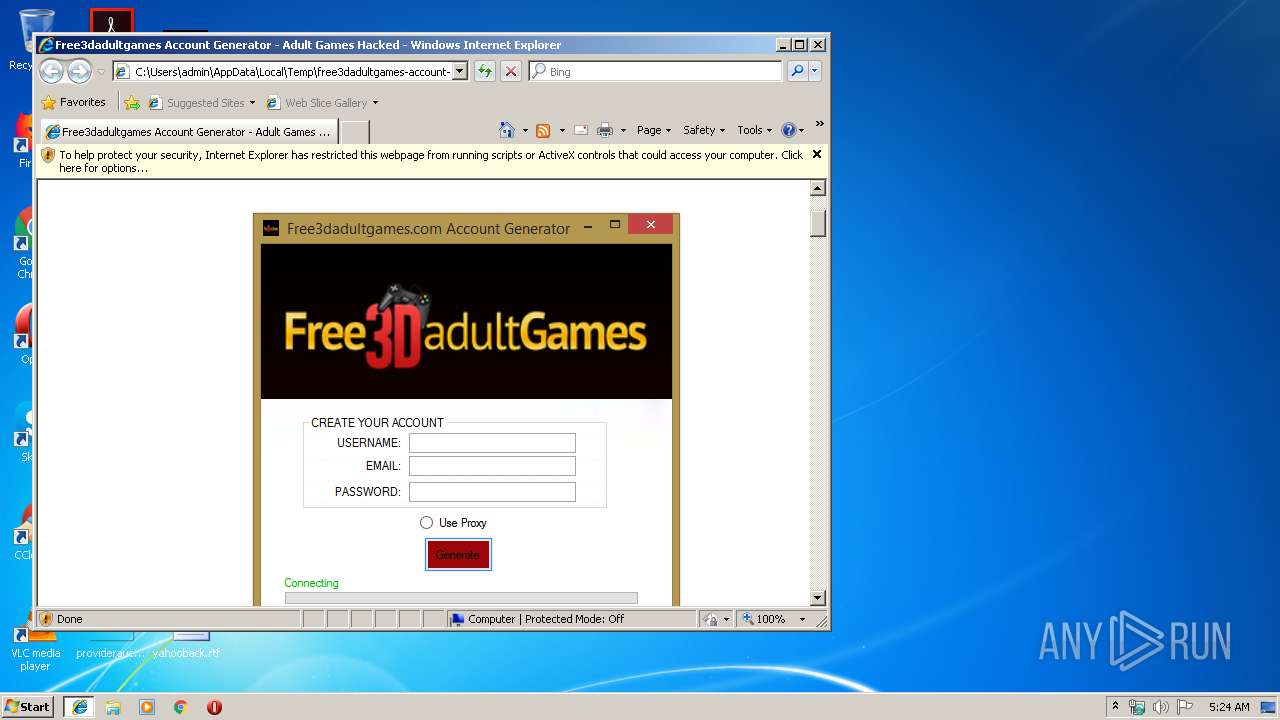
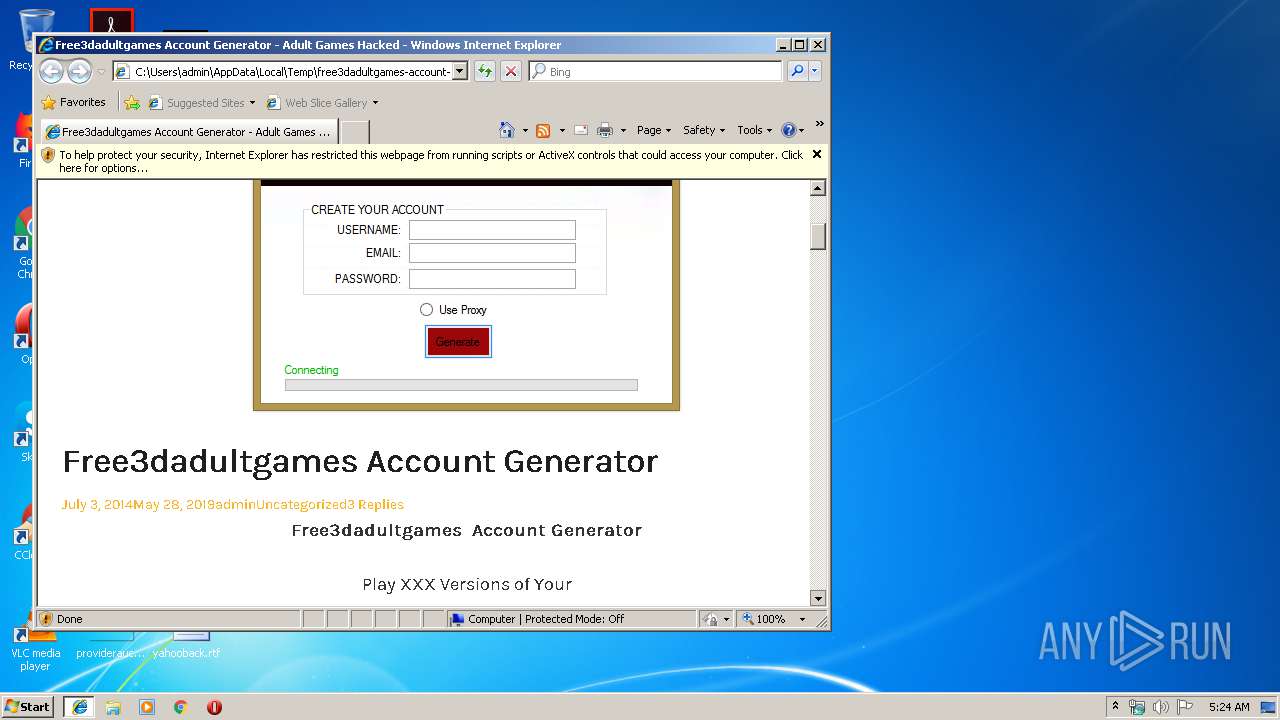
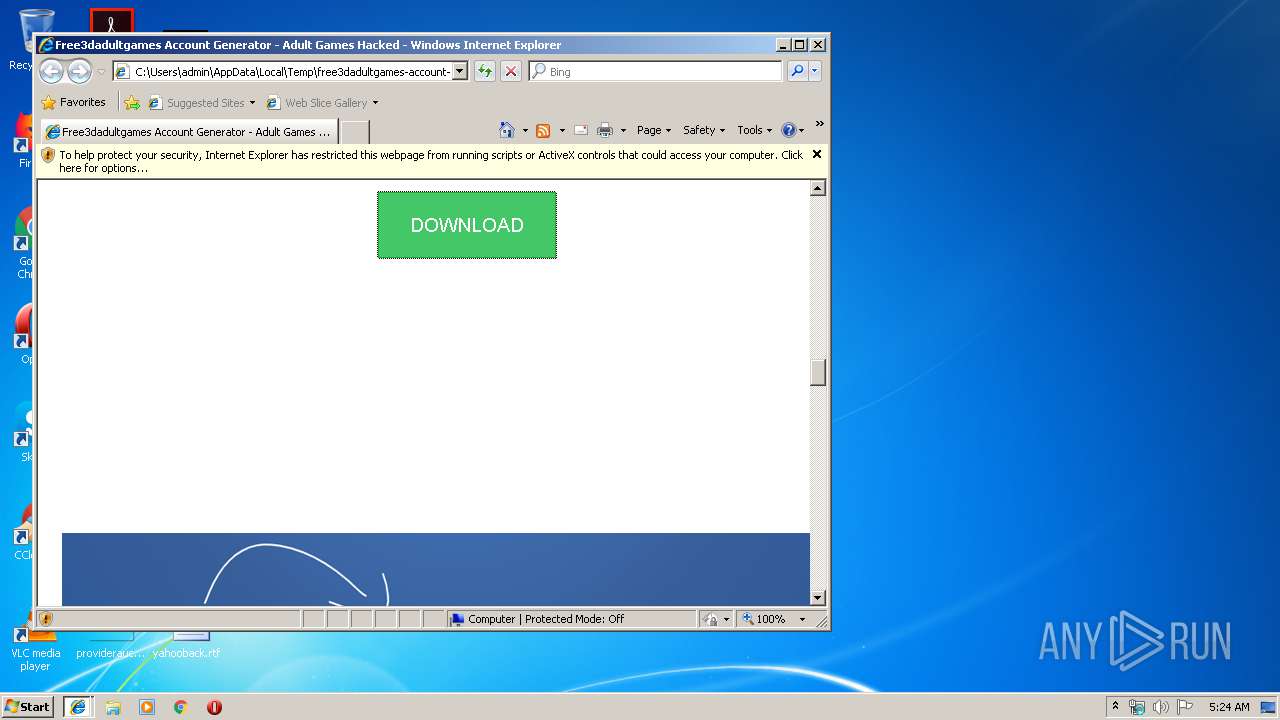
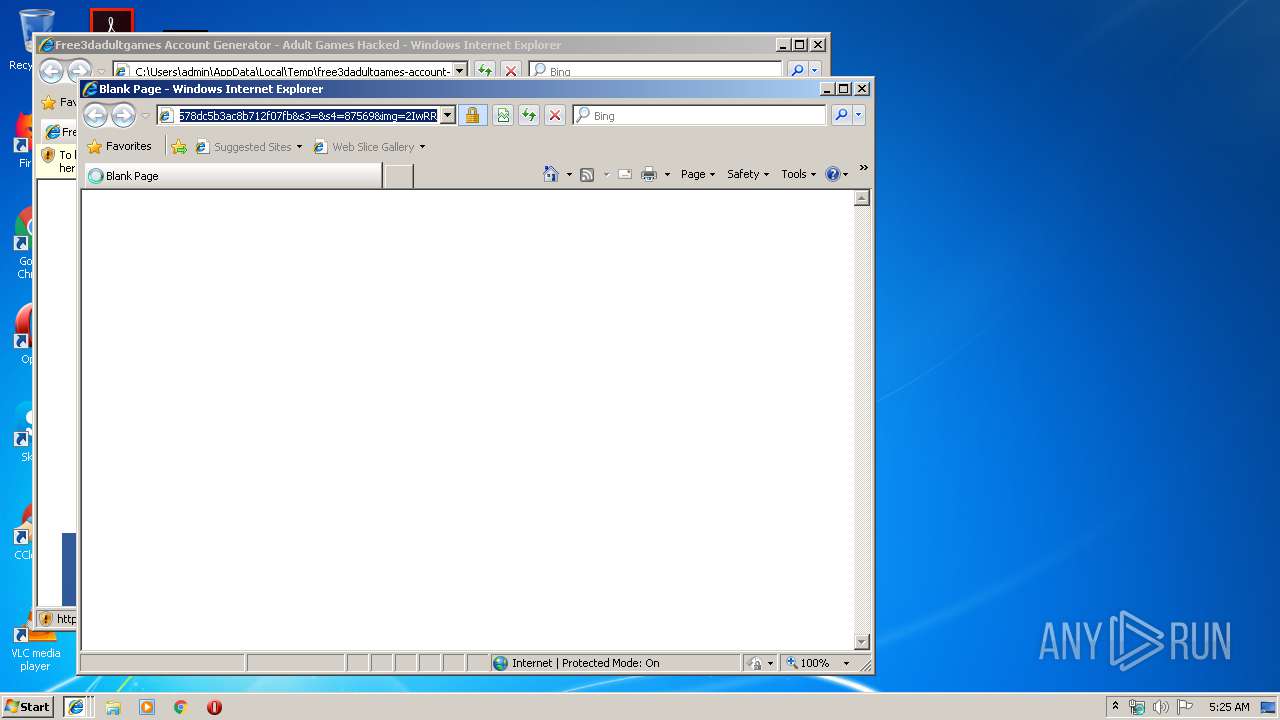
| download: | free3dadultgames-account-generator.html |
| Full analysis: | https://app.any.run/tasks/34269f5e-c512-41eb-81c3-ef2bfd8e505b |
| Verdict: | No threats detected |
| Analysis date: | July 23, 2019, 04:23:50 |
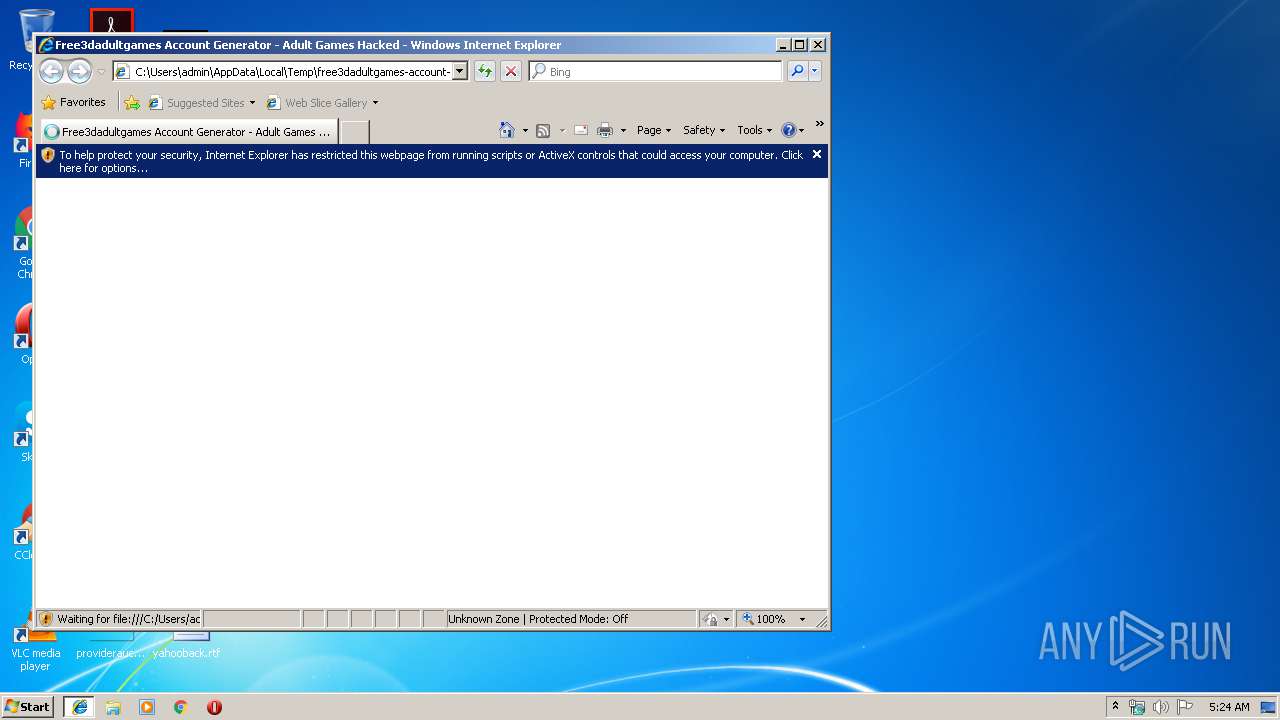
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 09F149D7527D08F96D3E5D1B6565469A |
| SHA1: | CFDDE2DC7F4FA6E6812FC54B1364F292ED879B37 |
| SHA256: | 5F697C16C76F5EA71307DDF9BBE76F618BD286FA446E0795DD99DBFB8CBE3769 |
| SSDEEP: | 768:zDDfS7Z6qK64r1LPeADCP2B4NJ5FsnmOLta1F3Bdg5bN2GAkT2qwLSt8Nvut1QA+:zZPeAeP2BThGFRdAKADnaI2d5 |
MALICIOUS
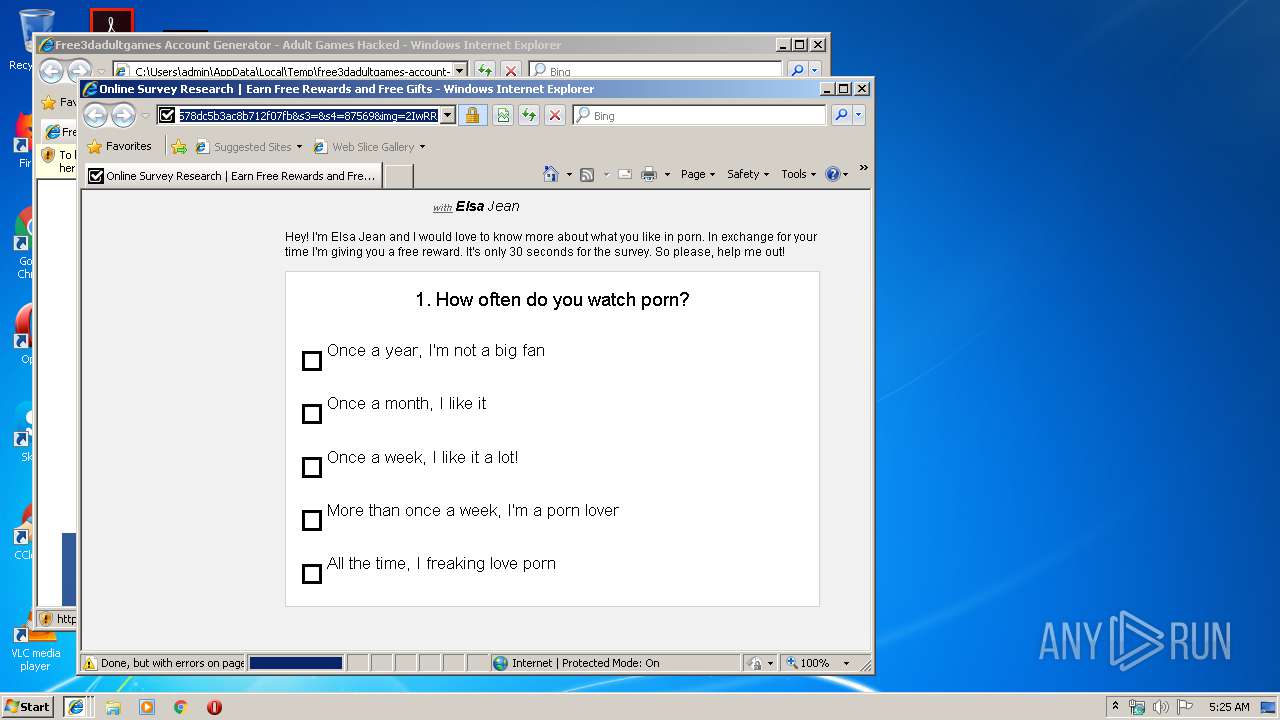
No malicious indicators.SUSPICIOUS
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4064)
INFO
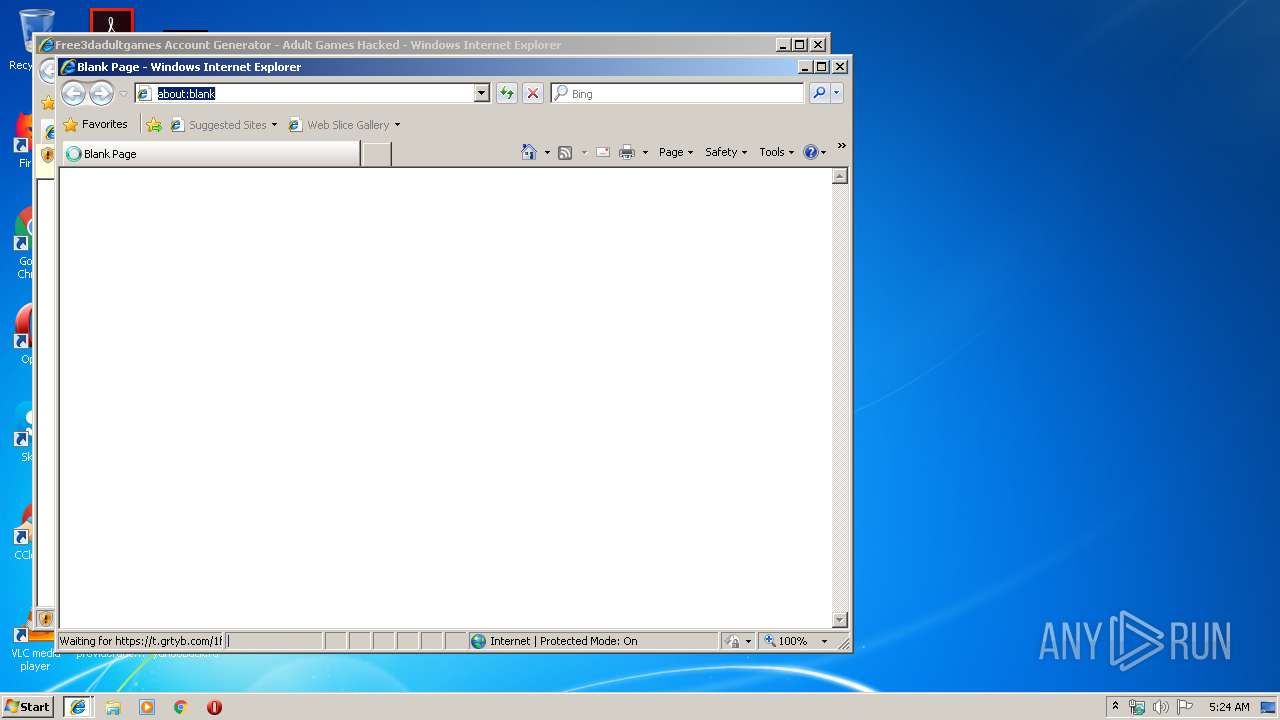
Changes internet zones settings
- iexplore.exe (PID: 2848)
Reads settings of System Certificates
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 2848)
Reads internet explorer settings
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 3776)
Reads Internet Cache Settings
- iexplore.exe (PID: 3804)
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 3776)
Application launched itself
- iexplore.exe (PID: 2848)
Creates files in the user directory
- iexplore.exe (PID: 2436)
- iexplore.exe (PID: 3776)
- iexplore.exe (PID: 2848)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 4064)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2848)
Changes settings of System certificates
- iexplore.exe (PID: 2848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | width=device-width, initial-scale=1 |
|---|---|
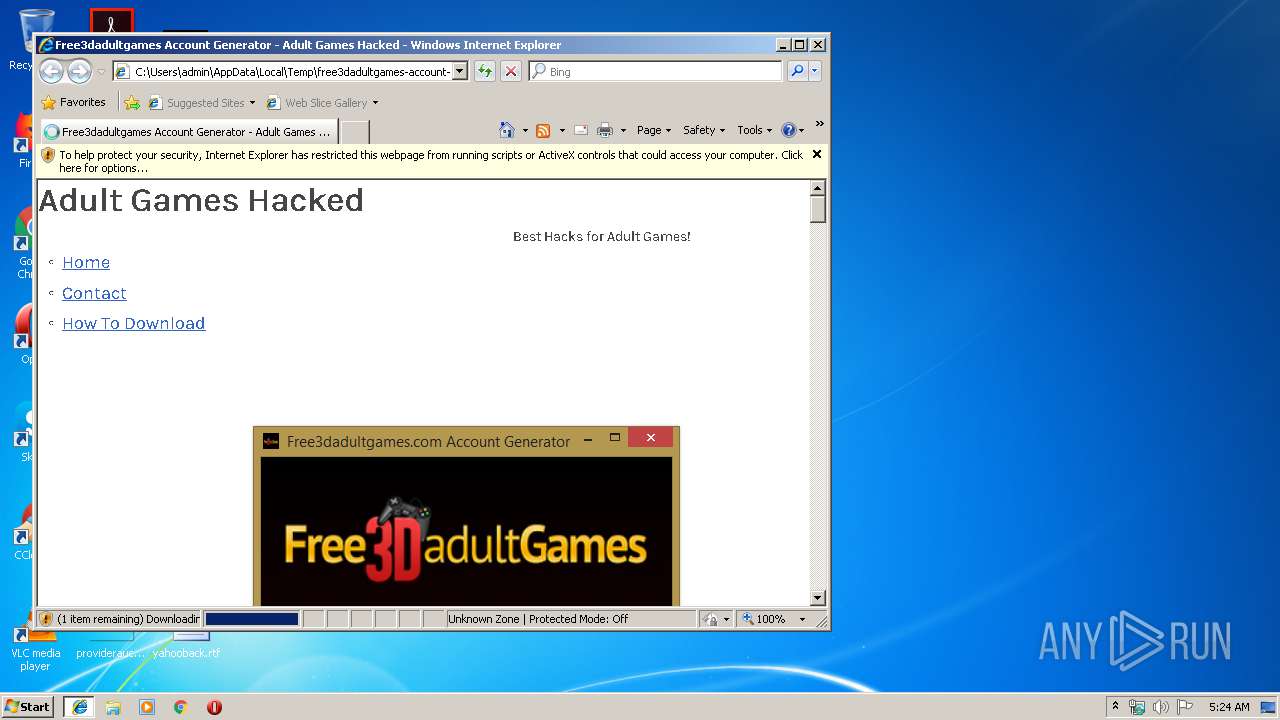
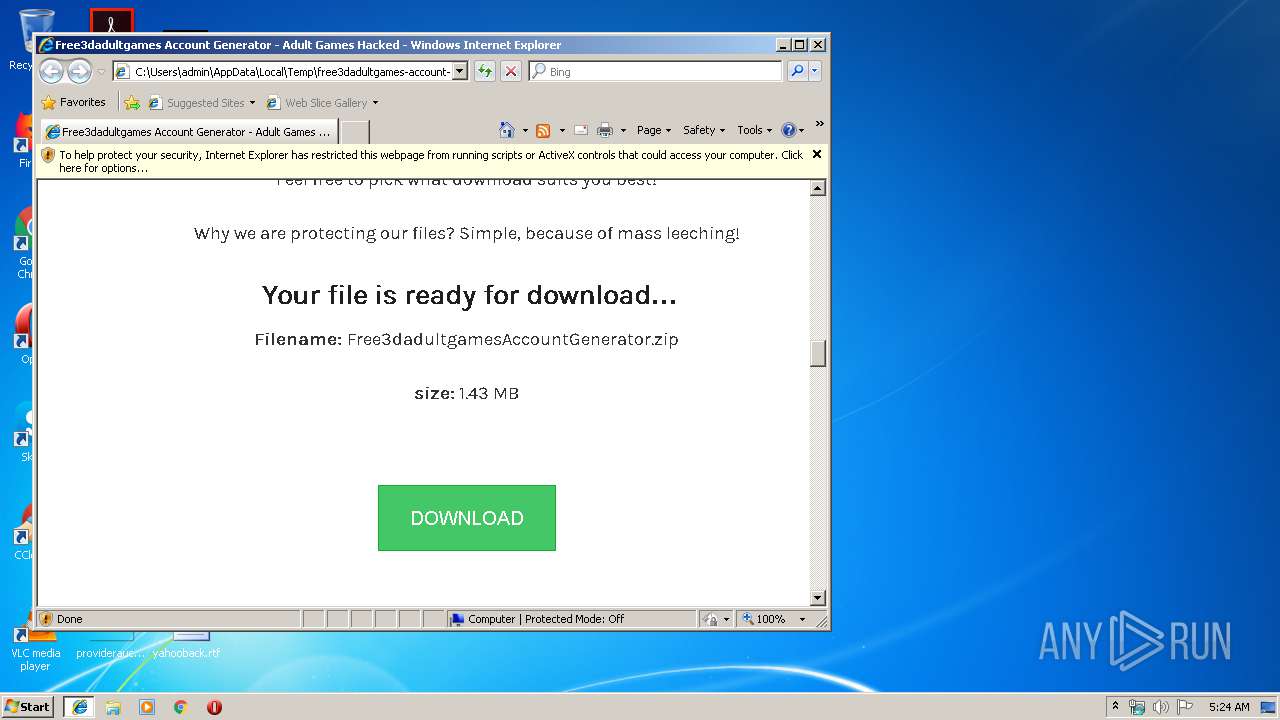
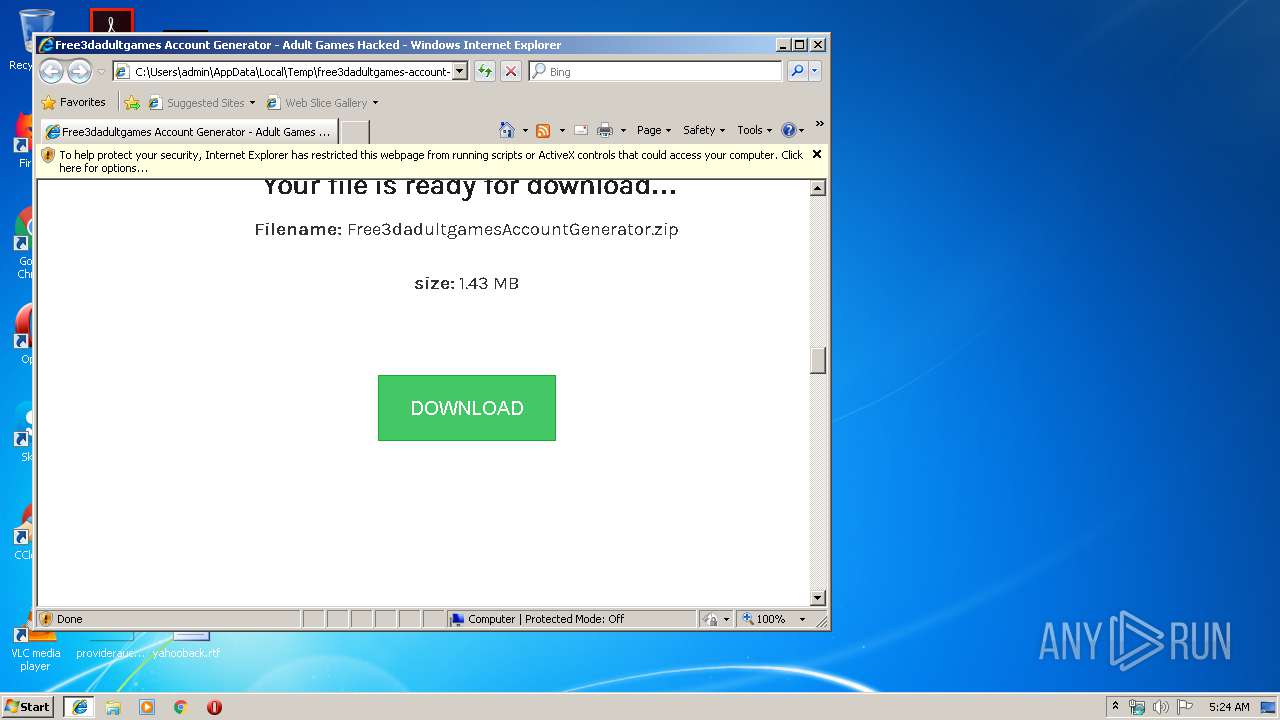
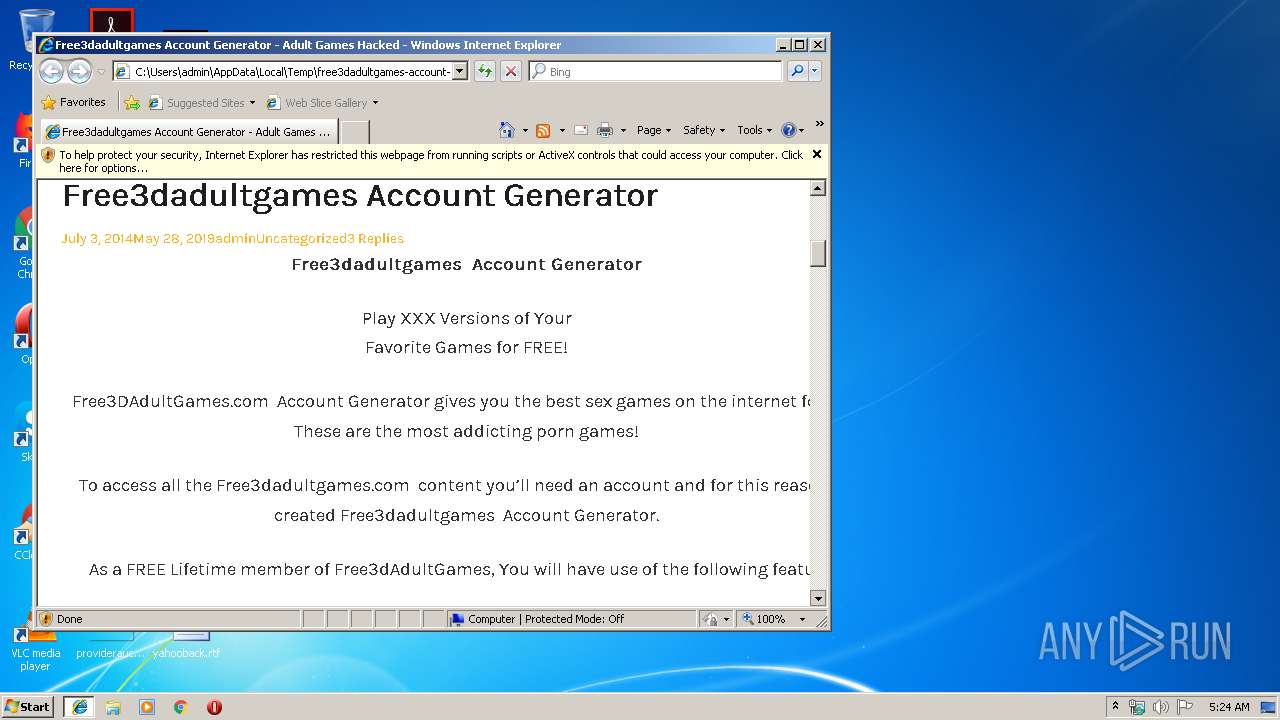
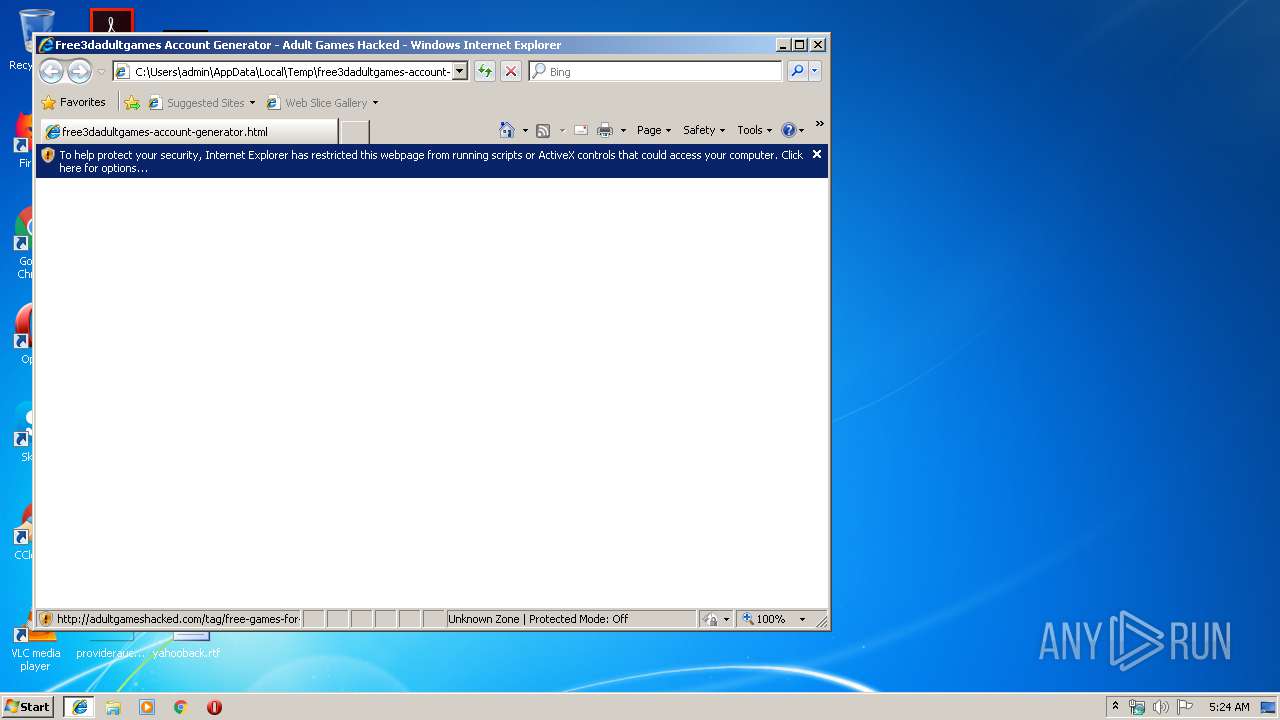
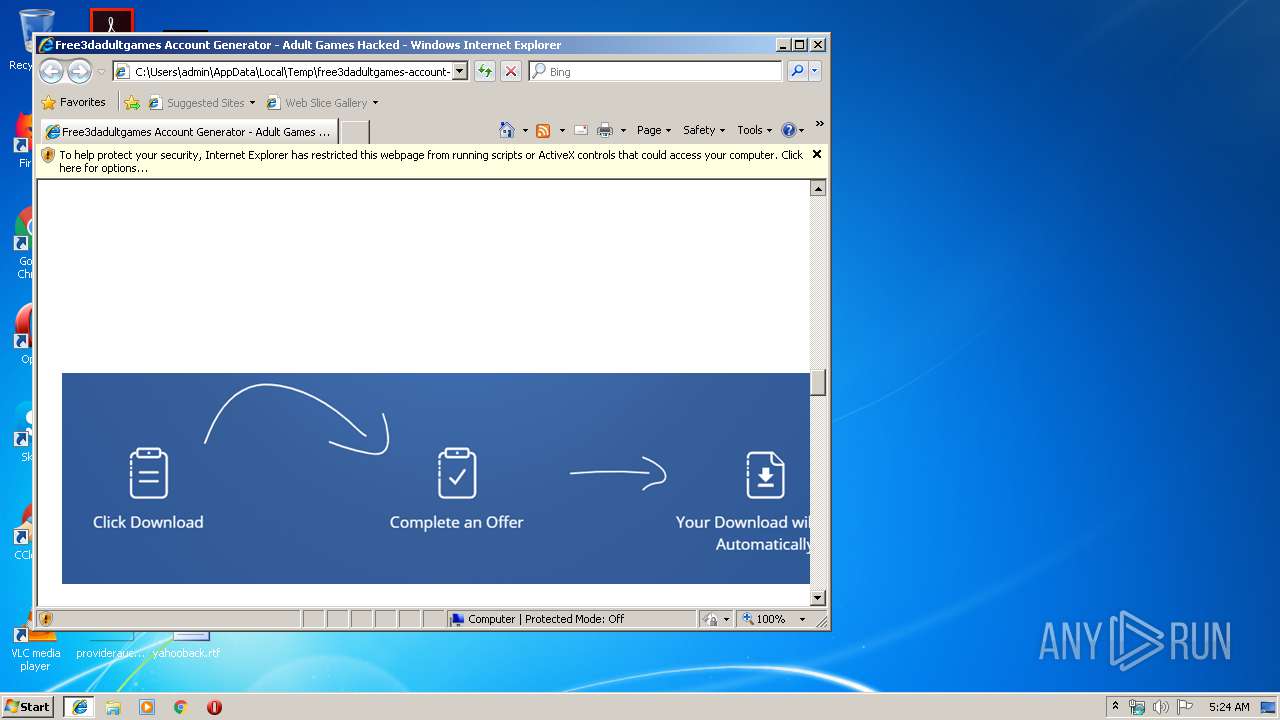
| Title: | Free3dadultgames Account Generator - Adult Games Hacked |
| twitterCard: | summary_large_image |
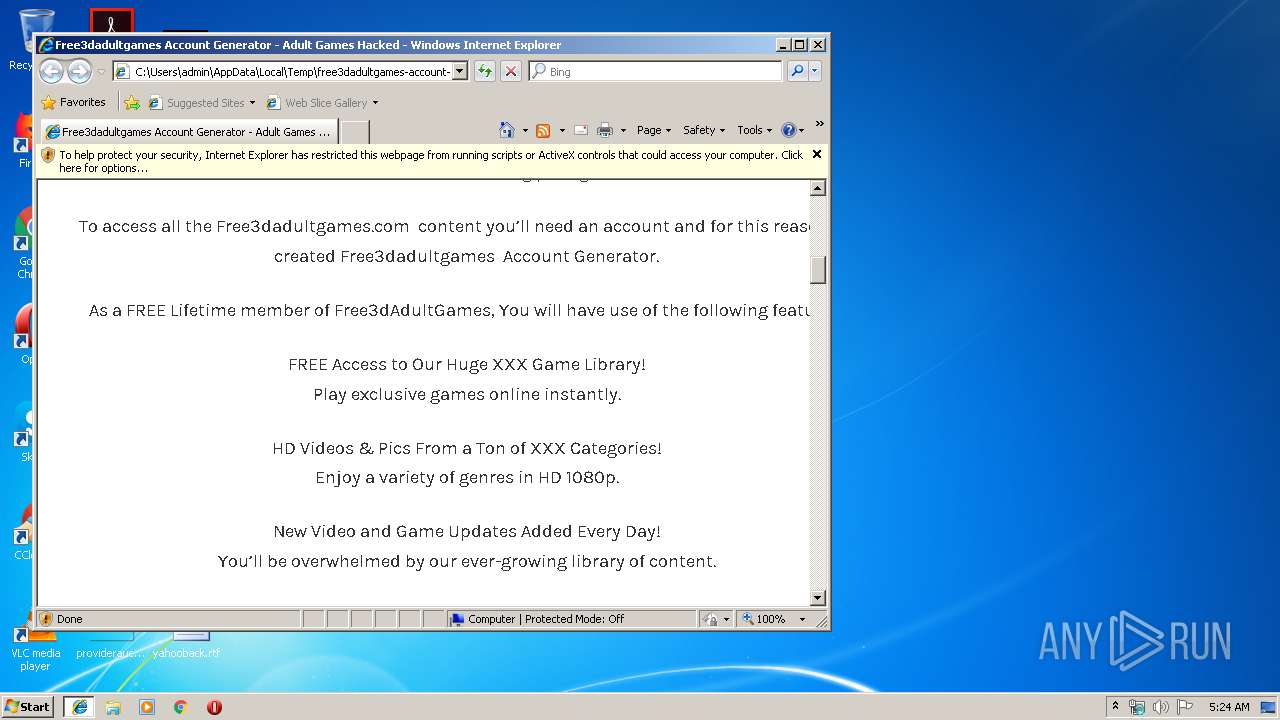
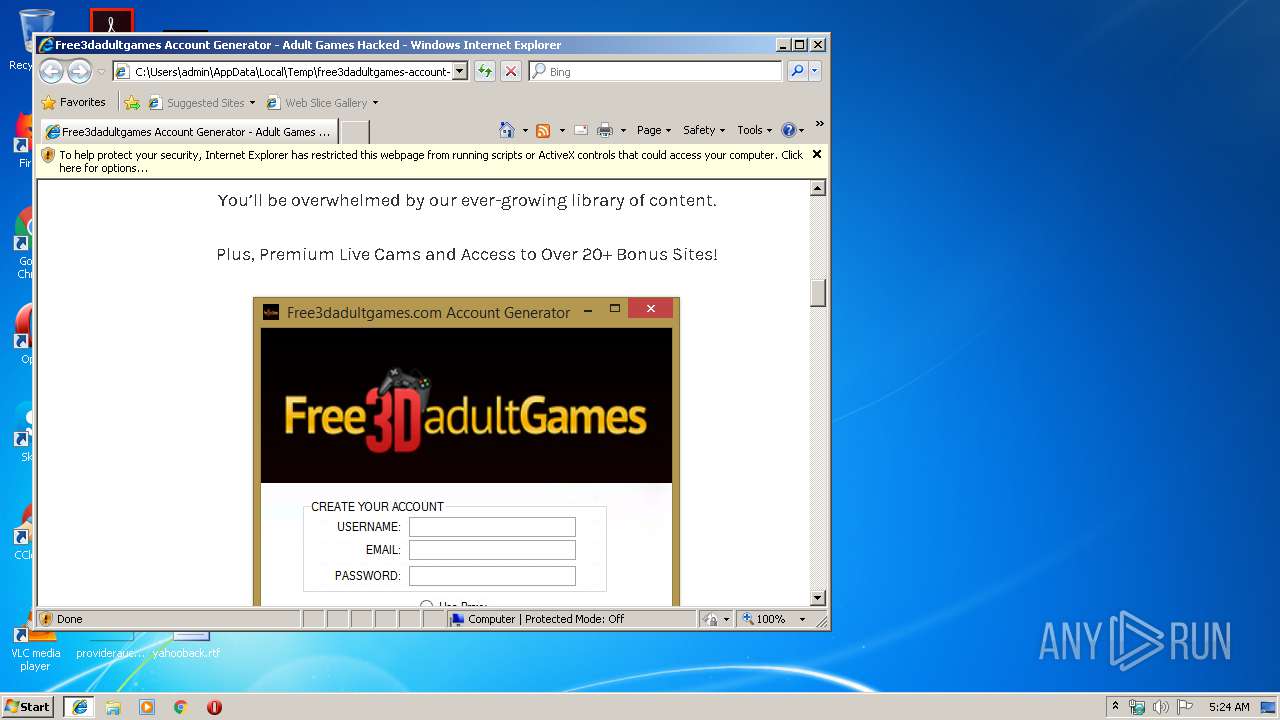
| twitterDescription: | Free3dadultgames Account Generator Play XXX Versions of Your Favorite Games for FREE! Free3DAdultGames.com Account Generator gives you the best sex games on the internet for free. These are the most addicting porn games! To access all the Free3dadultgames.com content you’ll need an account and for this reason we created Free3dadultgames Account Generator. As a FREE Lifetime… Read |
| twitterTitle: | Free3dadultgames Account Generator - Adult Games Hacked |
| twitterImage: | http://adultgameshacked.com/wp-content/uploads/2014/07/free3dadultgames1.png |
| Generator: | WordPress 5.2.2 |
Total processes
38
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2848 CREDAT:203009 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2848 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\free3dadultgames-account-generator.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3776 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2848 CREDAT:334081 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3804 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2848 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4064 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
Total events
1 023
Read events
839
Write events
180
Delete events
4
Modification events
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B790D7AD-AD01-11E9-B2FD-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2848) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307070002001700040018000B001E00 | |||
Executable files
0
Suspicious files
12
Text files
97
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2848 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\style[1].css | text | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\fontawesome[1].eot | eot | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\ie[1].css | text | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\faceboxmodal[1].css | text | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\faceboxmodal[1].js | html | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\widgets[1].js | text | |
MD5:— | SHA256:— | |||
| 3804 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\free3dadultgames1[1].png | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
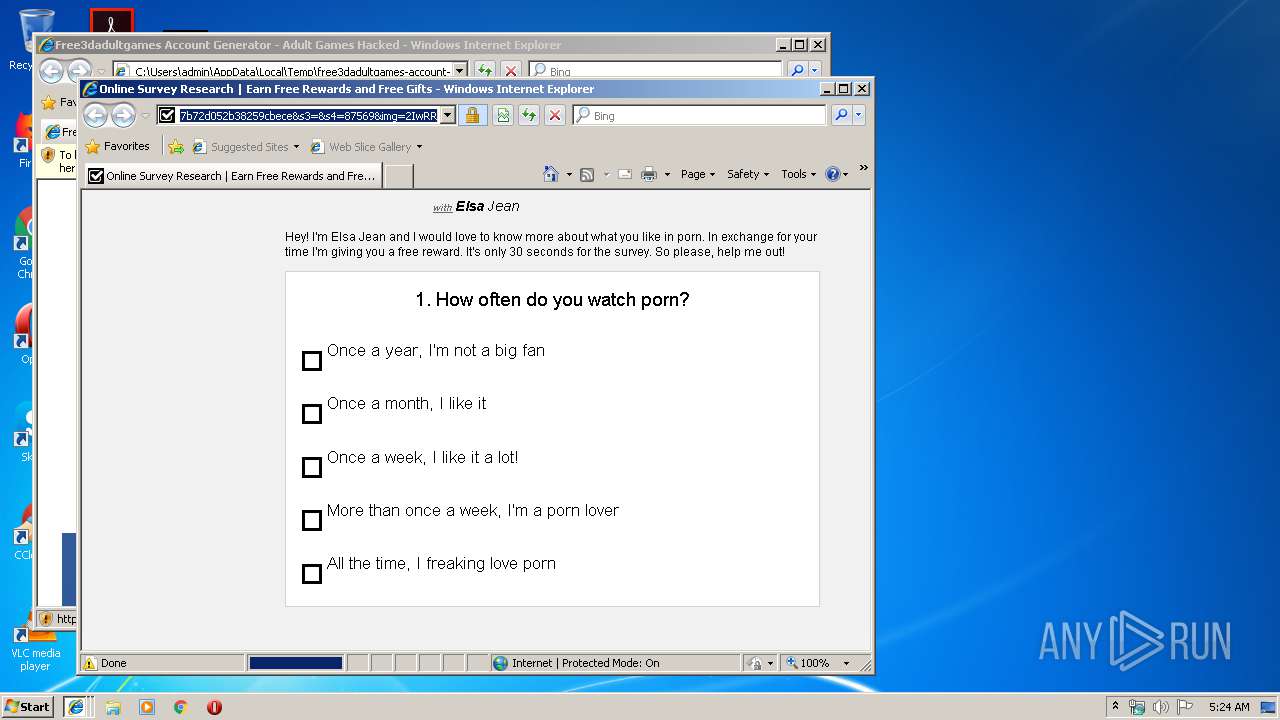
HTTP(S) requests
40
TCP/UDP connections
79
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | iexplore.exe | GET | — | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/themes/blogfeedly/js/custom.js?ver=1.6.0 | PL | — | — | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/themes/blogfeedly/fonts/fontawesome.eot?m20g1t | PL | eot | 4.66 Kb | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/themes/blogfeedly/style.css?ver=5.2.2 | PL | text | 9.05 Kb | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/themes/blogfeedly/css/ie.css?ver=1.6.0 | PL | text | 200 b | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/plugins/automatic-social-locker/css/faceboxmodal.css | PL | text | 719 b | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/uploads/2014/07/free3dadultgames1.png | PL | image | 52.5 Kb | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/uploads/2014/02/100-clean.png | PL | image | 85.4 Kb | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/plugins/automatic-social-locker/js/faceboxmodal.js | PL | html | 3.08 Kb | unknown |
3804 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/wp-content/uploads/2014/07/free3dadultgames.png | PL | image | 52.5 Kb | unknown |
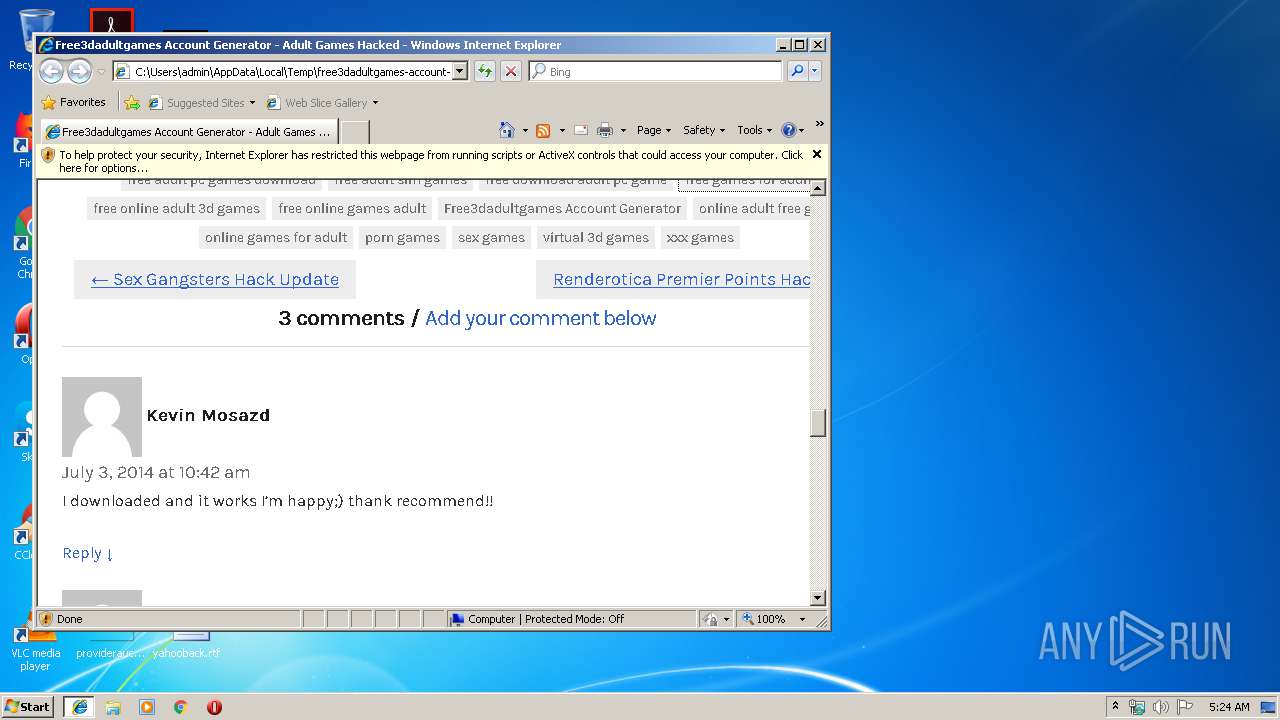
2436 | iexplore.exe | GET | 200 | 91.228.199.104:80 | http://adultgameshacked.com/tag/free-games-for-adult | PL | html | 6.54 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2848 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3804 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3804 | iexplore.exe | 91.228.199.104:80 | adultgameshacked.com | H88 S.A. | PL | unknown |
3804 | iexplore.exe | 172.217.23.163:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3804 | iexplore.exe | 192.0.78.9:443 | wordpress.com | Automattic, Inc | US | malicious |
3804 | iexplore.exe | 31.13.92.14:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2436 | iexplore.exe | 91.228.199.104:80 | adultgameshacked.com | H88 S.A. | PL | unknown |
2436 | iexplore.exe | 31.13.92.14:80 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
2436 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2436 | iexplore.exe | 93.184.220.66:443 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
adultgameshacked.com |
| unknown |
connect.facebook.net |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
platform.twitter.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
wordpress.com |
| whitelisted |
i.imgur.com |
| malicious |
1.gravatar.com |
| whitelisted |