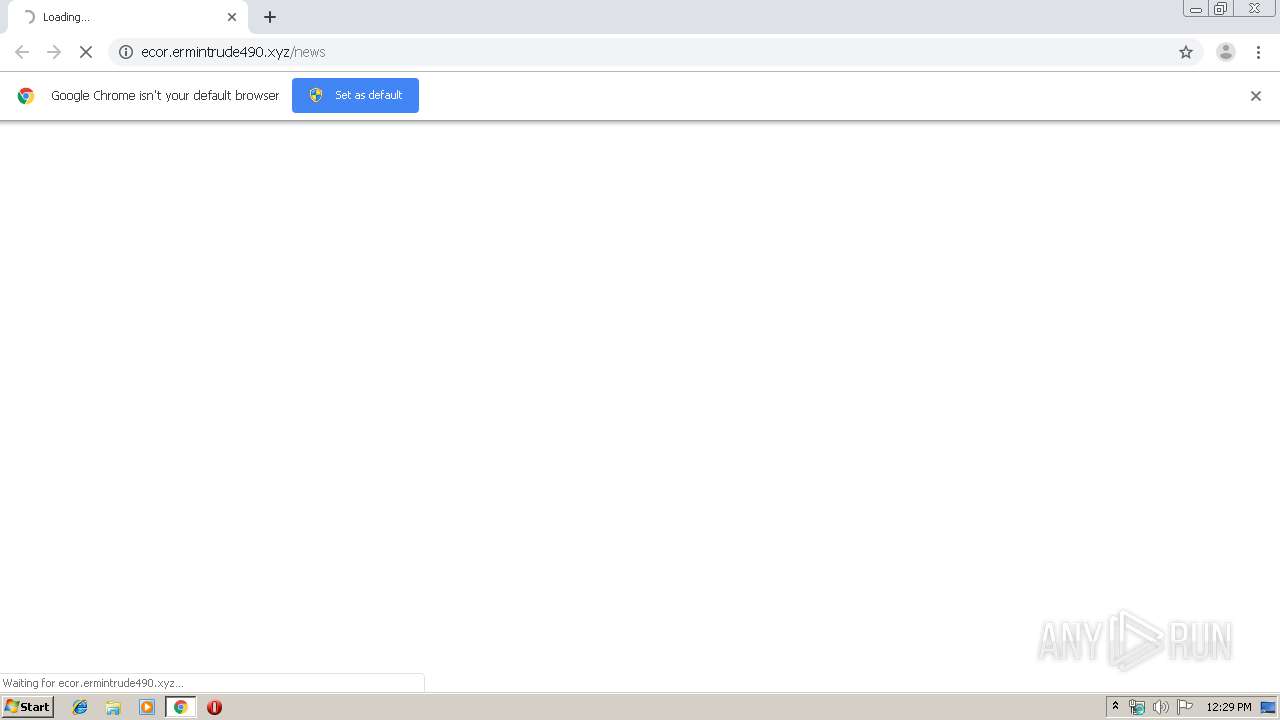
| URL: | http://ecor.Ermintrude490.xyz/news |
| Full analysis: | https://app.any.run/tasks/17266239-317c-41a1-a583-e8d759692881 |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 11:29:16 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A571A28BD41C4FE1A8D047046840A488 |
| SHA1: | C0A67405F85E5595C9EAFD76283B842F3550BBE1 |
| SHA256: | 5F1BD8148D08559FD8FB6A46BCE86636EC1544005803B16C98271B6F1CB9D3C4 |
| SSDEEP: | 3:N1KbdbgXNEAKLAl:CpEdw0l |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3412)
INFO
Application launched itself
- chrome.exe (PID: 3412)
Reads the hosts file
- chrome.exe (PID: 2832)
- chrome.exe (PID: 3412)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
23
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10597695335401386438 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 976 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=3881509473284878664 --mojo-platform-channel-handle=2840 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6159408332386587879 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3325355614608047380 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=4756398656555230842 --mojo-platform-channel-handle=1008 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10509991152875032603 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2760 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7261766995875397508 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2908 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17631367523954868754 --mojo-platform-channel-handle=3024 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,15041828206794184811,12833171140566102097,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14357615037565362211 --mojo-platform-channel-handle=1820 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
612
Read events
522
Write events
85
Delete events
5
Modification events
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3432) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3412-13212674970372500 |
Value: 259 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3412) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
26
Text files
175
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f91182e2-db34-46ff-92d6-79ae3dad60e2.tmp | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169bc7.TMP | text | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF169ba8.TMP | text | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169ba8.TMP | text | |
MD5:— | SHA256:— | |||
| 3412 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
37
DNS requests
18
Threats
44
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
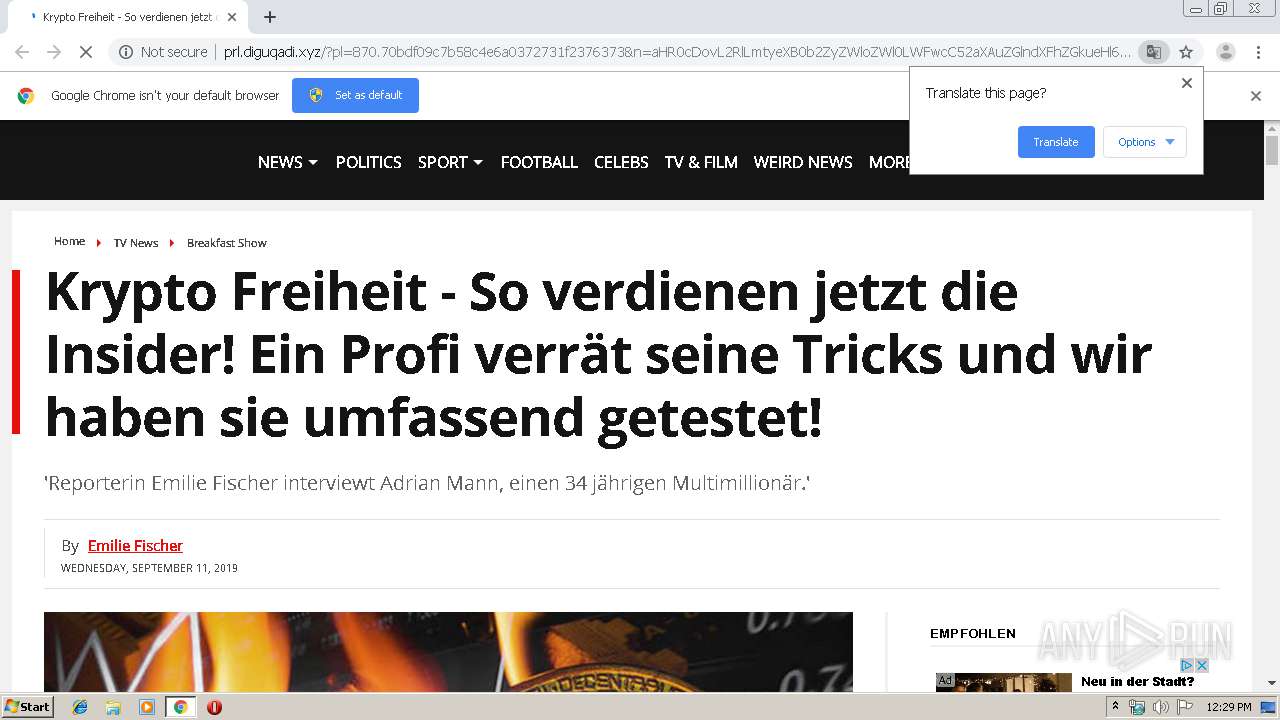
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/de_bitcoin-chart4.png | US | image | 64.4 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/adrian_de1.png | US | image | 199 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/css/tidyx.css | US | text | 7.60 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 47.254.173.118:80 | http://sly211.xyz/sl.html | US | html | 132 b | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/css/css.css | US | text | 115 b | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/cheak.gif | US | image | 2.00 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/adrian_de2.png | US | image | 206 Kb | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/bittrader-step1.png | US | image | 1.74 Mb | suspicious |
2832 | chrome.exe | GET | 200 | 104.24.114.83:80 | http://prl.diguqadi.xyz/prelands/870/img/day2_de_bitcoin.png | US | image | 10.6 Kb | suspicious |
2832 | chrome.exe | GET | 302 | 104.24.114.83:80 | http://vip.diguqadi.xyz/tracker?s_id=7&aff_id=225 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2832 | chrome.exe | 216.58.207.77:443 | accounts.google.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 47.254.173.118:80 | ecor.ermintrude490.xyz | Alibaba (China) Technology Co., Ltd. | US | malicious |
2832 | chrome.exe | 172.217.21.225:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.21.238:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 216.58.205.234:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
2832 | chrome.exe | 104.24.114.83:80 | vip.diguqadi.xyz | Cloudflare Inc | US | shared |
2832 | chrome.exe | 172.217.18.110:80 | translate.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ecor.ermintrude490.xyz |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sly211.xyz |
| suspicious |
clients2.google.com |
| whitelisted |
vip.diguqadi.xyz |
| suspicious |
prl.diguqadi.xyz |
| suspicious |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |
2832 | chrome.exe | Potentially Bad Traffic | AV INFO HTTP Request to a *.xyz domain |