| File name: | MEMZ.bat |
| Full analysis: | https://app.any.run/tasks/ed9a1b7f-8884-4f50-a755-e7c1cd9cd8af |
| Verdict: | Malicious activity |
| Analysis date: | December 14, 2024, 01:10:04 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 13A43C26BB98449FD82D2A552877013A |
| SHA1: | 71EB7DC393AC1F204488E11F5C1EEF56F1E746AF |
| SHA256: | 5F52365ACCB76D679B2B3946870439A62EB8936B9A0595F0FB0198138106B513 |
| SSDEEP: | 384:nnLhRNiqt0kCH2LR0GPXxGiZgCz+KG/yKhLdW79HOli+lz3:nLhRN9t0SR4iZtzlREBWhuF |
MALICIOUS
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 1520)
Uses base64 encoding (SCRIPT)
- cscript.exe (PID: 1520)
SUSPICIOUS
The process executes JS scripts
- cmd.exe (PID: 448)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 1520)
Script creates XML DOM node (SCRIPT)
- cscript.exe (PID: 1520)
Creates XML DOM element (SCRIPT)
- cscript.exe (PID: 1520)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 1520)
Sets XML DOM element text (SCRIPT)
- cscript.exe (PID: 1520)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 1520)
Creates a Folder object (SCRIPT)
- cscript.exe (PID: 1520)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 1520)
Executable content was dropped or overwritten
- cscript.exe (PID: 1520)
The executable file from the user directory is run by the CMD process
- MEMZ.exe (PID: 5604)
- MEMZ.exe (PID: 3732)
- MEMZ.exe (PID: 5616)
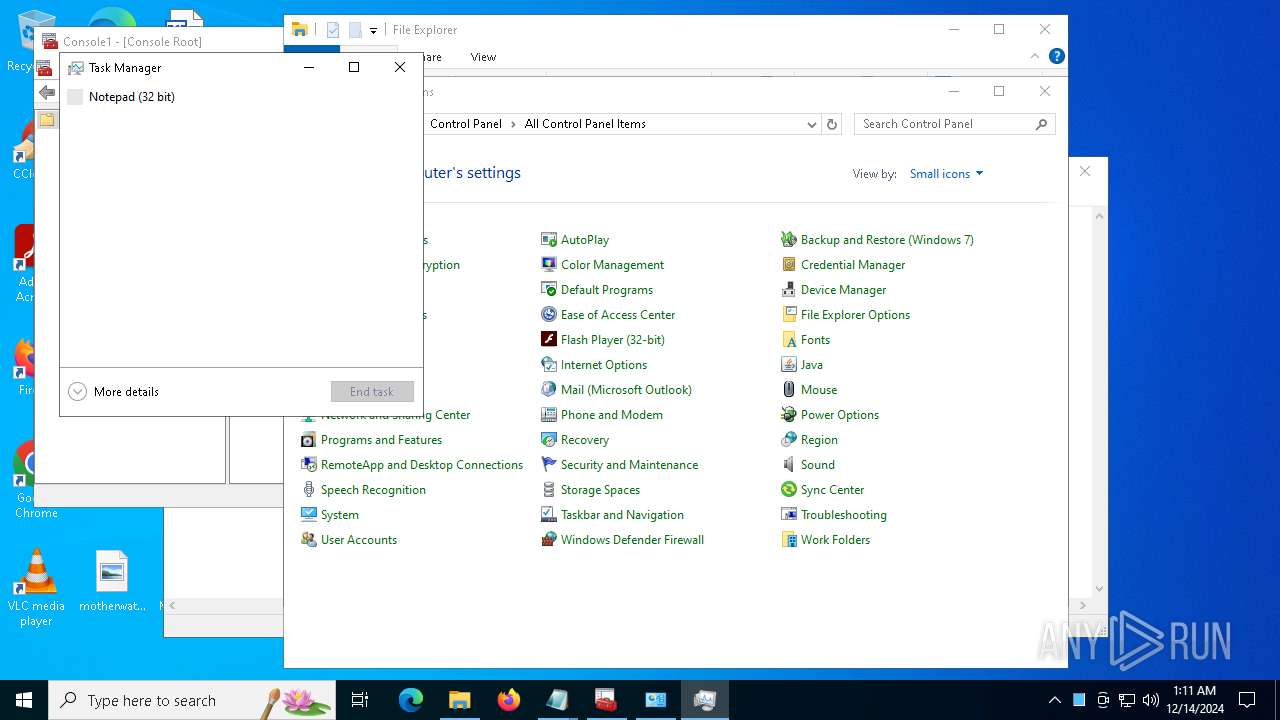
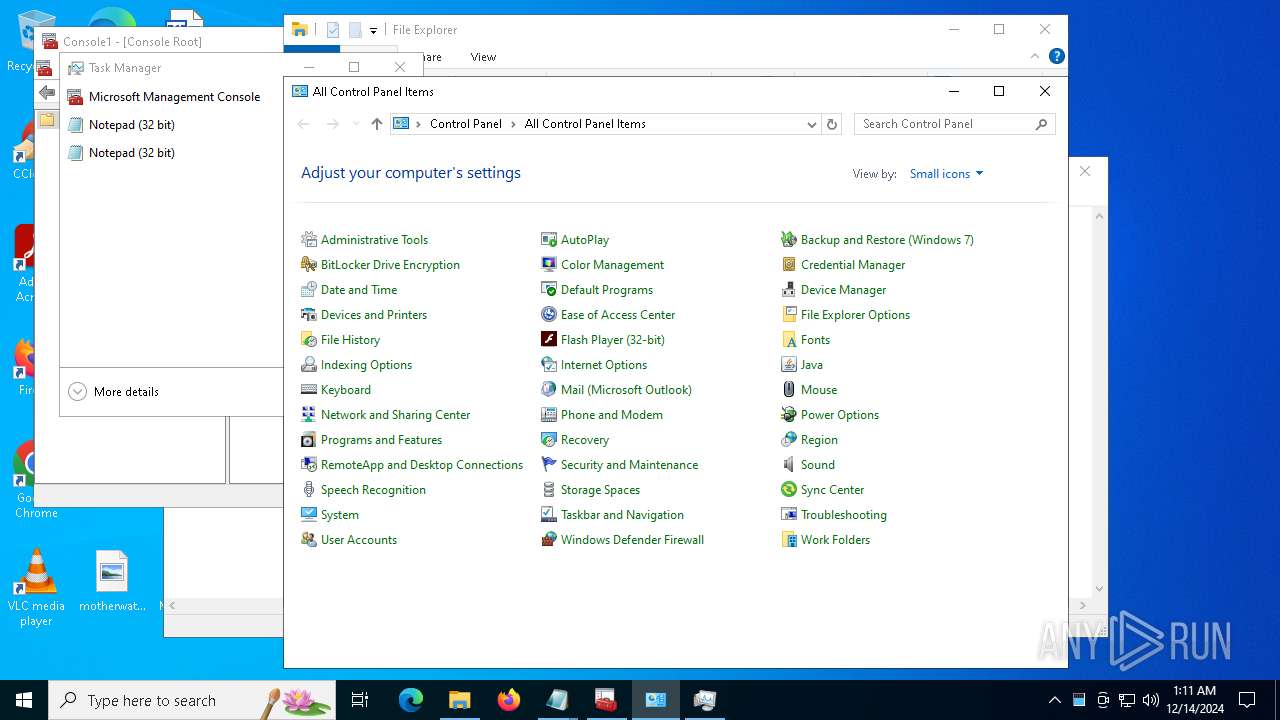
Application launched itself
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 5872)
Creates file in the systems drive root
- MEMZ.exe (PID: 1740)
- notepad.exe (PID: 2076)
- notepad.exe (PID: 3820)
- MEMZ.exe (PID: 2012)
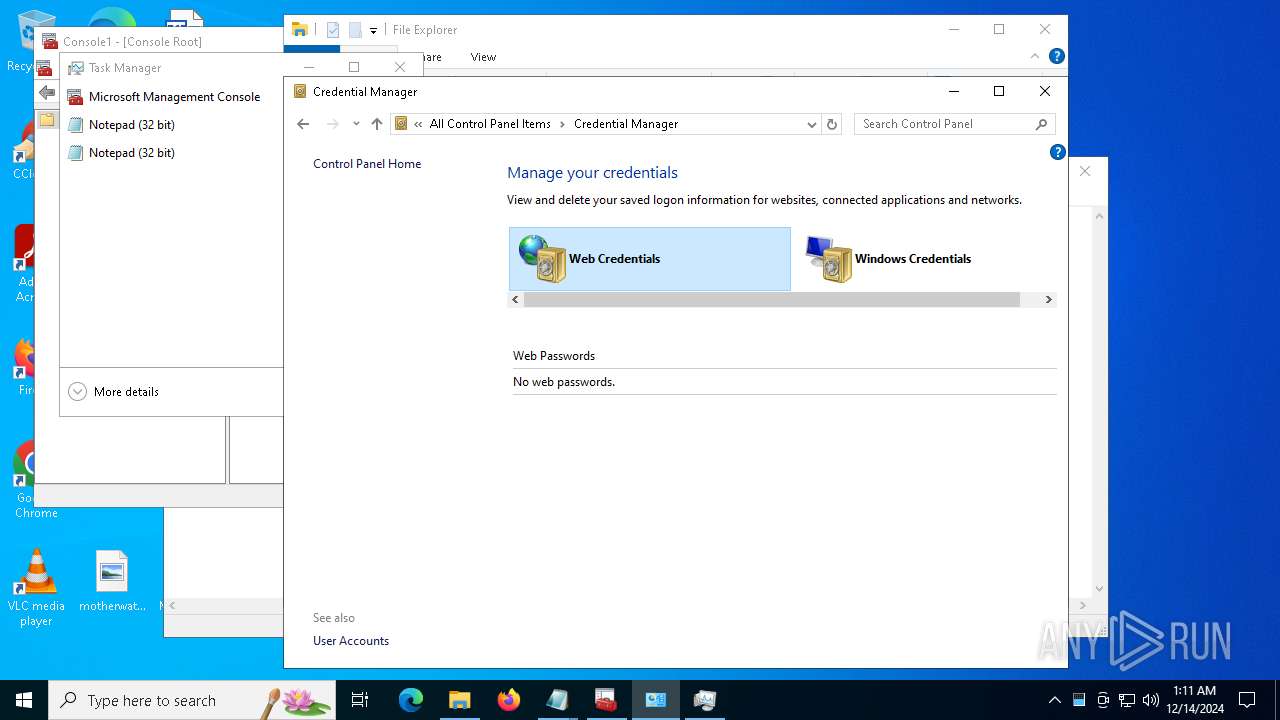
Reads security settings of Internet Explorer
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 5872)
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 2012)
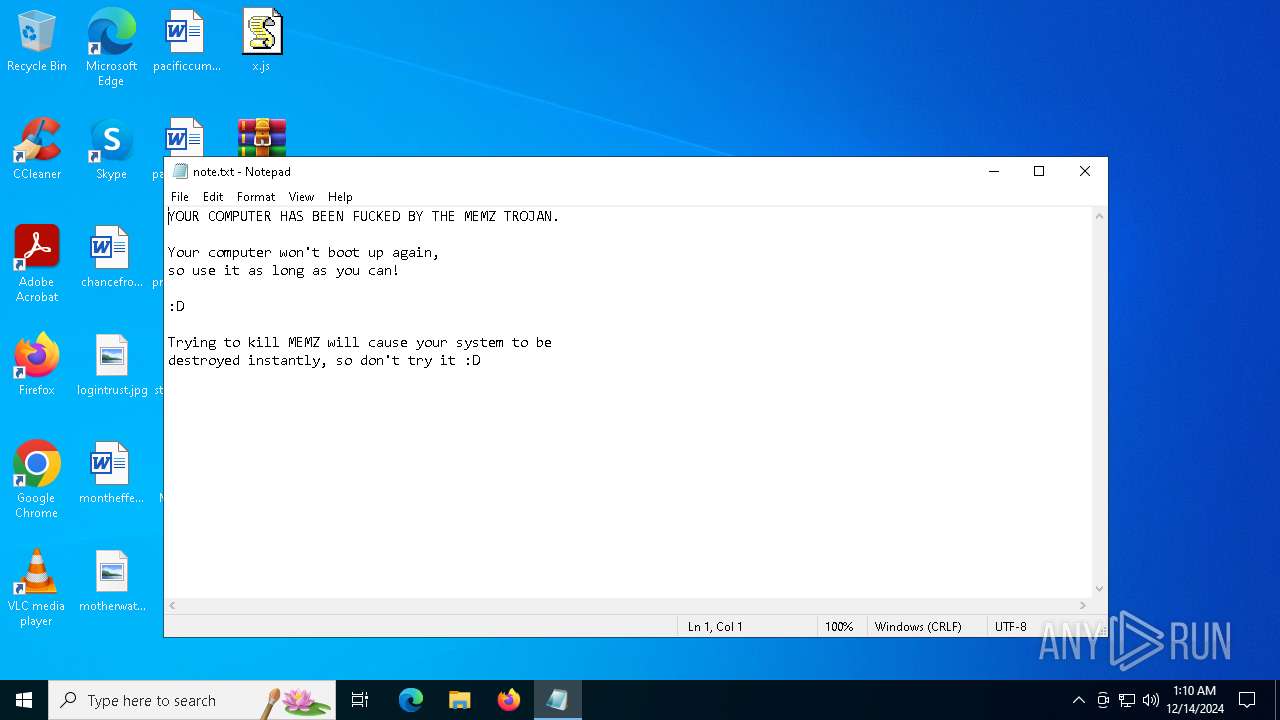
Start notepad (likely ransomware note)
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 2012)
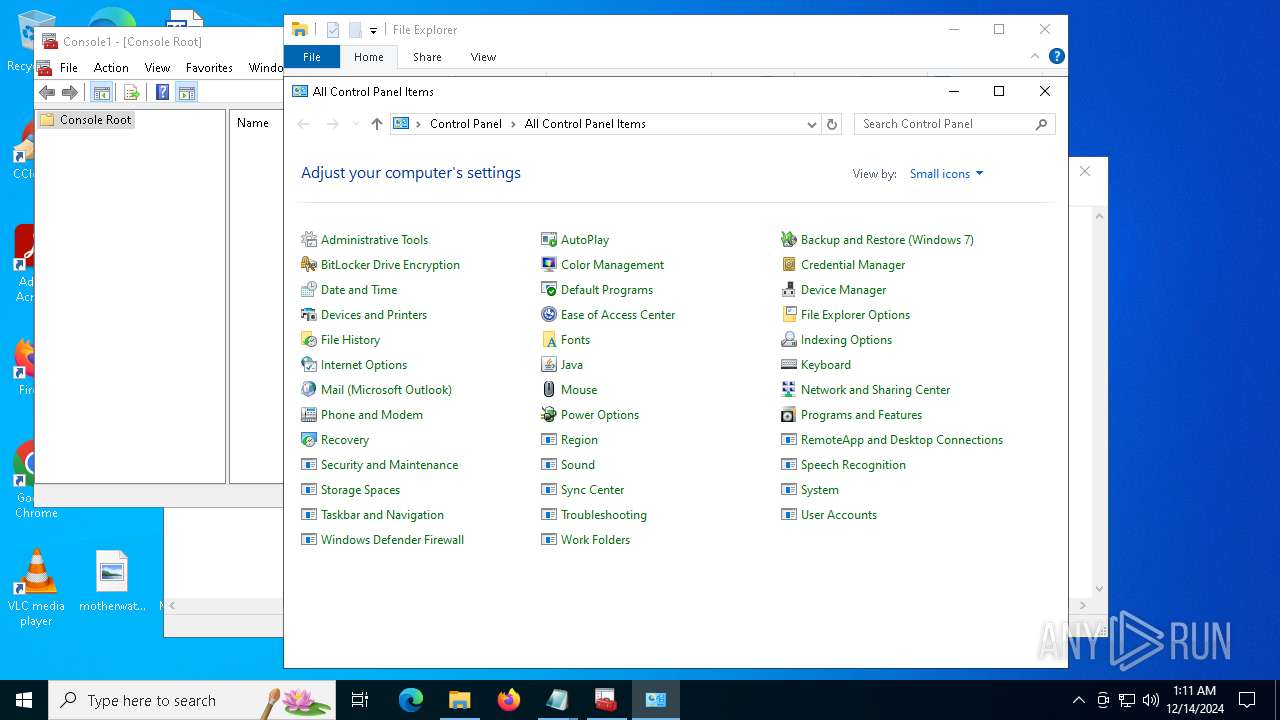
INFO
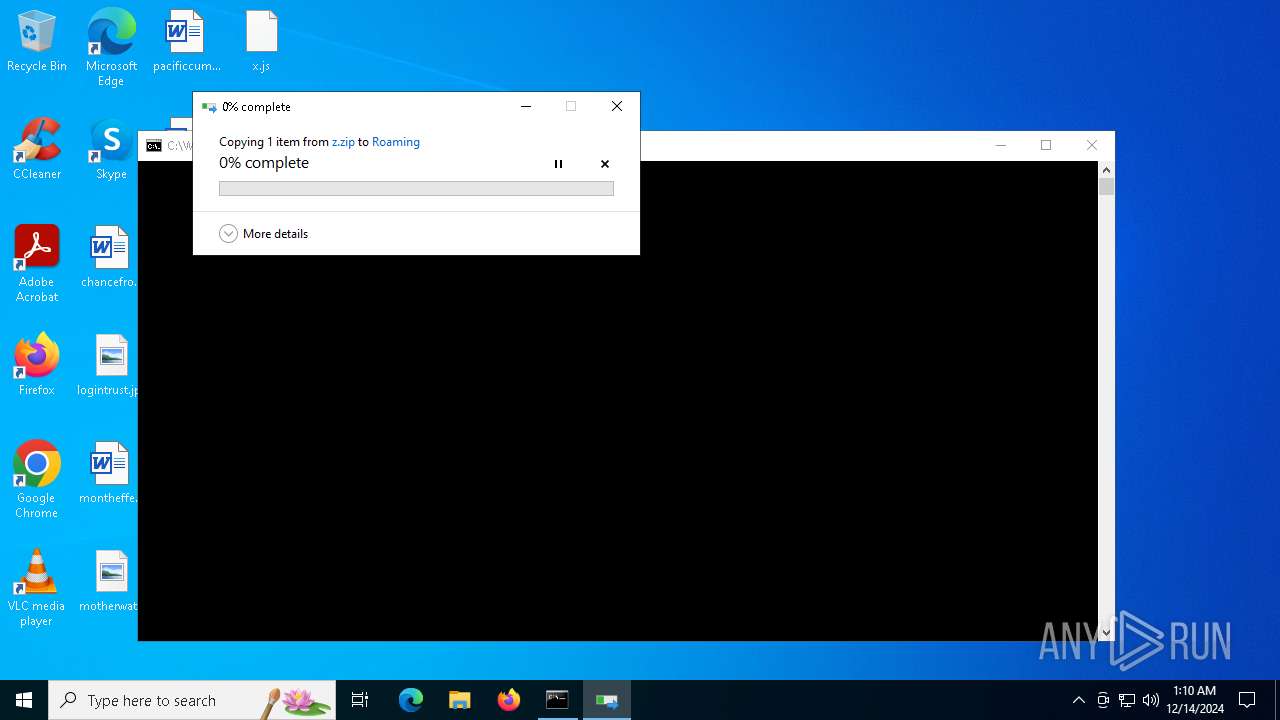
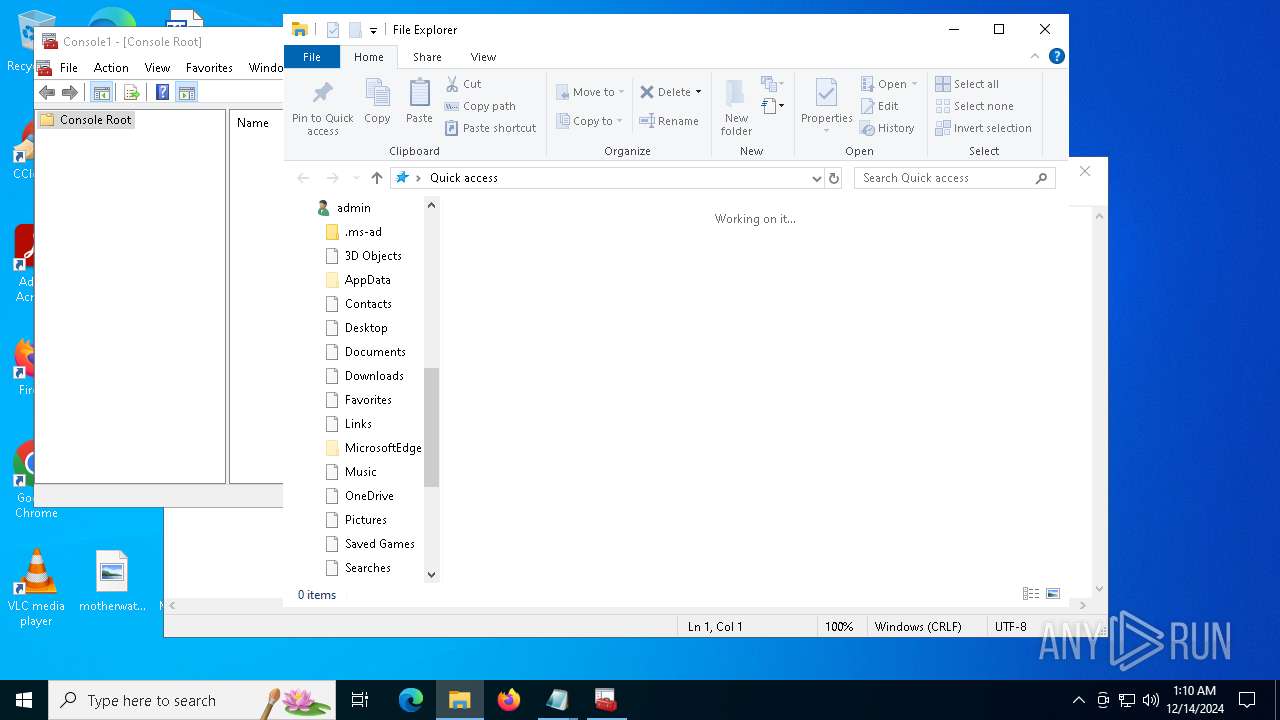
Creates files or folders in the user directory
- cscript.exe (PID: 1520)
- Taskmgr.exe (PID: 5776)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1520)
- notepad.exe (PID: 2076)
- mmc.exe (PID: 5076)
- mmc.exe (PID: 8)
- Taskmgr.exe (PID: 5776)
- explorer.exe (PID: 4244)
- calc.exe (PID: 7912)
- OpenWith.exe (PID: 8016)
- notepad.exe (PID: 3820)
The process uses the downloaded file
- cscript.exe (PID: 1520)
- cmd.exe (PID: 448)
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 5872)
- MEMZ.exe (PID: 2012)
Reads the computer name
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 5872)
- identity_helper.exe (PID: 6416)
- MEMZ.exe (PID: 2012)
Process checks computer location settings
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 5872)
- MEMZ.exe (PID: 2012)
Checks supported languages
- MEMZ.exe (PID: 4528)
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 5572)
- MEMZ.exe (PID: 5240)
- MEMZ.exe (PID: 4952)
- MEMZ.exe (PID: 5872)
- MEMZ.exe (PID: 2496)
- MEMZ.exe (PID: 4876)
- MEMZ.exe (PID: 3568)
- MEMZ.exe (PID: 1412)
- MEMZ.exe (PID: 5616)
- MEMZ.exe (PID: 5252)
- MEMZ.exe (PID: 2012)
- identity_helper.exe (PID: 6416)
- MEMZ.exe (PID: 5964)
Manual execution by a user
- MEMZ.exe (PID: 5460)
- MEMZ.exe (PID: 5872)
- msedge.exe (PID: 5972)
Reads the machine GUID from the registry
- MEMZ.exe (PID: 1740)
- MEMZ.exe (PID: 2012)
Sends debugging messages
- mmc.exe (PID: 5076)
Application launched itself
- msedge.exe (PID: 1016)
- msedge.exe (PID: 5972)
Reads Environment values
- identity_helper.exe (PID: 6416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
83
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 8 | "C:\WINDOWS\system32\mmc.exe" | C:\Windows\System32\mmc.exe | — | mmc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3772 --field-trial-handle=2252,i,13749372482569277237,1712378408806141846,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://softonic.com/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 448 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\MEMZ.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument http://play.clubpenguin.com/ | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | MEMZ.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x310,0x314,0x318,0x308,0x320,0x7ff820af5fd8,0x7ff820af5fe4,0x7ff820af5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1412 | "C:\Users\admin\Desktop\MEMZ.exe" /watchdog | C:\Users\admin\Desktop\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1520 | cscript x.js | C:\Windows\System32\cscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1740 | "C:\Users\admin\AppData\Roaming\MEMZ.exe" /main | C:\Users\admin\AppData\Roaming\MEMZ.exe | — | MEMZ.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 1856 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --mojo-platform-channel-handle=3988 --field-trial-handle=2252,i,13749372482569277237,1712378408806141846,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
19 262
Read events
19 156
Write events
104
Delete events
2
Modification events
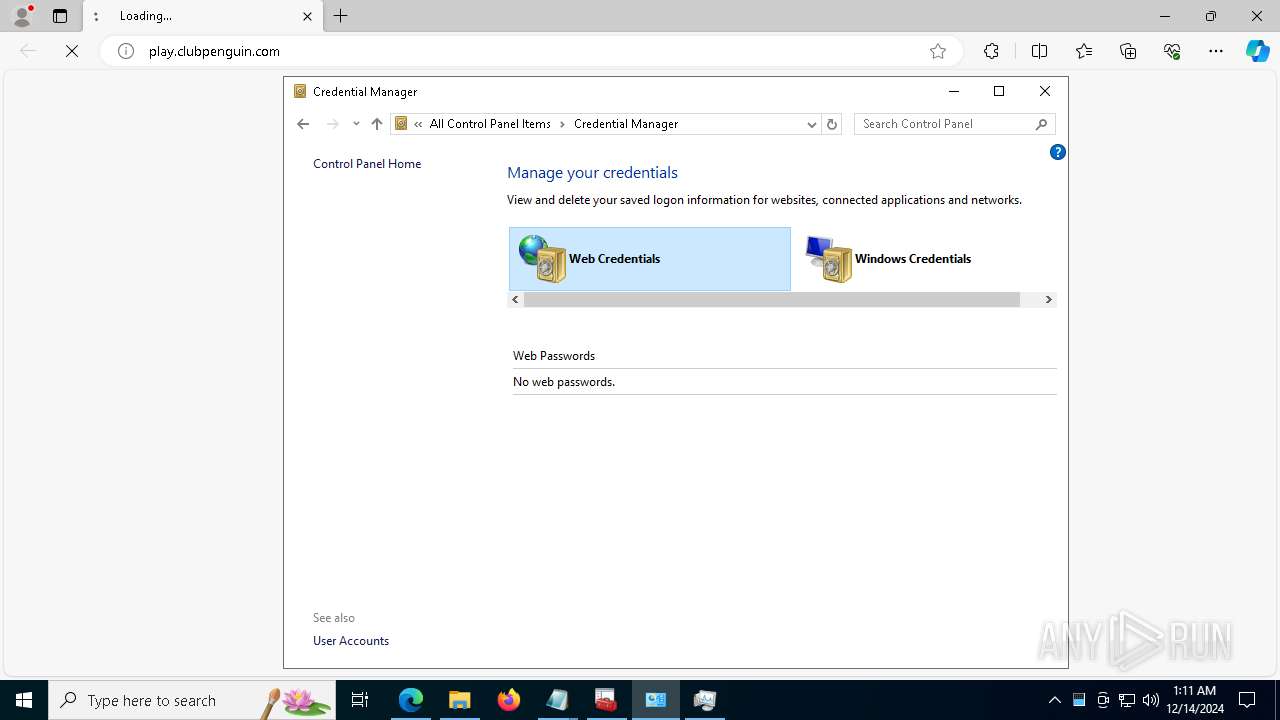
| (PID) Process: | (1520) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 010000000000000068D63DEFC44DDB01 | |||
| (PID) Process: | (1520) cscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script\Settings\Telemetry\cscript.exe |
| Operation: | write | Name: | JScriptSetScriptStateStarted |
Value: 1672130000000000 | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 0000000003000000040000000E000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (5776) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | delete value | Name: | Preferences |
Value: | |||
| (PID) Process: | (5776) Taskmgr.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\TaskManager |
| Operation: | write | Name: | Preferences |
Value: 0D00000060000000600000003400000034000000AF010000A8010000010000000000008000000080D8010080DF010080000100010000008000000080A802008058020080E803000000000000000000000F00000001000000A4DE8E000000000000000000EA000000000000008990000000000000FF000000010150020D000000E0DE8E0000000000FFFFFFFF96000000000000008B90000001000000000000000010100103000000F4DE8E0000000000FFFFFFFF78000000000000008C900000020000000000000001021200040000000CDF8E0000000000FFFFFFFF96000000000000008D900000030000000000000000011001020000002CDF8E0000000000FFFFFFFF32000000000000008A9000000400000000000000000820010500000040DF8E0000000000FFFFFFFFC8000000000000008E9000000500000000000000000110010600000064DF8E0000000000FFFFFFFF04010000000000008F9000000600000000000000000110010700000088DF8E0000000000FFFFFFFF49000000490000009090000007000000000000000004250008000000C8DE8E0000000000FFFFFFFF49000000490000009190000008000000000000000004250009000000A8DF8E0000000000FFFFFFFF4900000049000000929000000900000000000000000425080A000000BCDF8E0000000000FFFFFFFF4900000049000000939000000A00000000000000000425080B000000D8DF8E0000000000FFFFFFFF490000004900000039A000000B00000000000000000425091C000000F8DF8E0000000000FFFFFFFFC8000000000000003AA000000C00000000000000000110091D00000020E08E0000000000FFFFFFFF64000000000000004CA000000D00000000000000000215081E00000040E08E0000000000FFFFFFFF64000000000000004DA000000E0000000000000000021508030000000A00000001000000A4DE8E000000000000000000D7000000000000008990000000000000FF00000001015002040000000CDF8E00000000000100000096000000000000008D90000001000000000000000101100003000000F4DE8E0000000000FFFFFFFF64000000000000008C9000000200000000000000000210000C0000006CE08E0000000000030000006400000000000000949000000300000000000000010210000D00000094E08E0000000000FFFFFFFF6400000000000000959000000400000000000000000110010E000000B8E08E0000000000050000003200000000000000969000000500000000000000010420010F000000E0E08E0000000000060000003200000000000000979000000600000000000000010420011000000000E18E0000000000070000004600000000000000989000000700000000000000010110011100000020E18E0000000000FFFFFFFF6400000000000000999000000800000000000000000110010600000064DF8E00000000000900000004010000000000008F9000000900000000000000010110010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000040000000B00000001000000A4DE8E000000000000000000D7000000000000009E90000000000000FF000000010150021200000044E18E0000000000FFFFFFFF2D000000000000009B9000000100000000000000000420011400000064E18E0000000000FFFFFFFF64000000000000009D9000000200000000000000000110011300000088E18E0000000000FFFFFFFF64000000000000009C90000003000000000000000001100103000000F4DE8E0000000000FFFFFFFF64000000000000008C9000000400000000000000010210000700000088DF8E00000000000500000049000000490000009090000005000000000000000104210008000000C8DE8E00000000000600000049000000490000009190000006000000000000000104210009000000A8DF8E0000000000070000004900000049000000929000000700000000000000010421080A000000BCDF8E0000000000080000004900000049000000939000000800000000000000010421080B000000D8DF8E000000000009000000490000004900000039A000000900000000000000010421091C000000F8DF8E00000000000A00000064000000000000003AA000000A000000000000000001100900000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000020000000800000001000000A4DE8E000000000000000000C600000000000000B090000000000000FF0000000101500215000000A8E18E0000000000FFFFFFFF6B00000000000000B190000001000000000000000004250016000000D4E18E0000000000FFFFFFFF6B00000000000000B290000002000000000000000004250018000000F8E18E0000000000FFFFFFFF6B00000000000000B49000000300000000000000000425001700000020E28E0000000000FFFFFFFF6B00000000000000B39000000400000000000000000425001900000054E28E0000000000FFFFFFFFA000000000000000B59000000500000000000000000420011A00000080E28E0000000000FFFFFFFF7D00000000000000B69000000600000000000000000420011B000000B0E28E0000000000FFFFFFFF7D00000000000000B79000000700000000000000000420010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000DA00000000000000000000000000000000000000000000009D200000200000006400000064000000320000005000000050000000320000003200000028000000500000003C000000500000005000000032000000500000005000000050000000500000005000000050000000500000002800000050000000230000002300000023000000230000005000000050000000500000003200000032000000320000007800000078000000500000003C0000005000000050000000780000003200000078000000780000003200000050000000500000005000000050000000C8000000000000000100000002000000030000000400000005000000060000000700000008000000090000000A0000000B0000000C0000000D0000000E0000000F000000100000001100000012000000130000001400000015000000160000001700000018000000190000001A0000001B0000001C0000001D0000001E0000001F000000200000002100000022000000230000002400000025000000260000002700000028000000290000002A0000002B0000002C0000002D0000002E0000002F00000000000000000000001F00000000000000640000003200000078000000500000005000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000002000000030000000400000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000001000000000000000000010000000000 | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | Rev |
Value: 0 | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | FFlags |
Value: 18874369 | |||
| (PID) Process: | (4244) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\4\Shell\{0C3794F3-B545-43AA-A329-C37430C58D2A} |
| Operation: | write | Name: | Vid |
Value: {137E7700-3573-11CF-AE69-08002B2E1262} | |||
Executable files
8
Suspicious files
226
Text files
74
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1740 | MEMZ.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 2012 | MEMZ.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF14b525.TMP | binary | |
MD5:83AFF4B759F3B2CAD1027D2152E7730E | SHA256:4D45F208DF5C32896AC64F0B77080CB295630153A3B41C2D3E9246ED83B85AA7 | |||
| 1016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF14b43b.TMP | binary | |
MD5:DFFC82B8D23613E62A20204028CEF32F | SHA256:114690F0417A9A6B079EA8D0534F095B04467809DCA929EB0983059E1C60FB6C | |||
| 1016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:1C42329800C95BC1DB27E7657711FF1E | SHA256:D58993216FB0CBF52CED6DA4FCAEBFC8FCC7C1A37191954397BA77951B16BE9B | |||
| 5776 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3e2651cb230b5698\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF14b545.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF14b554.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
256
TCP/UDP connections
199
DNS requests
181
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1488 | RUXIMICS.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 401 | 13.107.6.158:443 | https://business.bing.com/api/v1/user/token/microsoftgraph?&clienttype=edge-omnibox | unknown | — | — | unknown |
— | — | OPTIONS | 200 | 2.20.245.132:443 | https://bzib.nelreports.net/api/report?cat=bingbusiness | unknown | — | — | unknown |
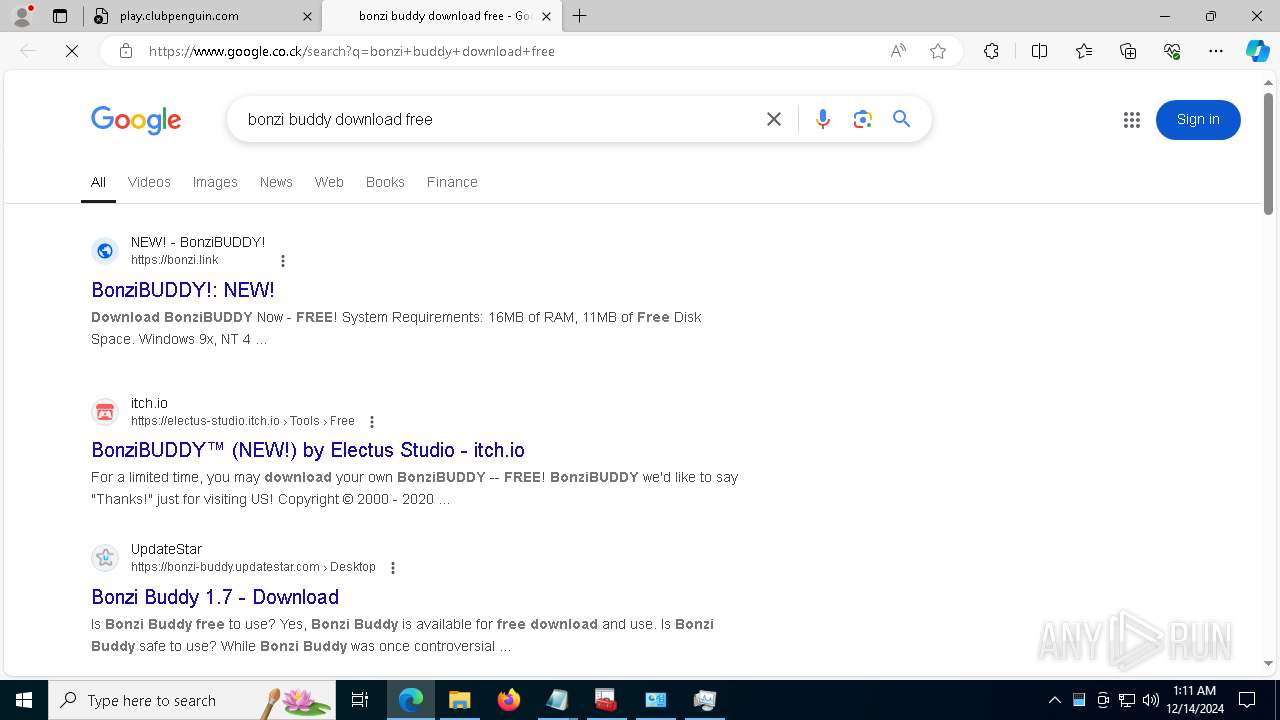
— | — | POST | 204 | 142.250.185.195:443 | https://www.google.co.ck/gen_204?s=web&t=cap&atyp=csi&ei=T9tcZ5GBG6PS2roPldbBgQs&rt=wsrt.3567,cbt.34,hst.31&opi=89978449&dt=&ts=300 | unknown | — | — | unknown |
— | — | GET | 204 | 142.250.185.68:443 | https://www.google.com/pagead/1p-conversion/16521530460/?gad_source=1&adview_type=4&adview_query_id=CIGXqIuKpooDFfbSFgUd5xIYZA | unknown | — | — | unknown |
— | — | GET | 204 | 142.250.186.66:443 | https://www.googleadservices.com/pagead/conversion/16521530460/?gad_source=1&adview_type=1&adview_query_id=CIGXqIuKpooDFfbSFgUd5xIYZA | unknown | — | — | unknown |
1488 | RUXIMICS.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.107.42.16:443 | https://config.edge.skype.com/config/v1/Edge/122.0.2365.59?clientId=4489578223053569932&agents=EdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=44&mngd=0&installdate=1661339457&edu=0&bphint=2&soobedate=1504771245&fg=1 | unknown | binary | 768 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1488 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1488 | RUXIMICS.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2356 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
1488 | RUXIMICS.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
play.clubpenguin.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
google.co.ck |
| whitelisted |
Threats
Process | Message |
|---|---|
mmc.exe |