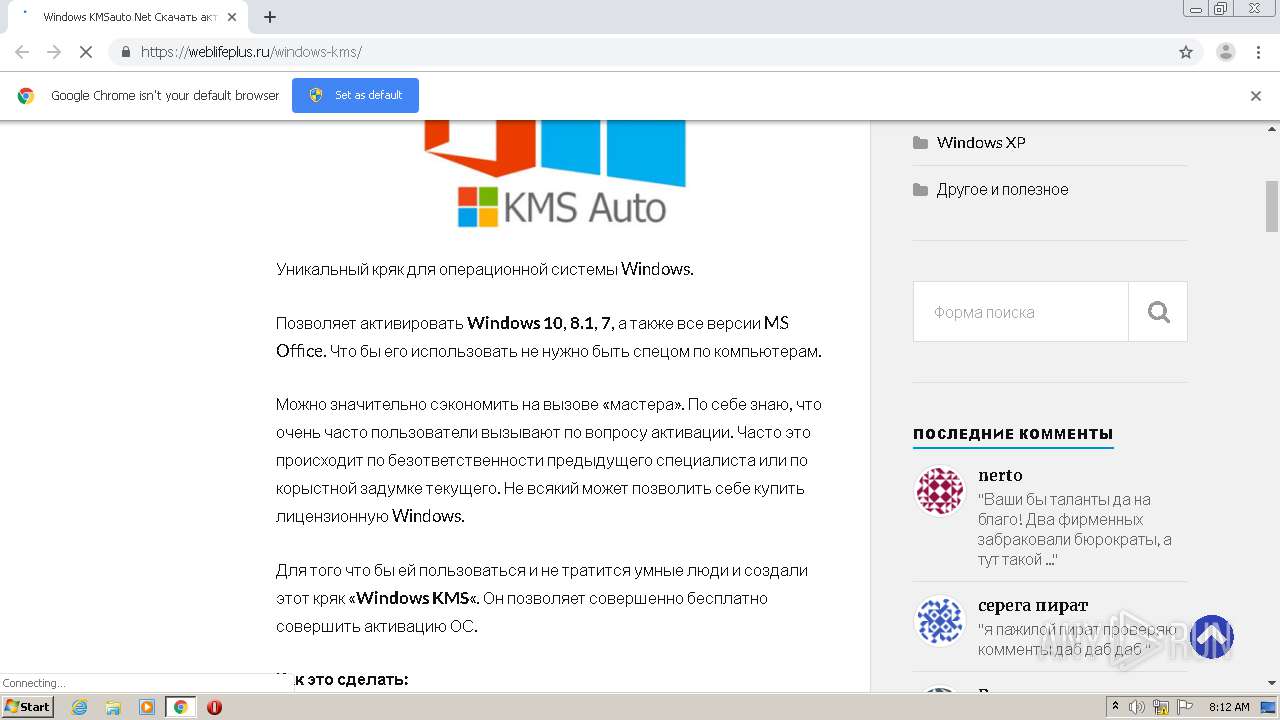
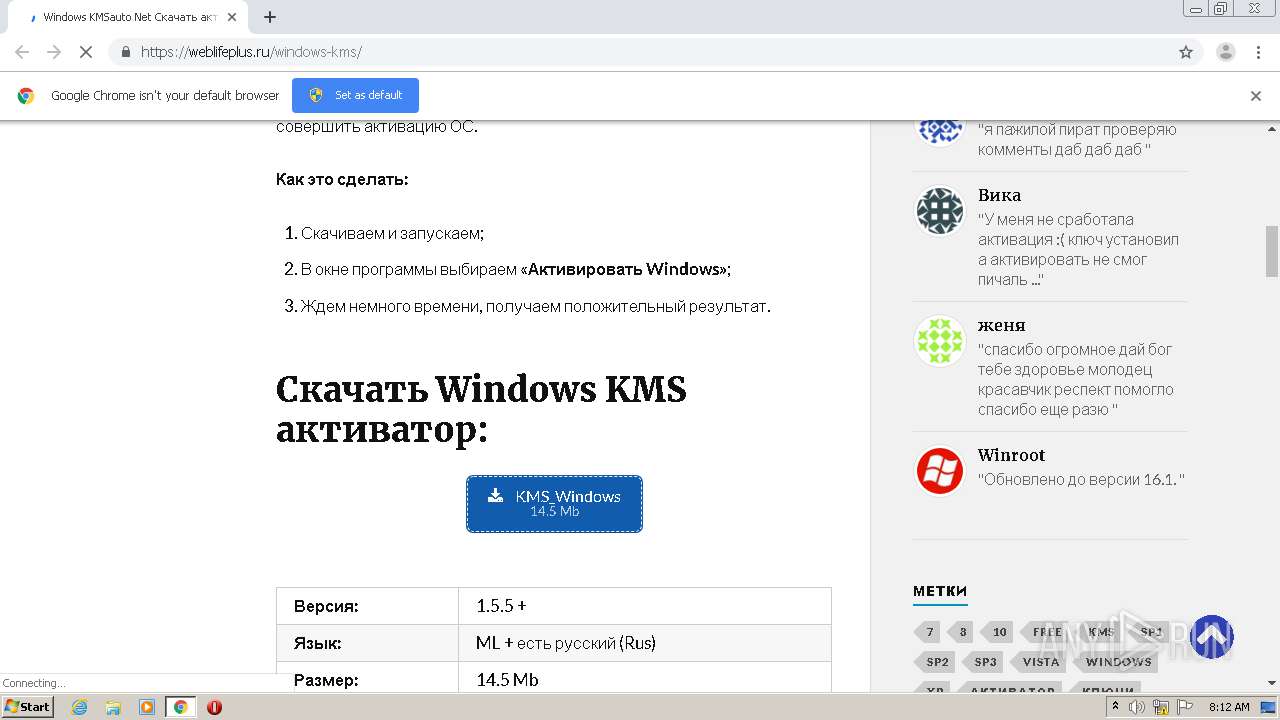
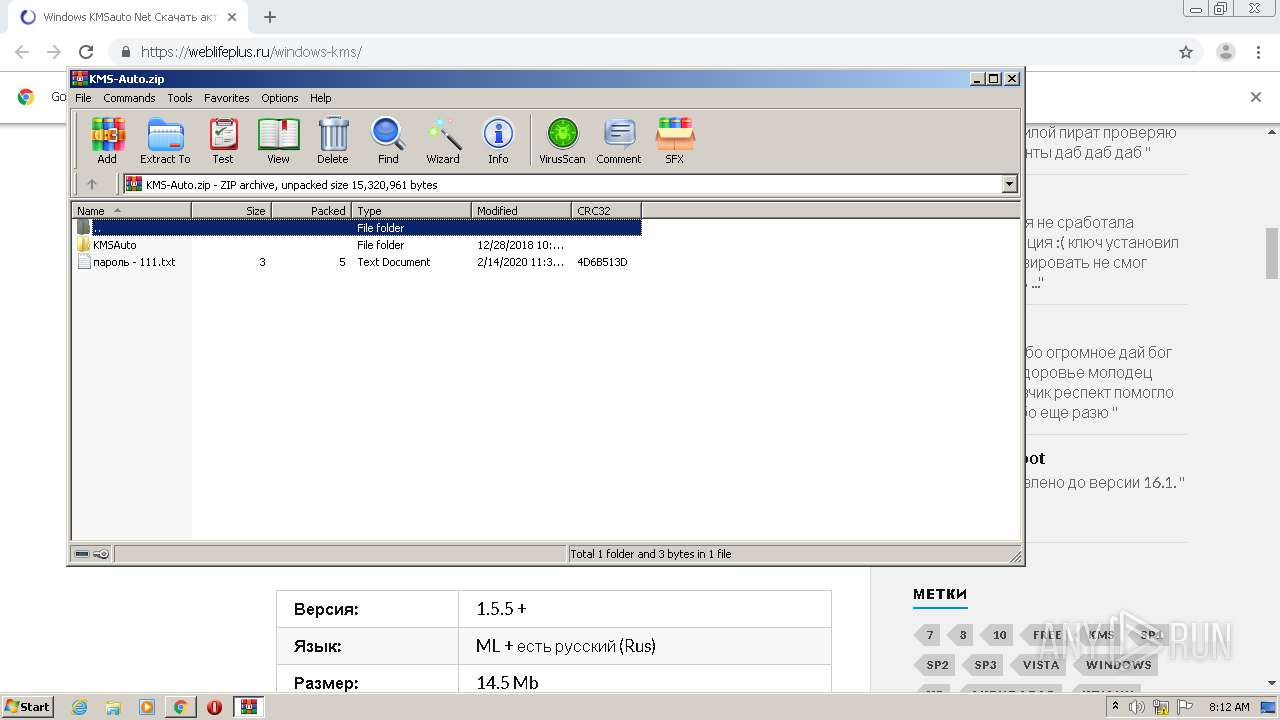
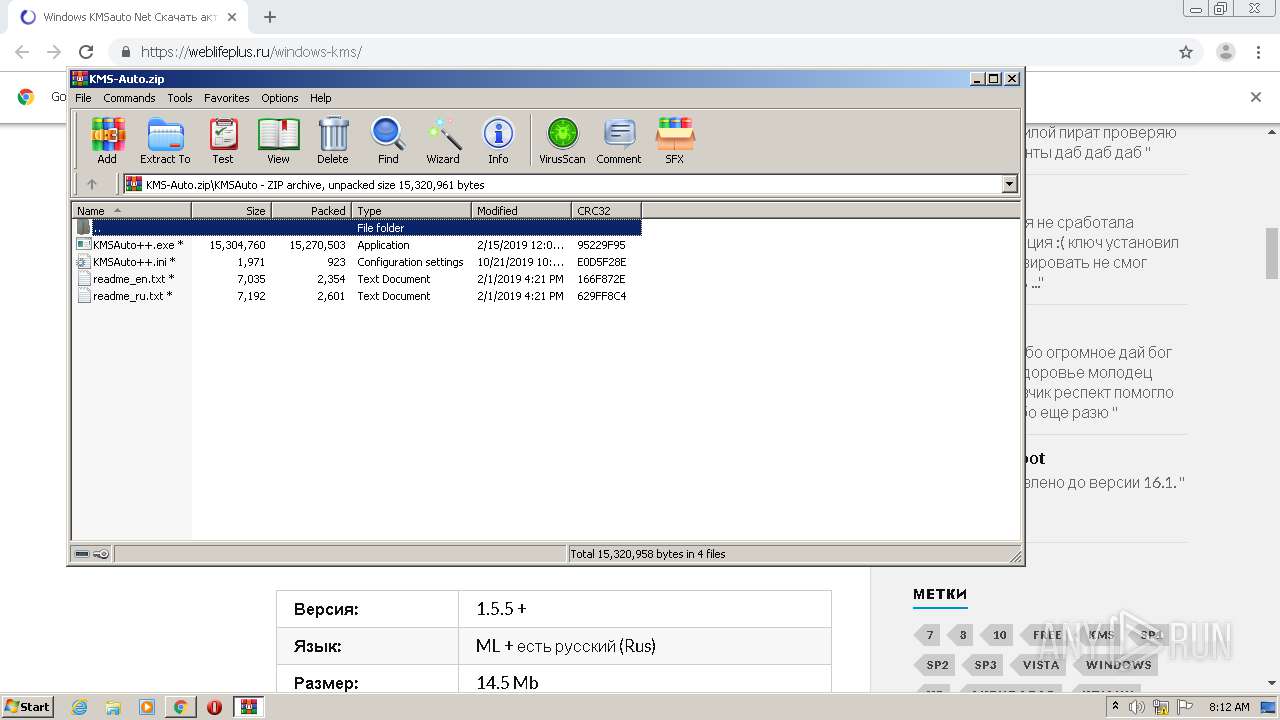
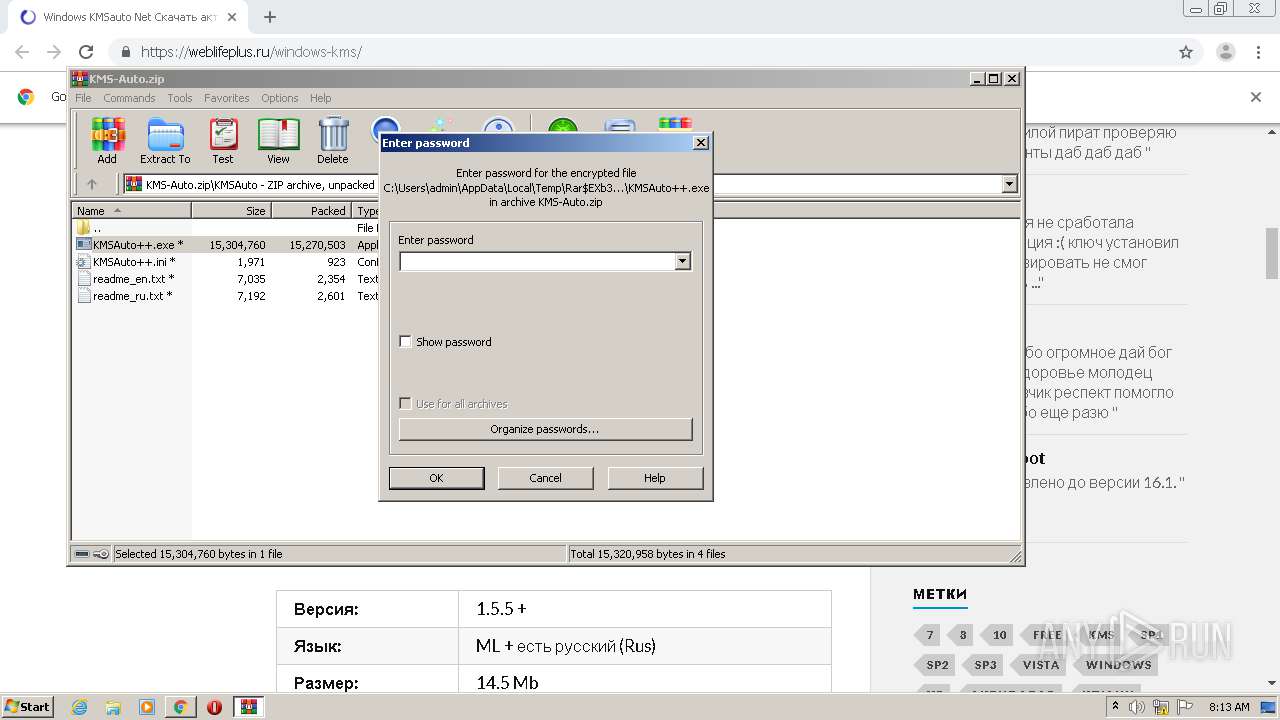
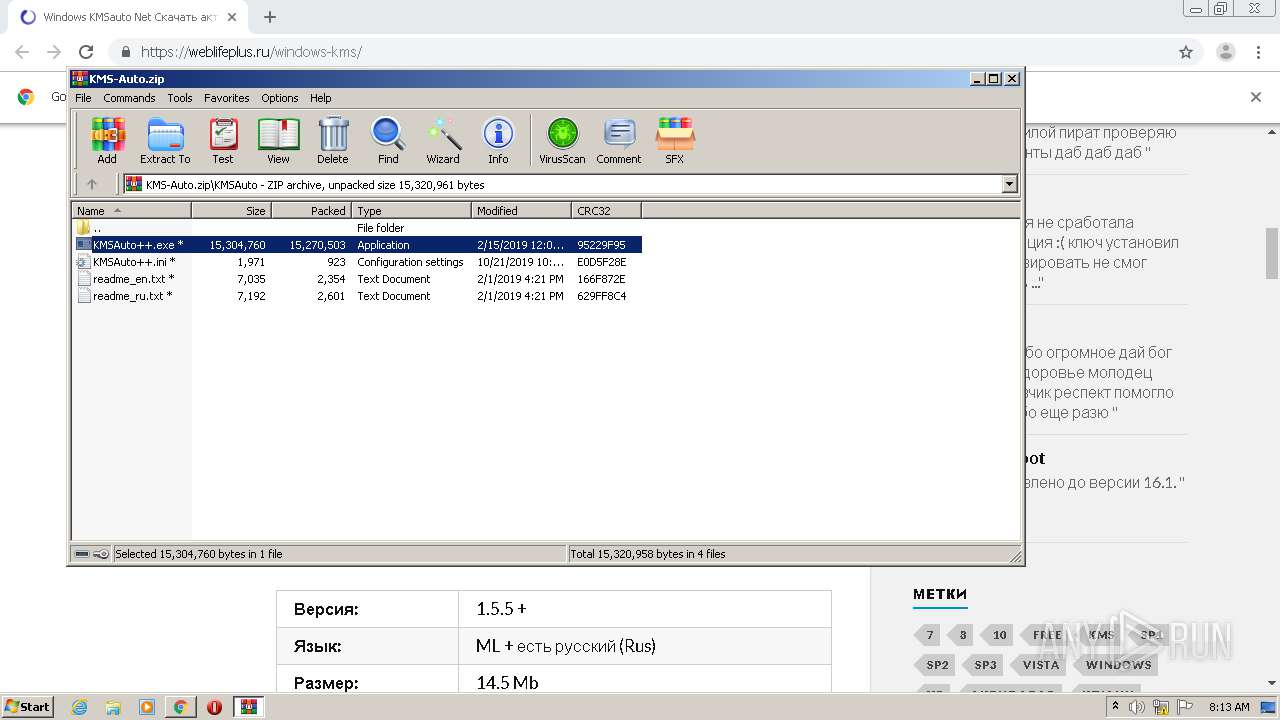
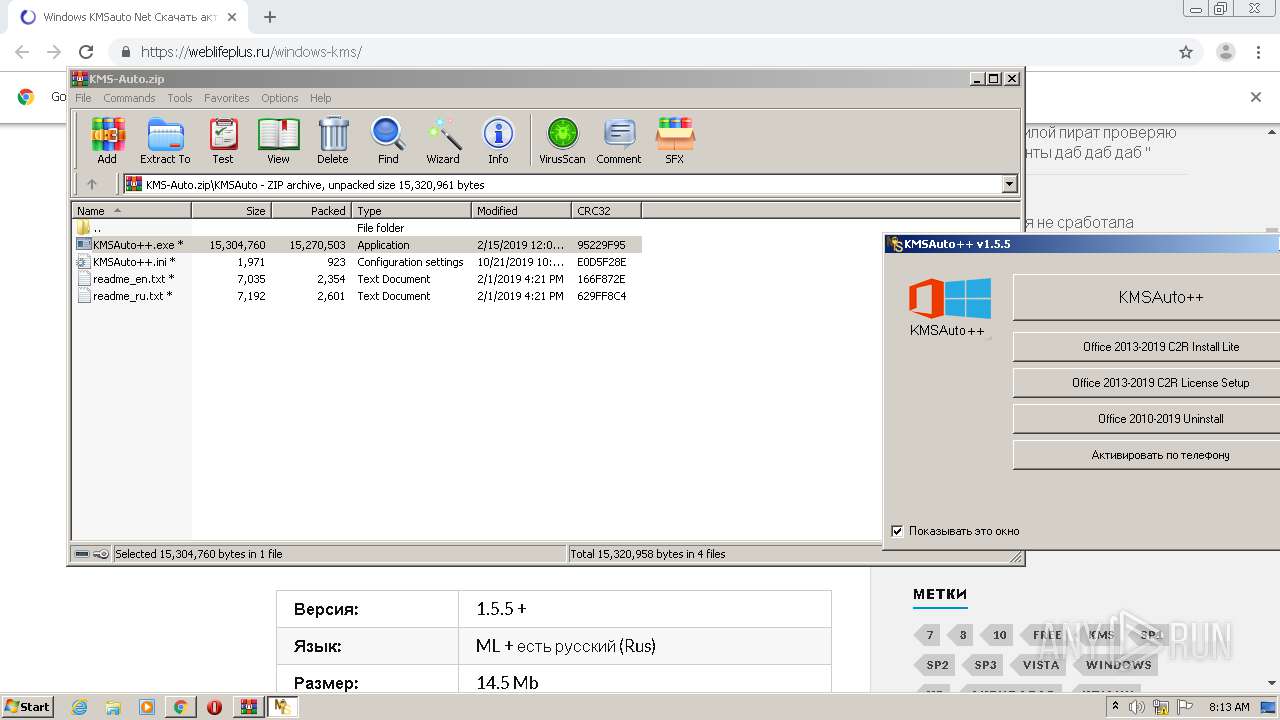
| URL: | https://weblifeplus.ru/windows-kms/ |
| Full analysis: | https://app.any.run/tasks/032c2cde-9021-42b1-ad9c-7c27d58c177c |
| Verdict: | Malicious activity |
| Analysis date: | October 20, 2020, 07:11:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0BA7B07953EE67FC0655FBB858F85F3A |
| SHA1: | 3A88A1A17DB48D919AFC324CC37D8B155851EAC8 |
| SHA256: | 5F3CCA46E76F036A4586FCCA6464BF5F91E1344D703508794BBBCC3A841A404F |
| SSDEEP: | 3:N8RpJJrDB/:2HN |
MALICIOUS
Changes settings of System certificates
- signtool.exe (PID: 3028)
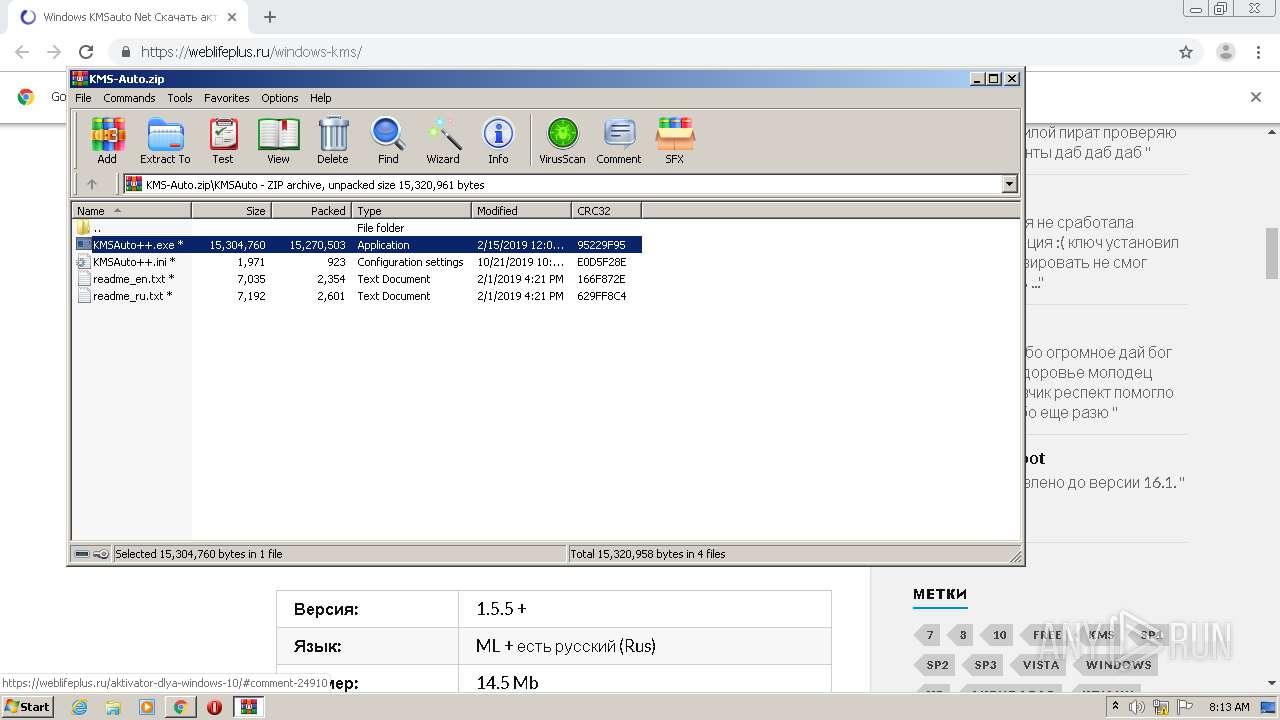
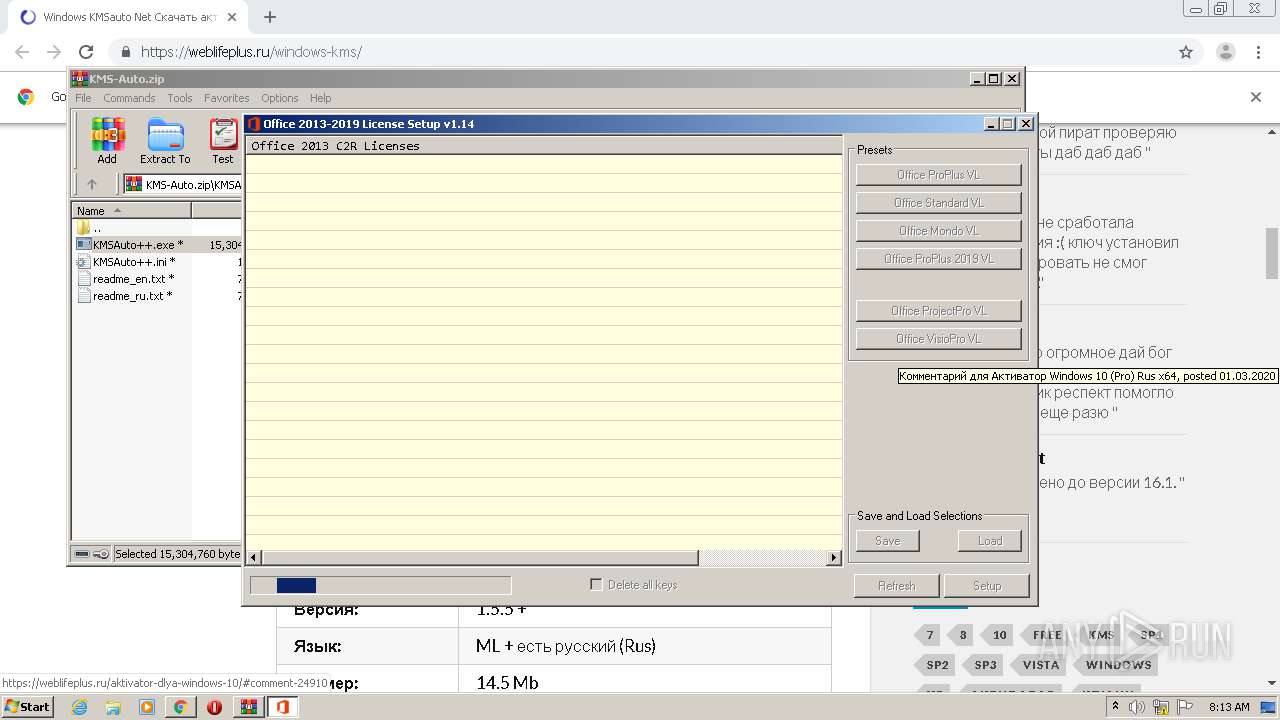
Application was dropped or rewritten from another process
- signtool.exe (PID: 3028)
- KMSAuto++.exe (PID: 492)
- KMSAuto++.exe (PID: 3504)
- OInstallLite.exe (PID: 2708)
- files.dat (PID: 3268)
- files.dat (PID: 3232)
- O15-19LicSetup.exe (PID: 3728)
- files.dat (PID: 3532)
SUSPICIOUS
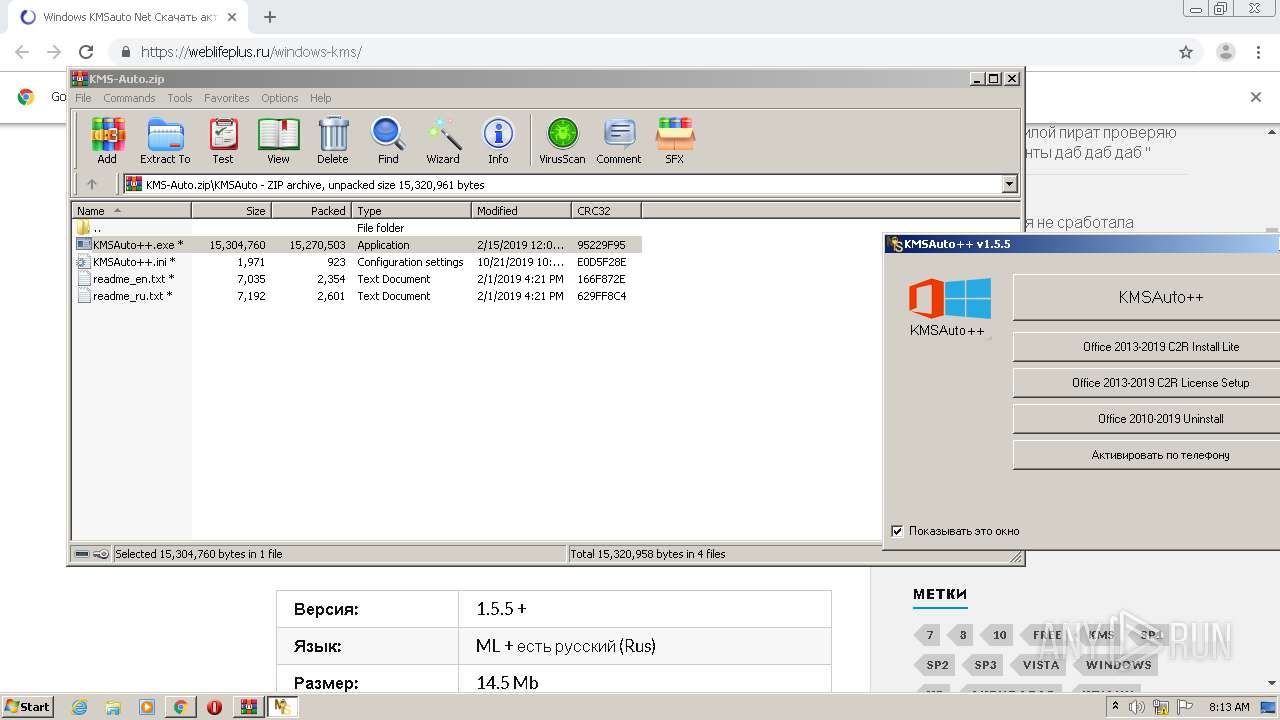
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3812)
- KMSAuto++.exe (PID: 3504)
- files.dat (PID: 3268)
- OInstallLite.exe (PID: 2708)
- O15-19LicSetup.exe (PID: 3728)
- files.dat (PID: 3532)
- files.dat (PID: 3232)
Adds / modifies Windows certificates
- signtool.exe (PID: 3028)
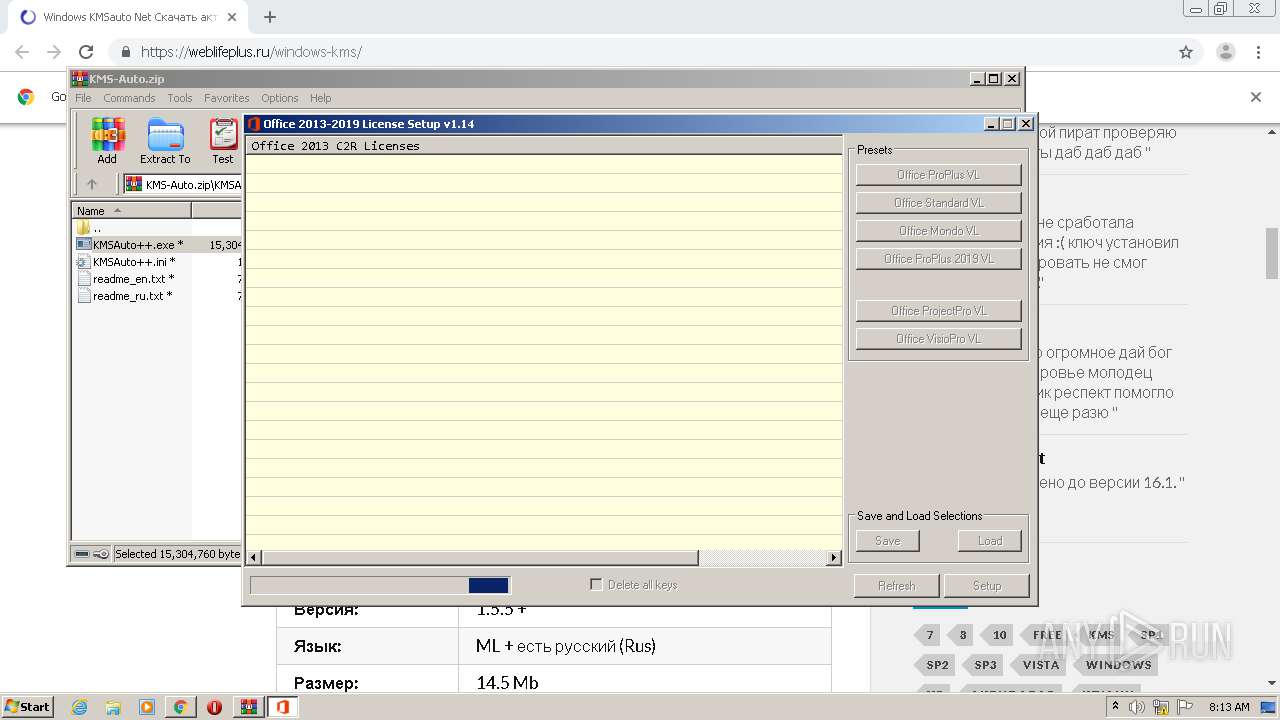
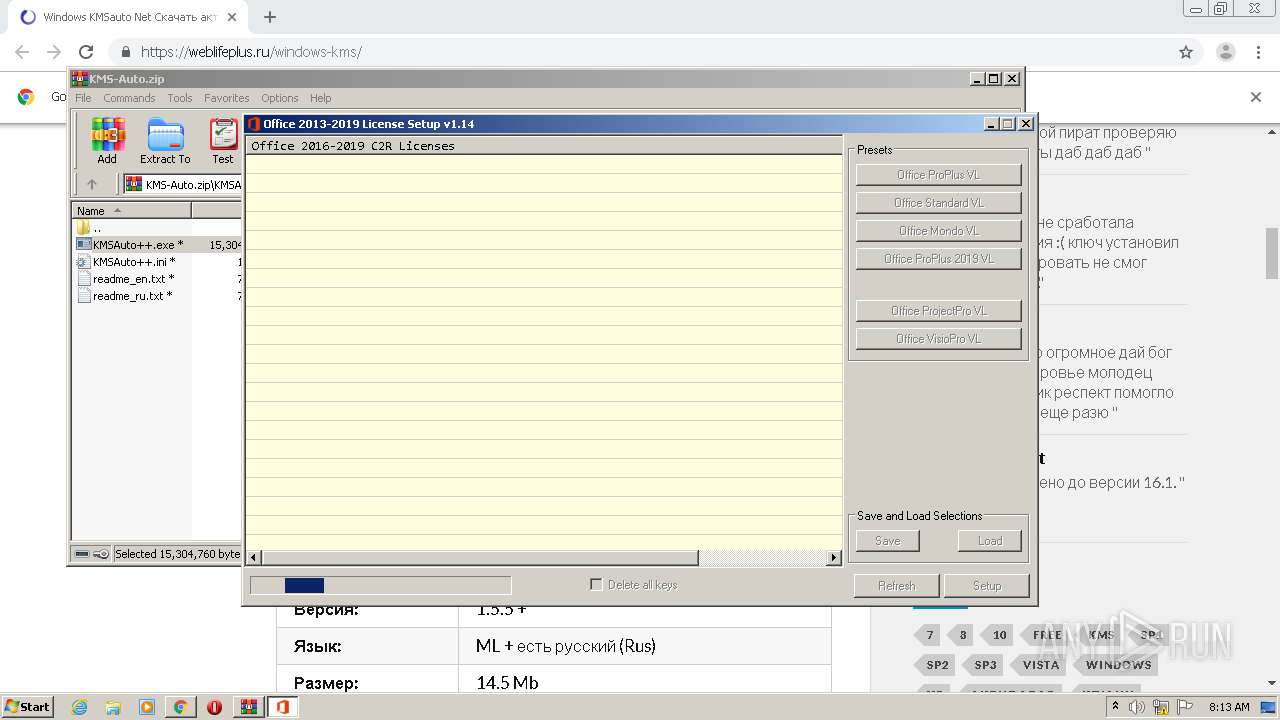
Starts CMD.EXE for commands execution
- OInstallLite.exe (PID: 2708)
- KMSAuto++.exe (PID: 3504)
- O15-19LicSetup.exe (PID: 3728)
Starts application with an unusual extension
- cmd.exe (PID: 3892)
- cmd.exe (PID: 3880)
- cmd.exe (PID: 2224)
Executes scripts
- cmd.exe (PID: 2456)
- cmd.exe (PID: 3836)
INFO
Application launched itself
- chrome.exe (PID: 3864)
Reads the hosts file
- chrome.exe (PID: 3864)
- chrome.exe (PID: 3588)
Reads Internet Cache Settings
- chrome.exe (PID: 3864)
Dropped object may contain Bitcoin addresses
- files.dat (PID: 3532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
34
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Windows\System32\cmd.exe" /c del "C:\Users\admin\AppData\Local\Temp\Rar$EXb3812.30950\KMSAuto\OInstallLite.exe" /F /Q | C:\Windows\System32\cmd.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 492 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3812.30950\KMSAuto\KMSAuto++.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb3812.30950\KMSAuto\KMSAuto++.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8376115503777012194,16878085622060341298,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17728402195562856576 --mojo-platform-channel-handle=1116 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2224 | "C:\Windows\System32\cmd.exe" /c files.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | O15-19LicSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2300 | "C:\Windows\System32\cmd.exe" /c copy C:\Windows\system32\Tasks\KMSAuto "C:\Users\admin\AppData\Local\Temp\KMSAuto.tmp" /Y | C:\Windows\System32\cmd.exe | — | KMSAuto++.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2456 | "C:\Windows\System32\cmd.exe" /c cscript.exe ospp.vbs /dstatusall | C:\Windows\System32\cmd.exe | — | O15-19LicSetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,8376115503777012194,16878085622060341298,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6530095006374097014 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=308 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
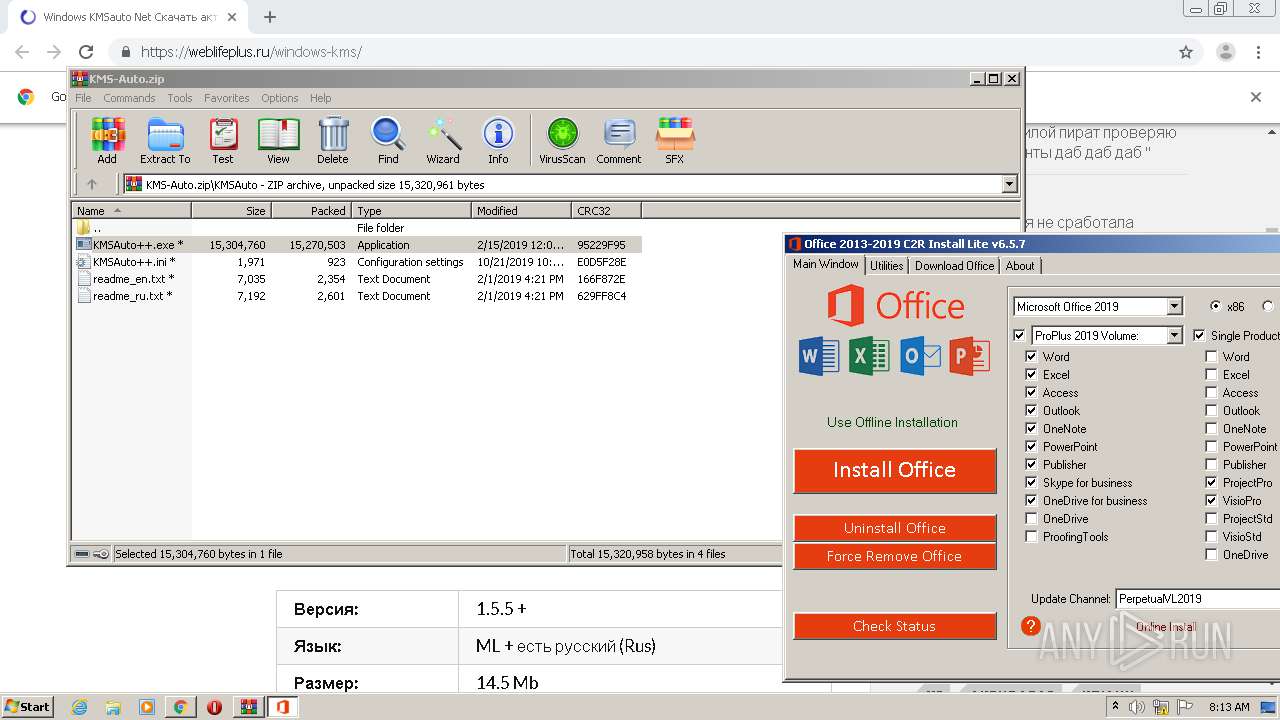
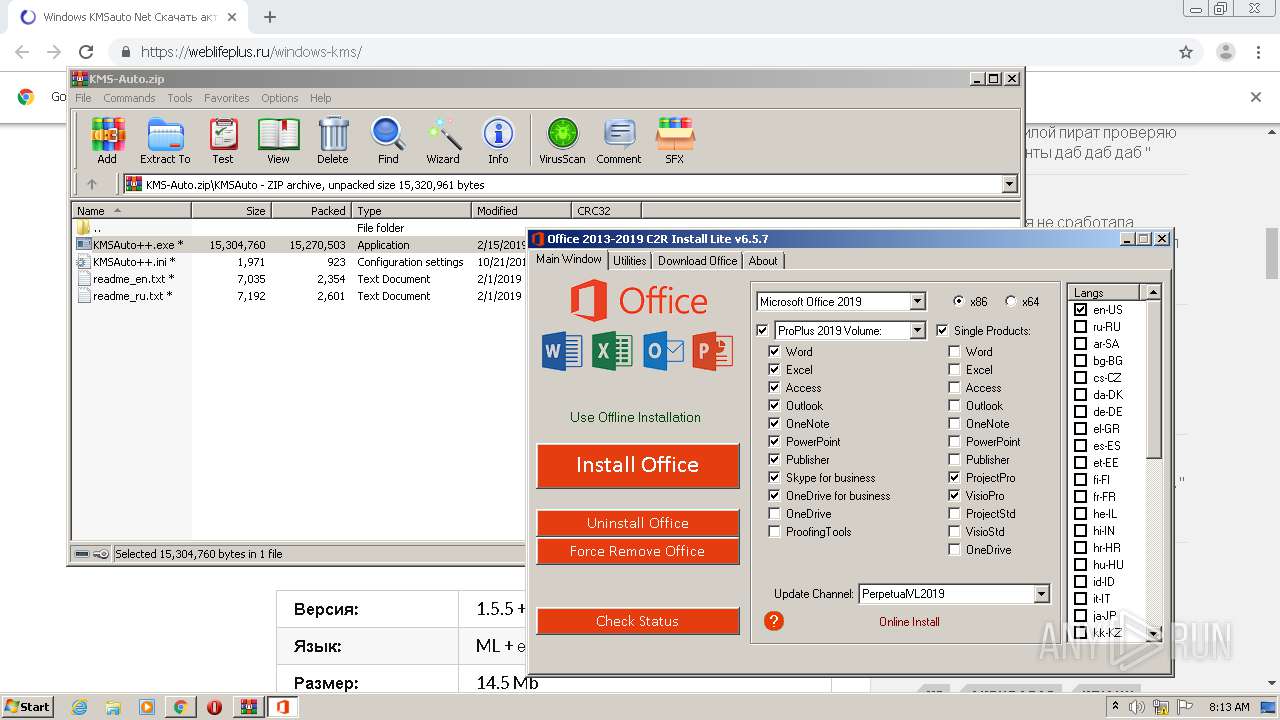
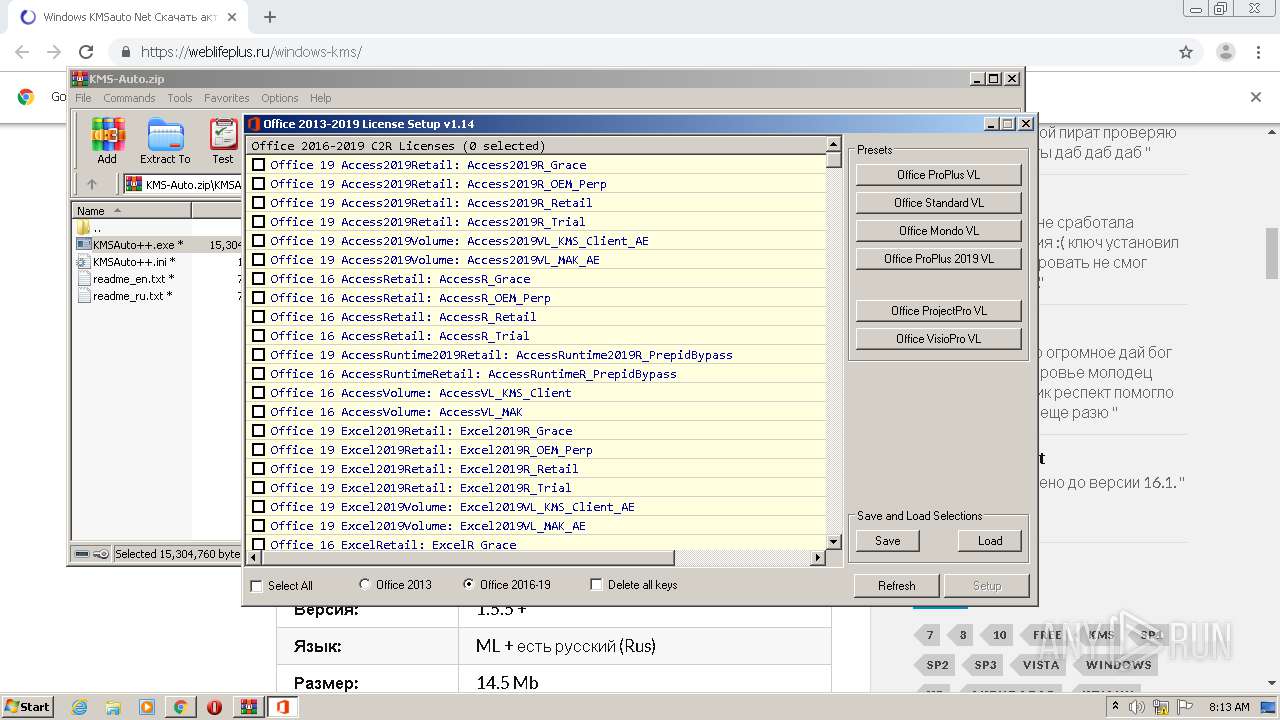
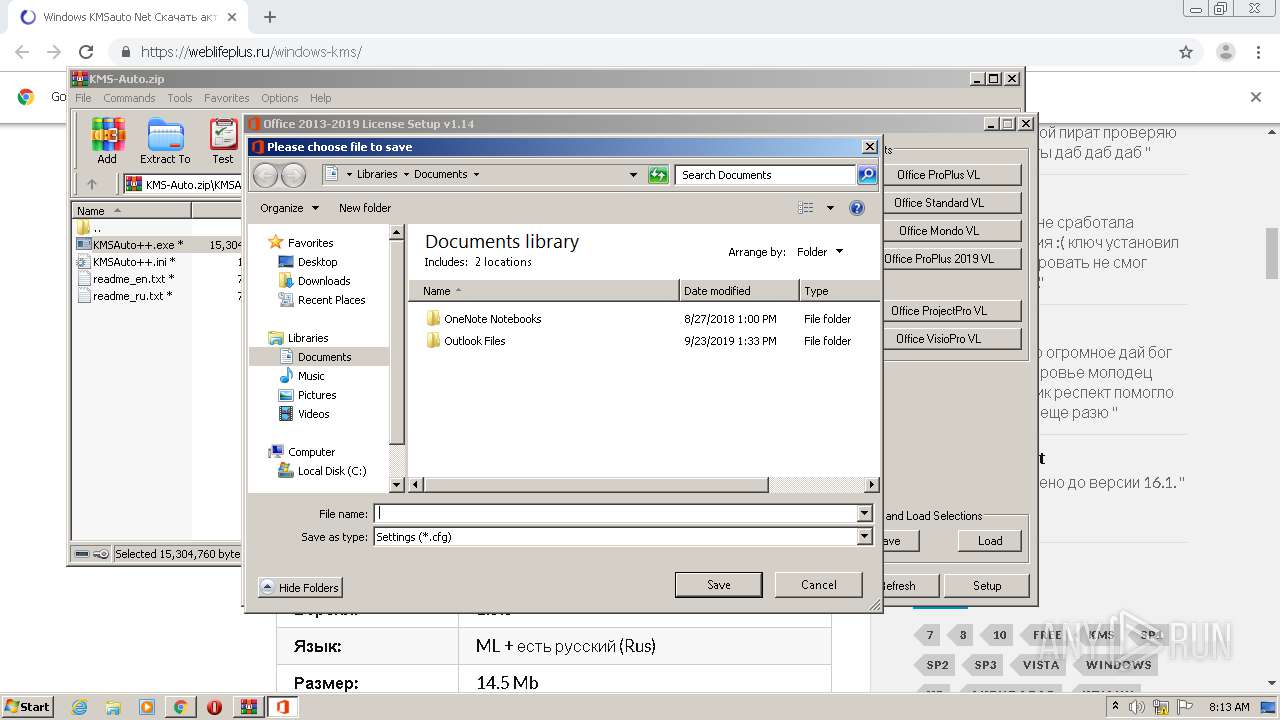
| 2708 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3812.30950\KMSAuto\OInstallLite.exe" /x=782 /y=232 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3812.30950\KMSAuto\OInstallLite.exe | KMSAuto++.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Office 2013-2016 C2R Install Lite Exit code: 0 Modules
| |||||||||||||||
| 2768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,8376115503777012194,16878085622060341298,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4675100441648771658 --mojo-platform-channel-handle=3064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 053
Read events
1 916
Write events
133
Delete events
4
Modification events
| (PID) Process: | (2548) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3864-13247651525271750 |
Value: 259 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3864) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3864-13247651525271750 |
Value: 259 | |||
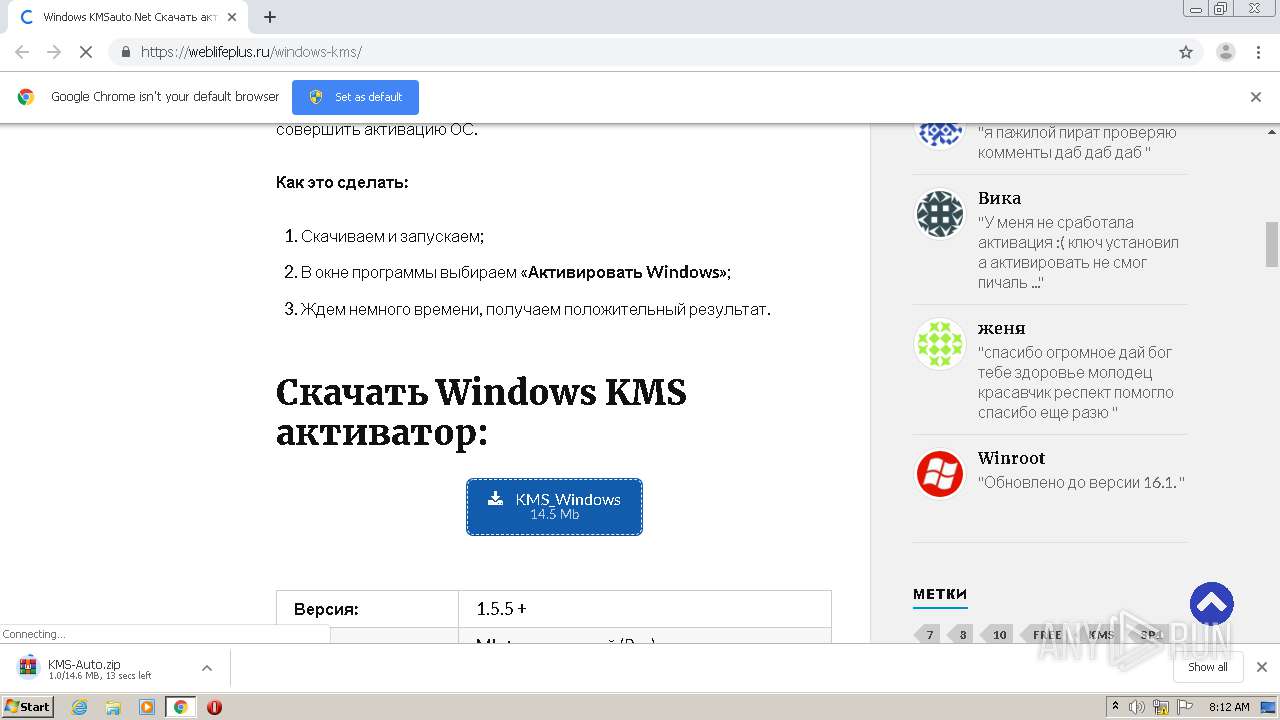
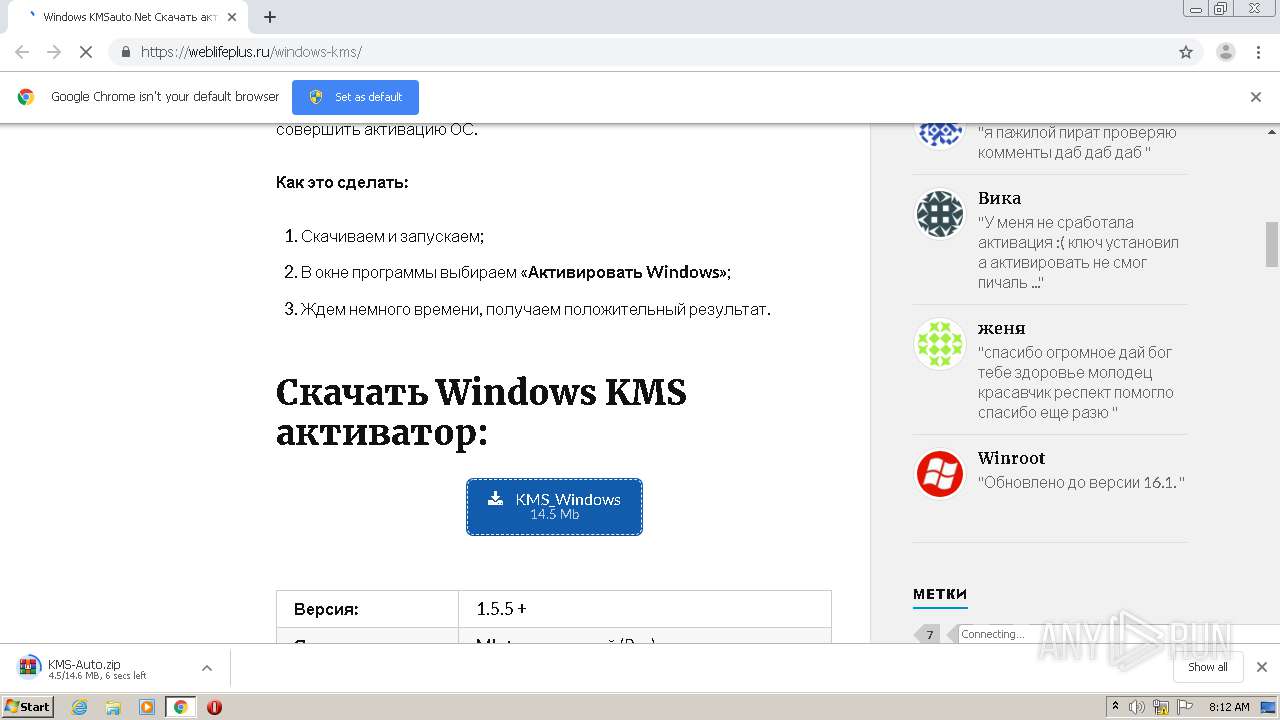
Executable files
20
Suspicious files
40
Text files
1 959
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F8E8DC5-F18.pma | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ba9b0f09-1c53-4d08-af61-65cf42663030.tmp | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old~RF2d41b1.TMP | text | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF2d4163.TMP | text | |
MD5:— | SHA256:— | |||
| 3864 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2d4124.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
40
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3028 | signtool.exe | GET | 200 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
3028 | signtool.exe | GET | 304 | 2.16.186.81:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3588 | chrome.exe | 92.53.114.245:443 | weblifeplus.ru | TimeWeb Ltd. | RU | malicious |
3588 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3588 | chrome.exe | 78.46.111.246:443 | jquerylibp.ru | Hetzner Online GmbH | DE | unknown |
3588 | chrome.exe | 216.58.212.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 216.58.207.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 216.58.207.42:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 172.217.22.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3588 | chrome.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
3588 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
weblifeplus.ru |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
jquerylibp.ru |
| unknown |
counter.yadro.ru |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
clients1.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |