| File name: | wtp_admin.exe |
| Full analysis: | https://app.any.run/tasks/6236fb0b-f5bc-4e3b-98ec-1984bac25398 |
| Verdict: | Malicious activity |
| Analysis date: | May 25, 2025, 06:01:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | 6C43CDC282BA9EB8BB60260D5F4D7D3C |
| SHA1: | 762E6B830DF5BBA9A783709F11706766A32677B8 |
| SHA256: | 5F327A79C49E3F0B53BB97F3994F7E863C780F62436BB9B33043ADDAC9206B4E |
| SSDEEP: | 98304:D5pC4Q7FeAvJopOUBltbgEB8kpPLAVuSFnTNaPERuueJBKpT+N3B8hU/XVbcYdk/:b8ecFVegBZ7QKkduoH4 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- wtp_admin.exe (PID: 7688)
Executable content was dropped or overwritten
- wtp_admin.exe (PID: 7688)
Reads security settings of Internet Explorer
- wtp_admin.exe (PID: 7688)
- WindowsTerminal.exe (PID: 7828)
Reads the date of Windows installation
- WindowsTerminal.exe (PID: 7828)
INFO
Create files in a temporary directory
- wtp_admin.exe (PID: 7688)
- WindowsTerminal.exe (PID: 7828)
Reads the computer name
- wtp_admin.exe (PID: 7688)
- WindowsTerminal.exe (PID: 7828)
- pwsh.exe (PID: 7956)
The sample compiled with english language support
- wtp_admin.exe (PID: 7688)
Checks supported languages
- wtp_admin.exe (PID: 7688)
- wt.exe (PID: 7812)
- WindowsTerminal.exe (PID: 7828)
- OpenConsole.exe (PID: 7936)
- pwsh.exe (PID: 7956)
Process checks computer location settings
- wtp_admin.exe (PID: 7688)
- WindowsTerminal.exe (PID: 7828)
- pwsh.exe (PID: 7956)
Checks proxy server information
- slui.exe (PID: 5864)
Reads the software policy settings
- slui.exe (PID: 5864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:04:07 14:39:21+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 128512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1ed60 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
136
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5864 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7564 | "C:\Users\admin\Desktop\wtp_admin.exe" | C:\Users\admin\Desktop\wtp_admin.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 7688 | "C:\Users\admin\Desktop\wtp_admin.exe" | C:\Users\admin\Desktop\wtp_admin.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7812 | "C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\wt.exe" | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\wt.exe | — | wtp_admin.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 7828 | wt.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\WindowsTerminal.exe | — | wt.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 7936 | "C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\OpenConsole.exe" --headless --textMeasurement graphemes --width 120 --height 30 --signal 0x904 --server 0x8f8 | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\OpenConsole.exe | — | WindowsTerminal.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
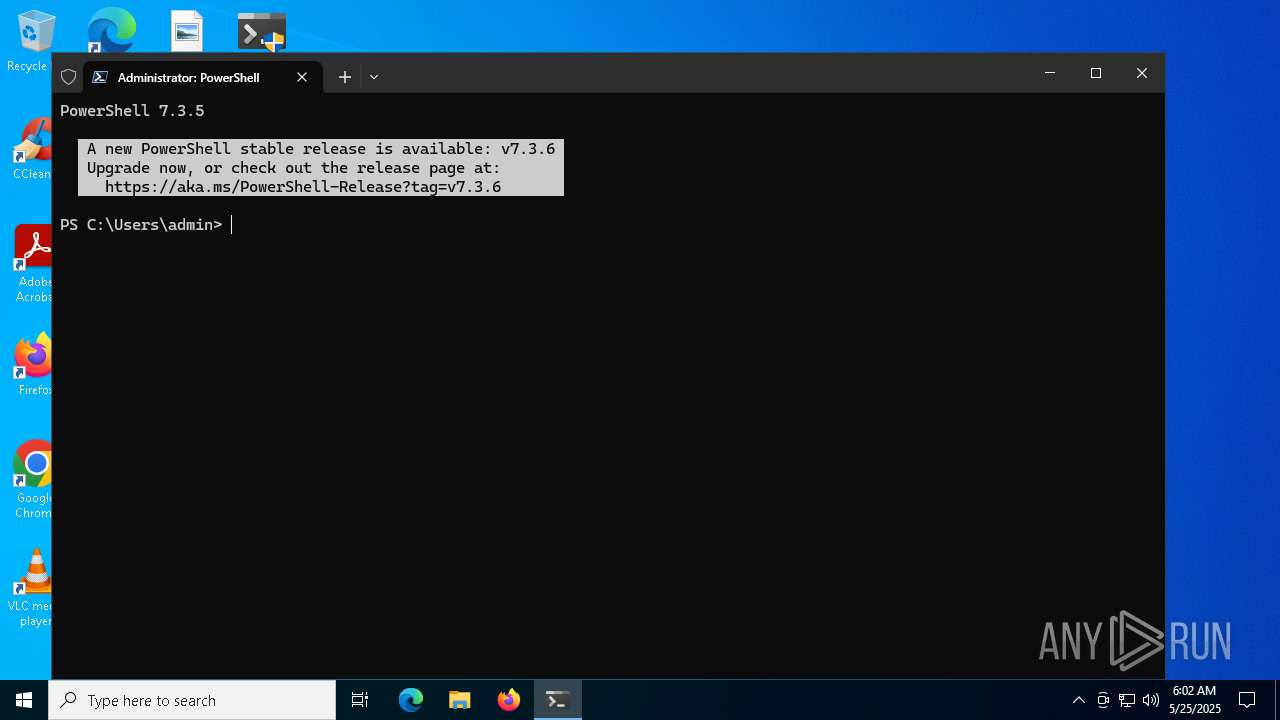
| 7956 | "C:\Program Files\PowerShell\7\pwsh.exe" | C:\Program Files\PowerShell\7\pwsh.exe | WindowsTerminal.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: pwsh Version: 7.3.5.500 Modules
| |||||||||||||||
Total events
10 757
Read events
10 756
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7688) wtp_admin.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR SFX |
| Operation: | write | Name: | C%%Users%admin%AppData%Local%Temp%Terminal-Portable |
Value: C:\Users\admin\AppData\Local\Temp\Terminal-Portable | |||
Executable files
17
Suspicious files
16
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\CascadiaCode.ttf | binary | |
MD5:206399278C4111A44FBF13DE6FFC12D0 | SHA256:54EAE6E26961E980EB3E1EC4EE30F6D3BA7A932A2028832BACEB91CC65844A65 | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\CascadiaMonoItalic.ttf | binary | |
MD5:20A3E5C10587755A8CD4D4959ED198E2 | SHA256:D9D23DFB03C6844448A24CF0337A657AC99965262874D2E6FB5B82AC0AC08C4D | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\CascadiaMono.ttf | binary | |
MD5:B7DE50B2E335EE645AB3B249D8A0FA65 | SHA256:08026F617EEA315CACA59898784E999F6CDB2D0C34D2040DEEB042BCDC359FA2 | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\CascadiaCodeItalic.ttf | binary | |
MD5:3FFC56F2BAE8F9370699A2A020AAA25B | SHA256:48E64F8D82ACD86956DF5F33076966EACF4D9C3EA620C9D88231FA94DA117F2C | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\elevate-shim.exe | executable | |
MD5:E35A40F6DC45793E05F34C20C4F4647D | SHA256:0926532F8812BB71CCB5364C232F59BB24D0034643EC41CEE825DC14C55732D2 | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\Images2\terminal_contrast-black.ico | image | |
MD5:6FF2FFDCFAE7D1F7E30348ACF28A71DC | SHA256:29864669D81E7D4E50A8ECC16E992B339658454F5234E1949C512A07EDBBABF4 | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\Microsoft.UI.Xaml.dll | executable | |
MD5:3EDCD2305516117CD065A0080D991923 | SHA256:8B92DE46C8950CED663E970A3352D3930FF3C978F3C73770935B5316CF6CA5AD | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\Microsoft.Terminal.Control.dll | executable | |
MD5:3A4DD3D593BE0E85FF6B84D062BE35BD | SHA256:29CF209DA36D63F35863AB63B54DA0B10DEBF143AEFDC1AD6D99C2A1DCDDFF8F | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\Microsoft.UI.Xaml3\Assets\NoiseAsset_256x256_PNG.png | image | |
MD5:81F27726C45346351ECA125BD062E9A7 | SHA256:4F2AA94A2E345A32DAE689176B86C644BEF87081FF9DAEF8C77417731862031B | |||
| 7688 | wtp_admin.exe | C:\Users\admin\AppData\Local\Temp\Terminal-Portable\Terminal\Microsoft.Terminal.Remoting.dll | executable | |
MD5:E99D3C4F55E6F2F0F007B80B8433DE91 | SHA256:B31BB390F8189074D5F403569C6A5D15CB78E44687E01700E31ACDD8E04D7D80 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
53
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.71:443 | https://login.live.com/RST2.srf | unknown | xml | 1.24 Kb | whitelisted |
— | — | POST | 400 | 20.190.159.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.2:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.159.71:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
7956 | pwsh.exe | GET | 200 | 2.20.245.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7956 | pwsh.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
— | — | POST | 400 | 40.126.32.134:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
— | — | POST | 400 | 20.190.160.131:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 203 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
2104 | svchost.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
7956 | pwsh.exe | 2.20.245.139:80 | crl.microsoft.com | Akamai International B.V. | SE | whitelisted |
7956 | pwsh.exe | 2.23.181.156:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
aka.ms |
| whitelisted |
powershellinfraartifacts-gkhedzdeaghdezhr.z01.azurefd.net |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7956 | pwsh.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |