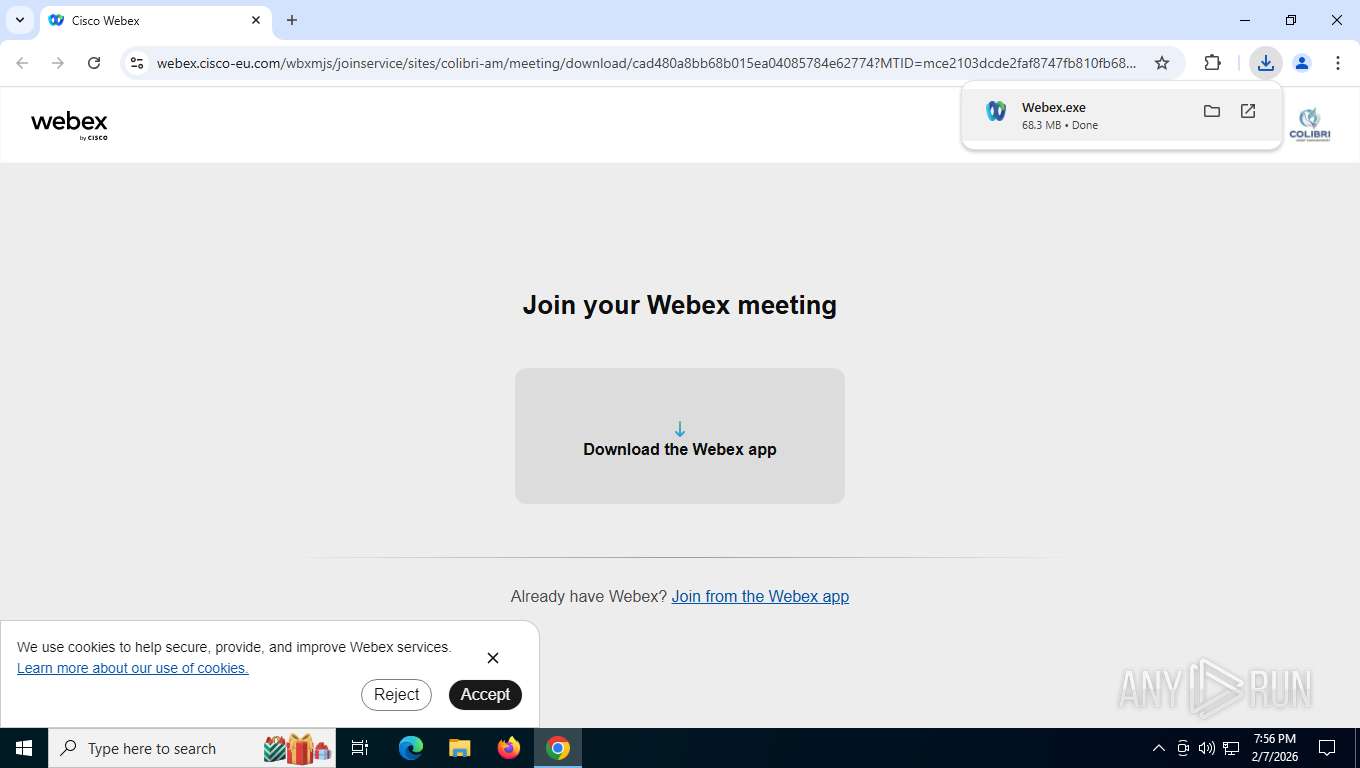
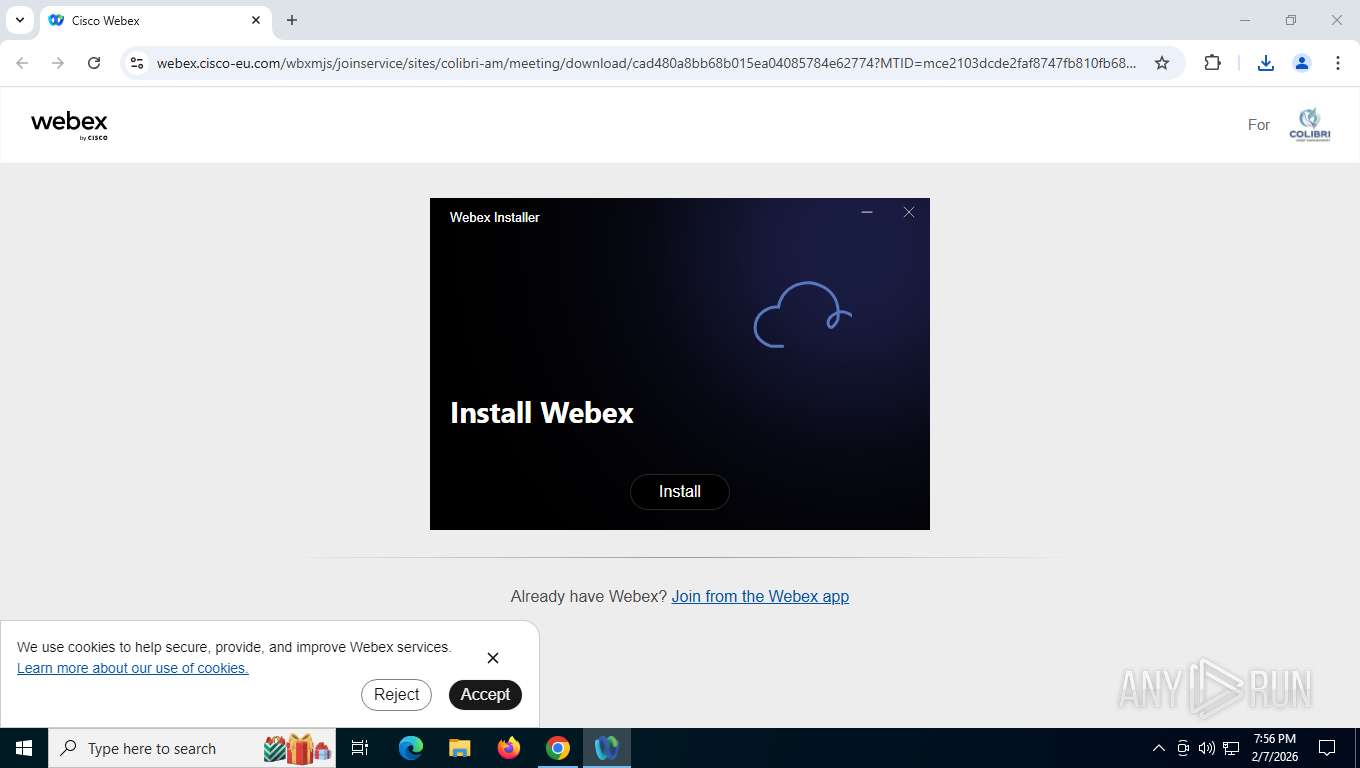
| URL: | https://webex.cisco-eu.com/colibri-am/j.php?MTID=mce2103dcde2faf8747fb810fb688b66c |
| Full analysis: | https://app.any.run/tasks/fd3f026f-aaa4-4276-b306-1f4fb3cd9766 |
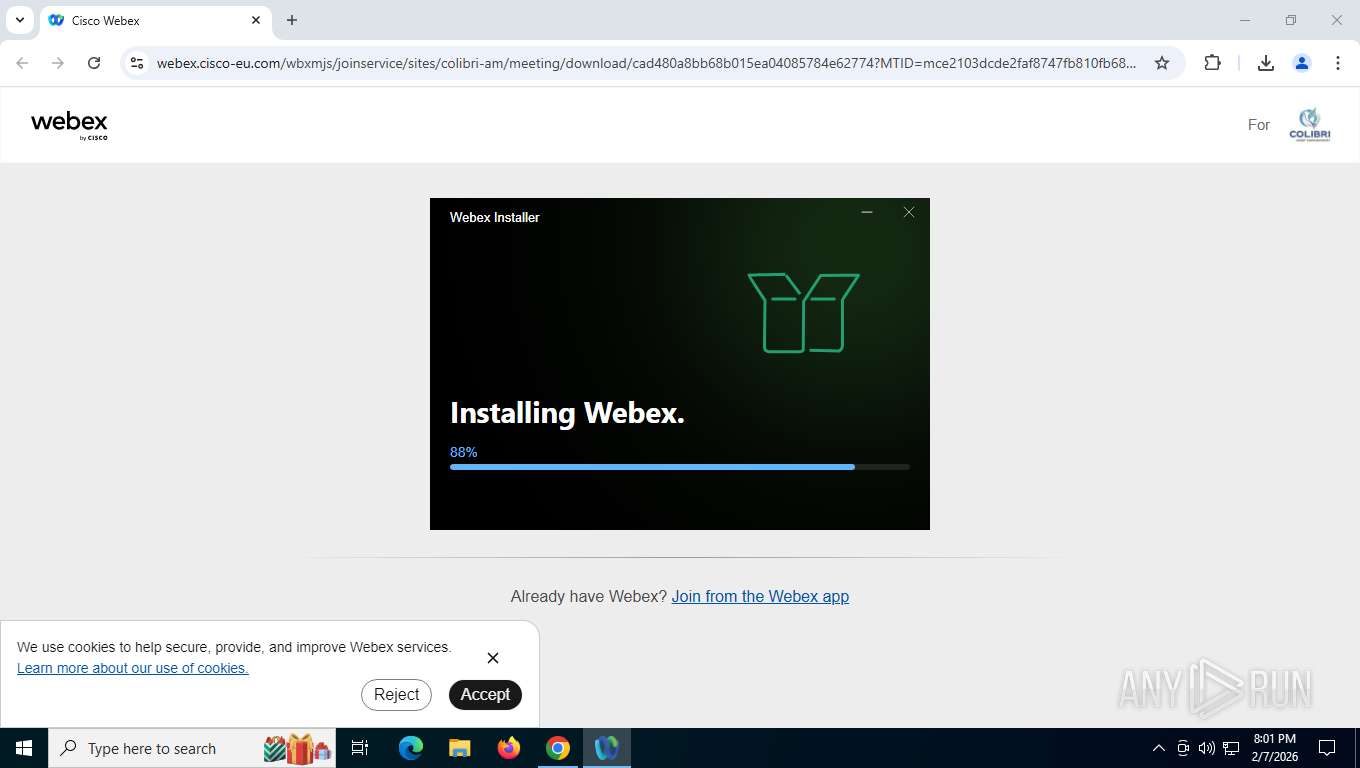
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
| Analysis date: | February 08, 2026, 00:56:24 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B0C2B1DFD3BCB0BAEB10609F19D9502E |
| SHA1: | CEB981494B30DE11D437032DD332106F7CBD6D27 |
| SHA256: | 5F34188C23B215C48110E11993596CDD1AFC615F793EEFA6895947FF1B3B4D0C |
| SSDEEP: | 3:N8Rgd5kKdJMZhPOIXENAXudKxd/G:2Wd5k0MjsNAXud+k |
MALICIOUS
Changes Windows Defender settings
- Webex for Windows.exe (PID: 5044)
Adds path to the Windows Defender exclusion list
- Webex for Windows.exe (PID: 5044)
Changes powershell execution policy (Bypass)
- Webex for Windows.exe (PID: 5044)
Changes the autorun value in the registry
- Discord.exe (PID: 9140)
Steals credentials from Web Browsers
- powershell.exe (PID: 6940)
Actions looks like stealing of personal data
- powershell.exe (PID: 6940)
SUSPICIOUS
The process creates files with name similar to system file names
- Webex.exe (PID: 9032)
Malware-specific behavior (creating "System.dll" in Temp)
- Webex.exe (PID: 9032)
Drops 7-zip archiver for unpacking
- Webex.exe (PID: 9032)
Executable content was dropped or overwritten
- Webex.exe (PID: 9032)
- powershell.exe (PID: 8584)
- Discord.exe (PID: 9140)
Process drops legitimate windows executable
- Webex.exe (PID: 9032)
- powershell.exe (PID: 8584)
- Discord.exe (PID: 9140)
Application launched itself
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
Starts POWERSHELL.EXE for commands execution
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
Creates new registry property (POWERSHELL)
- powershell.exe (PID: 1860)
Bypass execution policy to execute commands
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8772)
- powershell.exe (PID: 8584)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 5172)
The process bypasses the loading of PowerShell profile settings
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
Script adds exclusion path to Windows Defender
- Webex for Windows.exe (PID: 5044)
Gets file extension (POWERSHELL)
- powershell.exe (PID: 8584)
Process drops python dynamic module
- powershell.exe (PID: 8584)
- Discord.exe (PID: 9140)
The process drops C-runtime libraries
- powershell.exe (PID: 8584)
- Discord.exe (PID: 9140)
The executable file from the user directory is run by the CMD process
- Discord.exe (PID: 9140)
Starts CMD.EXE for commands execution
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 6940)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 6940)
Get information on the list of running processes
- Webex for Windows.exe (PID: 5044)
Possible stealing of messenger data
- Discord.exe (PID: 9140)
Starts NET.EXE to display or manage information about active sessions
- net.exe (PID: 4604)
- cmd.exe (PID: 1860)
Possibly malicious use of IEX has been detected
- Discord.exe (PID: 9140)
Escape characters obfuscation (POWERSHELL)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6940)
Probably obfuscated PowerShell command line is found
- Webex for Windows.exe (PID: 5044)
Loads Python modules
- pythonw.exe (PID: 4372)
- pythonw.exe (PID: 7960)
The process executes via Task Scheduler
- pythonw.exe (PID: 7960)
Gets path to any of the special folders (POWERSHELL)
- powershell.exe (PID: 7212)
- powershell.exe (PID: 6820)
Manipulates environment variables
- powershell.exe (PID: 6820)
Obfuscation pattern (POWERSHELL)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 6940)
Process uses powershell cmdlet to discover network configuration
- Webex for Windows.exe (PID: 5044)
Possible code assembly (raw parameter)
- powershell.exe (PID: 6940)
Possible stealing from browsers
- powershell.exe (PID: 6940)
Returns all items found within a container (POWERSHELL)
- powershell.exe (PID: 6940)
Searches for installed software
- powershell.exe (PID: 6820)
INFO
Drops script file
- chrome.exe (PID: 8556)
- powershell.exe (PID: 1860)
- powershell.exe (PID: 8772)
- powershell.exe (PID: 8584)
- powershell.exe (PID: 6940)
- Discord.exe (PID: 9140)
- powershell.exe (PID: 2640)
- powershell.exe (PID: 6820)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 6940)
- powershell.exe (PID: 7212)
- powershell.exe (PID: 5172)
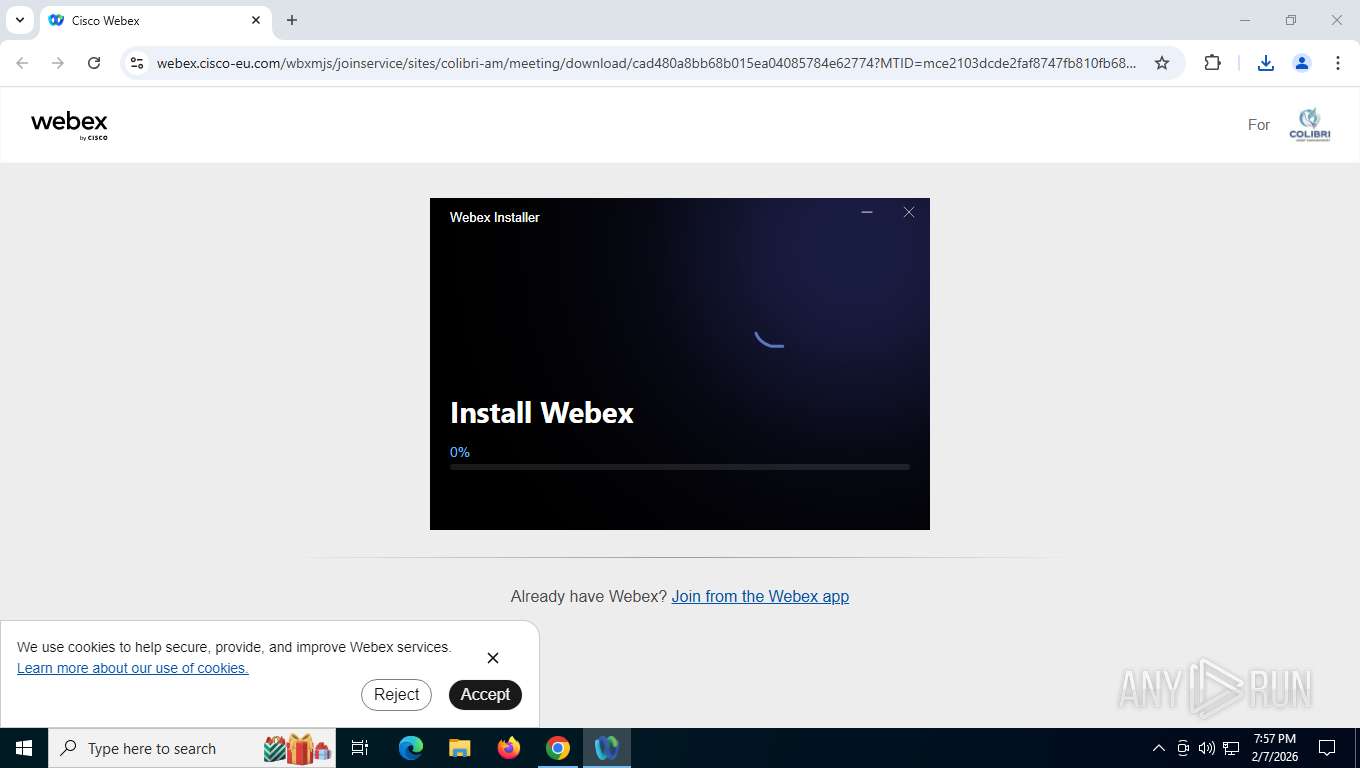
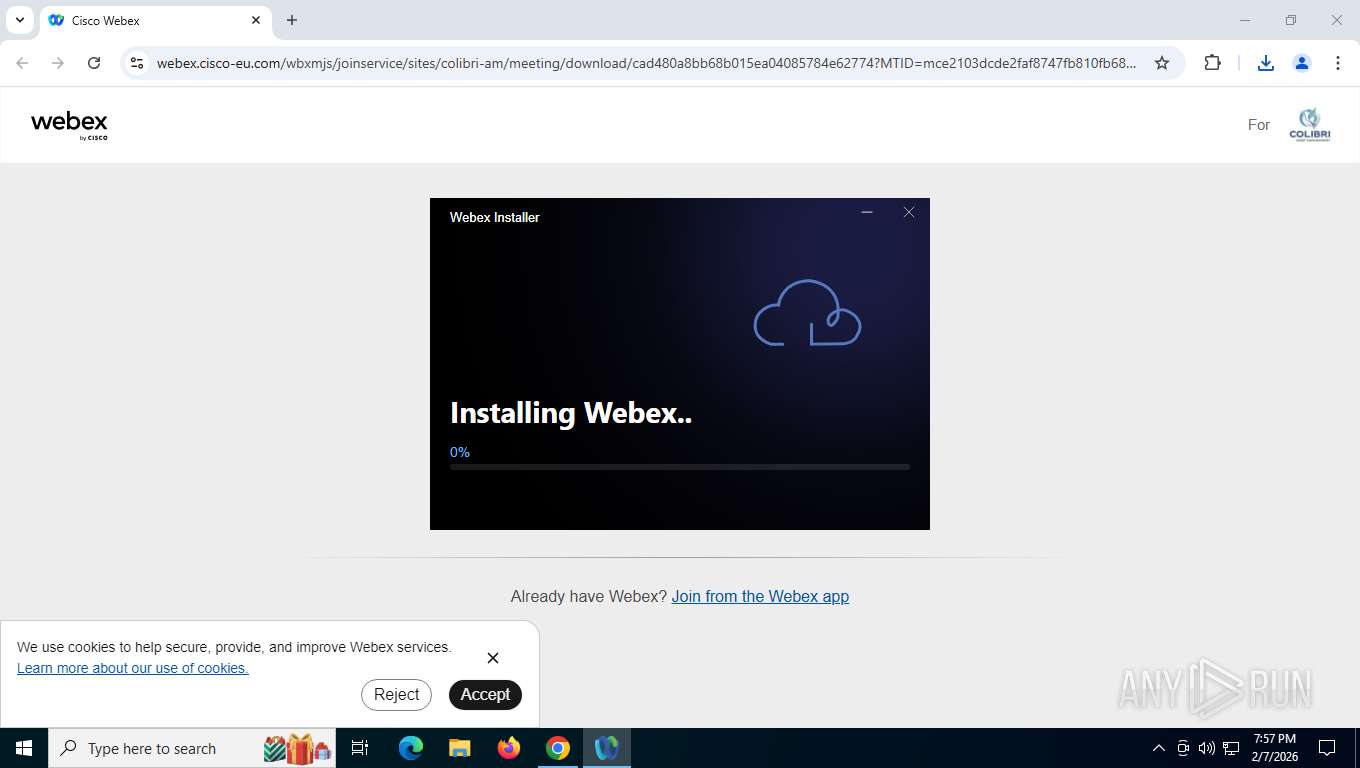
Create files in a temporary directory
- Webex.exe (PID: 9032)
- Webex for Windows.exe (PID: 5044)
- powershell.exe (PID: 6820)
Application launched itself
- chrome.exe (PID: 8556)
Executable content was dropped or overwritten
- chrome.exe (PID: 8556)
- chrome.exe (PID: 5412)
- chrome.exe (PID: 4876)
Checks supported languages
- Webex.exe (PID: 9032)
- Webex for Windows.exe (PID: 5044)
- Webex for Windows.exe (PID: 8356)
- Webex for Windows.exe (PID: 6172)
- Webex for Windows.exe (PID: 5728)
- Discord.exe (PID: 4272)
- Discord.exe (PID: 9140)
- Discord.exe (PID: 1136)
- Discord.exe (PID: 9016)
- Discord.exe (PID: 8748)
- Discord.exe (PID: 7856)
- pythonw.exe (PID: 4372)
- pythonw.exe (PID: 7960)
- Webex for Windows.exe (PID: 8148)
Reads the computer name
- Webex.exe (PID: 9032)
- Webex for Windows.exe (PID: 5044)
- Webex for Windows.exe (PID: 8356)
- Webex for Windows.exe (PID: 5728)
- Discord.exe (PID: 9140)
- Discord.exe (PID: 4272)
- Discord.exe (PID: 9016)
- Discord.exe (PID: 1136)
- pythonw.exe (PID: 4372)
- Discord.exe (PID: 8748)
- pythonw.exe (PID: 7960)
- Webex for Windows.exe (PID: 8148)
The sample compiled with english language support
- Webex.exe (PID: 9032)
- powershell.exe (PID: 8584)
- Discord.exe (PID: 9140)
- chrome.exe (PID: 5412)
- chrome.exe (PID: 4876)
Reads security settings of Internet Explorer
- Webex.exe (PID: 9032)
- powershell.exe (PID: 6820)
- Webex for Windows.exe (PID: 8148)
Reads Environment values
- Webex for Windows.exe (PID: 5044)
- pythonw.exe (PID: 4372)
- Webex for Windows.exe (PID: 8148)
- pythonw.exe (PID: 7960)
Process checks computer location settings
- Webex for Windows.exe (PID: 5044)
- Webex for Windows.exe (PID: 6172)
- Discord.exe (PID: 9140)
Reads product name
- Webex for Windows.exe (PID: 5044)
- pythonw.exe (PID: 4372)
- pythonw.exe (PID: 7960)
Creates files or folders in the user directory
- Webex for Windows.exe (PID: 5044)
- Webex for Windows.exe (PID: 5728)
- Discord.exe (PID: 9140)
- Webex for Windows.exe (PID: 8148)
Reads the machine GUID from the registry
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
- pythonw.exe (PID: 4372)
- Webex for Windows.exe (PID: 8148)
There is functionality for taking screenshot (YARA)
- Webex.exe (PID: 9032)
- Webex for Windows.exe (PID: 8356)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8772)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8772)
- powershell.exe (PID: 8584)
- powershell.exe (PID: 7212)
- powershell.exe (PID: 5732)
- powershell.exe (PID: 5172)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 8584)
Using PowerShell for ZIP File Operations
- powershell.exe (PID: 8584)
Node.js compiler has been detected
- Webex for Windows.exe (PID: 5044)
- Webex for Windows.exe (PID: 8356)
- Webex for Windows.exe (PID: 5728)
- Webex for Windows.exe (PID: 6172)
Reads CPU info
- Webex for Windows.exe (PID: 5044)
Checks proxy server information
- Webex for Windows.exe (PID: 5044)
- Discord.exe (PID: 9140)
- powershell.exe (PID: 7212)
- slui.exe (PID: 4468)
Python executable
- pythonw.exe (PID: 4372)
- pythonw.exe (PID: 7960)
Launching a file from a Registry key
- Discord.exe (PID: 9140)
Disables trace logs
- powershell.exe (PID: 7212)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7212)
Returns hidden items found within a container (POWERSHELL)
- conhost.exe (PID: 3188)
- conhost.exe (PID: 1836)
- conhost.exe (PID: 8052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
248
Monitored processes
91
Malicious processes
6
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=1292,i,4617391245915704738,16651543076928763627,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=3912 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=7156,i,4617391245915704738,16651543076928763627,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=4772 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1080 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1136 | "C:\Users\admin\AppData\Local\Webex\Discord.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\discord" --field-trial-handle=1720,i,10543399191980447857,17545823309818747003,262144 --enable-features=EnableTransparentHwndEnlargement --disable-features=ScreenAIOCREnabled,SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit --variations-seed-version --mojo-platform-channel-handle=1896 /prefetch:3 | C:\Users\admin\AppData\Local\Webex\Discord.exe | — | Discord.exe | |||||||||||
User: admin Company: Discord Inc. Integrity Level: HIGH Description: Discord Version: 1.0.9219 Modules
| |||||||||||||||
| 1692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --field-trial-handle=6792,i,4617391245915704738,16651543076928763627,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=6684 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1836 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffd700efff8,0x7ffd700f0004,0x7ffd700f0010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 133.0.6943.127 Modules
| |||||||||||||||
| 1860 | powershell.exe -NoProfile -ExecutionPolicy Bypass -Command "Try { New-Item -Path \"HKLM:\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications\" -Force | Out-Null; New-ItemProperty -Path \"HKLM:\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications\" -Name \"DisableEnhancedNotifications\" -Value 1 -PropertyType DWord -Force | Out-Null } Catch {}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Webex for Windows.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | C:\WINDOWS\system32\cmd.exe /d /s /c "net session" | C:\Windows\System32\cmd.exe | — | Discord.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --field-trial-handle=5372,i,4617391245915704738,16651543076928763627,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version=20251218-201203.402000 --mojo-platform-channel-handle=5928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
Total events
81 571
Read events
81 547
Write events
4
Delete events
20
Modification events
| (PID) Process: | (5044) Webex for Windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (5044) Webex for Windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (5044) Webex for Windows.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (1860) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (1860) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Defender Security Center\Notifications |
| Operation: | write | Name: | DisableEnhancedNotifications |
Value: 1 | |||
| (PID) Process: | (9140) Discord.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | electron.app.Discord |
Value: C:\Windows\explorer.exe C:\Users\admin\AppData\Roaming\webex_session\Discord.exe | |||
| (PID) Process: | (9140) Discord.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\StartupApproved\Run |
| Operation: | delete value | Name: | electron.app.Discord |
Value: | |||
| (PID) Process: | (8148) Webex for Windows.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: Webex for Windows.exe | |||
| (PID) Process: | (8148) Webex for Windows.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\DirectDraw\MostRecentApplication |
| Operation: | write | Name: | ID |
Value: | |||
Executable files
91
Suspicious files
562
Text files
232
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF1e50cd.TMP | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF1e50dd.TMP | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old~RF1e50ec.TMP | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Segmentation Platform\SegmentInfoDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF1e50ec.TMP | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF1e50ec.TMP | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 8556 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF1e50fc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
124
TCP/UDP connections
67
DNS requests
69
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7832 | chrome.exe | GET | 302 | 172.67.182.140:443 | https://webex.cisco-eu.com/cdn-cgi/challenge-platform/scripts/jsd/main.js | unknown | — | — | unknown |
7832 | chrome.exe | OPTIONS | 200 | 35.190.80.1:443 | https://a.nel.cloudflare.com/report/v4?s=VGvuBO%2F8CgAB1VkmqoKjbcd2bEVlque8LWXru6f1wAicTVNV5VtLdhD5kOLZf%2BLIOdSRZ5hHGX8J0sh9oMCishl6%2FuLmEUMKxipsDFTciMpvWA%3D%3D | unknown | — | — | unknown |
7832 | chrome.exe | GET | 200 | 172.217.16.206:80 | http://clients2.google.com/time/1/current?cup2key=8:TyUXvjOhloRjOMiEyac8VklvmB0QUxcfOM6ulQ8AIyk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7832 | chrome.exe | GET | 200 | 142.251.13.94:443 | https://clientservices.googleapis.com/chrome-variations/seed?osname=win&channel=stable&milestone=133 | unknown | compressed | 83.6 Kb | whitelisted |
7832 | chrome.exe | POST | 200 | 142.251.127.84:443 | https://accounts.google.com/ListAccounts?gpsia=1&source=ChromiumBrowser&json=standard | unknown | text | 17 b | whitelisted |
7832 | chrome.exe | GET | 200 | 172.67.182.140:443 | https://webex.cisco-eu.com/styles/main.css | unknown | text | 128 Kb | unknown |
7832 | chrome.exe | GET | 200 | 172.67.182.140:443 | https://webex.cisco-eu.com/colibri-am/j.php?MTID=mce2103dcde2faf8747fb810fb688b66c | unknown | text | 11.4 Kb | unknown |
7832 | chrome.exe | GET | 200 | 172.67.182.140:443 | https://webex.cisco-eu.com/styles/vendor.css | unknown | text | 22.6 Kb | unknown |
7832 | chrome.exe | GET | 200 | 172.67.182.140:443 | https://webex.cisco-eu.com/wbxmjs/joinservice/sites/colibri-am/meeting/download/cad480a8bb68b015ea04085784e62774?MTID=mce2103dcde2faf8747fb810fb688b66c | unknown | html | 30.3 Kb | unknown |
7832 | chrome.exe | GET | 200 | 172.67.182.140:443 | https://webex.cisco-eu.com/styles/components.css | unknown | text | 128 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
3344 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5512 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7832 | chrome.exe | 172.217.16.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
7832 | chrome.exe | 172.217.16.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
7832 | chrome.exe | 142.251.13.94:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
7832 | chrome.exe | 142.251.127.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7832 | chrome.exe | 172.67.182.140:443 | webex.cisco-eu.com | CLOUDFLARENET | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
webex.cisco-eu.com |
| unknown |
accounts.google.com |
| whitelisted |
api.cisco-eu.com |
| unknown |
a.nel.cloudflare.com |
| whitelisted |
mediu.webex.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7832 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
7832 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
3344 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7832 | chrome.exe | Misc activity | ET INFO DropBox User Content Domain (dl .dropboxusercontent .com in TLS SNI) |
5728 | Webex for Windows.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
5728 | Webex for Windows.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7832 | chrome.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
7832 | chrome.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2292 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
Process | Message |
|---|---|
Webex for Windows.exe | [5044:0207/195659.436:INFO:CONSOLE(2)] "TypeError: ipcRenderer.handle is not a function", source: node:electron/js2c/renderer_init (2)
|
Webex for Windows.exe | [5044:0207/195659.436:INFO:CONSOLE(2)] "Unable to load preload script: C:\Users\admin\AppData\Local\Temp\38iRQBT4lzi02T9GKmI19dr36U7\resources\app.asar\preload.entry.js", source: node:electron/js2c/renderer_init (2)
|
Webex for Windows.exe | [5044:0207/195659.662:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.661Z] [RENDERER][DEBUG] Renderer bootstrapped [object Object]", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195659.663:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.662Z] [RENDERER][DEBUG] initializeDefaultPath invoked", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195659.665:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.664Z] [RENDERER][DEBUG] Received appDataPath from main C:\Users\admin\AppData\Local", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195659.665:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.664Z] [RENDERER][DEBUG] Settings path input populated C:\Users\admin\AppData\Local\Webex", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195659.765:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.765Z] [RENDERER][DEBUG] Loading initial lottie animation cloud.json", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195659.766:INFO:CONSOLE(25)] "[2026-02-08T00:56:59.765Z] [RENDERER][DEBUG] loadLottieAnimation invoked cloud.json", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195700.170:INFO:CONSOLE(25)] "[2026-02-08T00:57:00.169Z] [RENDERER][DEBUG] checkWebView2Runtime invoked", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|
Webex for Windows.exe | [5044:0207/195700.172:INFO:CONSOLE(25)] "[2026-02-08T00:57:00.171Z] [RENDERER][DEBUG] WebView2 runtime status true", source: file:///C:/Users/admin/AppData/Local/Temp/38iRQBT4lzi02T9GKmI19dr36U7/resources/app.asar/renderer.js (25)
|