| File name: | magicline4nx_setup__1_.exe |
| Full analysis: | https://app.any.run/tasks/5dc1ade0-6b4d-4ebe-a7a5-7c1f8fcd6f14 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2023, 06:45:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 0FFEB1E177A6F902BBDAE613486464C8 |
| SHA1: | C6BF7F4B8A39FFB30073D831569BDEFDC3D95C75 |
| SHA256: | 5F51FCB5BFEDCDE3C45F0274E74758E7574E68D9C1ED39E86F7EE2034BED30D8 |
| SSDEEP: | 196608:GX+DXPqHEkl4PwBqcIZiNWj9tCLK0nzycqQBGG1y+8deWlcfV:GODXPqWPcdNWj7WbzyyICqI1fV |
MALICIOUS
Loads dropped or rewritten executable
- magicline4nx_setup__1_.exe (PID: 3936)
- certutil.exe (PID: 2480)
- certutil.exe (PID: 3356)
- MagicLine4NX.exe (PID: 1160)
- MagicLine4NX.exe (PID: 3540)
- MagicLine4NX.exe (PID: 3720)
Application was dropped or rewritten from another process
- certmgr.exe (PID: 3924)
- certutil.exe (PID: 2480)
- certutil.exe (PID: 3356)
- MagicLine4NXServices.exe (PID: 116)
- MagicLine4NXServices.exe (PID: 2592)
- MagicLine4NX.exe (PID: 1160)
- MagicLine4NX.exe (PID: 3540)
- MagicLine4NX.exe (PID: 3720)
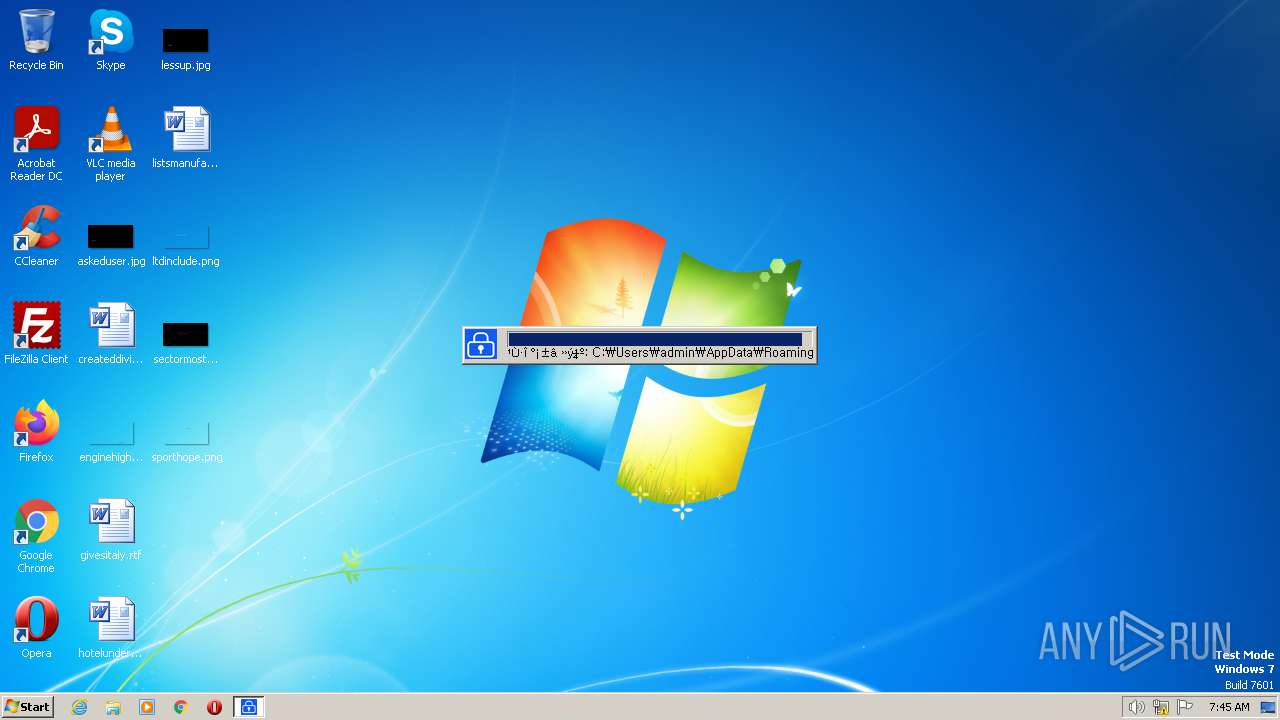
Actions looks like stealing of personal data
- cscript.exe (PID: 2700)
- certutil.exe (PID: 2480)
- cscript.exe (PID: 3412)
- certutil.exe (PID: 3356)
SUSPICIOUS
Starts CMD.EXE for commands execution
- magicline4nx_setup__1_.exe (PID: 3936)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 240)
- cmd.exe (PID: 3396)
The process creates files with name similar to system file names
- magicline4nx_setup__1_.exe (PID: 3936)
Reads the Internet Settings
- magicline4nx_setup__1_.exe (PID: 3936)
- cscript.exe (PID: 2700)
- cscript.exe (PID: 3412)
Executable content was dropped or overwritten
- magicline4nx_setup__1_.exe (PID: 3936)
Starts application with an unusual extension
- magicline4nx_setup__1_.exe (PID: 3936)
Starts SC.EXE for service management
- nsD437.tmp (PID: 452)
- nsD4B5.tmp (PID: 2884)
- nsF64C.tmp (PID: 2404)
The process executes VB scripts
- nsEB4C.tmp (PID: 2288)
- nsED22.tmp (PID: 3176)
Changes internet zones settings
- magicline4nx_setup__1_.exe (PID: 3936)
Reads the BIOS version
- MagicLine4NXServices.exe (PID: 116)
- MagicLine4NXServices.exe (PID: 2592)
- MagicLine4NX.exe (PID: 1160)
- MagicLine4NX.exe (PID: 3540)
- MagicLine4NX.exe (PID: 3720)
Executes as Windows Service
- MagicLine4NXServices.exe (PID: 2592)
INFO
Checks supported languages
- magicline4nx_setup__1_.exe (PID: 3936)
- nsD437.tmp (PID: 452)
- nsD4B5.tmp (PID: 2884)
- nsE783.tmp (PID: 3920)
- certmgr.exe (PID: 3924)
- nsEB4C.tmp (PID: 2288)
- certutil.exe (PID: 2480)
- nsED22.tmp (PID: 3176)
- certutil.exe (PID: 3356)
- nsF0AD.tmp (PID: 3968)
- MagicLine4NXServices.exe (PID: 116)
- nsF64C.tmp (PID: 2404)
- MagicLine4NXServices.exe (PID: 2592)
- MagicLine4NX.exe (PID: 1160)
- MagicLine4NX.exe (PID: 3540)
- MagicLine4NX.exe (PID: 3720)
Reads the computer name
- magicline4nx_setup__1_.exe (PID: 3936)
- certutil.exe (PID: 2480)
- certutil.exe (PID: 3356)
- MagicLine4NXServices.exe (PID: 116)
- MagicLine4NXServices.exe (PID: 2592)
- MagicLine4NX.exe (PID: 1160)
Create files in a temporary directory
- magicline4nx_setup__1_.exe (PID: 3936)
The process checks LSA protection
- magicline4nx_setup__1_.exe (PID: 3936)
- taskkill.exe (PID: 3280)
- taskkill.exe (PID: 3688)
- cscript.exe (PID: 2700)
- cscript.exe (PID: 3412)
- MagicLine4NX.exe (PID: 1160)
Creates files in the program directory
- magicline4nx_setup__1_.exe (PID: 3936)
Creates files or folders in the user directory
- magicline4nx_setup__1_.exe (PID: 3936)
- certutil.exe (PID: 3356)
Reads security settings of Internet Explorer
- cscript.exe (PID: 2700)
- cscript.exe (PID: 3412)
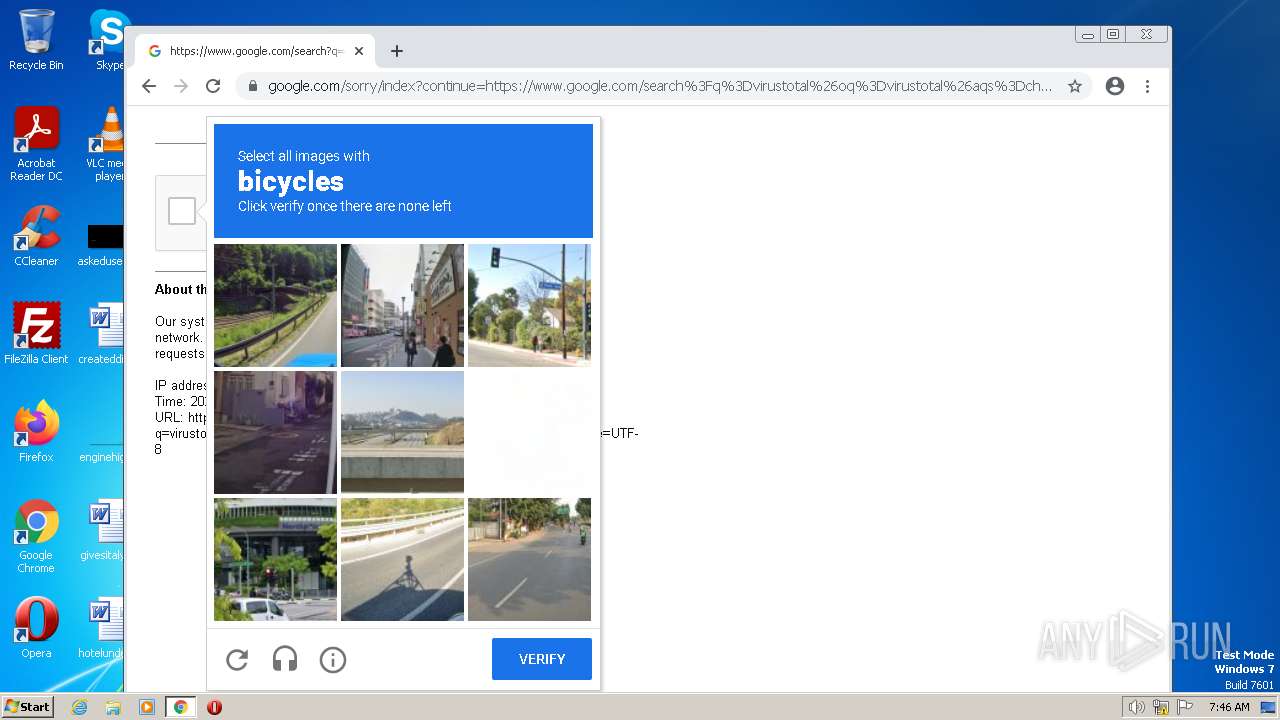
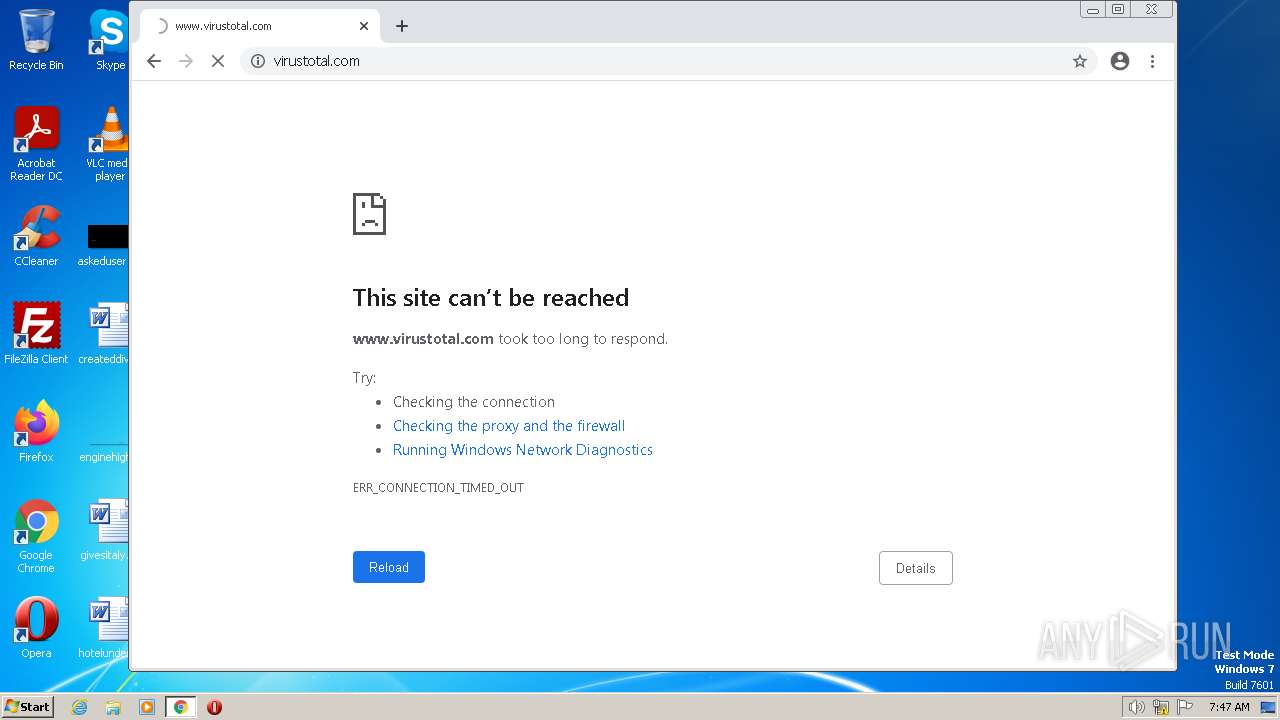
Manual execution by a user
- chrome.exe (PID: 3388)
- MagicLine4NX.exe (PID: 3540)
- MagicLine4NX.exe (PID: 3720)
Reads the machine GUID from the registry
- MagicLine4NX.exe (PID: 1160)
Application launched itself
- chrome.exe (PID: 3388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| ProductVersion: | MagicLine4Web |
|---|---|
| ProductName: | MagicLine4NX |
| LegalCopyright: | Copyright (C) 2016 Dreamsecurity Co., Ltd. All rights reserved. |
| FileVersion: | 1.0.0.28 |
| FileDescription: | MagicLine4NX |
| CompanyName: | Dreamsecurity, Inc. |
| CharacterSet: | Windows, Korea (Shift - KSC 5601) |
| LanguageCode: | Korean |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.28 |
| FileVersionNumber: | 1.0.0.28 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x310f |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 162816 |
| CodeSize: | 24576 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2015:12:27 06:26:04+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Dec-2015 06:26:04 |
| Detected languages: |
|
| CompanyName: | Dreamsecurity, Inc. |
| FileDescription: | MagicLine4NX |
| FileVersion: | 1.0.0.28 |
| LegalCopyright: | Copyright (C) 2016 Dreamsecurity Co., Ltd. All rights reserved. |
| ProductName: | MagicLine4NX |
| ProductVersion: | MagicLine4Web |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 27-Dec-2015 06:26:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005FDD | 0x00006000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50763 |
.rdata | 0x00007000 | 0x0000131E | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14401 |
.data | 0x00009000 | 0x000254F8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13081 |
.ndata | 0x0002F000 | 0x0000C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00005ED0 | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.53083 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28852 | 1071 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.76625 | 5189 | UNKNOWN | English - United States | RT_ICON |
3 | 4.68558 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 5.68846 | 3240 | UNKNOWN | English - United States | RT_ICON |
5 | 6.12825 | 1864 | UNKNOWN | English - United States | RT_ICON |
6 | 0.573426 | 1384 | UNKNOWN | English - United States | RT_ICON |
103 | 2.91321 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.46055 | 236 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.85274 | 264 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.36476 | 76 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
101
Monitored processes
51
Malicious processes
12
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe" -install | C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NXServices.exe | nsF0AD.tmp | ||||||||||||
User: admin Company: Dreamsecurity Integrity Level: HIGH Description: MagicLine4NXServices Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
| 240 | "C:\Windows\System32\cmd.exe" /C taskkill /f /im NTSMagicLineNP.exe | C:\Windows\System32\cmd.exe | — | magicline4nx_setup__1_.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 452 | "C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsD437.tmp" sc stop MagicLine4NXSVC | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsD437.tmp | — | magicline4nx_setup__1_.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1060 Modules
| |||||||||||||||
| 844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2784 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1036 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX.exe" | C:\Program Files\DreamSecurity\MagicLine4NX\MagicLine4NX.exe | MagicLine4NXServices.exe | ||||||||||||
User: admin Company: Dreamsecurity Integrity Level: MEDIUM Description: MagicLine4NX Exit code: 0 Version: 1.0.0.28 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2604 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,7914992985731010869,7172433191152675286,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
16 716
Read events
16 575
Write events
135
Delete events
6
Modification events
| (PID) Process: | (3936) magicline4nx_setup__1_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3936) magicline4nx_setup__1_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3936) magicline4nx_setup__1_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3936) magicline4nx_setup__1_.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3936) magicline4nx_setup__1_.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Internet Explorer\ProtocolExecute\NTSMagicLineNP |
| Operation: | write | Name: | WarnOnOpen |
Value: 0 | |||
| (PID) Process: | (2700) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2700) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2700) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2700) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3412) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
36
Suspicious files
102
Text files
137
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\System.dll | executable | |
MD5:4D3B19A81BD51F8CE44B93643A4E3A99 | SHA256:FDA0018AB182AC6025D2FC9A2EFCCE3745D1DA21CE5141859F8286CF319A52CE | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsProcess.dll | executable | |
MD5:FAA7F034B38E729A983965C04CC70FC1 | SHA256:579A034FF5AB9B732A318B1636C2902840F604E8E664F5B93C07A99253B3C9CF | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsD4B5.tmp | executable | |
MD5:3EB4CD50DCB9F5981F5408578CB7FB70 | SHA256:1C2F19E57DC72587AA00800A498C5F581B7D6761DC13B24BCF287EA7BD5CA2BF | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\NsisUtil.dll | executable | |
MD5:59541B9DA3C09F318A58BEF52C9FF131 | SHA256:74A542EF3BBE0673453286DFEB335C1D7BDE4E601C932A3D0D04C85EB098BB47 | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\KillProcDLL.dll | executable | |
MD5:83142EAC84475F4CA889C73F10D9C179 | SHA256:AE2F1658656E554F37E6EAC896475A3862841A18FFC6FAD2754E2D3525770729 | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Program Files\DreamSecurity\MagicLine4NX\MagicCrypto32V22.dll | executable | |
MD5:6A3EB6617EF4CE8200DC2F9533D8F33B | SHA256:E82A1E934FC7195BFBF911FEC09CBA19A8DAD304B2BC9212A16EDD1D5E3CA8DF | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsExec.dll | executable | |
MD5:3EB4CD50DCB9F5981F5408578CB7FB70 | SHA256:1C2F19E57DC72587AA00800A498C5F581B7D6761DC13B24BCF287EA7BD5CA2BF | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Users\admin\AppData\Local\Temp\nsaCF73.tmp\nsD437.tmp | executable | |
MD5:3EB4CD50DCB9F5981F5408578CB7FB70 | SHA256:1C2F19E57DC72587AA00800A498C5F581B7D6761DC13B24BCF287EA7BD5CA2BF | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Program Files\DreamSecurity\MagicLine4NX\IssuerOid_Eng.conf | text | |
MD5:F1EBA7DDDC7C4BAEDEC17262E1856335 | SHA256:6C8BFD46D492A8DC9CFAB616DEA02C4C032FCAB1008390C4B8311A5AA0E8EB22 | |||
| 3936 | magicline4nx_setup__1_.exe | C:\Program Files\DreamSecurity\MagicLine4NX\CertManager.dll | executable | |
MD5:043F110E1C505BD8D567595983146160 | SHA256:0D40ACEF75C1C98E3E081A4E0E92609495F40BEC60A341F27CE8C7ADD5957F38 | |||
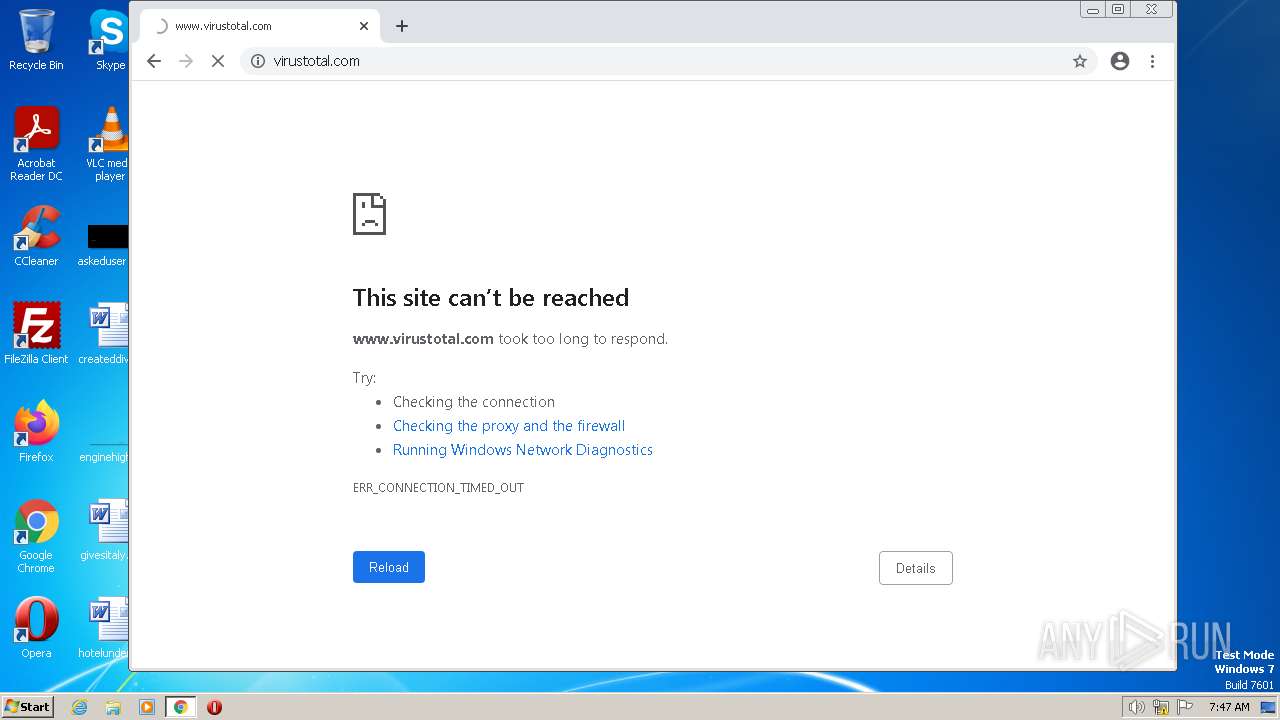
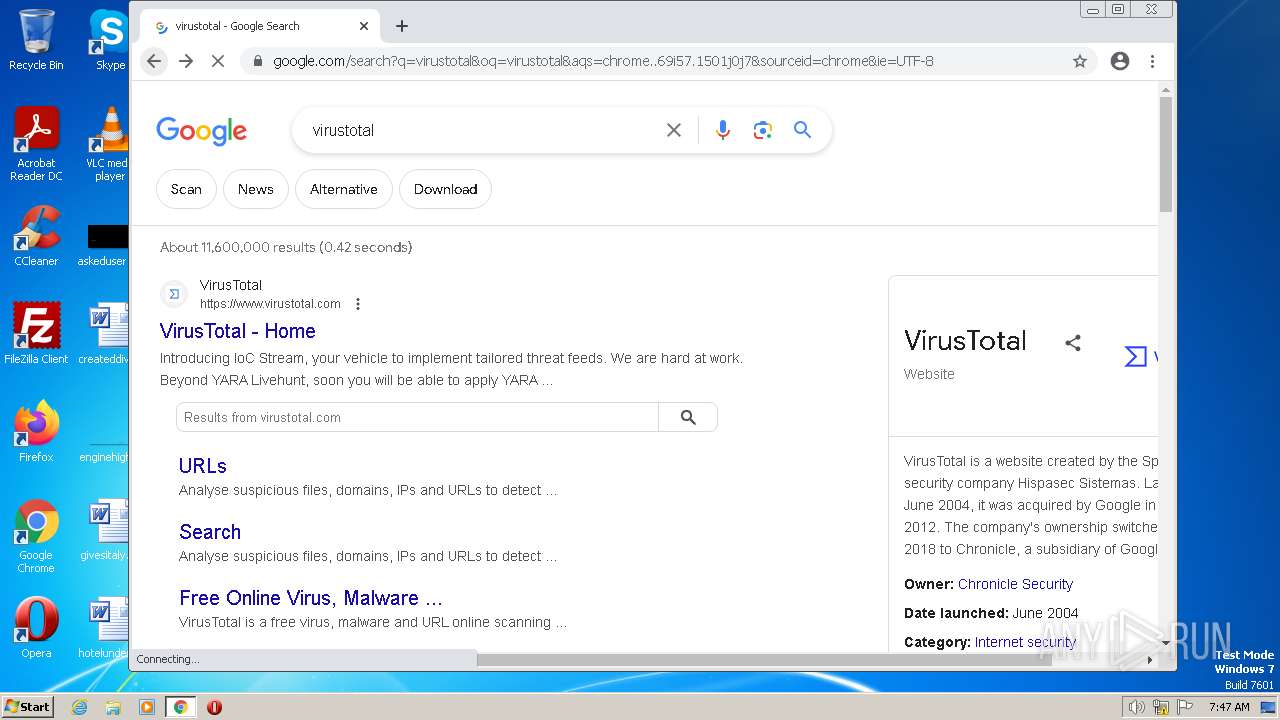
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
77
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
852 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | — | — | whitelisted |
2140 | chrome.exe | GET | 204 | 142.250.186.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
2140 | chrome.exe | GET | 204 | 142.250.186.163:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 5.74 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 12.3 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 10.1 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 8.60 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 34.9 Kb | whitelisted |
852 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/j2hxfei2occ5siitujtlwgp6xi_3/ojhpjlocmbogdgmfpkhlaaeamibhnphh_3_all_gplutbkdljxxbjolk3siq7kive.crx3 | US | binary | 9.51 Kb | whitelisted |
2140 | chrome.exe | POST | 200 | 142.250.184.227:80 | http://update.googleapis.com/service/update2/json?cup2key=10:973597806&cup2hreq=d9168fdac616360d71384853445eec5e5dbd71a1a1d957f2d8b9749e9fbf2fce | US | text | 2.36 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1896 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3388 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2140 | chrome.exe | 142.250.185.238:443 | clients2.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 172.217.16.205:443 | accounts.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 216.58.212.163:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
2140 | chrome.exe | 142.250.184.225:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
Process | Message |
|---|---|
MagicLine4NXServices.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NXServices.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|
MagicLine4NX.exe |
%s------------------------------------------------
--- Themida Professional ---
--- (c)2012 Oreans Technologies ---
------------------------------------------------
|