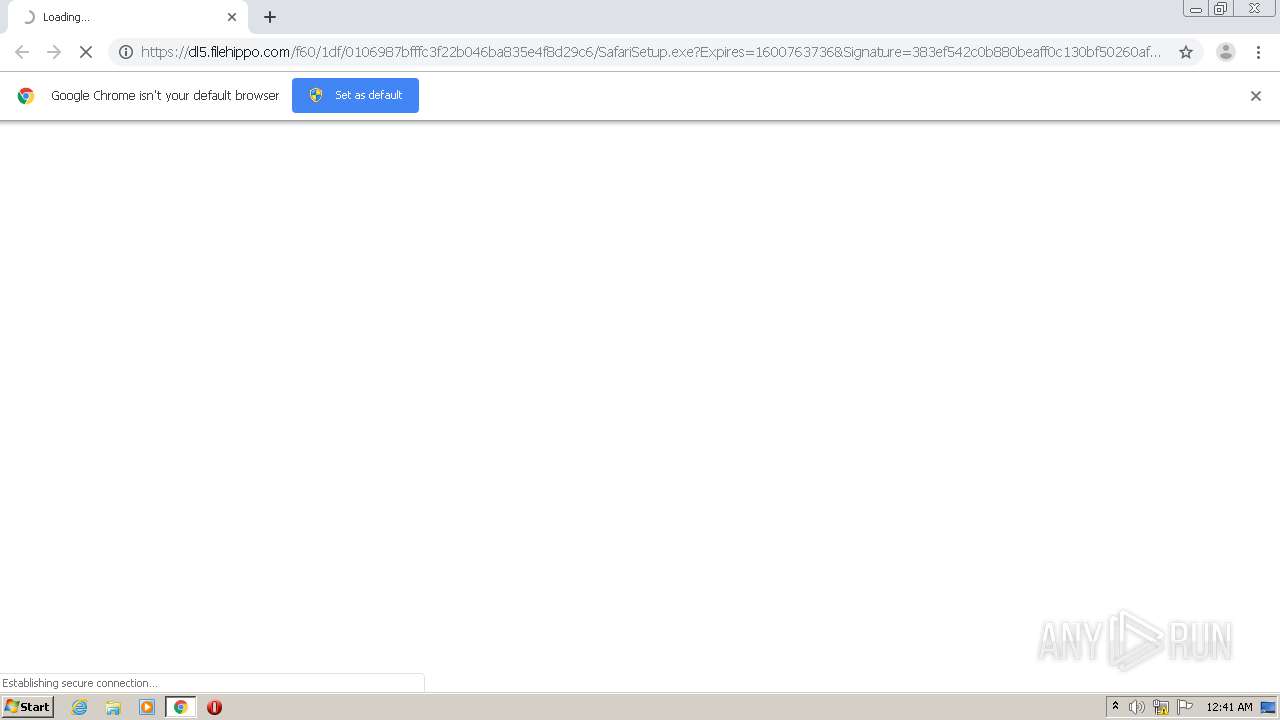
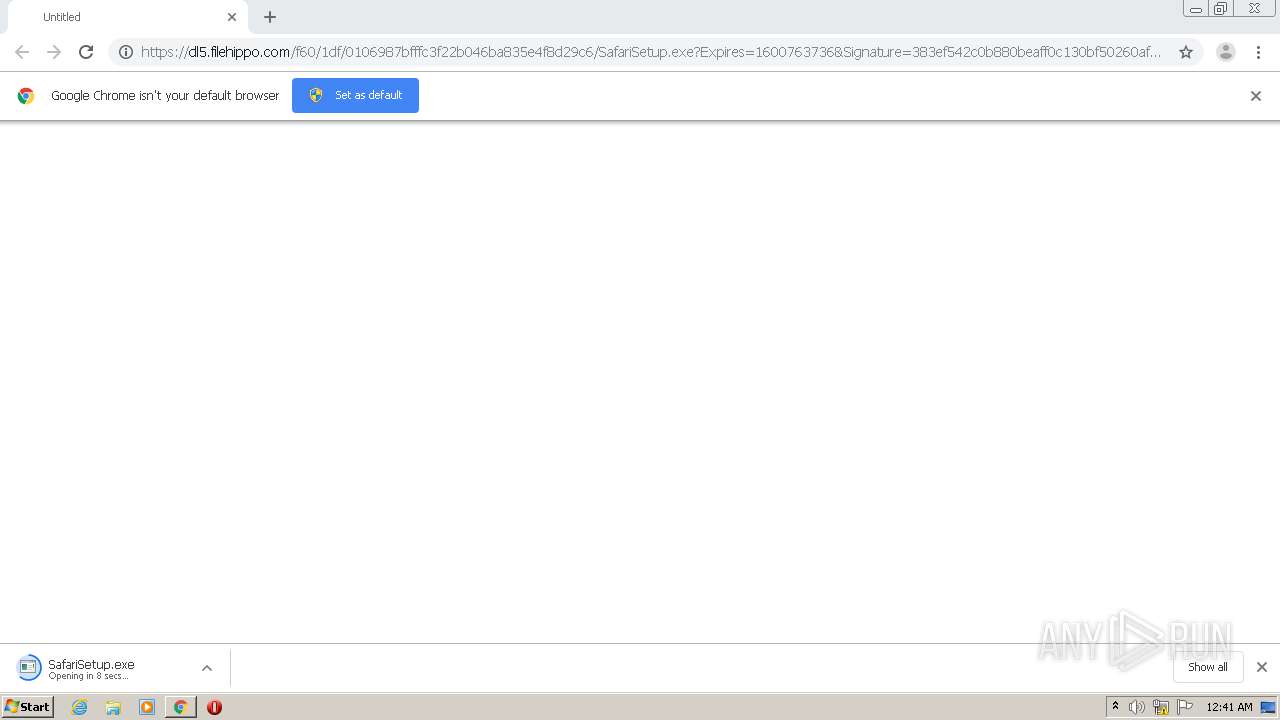
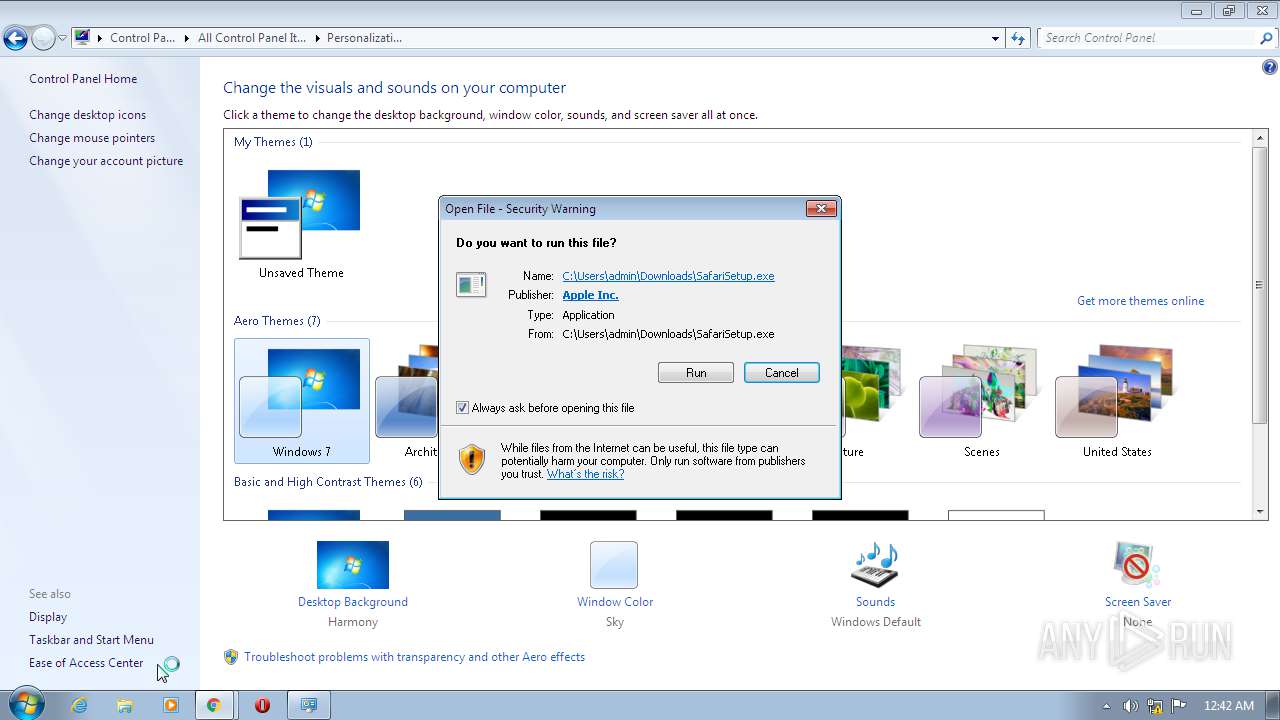
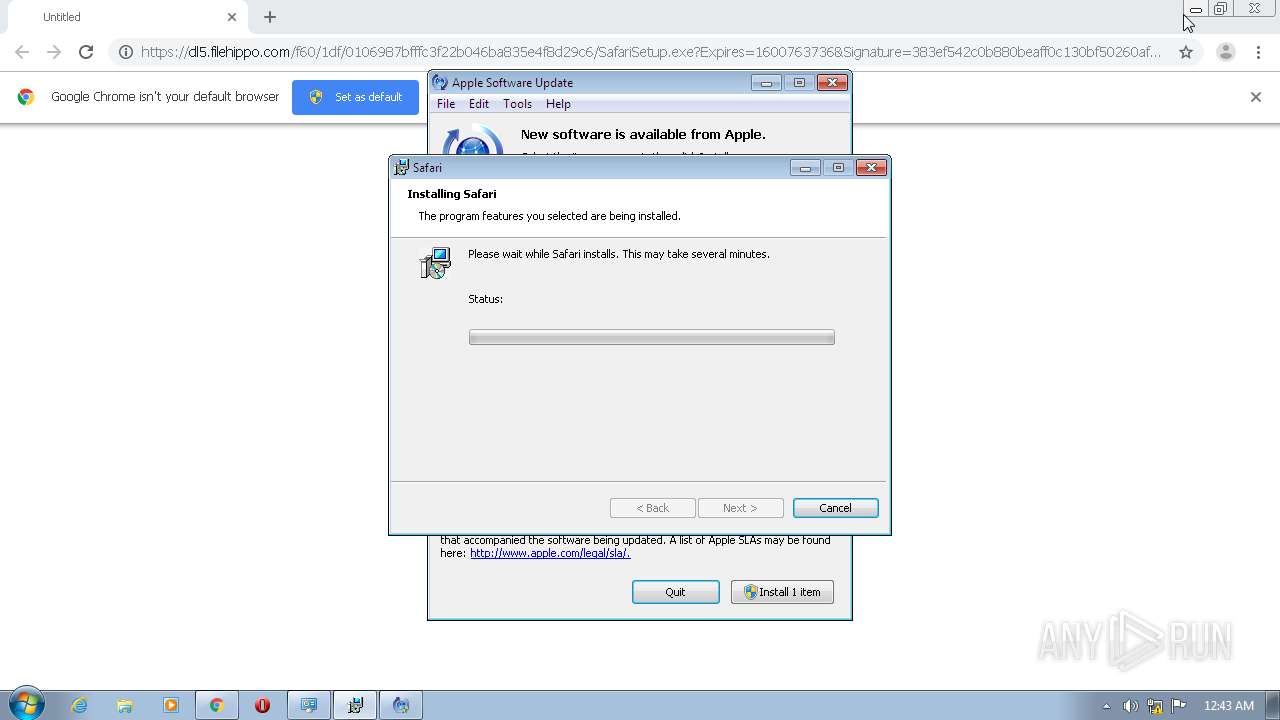
| URL: | https://dl5.filehippo.com/f60/1df/0106987bfffc3f22b046ba835e4f8d29c6/SafariSetup.exe?Expires=1600763736&Signature=383ef542c0b880beaff0c130bf50260af9cb2b5d&url=https://filehippo.com/download_safari/&Filename=SafariSetup.exe |
| Full analysis: | https://app.any.run/tasks/9b2b90ae-4a53-481d-8c53-dd0eea8f68a9 |
| Verdict: | Malicious activity |
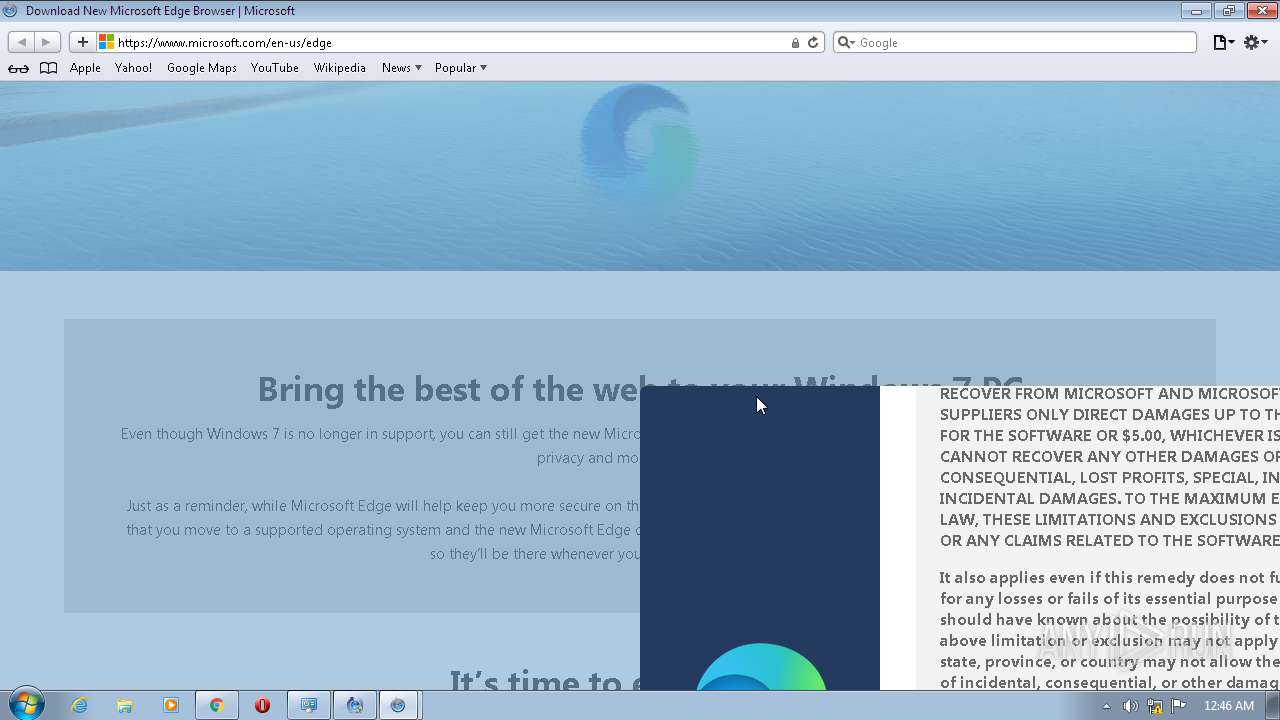
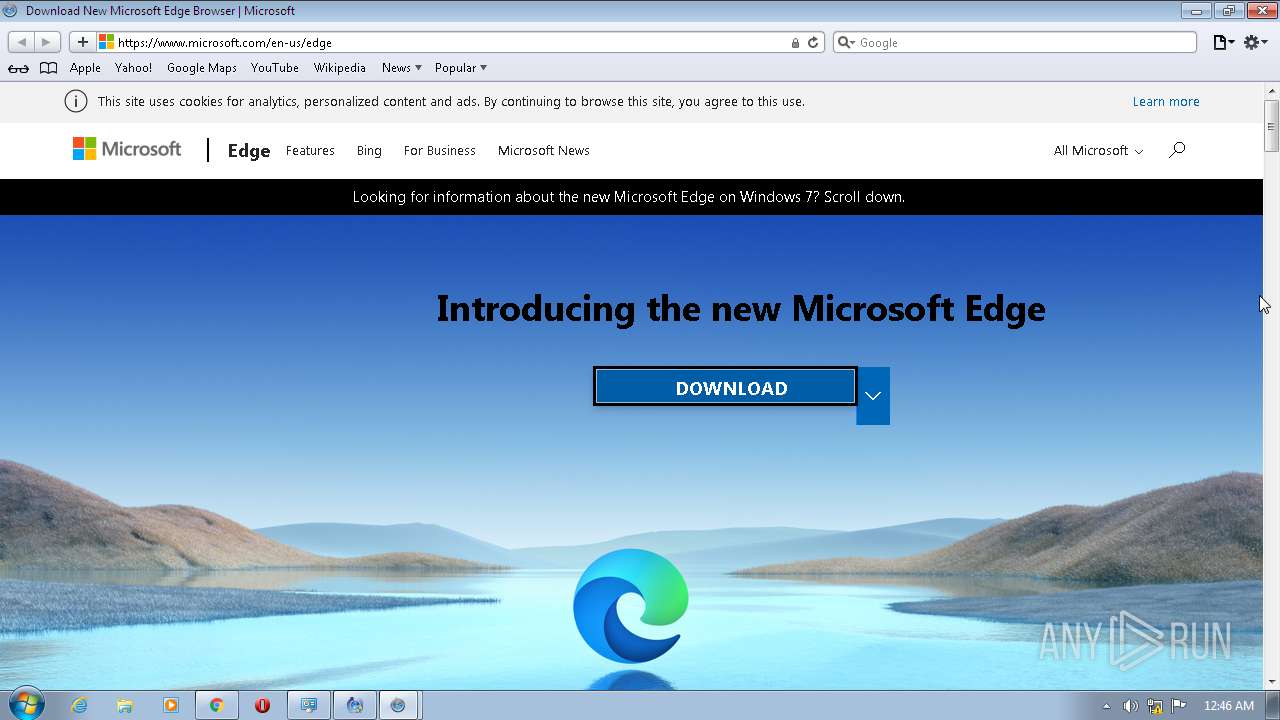
| Analysis date: | September 21, 2020, 23:41:04 |
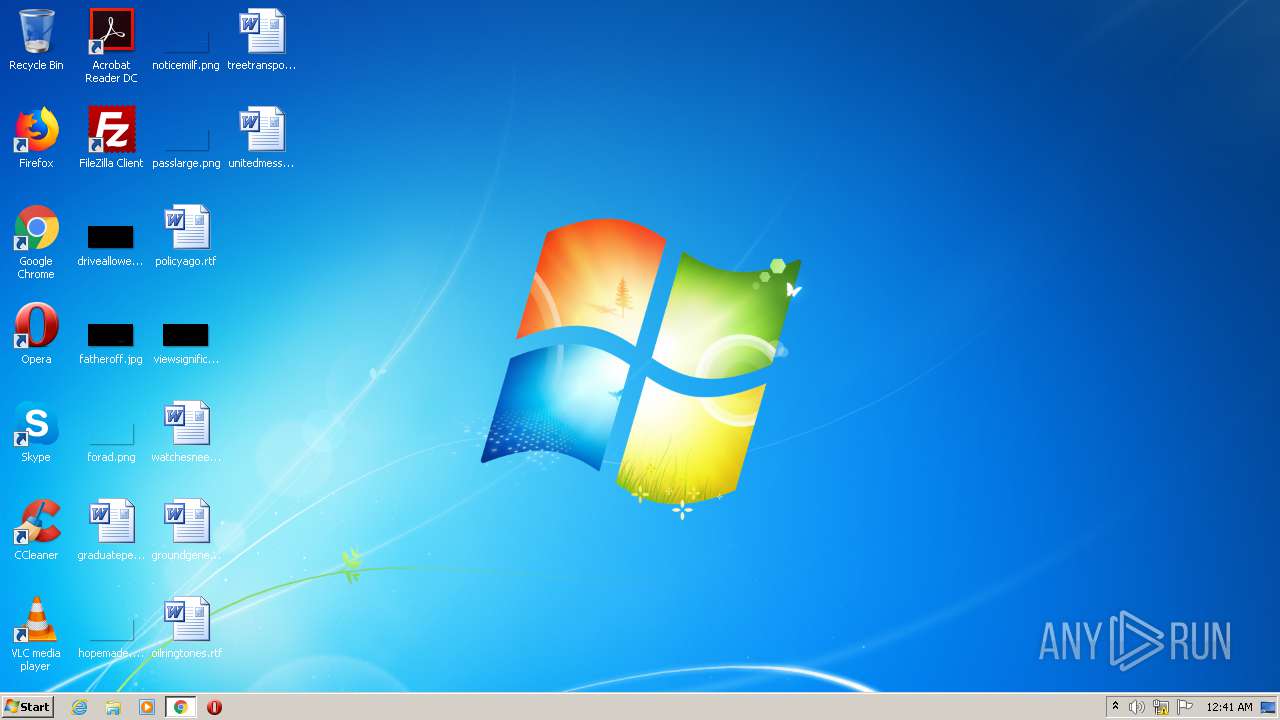
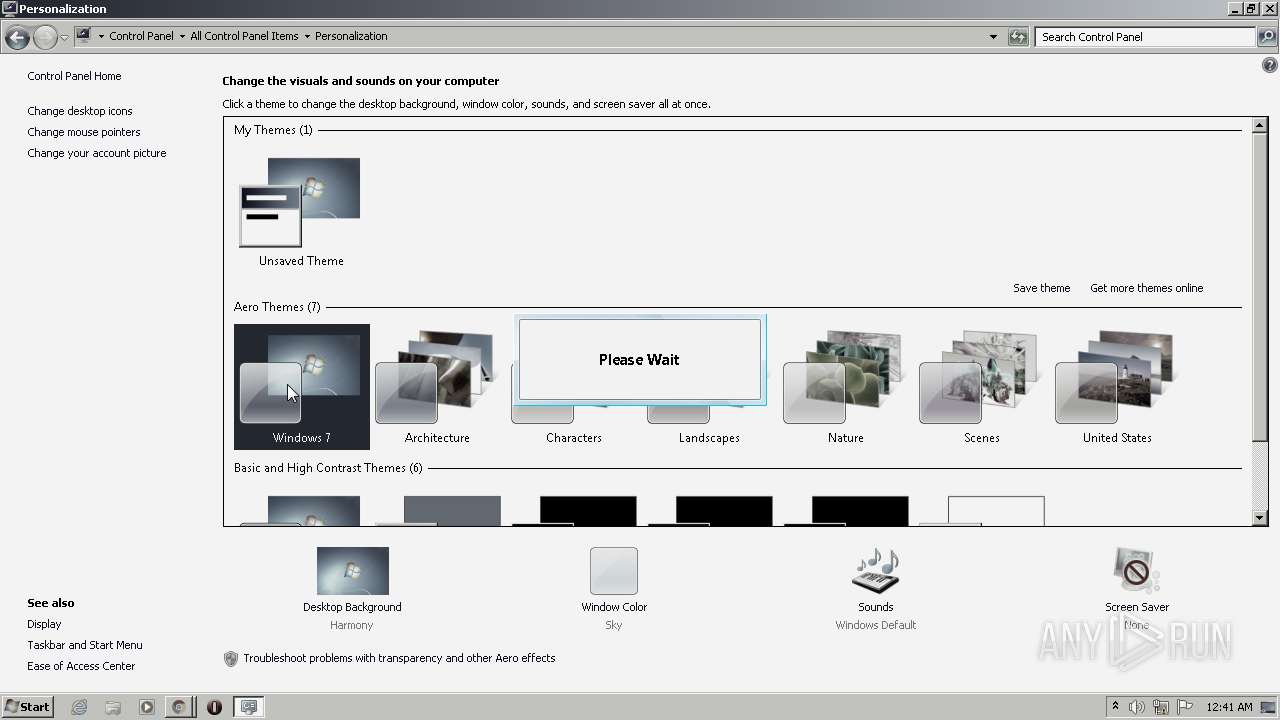
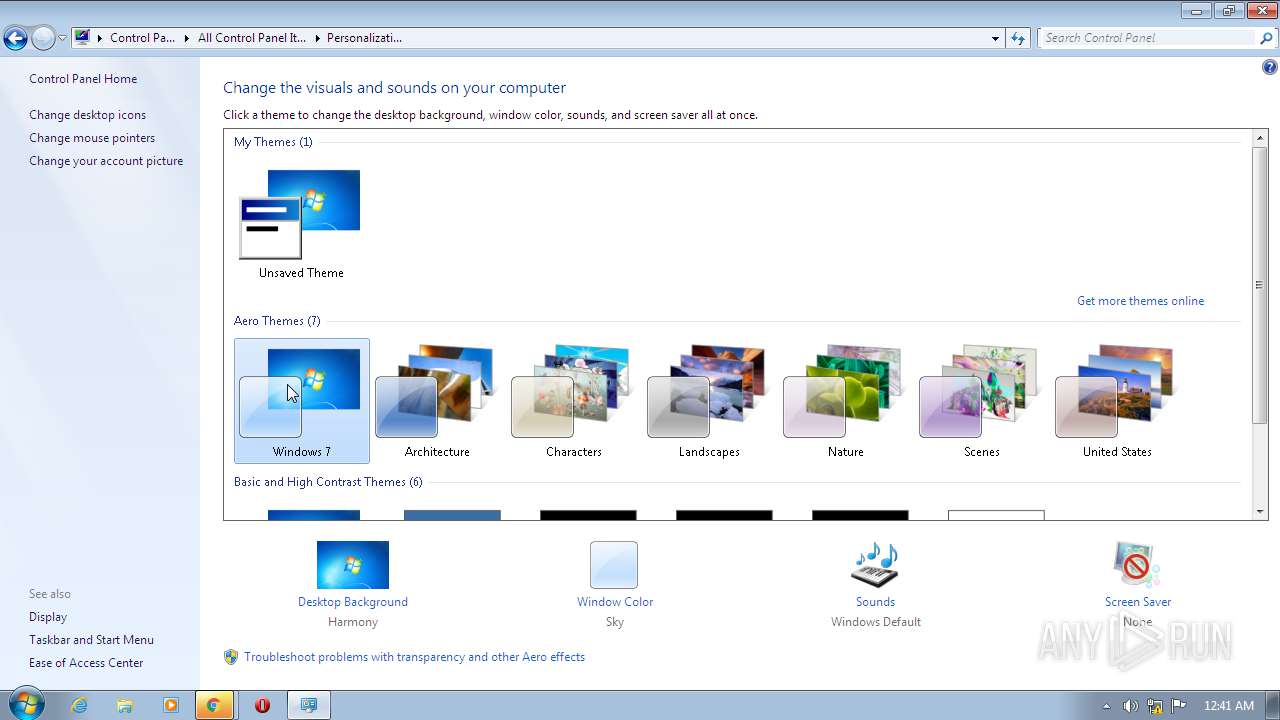
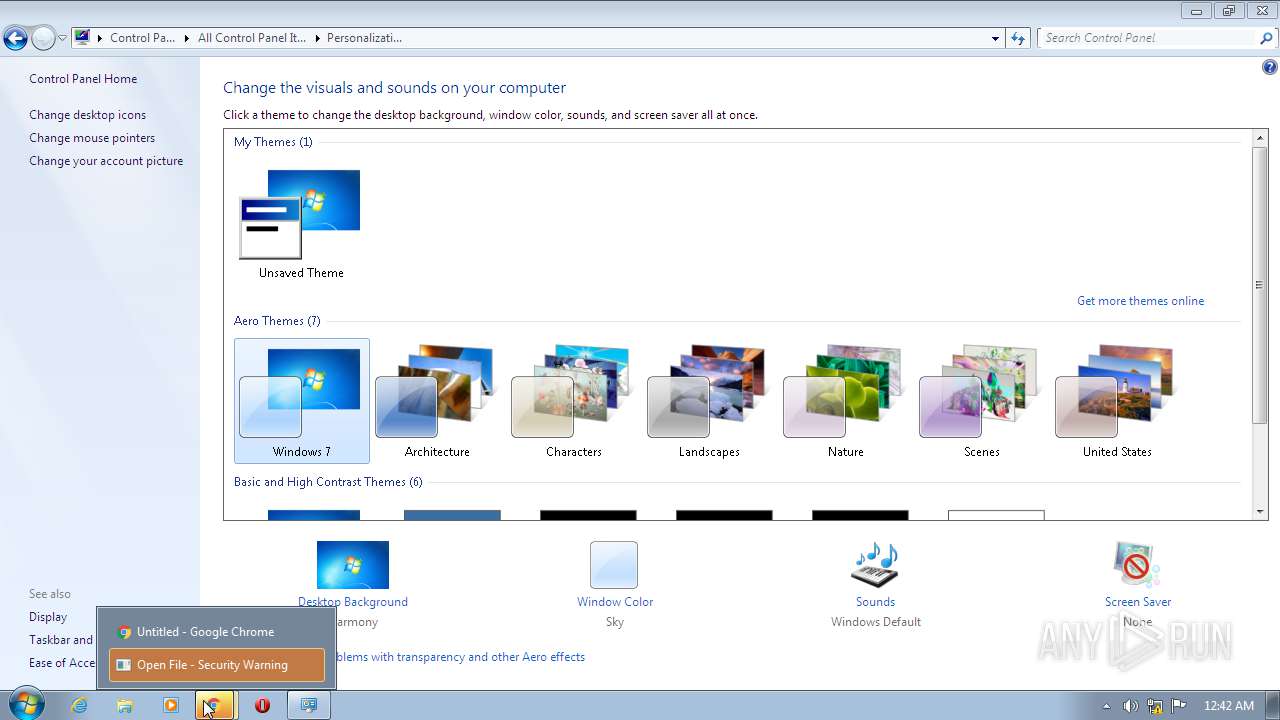
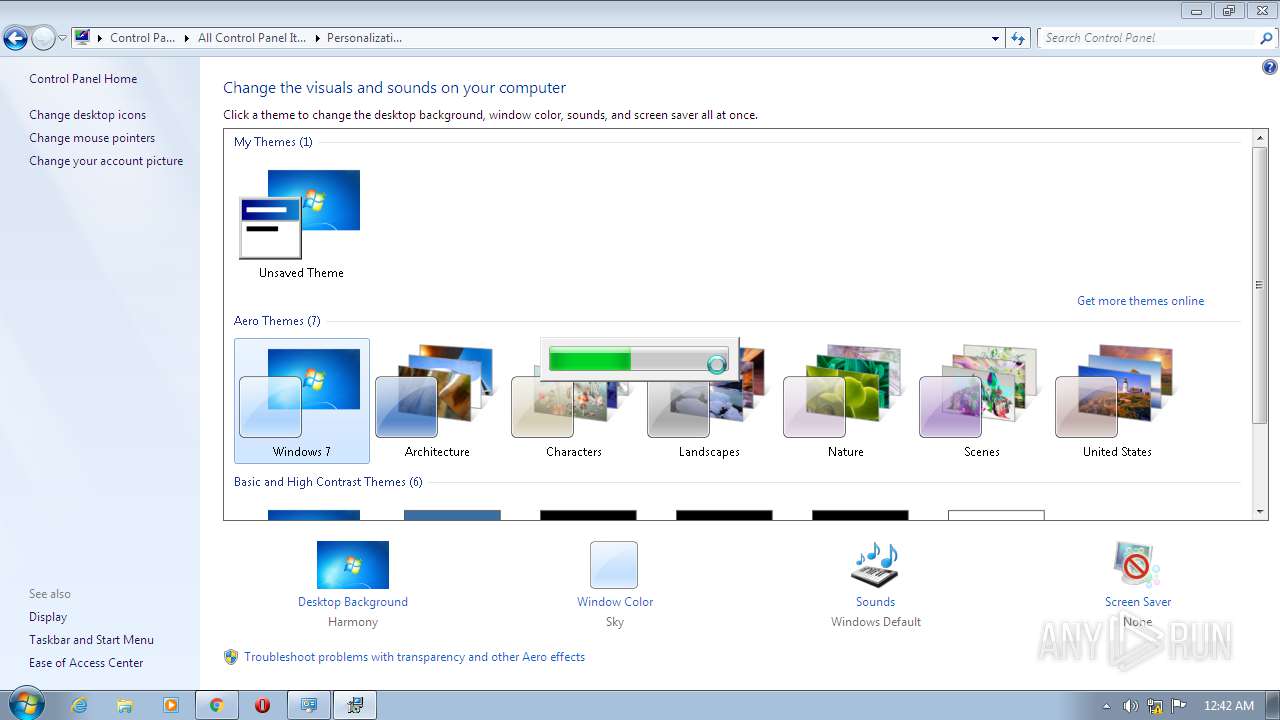
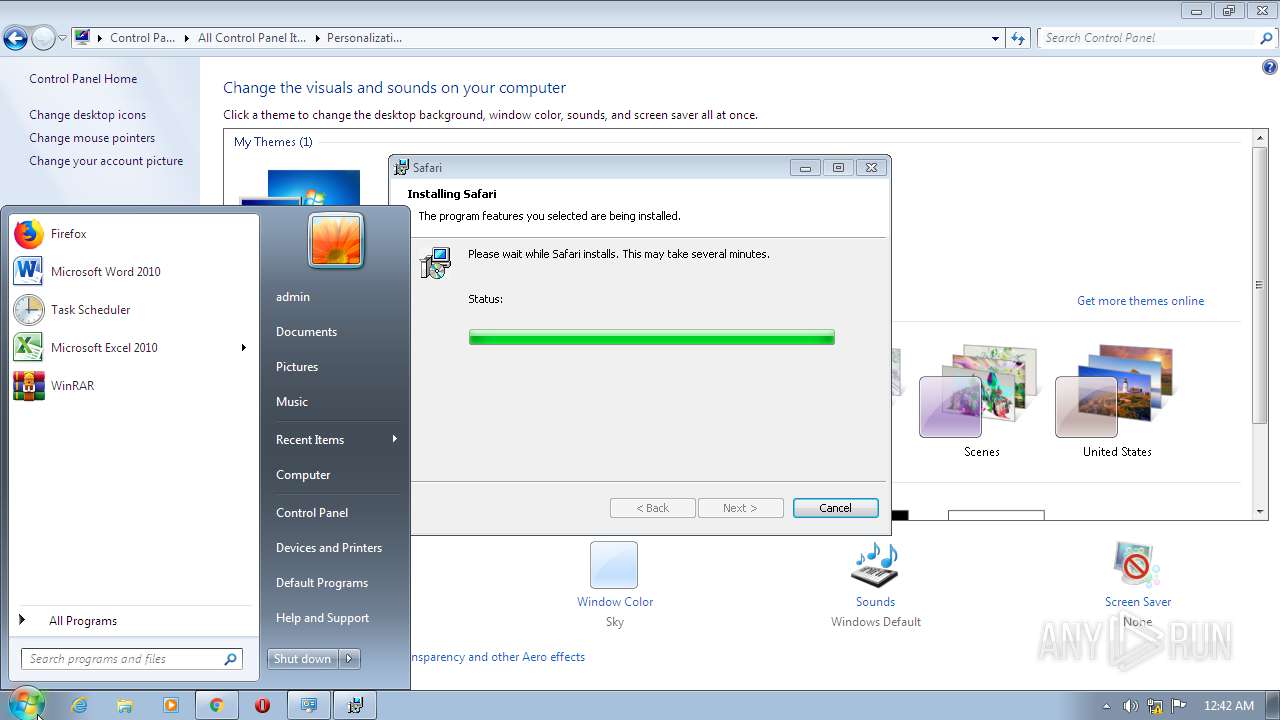
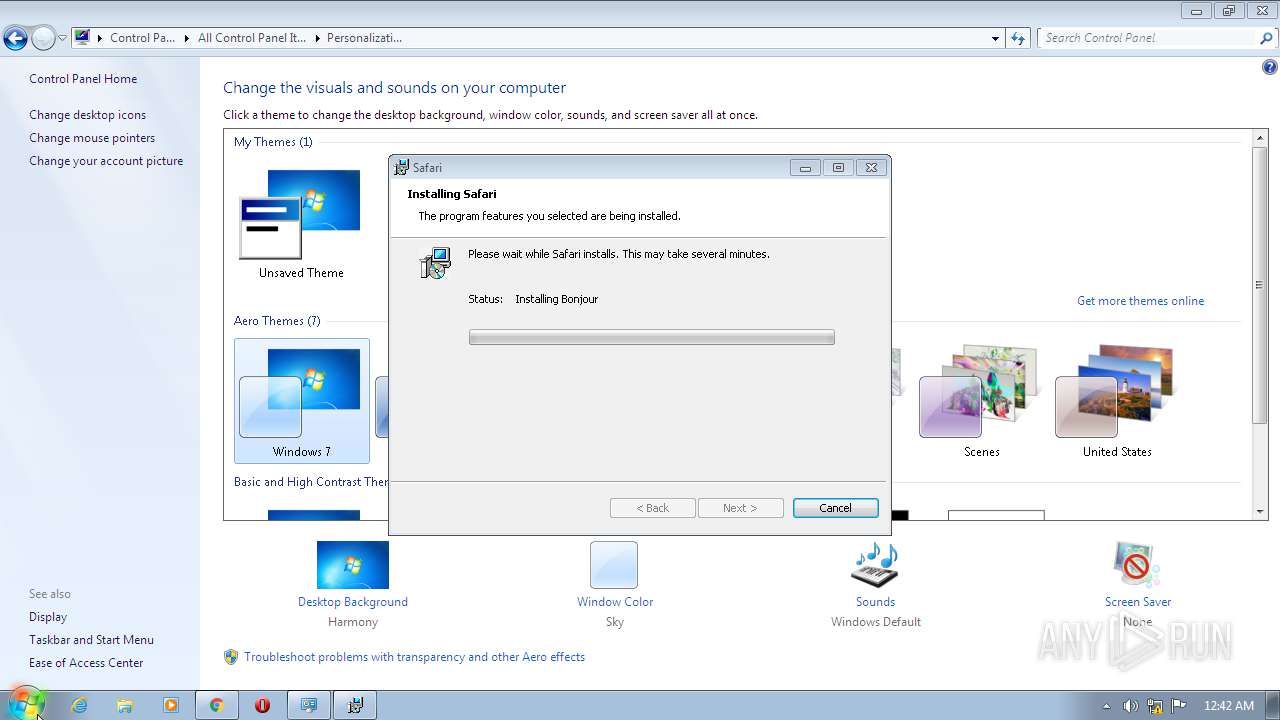
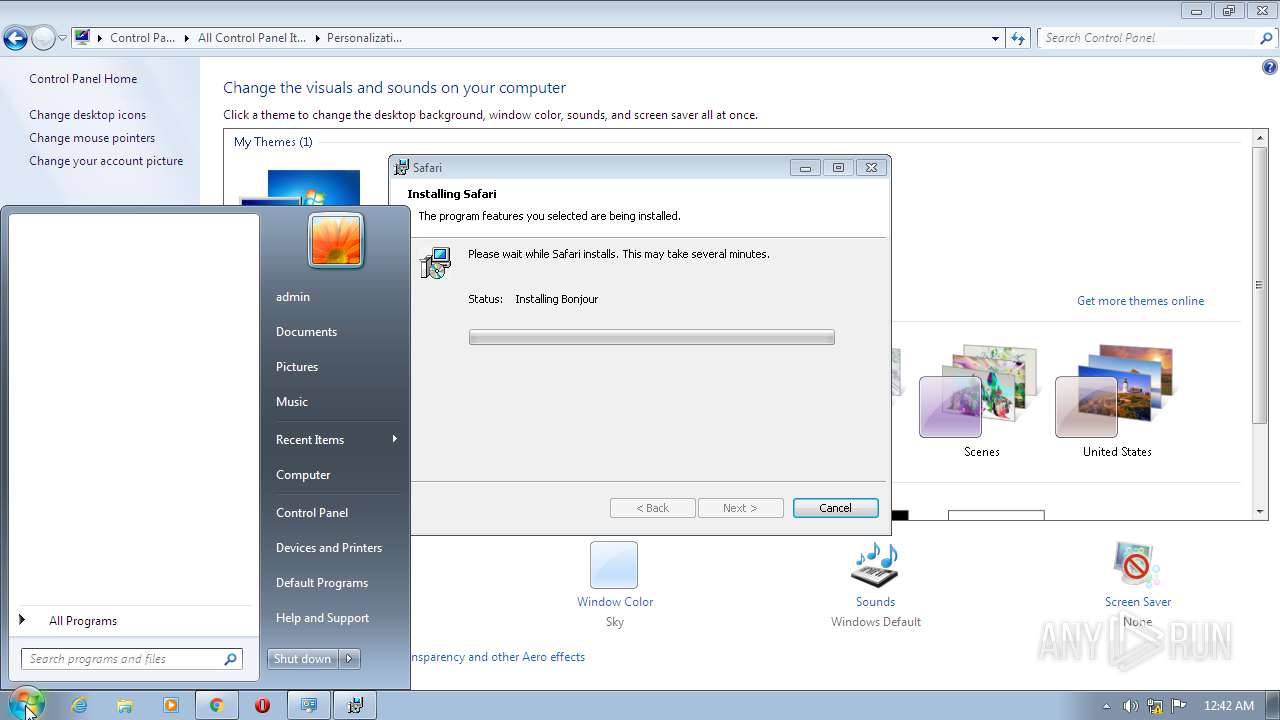
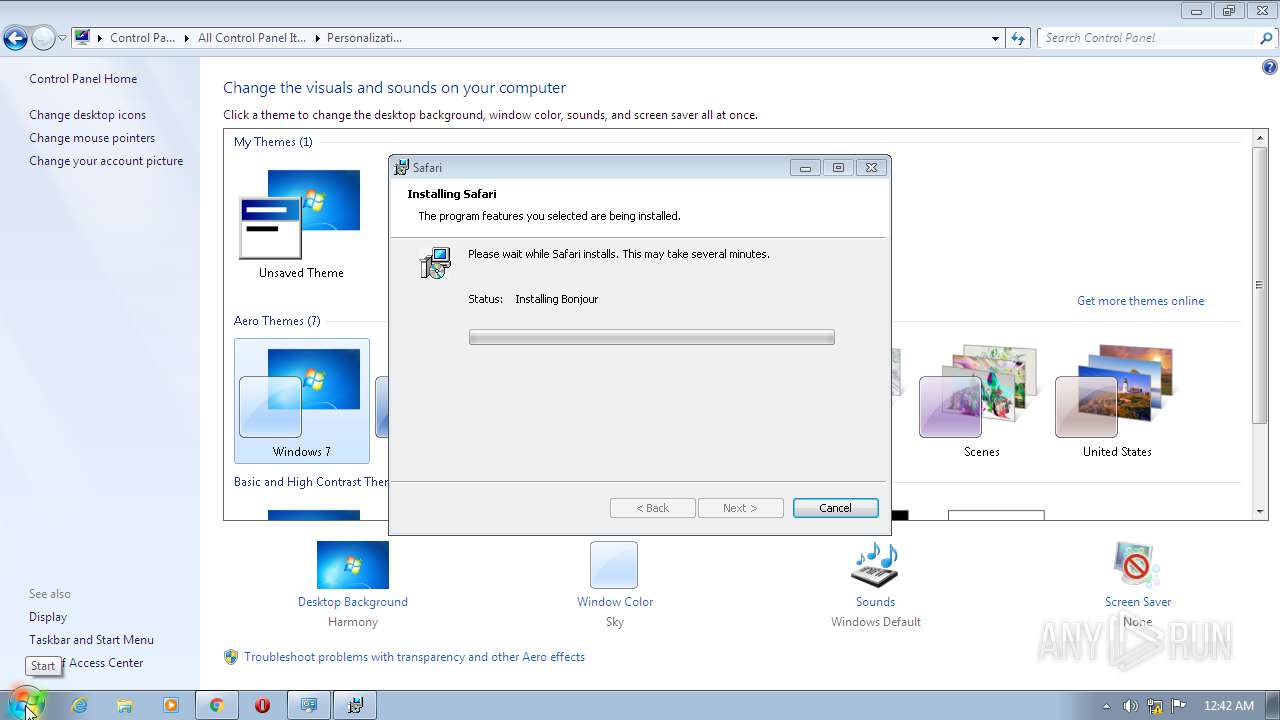
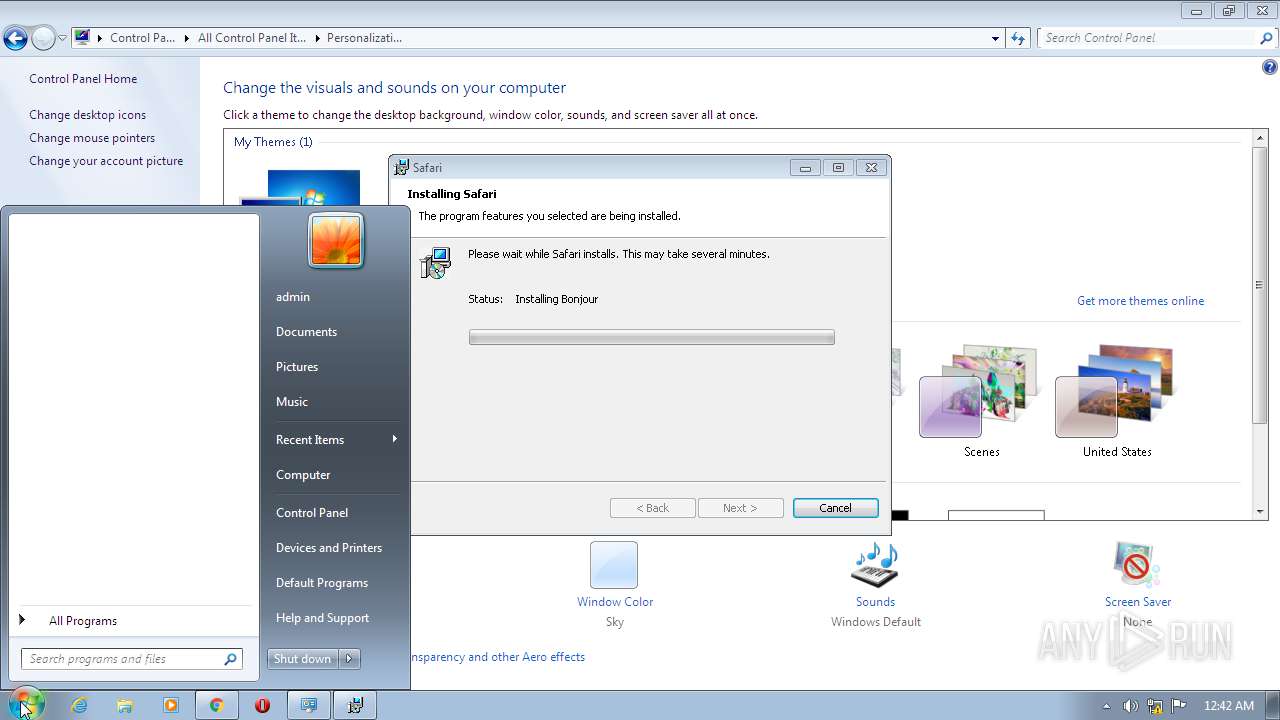
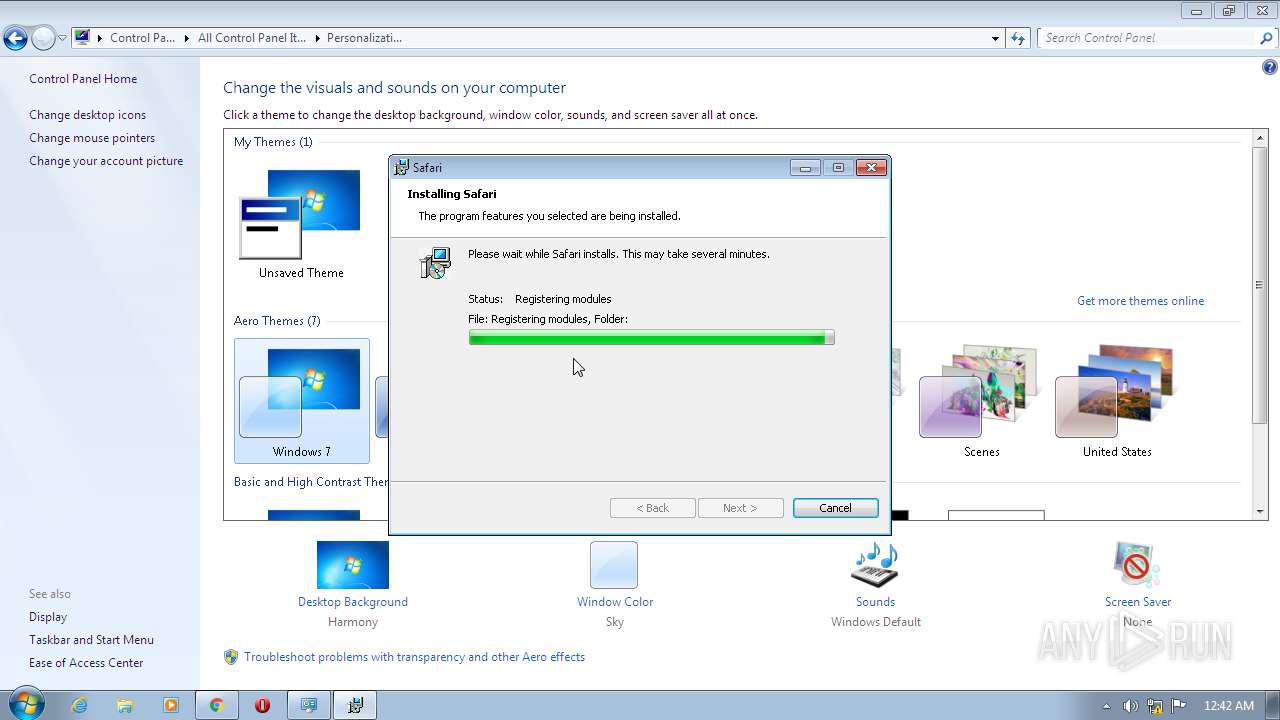
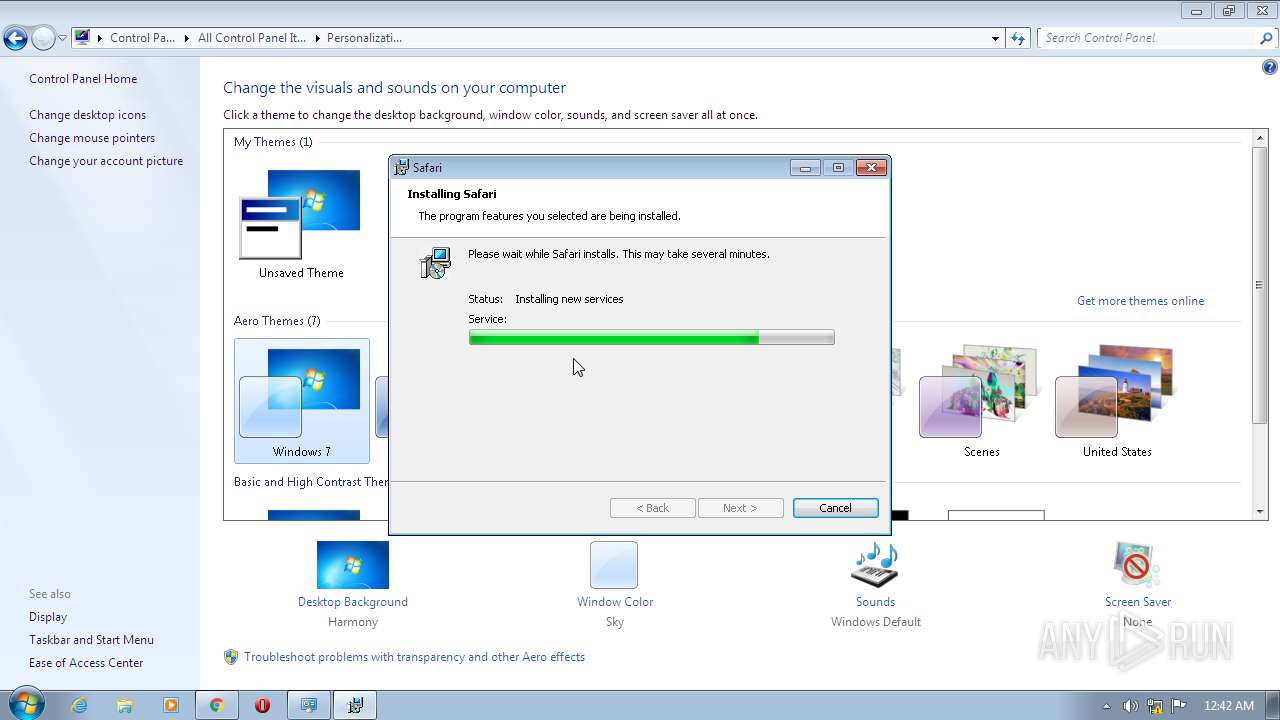
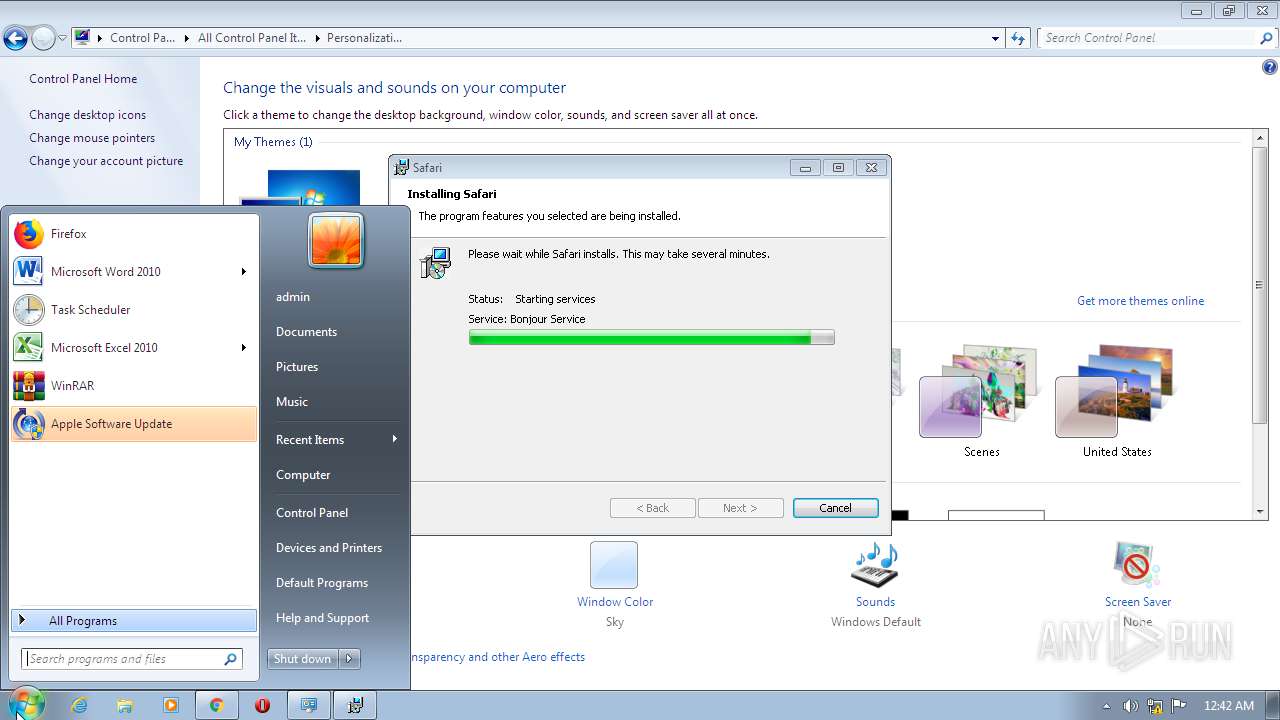
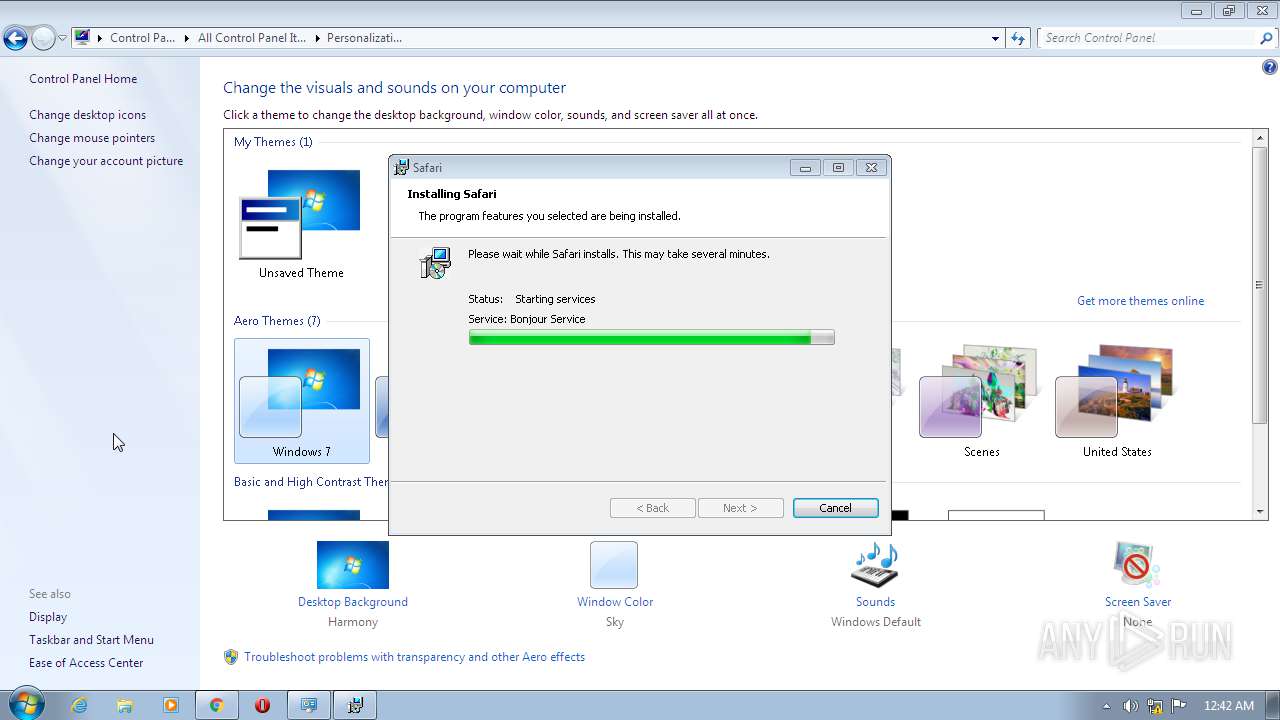
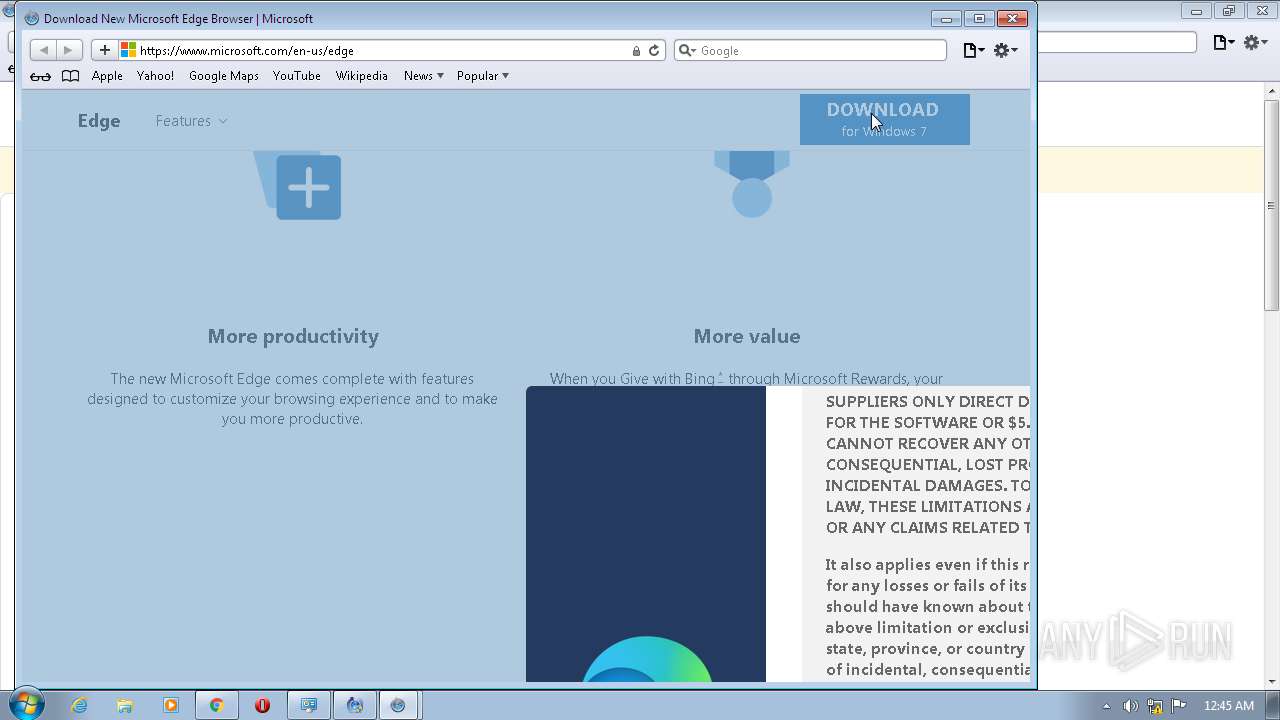
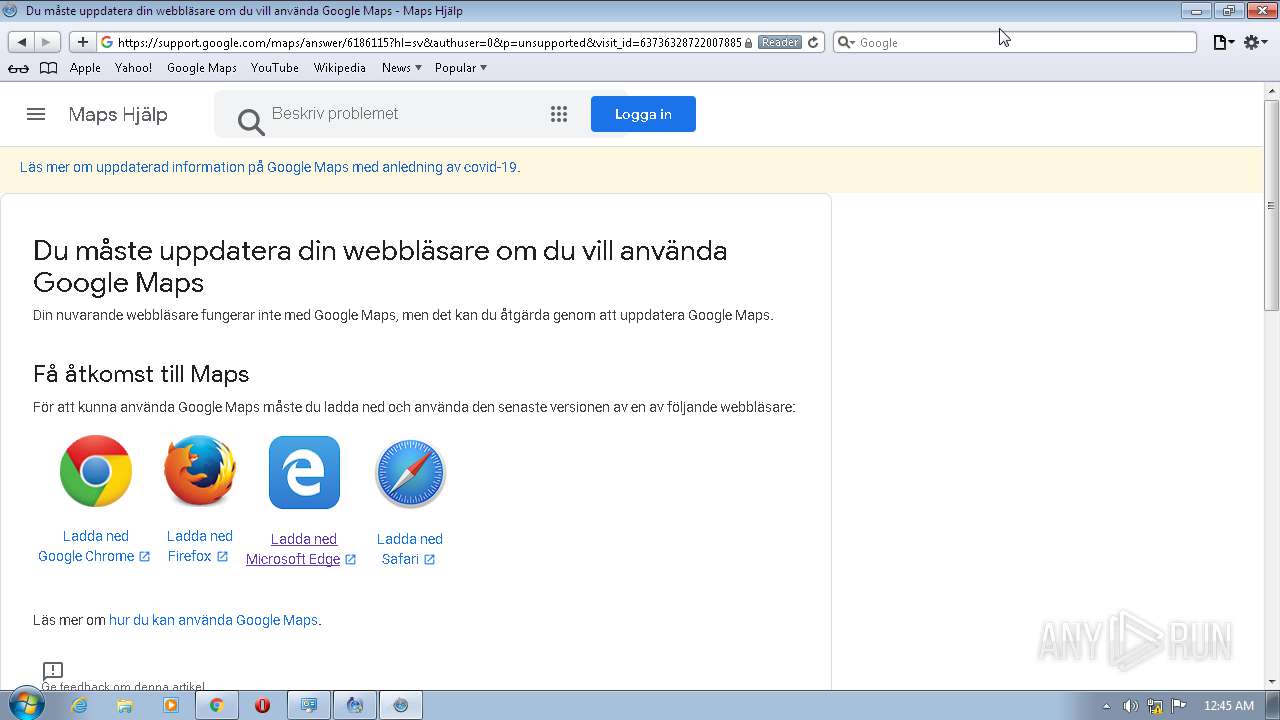
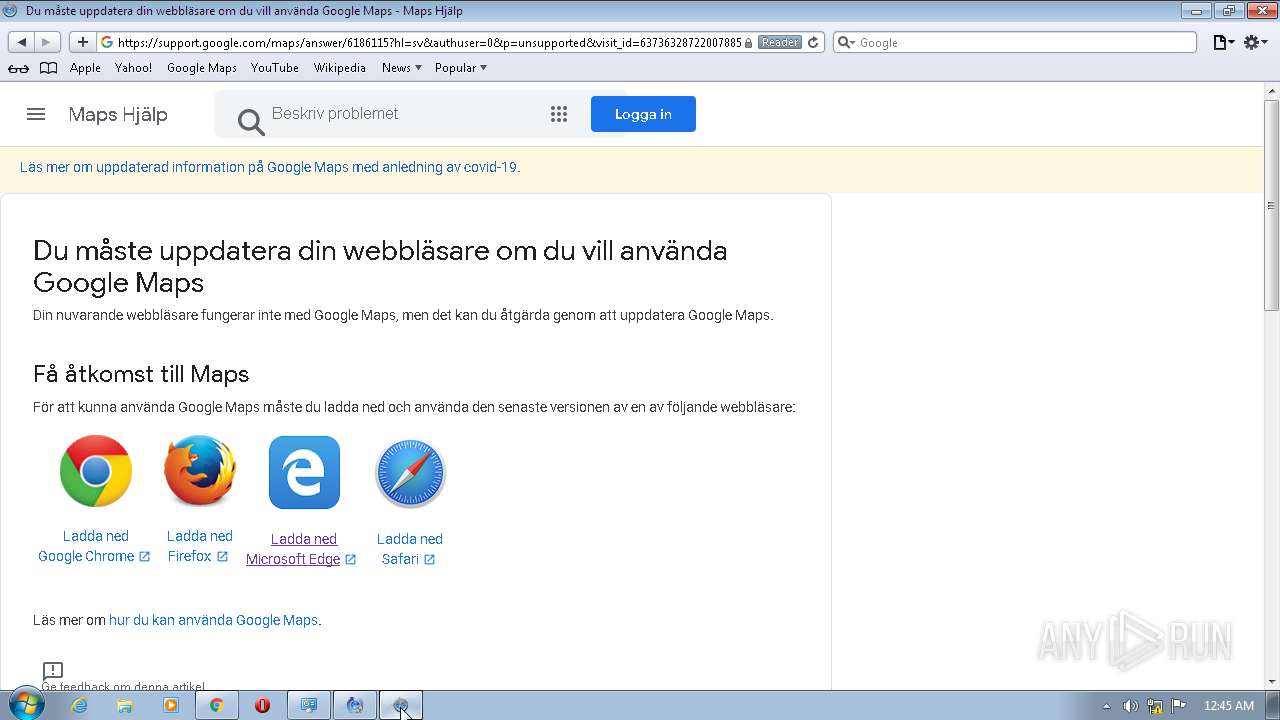
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 17EE6388DFC1D764494E98ED476371AE |
| SHA1: | A1AEB0F64AA2397BE3AEEB83B22BBD2F14F7BDFC |
| SHA256: | 5F3FE01AC01E3BEEA9F9853E7CA4D1B439E1C32CB8E706979307A13751048433 |
| SSDEEP: | 6:2nVkbWycrll/YUrCAJ9g41u3ORROikMz3/UlA:2VaiPJaOZfz9 |
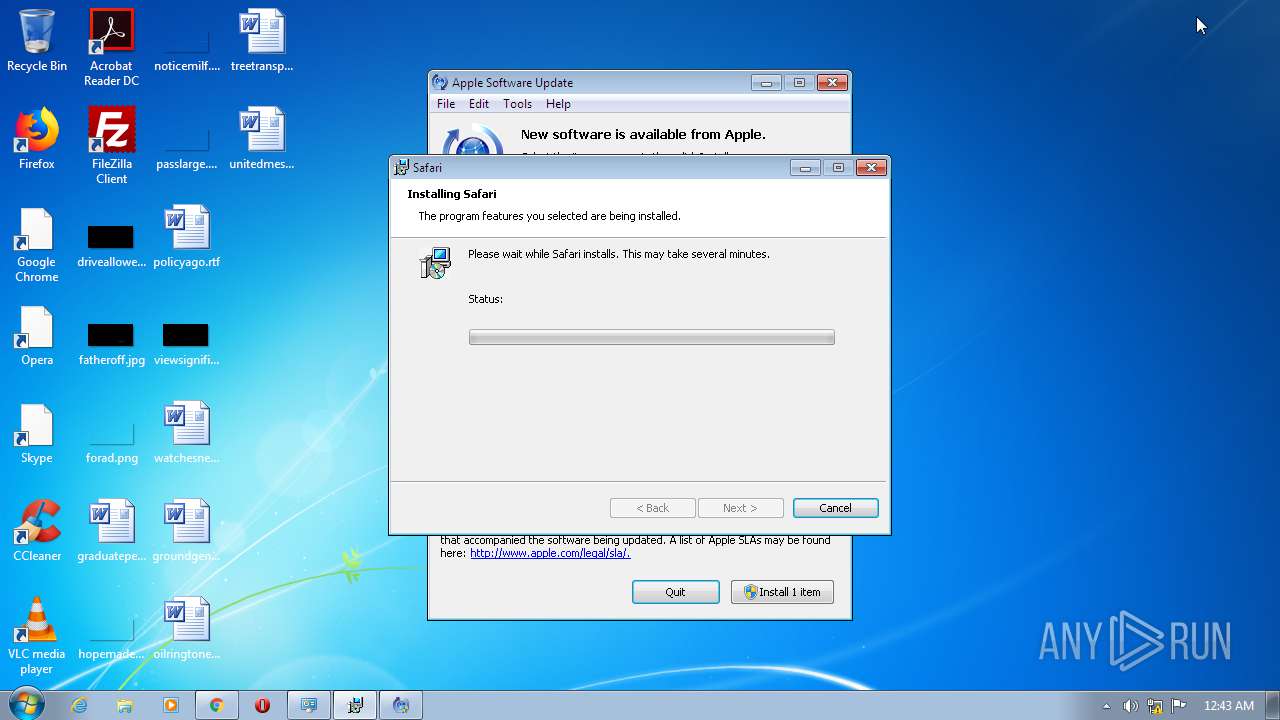
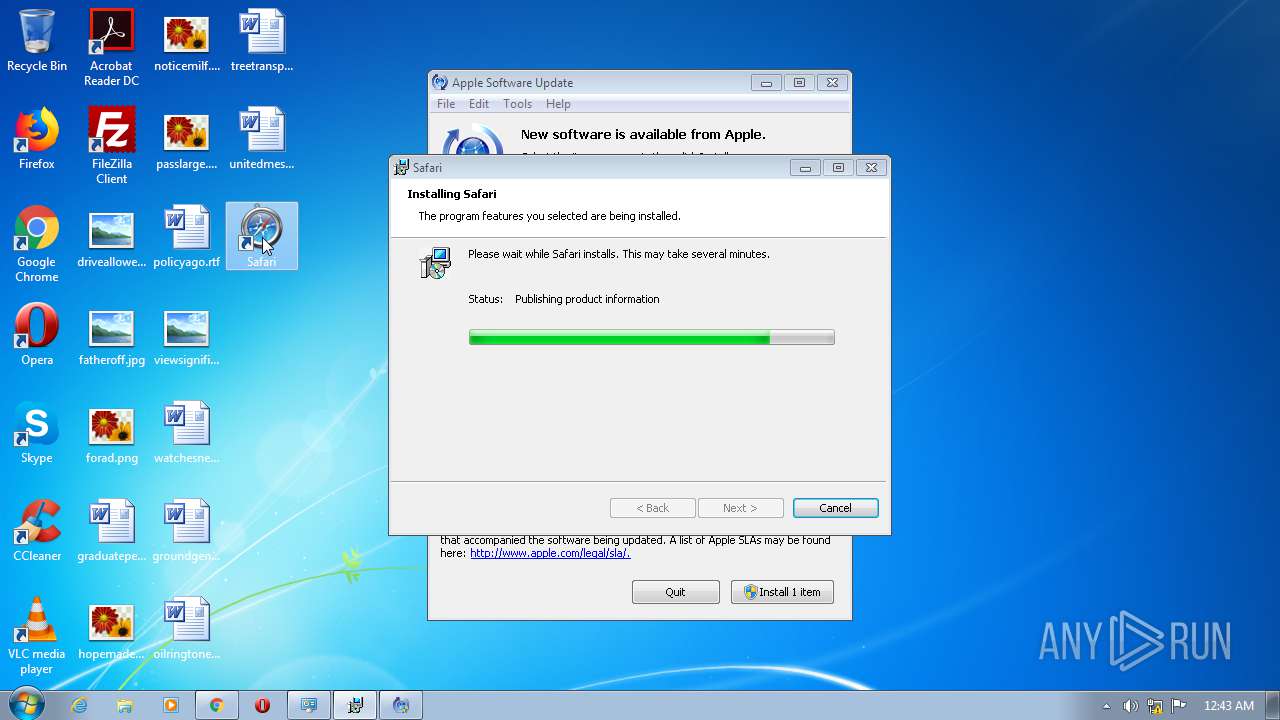
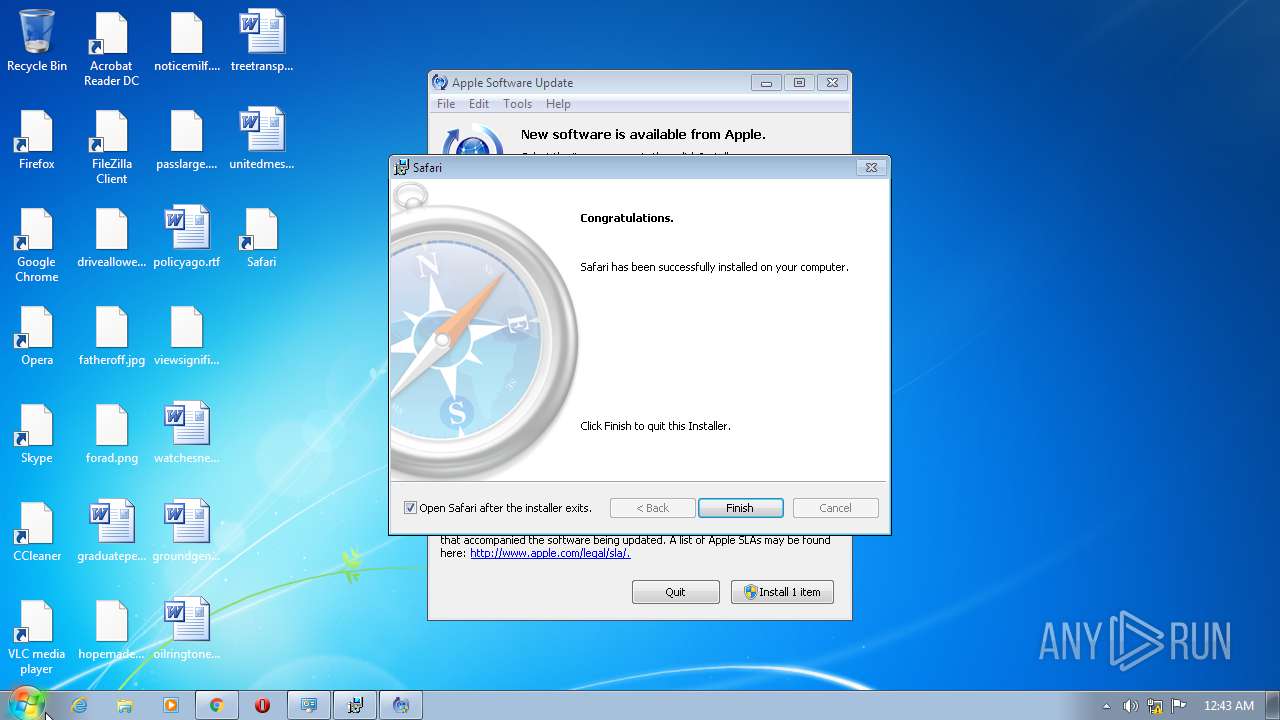
MALICIOUS
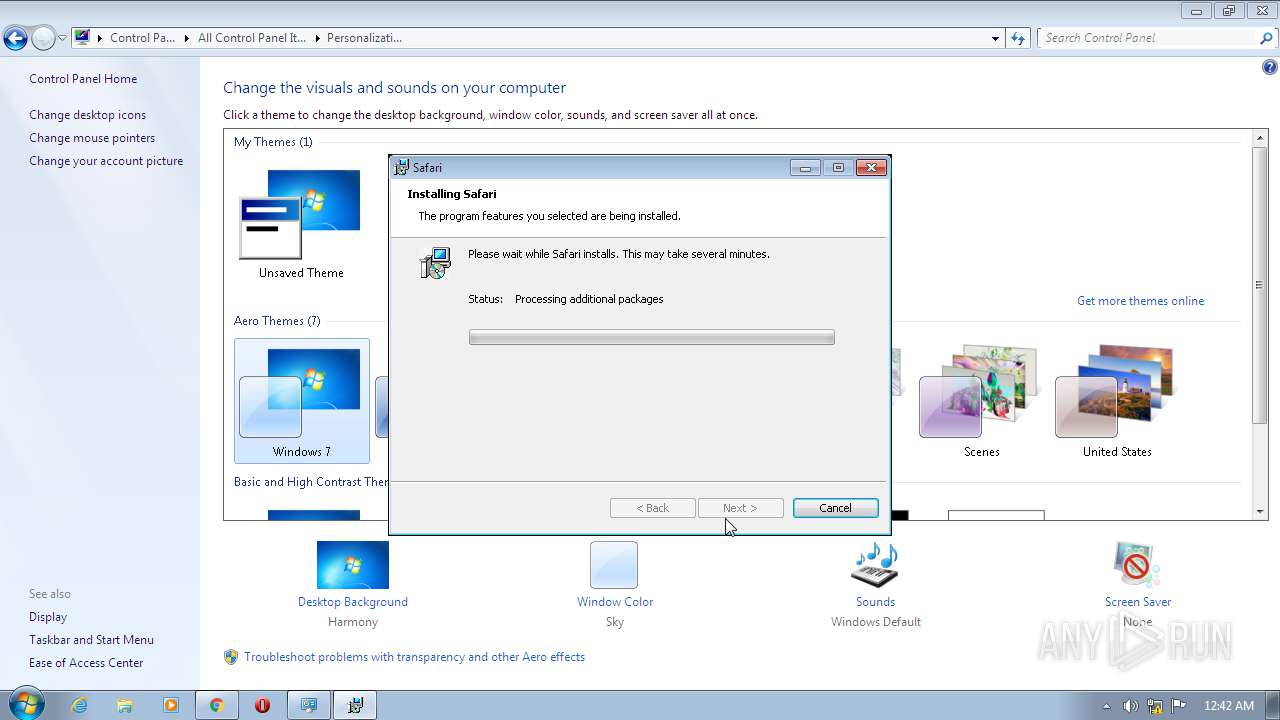
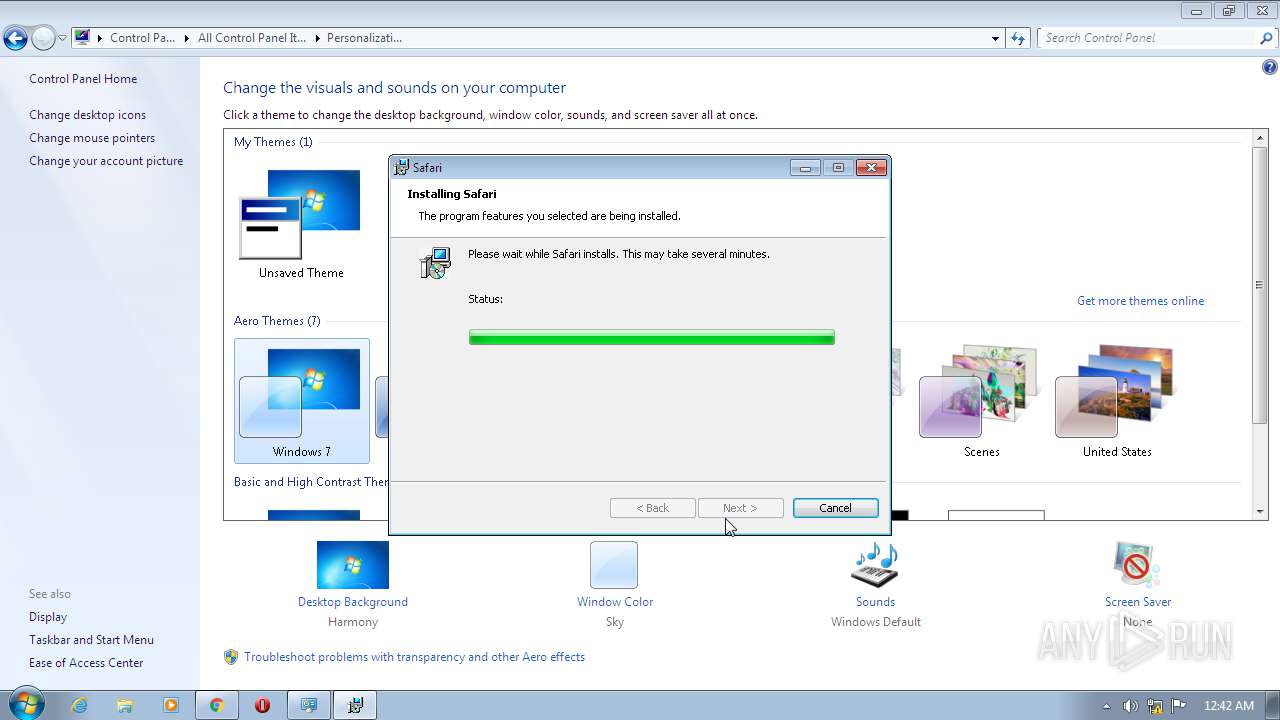
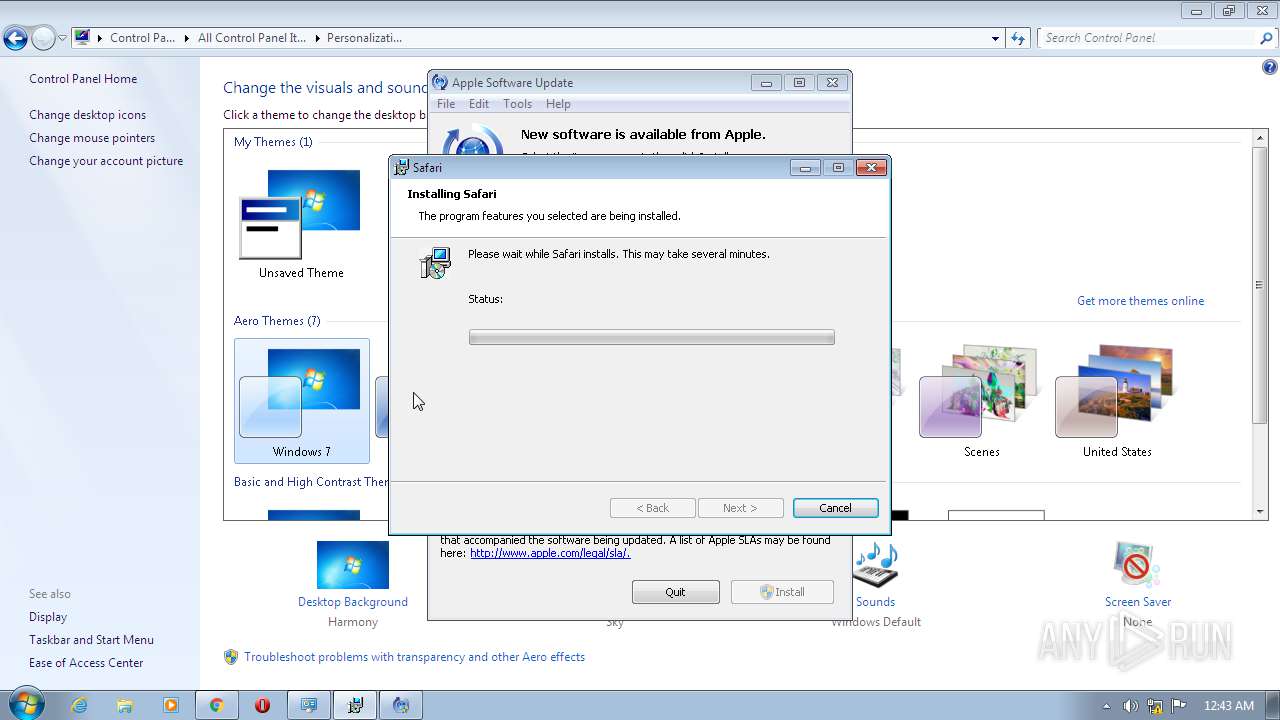
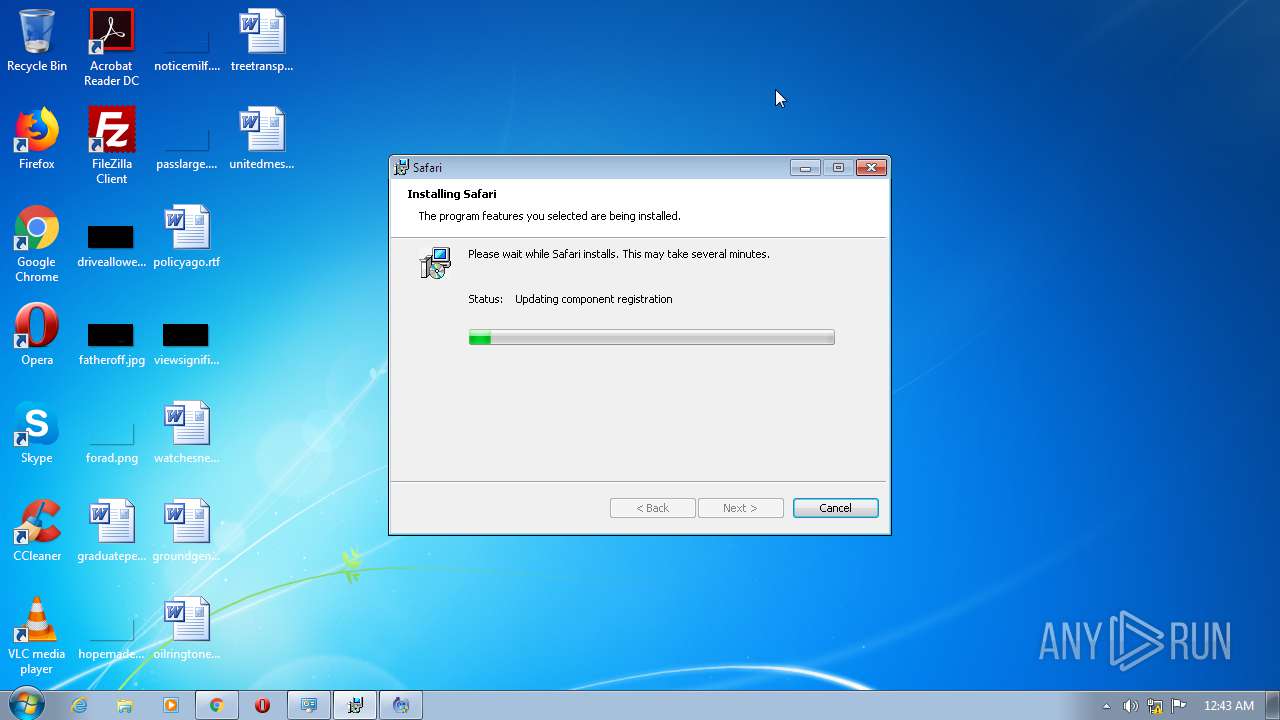
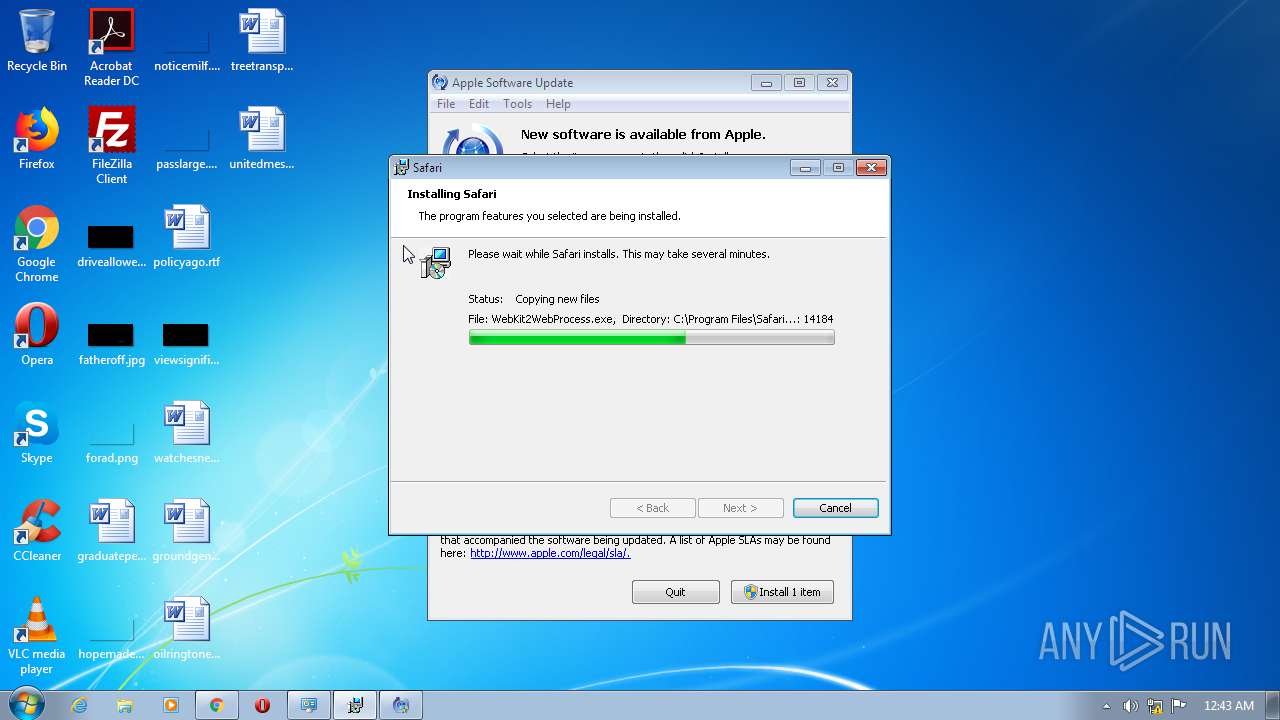
Application was dropped or rewritten from another process
- SafariSetup.exe (PID: 1800)
- SetupAdmin.exe (PID: 1932)
- SetupAdmin.exe (PID: 1196)
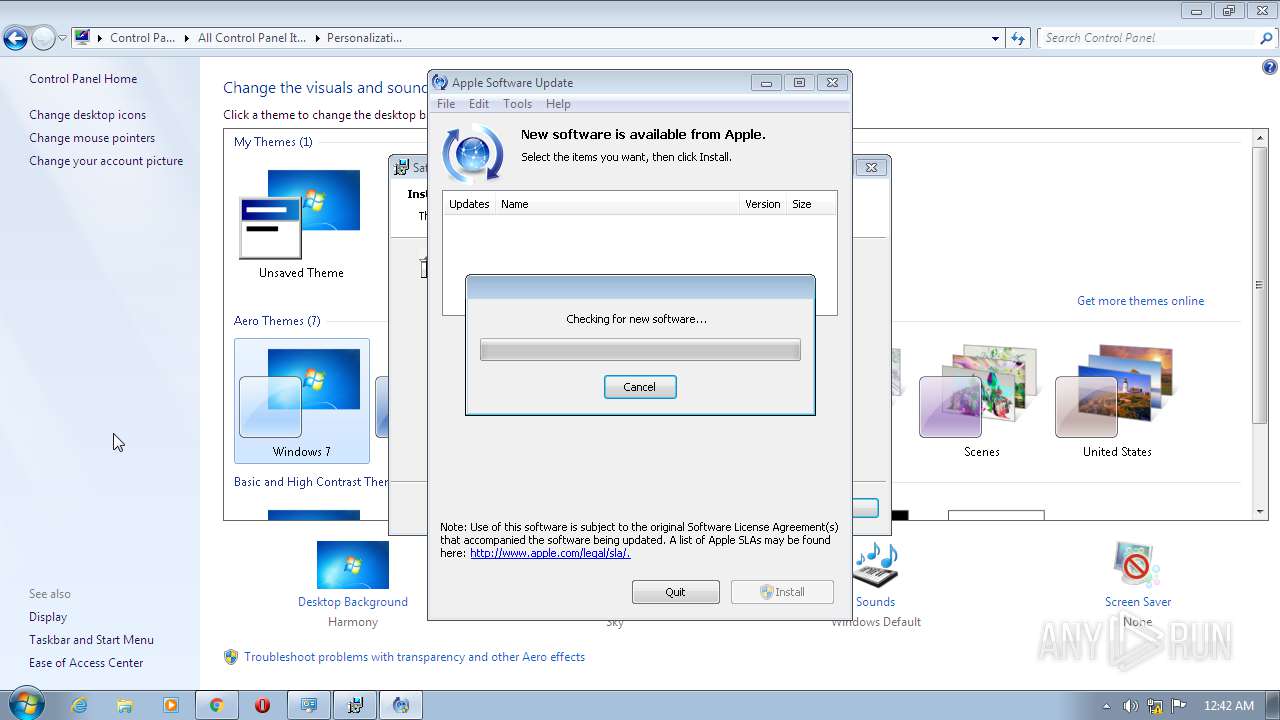
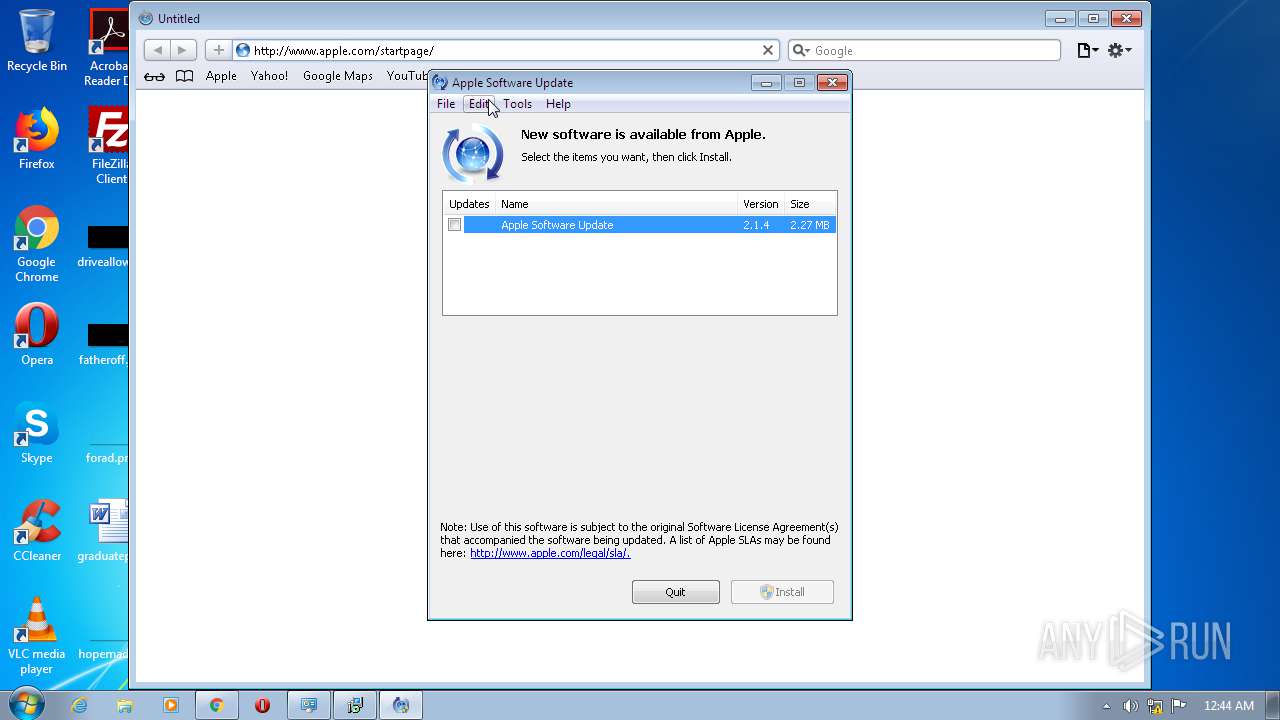
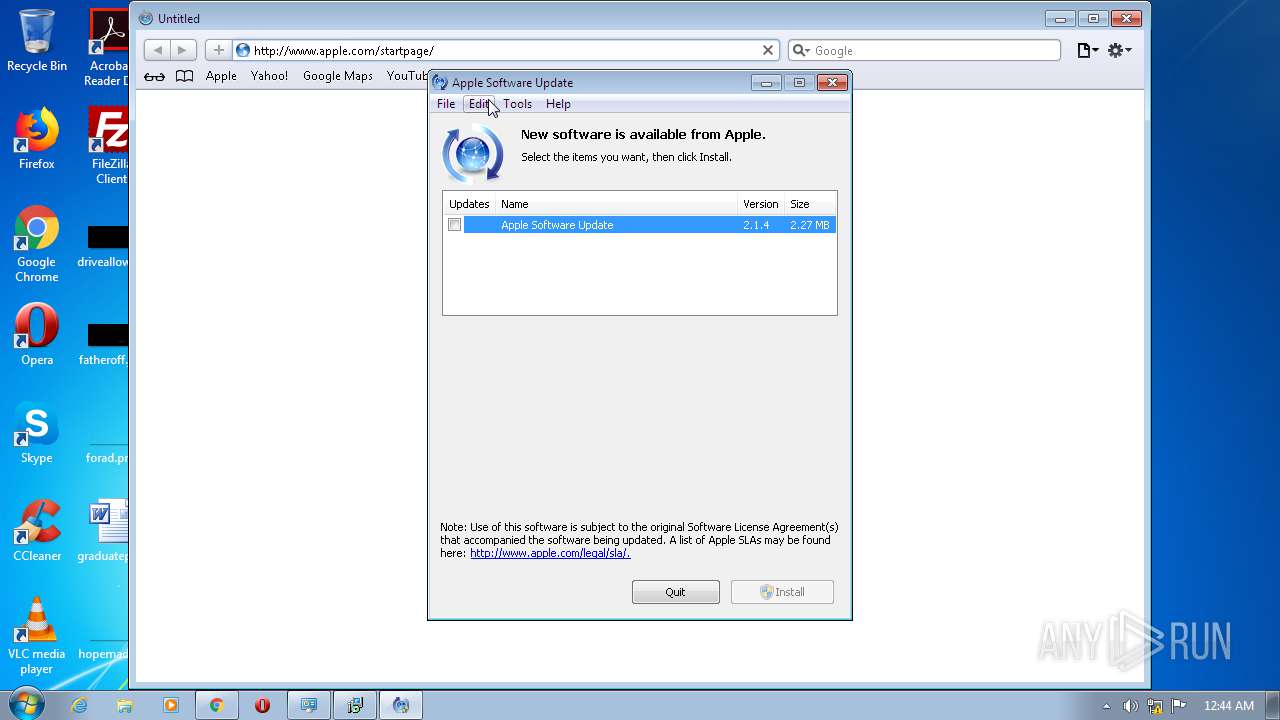
- SoftwareUpdate.exe (PID: 3280)
- mDNSResponder.exe (PID: 3416)
- SoftwareUpdate.exe (PID: 3356)
- Safari.exe (PID: 3488)
- WebKit2WebProcess.exe (PID: 3484)
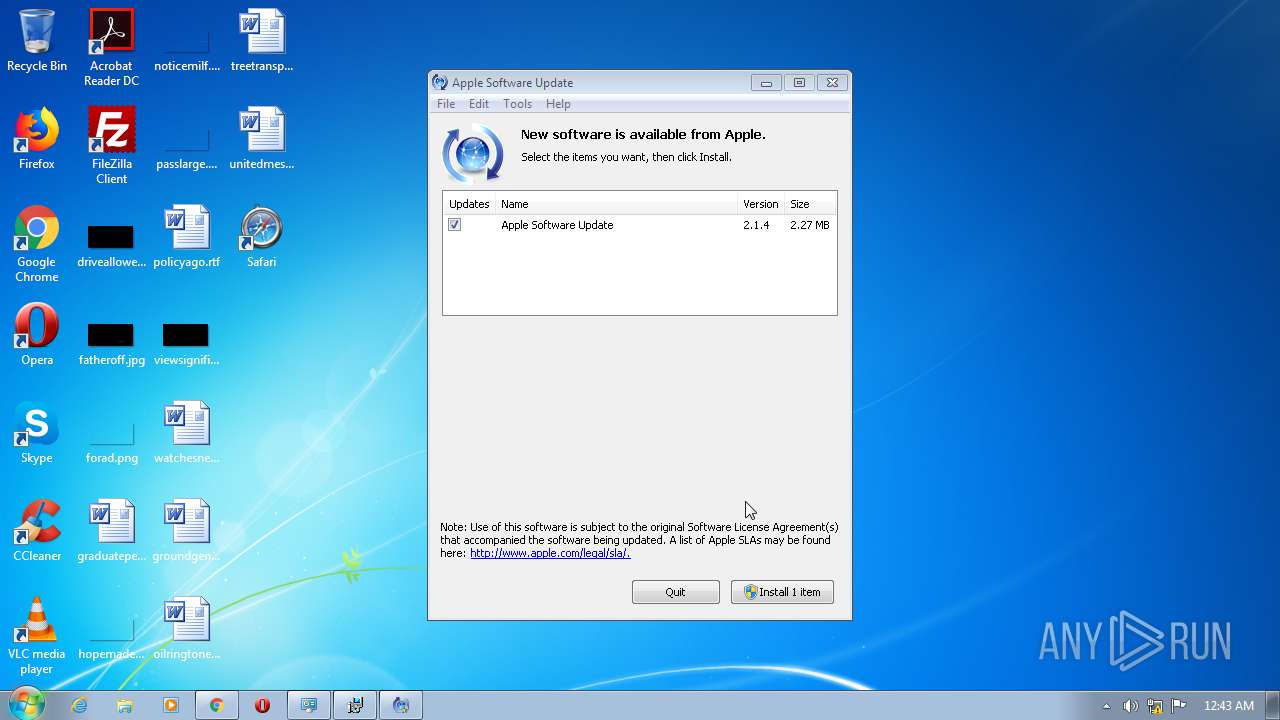
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2392)
- MsiExec.exe (PID: 2304)
- svchost.exe (PID: 676)
- DllHost.exe (PID: 296)
- MsiExec.exe (PID: 2588)
- SoftwareUpdate.exe (PID: 3280)
- explorer.exe (PID: 352)
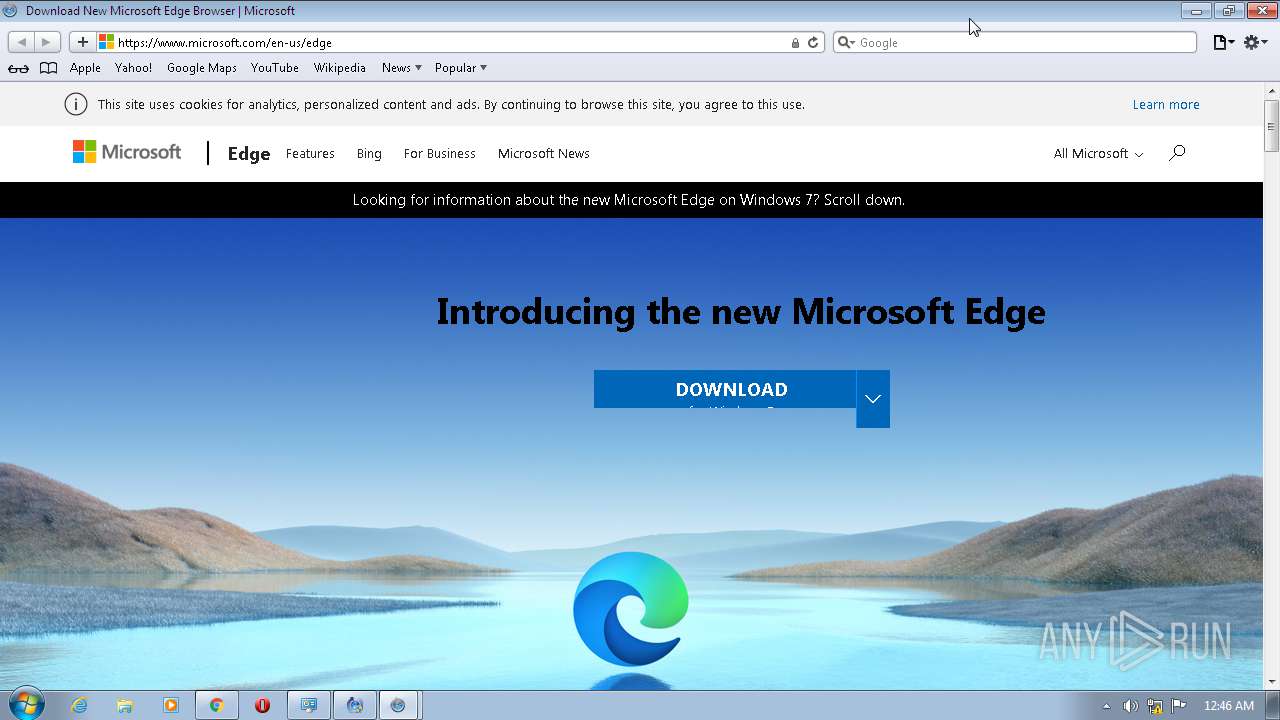
- chrome.exe (PID: 1704)
- svchost.exe (PID: 856)
- DllHost.exe (PID: 4036)
- Safari.exe (PID: 3488)
- WebKit2WebProcess.exe (PID: 3484)
- SoftwareUpdate.exe (PID: 3356)
Loads the Task Scheduler COM API
- DllHost.exe (PID: 296)
- DllHost.exe (PID: 4036)
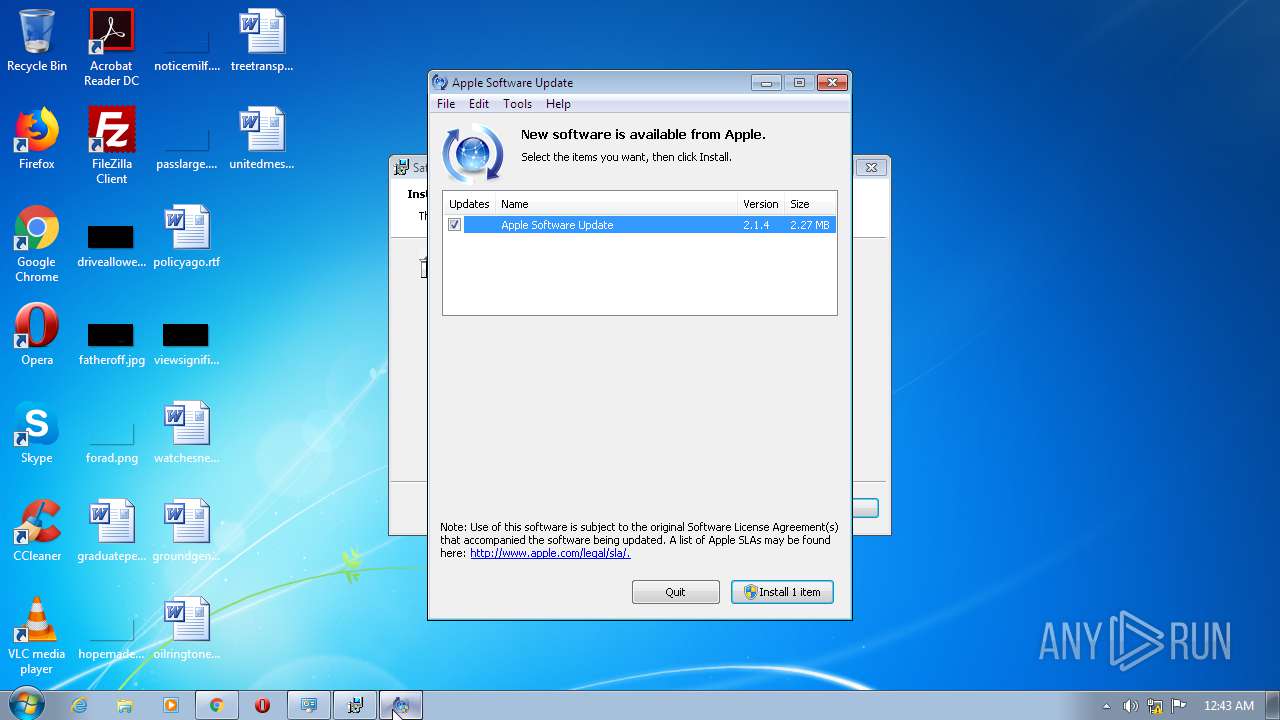
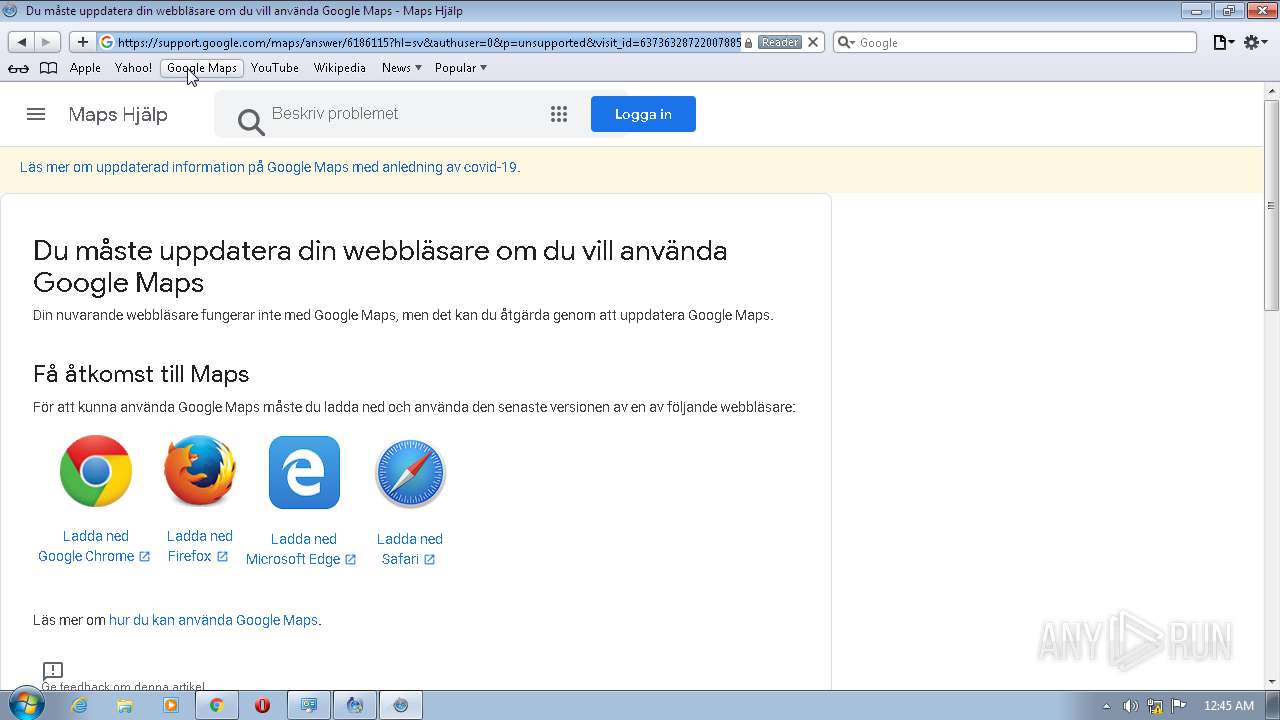
Changes settings of System certificates
- Safari.exe (PID: 3488)
- WebKit2WebProcess.exe (PID: 3484)
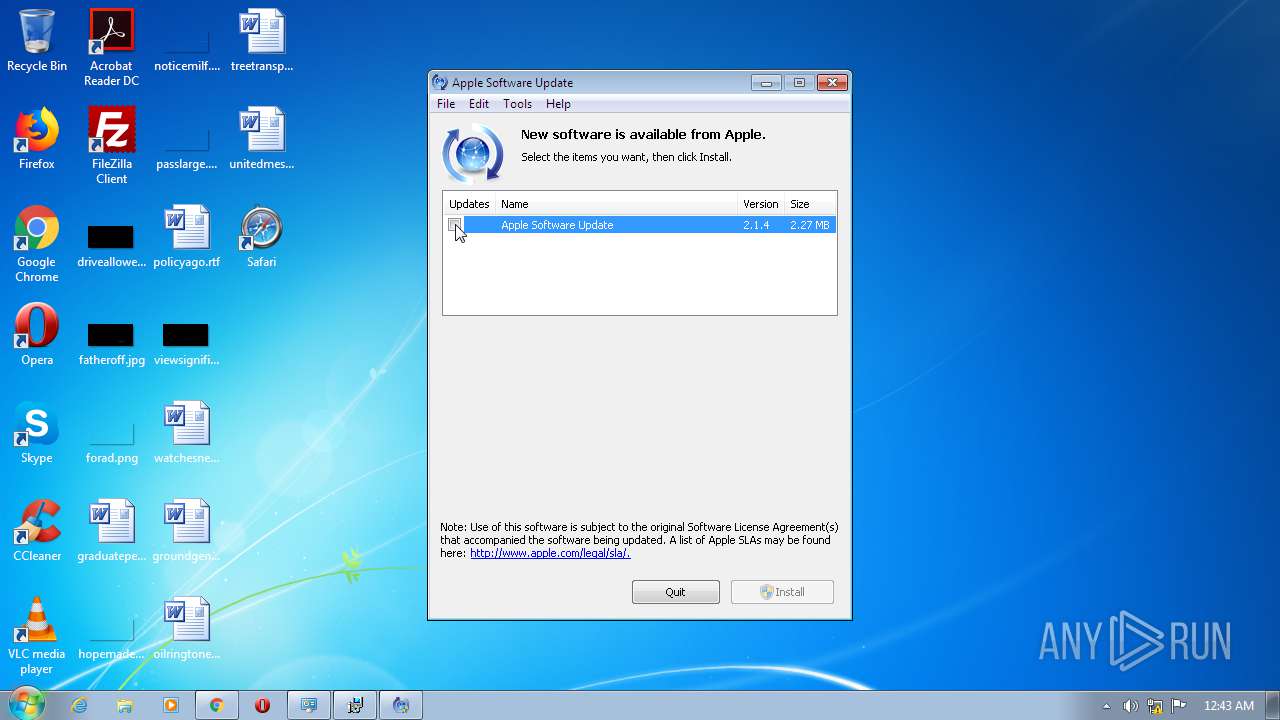
SUSPICIOUS
Executable content was dropped or overwritten
- SafariSetup.exe (PID: 1800)
- chrome.exe (PID: 4092)
- msiexec.exe (PID: 2452)
Creates files in the user directory
- explorer.exe (PID: 352)
- Safari.exe (PID: 3488)
- WebKit2WebProcess.exe (PID: 3484)
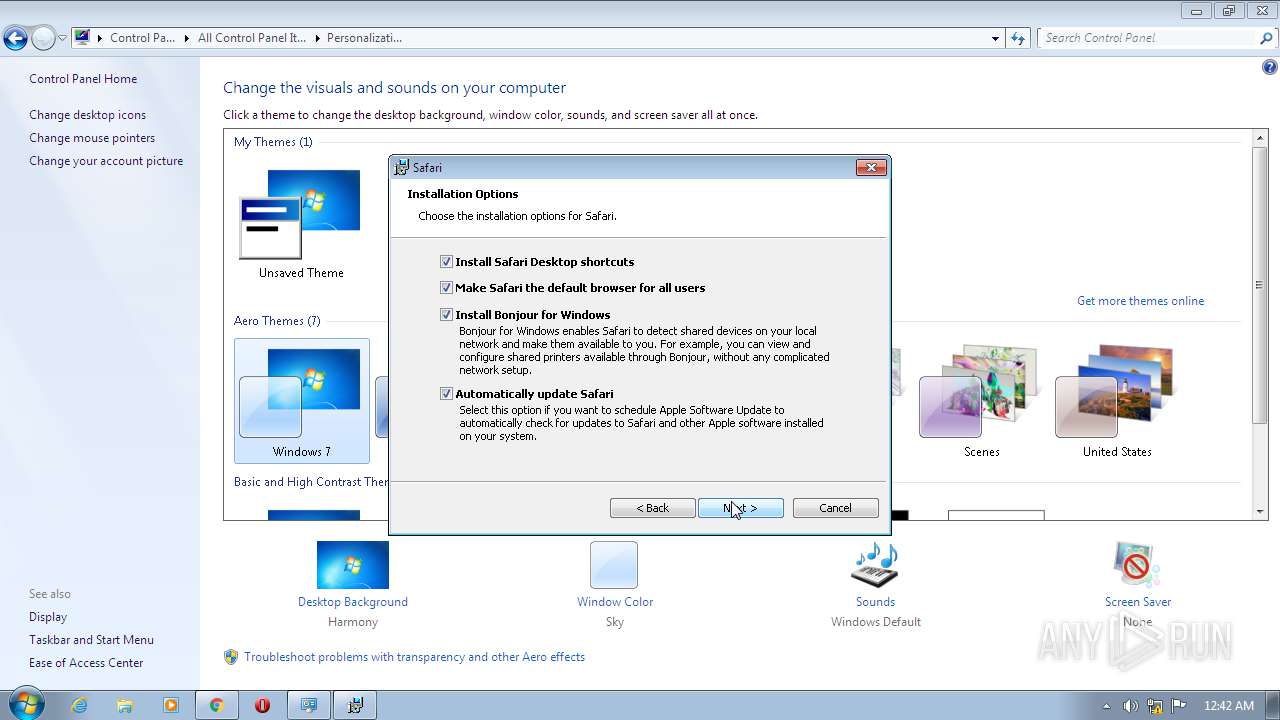
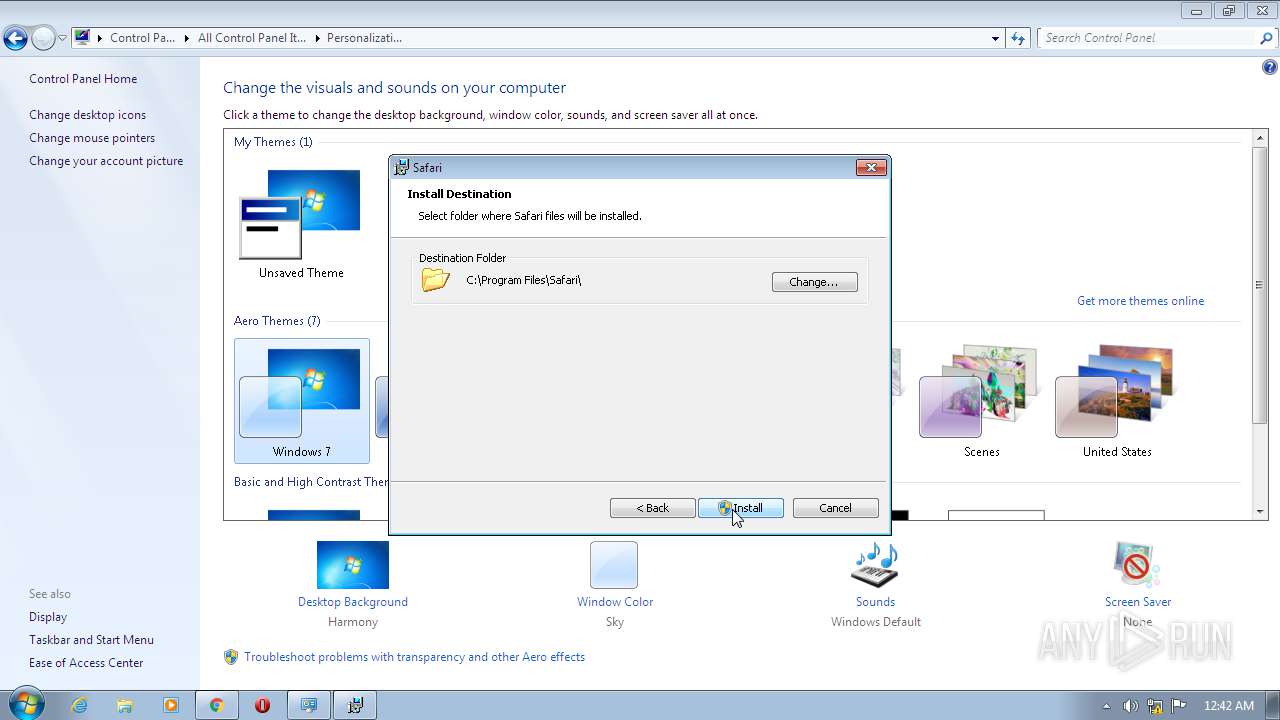
Starts Microsoft Installer
- SafariSetup.exe (PID: 1800)
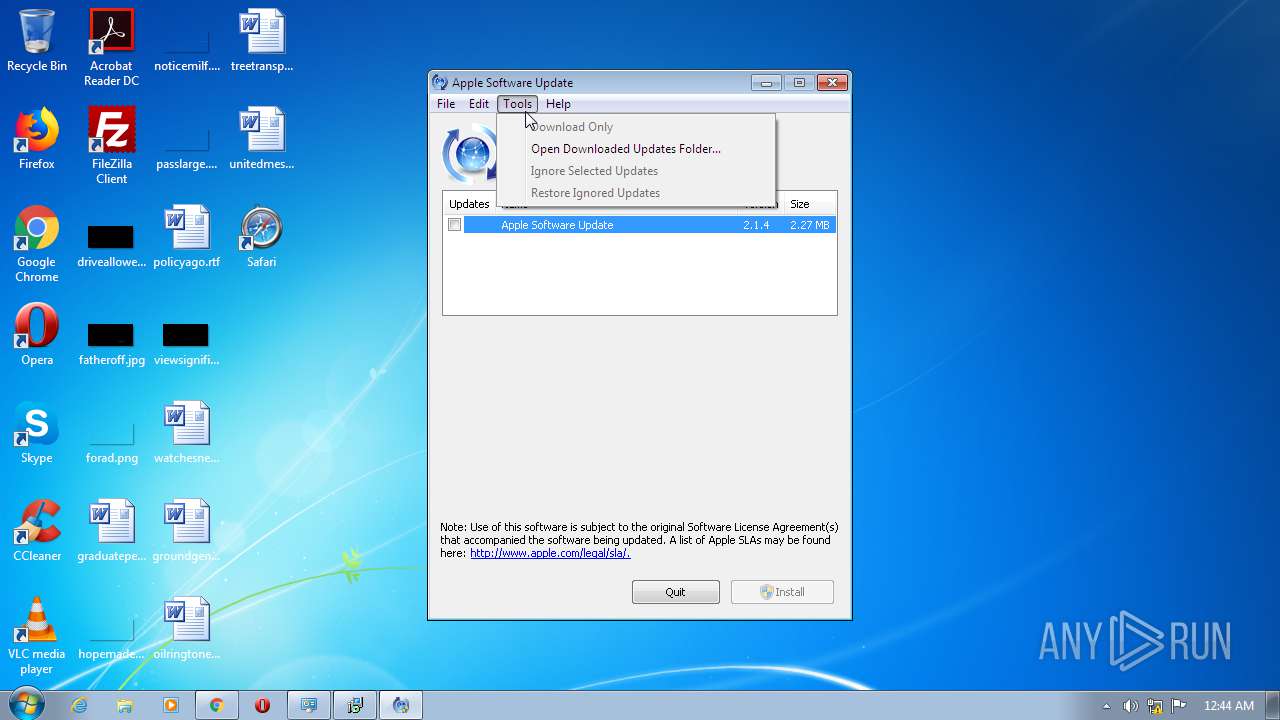
Executed via COM
- DllHost.exe (PID: 296)
- DllHost.exe (PID: 4036)
- DllHost.exe (PID: 3584)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 856)
Creates COM task schedule object
- MsiExec.exe (PID: 2392)
Creates files in the Windows directory
- svchost.exe (PID: 856)
Executed as Windows Service
- mDNSResponder.exe (PID: 3416)
Reads internet explorer settings
- SoftwareUpdate.exe (PID: 3356)
Reads Internet Cache Settings
- SoftwareUpdate.exe (PID: 3356)
- DllHost.exe (PID: 3584)
- WebKit2WebProcess.exe (PID: 3484)
- Safari.exe (PID: 3488)
Adds / modifies Windows certificates
- Safari.exe (PID: 3488)
- WebKit2WebProcess.exe (PID: 3484)
Modifies files in Chrome extension folder
- chrome.exe (PID: 4092)
INFO
Application launched itself
- chrome.exe (PID: 4092)
Reads the hosts file
- chrome.exe (PID: 4092)
- chrome.exe (PID: 1704)
Reads Internet Cache Settings
- chrome.exe (PID: 4092)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 4012)
- MsiExec.exe (PID: 2844)
- MsiExec.exe (PID: 1876)
- MsiExec.exe (PID: 2680)
- MsiExec.exe (PID: 2880)
- MsiExec.exe (PID: 2136)
Reads settings of System Certificates
- chrome.exe (PID: 1704)
Dropped object may contain Bitcoin addresses
- SoftwareUpdate.exe (PID: 3356)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
88
Monitored processes
42
Malicious processes
8
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12759388776928340226,2827074850154119048,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6033188606228072522 --mojo-platform-channel-handle=2132 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 296 | C:\Windows\system32\DllHost.exe /Processid:{16D99191-6280-4B33-A2F5-04805A0FC582} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 352 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 372 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12759388776928340226,2827074850154119048,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16206378656216636483 --mojo-platform-channel-handle=1904 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 676 | C:\Windows\system32\svchost.exe -k RPCSS | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 856 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1196 | "C:\Users\admin\AppData\Local\Temp\IXP912.TMP\SetupAdmin.exe" /evt E783 /pid 2844 /mon 512 524 | C:\Users\admin\AppData\Local\Temp\IXP912.TMP\SetupAdmin.exe | MsiExec.exe | ||||||||||||
User: admin Company: Apple Inc. Integrity Level: HIGH Description: Apple Installer (Elevated) Exit code: 0 Version: 5.34.57.2 Modules
| |||||||||||||||
| 1276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,12759388776928340226,2827074850154119048,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11682359404802882158 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2448 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,12759388776928340226,2827074850154119048,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=9163786079732258108 --mojo-platform-channel-handle=1520 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
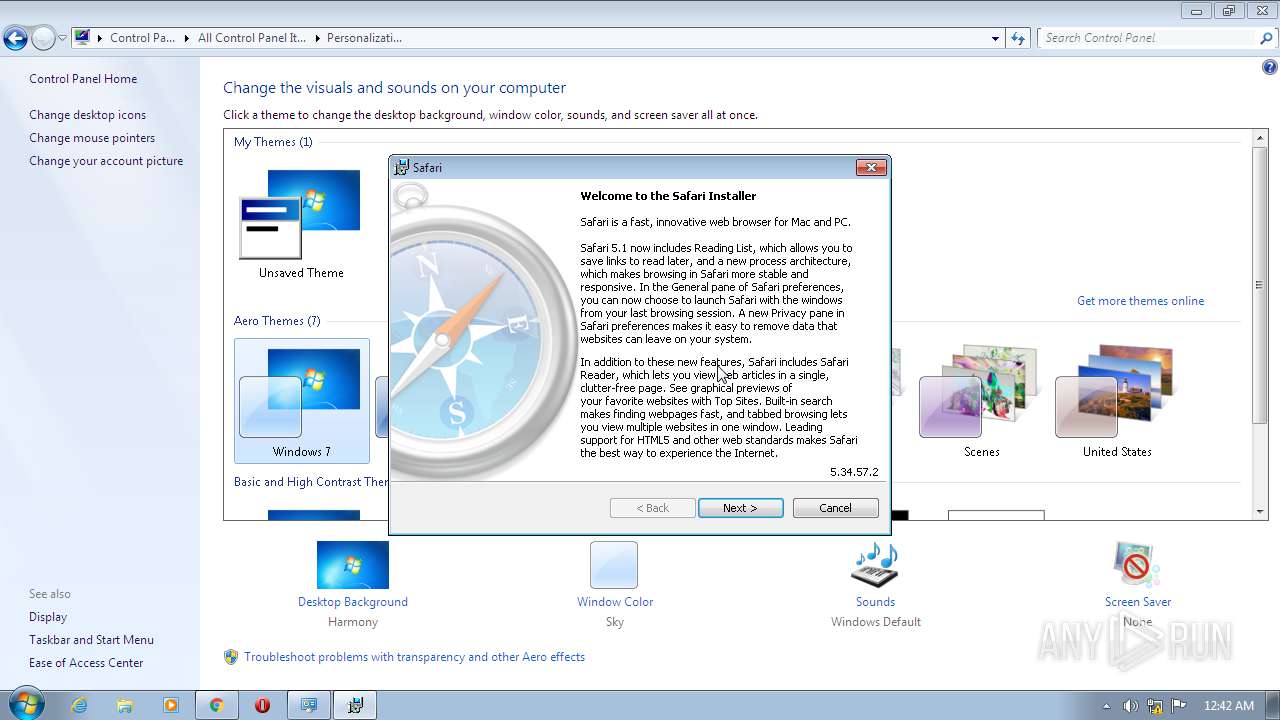
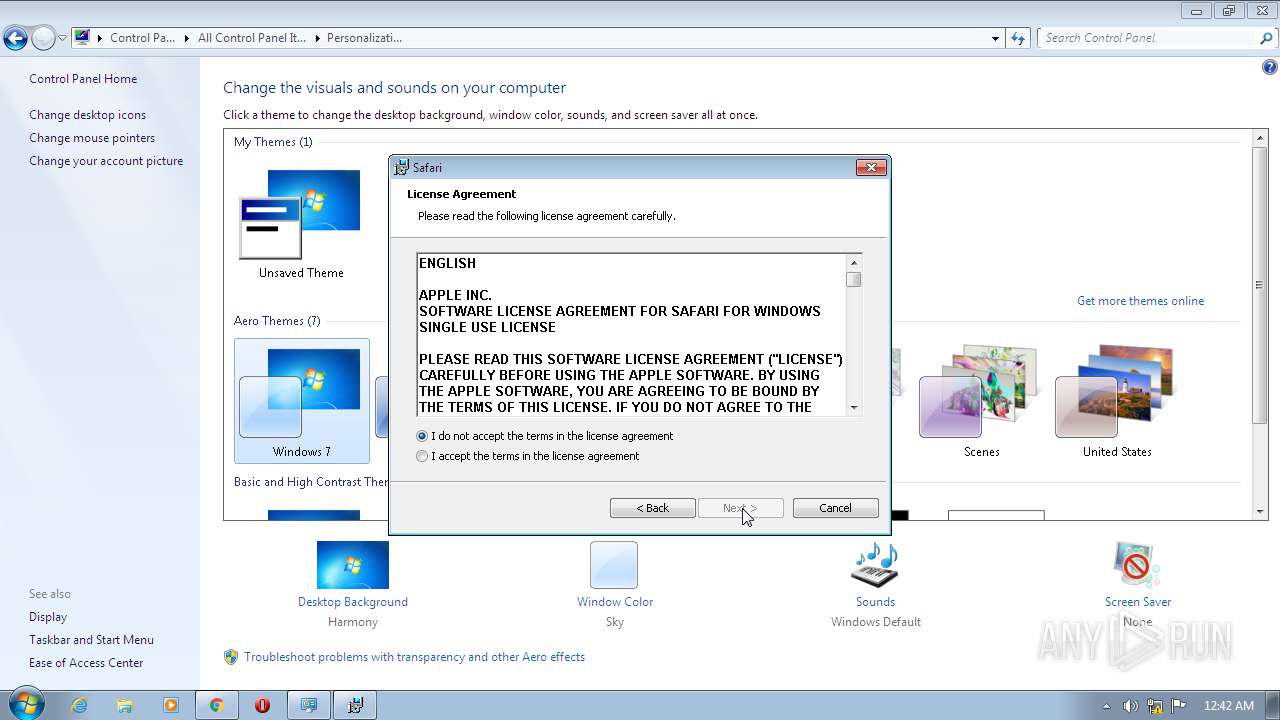
| 1800 | "C:\Users\admin\Downloads\SafariSetup.exe" | C:\Users\admin\Downloads\SafariSetup.exe | chrome.exe | ||||||||||||
User: admin Company: Apple Inc. Integrity Level: MEDIUM Description: Safari Installer Exit code: 0 Version: 5.34.57.2 Modules
| |||||||||||||||
Total events
13 378
Read events
12 060
Write events
1 285
Delete events
33
Modification events
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 4092-13245205278761125 |
Value: 259 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (4092) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
7
Suspicious files
93
Text files
191
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\179799b8-8ff6-44d9-8316-28655d4968e1.tmp | — | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 856 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFed5ba.TMP | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFed79f.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
83
TCP/UDP connections
106
DNS requests
69
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/27/49/061-4514/Tcfqf4NdtQTpYj7Pn8qwLgWgj6kYcy26Zf/061-4514.English.dist | US | xml | 2.21 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/12/45/061-4249/7ck27nGQBsHQNcnMMjtmLbDJm2zPbRxj4h/061-4249.English.dist | US | xml | 2.07 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/54/37/061-5790/mxbPrKRvB9G6cvrjY2QPNVQPYj3nrjwbgX/061-5790.English.dist | US | xml | 6.86 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/56/25/041-3097/SrjbZVKzSxP5VNSHnnDMQrb78YZz66DYww/041-3097.English.dist | US | xml | 6.69 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/28/43/061-7509/P7wtsjhJPsT9FM8Zff4FKg6FYM4W2yGP5B/061-7509.English.dist | US | xml | 2.48 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/59/27/041-0516/rRmQxLKryPBcF33yFvzhw7SYLDRntjXj9K/041-0516.English.dist | US | xml | 7.13 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/51/48/061-9539/XzrZsqWRT9FLLVN6tBfk4mjVmtqvNDHwC7/061-9539.English.dist | US | xml | 2.35 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/50/36/061-9848/kJvM5Qq2gBCSHSrxsdNfyn7NPjVYNHX7ZR/061-9848.English.dist | US | xml | 6.74 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/28/51/041-0517/cvDMxJL5q6TQ2t8899HH8mvzjdHkDFwr99/041-0517.English.dist | US | xml | 7.14 Kb | whitelisted |
3356 | SoftwareUpdate.exe | GET | 200 | 17.253.57.204:80 | http://swcdn.apple.com/content/downloads/26/11/061-8155/wdTHYKkFWMCC8dDLHkycj3BLMxvq2wjwYD/061-8155.English.dist | US | xml | 2.33 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1704 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.22.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 67.27.158.126:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | malicious |
1704 | chrome.exe | 199.232.194.133:443 | dl5.filehippo.com | — | US | suspicious |
1704 | chrome.exe | 142.250.74.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1704 | chrome.exe | 172.217.18.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
3356 | SoftwareUpdate.exe | 104.111.249.241:80 | swcatalog.apple.com | Akamai International B.V. | NL | unknown |
3356 | SoftwareUpdate.exe | 17.146.232.26:80 | swpost.apple.com | Apple Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
dl5.filehippo.com |
| suspicious |
accounts.google.com |
| shared |
www.download.windowsupdate.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
swcatalog.apple.com |
| unknown |
swcdn.apple.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
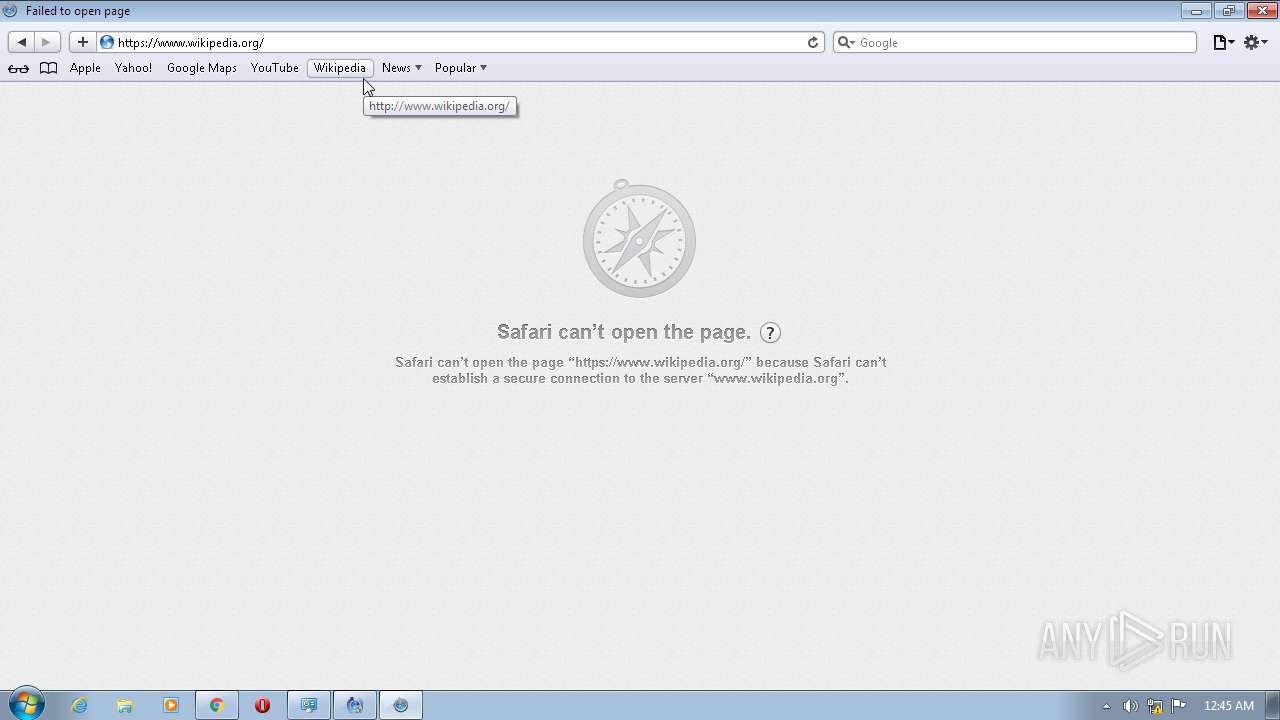
3484 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3484 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3484 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3484 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3484 | WebKit2WebProcess.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
WebKit2WebProcess.exe | Safari
|
WebKit2WebProcess.exe | ASL checking for logging parameters in environment variable "asl.log"
|
WebKit2WebProcess.exe | ASL checking for logging parameters in environment variable "WebKit2WebProcess.exe.log"
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] (Initialize|Accept)SecurityContext failed with error 0x80090302
|
WebKit2WebProcess.exe | ASL logging to file "C:\Users\admin\AppData\Roaming\Apple Computer\Logs\asl.004513_22Sep20.log"
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] CertGetCertificateChain failed with error 0x80090301
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] (Initialize|Accept)SecurityContext failed with error 0x80090326
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] CertGetCertificateChain failed with error 0x80090301
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] (Initialize|Accept)SecurityContext failed with error 0x80090302
|
WebKit2WebProcess.exe | [com.apple.WebKit2WebProcess WebKit2WebProcess.exe] CertGetCertificateChain failed with error 0x80090301
|