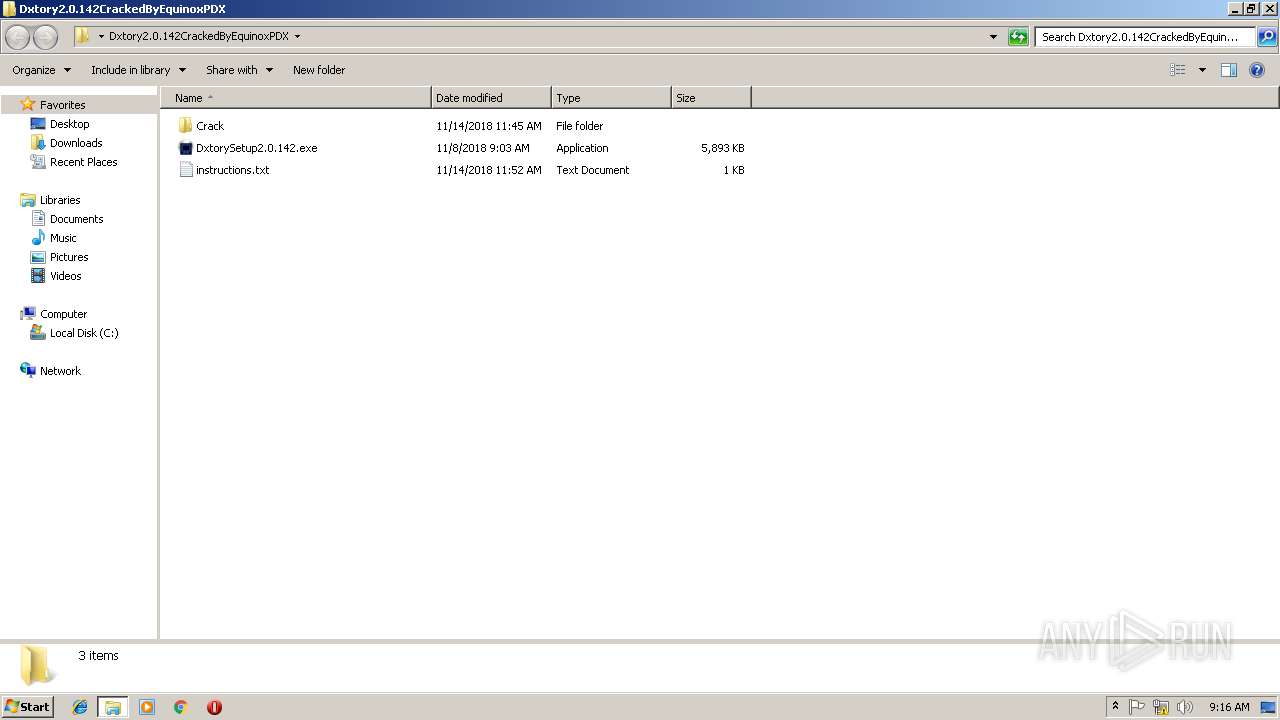
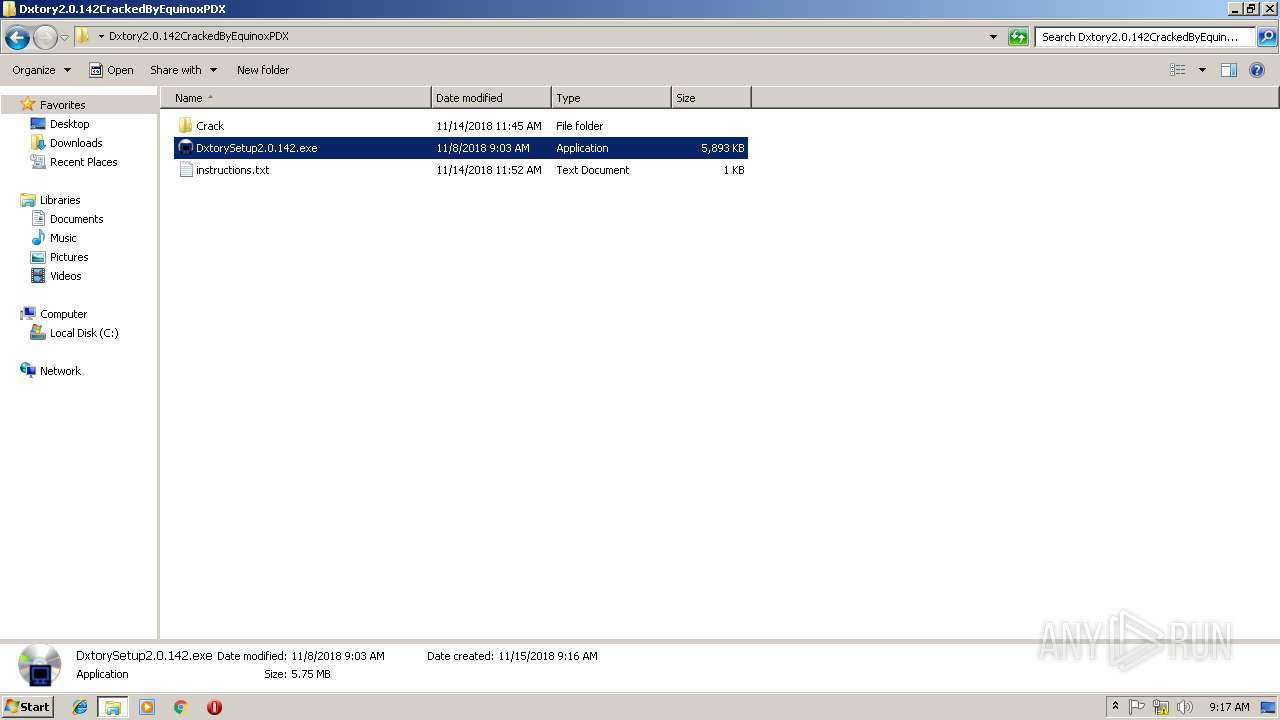
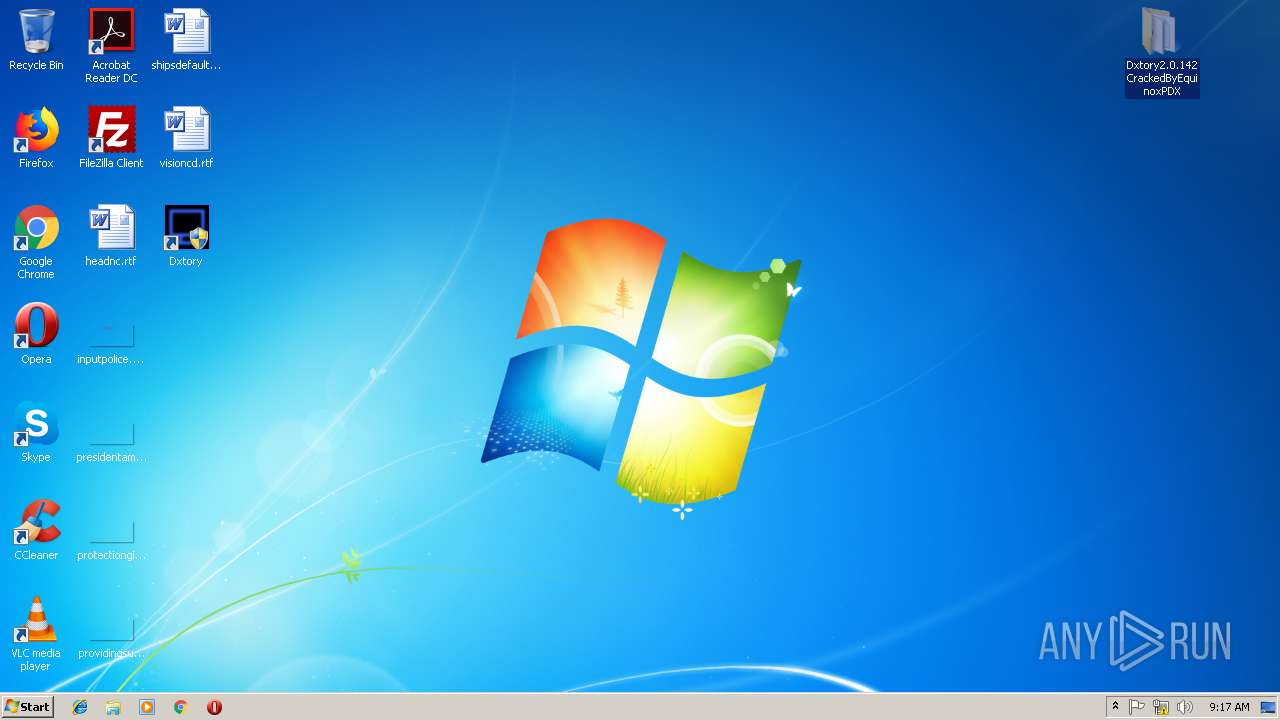
| File name: | Dxtory2.0.142CrackedByEquinoxPDX.zip |
| Full analysis: | https://app.any.run/tasks/7ba71566-e4e6-4940-9c83-b5e8207450e6 |
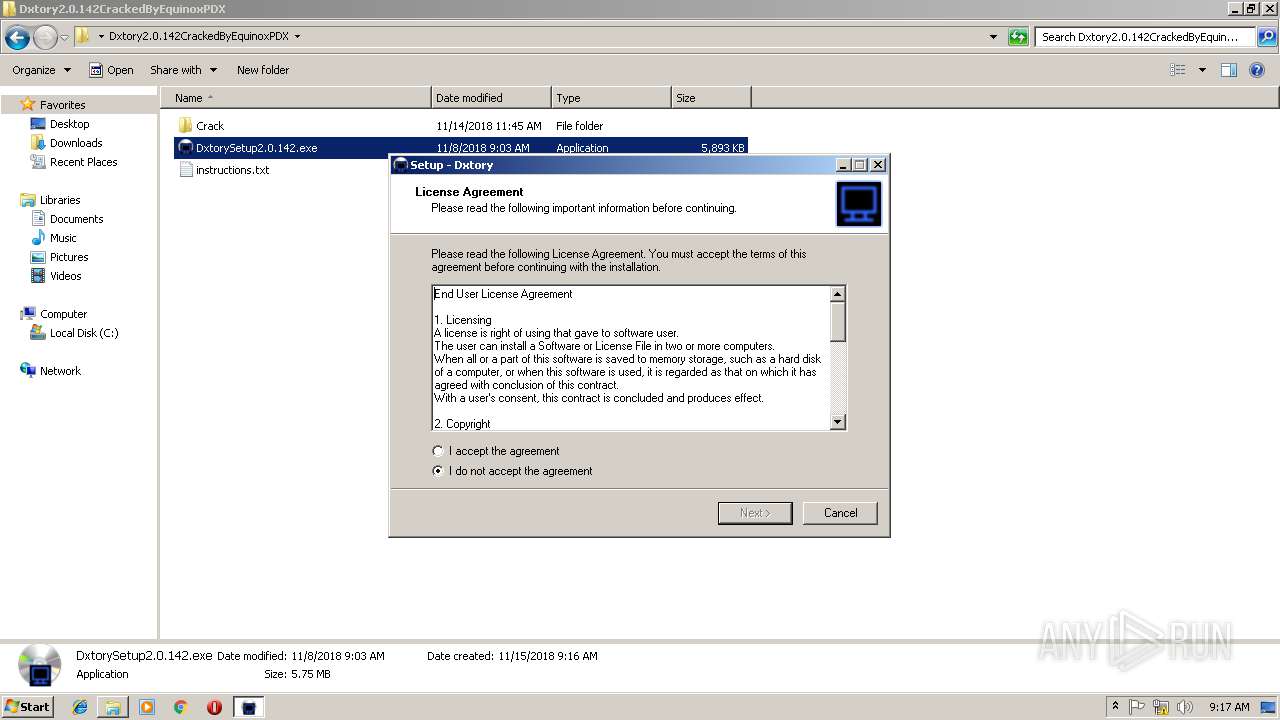
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 09:16:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
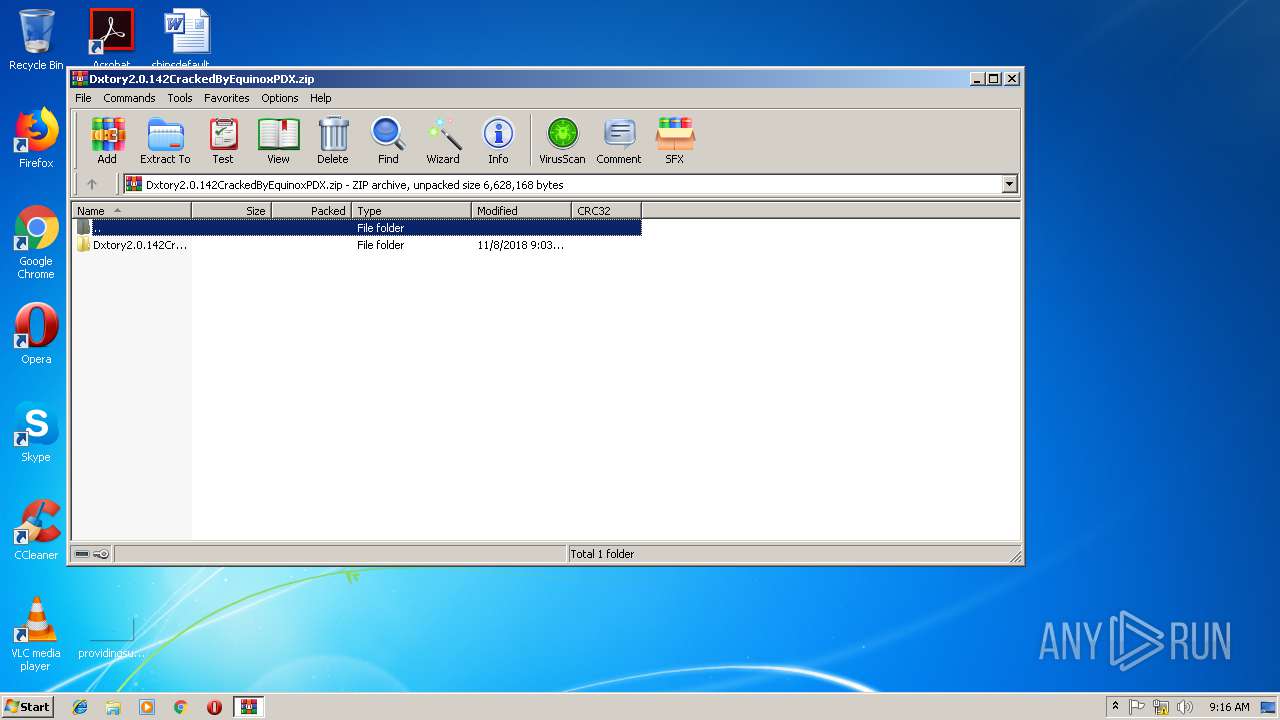
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 98B7137C1ACE48B2804A2D48CE4239E9 |
| SHA1: | B9565F1BA7665EAC90C6A4337BE9CA54D649A834 |
| SHA256: | 5EDC053417BCF429C42AF87DE7C6A1532CA9209410778071CE8250E84D384614 |
| SSDEEP: | 98304:mEMud9nSYEhLEK+nrZAhss1v6wRcTjuY9zMgCpqhk2kjSKsR+xXSMMfLmzPh8KvW:mEMuMtMrvr9zMbpqhk2FKsRwX3MfLmDW |
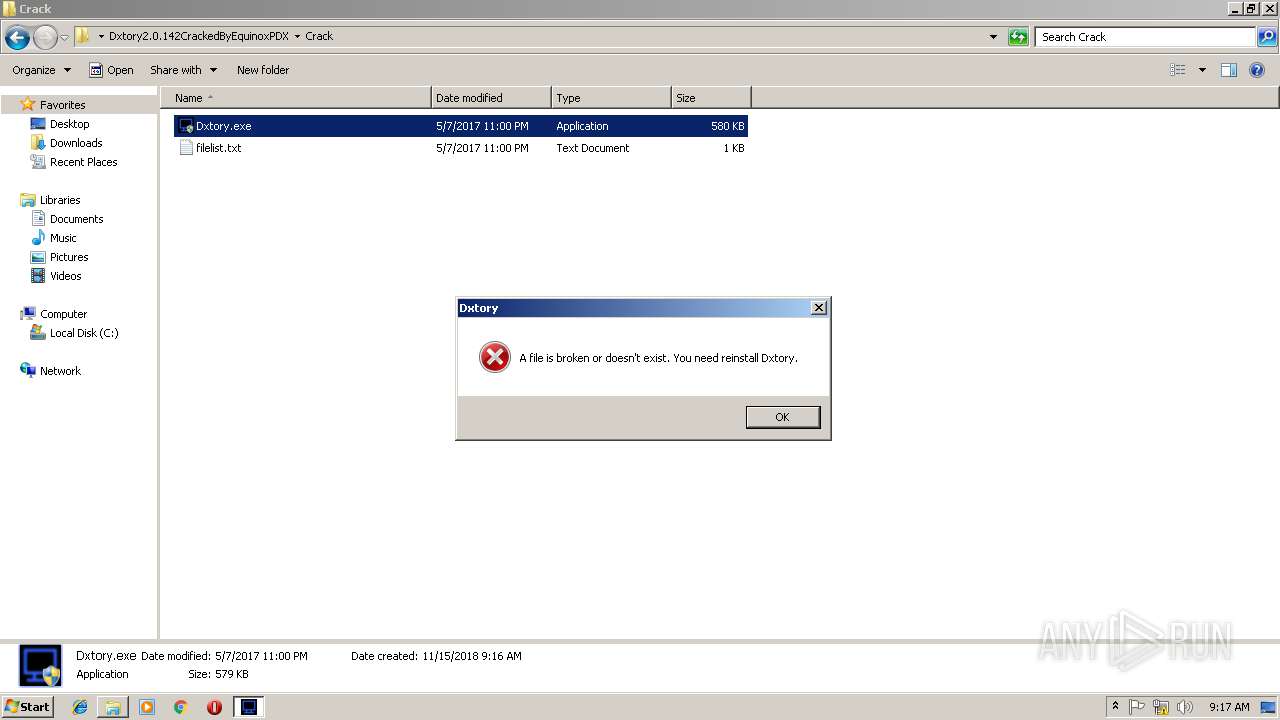
MALICIOUS
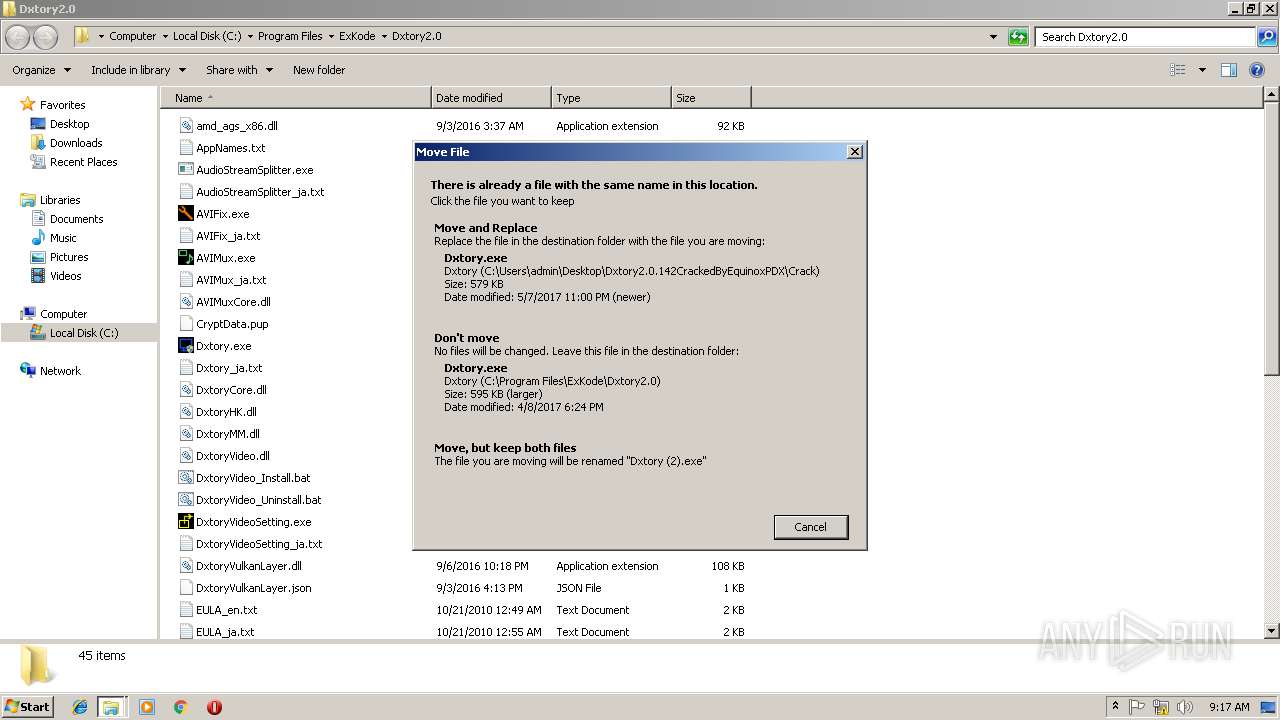
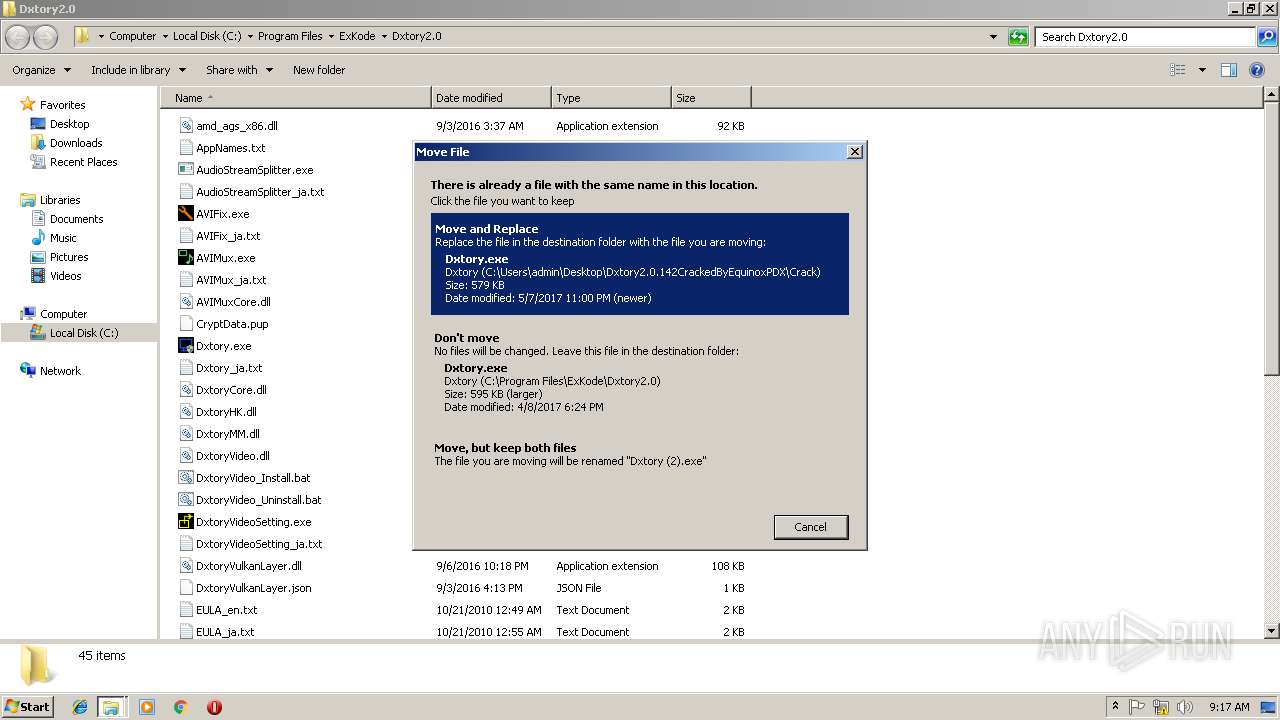
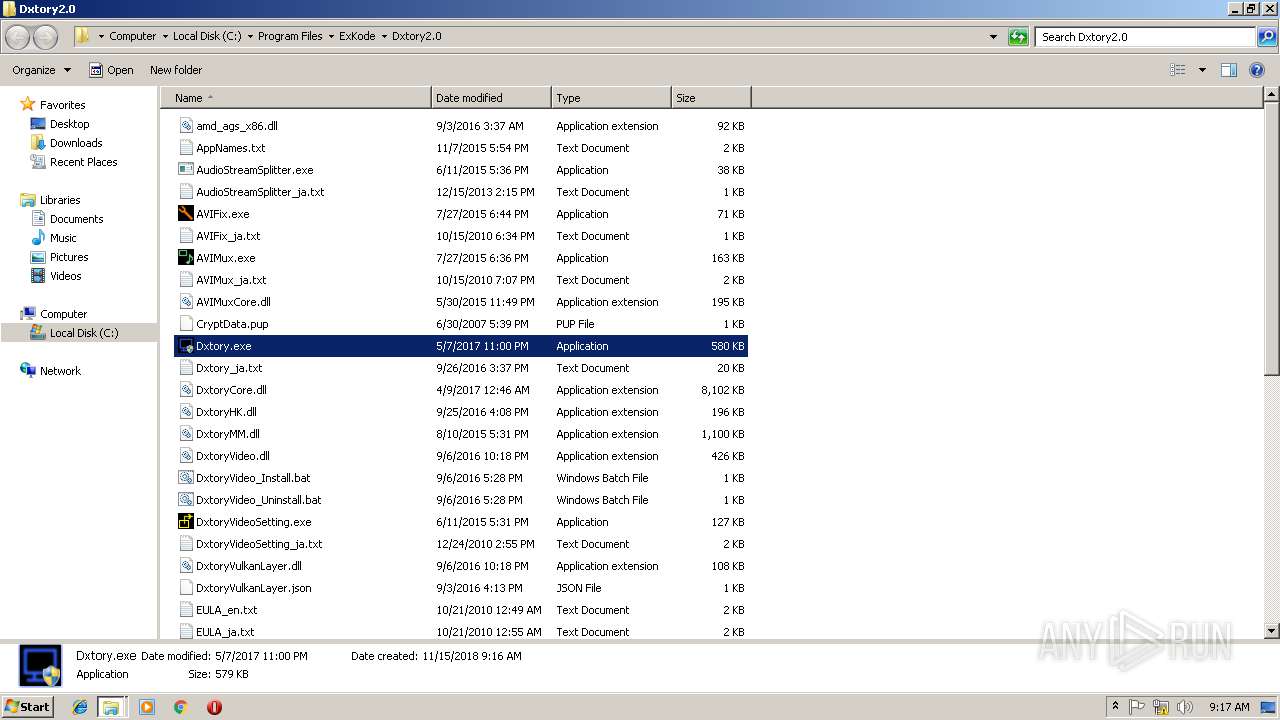
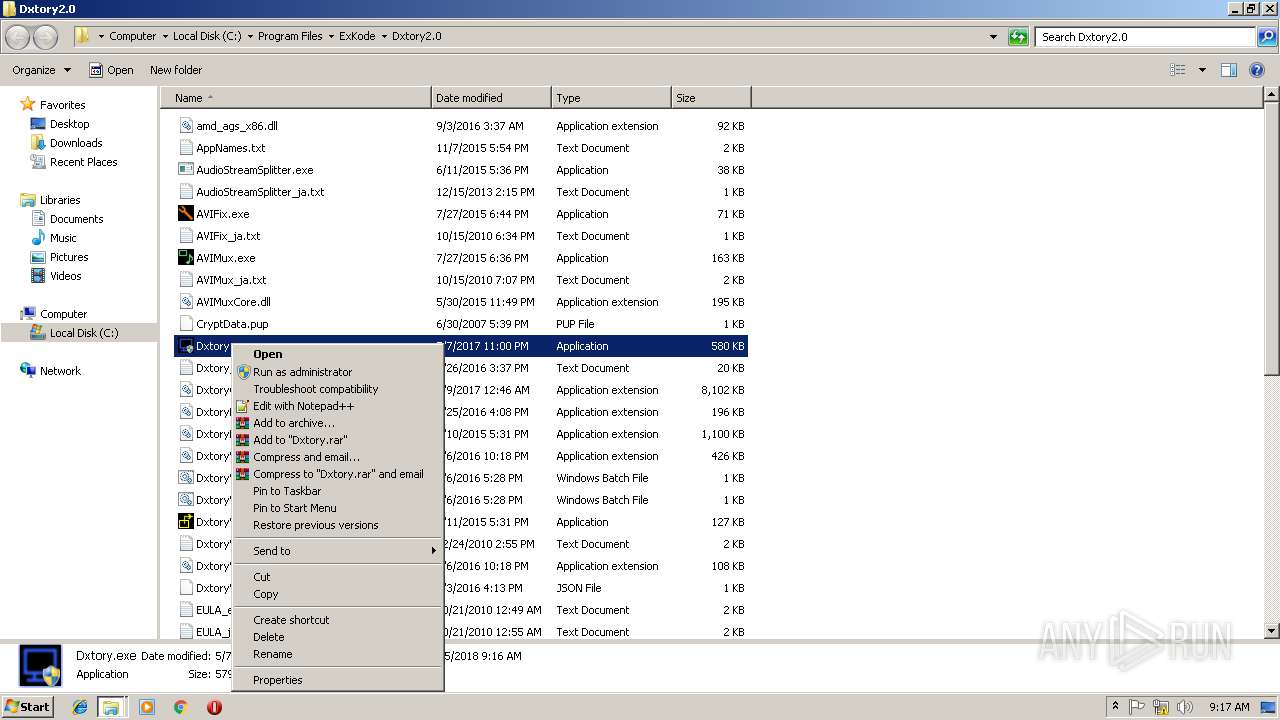
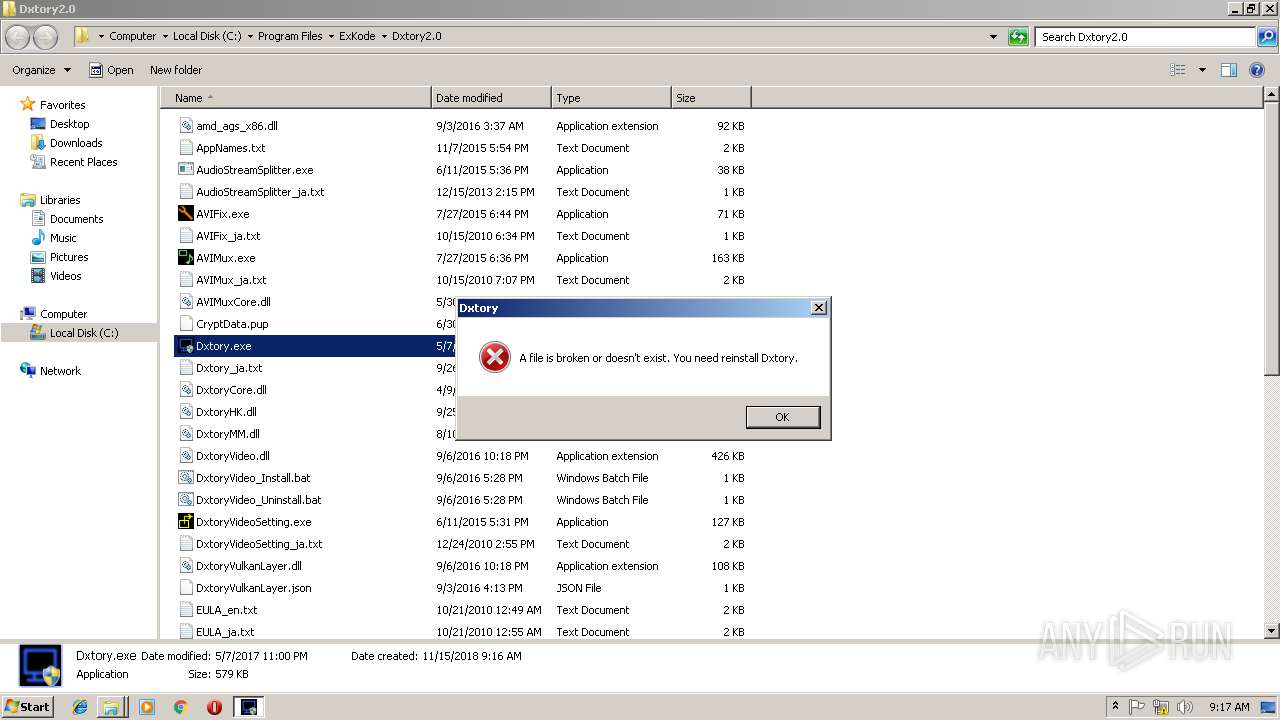
Application was dropped or rewritten from another process
- DxtorySetup2.0.142.exe (PID: 3172)
- Dxtory.exe (PID: 2492)
- DxtorySetup2.0.142.exe (PID: 3436)
- Dxtory.exe (PID: 1816)
- Dxtory.exe (PID: 3664)
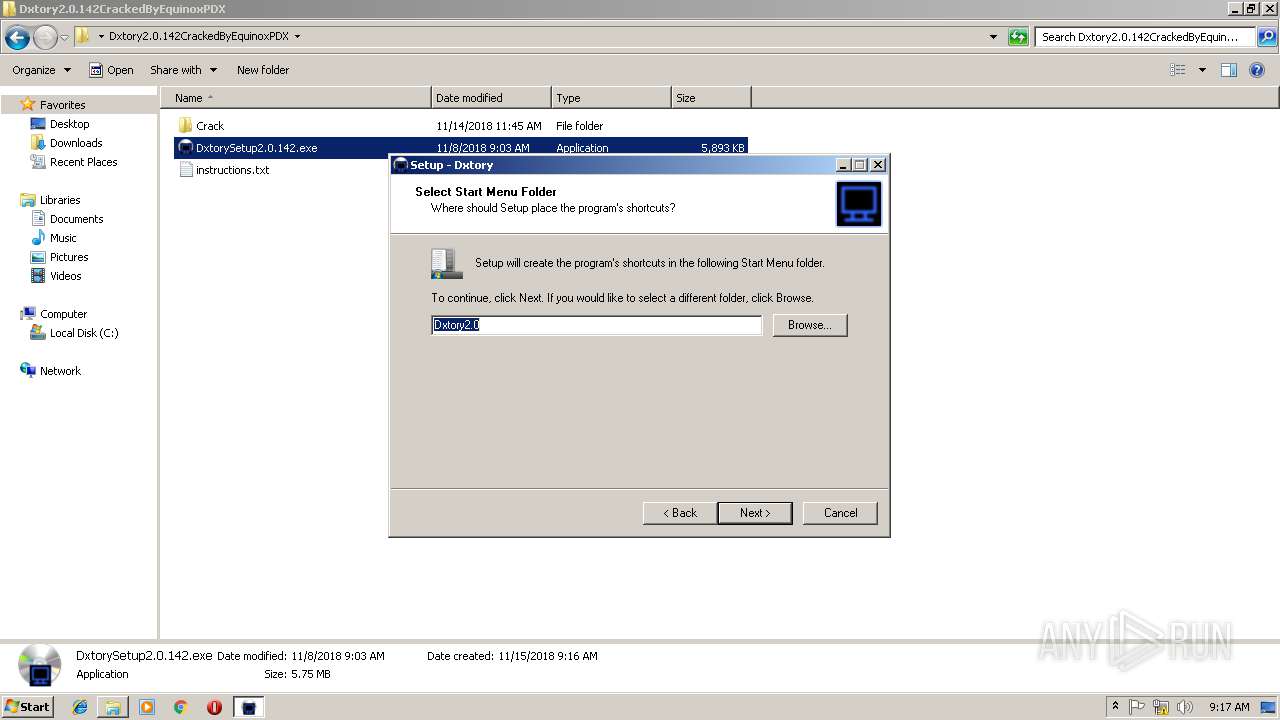
Registers / Runs the DLL via REGSVR32.EXE
- DxtorySetup2.0.142.tmp (PID: 3760)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2500)
- rundll32.exe (PID: 4072)
- regsvr32.exe (PID: 3596)
- Dxtory.exe (PID: 3664)
- rundll32.exe (PID: 3420)
- rundll32.exe (PID: 2880)
Changes the autorun value in the registry
- DxtorySetup2.0.142.tmp (PID: 3760)
SUSPICIOUS
Executable content was dropped or overwritten
- DxtorySetup2.0.142.exe (PID: 3172)
- WinRAR.exe (PID: 3404)
- DxtorySetup2.0.142.exe (PID: 3436)
- DllHost.exe (PID: 3204)
- DxtorySetup2.0.142.tmp (PID: 3760)
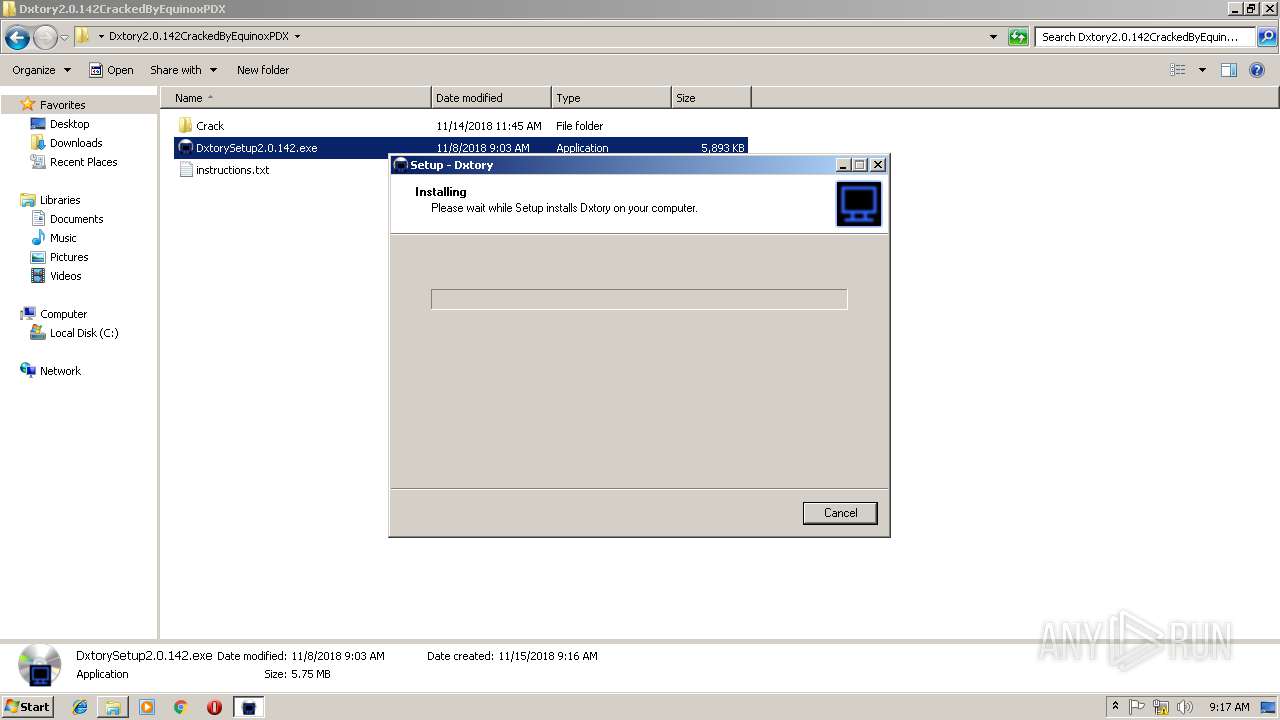
Reads Windows owner or organization settings
- DxtorySetup2.0.142.tmp (PID: 3760)
Creates files in the Windows directory
- DxtorySetup2.0.142.tmp (PID: 3760)
Creates COM task schedule object
- regsvr32.exe (PID: 2500)
- regsvr32.exe (PID: 3596)
Uses RUNDLL32.EXE to load library
- DxtorySetup2.0.142.tmp (PID: 3760)
Creates files in the user directory
- Dxtory.exe (PID: 1816)
Reads the Windows organization settings
- DxtorySetup2.0.142.tmp (PID: 3760)
Modifies the open verb of a shell class
- DxtorySetup2.0.142.tmp (PID: 3760)
INFO
Application was dropped or rewritten from another process
- DxtorySetup2.0.142.tmp (PID: 3992)
- DxtorySetup2.0.142.tmp (PID: 3760)
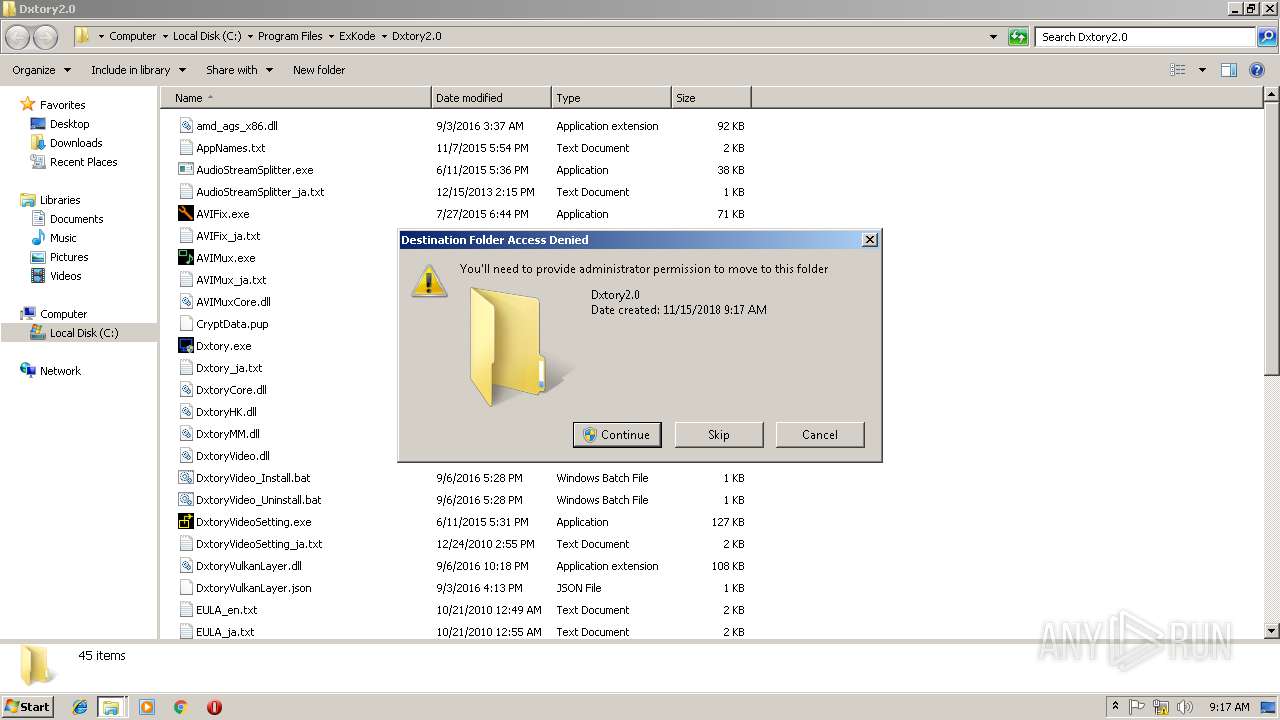
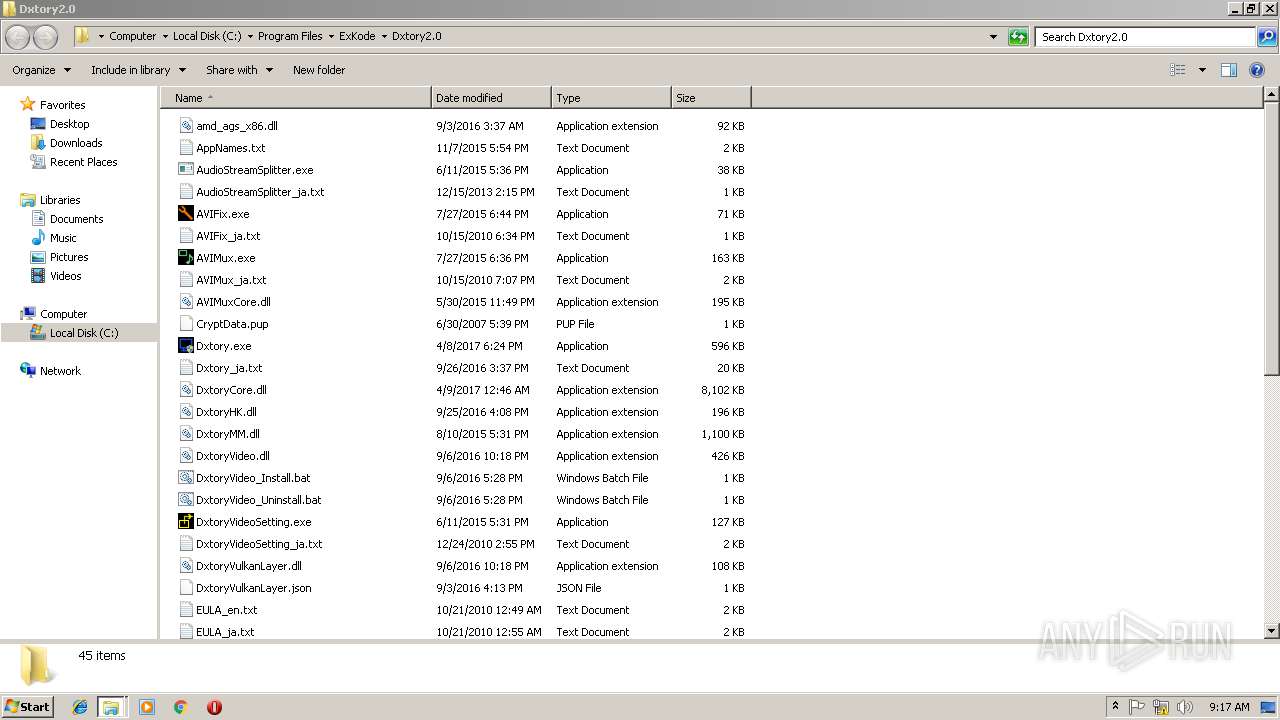
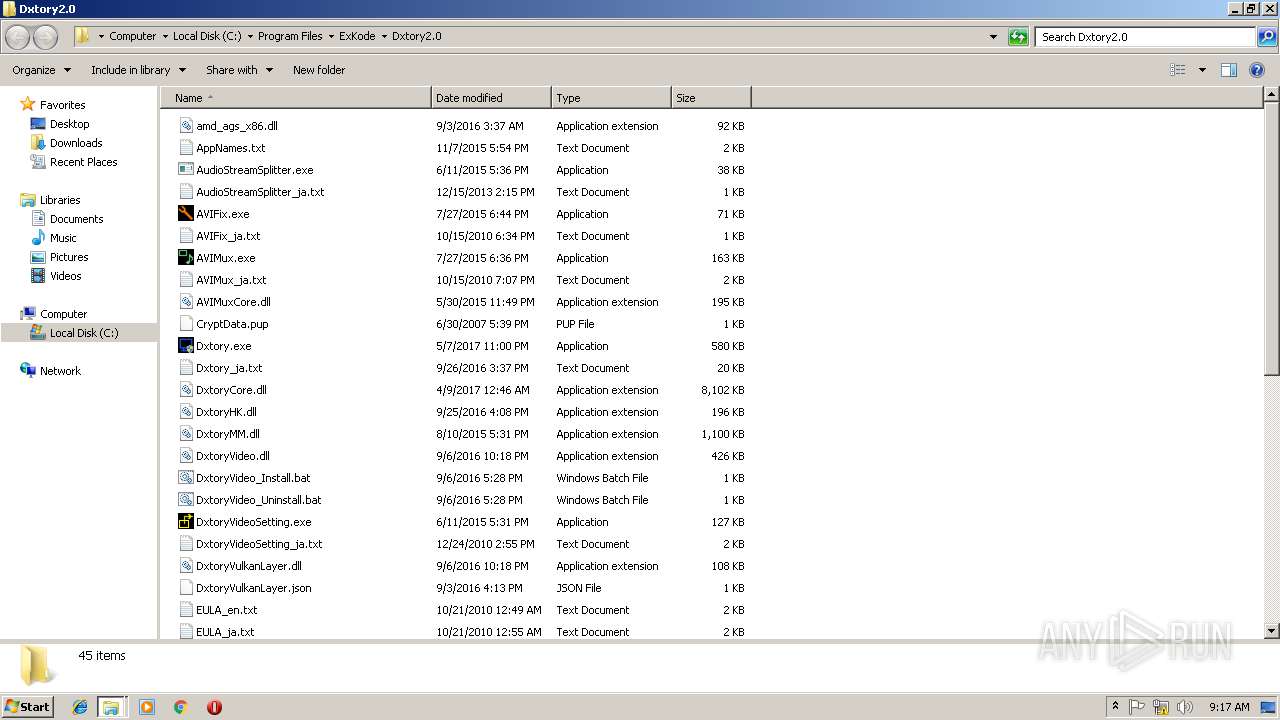
Creates files in the program directory
- DxtorySetup2.0.142.tmp (PID: 3760)
Creates a software uninstall entry
- DxtorySetup2.0.142.tmp (PID: 3760)
Loads dropped or rewritten executable
- DxtorySetup2.0.142.tmp (PID: 3760)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:11:08 03:03:11 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Dxtory2.0.142CrackedByEquinoxPDX/ |
Total processes
63
Monitored processes
14
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
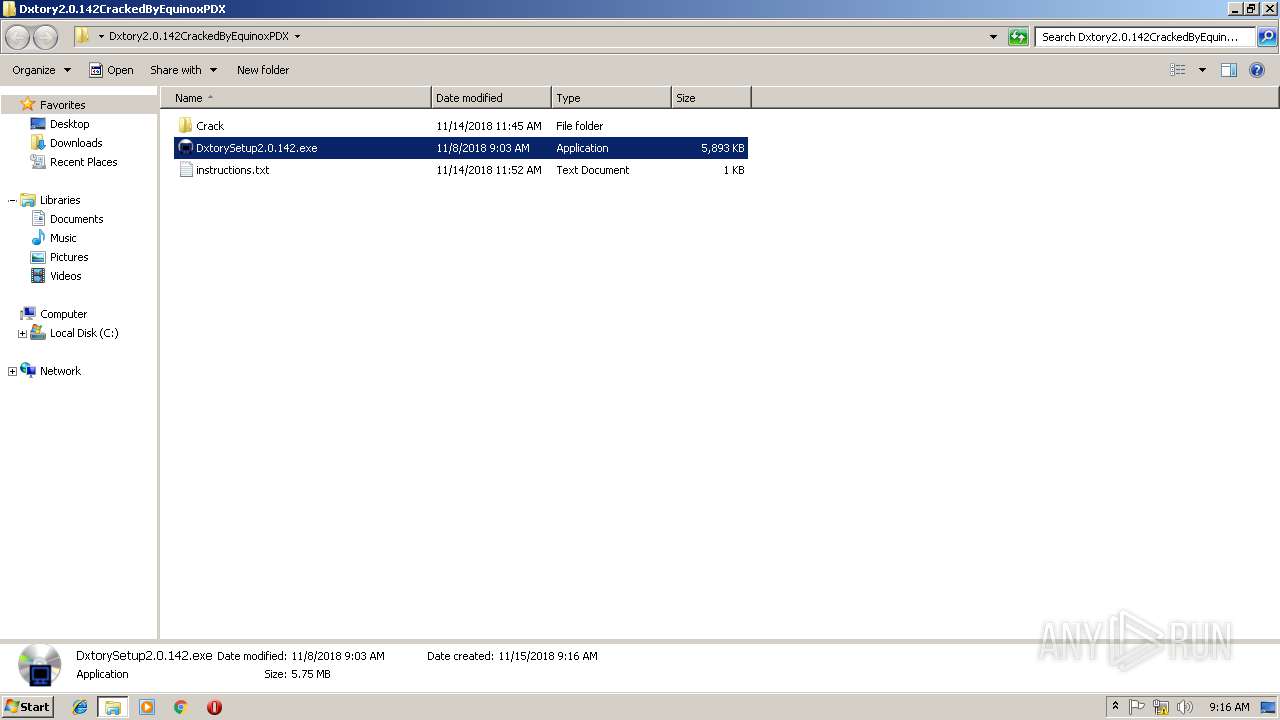
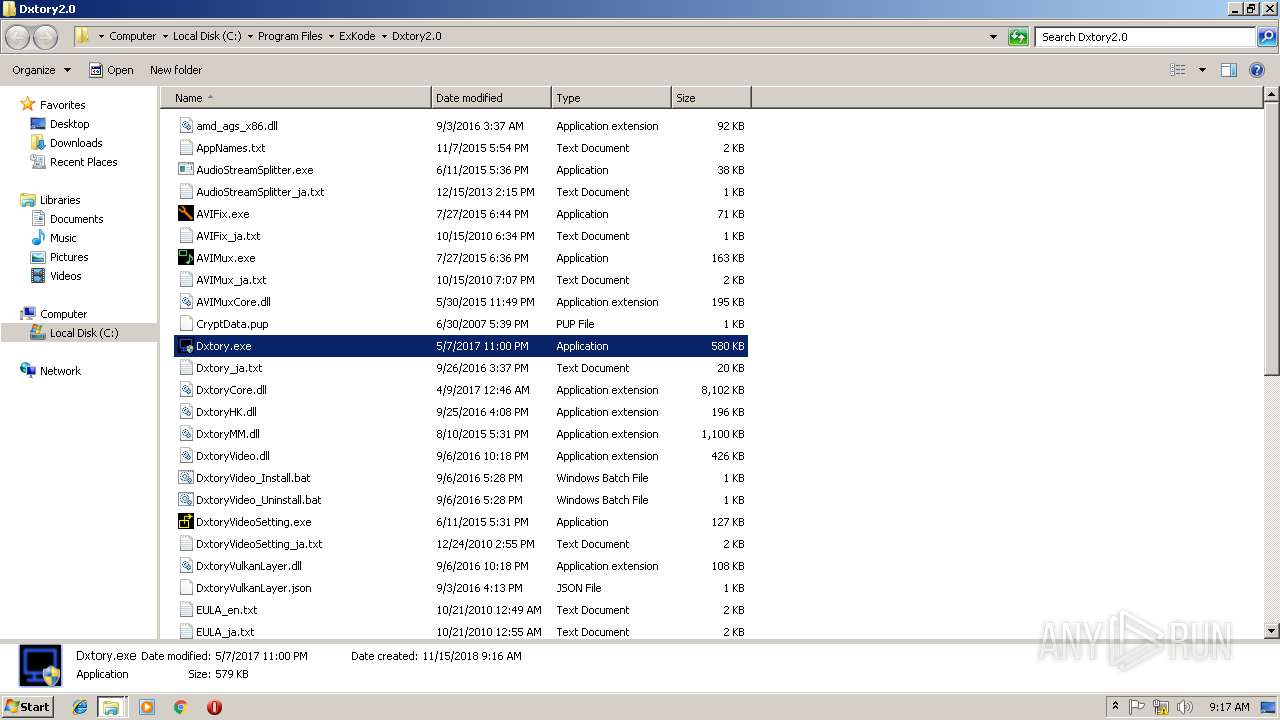
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
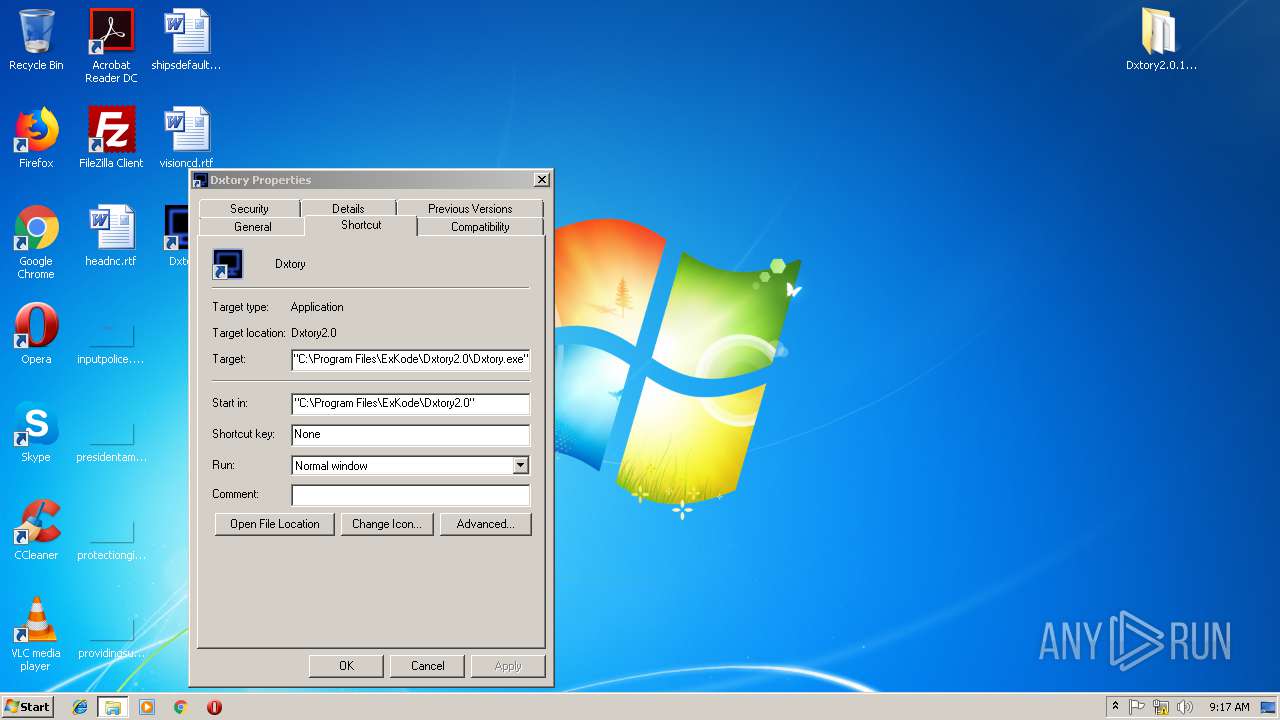
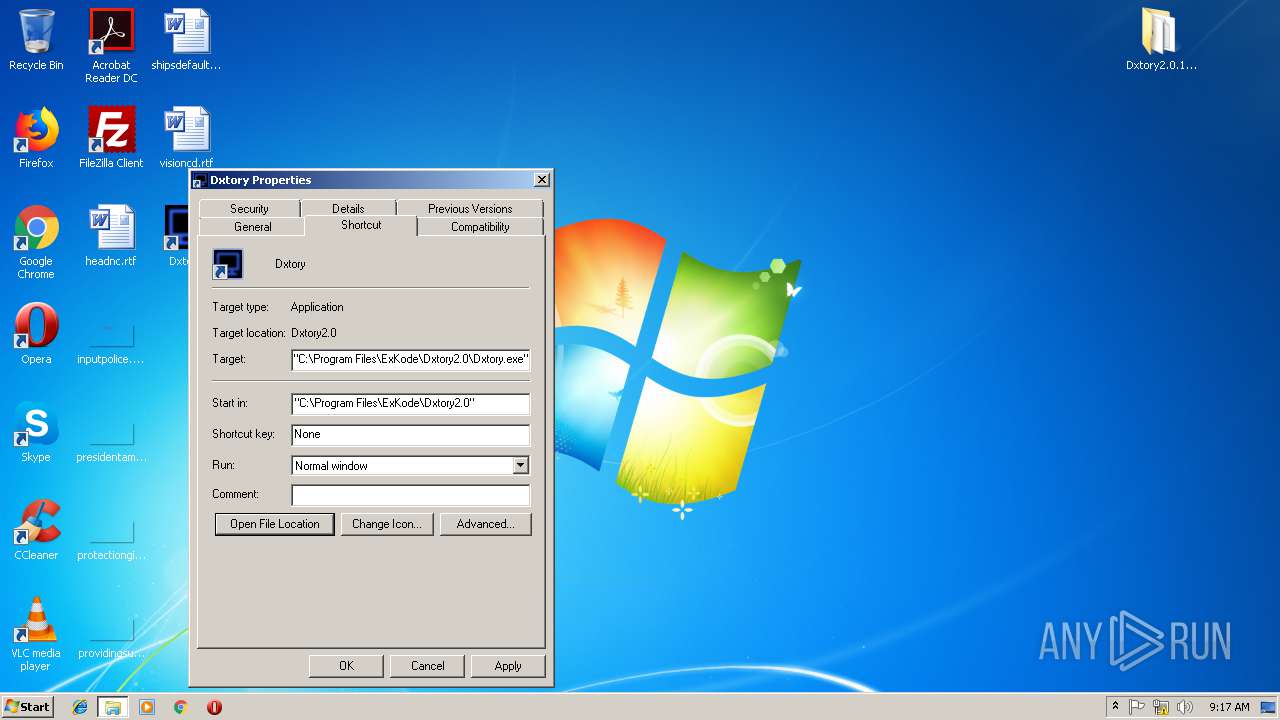
| 1816 | "C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe" /BUILD_JUMPLIST | C:\Program Files\ExKode\Dxtory2.0\Dxtory.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Exit code: 0 Version: 2.0.0.142 Modules
| |||||||||||||||
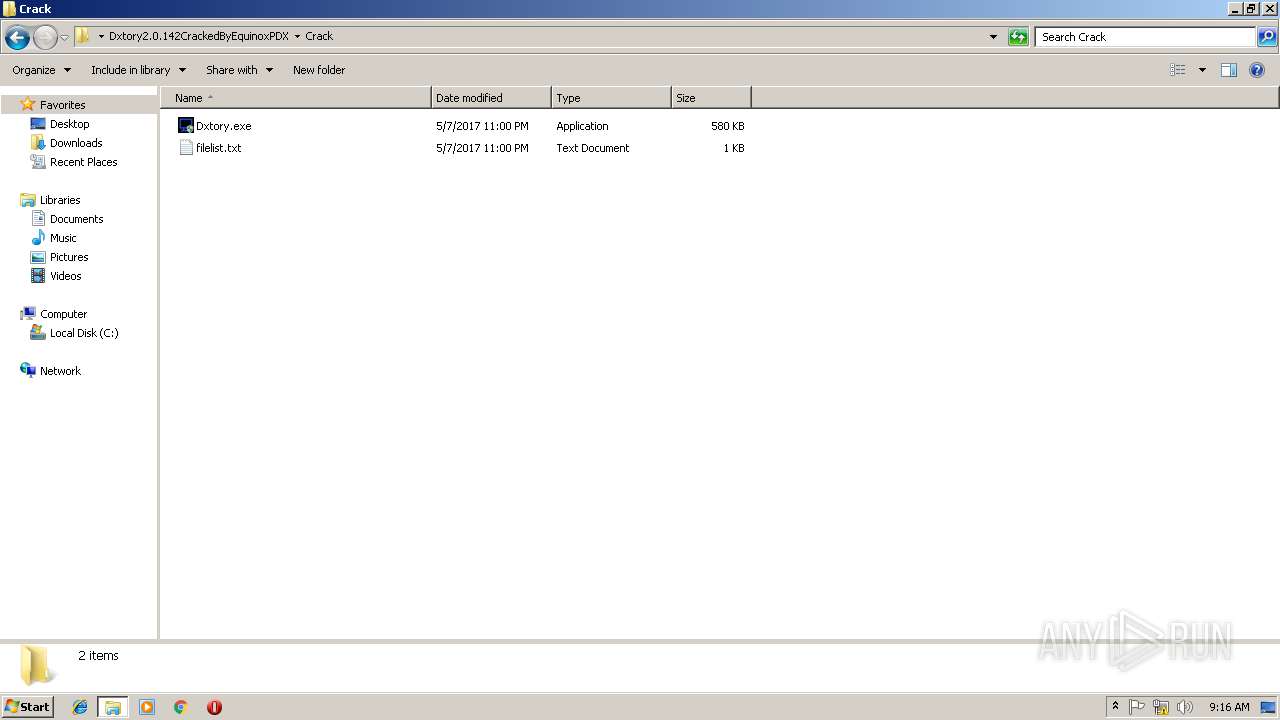
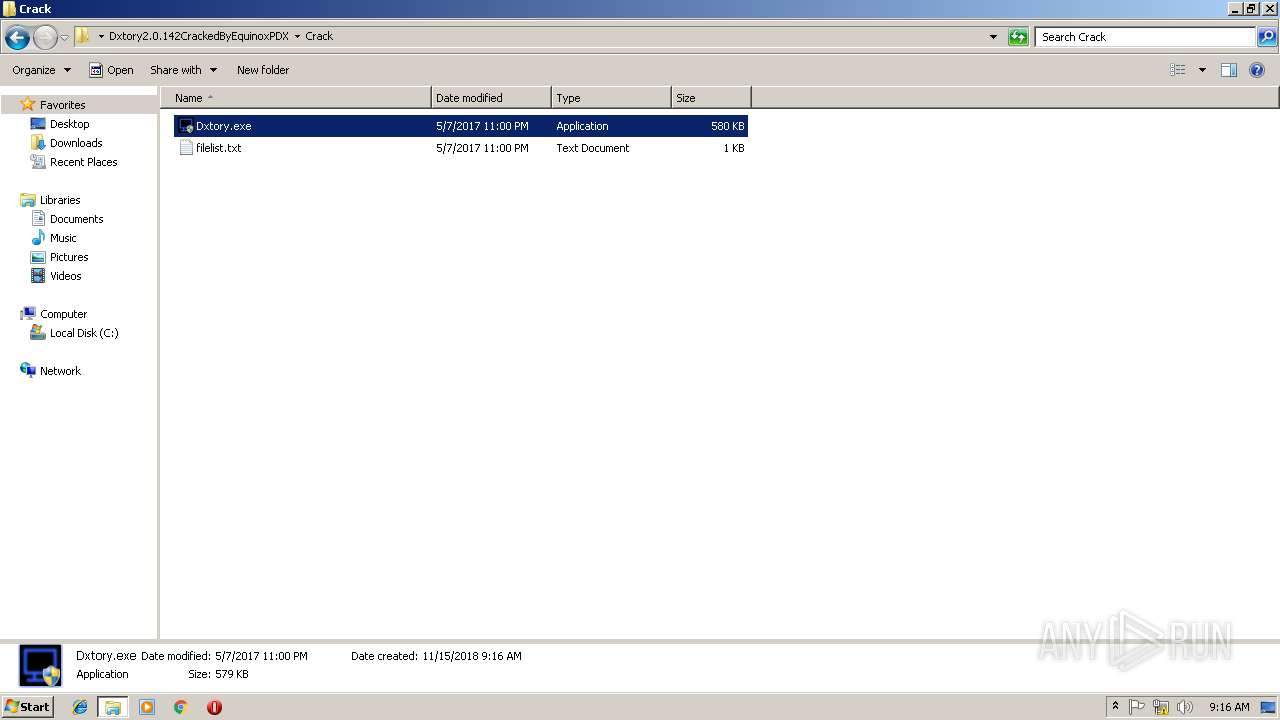
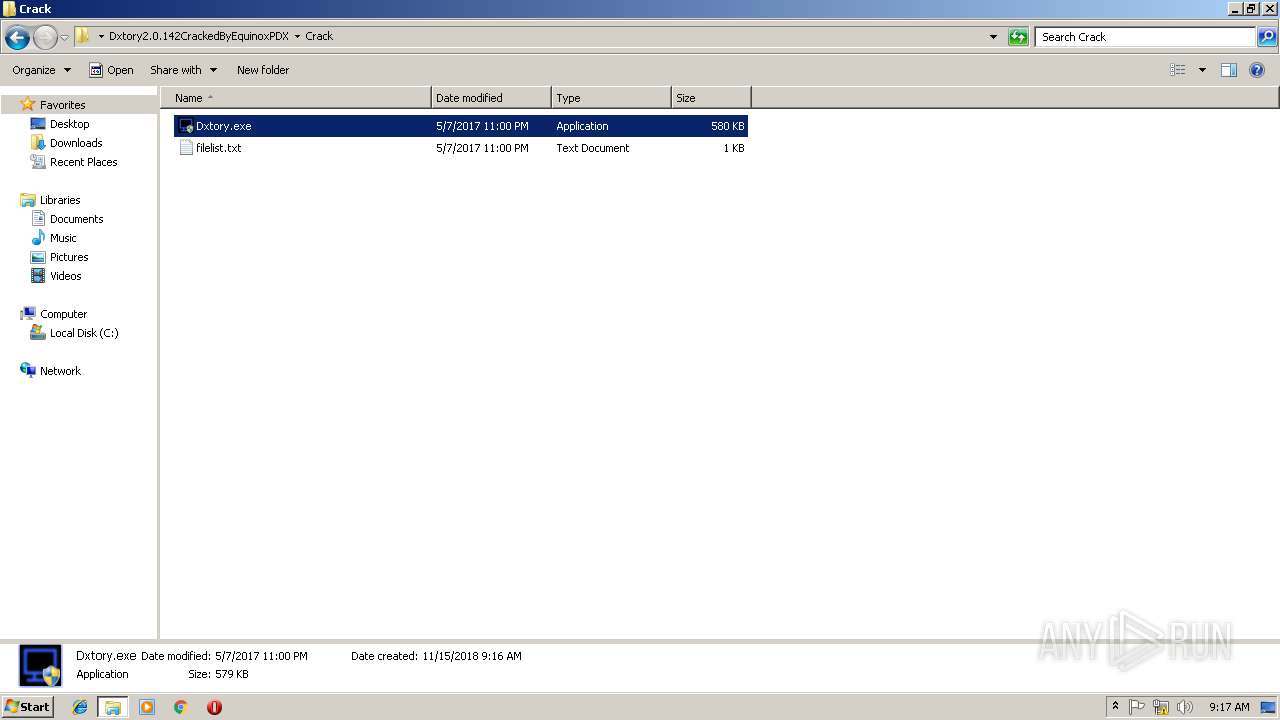
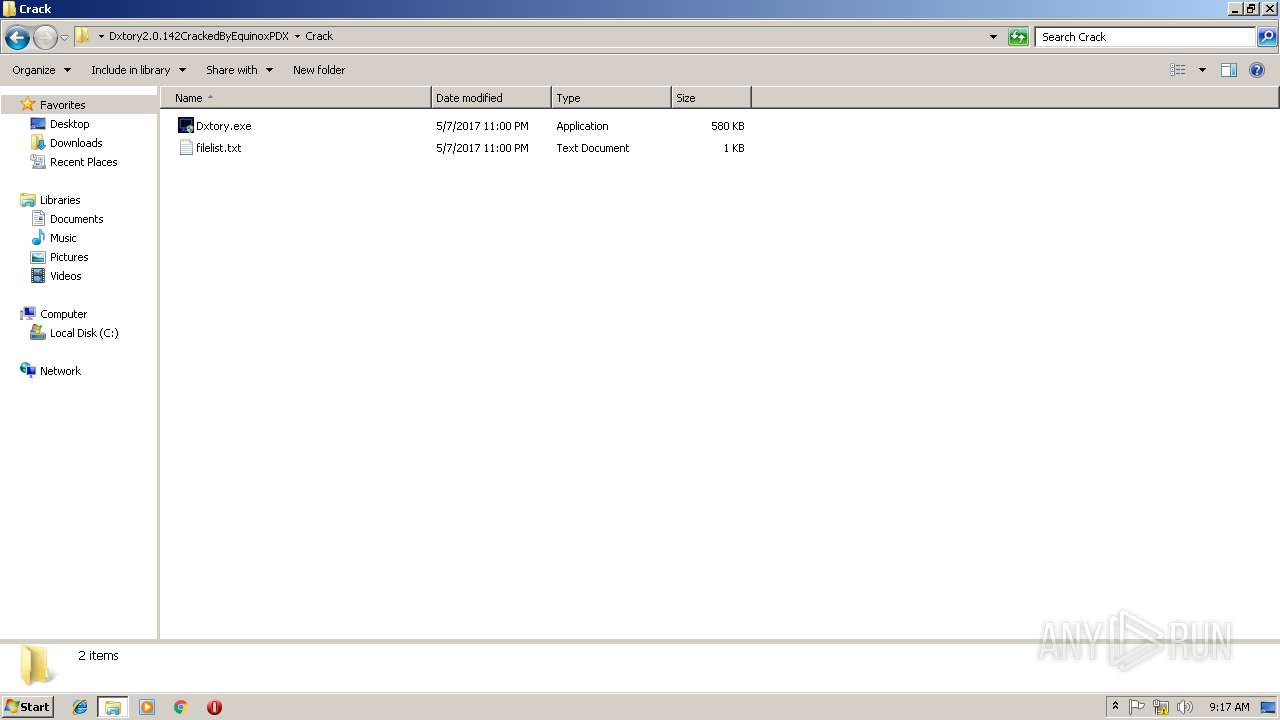
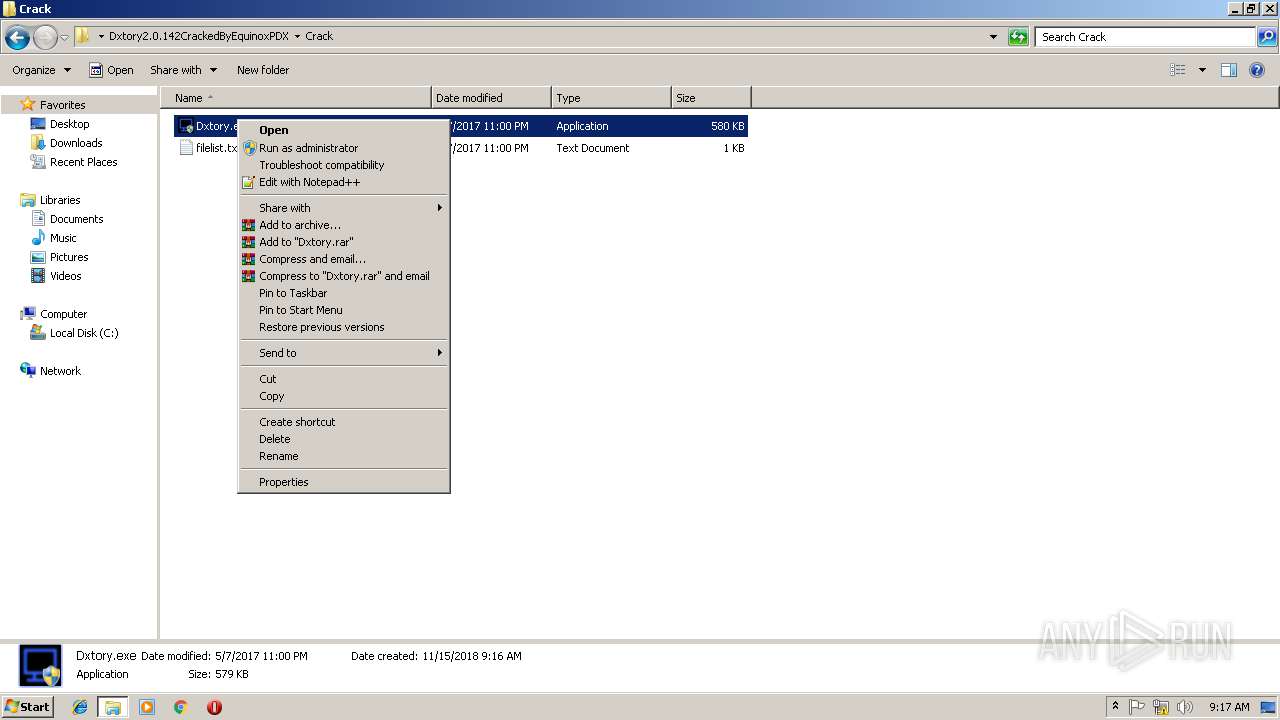
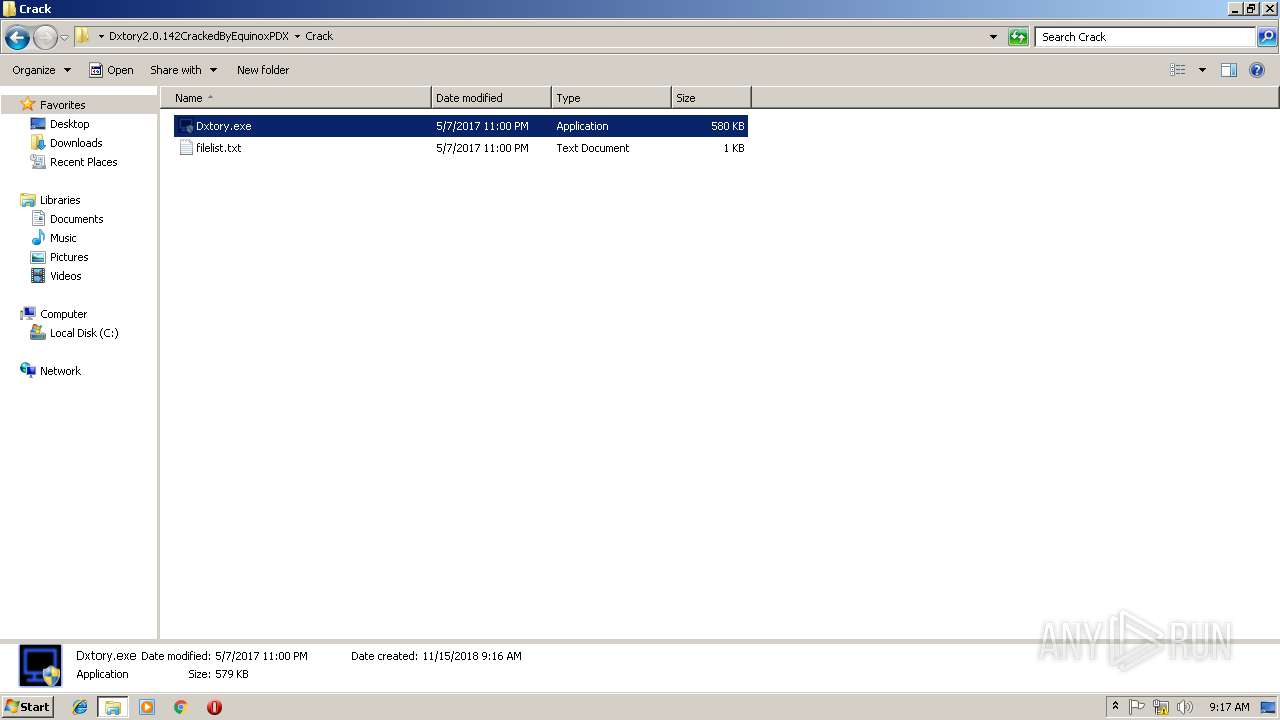
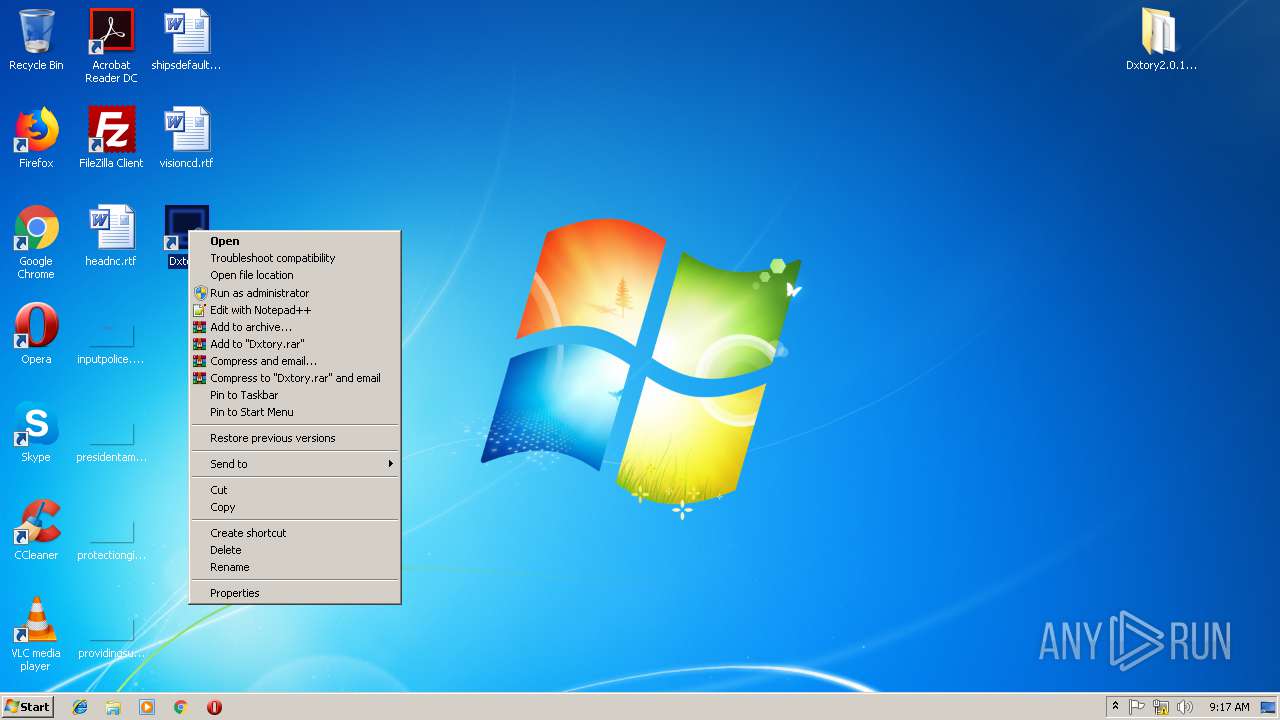
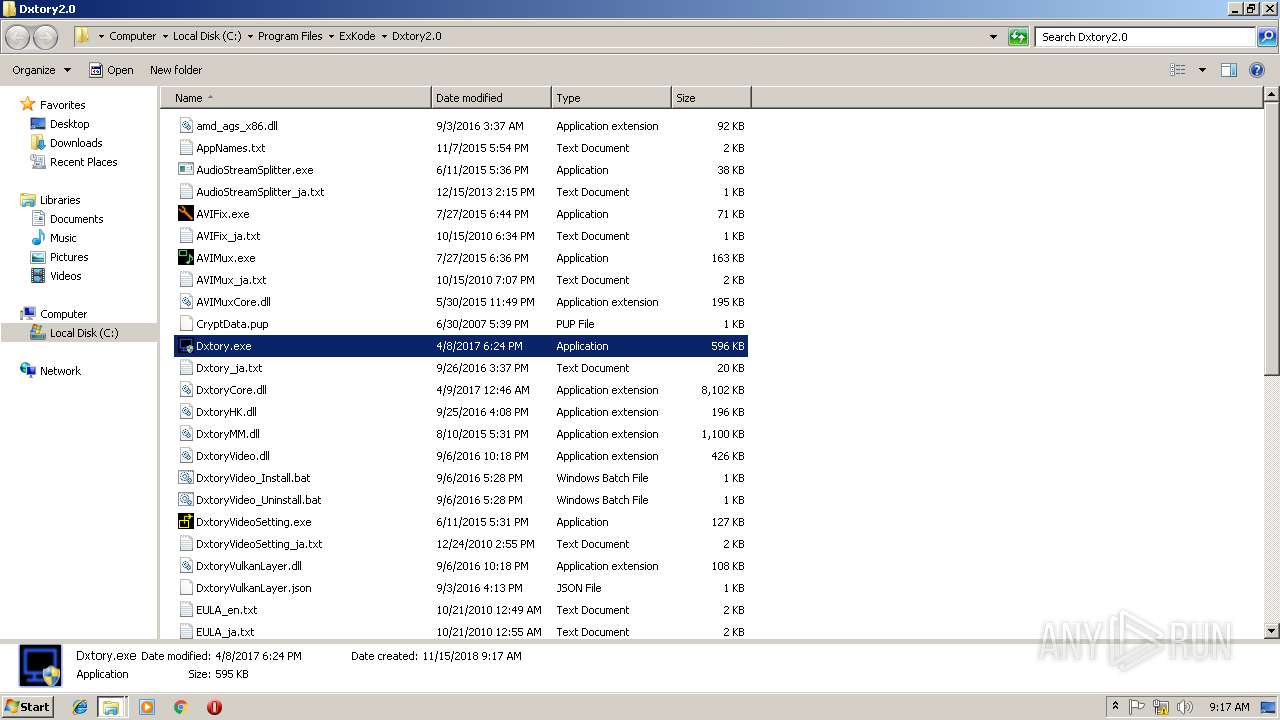
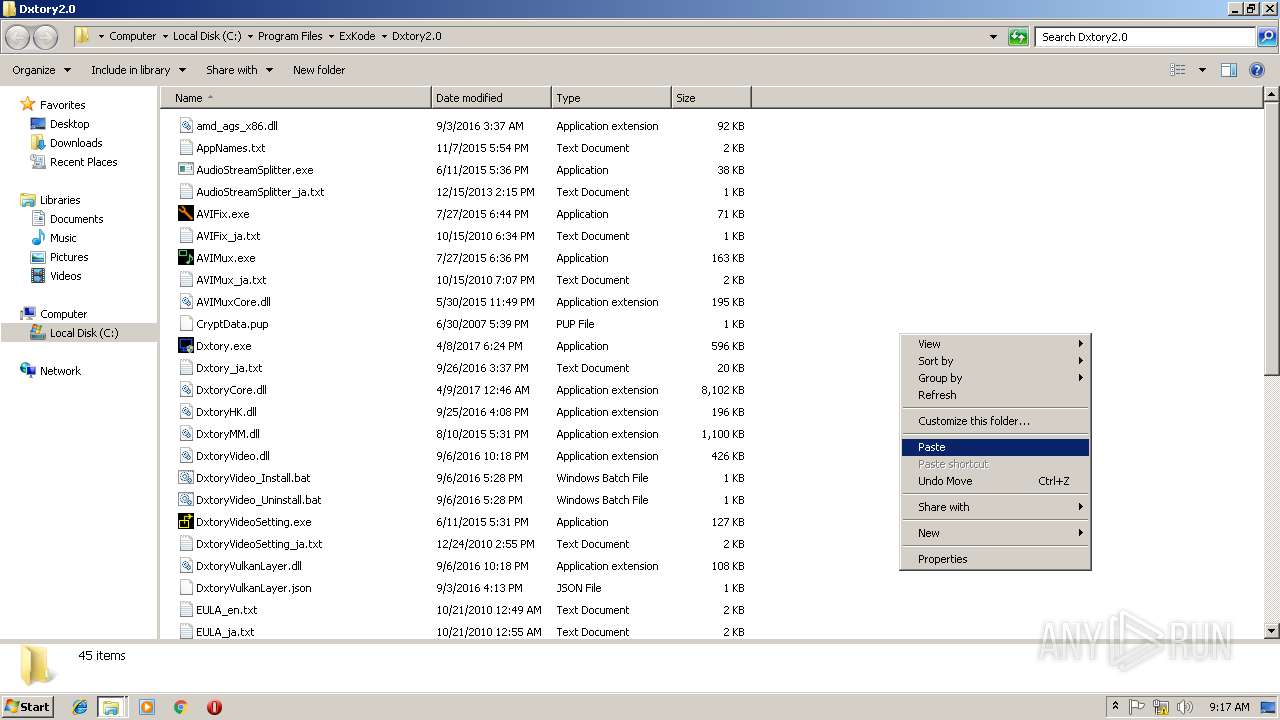
| 2492 | "C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\Crack\Dxtory.exe" | C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\Crack\Dxtory.exe | explorer.exe | ||||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Exit code: 0 Version: 2.0.0.142 Modules
| |||||||||||||||
| 2500 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\ExKode\Dxtory2.0\DxtoryVideo.dll" | C:\Windows\system32\regsvr32.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2880 | "C:\Windows\system32\rundll32.exe" DxtoryCodec.dll,InstallCodec | C:\Windows\system32\rundll32.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
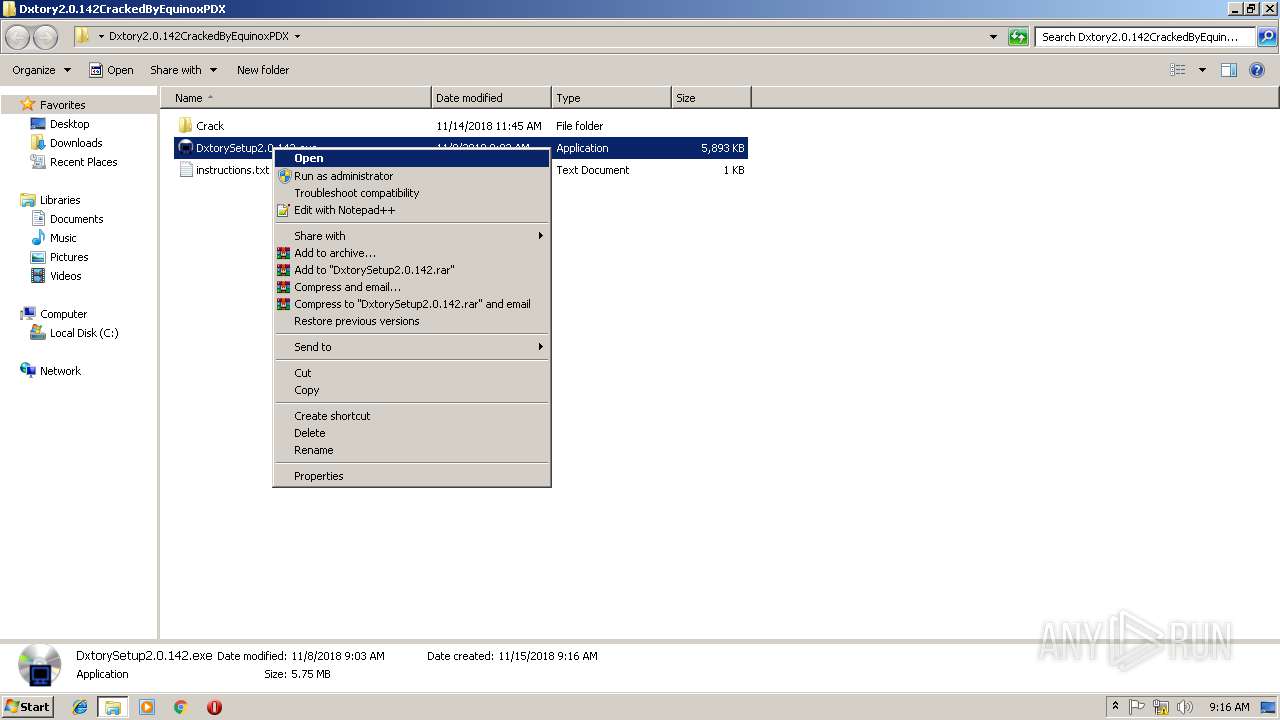
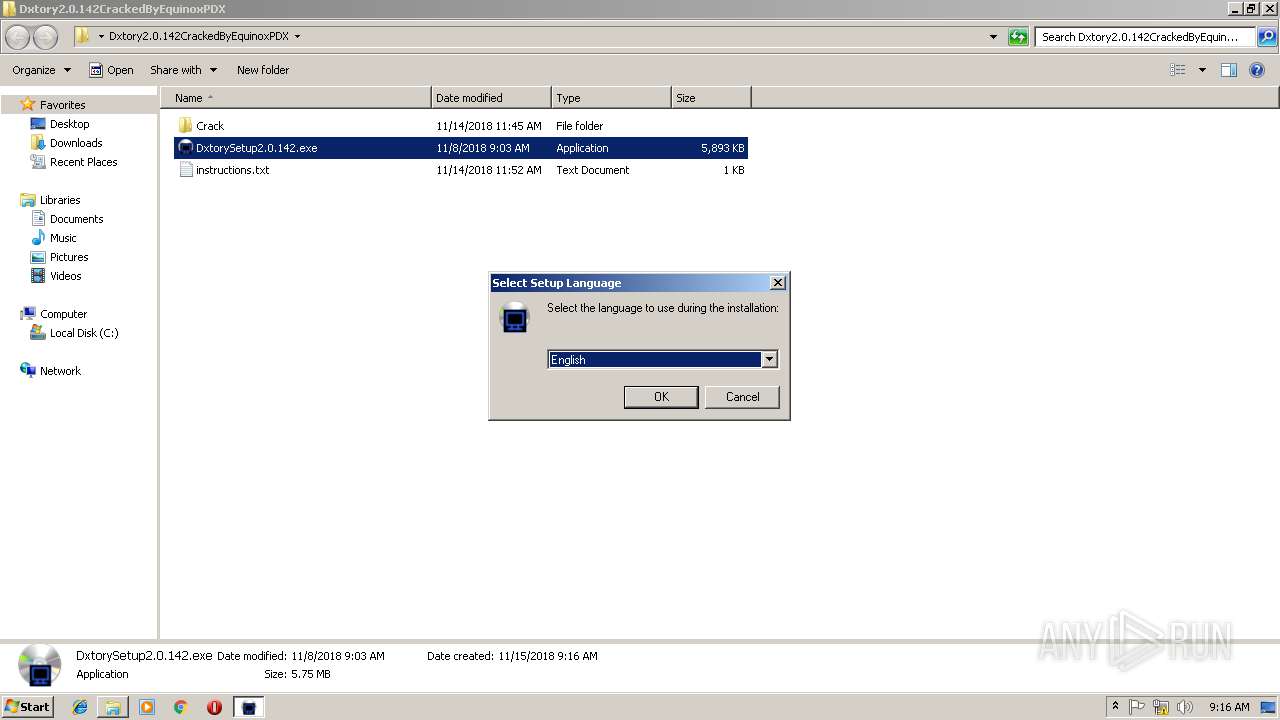
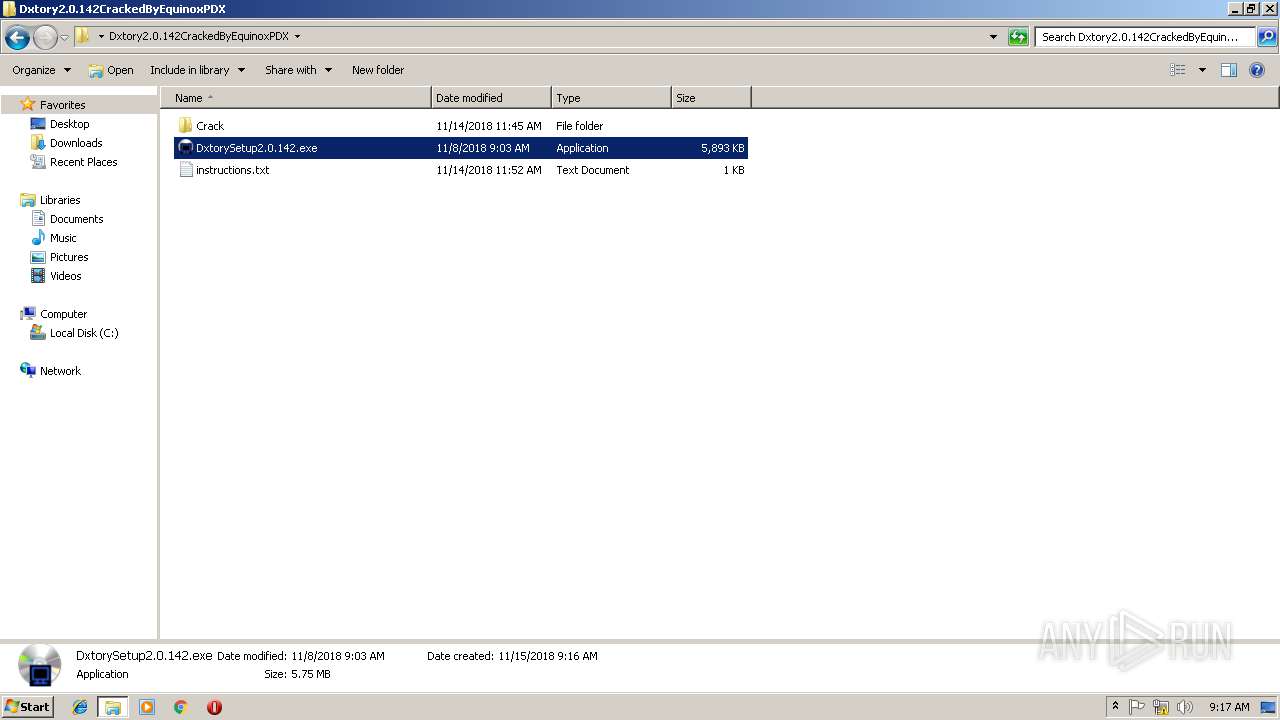
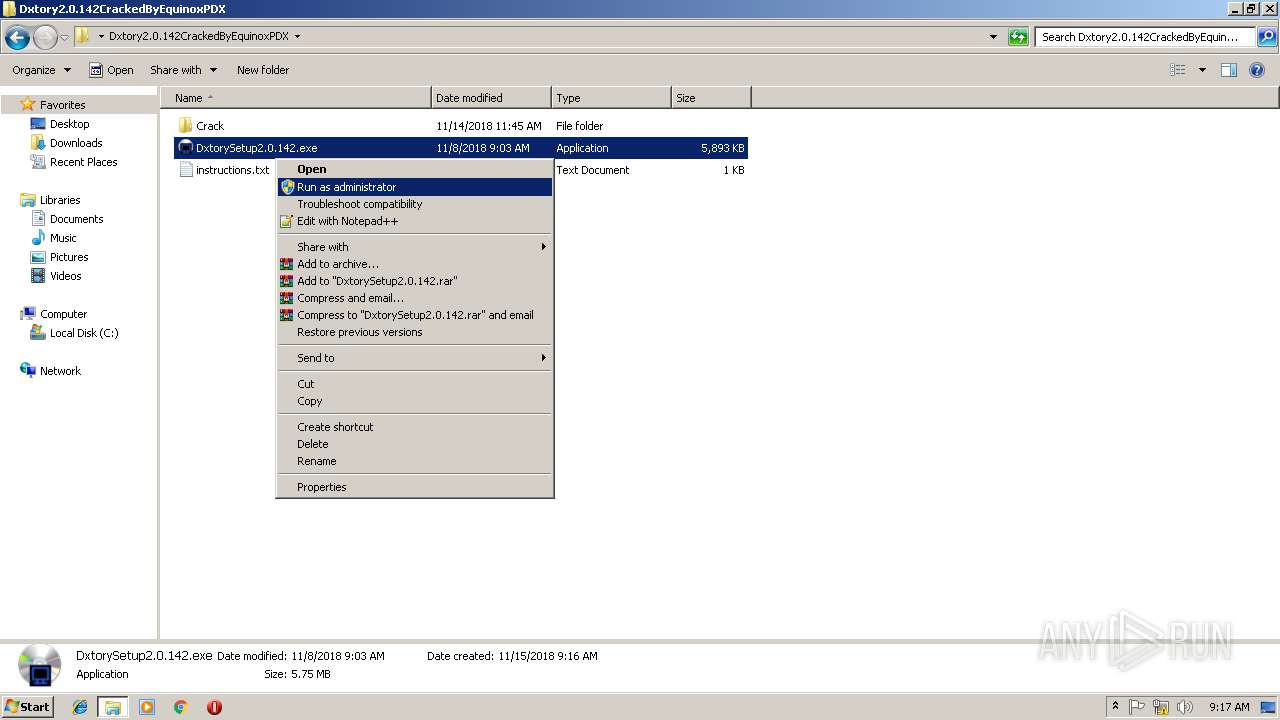
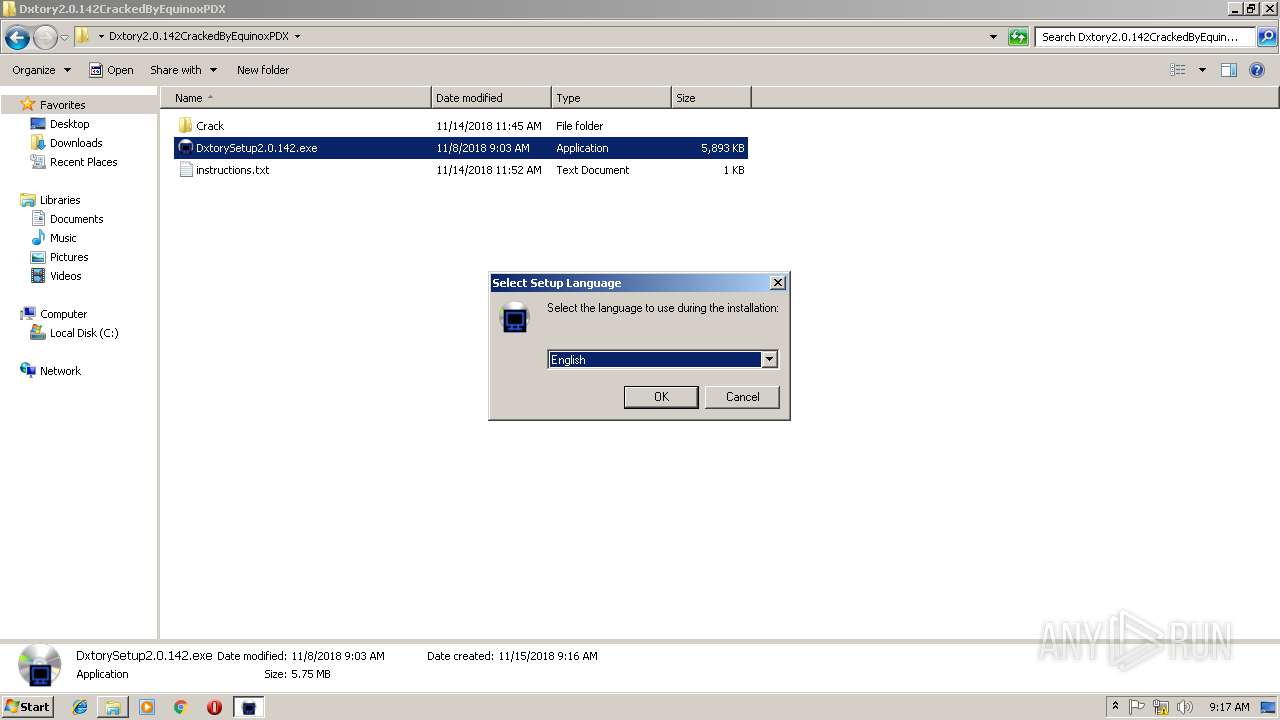
| 3172 | "C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\DxtorySetup2.0.142.exe" | C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\DxtorySetup2.0.142.exe | explorer.exe | ||||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Setup Exit code: 1 Version: Modules
| |||||||||||||||
| 3204 | C:\Windows\system32\DllHost.exe /Processid:{3AD05575-8857-4850-9277-11B85BDB8E09} | C:\Windows\system32\DllHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
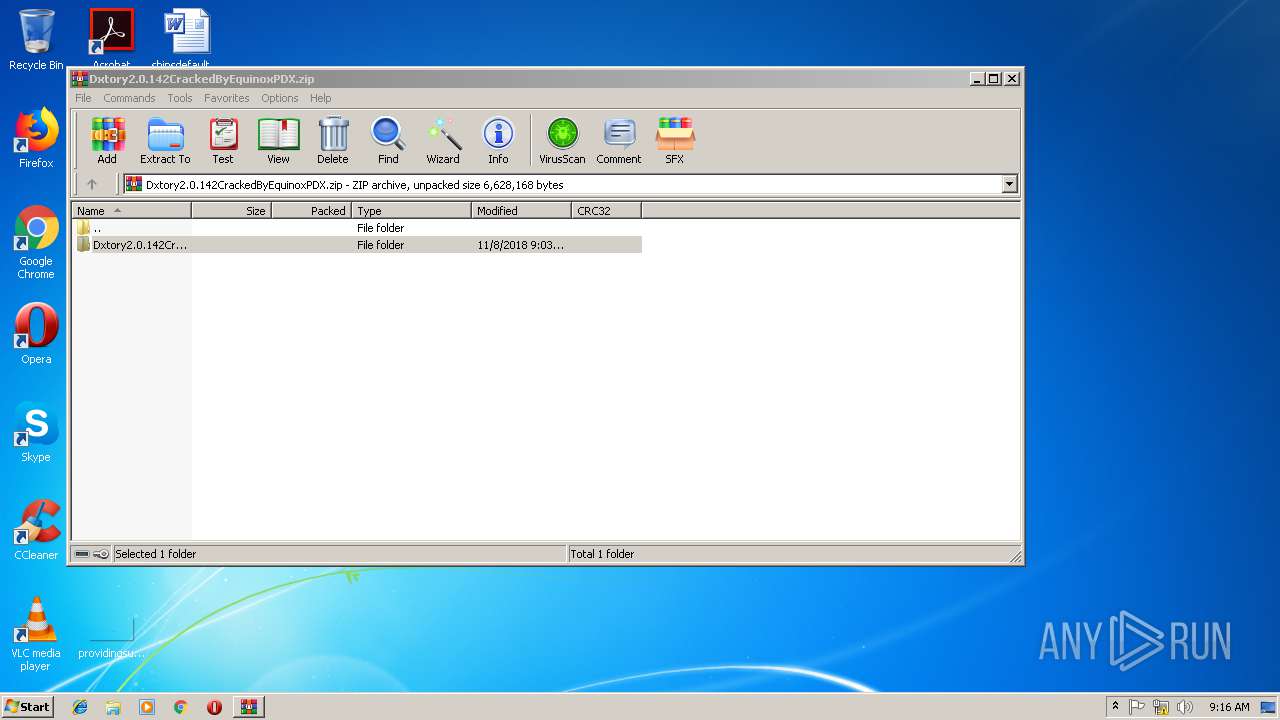
| 3404 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Dxtory2.0.142CrackedByEquinoxPDX.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3420 | "C:\Windows\system32\rundll32.exe" "C:\Program Files\ExKode\Dxtory2.0\DxtoryCore.dll",DxCore_InitInterfaceInfo | C:\Windows\system32\rundll32.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
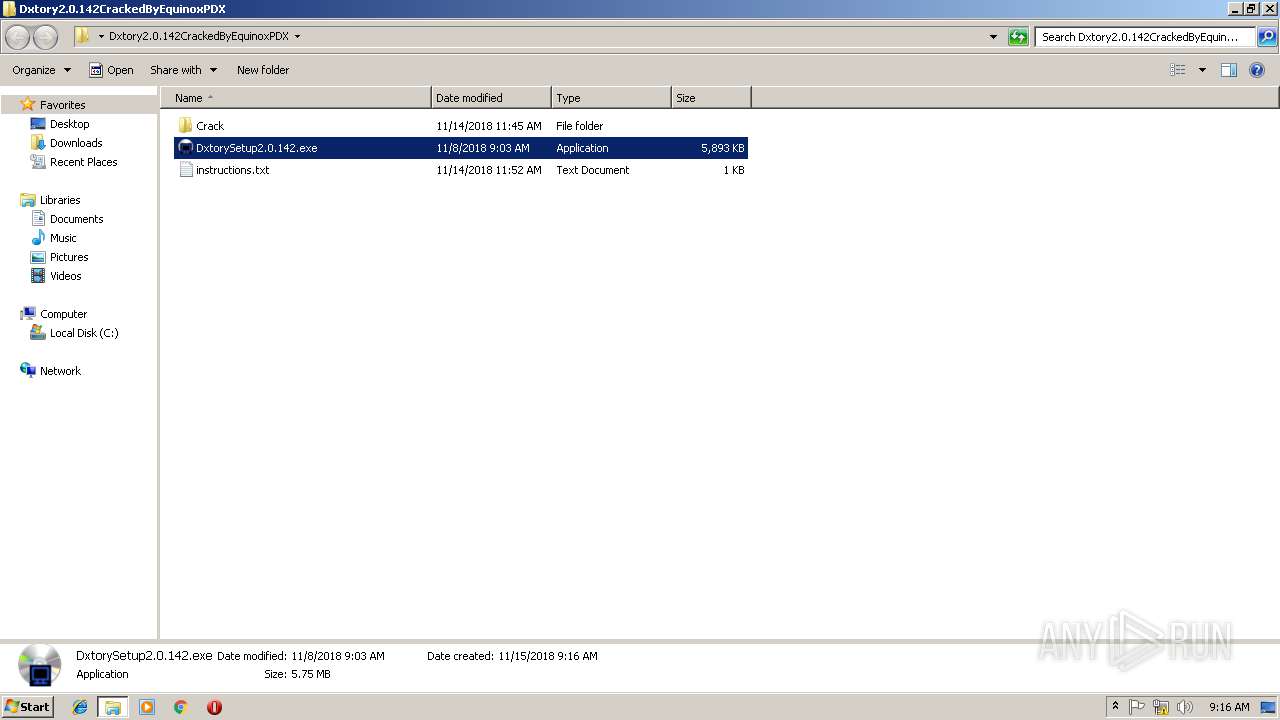
| 3436 | "C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\DxtorySetup2.0.142.exe" | C:\Users\admin\Desktop\Dxtory2.0.142CrackedByEquinoxPDX\DxtorySetup2.0.142.exe | explorer.exe | ||||||||||||
User: admin Company: ExKode Co. Ltd. Integrity Level: HIGH Description: Dxtory Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3596 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\DxtoryCodec.dll" | C:\Windows\system32\regsvr32.exe | — | DxtorySetup2.0.142.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 021
Read events
866
Write events
149
Delete events
6
Modification events
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Dxtory2.0.142CrackedByEquinoxPDX.zip | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (3404) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
26
Suspicious files
4
Text files
25
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-HJH0P.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-R7R54.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-KFI84.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-5M3PB.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-V0PQN.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-BR7PO.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-EOKE8.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-VATIV.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-8951N.tmp | — | |
MD5:— | SHA256:— | |||
| 3760 | DxtorySetup2.0.142.tmp | C:\Program Files\ExKode\Dxtory2.0\is-8DIVP.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report