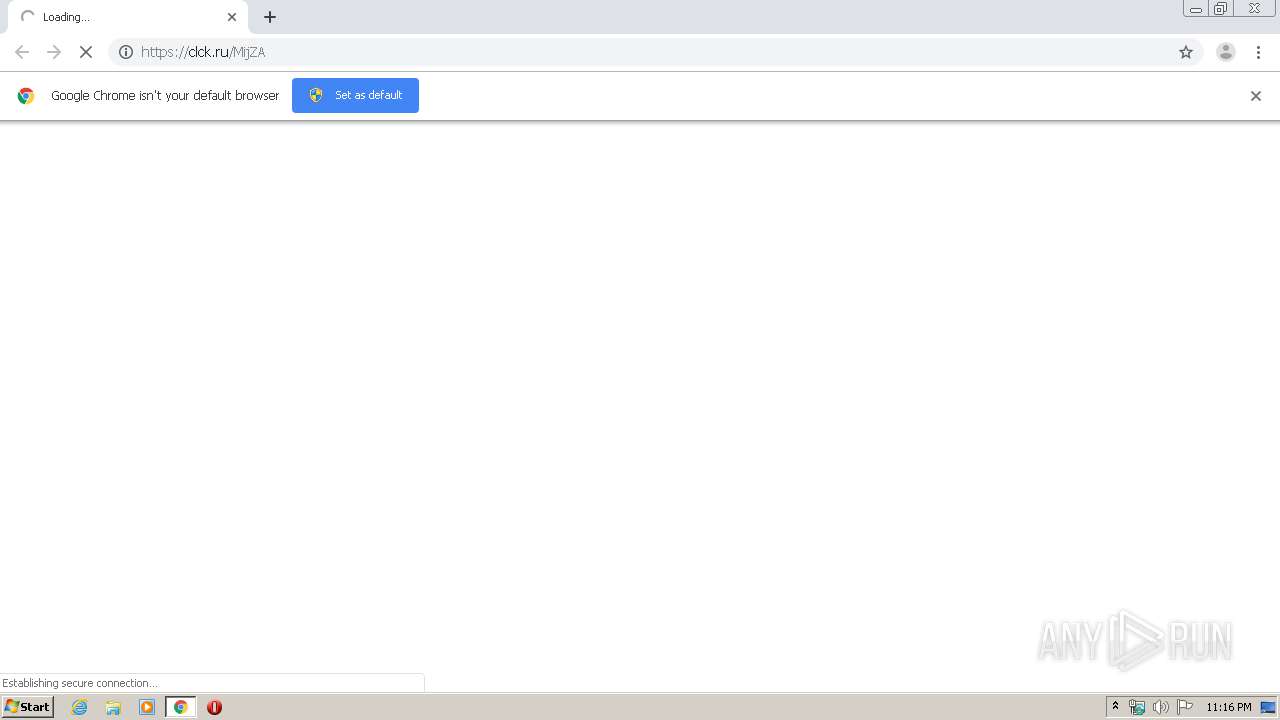
| URL: | https://clck.ru/MijZA |
| Full analysis: | https://app.any.run/tasks/be745e13-1a29-4f9b-8985-f99903343599 |
| Verdict: | Malicious activity |
| Analysis date: | March 30, 2020, 22:16:10 |
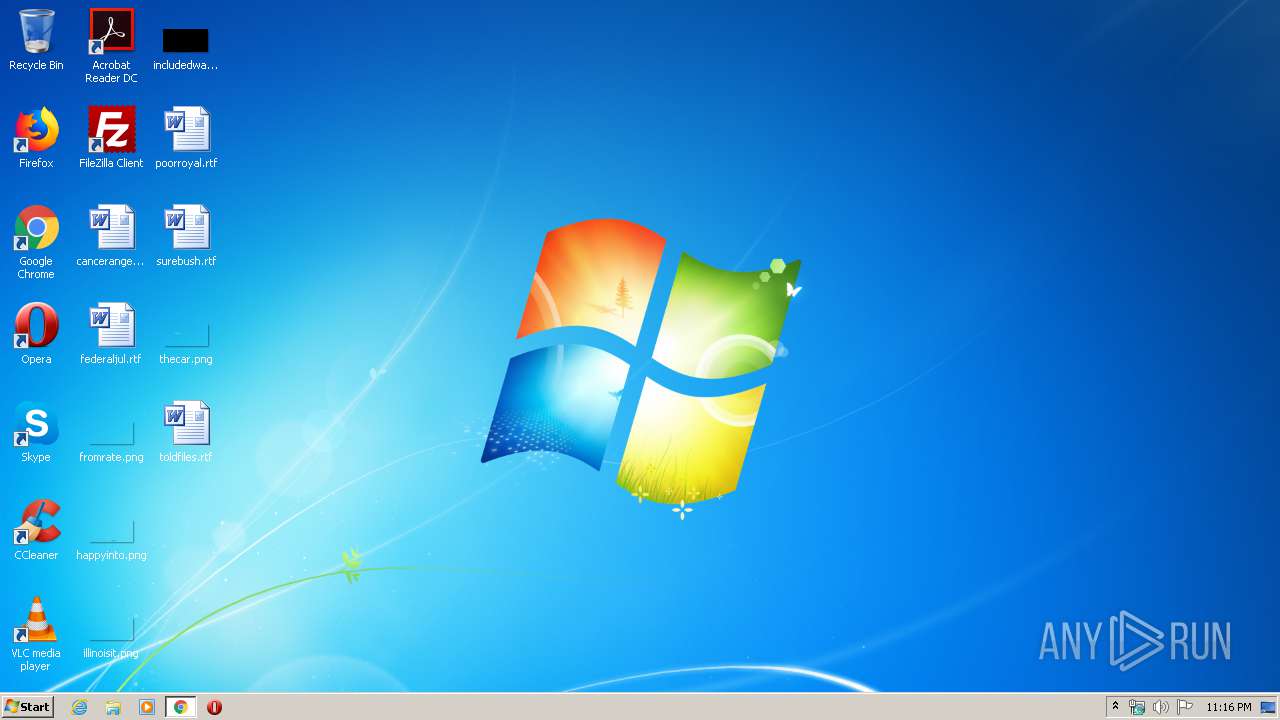
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CD33CBD123355D91F01EF589339BFD33 |
| SHA1: | 4FE211F9171DE51955B4934F558DC5953E42599F |
| SHA256: | 5F3AEED6543C1C7094E26F47578C97975DD644D3DA2F3B2D0A1A3B617DFBF2B2 |
| SSDEEP: | 3:N8UZLXQKC:2U5C |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2896)
INFO
Reads the hosts file
- chrome.exe (PID: 2896)
- chrome.exe (PID: 2716)
Application launched itself
- chrome.exe (PID: 2896)
Reads settings of System Certificates
- chrome.exe (PID: 2716)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6535957079873128851 --mojo-platform-channel-handle=3588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4066818636150843020 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2492 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1469623260513502355 --mojo-platform-channel-handle=4256 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1068085250160162473 --mojo-platform-channel-handle=3144 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13362828437553521398 --mojo-platform-channel-handle=3852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8369693834412742630 --mojo-platform-channel-handle=1068 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12390355734138366430 --mojo-platform-channel-handle=4040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12162372407468099844 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=17486344718262192759 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12158861347982136967,52764981601243266,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3416791049572561094 --mojo-platform-channel-handle=4360 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
848
Read events
768
Write events
75
Delete events
5
Modification events
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3336) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2896-13230080185782625 |
Value: 259 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2896) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
16
Text files
154
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E826FBA-B50.pma | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\81b36b4c-9976-4706-b11e-43944a53bbd5.tmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c5e.TMP | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c6e.TMP | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e04.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
21
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | chrome.exe | GET | 301 | 219.94.128.185:80 | http://arc-structure.sakura.ne.jp/ys4/rank.cgi?mode=link&id=358&url=http://tiny.cc/38j3lz | JP | — | — | unknown |
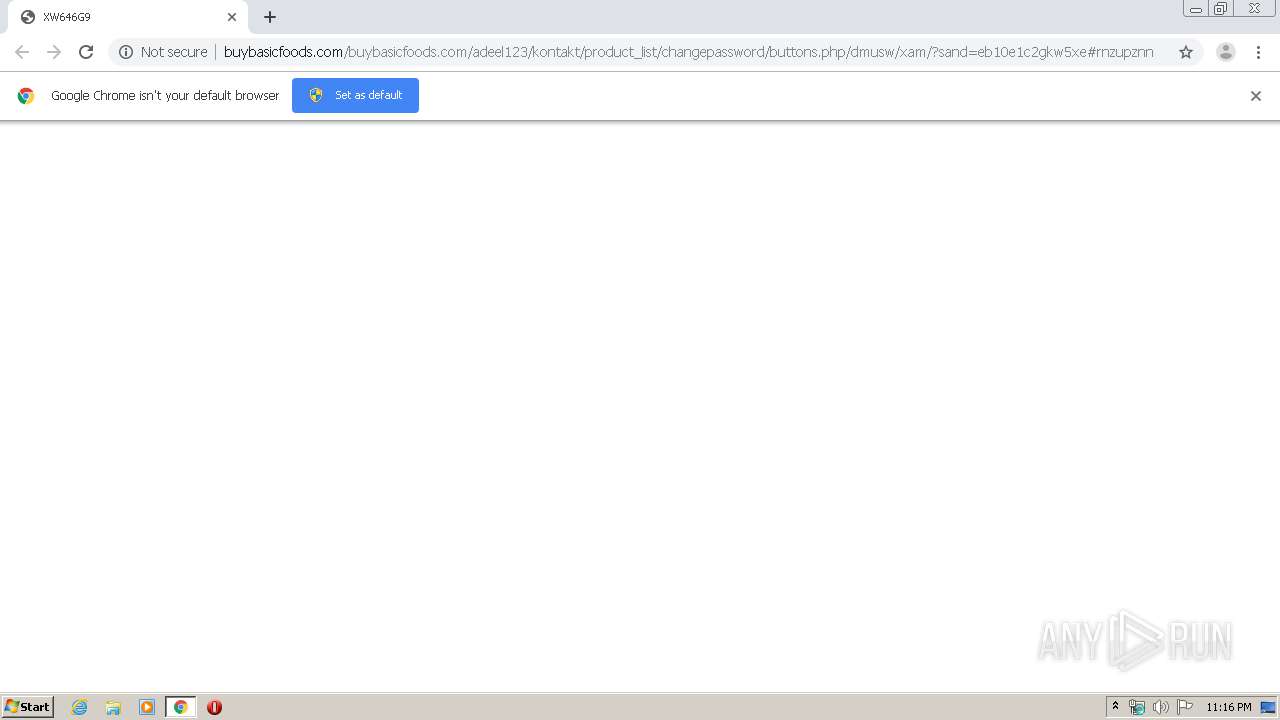
2716 | chrome.exe | GET | 200 | 107.180.58.50:80 | http://buybasicfoods.com/buybasicfoods.com/adeel123/kontakt/product_list/changepassword/buttons.php/dmusw/xam/?sand=eb10e1c2gkw5xe | US | html | 1.07 Kb | malicious |
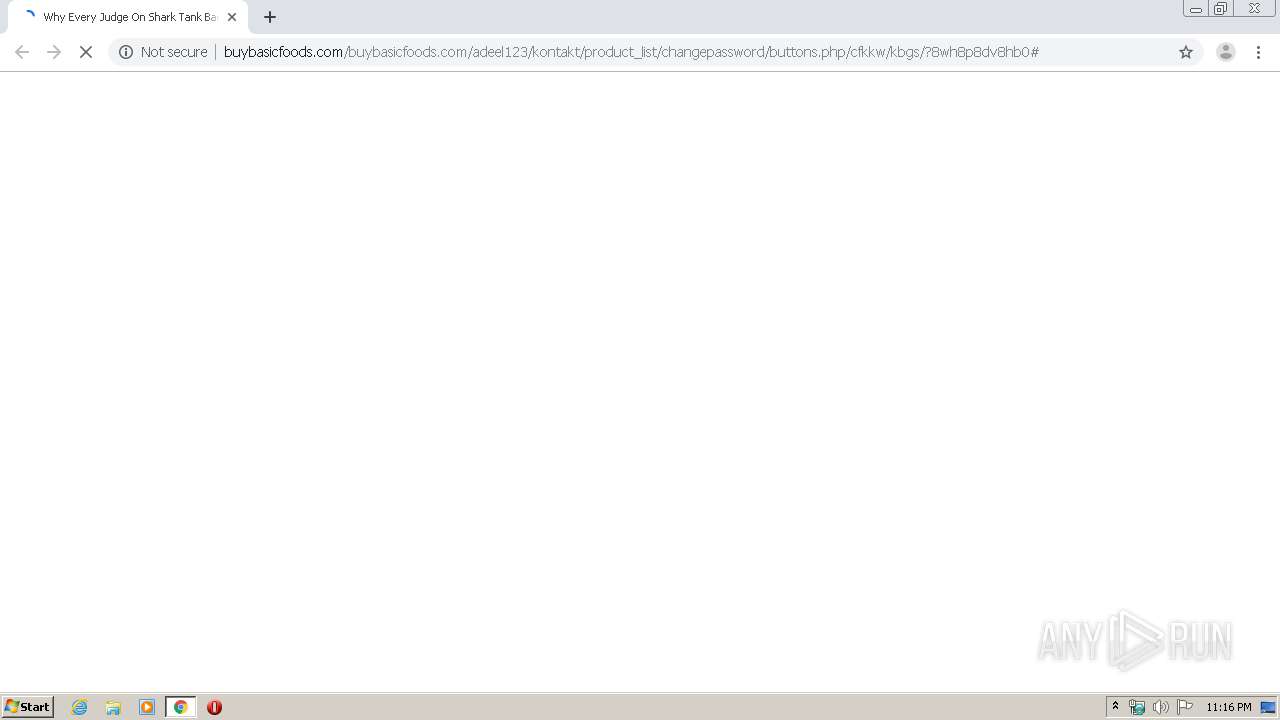
2716 | chrome.exe | GET | 200 | 107.180.58.50:80 | http://buybasicfoods.com/buybasicfoods.com/adeel123/kontakt/product_list/changepassword/buttons.php/cfkkw/kbgs/?8wh8p8dv8hb0 | US | html | 942 Kb | malicious |
2716 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 525 b | whitelisted |
2716 | chrome.exe | GET | 301 | 192.241.240.89:80 | http://tiny.cc/38j3lz | US | html | 184 b | malicious |
2716 | chrome.exe | GET | 503 | 107.180.58.50:80 | http://buybasicfoods.com/favicon.ico | US | html | 428 b | malicious |
2716 | chrome.exe | GET | 200 | 74.125.153.27:80 | http://r5---sn-hpa7zned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=QJ&mip=185.128.27.151&mm=28&mn=sn-hpa7zned&ms=nvh&mt=1585606512&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
2716 | chrome.exe | GET | 200 | 74.125.153.27:80 | http://r5---sn-hpa7zned.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mh=bs&mip=185.128.27.151&mm=28&mn=sn-hpa7zned&ms=nvh&mt=1585606512&mv=m&mvi=4&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
2716 | chrome.exe | GET | 500 | 107.180.58.50:80 | http://buybasicfoods.com/favicon.ico | US | text | 22 b | malicious |
2716 | chrome.exe | GET | 200 | 104.17.64.4:80 | http://cdnjs.cloudflare.com/ajax/libs/jquery/1.12.4/jquery.min.js | US | text | 33.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2716 | chrome.exe | 172.217.18.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 213.180.204.221:443 | clck.ru | YANDEX LLC | RU | whitelisted |
2716 | chrome.exe | 77.88.21.232:443 | sba.yandex.net | YANDEX LLC | RU | whitelisted |
2716 | chrome.exe | 219.94.128.185:80 | arc-structure.sakura.ne.jp | SAKURA Internet Inc. | JP | unknown |
2716 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
2716 | chrome.exe | 192.241.240.89:80 | tiny.cc | Digital Ocean, Inc. | US | malicious |
2716 | chrome.exe | 192.241.240.89:443 | tiny.cc | Digital Ocean, Inc. | US | malicious |
2716 | chrome.exe | 107.180.58.50:80 | buybasicfoods.com | GoDaddy.com, LLC | US | malicious |
2716 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
2716 | chrome.exe | 216.58.207.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clck.ru |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sba.yandex.net |
| whitelisted |
arc-structure.sakura.ne.jp |
| unknown |
tiny.cc |
| malicious |
buybasicfoods.com |
| malicious |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1052 | svchost.exe | A Network Trojan was detected | ET POLICY URL Shortener Service Domain in DNS Lookup (tiny .cc) |
1052 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2716 | chrome.exe | A Network Trojan was detected | ET POLICY Observed SSL Cert (URL Shortener Service - tiny .cc) |