| File name: | 16325-16325-16325-163250.doc |
| Full analysis: | https://app.any.run/tasks/5039dbfc-7b2e-42be-87d0-db71ae8ae4c7 |
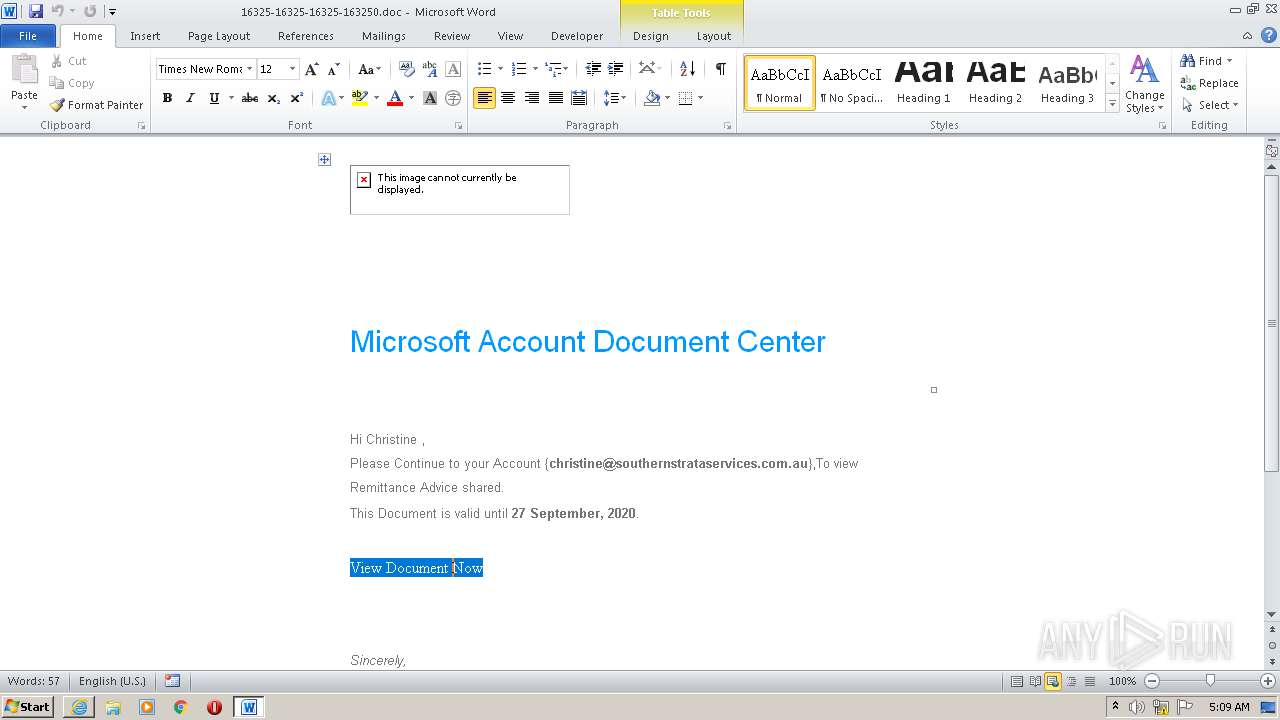
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 04:06:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | FB5F468EC0181F2A95F22EE8EC2EF130 |
| SHA1: | 07EE73E843C0148733EEA87CEC381A6038E7476E |
| SHA256: | 5ED6B9153000CB0B666DDB2D45ED660B4024B089FFC9CC577C8620DFD84D7732 |
| SSDEEP: | 768:hzpUQM4rt0+7QVbrFi+vC/7F5yGoJevr40xCZbZq5een0TEcm0Frrrveeeei6r4a:9rt0p5hajiGievr40gVw5een0TEcm0pv |
MALICIOUS
No malicious indicators.SUSPICIOUS
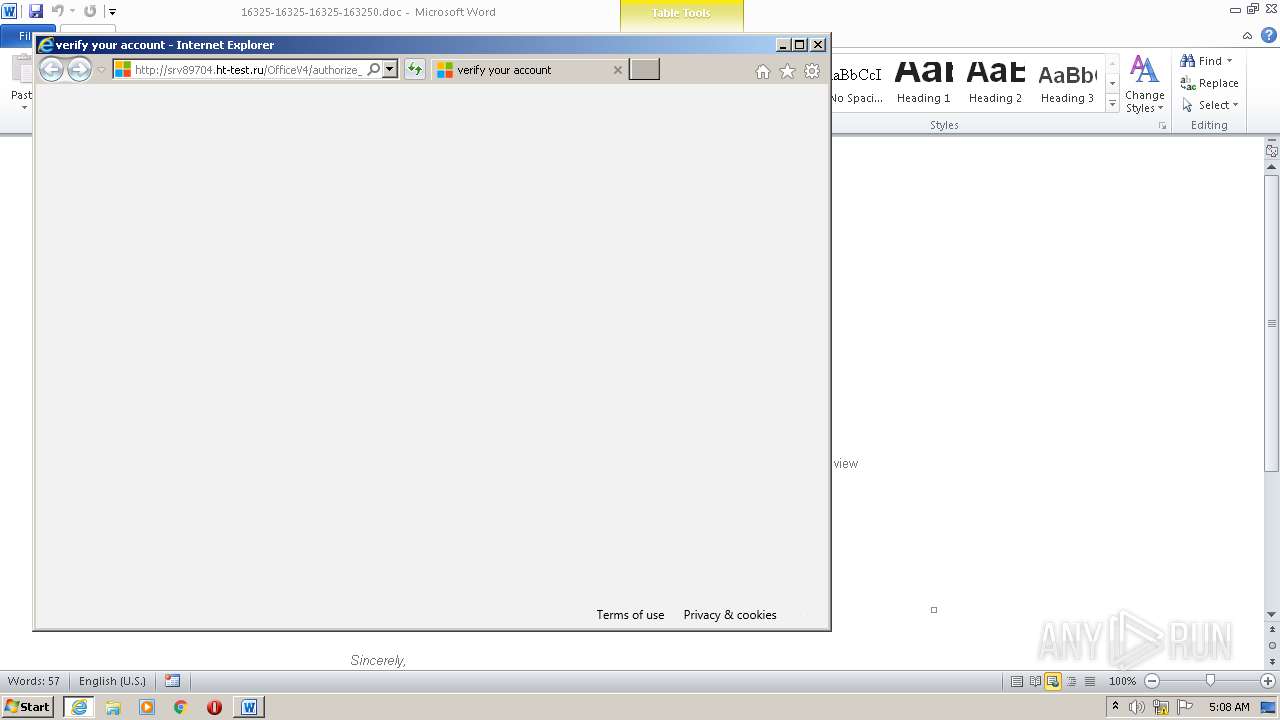
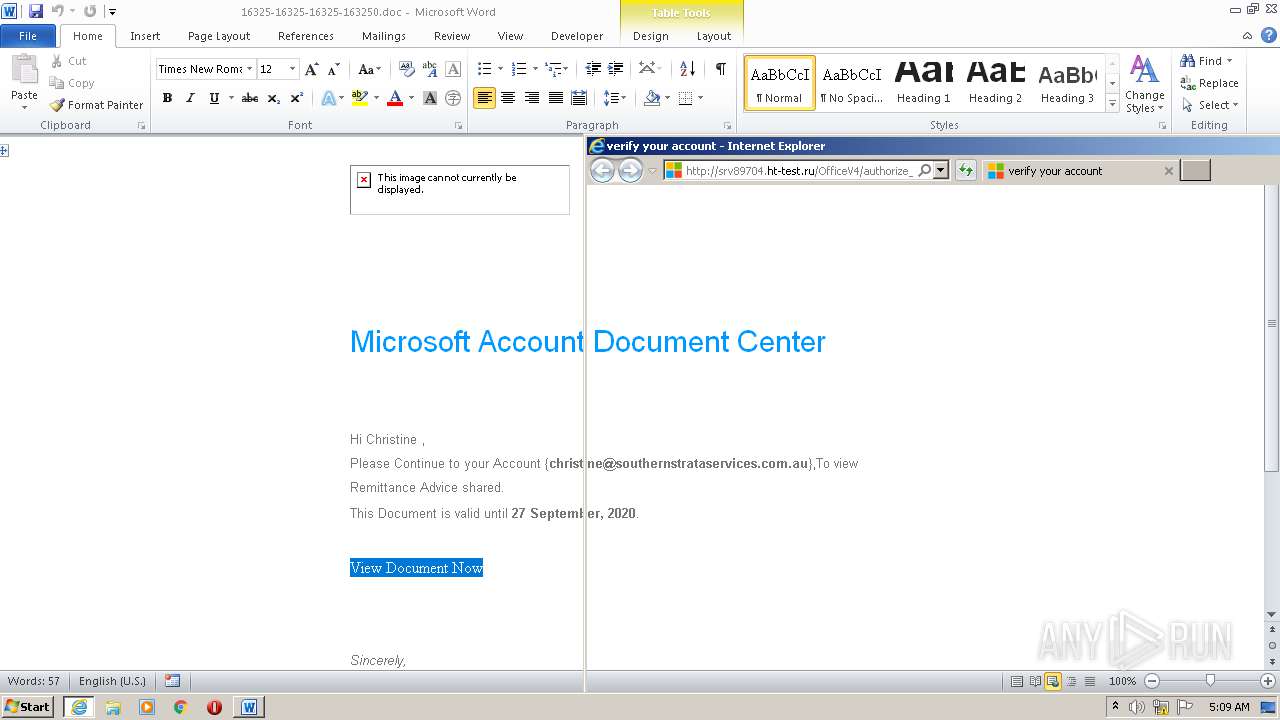
Executed via COM
- iexplore.exe (PID: 2684)
INFO
Reads Internet Cache Settings
- WINWORD.EXE (PID: 584)
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 3400)
Creates files in the user directory
- WINWORD.EXE (PID: 584)
- iexplore.exe (PID: 2684)
Manual execution by user
- chrome.exe (PID: 3436)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2692)
Application launched itself
- chrome.exe (PID: 3436)
- iexplore.exe (PID: 2684)
Changes settings of System certificates
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 2692)
Reads the hosts file
- chrome.exe (PID: 3436)
- chrome.exe (PID: 2776)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 584)
Changes internet zones settings
- iexplore.exe (PID: 2684)
Reads settings of System Certificates
- WINWORD.EXE (PID: 584)
- iexplore.exe (PID: 3400)
- iexplore.exe (PID: 2684)
Reads internet explorer settings
- WINWORD.EXE (PID: 584)
- iexplore.exe (PID: 2692)
- iexplore.exe (PID: 3400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| PixelsPerInch: | 96 |
|---|---|
| HTTPEquivXUACompatible: | IE=edge |
| viewport: | width=device-width, initial-scale=1 |
| Title: | *|MC:SUBJECT|* |
Total processes
66
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
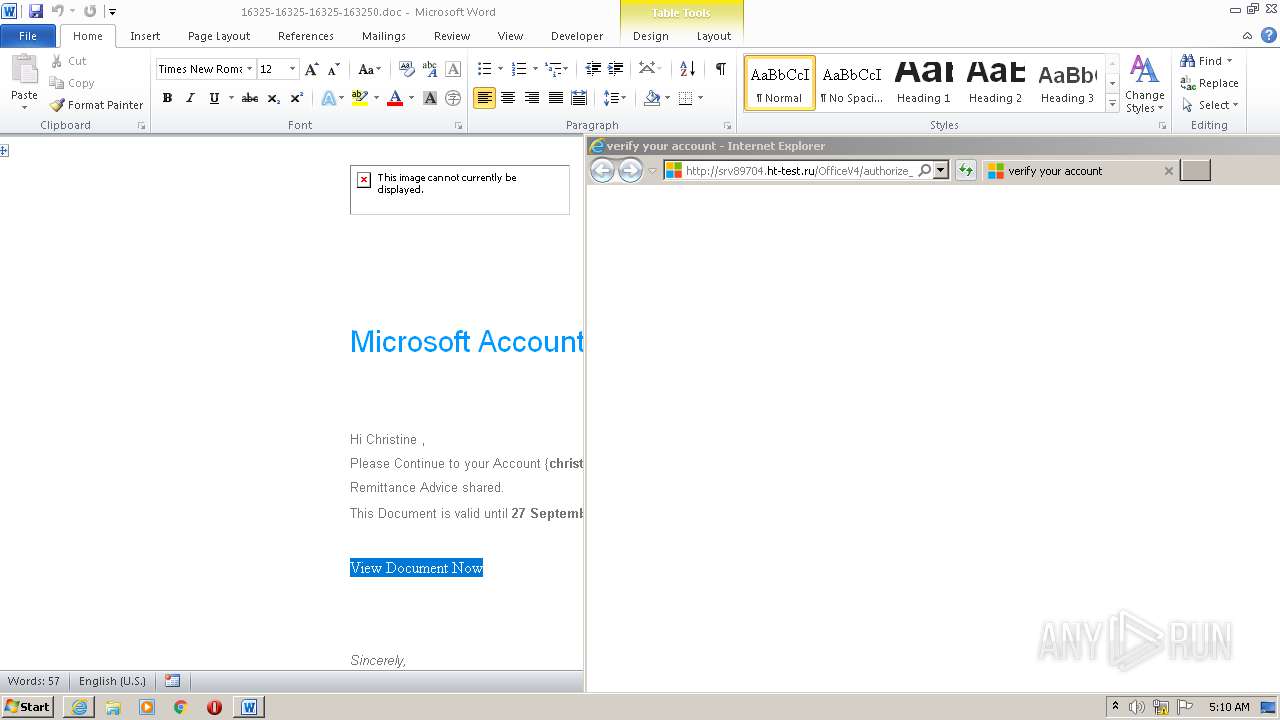
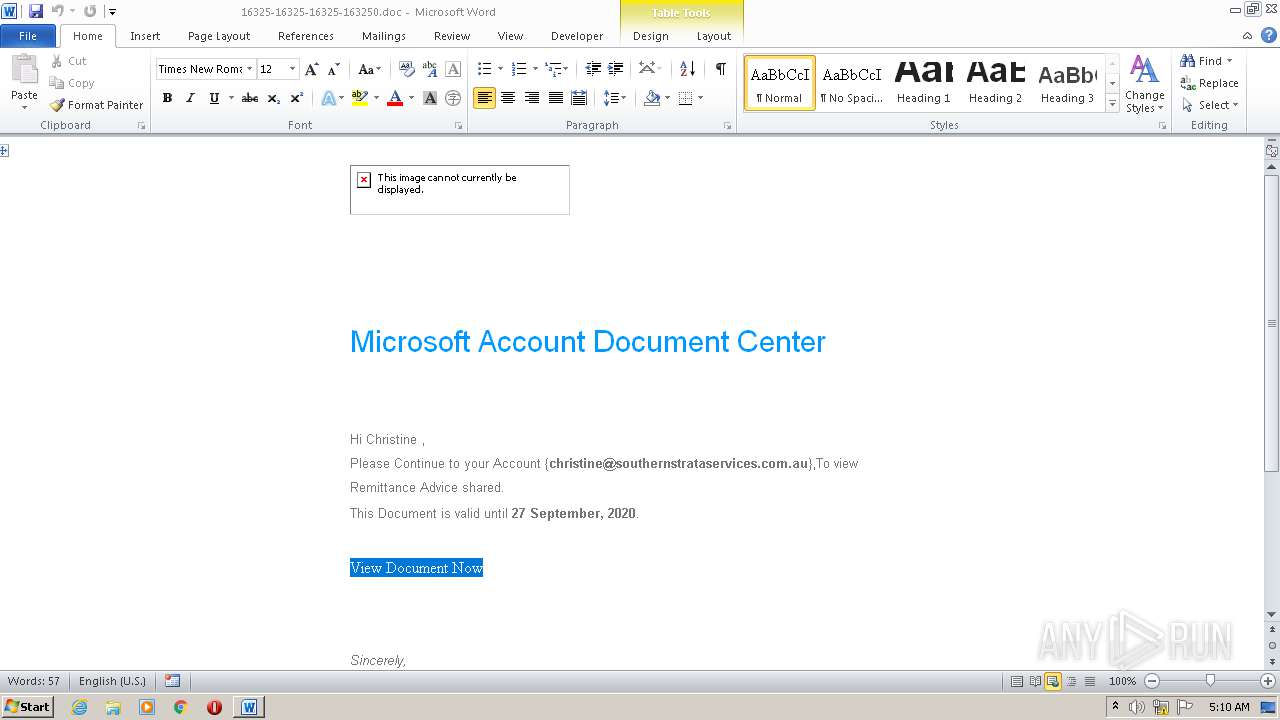
| 584 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\16325-16325-16325-163250.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4852043205862728134 --mojo-platform-channel-handle=3404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10231673742924310279 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1064 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11037756867889508103 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7155492152025835203 --mojo-platform-channel-handle=3432 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x60eaa9d0,0x60eaa9e0,0x60eaa9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2352 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8807694183037173481 --mojo-platform-channel-handle=3316 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3182611374293559064 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2532 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,2655571448757889271,11871144869221290735,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16467702734489658697 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2096 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
3 519
Read events
2 595
Write events
768
Delete events
156
Modification events
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | :ec |
Value: 3A65630048020000010000000000000000000000 | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (584) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
496
Text files
150
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA51A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Cab52DB.tmp | — | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Tar52EB.tmp | — | |
MD5:— | SHA256:— | |||
| 3400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab5B36.tmp | — | |
MD5:— | SHA256:— | |||
| 3400 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar5B37.tmp | — | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5080DC7A65DB6A5960ECD874088F3328_862BA1770B2FEE013603D2FF9ABEAFDA | binary | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_2DBE917624E9880FE0C7C5570D56E691 | der | |
MD5:— | SHA256:— | |||
| 584 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$325-16325-16325-163250.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
96
DNS requests
55
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
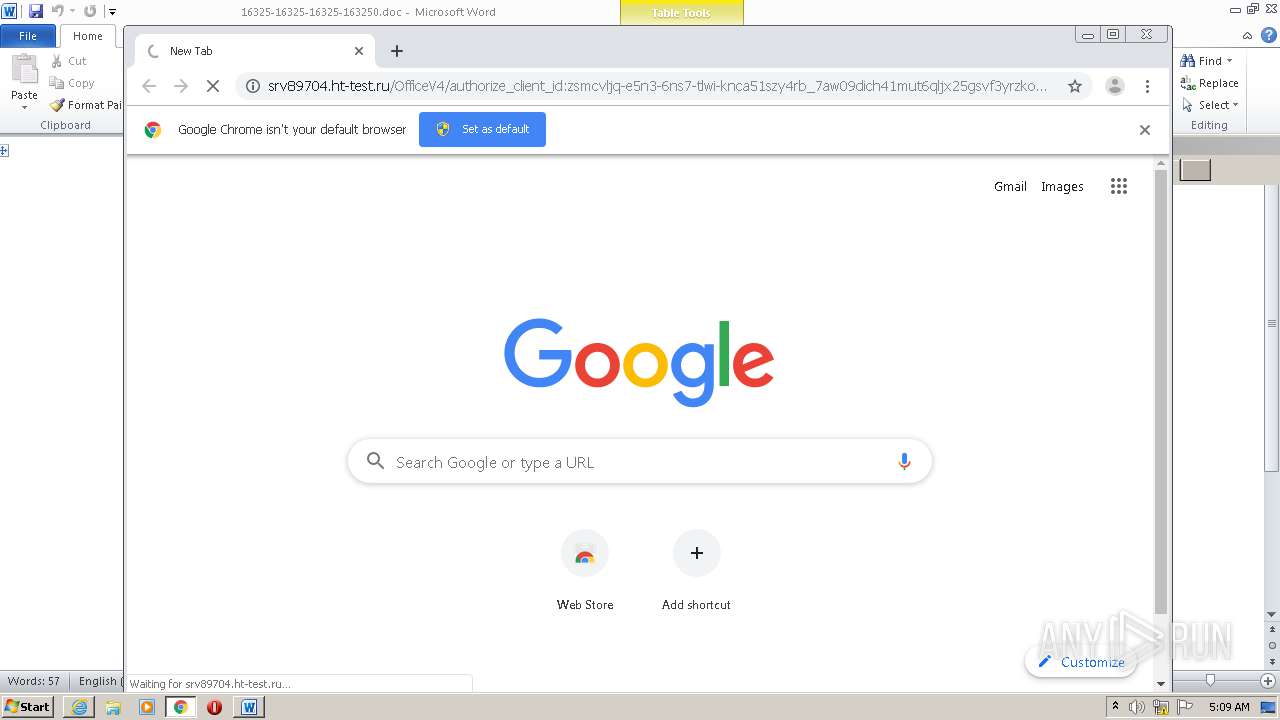
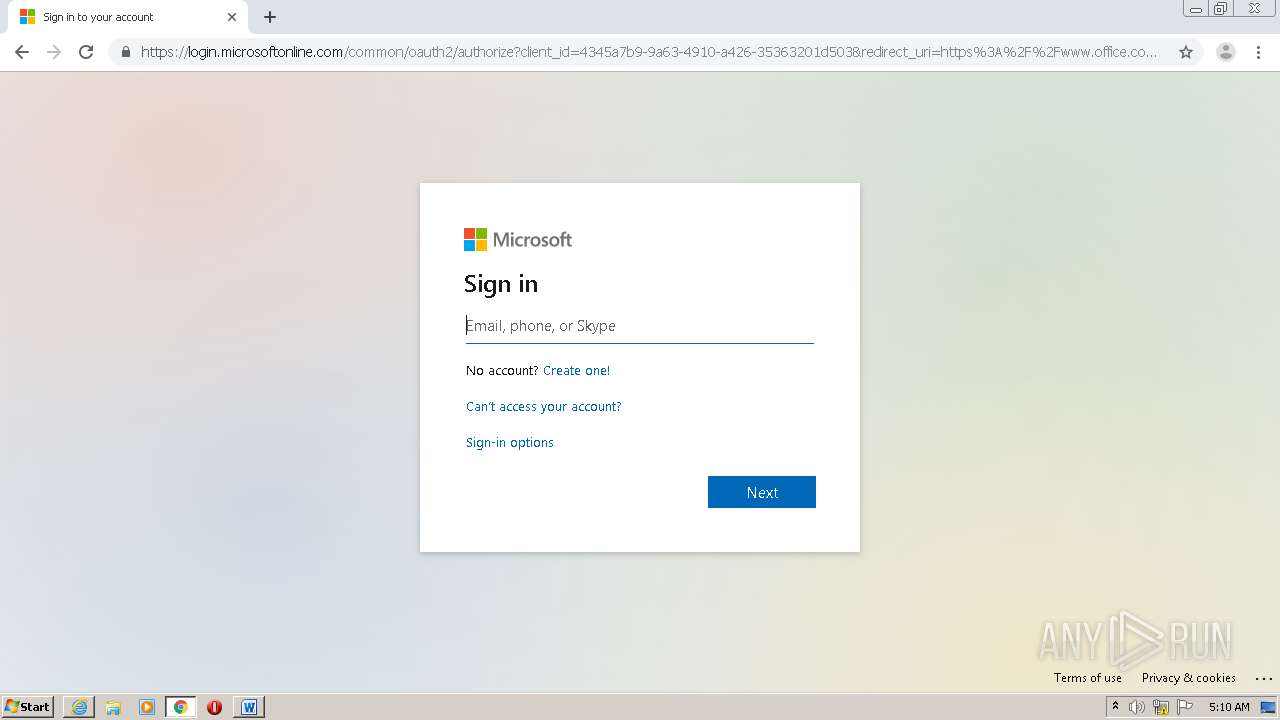
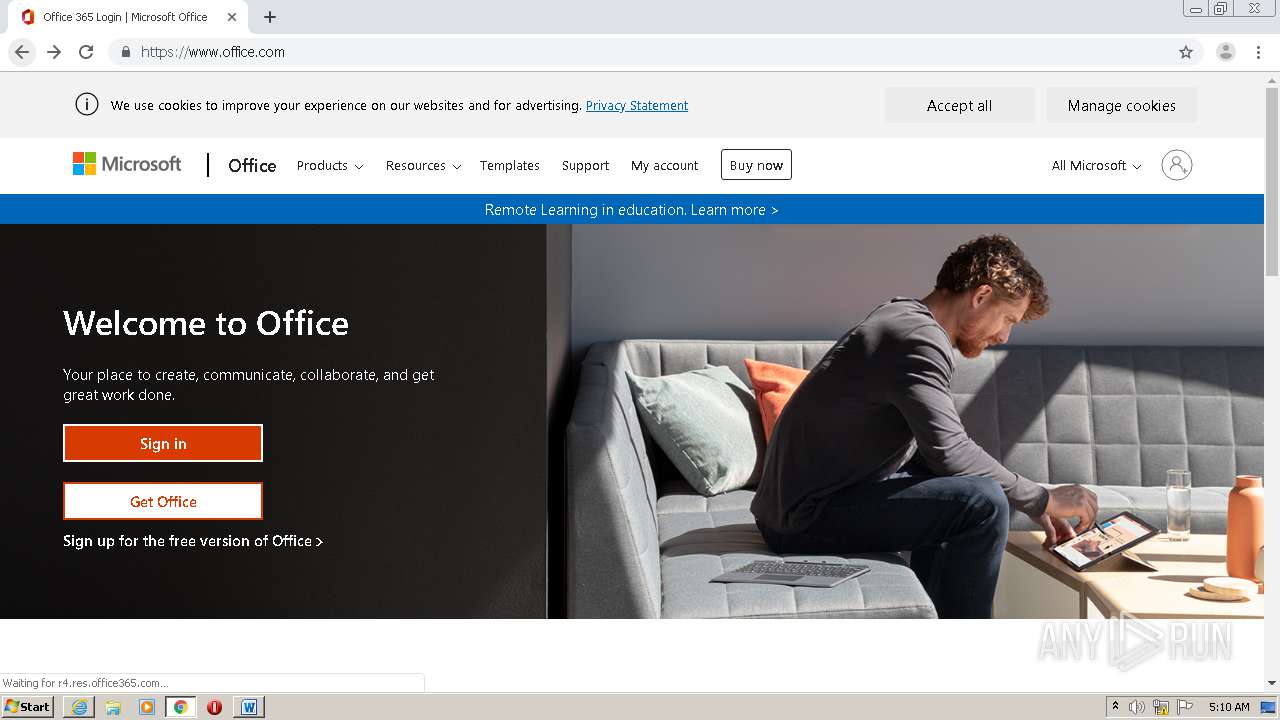
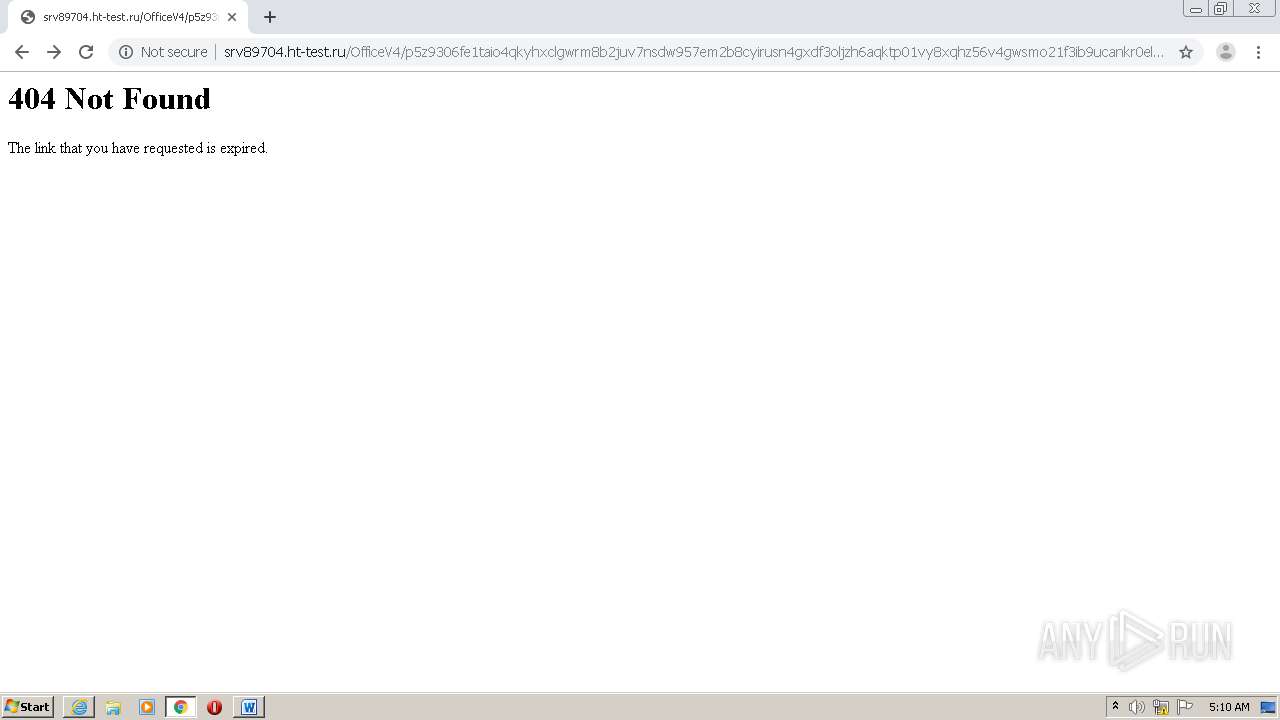
3400 | iexplore.exe | GET | — | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/css/style.css | RU | — | — | suspicious |
584 | WINWORD.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCEQDwHUvue3yjezwFZqwFlyRY | US | der | 728 b | whitelisted |
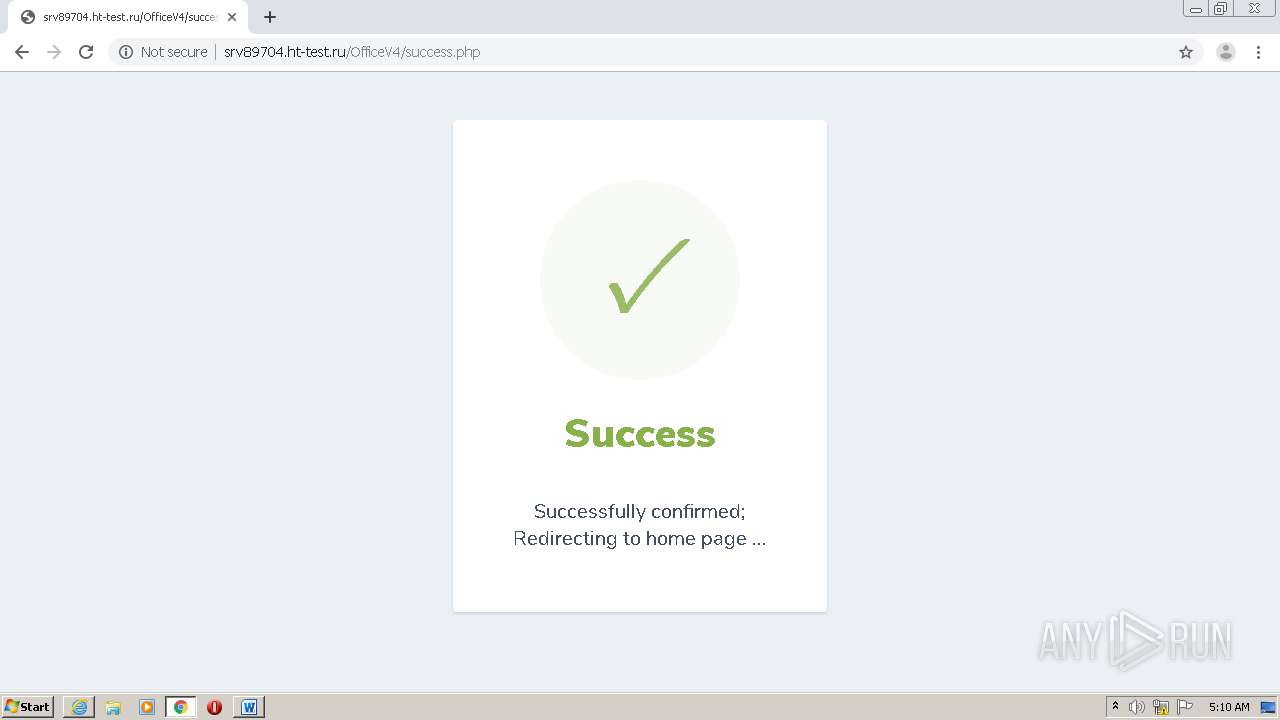
3400 | iexplore.exe | GET | 302 | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/Y2hyaXN0aW5lQHNvdXRoZXJuc3RyYXRhc2VydmljZXMuY29tLmF1 | RU | htm | 12.9 Kb | suspicious |
584 | WINWORD.EXE | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEGfe9D7xe9riT%2FWUBgbSwIQ%3D | US | der | 471 b | whitelisted |
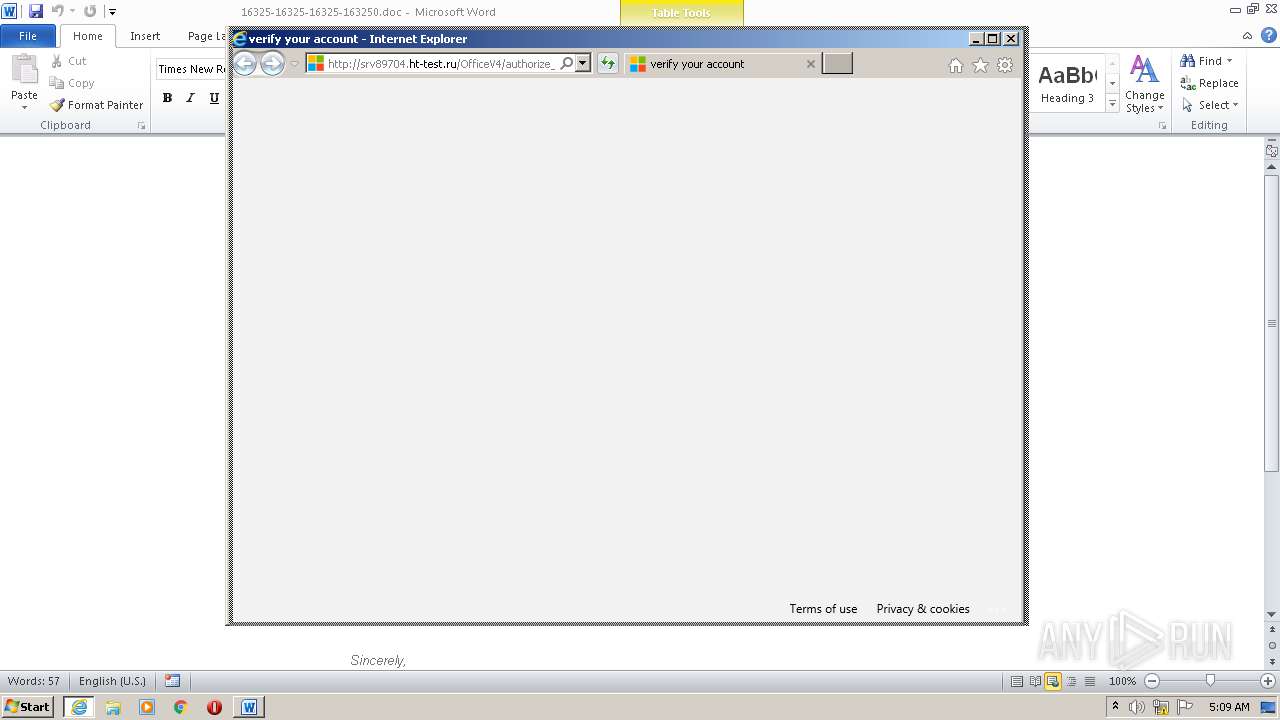
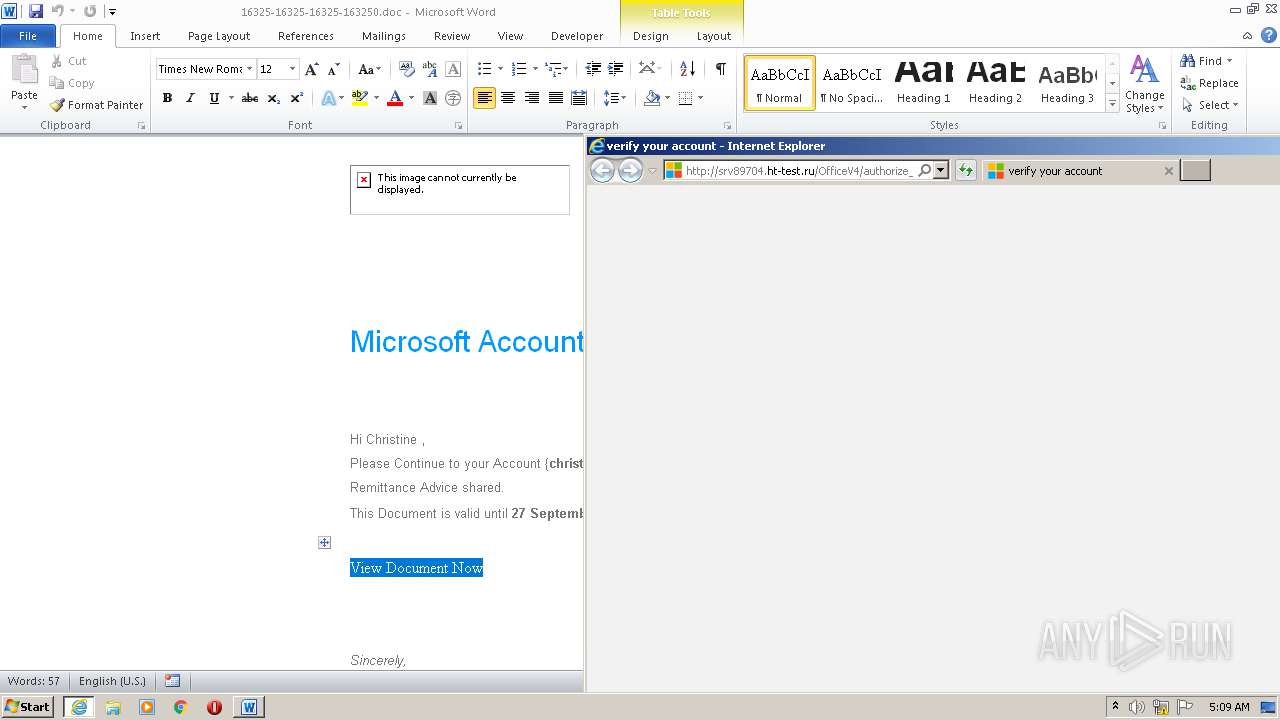
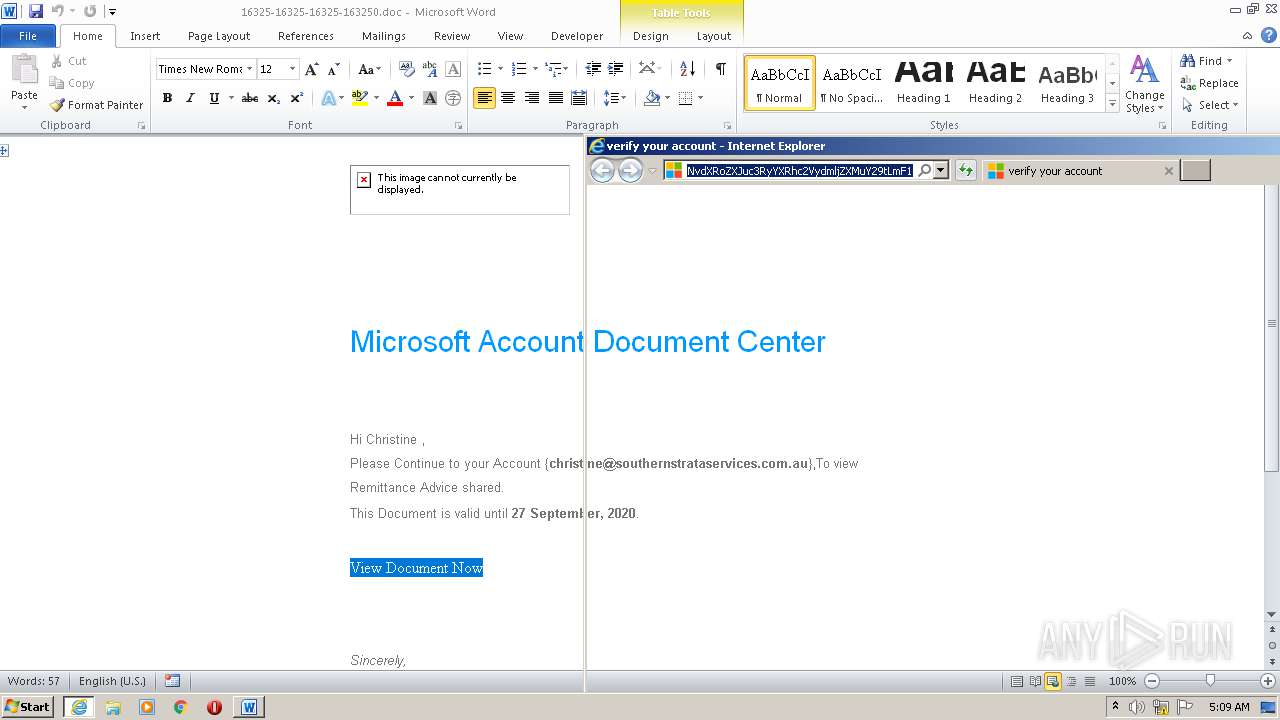
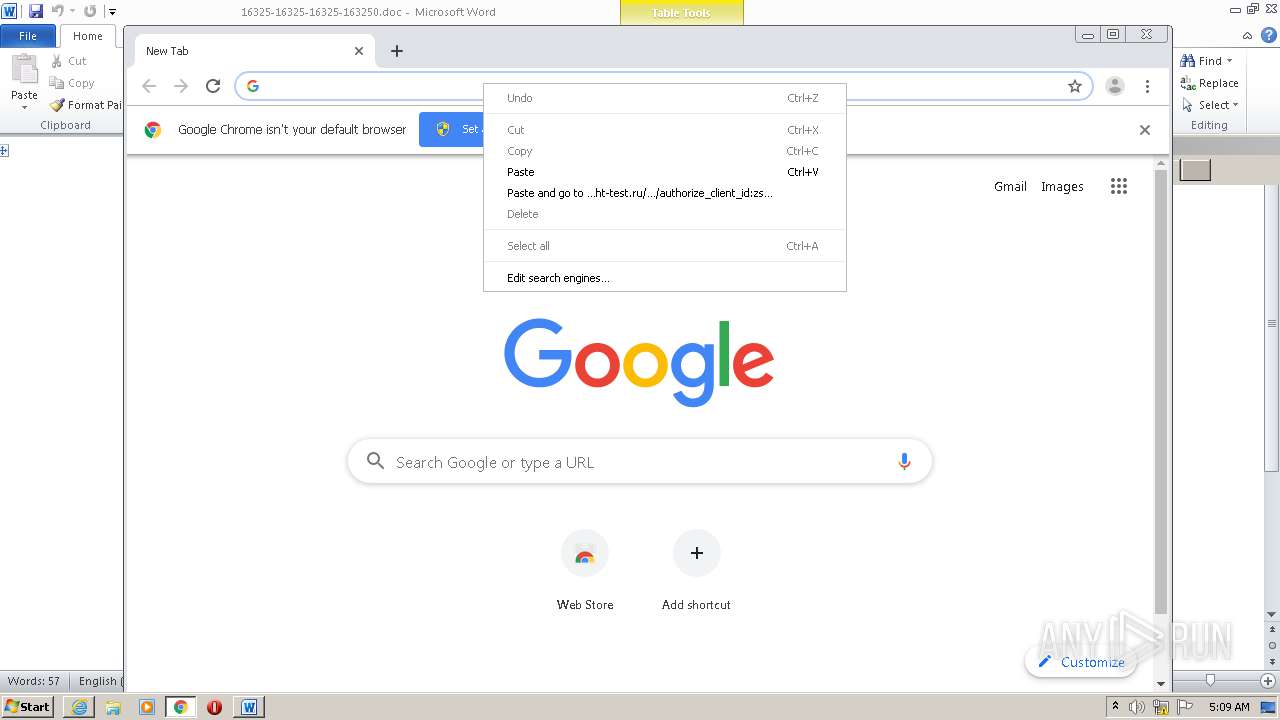
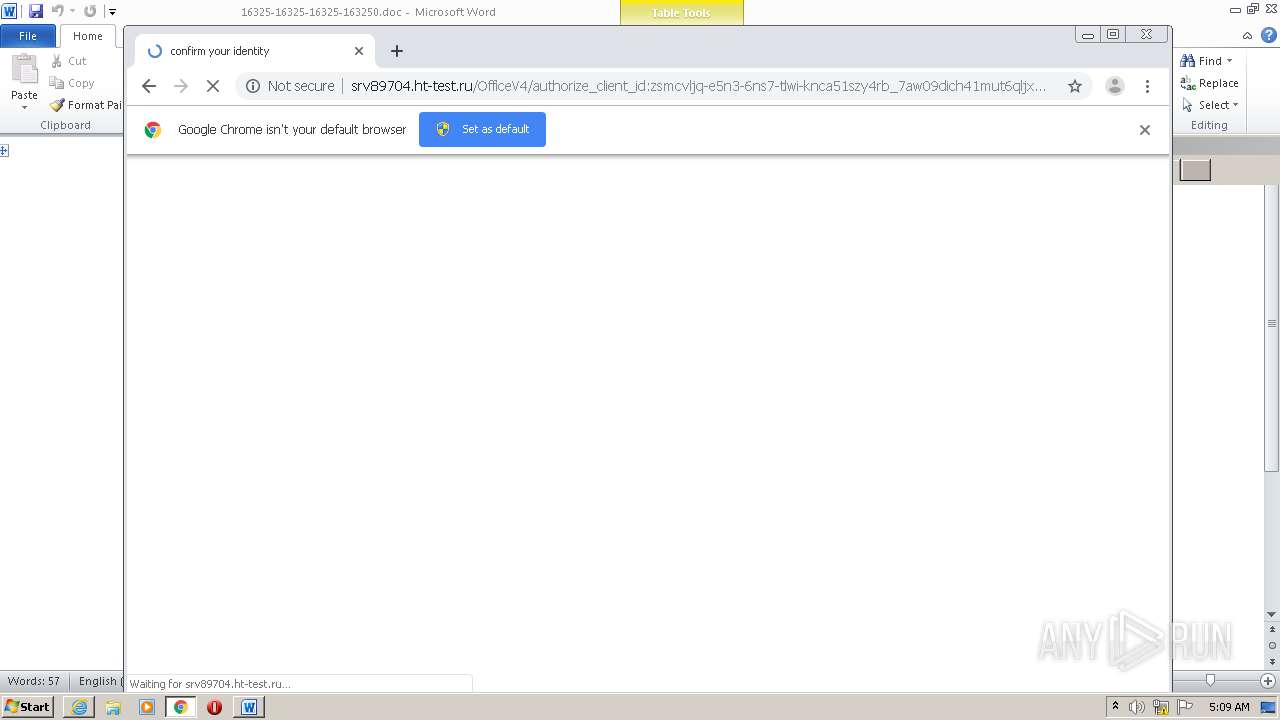
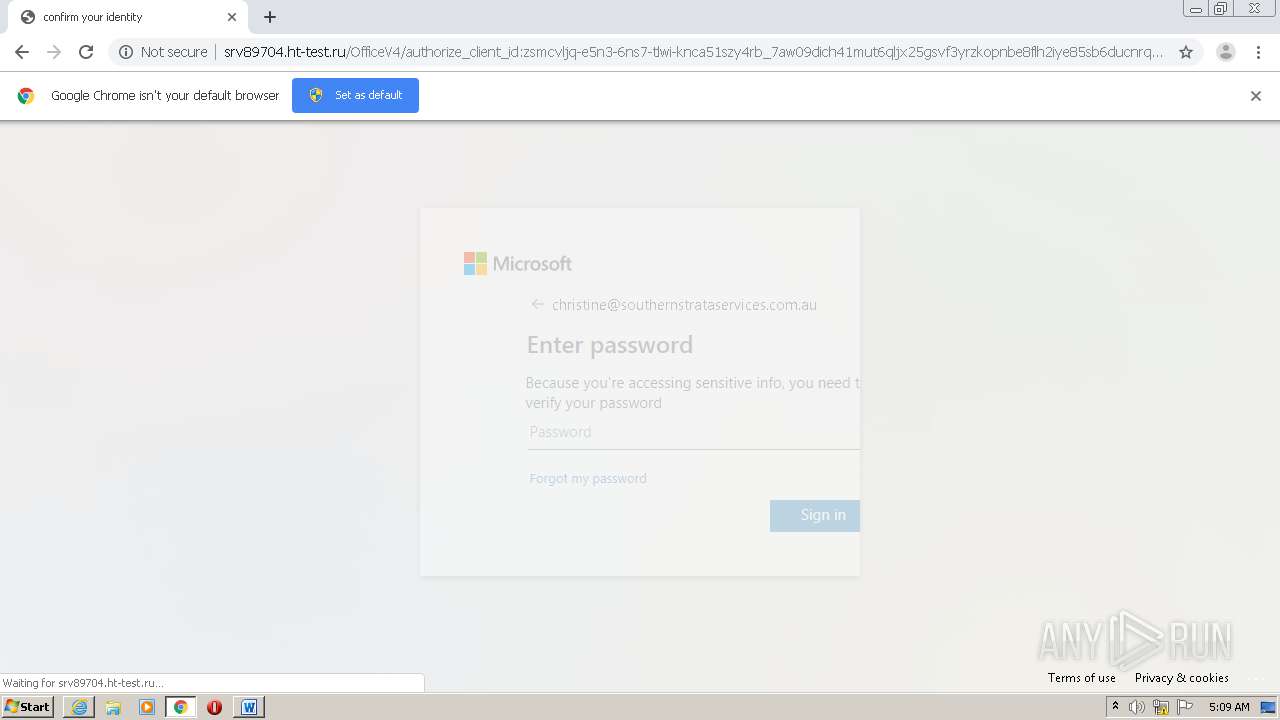
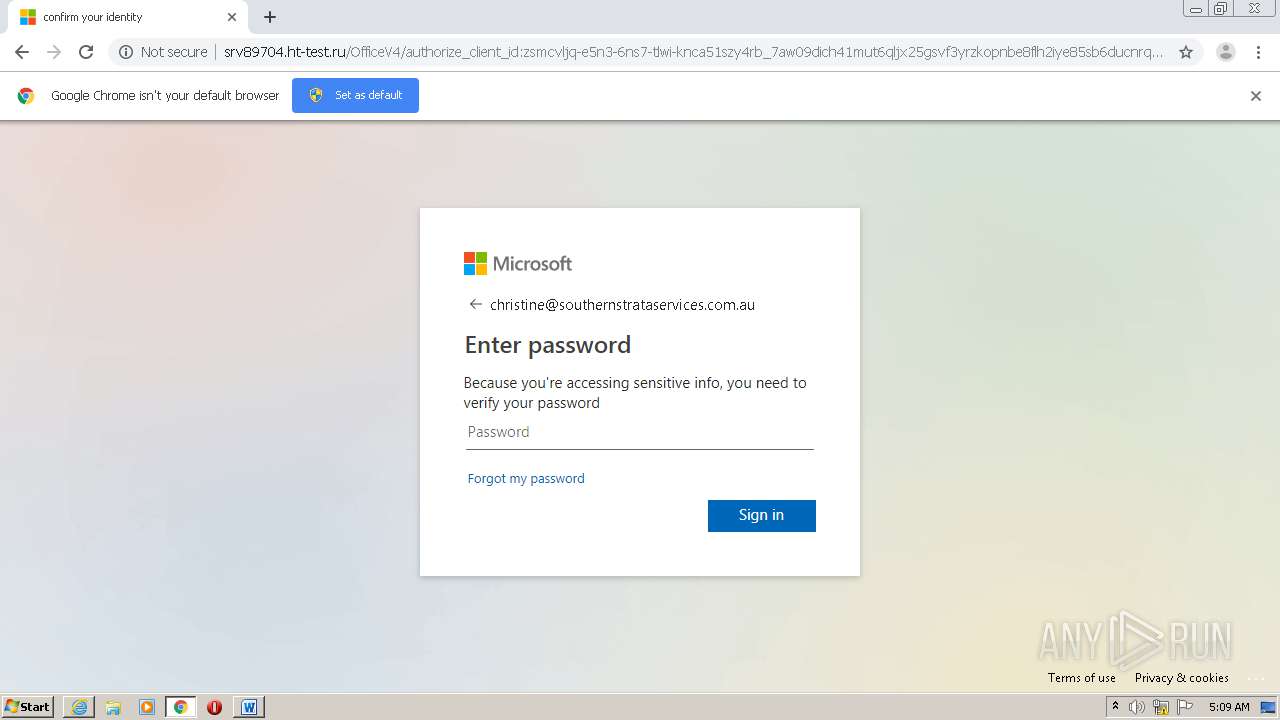
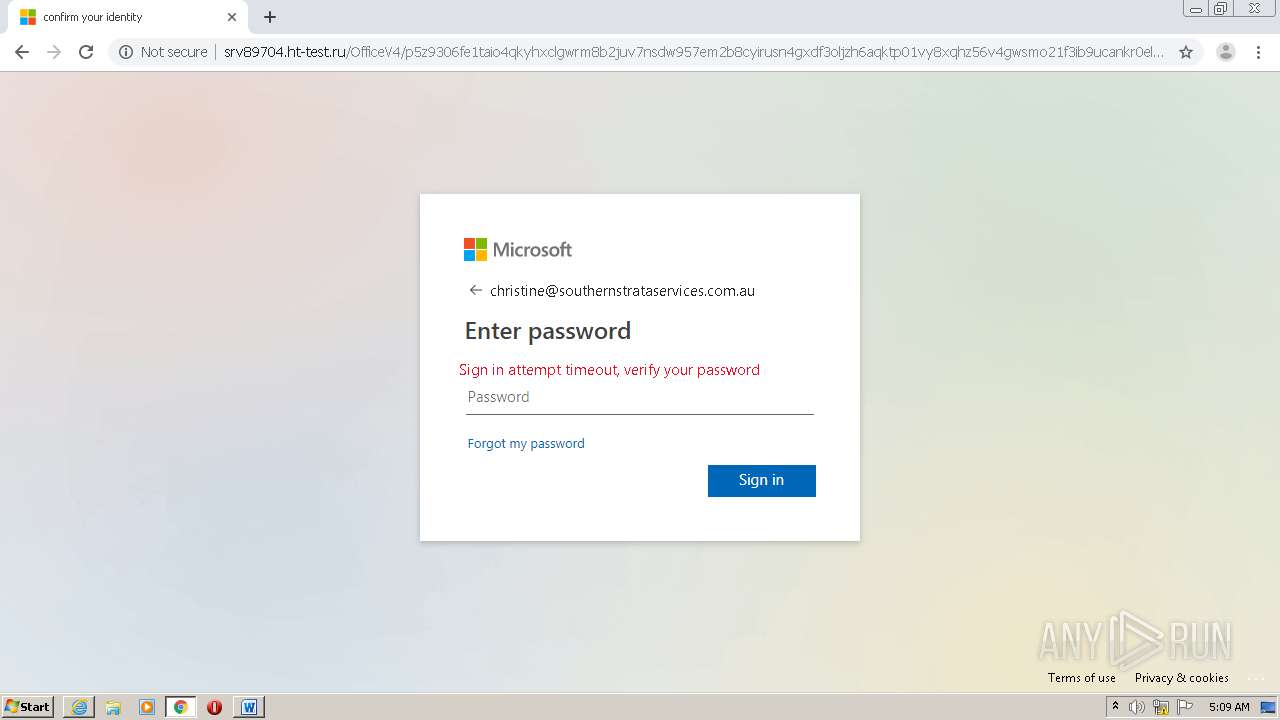
3400 | iexplore.exe | GET | 200 | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/authorize_client_id:zsmcvljq-e5n3-6ns7-tlwi-knca51szy4rb_7aw09dich41mut6qljx25gsvf3yrzkopnbe8flh2iye85sb6ducnrqxjam970vwgzt4okp13ph421gorsejln0ciukqmxza85vw36fdt9y7b?data=Y2hyaXN0aW5lQHNvdXRoZXJuc3RyYXRhc2VydmljZXMuY29tLmF1 | RU | htm | 12.9 Kb | suspicious |
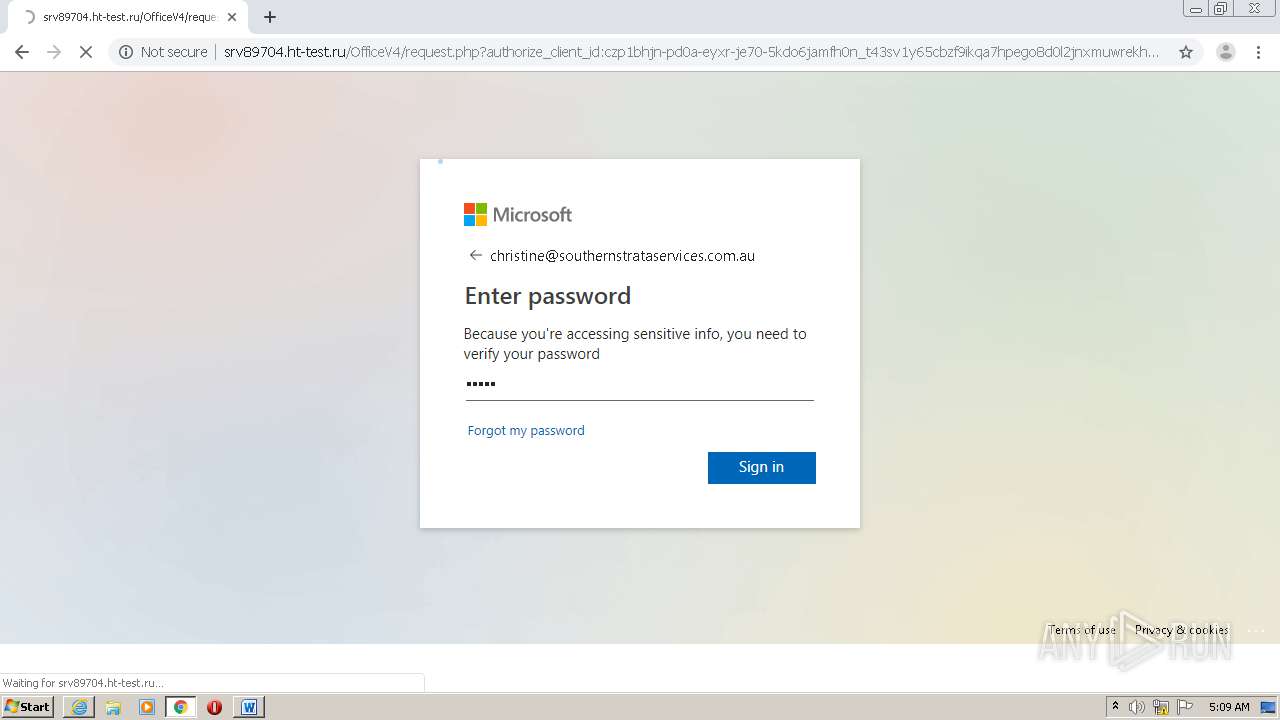
3400 | iexplore.exe | POST | — | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/api.php | RU | — | — | suspicious |
3400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
3400 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
3400 | iexplore.exe | GET | 200 | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/images/arrow_left.svg | RU | image | 513 b | suspicious |
3400 | iexplore.exe | GET | 200 | 78.110.50.127:80 | http://srv89704.ht-test.ru/OfficeV4/images/enterpass.png | RU | image | 1.41 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
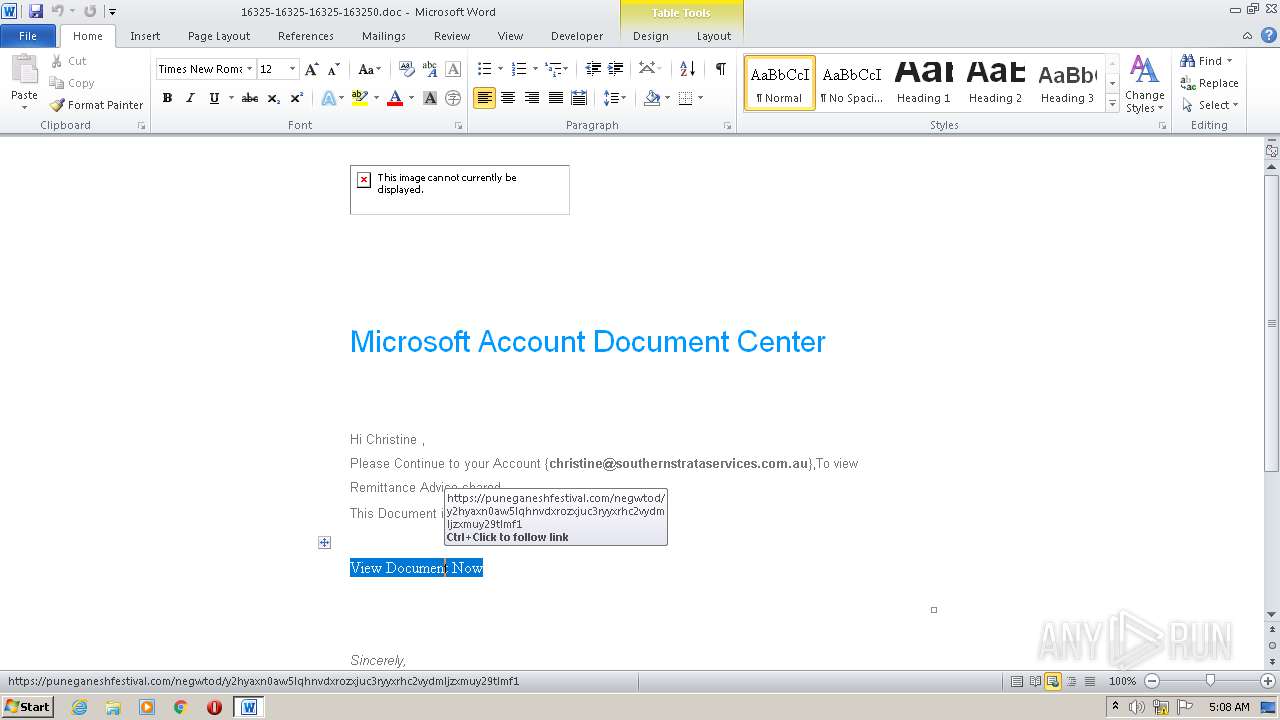
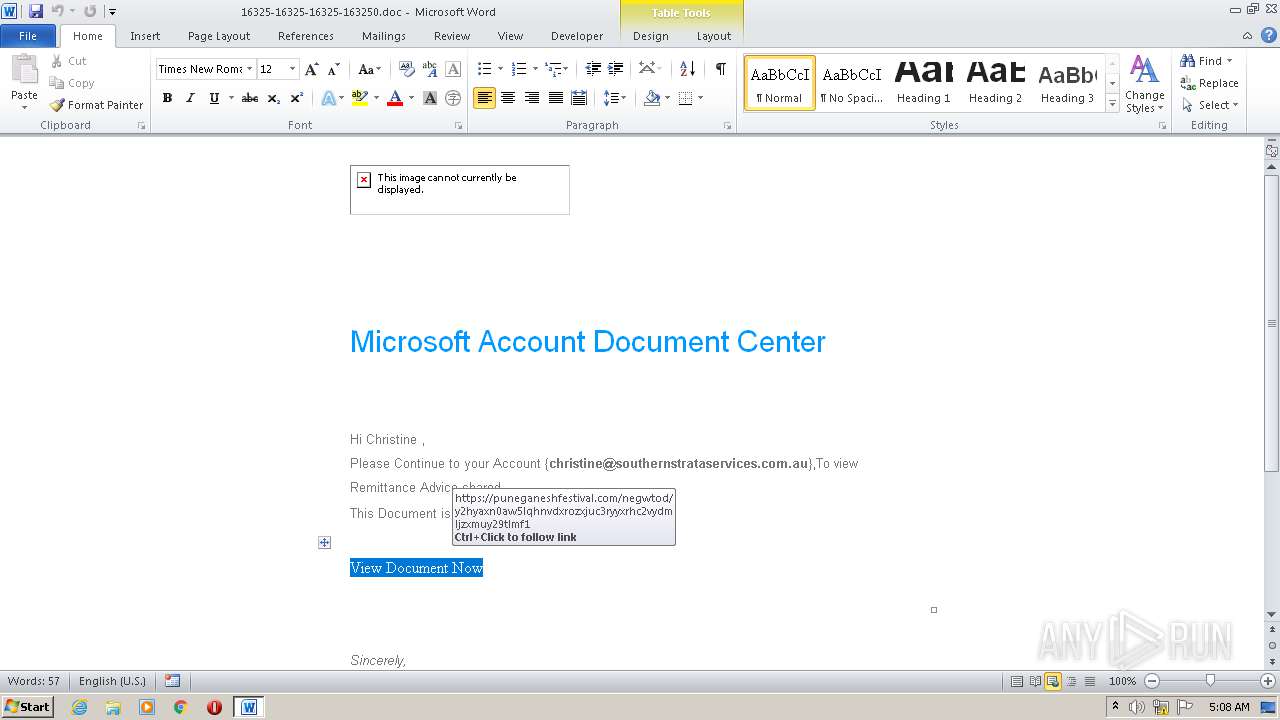
584 | WINWORD.EXE | 72.9.153.136:443 | puneganeshfestival.com | Dallas Infrastructure Services, LLC | US | malicious |
3400 | iexplore.exe | 72.9.153.136:443 | puneganeshfestival.com | Dallas Infrastructure Services, LLC | US | malicious |
3400 | iexplore.exe | 78.110.50.127:80 | srv89704.ht-test.ru | ZAO Hosting Telesystems | RU | malicious |
2684 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3400 | iexplore.exe | 104.109.84.139:443 | secure.aadcdn.microsoftonline-p.com | Akamai International B.V. | NL | unknown |
3400 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2684 | iexplore.exe | 78.110.50.127:80 | srv89704.ht-test.ru | ZAO Hosting Telesystems | RU | malicious |
1056 | svchost.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1056 | svchost.exe | 2.16.186.74:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
1056 | svchost.exe | 216.58.208.35:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
puneganeshfestival.com |
| malicious |
ocsp.comodoca.com |
| whitelisted |
srv89704.ht-test.ru |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
secure.aadcdn.microsoftonline-p.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2776 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |
2776 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY HTTP POST contains pass= in cleartext |