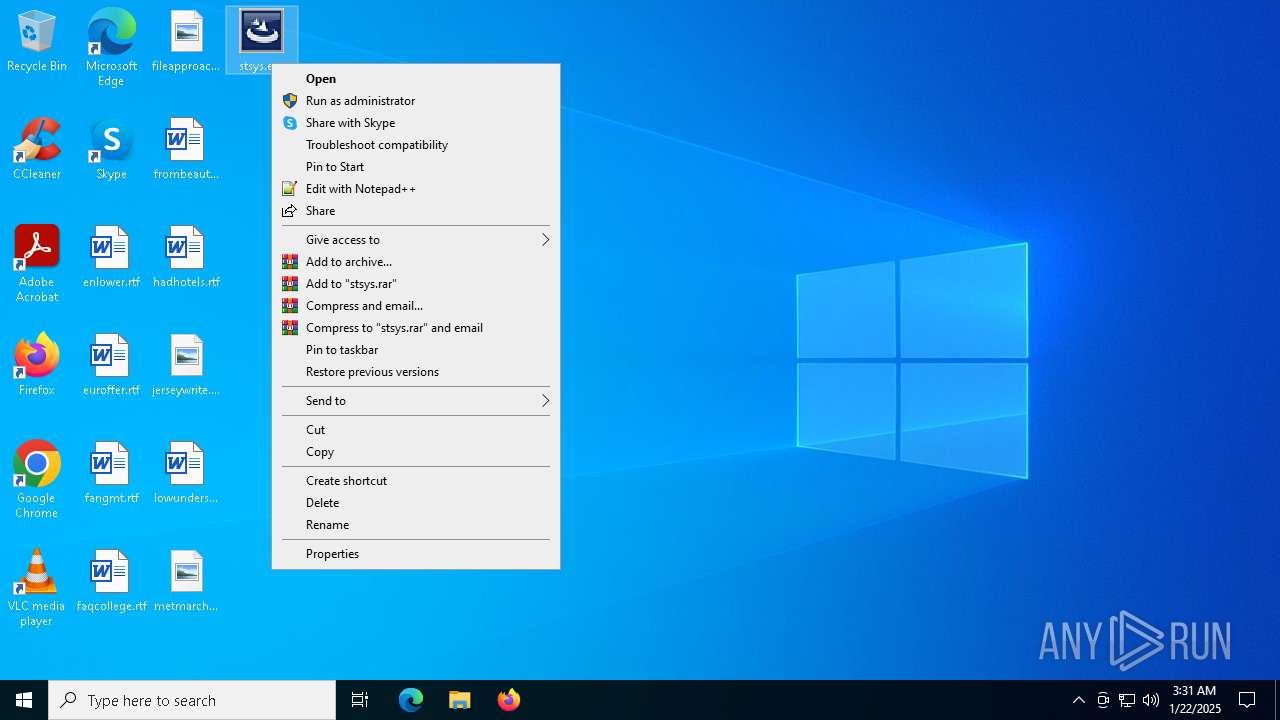
| File name: | stsys.exe |
| Full analysis: | https://app.any.run/tasks/b3d9853e-2c4c-4dca-b00e-a7302459becf |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2025, 03:31:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | 5E8EC47E74DC09C6C1D33F985B2DD85D |
| SHA1: | 8E0FE79FFA9A2DBCEFED4CFDBB91A180F2858B10 |
| SHA256: | 5F351A246FBD729DB808EFBC513C0F54F57E7F7ED2F1069C5443C800817EEA28 |
| SSDEEP: | 6144:+6XnW2Kg+zWnv2UAO3iaM25DZgCaYi73U2rRCpfAbq8bb:D3BDZfGrRCpfAbq8X |
MALICIOUS
MOFKSYS has been detected (YARA)
- stsys.exe (PID: 5464)
Changes the autorun value in the registry
- explorer.exe (PID: 7072)
- svchost.exe (PID: 7128)
SUSPICIOUS
There is functionality for taking screenshot (YARA)
- stsys.exe (PID: 5464)
The process creates files with name similar to system file names
- stsys.exe (PID: 7040)
- spoolsv.exe (PID: 7100)
Starts itself from another location
- stsys.exe (PID: 7040)
- spoolsv.exe (PID: 7100)
- svchost.exe (PID: 7128)
- explorer.exe (PID: 7072)
Executable content was dropped or overwritten
- stsys.exe (PID: 7040)
- spoolsv.exe (PID: 7100)
- explorer.exe (PID: 7072)
Creates or modifies Windows services
- svchost.exe (PID: 7128)
INFO
Reads the computer name
- stsys.exe (PID: 5464)
- stsys.exe (PID: 7040)
- svchost.exe (PID: 7128)
- explorer.exe (PID: 7072)
Create files in a temporary directory
- stsys.exe (PID: 5464)
- stsys.exe (PID: 7040)
- spoolsv.exe (PID: 7100)
- svchost.exe (PID: 7128)
- spoolsv.exe (PID: 7156)
- explorer.exe (PID: 7072)
Checks supported languages
- stsys.exe (PID: 5464)
- stsys.exe (PID: 7040)
- explorer.exe (PID: 7072)
- spoolsv.exe (PID: 7156)
- svchost.exe (PID: 7128)
- spoolsv.exe (PID: 7100)
The sample compiled with english language support
- stsys.exe (PID: 5464)
Failed to create an executable file in Windows directory
- stsys.exe (PID: 5464)
Manual execution by a user
- stsys.exe (PID: 7040)
Creates files or folders in the user directory
- explorer.exe (PID: 7072)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:06:14 19:01:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 176128 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3670 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft |
| ProductName: | Win |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Win |
| OriginalFileName: | Win.exe |
Total processes
141
Monitored processes
10
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | at.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3612 | at 03:33 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\SysWOW64\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5464 | "C:\Users\admin\Desktop\stsys.exe" | C:\Users\admin\Desktop\stsys.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 6276 | at 03:34 /interactive /every:M,T,W,Th,F,S,Su c:\windows\system\svchost.exe | C:\Windows\SysWOW64\at.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Schedule service command line interface Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6280 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | at.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7040 | "C:\Users\admin\Desktop\stsys.exe" | C:\Users\admin\Desktop\stsys.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7072 | c:\windows\system\explorer.exe | C:\Windows\System\explorer.exe | stsys.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7100 | c:\windows\system\spoolsv.exe SE | C:\Windows\System\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7128 | c:\windows\system\svchost.exe | C:\Windows\System\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7156 | c:\windows\system\spoolsv.exe PR | C:\Windows\System\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
787
Read events
766
Write events
15
Delete events
6
Modification events
| (PID) Process: | (5464) stsys.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7040) stsys.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7072) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Active Setup\Installed Components\{Y479C6D0-OTRW-U5GH-S1EE-E0AC10B4E666} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\mrsys.exe MR | |||
| (PID) Process: | (7072) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (7072) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (7072) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\system\explorer.exe RO | |||
| (PID) Process: | (7072) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\system\svchost.exe RO | |||
| (PID) Process: | (7128) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\system\explorer.exe RO | |||
| (PID) Process: | (7128) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\system\svchost.exe RO | |||
| (PID) Process: | (7128) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Active Setup\Installed Components\{F146C9B1-VMVQ-A9RC-NUFL-D0BA00B4E999} |
| Operation: | write | Name: | StubPath |
Value: C:\Users\admin\AppData\Roaming\mrsys.exe MR | |||
Executable files
4
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7072 | explorer.exe | C:\Windows\System\spoolsv.exe | executable | |
MD5:5615EF8E8FC4588219F0F945F3F148D5 | SHA256:1FA1F344E92C414D92419096E5A704B9D078710DEC4AE00A63FB2500E72D4DF8 | |||
| 5464 | stsys.exe | C:\Users\admin\AppData\Local\Temp\~DFF990572A8FB5ADBE.TMP | binary | |
MD5:DC2E5BDC5897C950F35C415776247F7E | SHA256:53B030FA930F1A5A9A803F55A30889EDC3B719ACDAA9398E8FA9A89FACB8DC6D | |||
| 7156 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFD215007BFA28E9F7.TMP | binary | |
MD5:076912FE57C189BB42AB679F8883E788 | SHA256:19B3D77467D01F624E453215366E3EFC3CDC1B0B4D36394E3F3C89B0D8724897 | |||
| 7100 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DFEAA9CED4D773D9FB.TMP | binary | |
MD5:076912FE57C189BB42AB679F8883E788 | SHA256:19B3D77467D01F624E453215366E3EFC3CDC1B0B4D36394E3F3C89B0D8724897 | |||
| 7100 | spoolsv.exe | C:\Windows\System\svchost.exe | executable | |
MD5:AFA6CFD76D16B82A169B69952D4E313C | SHA256:C0C490CA886594C3D787CE662E1AC204D153D8E659C0723DDC5E64FDA5906F50 | |||
| 7072 | explorer.exe | C:\Users\admin\AppData\Roaming\mrsys.exe | executable | |
MD5:49460D897B400172C4536531694B323B | SHA256:B3BEB7B77541B90CFA6010473DC916383EFE89FDA19F8144470F1C3E54298DDB | |||
| 7040 | stsys.exe | C:\Users\admin\AppData\Local\Temp\~DF7BE9491EBF216C4B.TMP | binary | |
MD5:1E878AEEEF3F83B9C32616A01DDD62E7 | SHA256:49048ED011A20E77911A12BF8C1AA5B4274276676DAF477025562E5C0D648915 | |||
| 7040 | stsys.exe | C:\Windows\System\explorer.exe | executable | |
MD5:2CCFAA9CEF8964AB172F613D77BA86BF | SHA256:B86EA1F7B2BE3B5AA27F12366FCBD40150ACDDA7DCBBDFCB3AFADC3F46610492 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6332 | backgroundTaskHost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
4388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
4388 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5064 | SearchApp.exe | 104.126.37.145:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2084 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1176 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1076 | svchost.exe | 184.30.18.9:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |