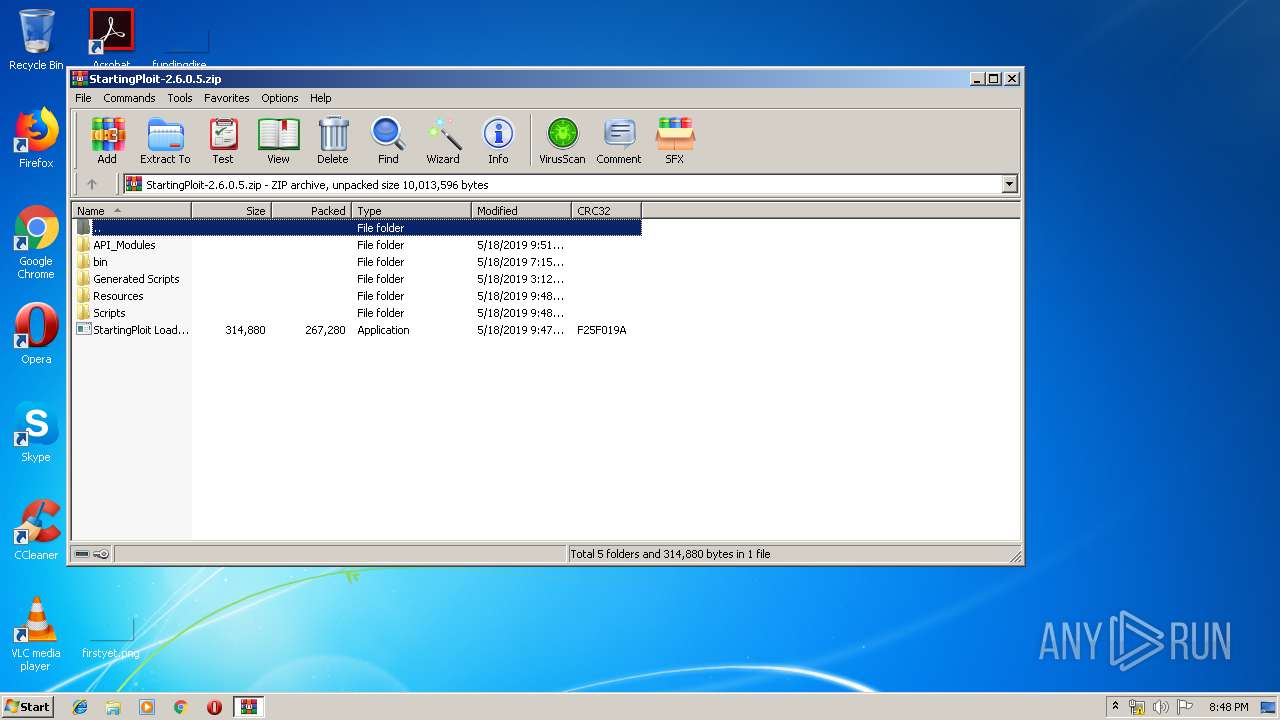
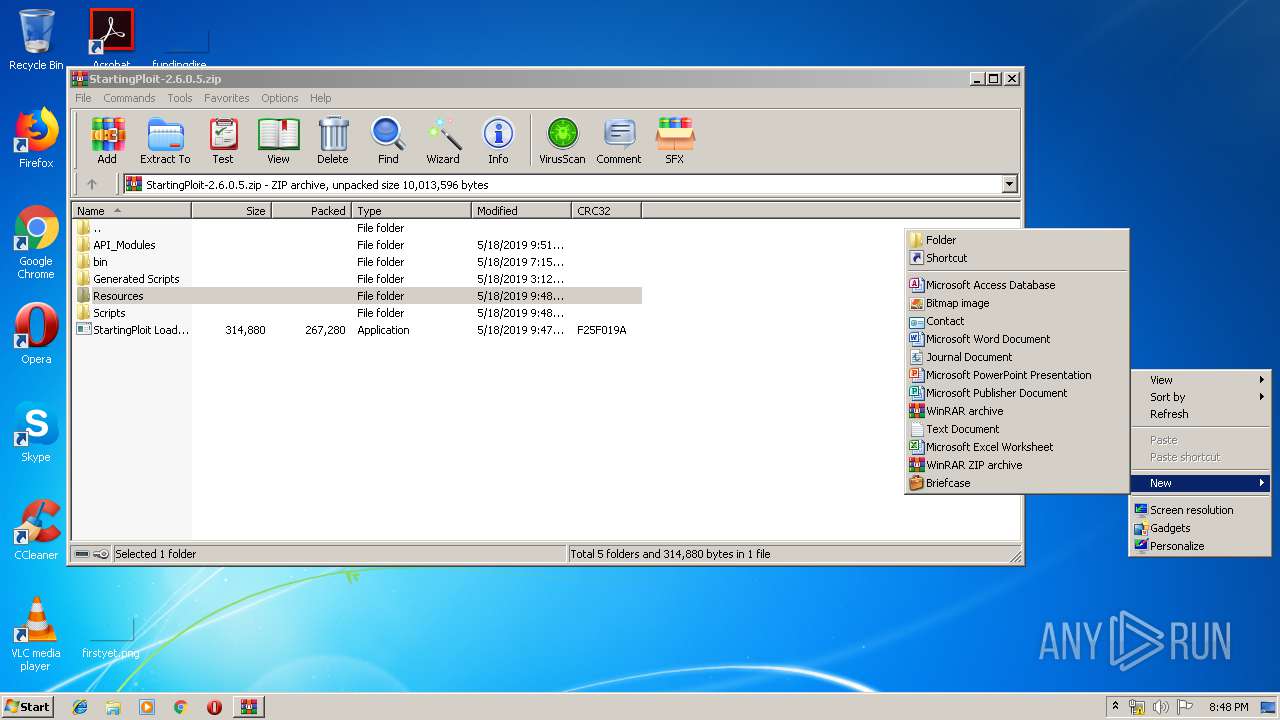
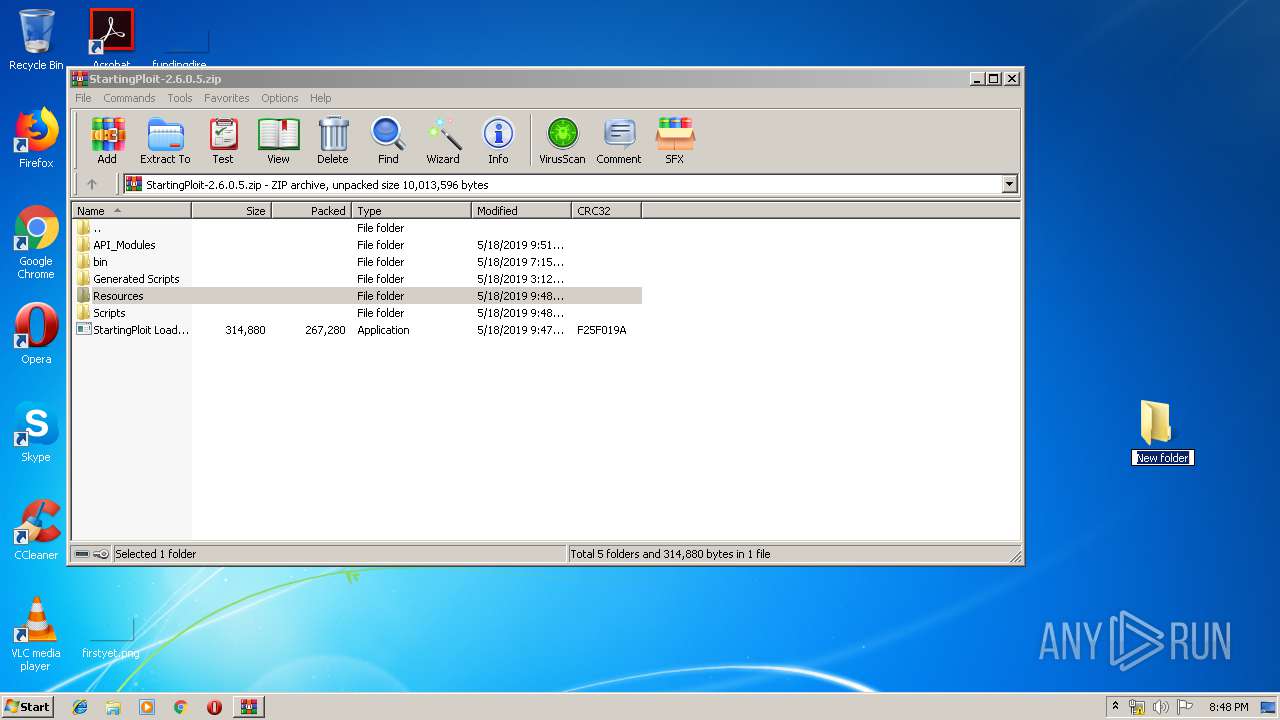
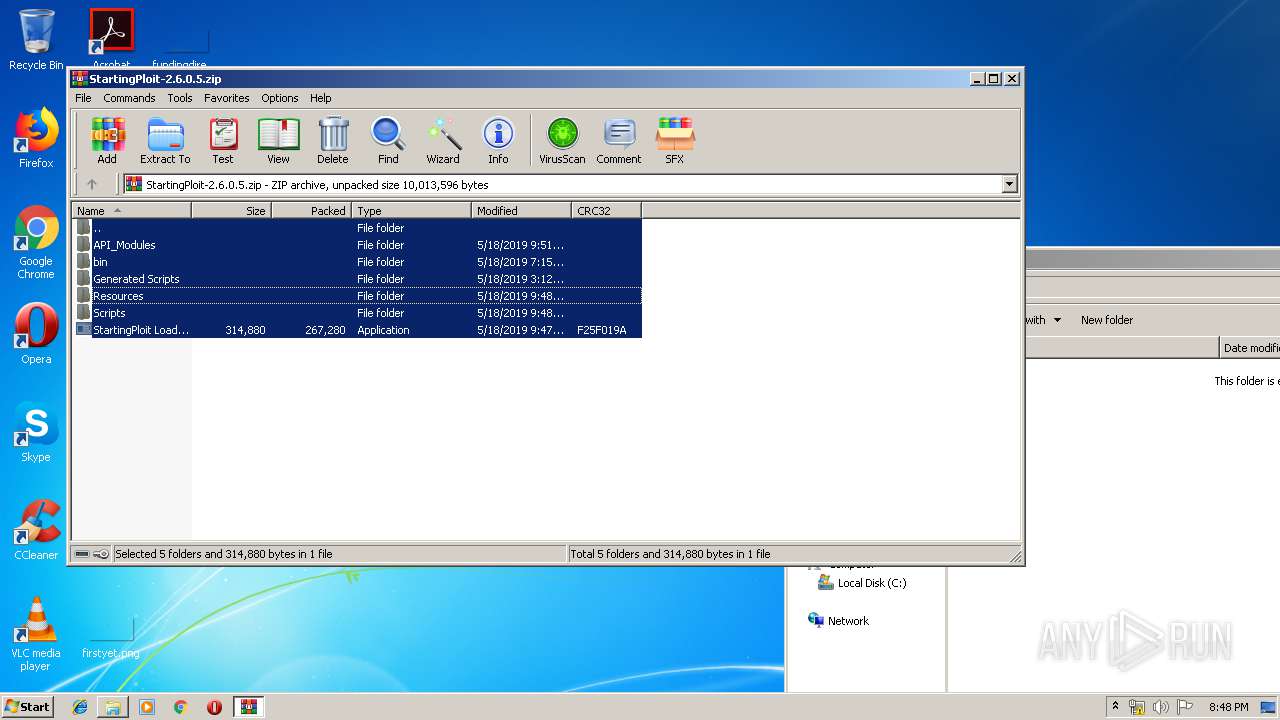
| download: | StartingPloit-2.6.0.5.zip |
| Full analysis: | https://app.any.run/tasks/ae4b5ad1-d208-4241-b366-31bc44236062 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2019, 19:47:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 2921B5133C86573FE68197375EDC73C0 |
| SHA1: | AF1AD167D9EC2644AE6E40C3B34B130737DF741C |
| SHA256: | 5ED3B7A374F46F7389E60211B40A16A155D448C7BE706AF5E48C36616B5D0C9A |
| SSDEEP: | 196608:H5n1AkEt/kzMGWbiuab/ji4SUqB3vDfHmH6m9i3:H5nOHKMGWbiuaTj4v7mH6m9c |
MALICIOUS
Application was dropped or rewritten from another process
- StartingPloit Loader.exe (PID: 3512)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3976)
INFO
Manual execution by user
- StartingPloit Loader.exe (PID: 3512)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:05:18 14:48:10 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Resources/ |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
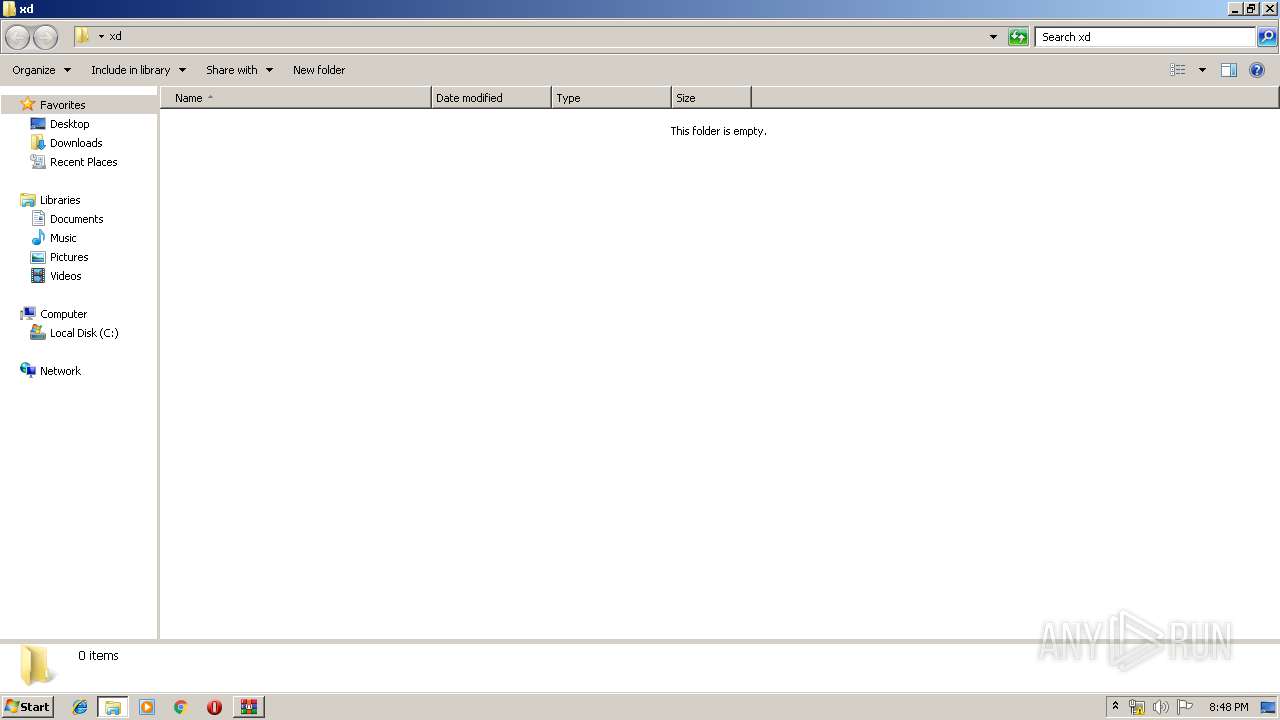
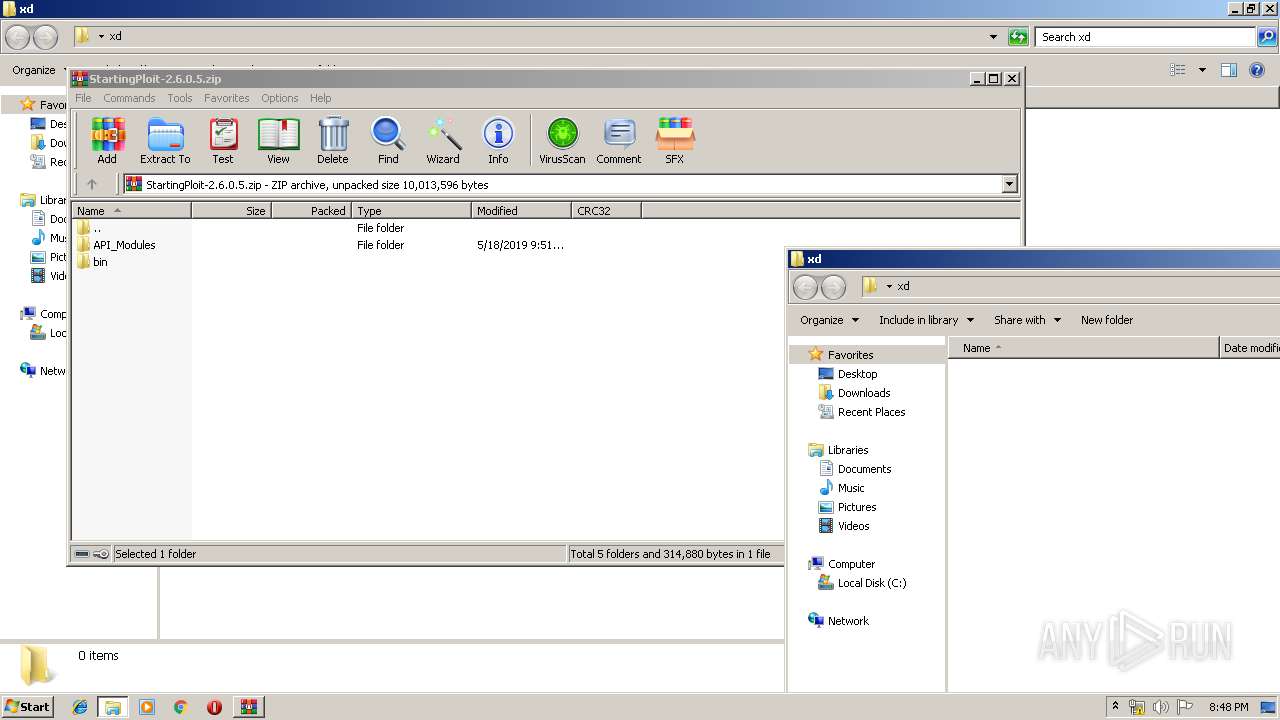
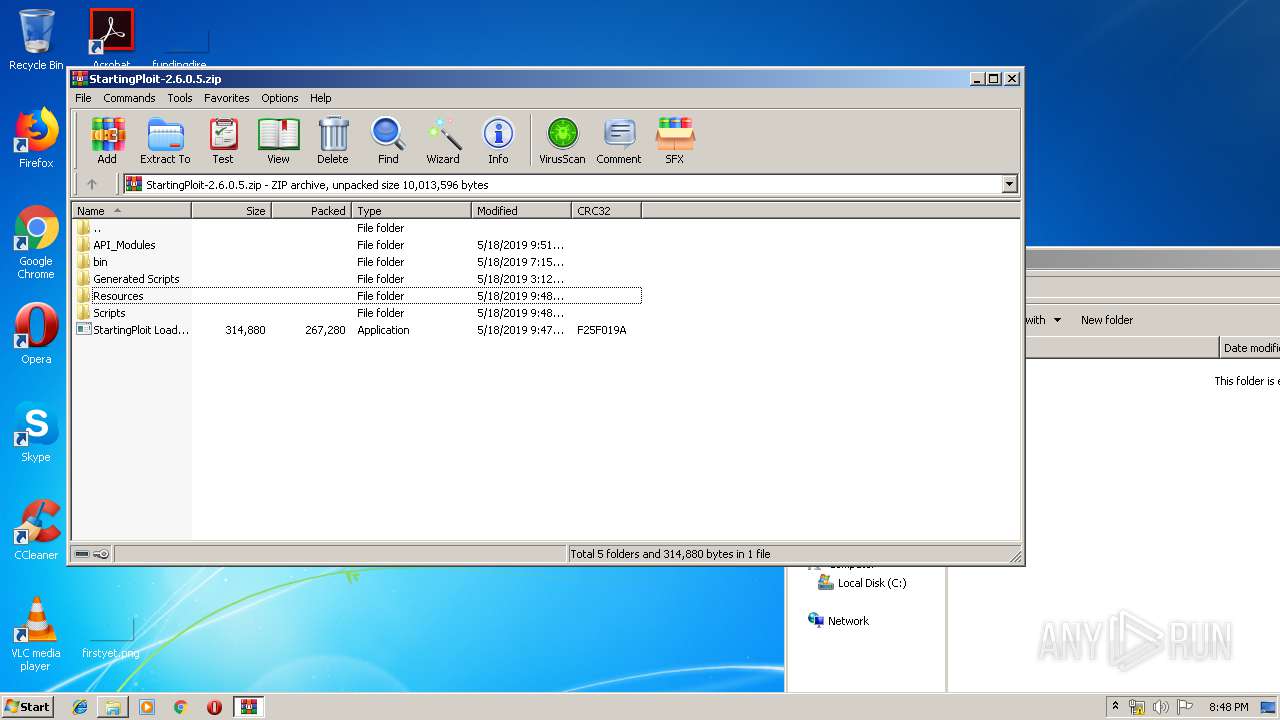
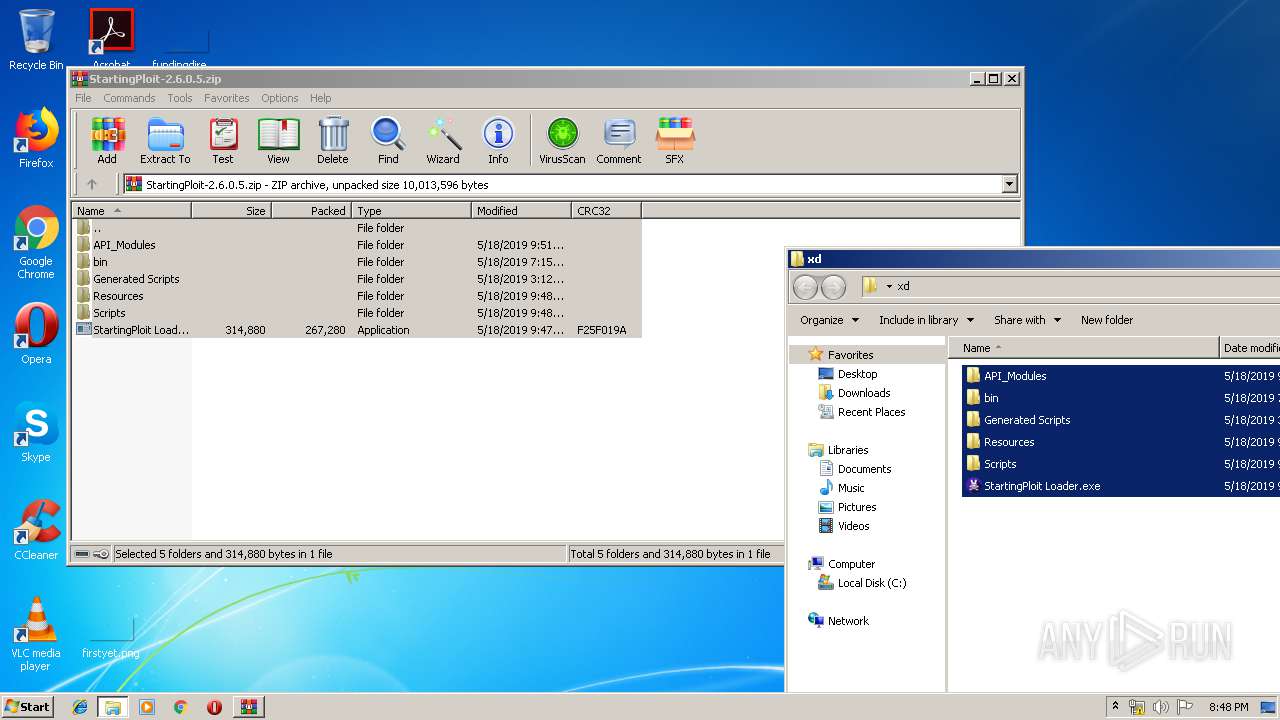
| 3512 | "C:\Users\admin\Desktop\xd\StartingPloit Loader.exe" | C:\Users\admin\Desktop\xd\StartingPloit Loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: startingloit_loader Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
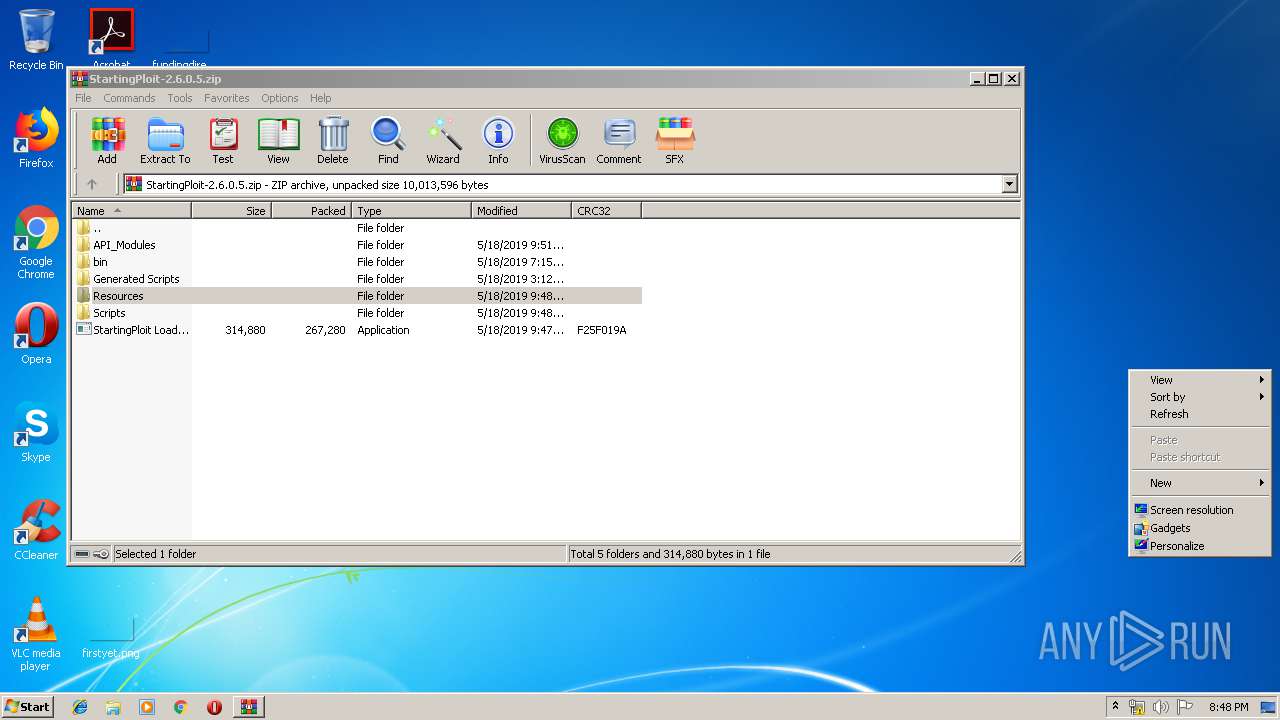
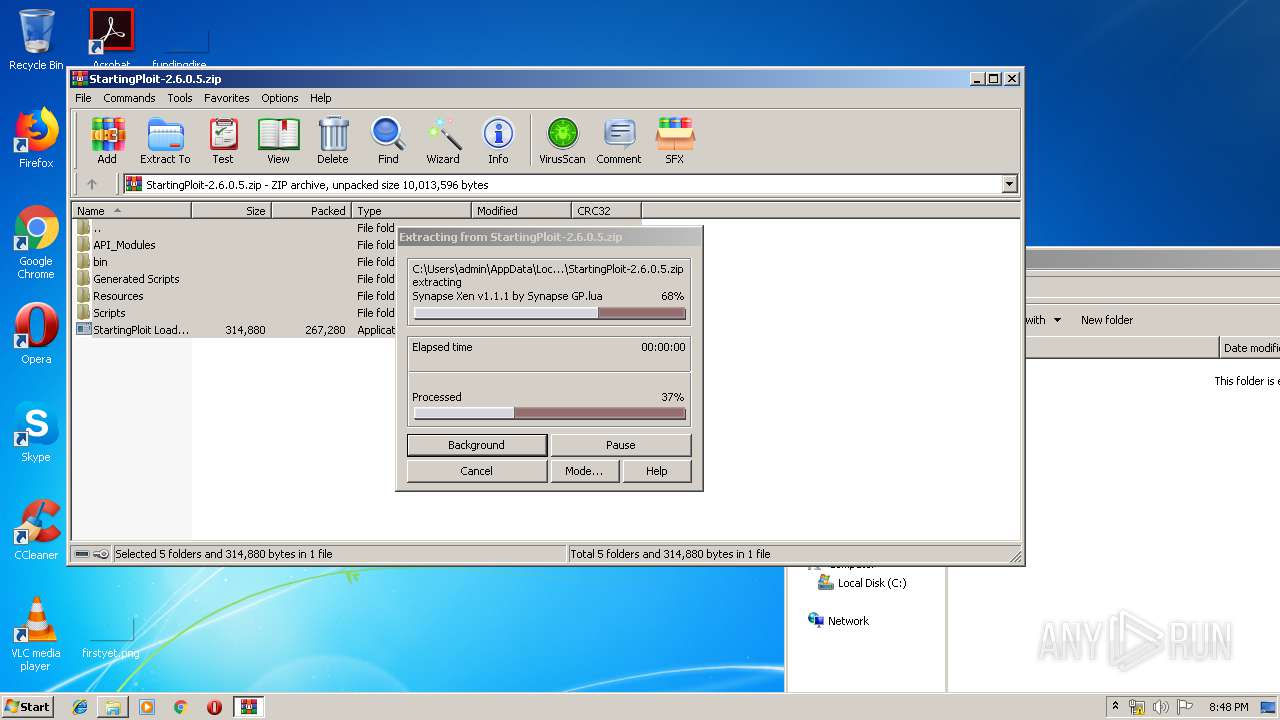
| 3976 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\StartingPloit-2.6.0.5.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
460
Read events
440
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\70\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\StartingPloit-2.6.0.5.zip | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3976) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3512) StartingPloit Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\StartingPloit Loader_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3512) StartingPloit Loader.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\StartingPloit Loader_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
119
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Resources\Lua.langproj | xml | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Resources\Dark.vssettings | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Resources\Lua.langdef | xml | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Bank and Jewelry Store Autorob.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Assassin Aimbot.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Base Wars GUI.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\City Life Grab Knife.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Arcane Adventures GUI.txt | text | |
MD5:— | SHA256:— | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Azure Mines X-Ray.txt | text | |
MD5:580D74F9CD4BACCAEB3B047F73FB1E3E | SHA256:CD75403870FE61C84EF1C087A07F56E3D40EFAA5C41B3CBD10527E8A802F804F | |||
| 3976 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3976.42912\Scripts\Games\Blox Hunt GUI.txt | text | |
MD5:34C09F4D82FC2F72087132F89F586FF9 | SHA256:89991D67AE4FDAA4E6BDF67A45086C0CF1F0D44A4E8415A86671D1D9236E49C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.25.61.13:443 | textuploader.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
textuploader.com |
| suspicious |