| File name: | rule34.xxx_downloader.zip |
| Full analysis: | https://app.any.run/tasks/c0b5b591-c9d0-4fe8-9e8a-2ddef033af40 |
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2022, 15:07:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 5E9BED728A606610EEC137F5DDCFA049 |
| SHA1: | C26B314946C1BF002C906652872EFC3F3594CB5A |
| SHA256: | 5F5235E87E74890465D2BC45178B14F2B2BD869BAB3747425C852B6609855045 |
| SSDEEP: | 12288:4RZEVeP1zpihYljNcKb37bvqqbPvCtEfwTPyn0:4Lqi7sKhLb37+M6tEp0 |
MALICIOUS
Application was dropped or rewritten from another process
- r34dl_installer.exe (PID: 3256)
- r34dl_installer.exe (PID: 3736)
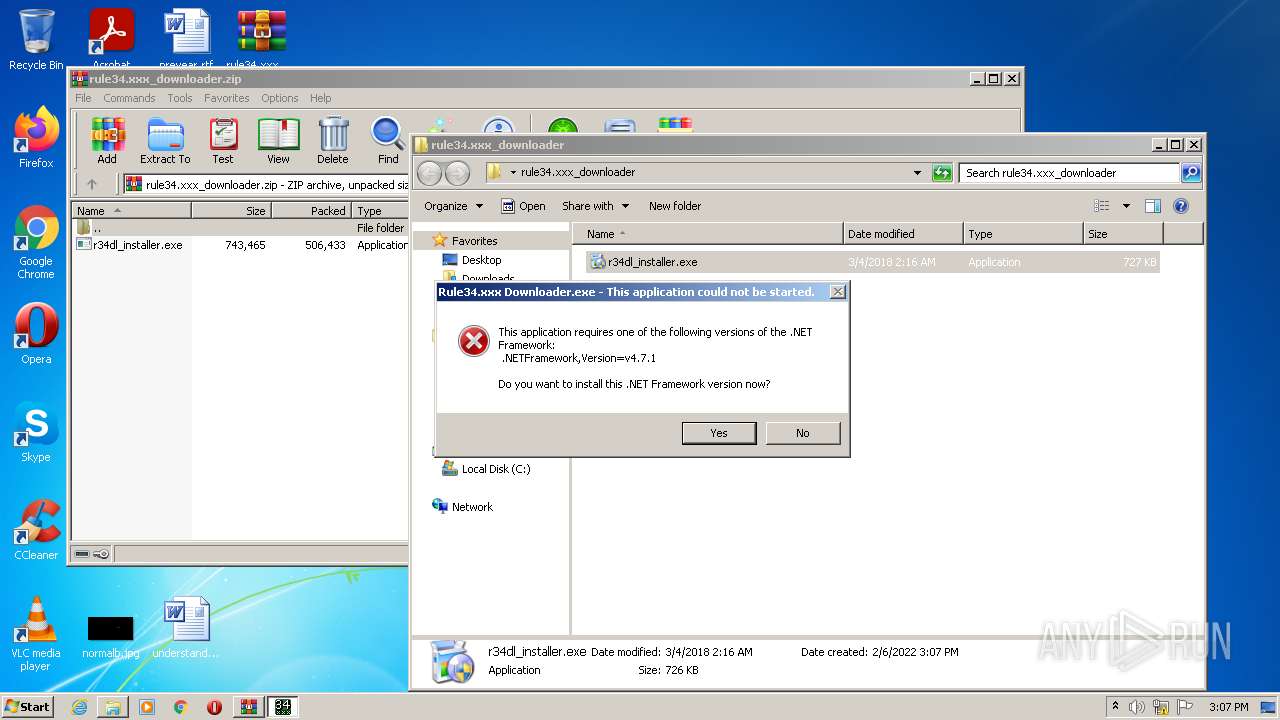
- Rule34.xxx Downloader.exe (PID: 2756)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3748)
- r34dl_installer.exe (PID: 3736)
- Rule34.xxx Downloader.exe (PID: 2756)
Reads the computer name
- WinRAR.exe (PID: 3748)
- r34dl_installer.exe (PID: 3736)
- Rule34.xxx Downloader.exe (PID: 2756)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3748)
- r34dl_installer.exe (PID: 3736)
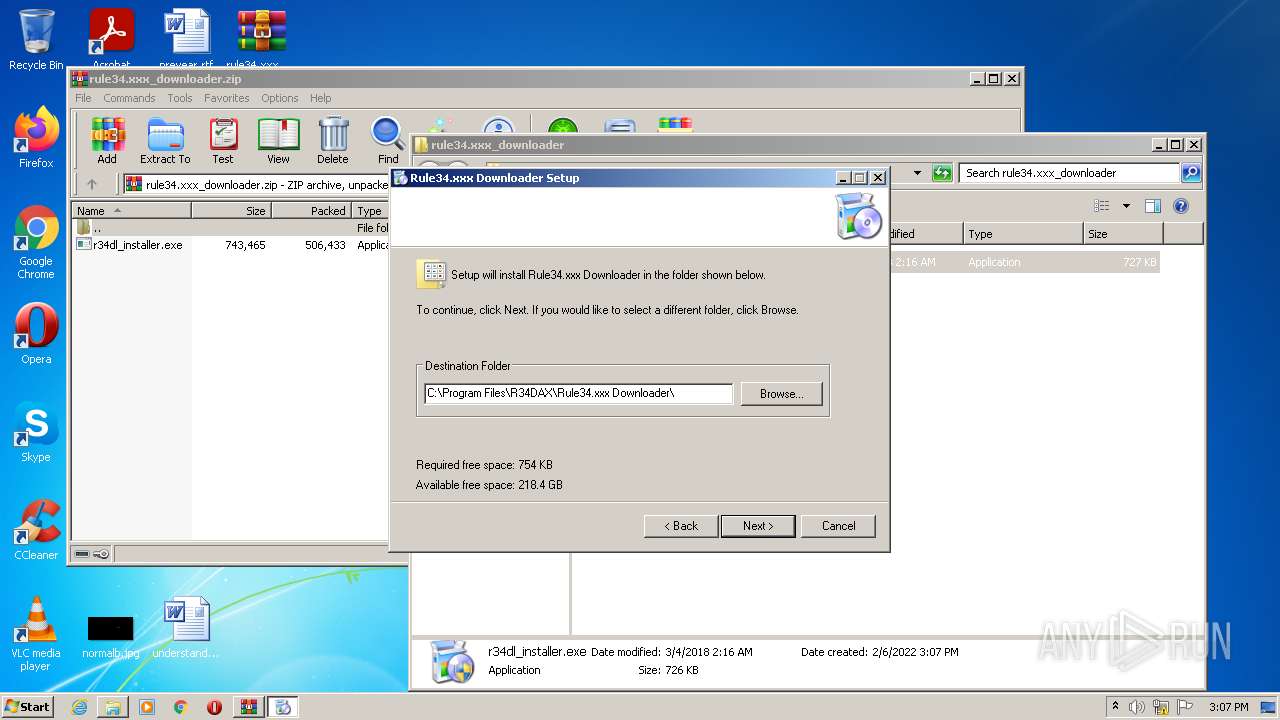
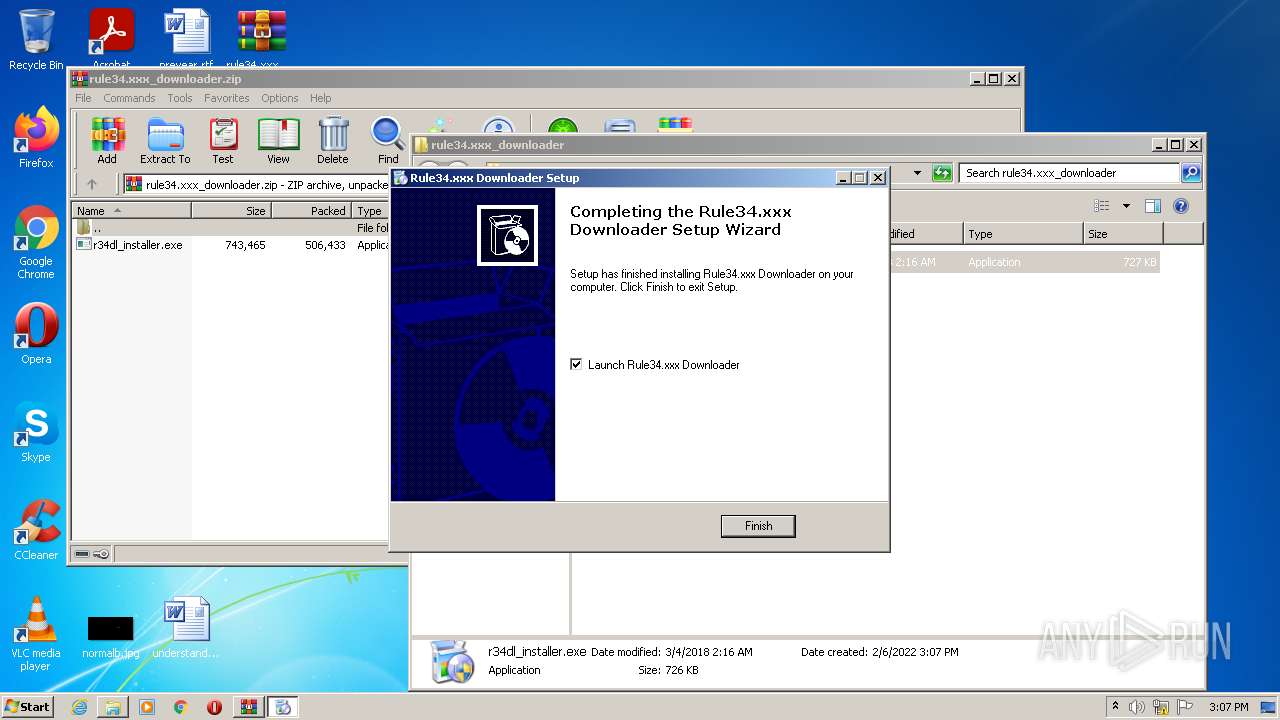
Creates a directory in Program Files
- r34dl_installer.exe (PID: 3736)
Creates files in the program directory
- r34dl_installer.exe (PID: 3736)
Drops a file that was compiled in debug mode
- r34dl_installer.exe (PID: 3736)
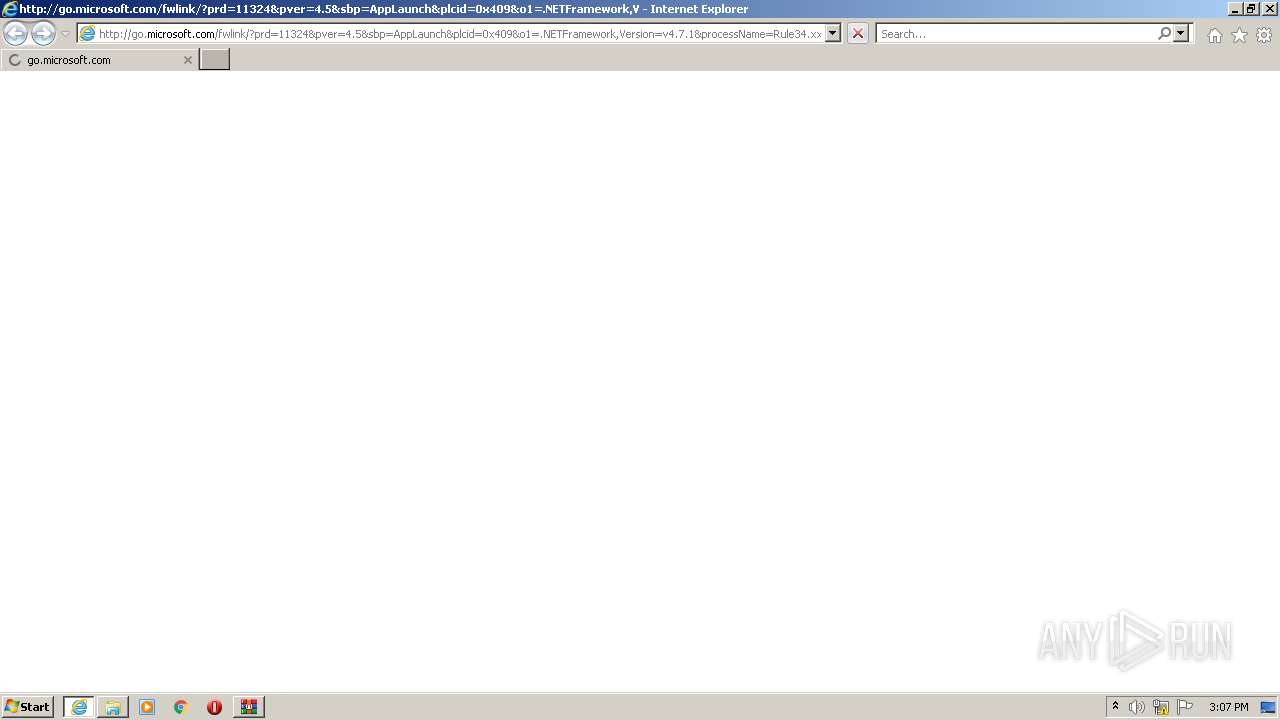
Starts Internet Explorer
- Rule34.xxx Downloader.exe (PID: 2756)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3636)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 3748)
- iexplore.exe (PID: 3636)
Manual execution by user
- r34dl_installer.exe (PID: 3256)
- r34dl_installer.exe (PID: 3736)
Checks supported languages
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 3636)
Reads the computer name
- iexplore.exe (PID: 3236)
- iexplore.exe (PID: 3636)
Application launched itself
- iexplore.exe (PID: 3236)
Changes internet zones settings
- iexplore.exe (PID: 3236)
Checks Windows Trust Settings
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 3236)
Changes settings of System certificates
- iexplore.exe (PID: 3636)
Reads internet explorer settings
- iexplore.exe (PID: 3636)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3636)
Creates files in the user directory
- iexplore.exe (PID: 3636)
Reads settings of System Certificates
- iexplore.exe (PID: 3636)
- iexplore.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
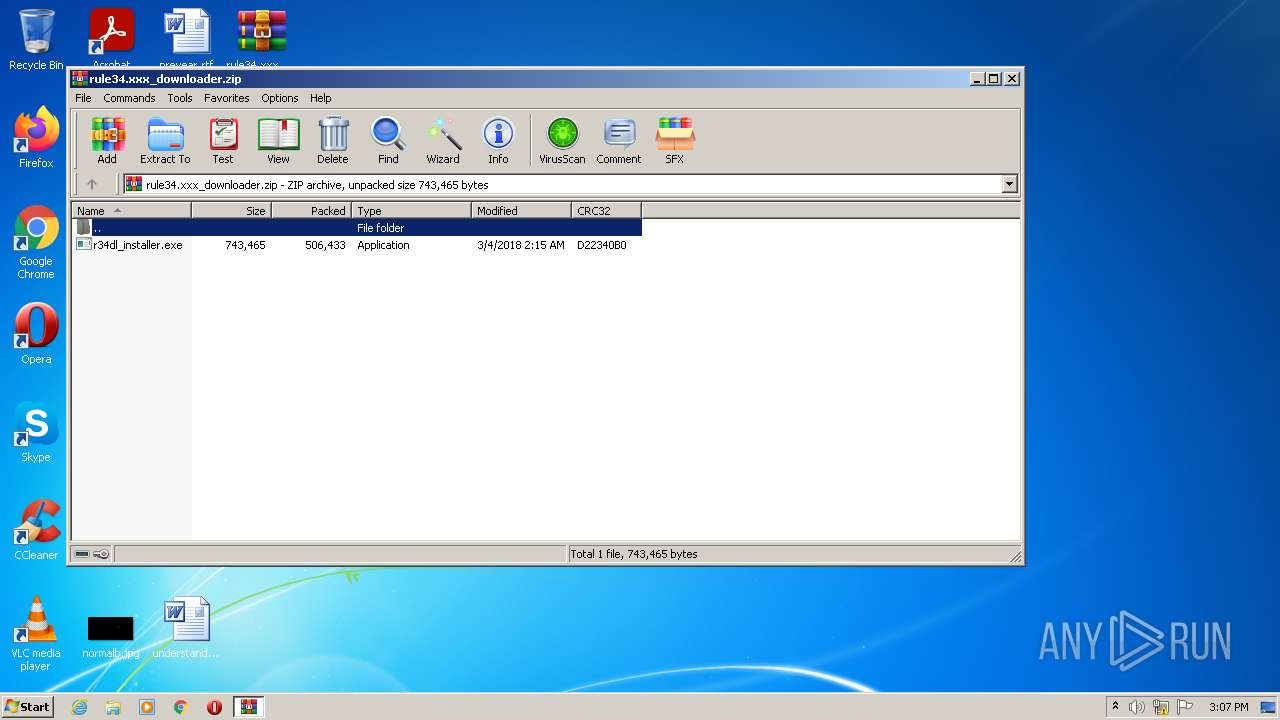
| ZipFileName: | r34dl_installer.exe |
|---|---|
| ZipUncompressedSize: | 743465 |
| ZipCompressedSize: | 506433 |
| ZipCRC: | 0xd22340b0 |
| ZipModifyDate: | 2018:03:04 05:15:29 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
47
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
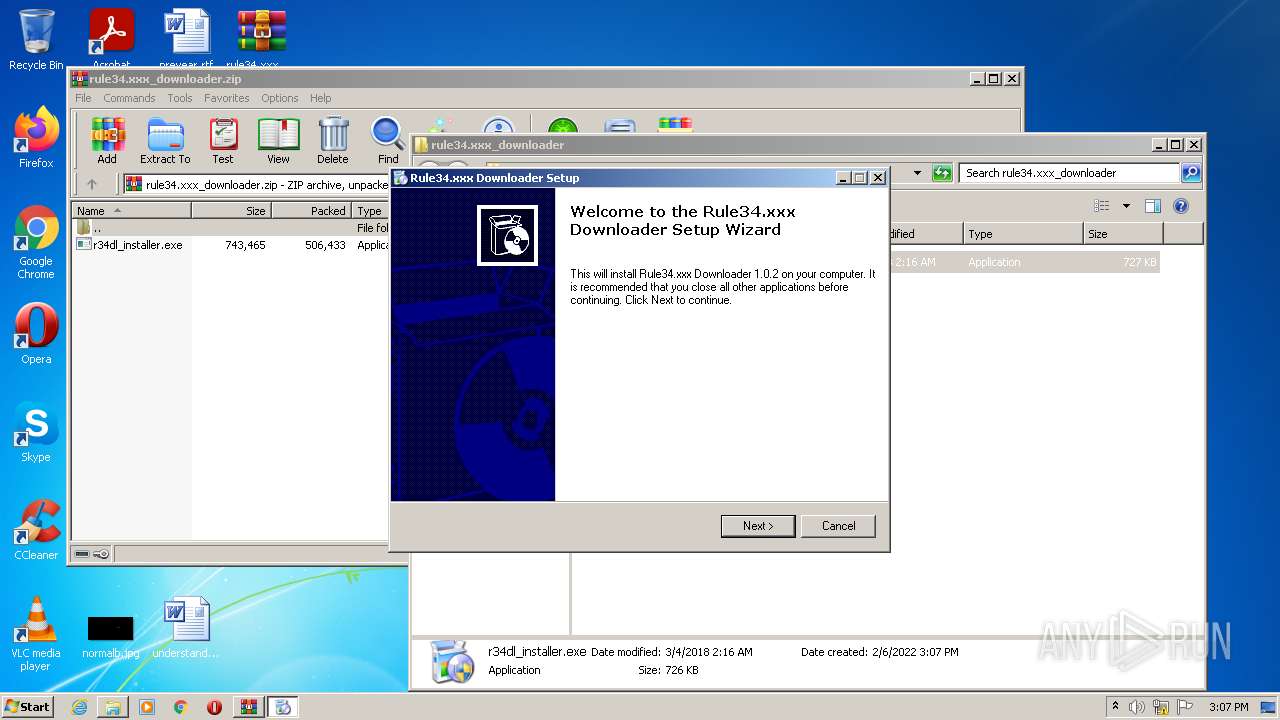
| 2756 | "C:\Program Files\R34DAX\Rule34.xxx Downloader\Rule34.xxx Downloader.exe" | C:\Program Files\R34DAX\Rule34.xxx Downloader\Rule34.xxx Downloader.exe | — | r34dl_installer.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Rule34.xxx Downloader Exit code: 2148734720 Version: 1.0.2.0 Modules
| |||||||||||||||
| 3236 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.7.1&processName=Rule34.xxx Downloader.exe&platform=0000&osver=5&isServer=0&shimver=4.0.30319.34209 | C:\Program Files\Internet Explorer\iexplore.exe | Rule34.xxx Downloader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
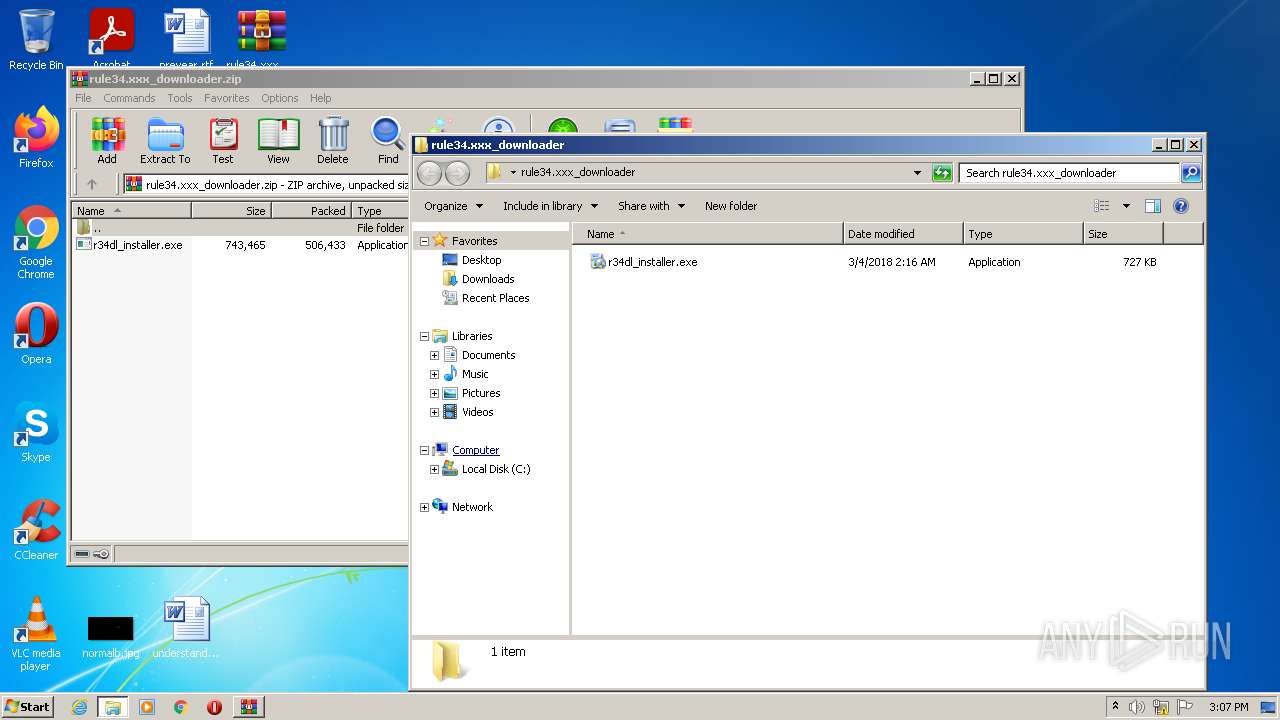
| 3256 | "C:\Users\admin\Desktop\rule34.xxx_downloader\r34dl_installer.exe" | C:\Users\admin\Desktop\rule34.xxx_downloader\r34dl_installer.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3636 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3236 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3736 | "C:\Users\admin\Desktop\rule34.xxx_downloader\r34dl_installer.exe" | C:\Users\admin\Desktop\rule34.xxx_downloader\r34dl_installer.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3748 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\rule34.xxx_downloader.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
17 855
Read events
17 676
Write events
179
Delete events
0
Modification events
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\rule34.xxx_downloader.zip | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3748) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
11
Text files
41
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\SC.dat | text | |
MD5:48B37C8AAF8EDCEA7DF8594B21C85228 | SHA256:48D2C856AD35A6E9E39FA4D286DA2833F009EB55ECEB683D747ED1DA2F71C194 | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\OS.dat | text | |
MD5:FCECC1ED4D6EF93A61375BC8F69B1FAD | SHA256:D6C19A25F14F17C8048CDC3C900FA7ED620807E461BE018DF0D1EF6F38296FBF | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\licence.rtf | text | |
MD5:3E916F4316ABF0C22904109AD166100B | SHA256:820E92AA138876BC7A80B7F47028379C9BE4A7E8BC33C359ADD3D0E0E812729E | |||
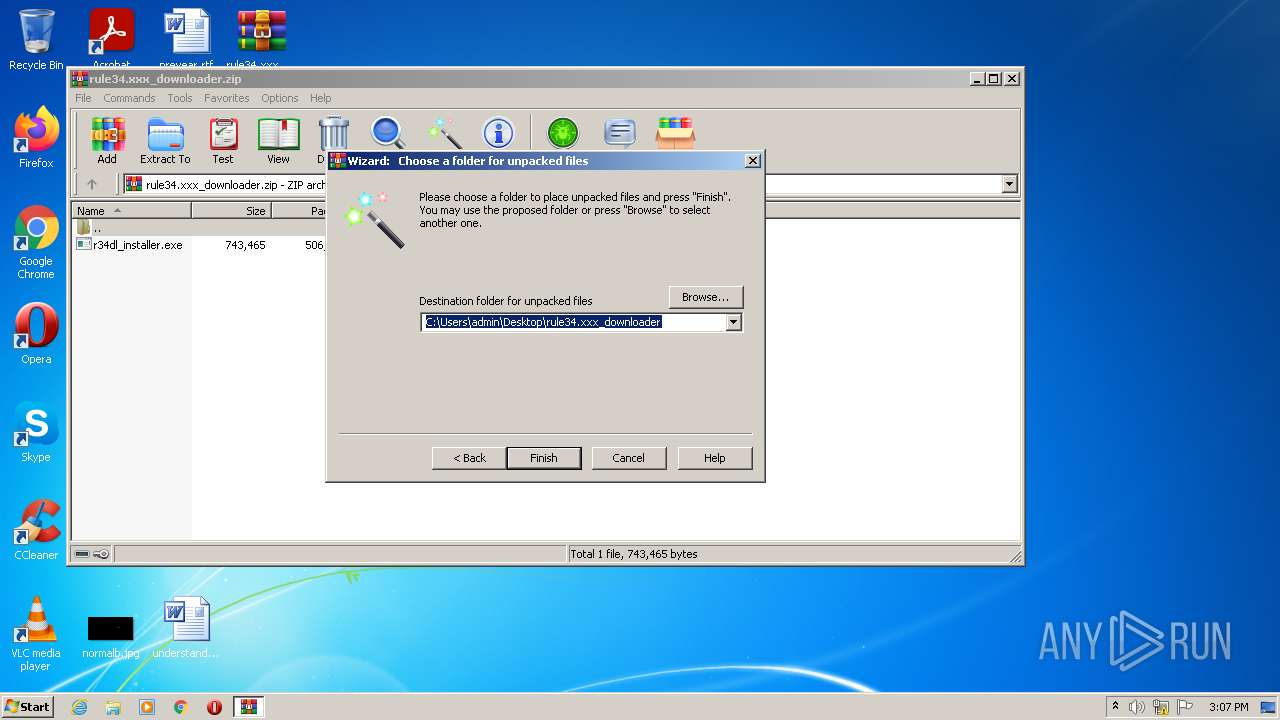
| 3748 | WinRAR.exe | C:\Users\admin\Desktop\rule34.xxx_downloader\r34dl_installer.exe | executable | |
MD5:13361B1054F5885504E5B12DC07DBCD6 | SHA256:701308606E2068944C1E92DEFA3144541DEDAACF421006127904F48FF37CB50B | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\Setup.cab | compressed | |
MD5:997C4BFB094B7EEB54ED7EB1CB430833 | SHA256:B0941EFD45861DEF681E0D07AE557B9E31DF29D0B22C23107DB2E328E4B02EAF | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\Desktop.dat | text | |
MD5:91291B2CCA70EE16630B256FCA108A7D | SHA256:FA8A7C03BA22660632719E63F78BDA9B24DBE7540961DC95CB5E85736EDB39F7 | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\English.ifl | text | |
MD5:DC51022CF78C9B519F2058983A773119 | SHA256:93E28A5125B4864773F53D1C5F87C1756EFA0C2D60D5C3FD6B34AA920080F568 | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\languages.dat | text | |
MD5:A6FB0111CBF1CBF35E3AFA2392E206BC | SHA256:59C8B5AE2D98ACAE9FDD97095A908230F28B2A5C4DFB27CEEB5814ADF906727B | |||
| 3736 | r34dl_installer.exe | C:\Program Files\R34DAX\Rule34.xxx Downloader\Rule34.xxx Downloader.exe | executable | |
MD5:1C66647651A617B670925819B417C5F5 | SHA256:85CA1802CB4636DCF765CF28CA10785F99E1DD4F6A32A20BF130606A5C274097 | |||
| 3736 | r34dl_installer.exe | C:\Users\admin\AppData\Local\Temp\IF{63839391-6834-4B86-A694-D36C1D8DB405}\Default.ifl | text | |
MD5:DC51022CF78C9B519F2058983A773119 | SHA256:93E28A5125B4864773F53D1C5F87C1756EFA0C2D60D5C3FD6B34AA920080F568 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
30
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b50da259449b16b3 | US | compressed | 4.70 Kb | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3636 | iexplore.exe | GET | 200 | 209.197.3.8:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2b450eed2f3c397a | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3636 | iexplore.exe | 104.89.38.104:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
3636 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3636 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3636 | iexplore.exe | 13.107.246.69:443 | dotnet.microsoft.com | Microsoft Corporation | US | suspicious |
3636 | iexplore.exe | 92.123.195.43:443 | statics-marketingsites-wcus-ms-com.akamaized.net | Akamai International B.V. | — | whitelisted |
3636 | iexplore.exe | 2.21.143.74:443 | www.microsoft.com | Telia Company AB | — | malicious |
3636 | iexplore.exe | 92.123.195.50:443 | img-prod-cms-rt-microsoft-com.akamaized.net | Akamai International B.V. | — | whitelisted |
3636 | iexplore.exe | 152.199.21.175:443 | az416426.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3636 | iexplore.exe | 40.78.253.202:443 | dc.services.visualstudio.com | Microsoft Corporation | US | unknown |
3236 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
statics-marketingsites-wcus-ms-com.akamaized.net |
| whitelisted |
img-prod-cms-rt-microsoft-com.akamaized.net |
| whitelisted |
az416426.vo.msecnd.net |
| whitelisted |
wcpstatic.microsoft.com |
| whitelisted |
api.bing.com |
| whitelisted |