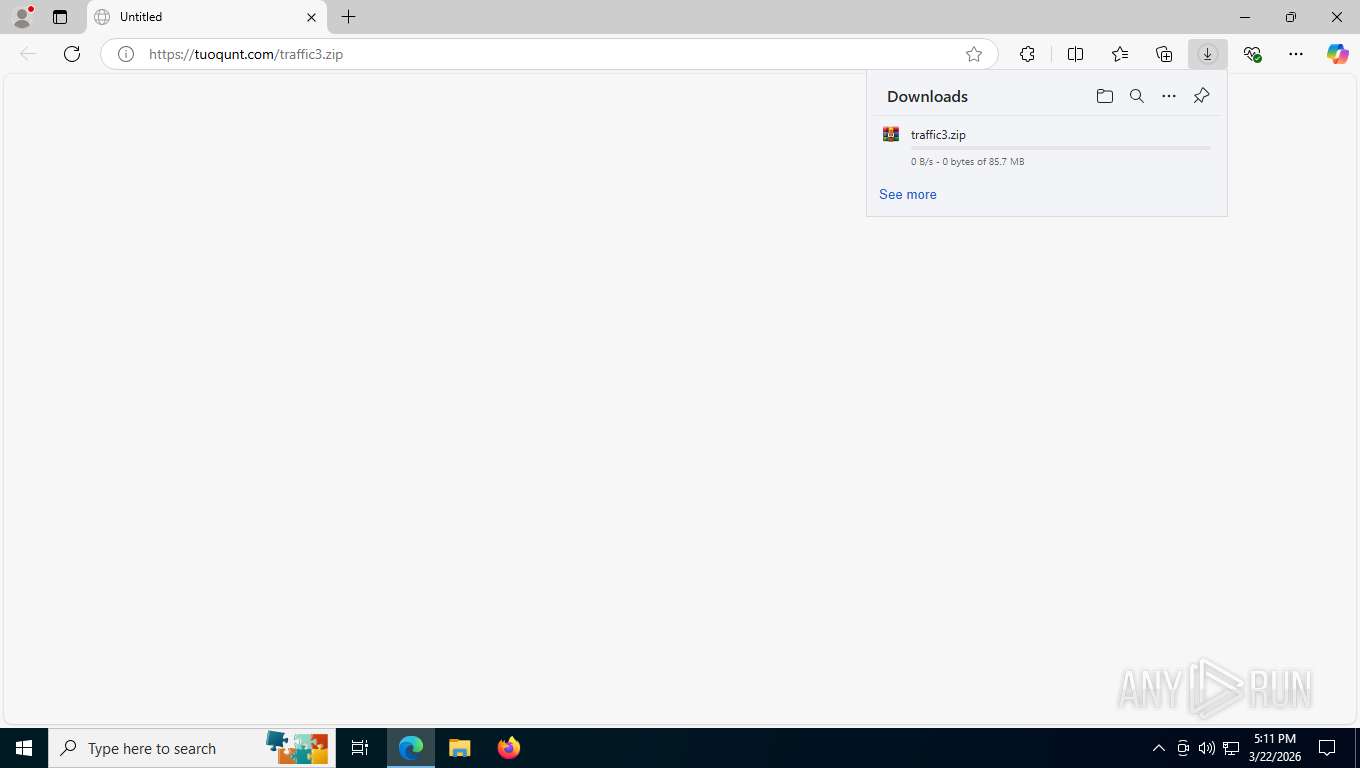
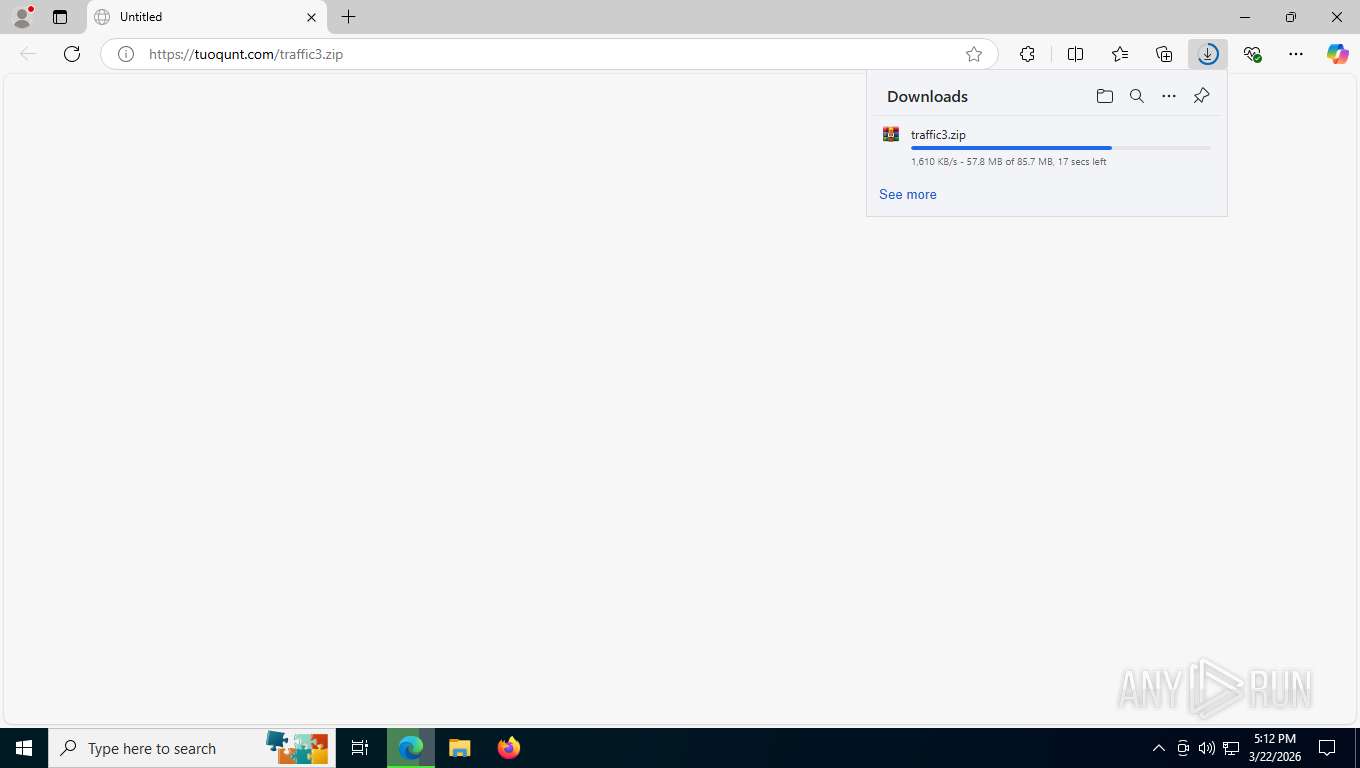
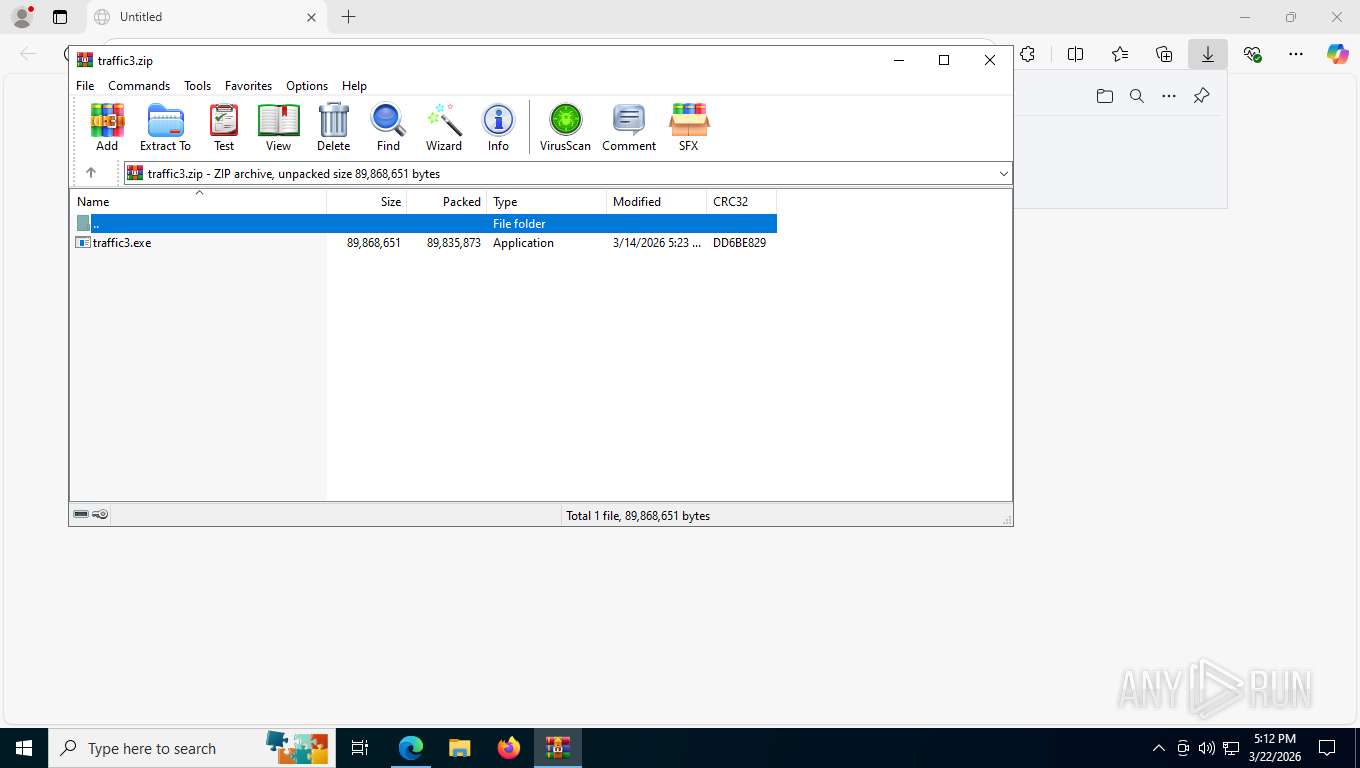
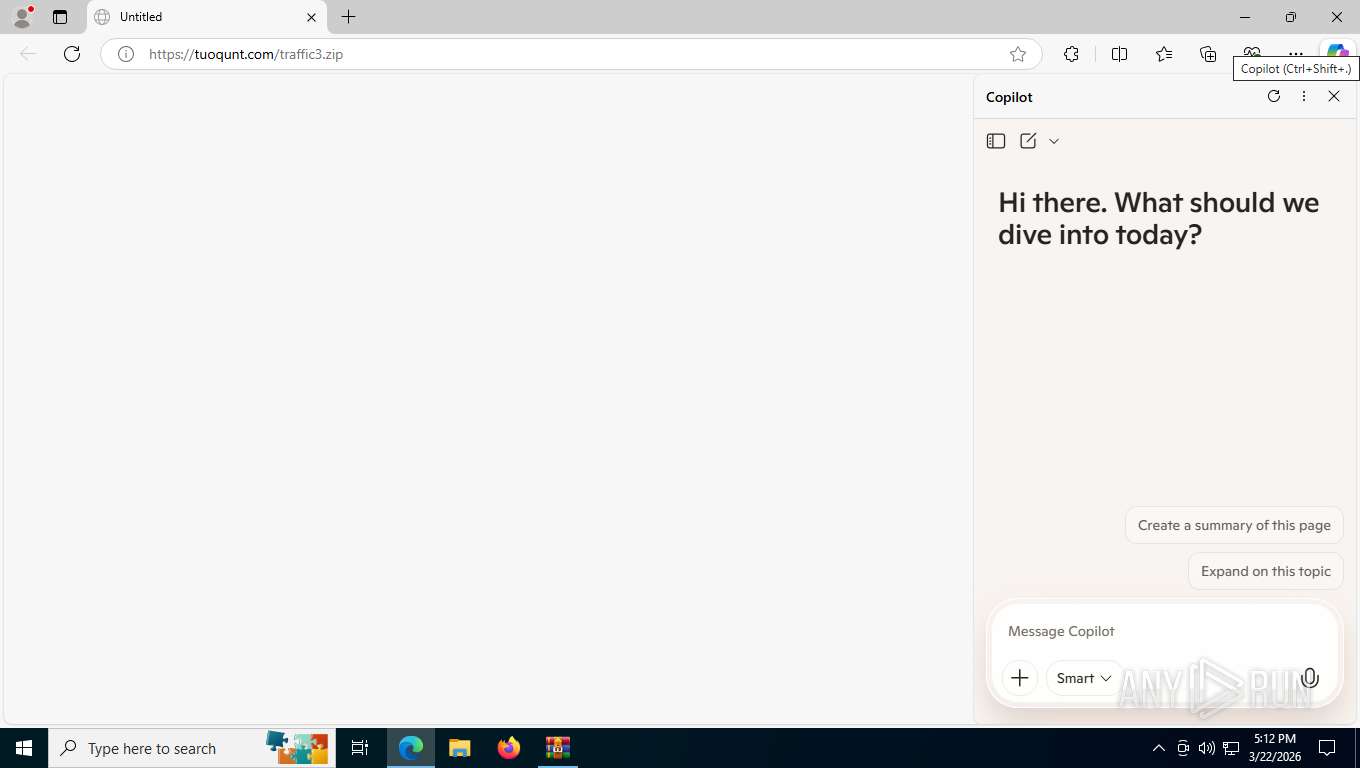
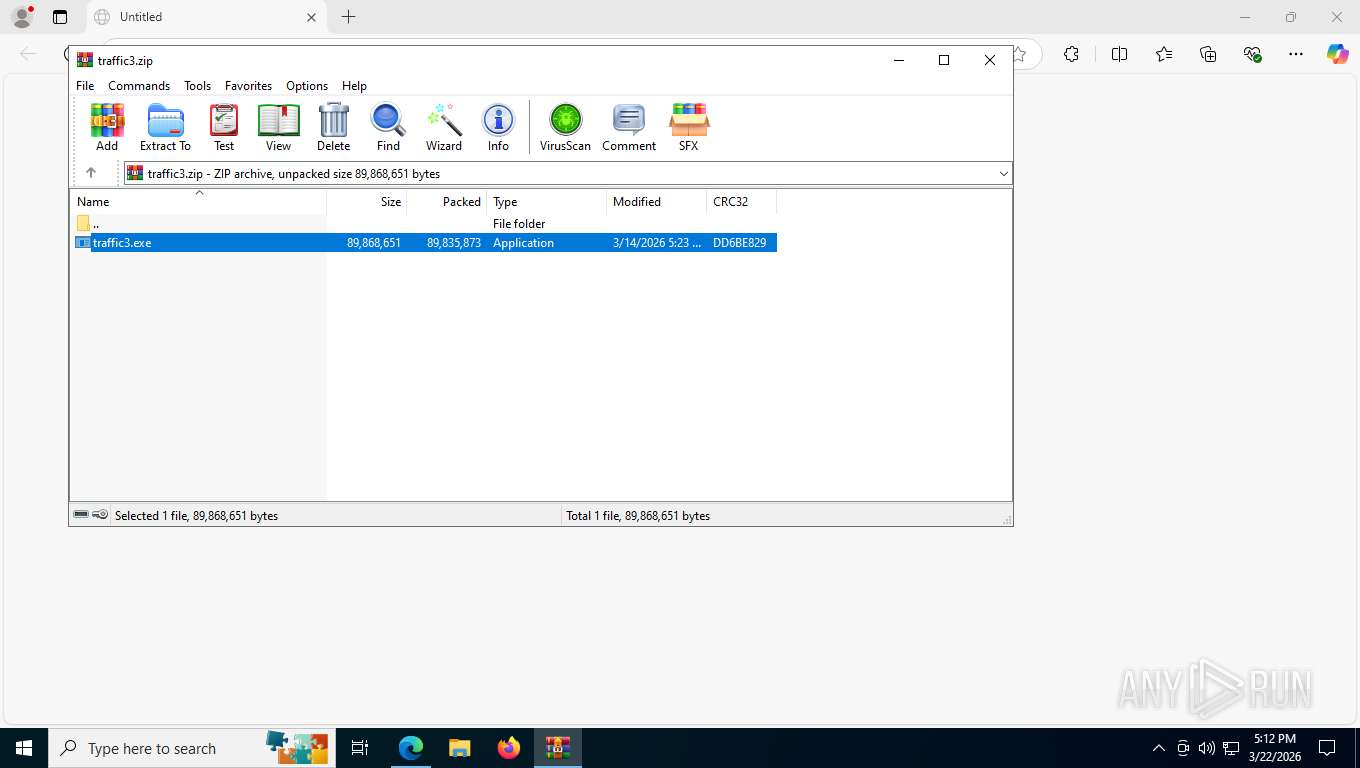
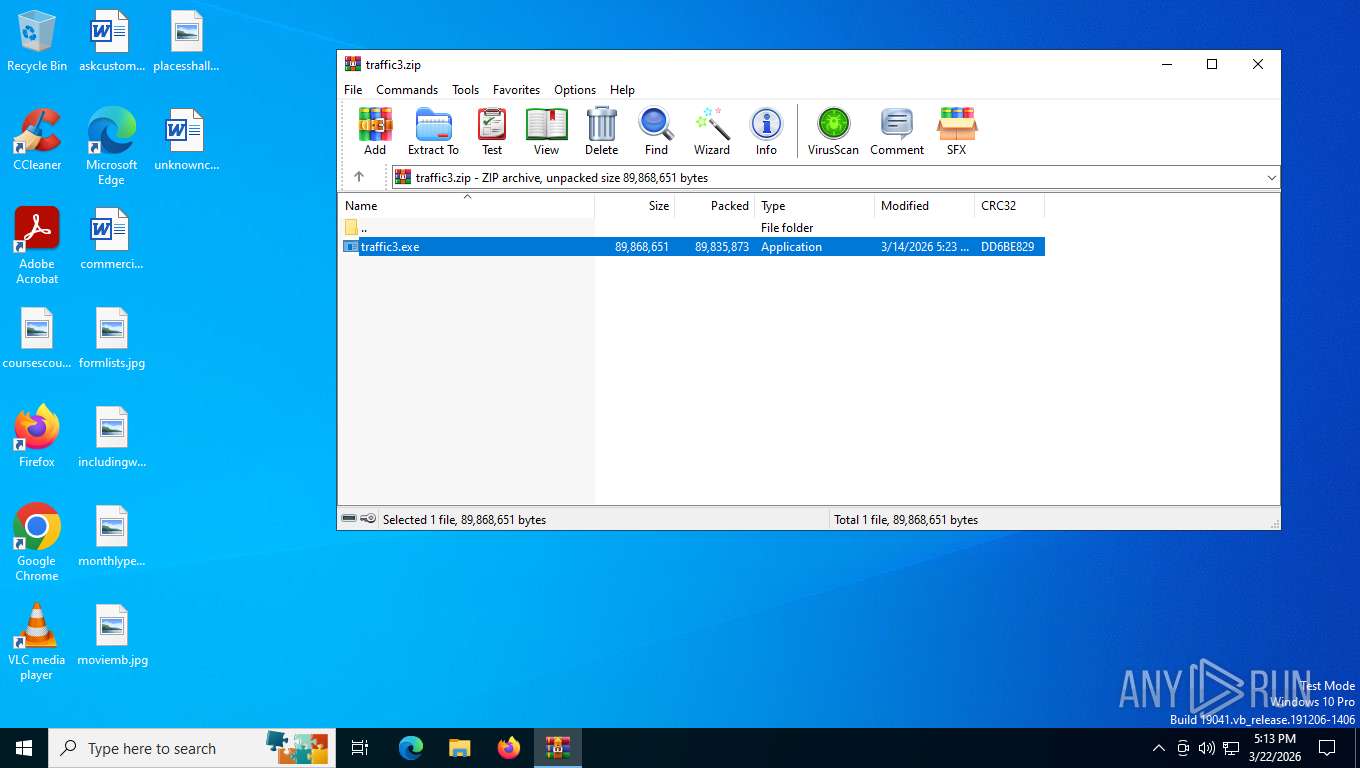
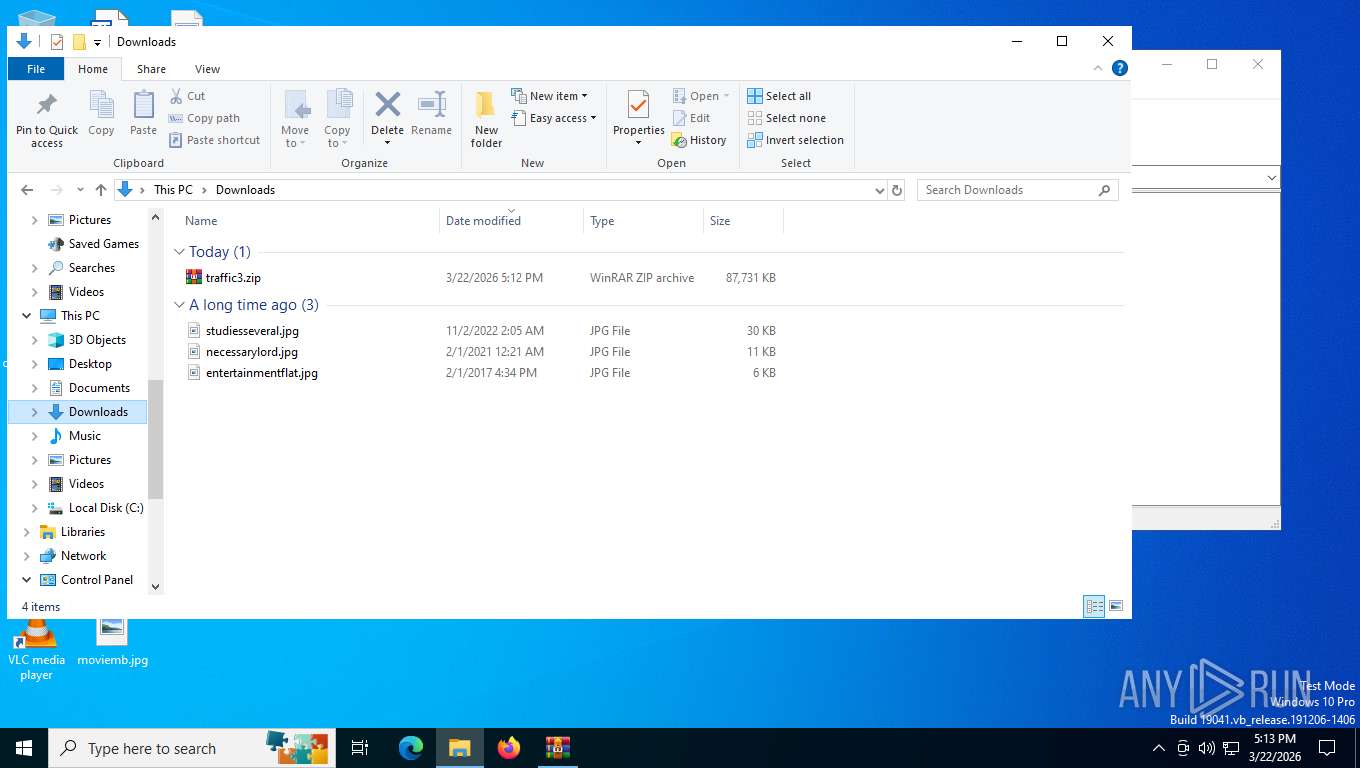
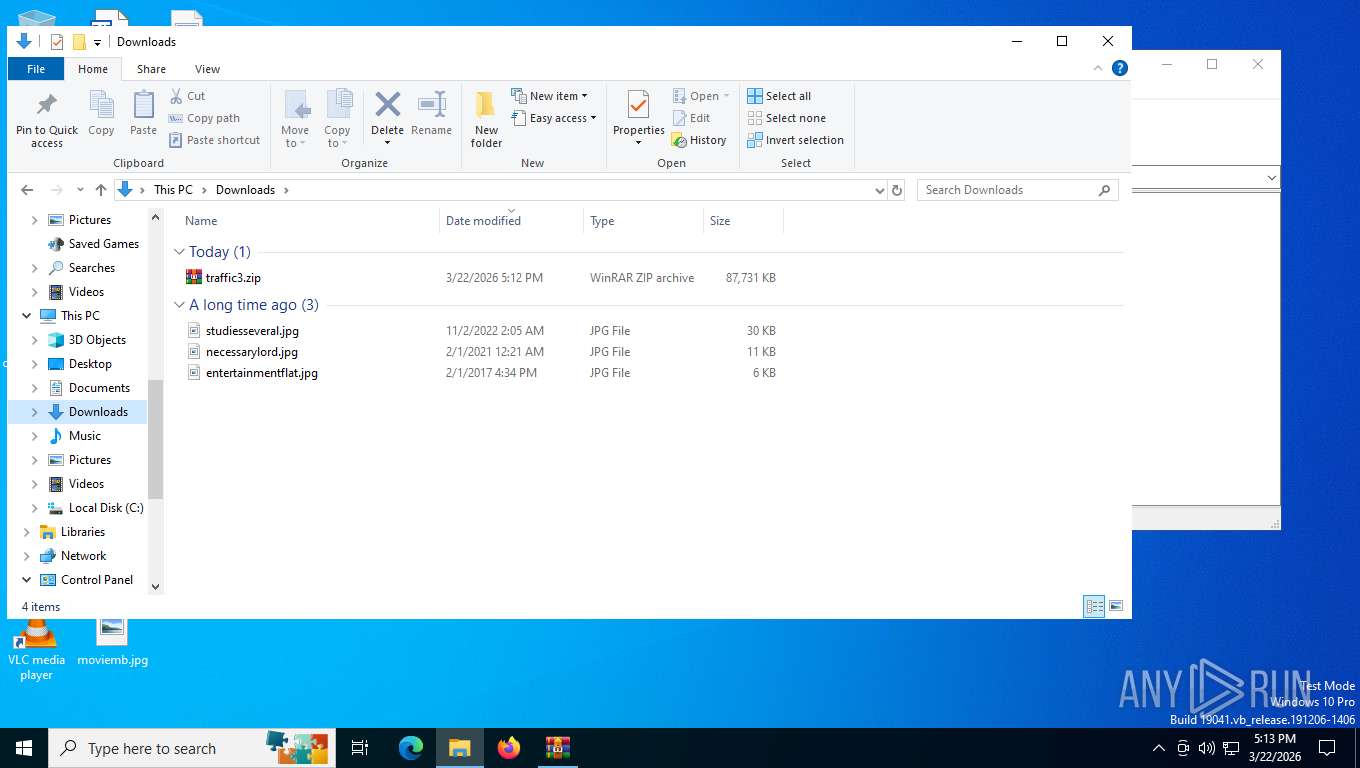
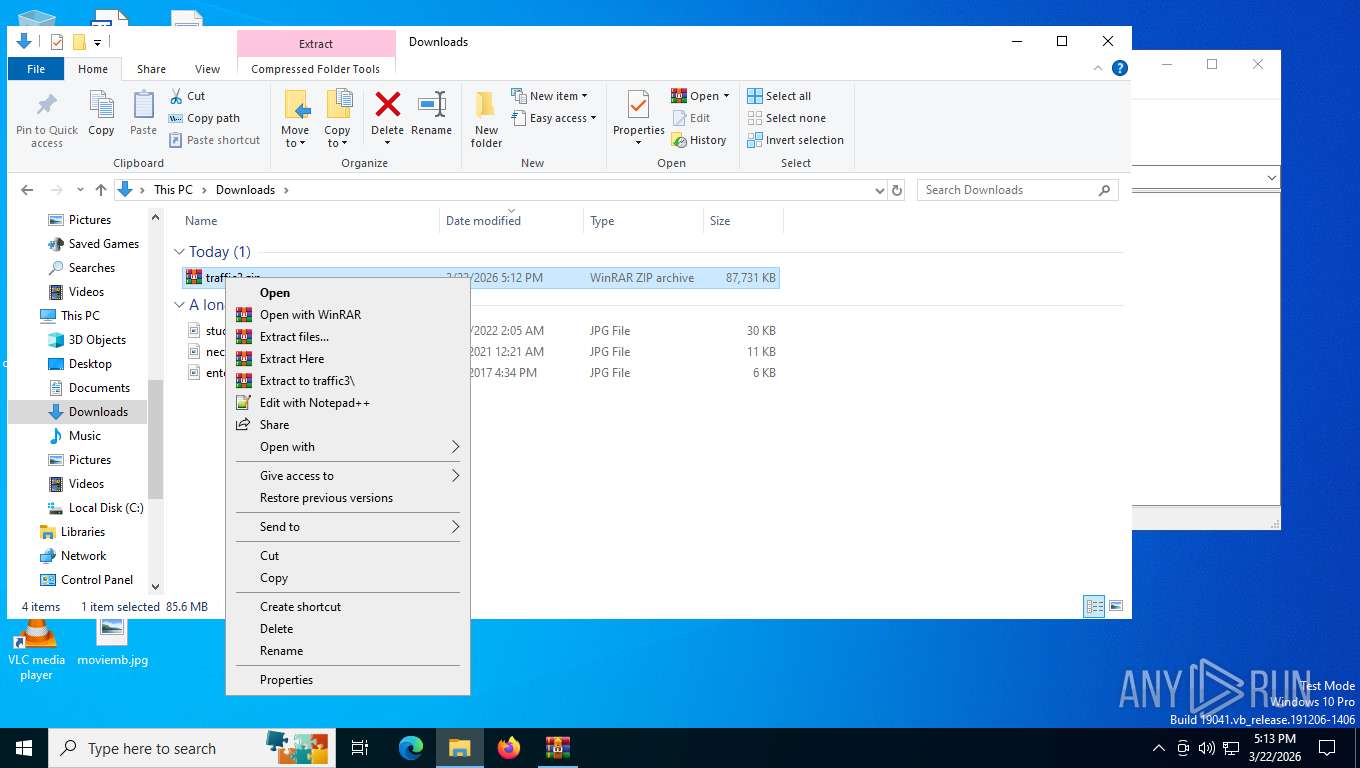
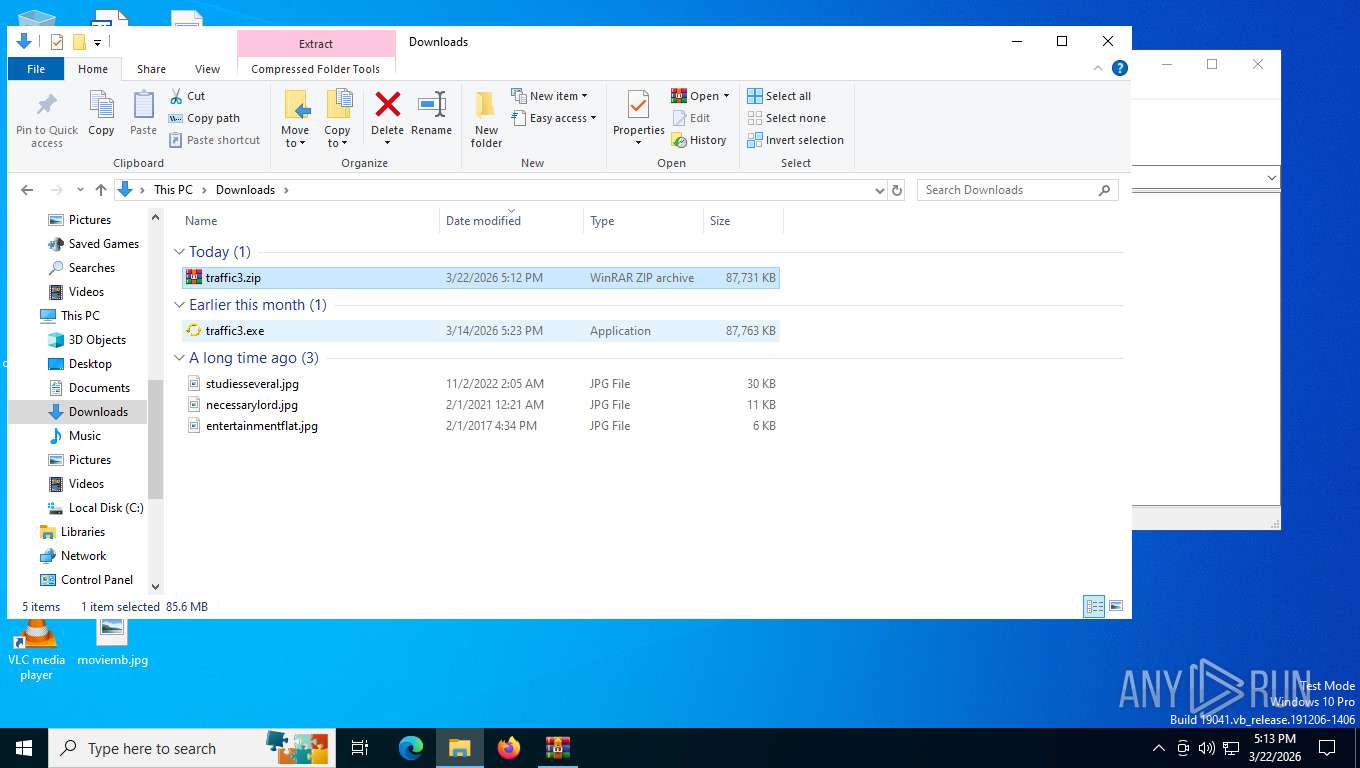
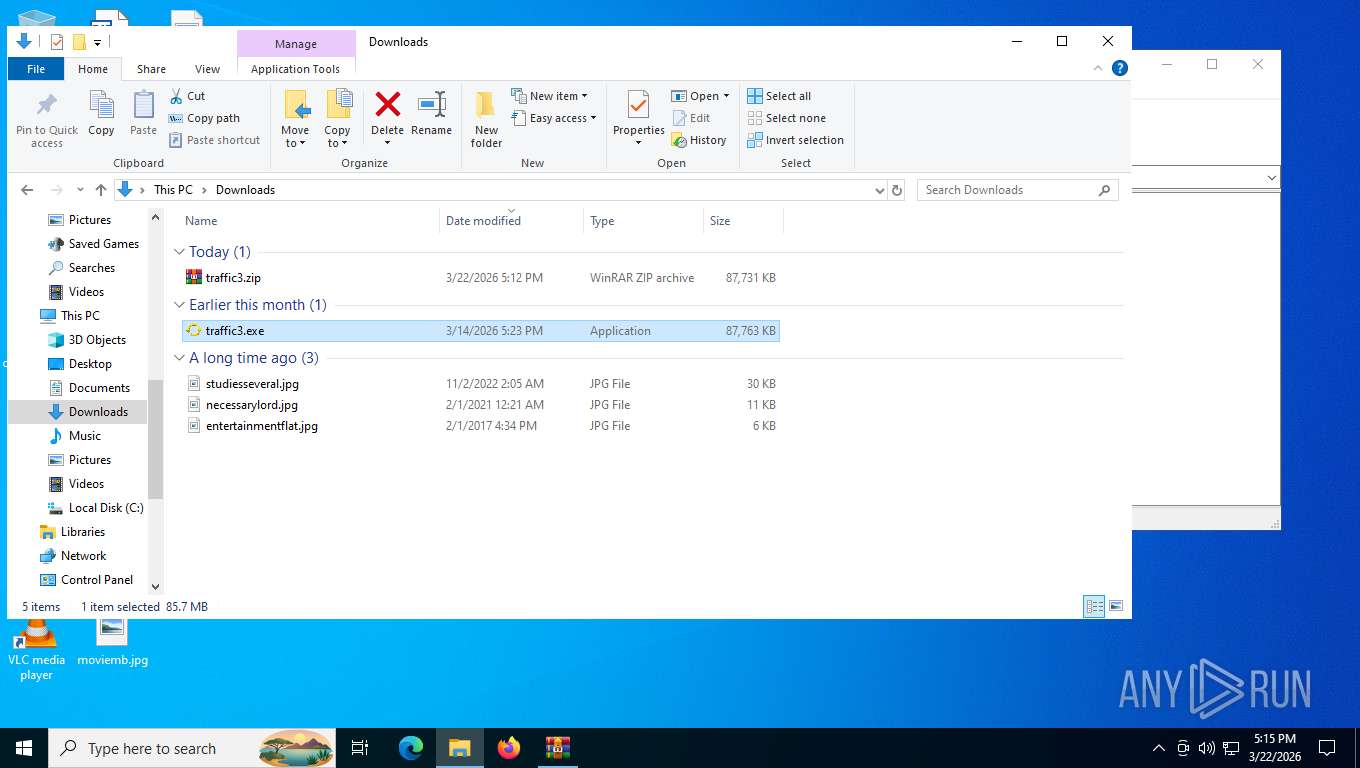
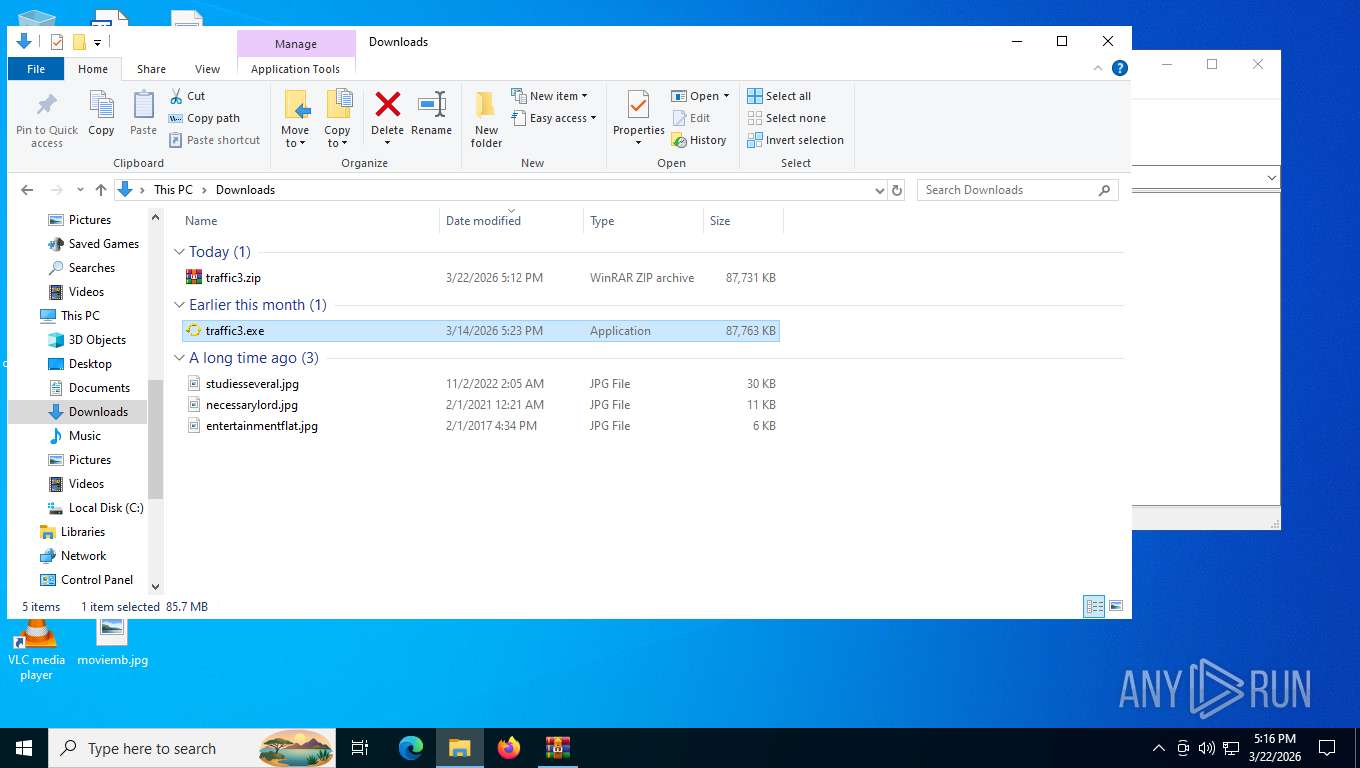
| URL: | https://tuoqunt.com/traffic3.zip |
| Full analysis: | https://app.any.run/tasks/30cbb0dc-c90e-4638-b481-ed436f277e56 |
| Verdict: | Malicious activity |
| Threats: | CastleLoader is a modern malware loader designed to quietly establish initial access and deliver follow-up payloads such as stealers, RATs, and ransomware. It focuses on stealth, flexibility, and rapid payload rotation, making it an effective tool for financially motivated threat actors and a persistent problem for enterprise defenders. |
| Analysis date: | March 22, 2026, 21:11:42 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 626850BDD5214C64988CCF29B12A0C72 |
| SHA1: | 7BB4E0C4888A7081632E9DEE1FB51A9673A445D1 |
| SHA256: | 5EA9B76E32A847BDB9D7B4586DAB6330BA6832FD13A9C36A428AAD64211F93EF |
| SSDEEP: | 3:N8YPQLFEDa4:2YP5u4 |
MALICIOUS
CASTLELOADER has been detected (YARA)
- pythonw.exe (PID: 2304)
- pythonw.exe (PID: 1268)
SUSPICIOUS
Contacting a server suspected of hosting an CnC
- msedge.exe (PID: 4136)
Process drops python dynamic module
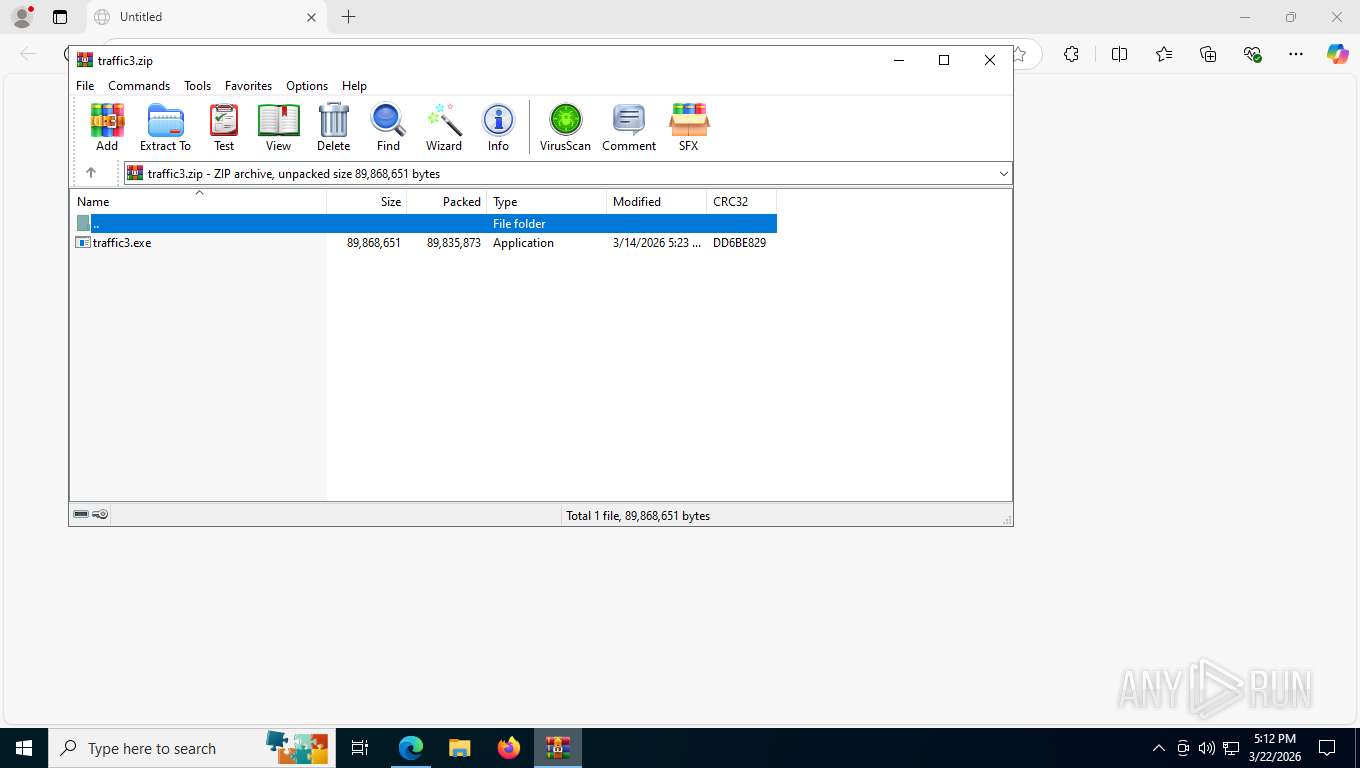
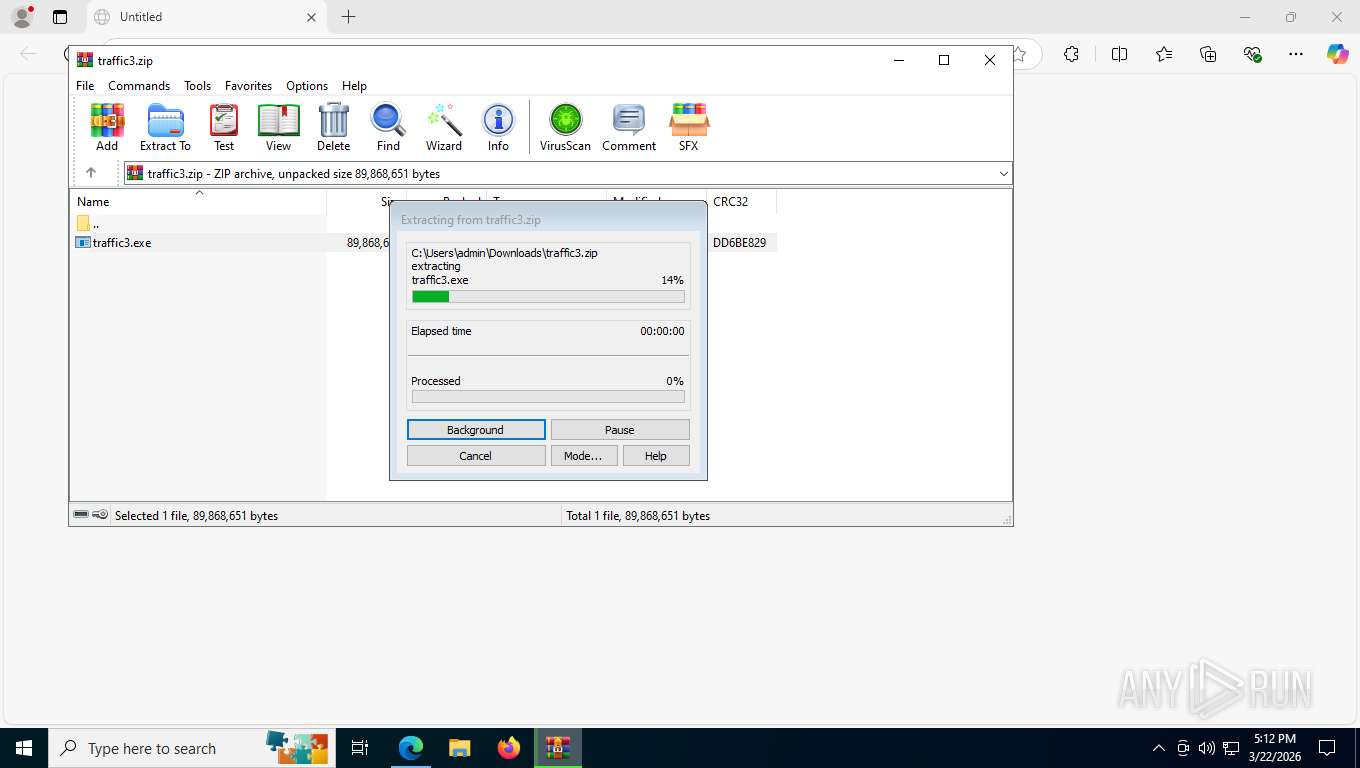
- traffic3.exe (PID: 6732)
Loads Python modules
- pythonw.exe (PID: 2304)
- pythonw.exe (PID: 1268)
INFO
Checks supported languages
- identity_helper.exe (PID: 4772)
- traffic3.exe (PID: 6732)
- pythonw.exe (PID: 2304)
- identity_helper.exe (PID: 6592)
- traffic3.exe (PID: 8744)
- pythonw.exe (PID: 1268)
Application launched itself
- msedge.exe (PID: 5784)
- msedge.exe (PID: 8860)
Reads Environment values
- identity_helper.exe (PID: 4772)
- identity_helper.exe (PID: 6592)
Reads the computer name
- identity_helper.exe (PID: 4772)
- traffic3.exe (PID: 6732)
- pythonw.exe (PID: 2304)
- identity_helper.exe (PID: 6592)
- pythonw.exe (PID: 1268)
- traffic3.exe (PID: 8744)
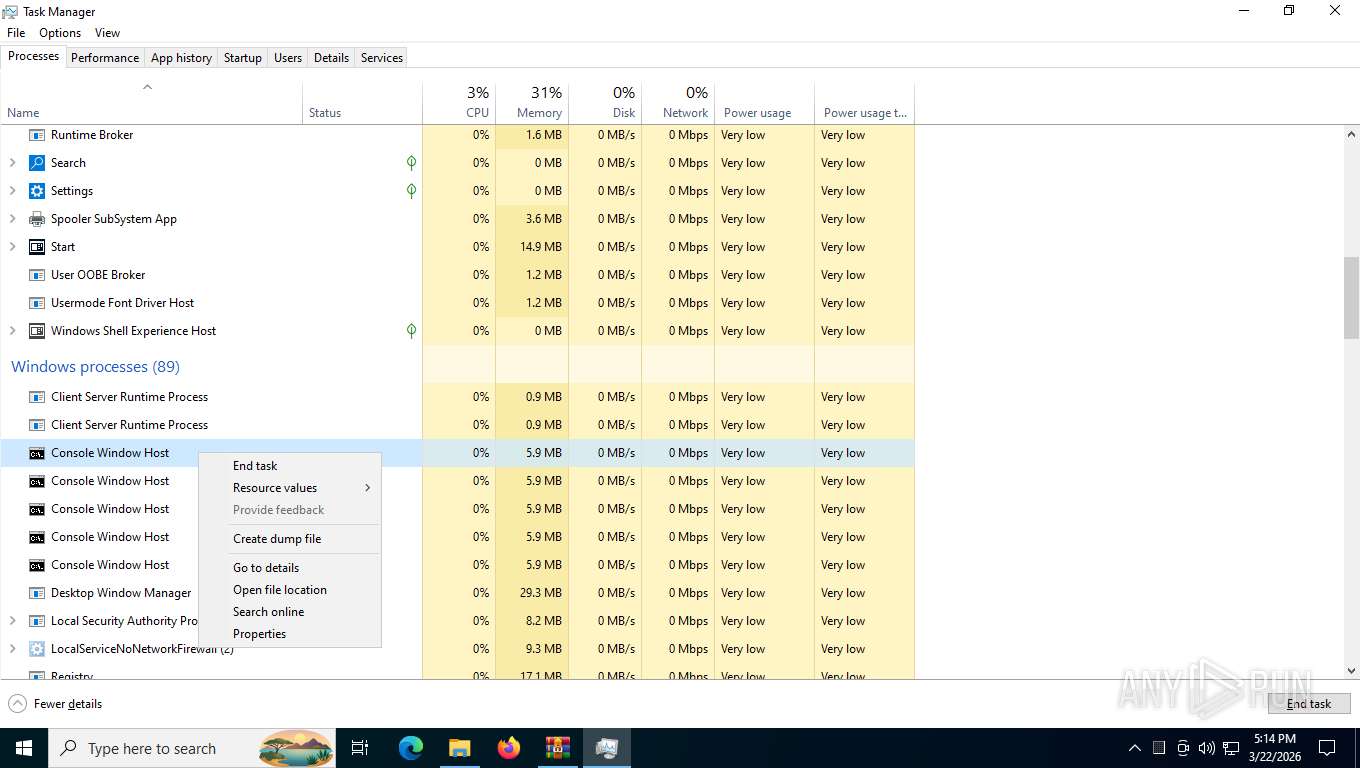
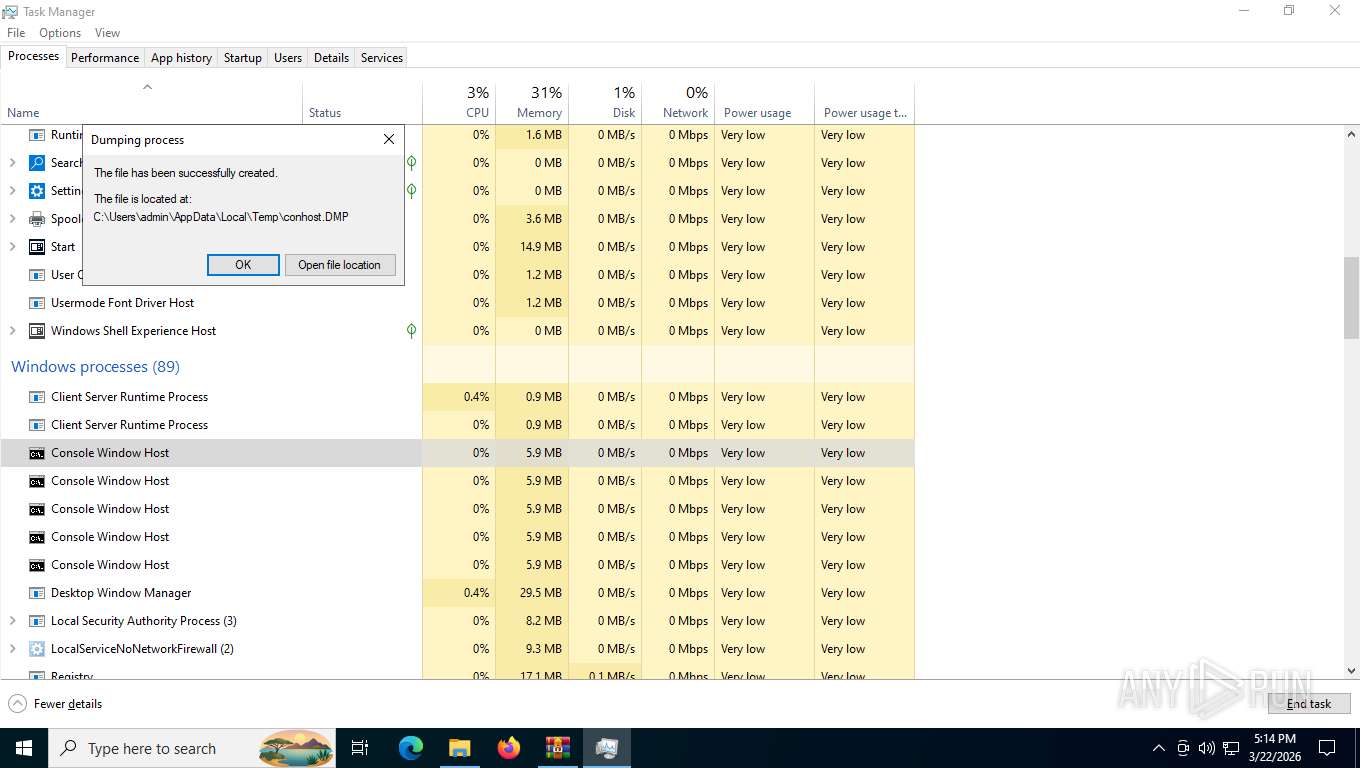
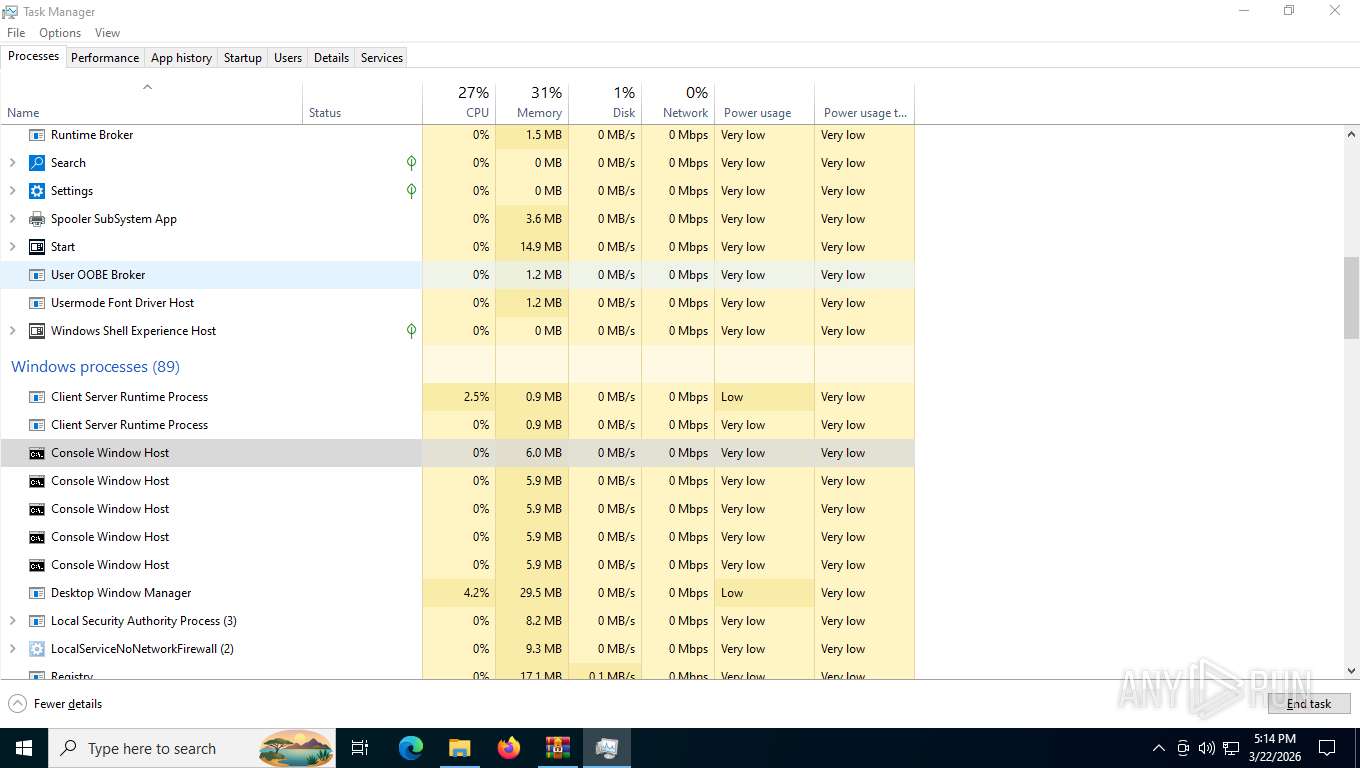
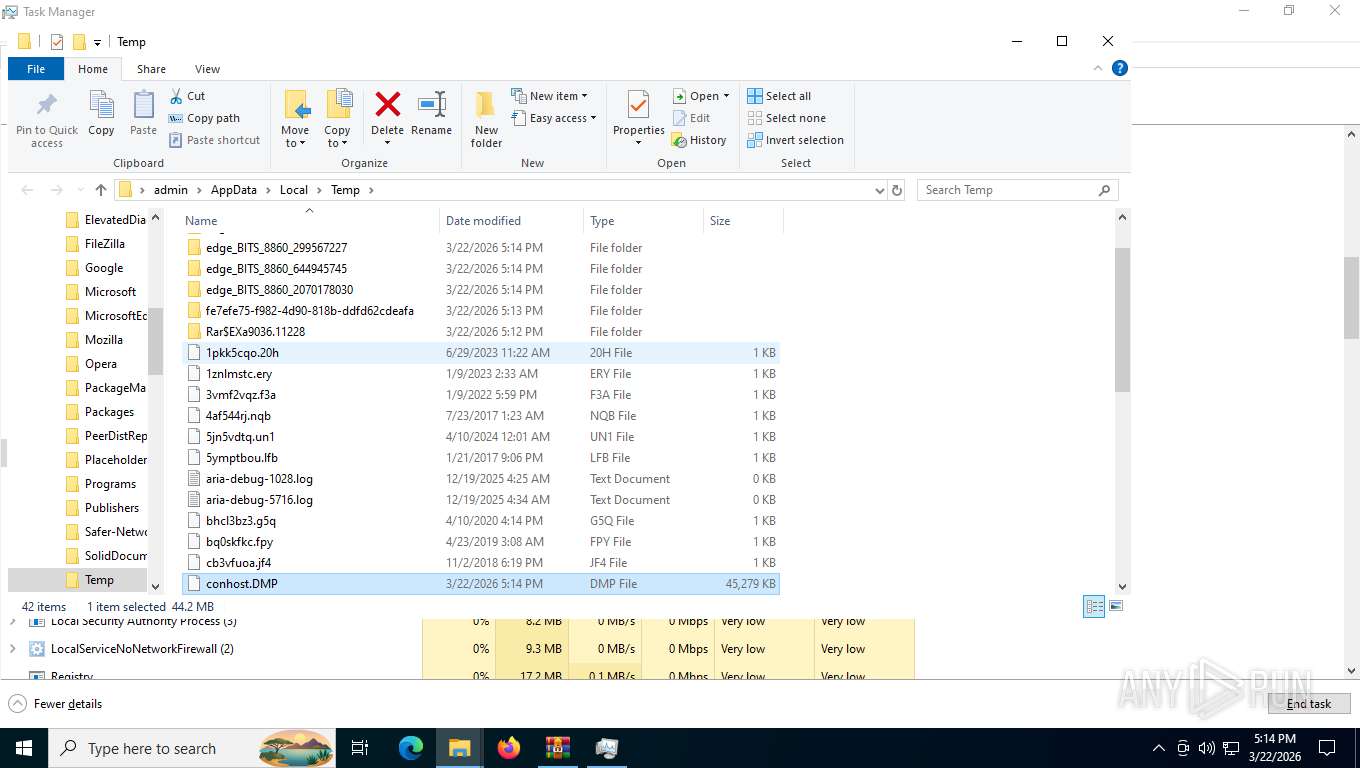
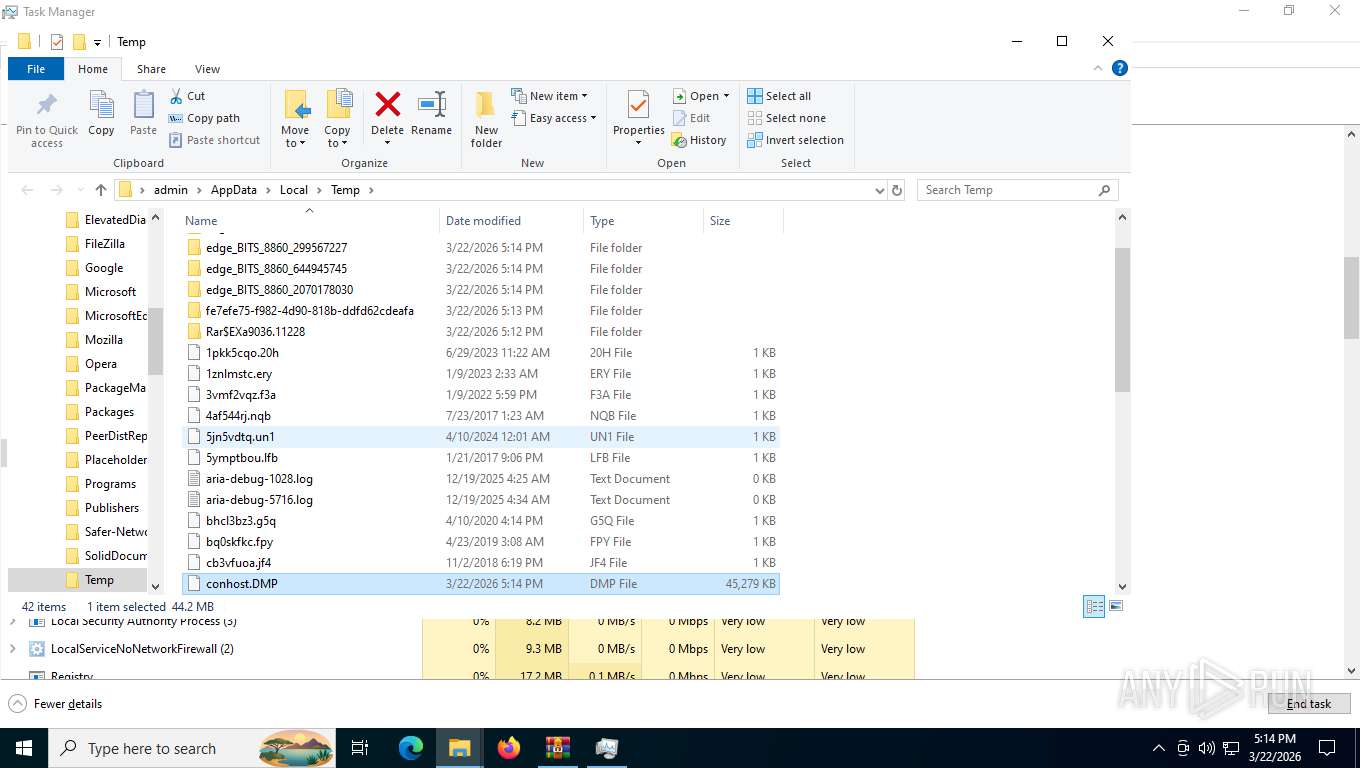
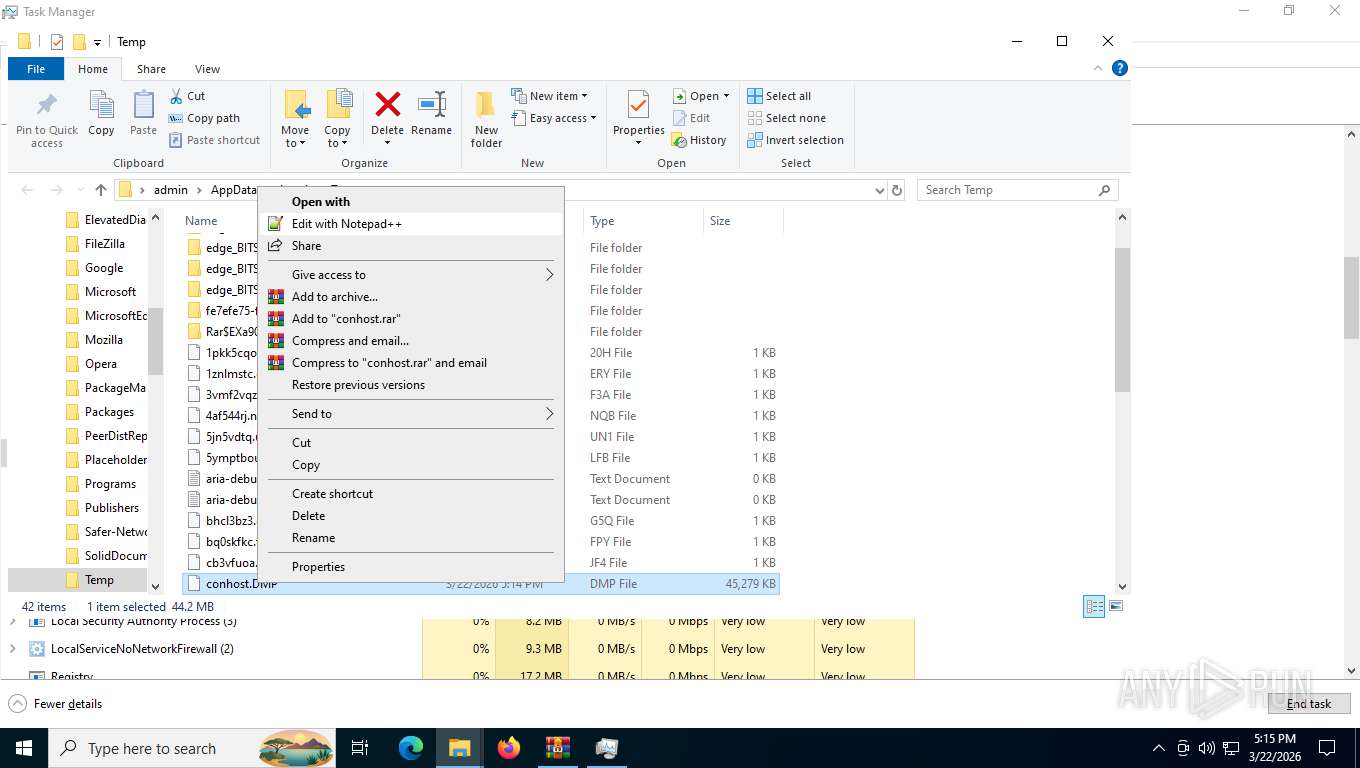
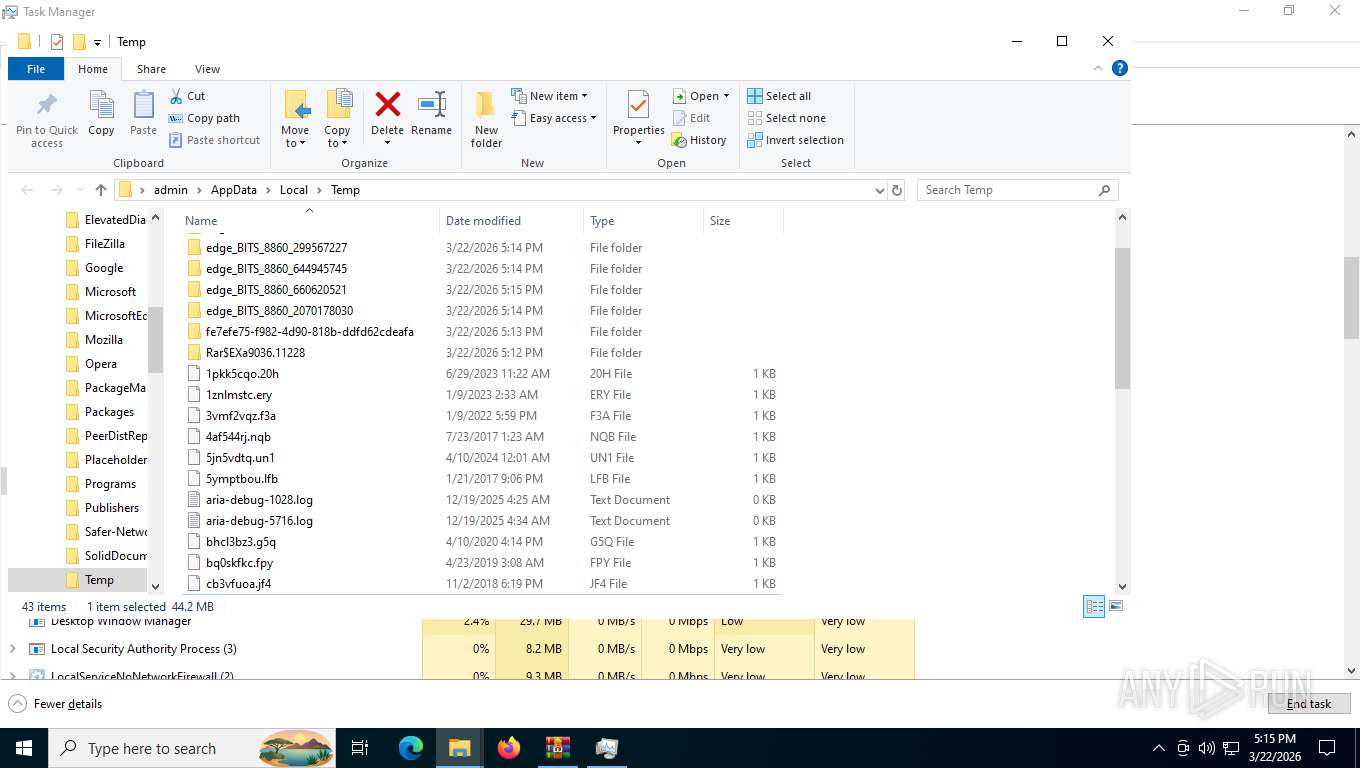
Create files in a temporary directory
- traffic3.exe (PID: 6732)
- traffic3.exe (PID: 8744)
- Taskmgr.exe (PID: 1132)
Reads security settings of Internet Explorer
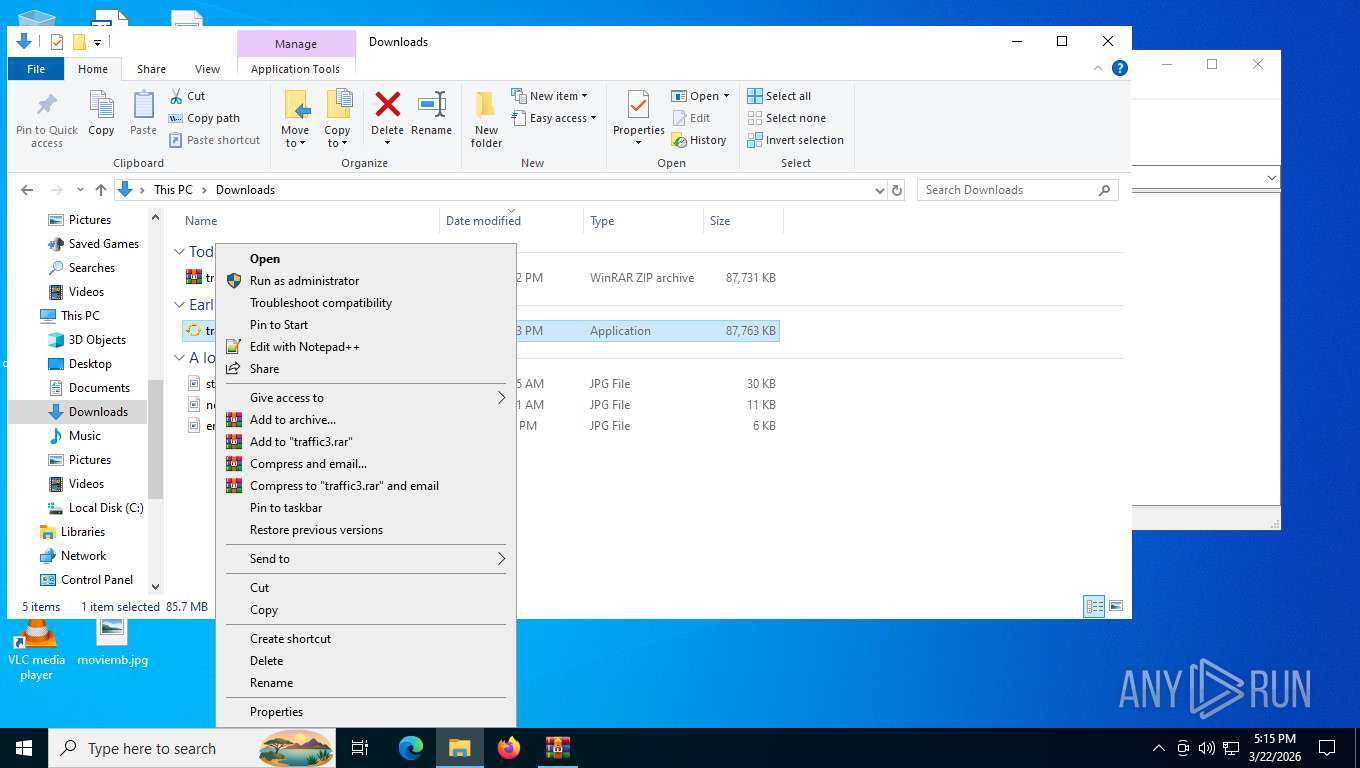
- WinRAR.exe (PID: 9036)
- traffic3.exe (PID: 6732)
- pythonw.exe (PID: 2304)
- pythonw.exe (PID: 1268)
- Taskmgr.exe (PID: 1132)
- traffic3.exe (PID: 8744)
Python executable
- pythonw.exe (PID: 2304)
- pythonw.exe (PID: 1268)
Reads the machine GUID from the registry
- pythonw.exe (PID: 2304)
- pythonw.exe (PID: 1268)
Creates files in the program directory
- pythonw.exe (PID: 2304)
Creates files or folders in the user directory
- WerFault.exe (PID: 8180)
- pythonw.exe (PID: 2304)
- WerFault.exe (PID: 8576)
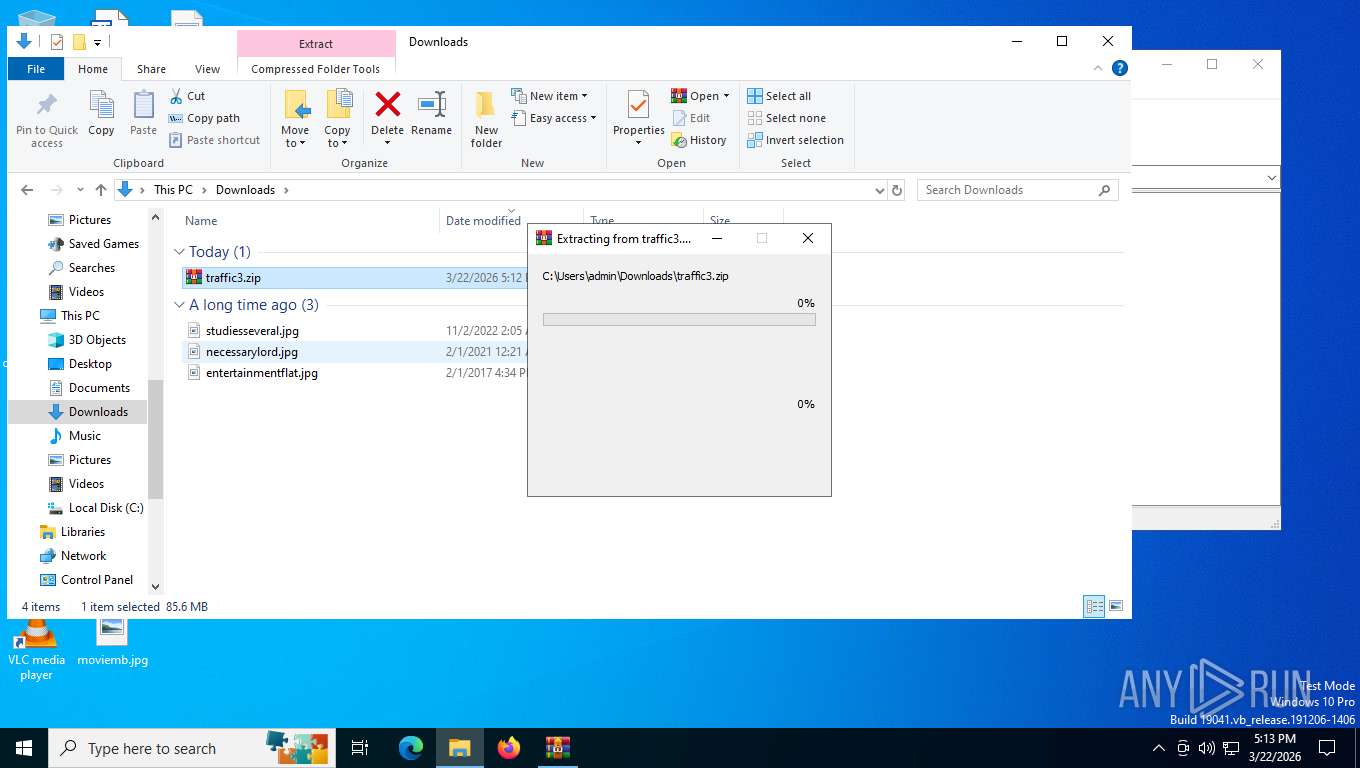
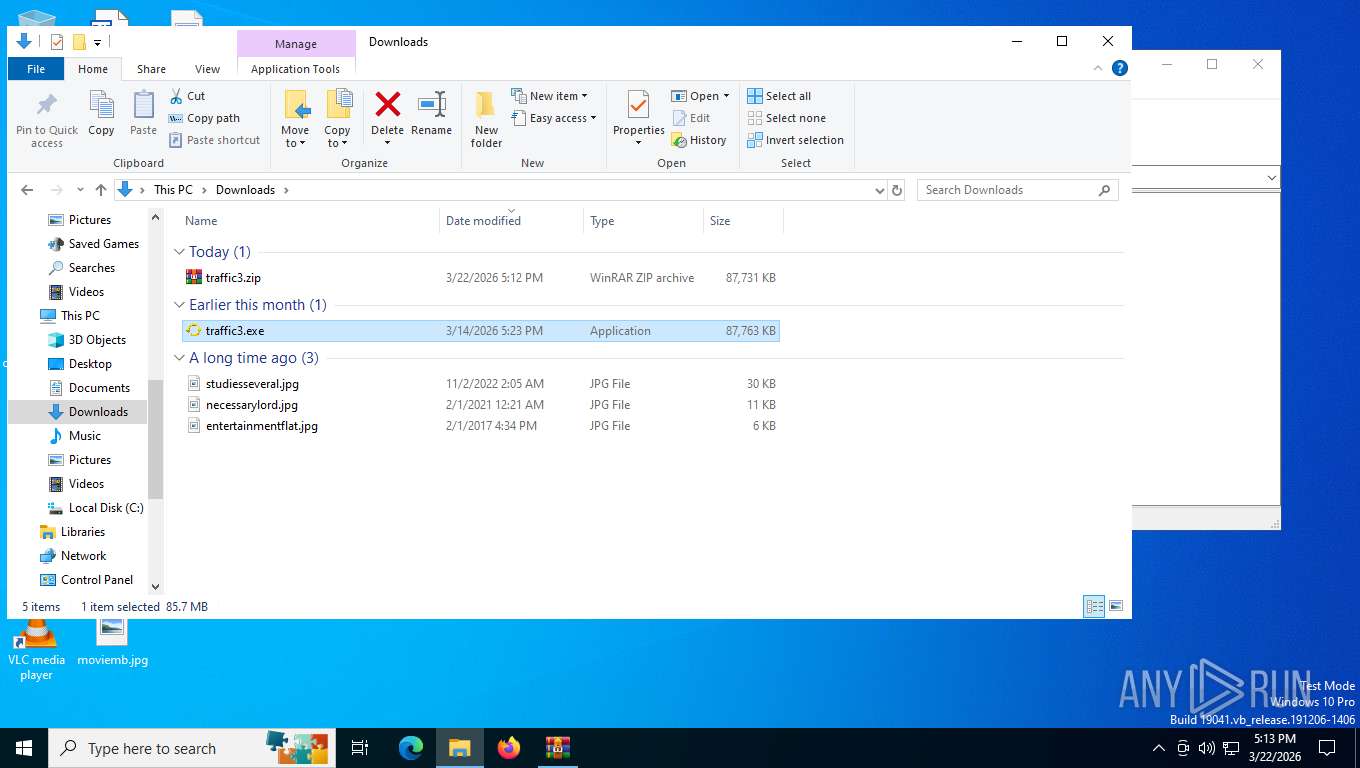
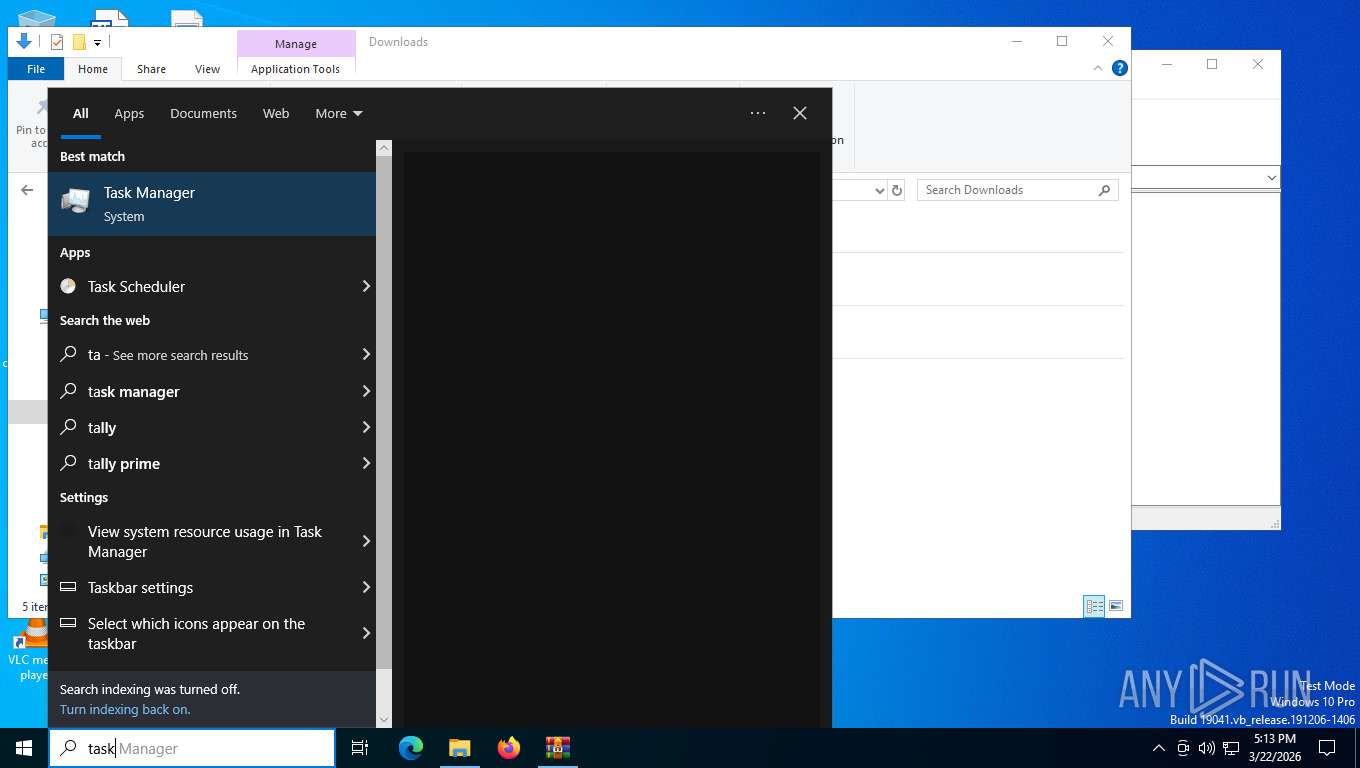
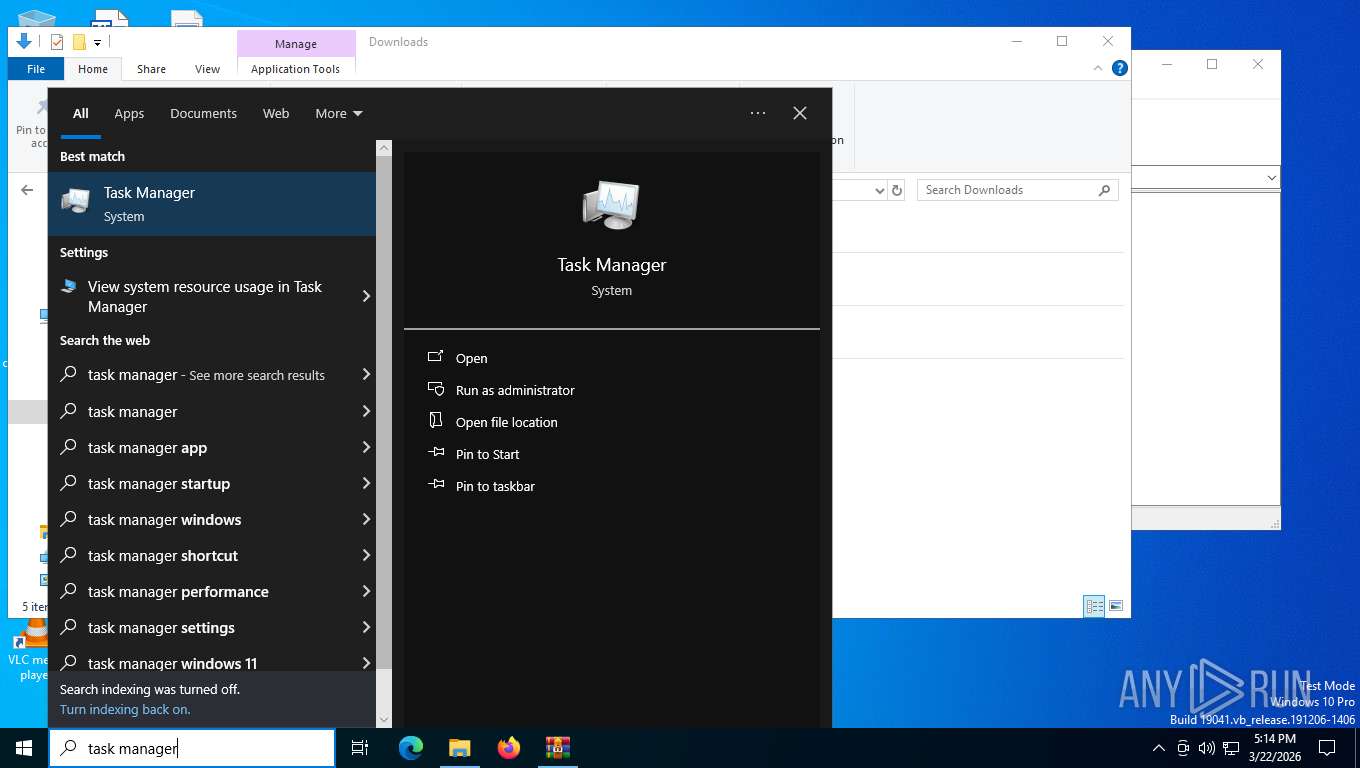
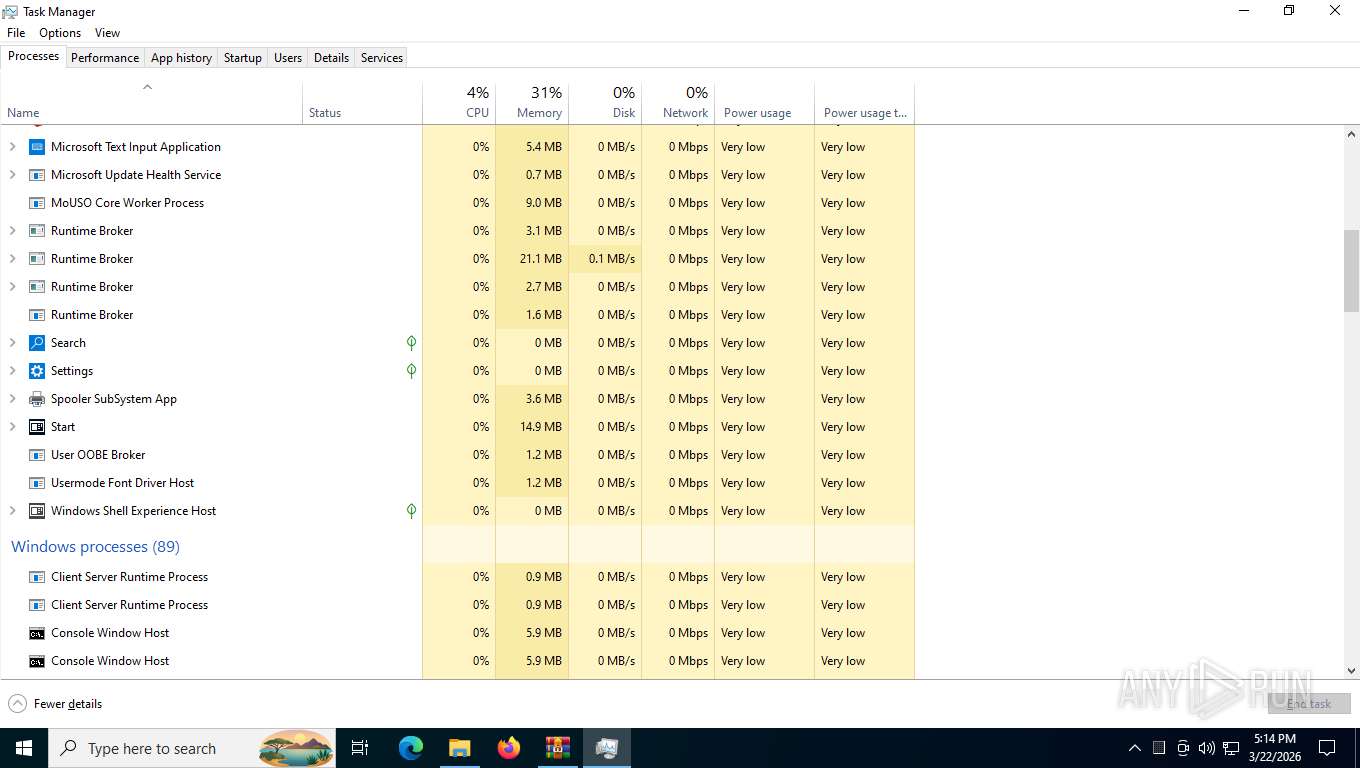
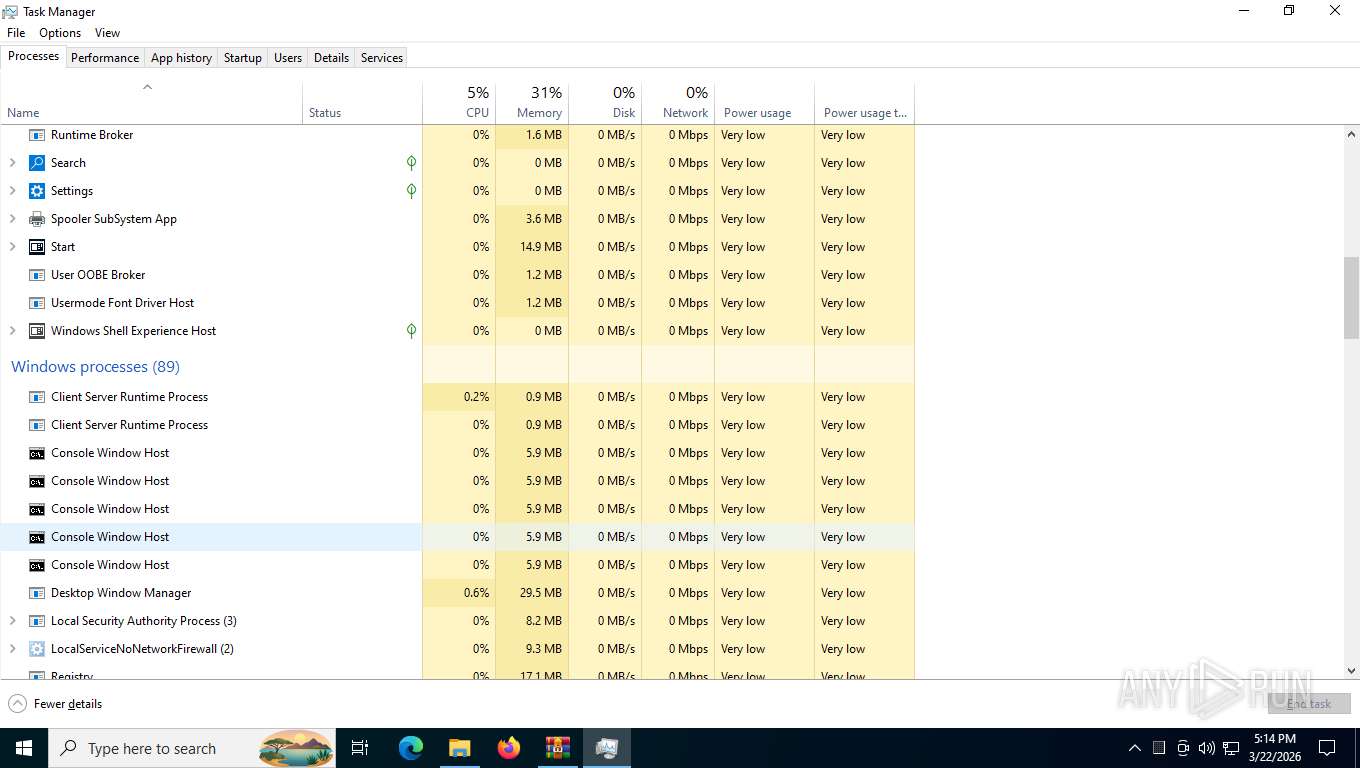
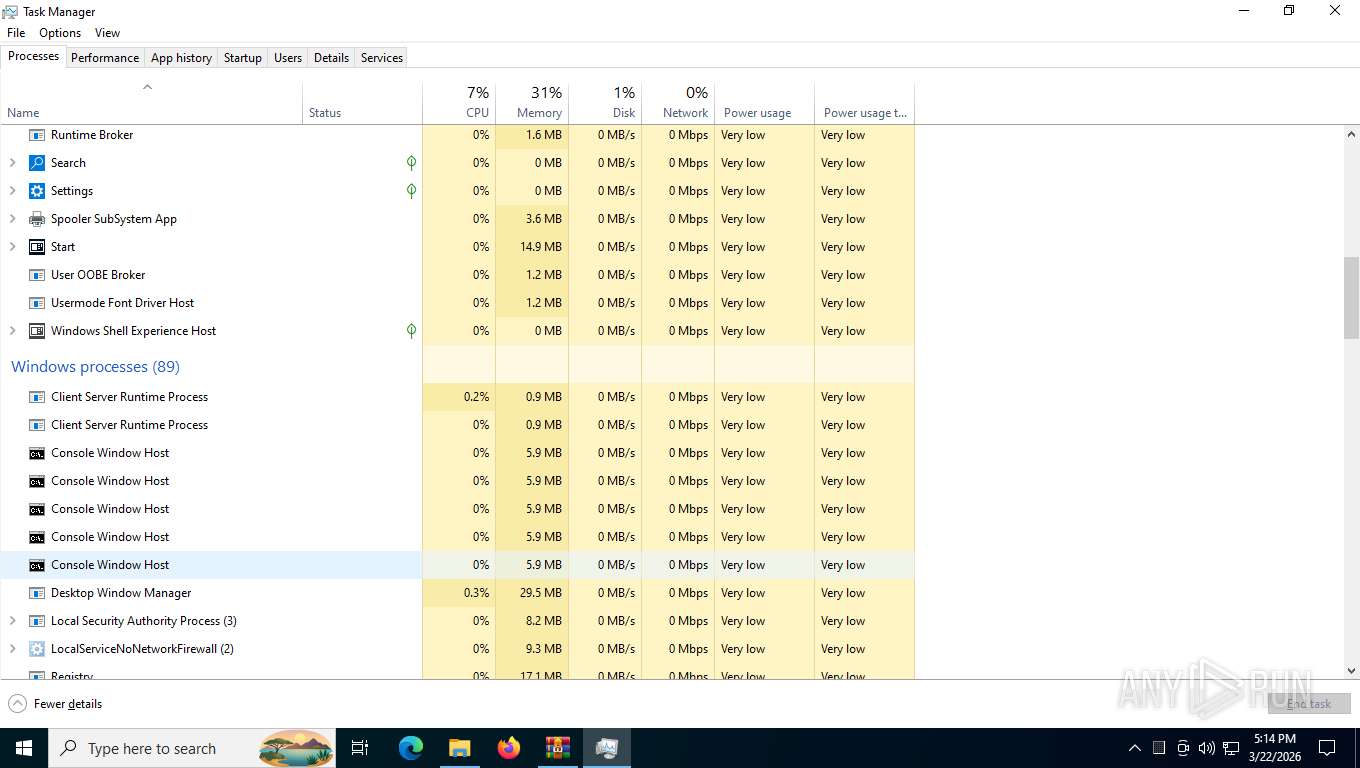
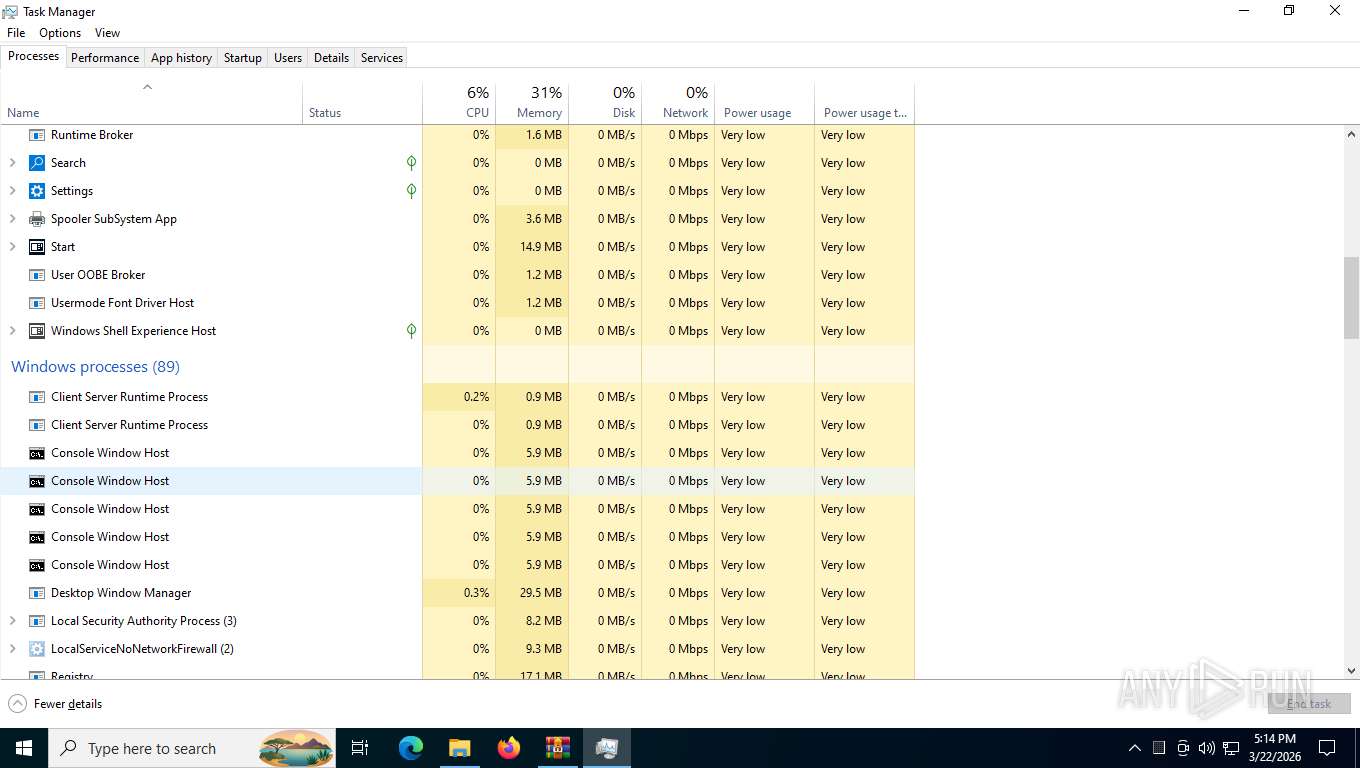
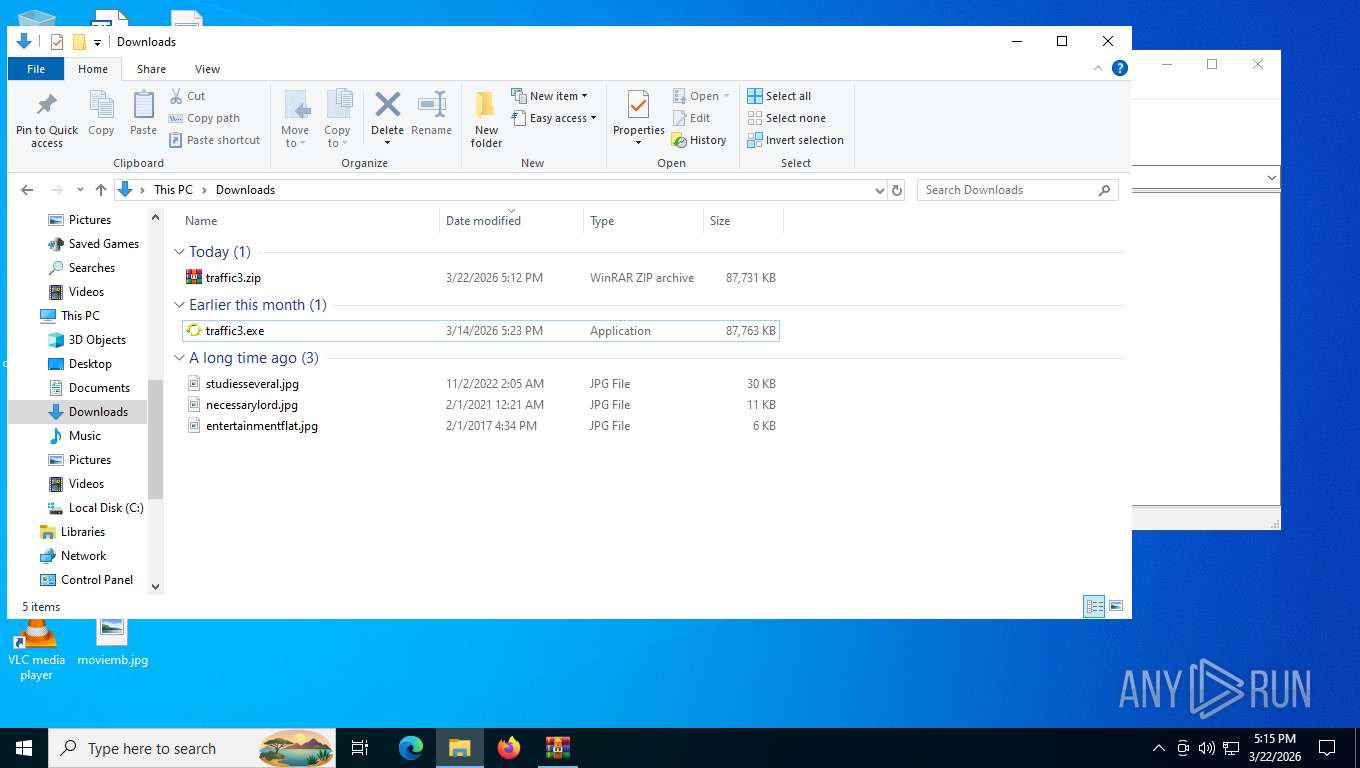
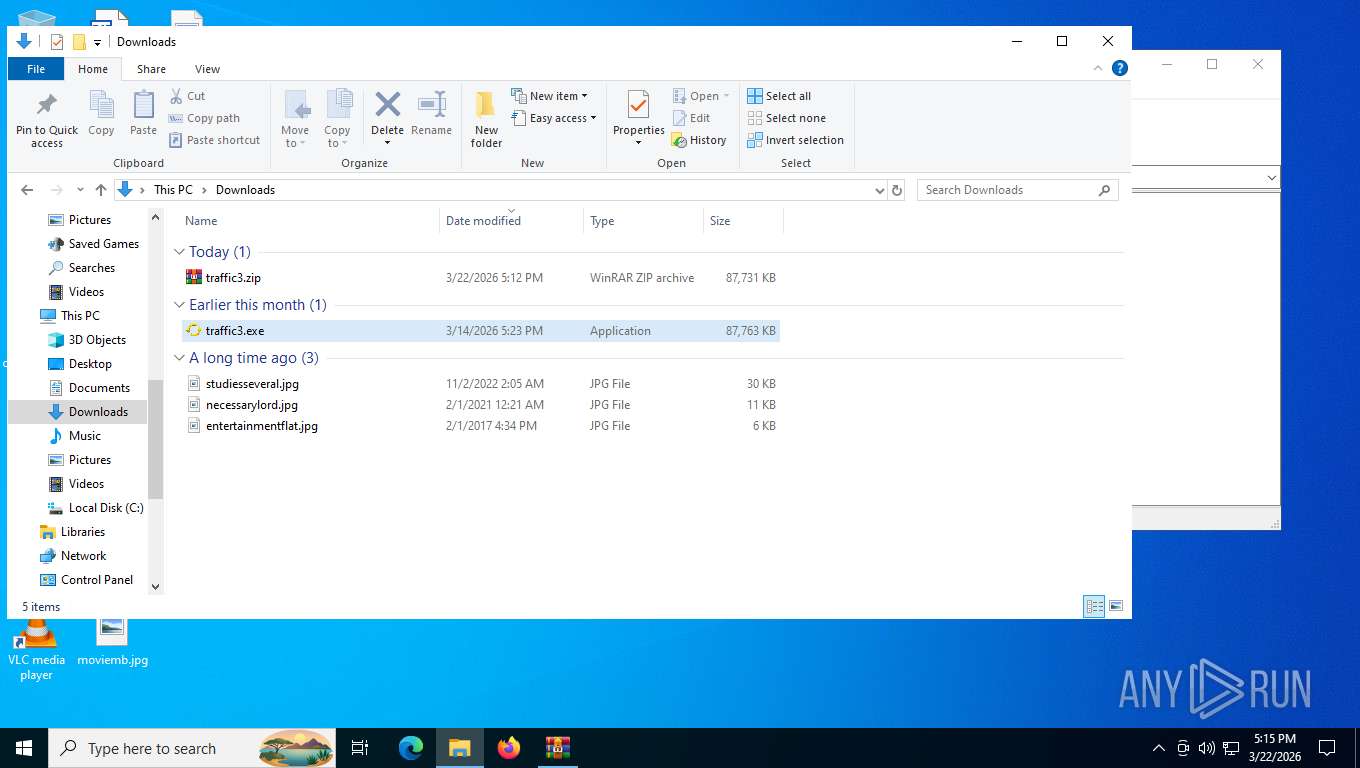
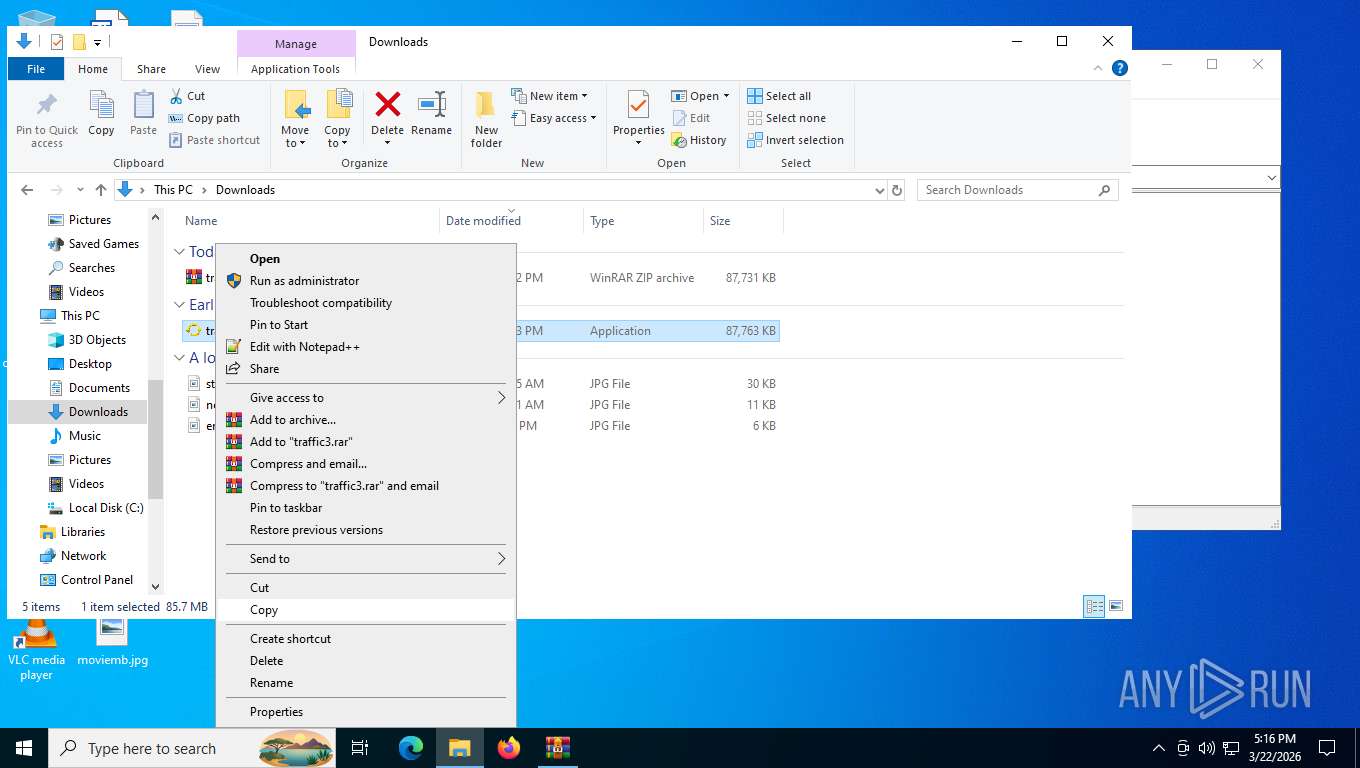
Manual execution by a user
- traffic3.exe (PID: 8744)
- WinRAR.exe (PID: 4124)
- Taskmgr.exe (PID: 4280)
- Taskmgr.exe (PID: 1132)
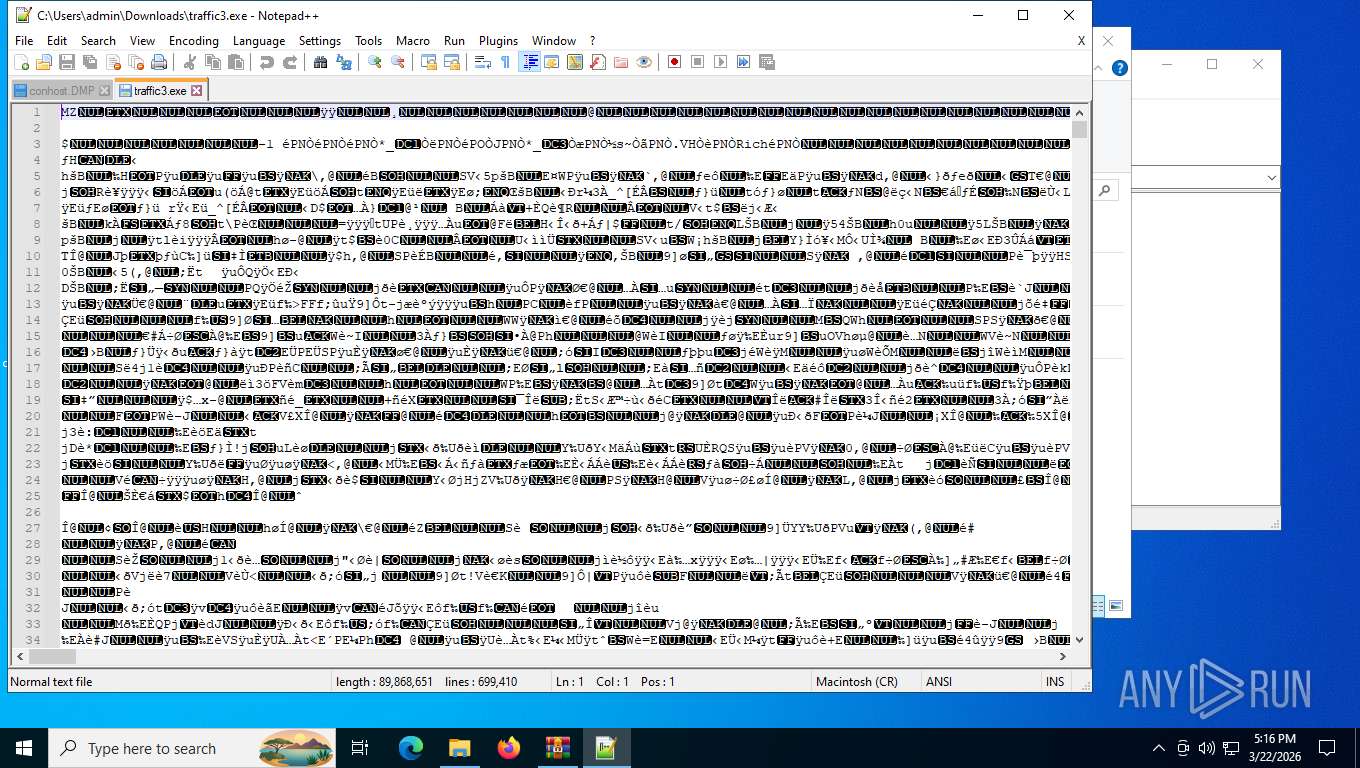
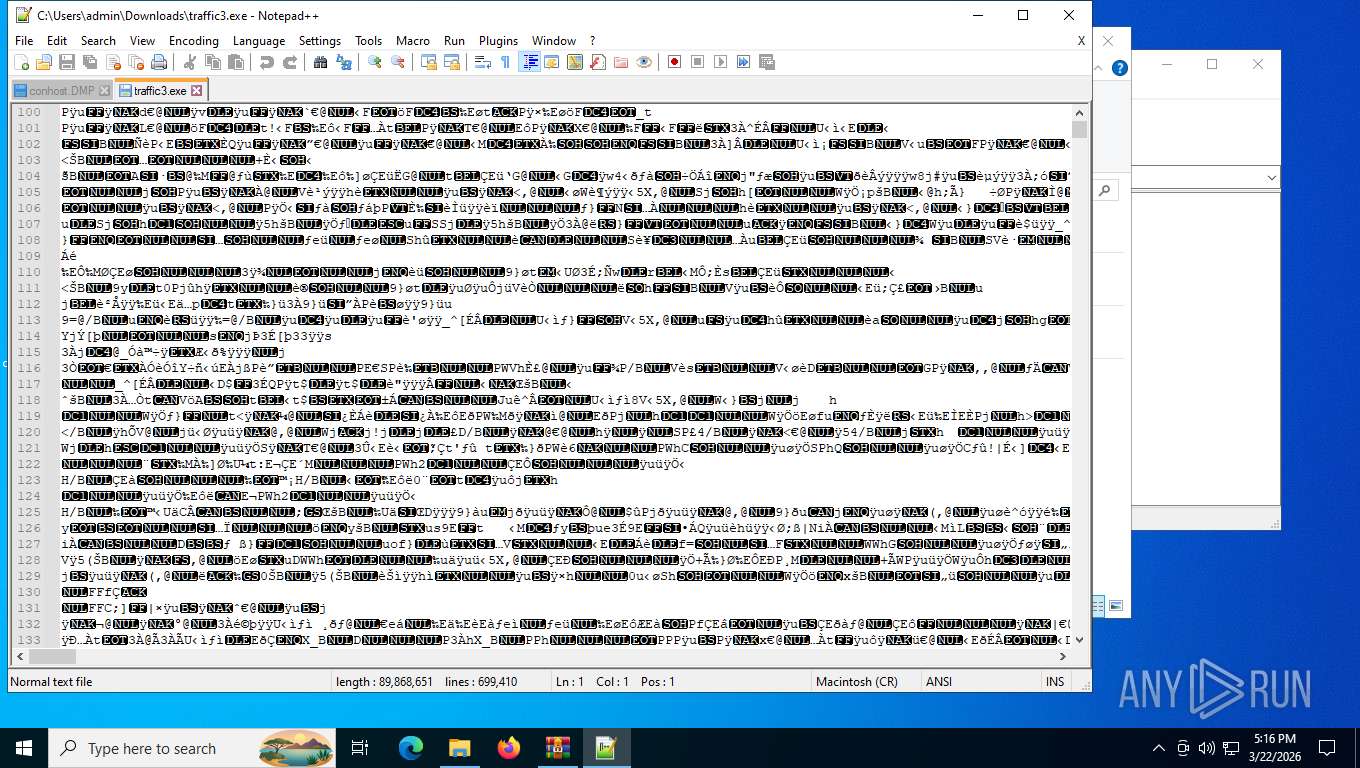
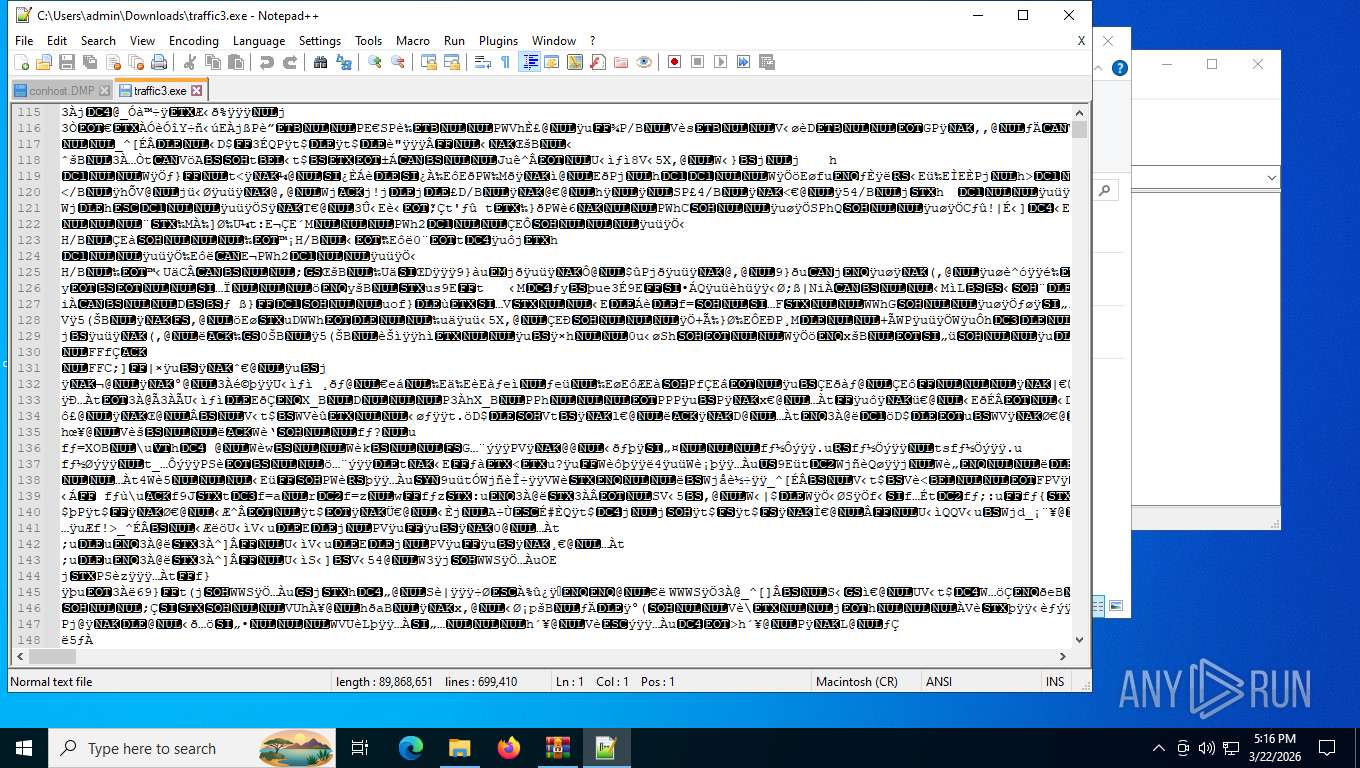
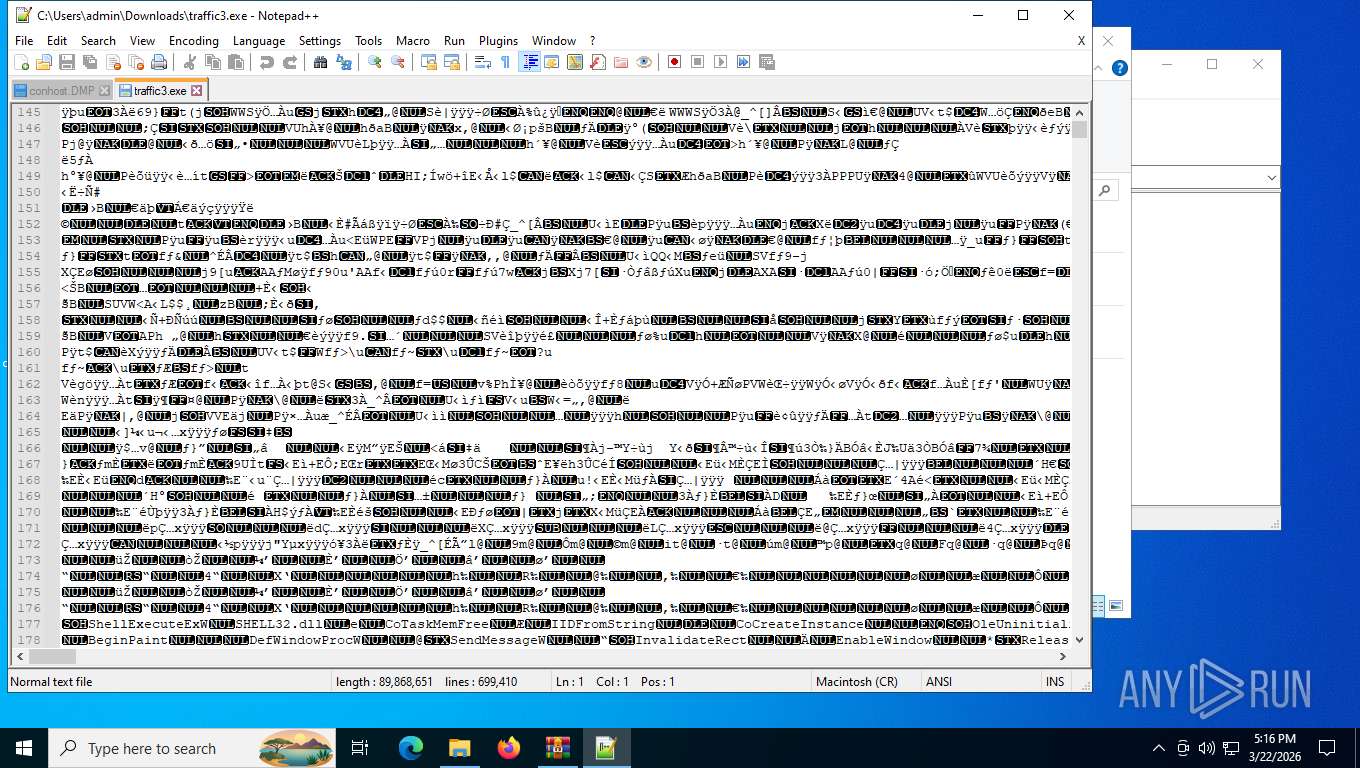
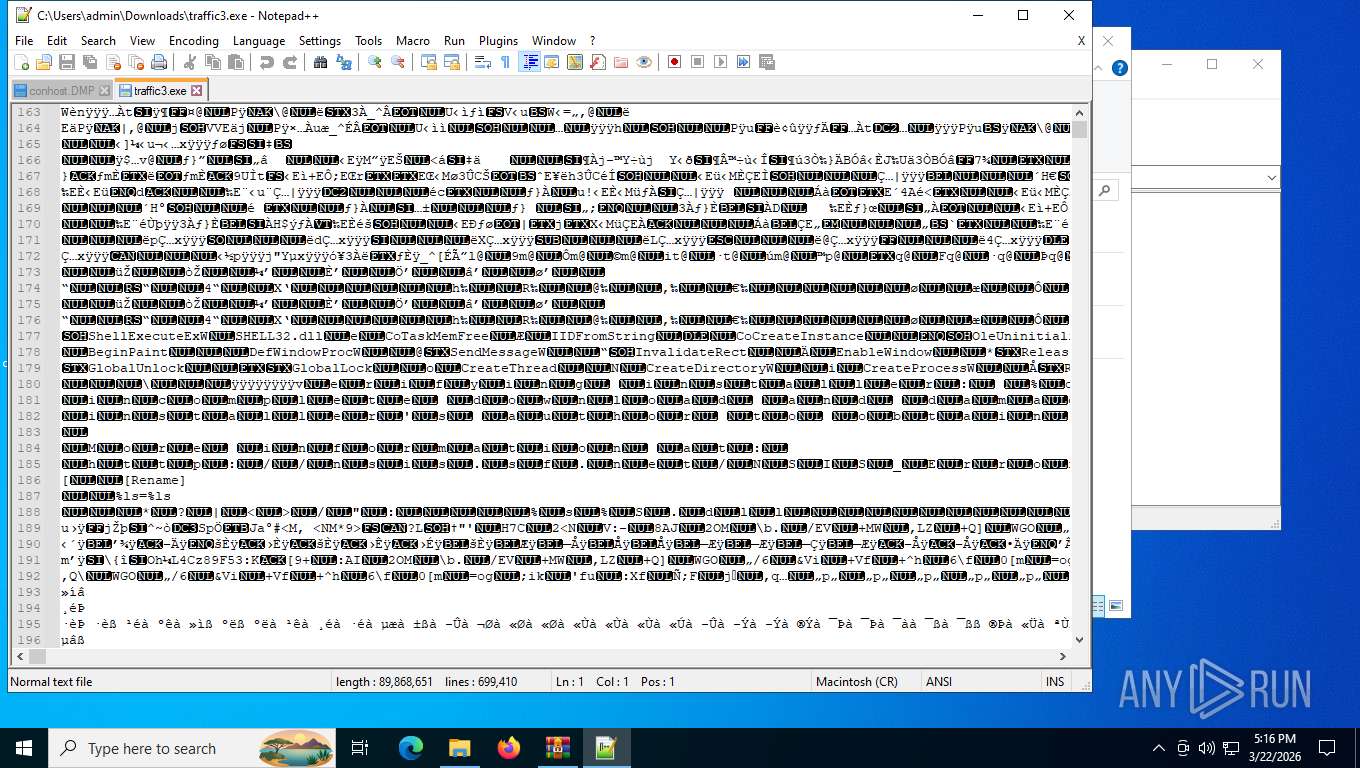
- notepad++.exe (PID: 2960)
- notepad++.exe (PID: 8648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
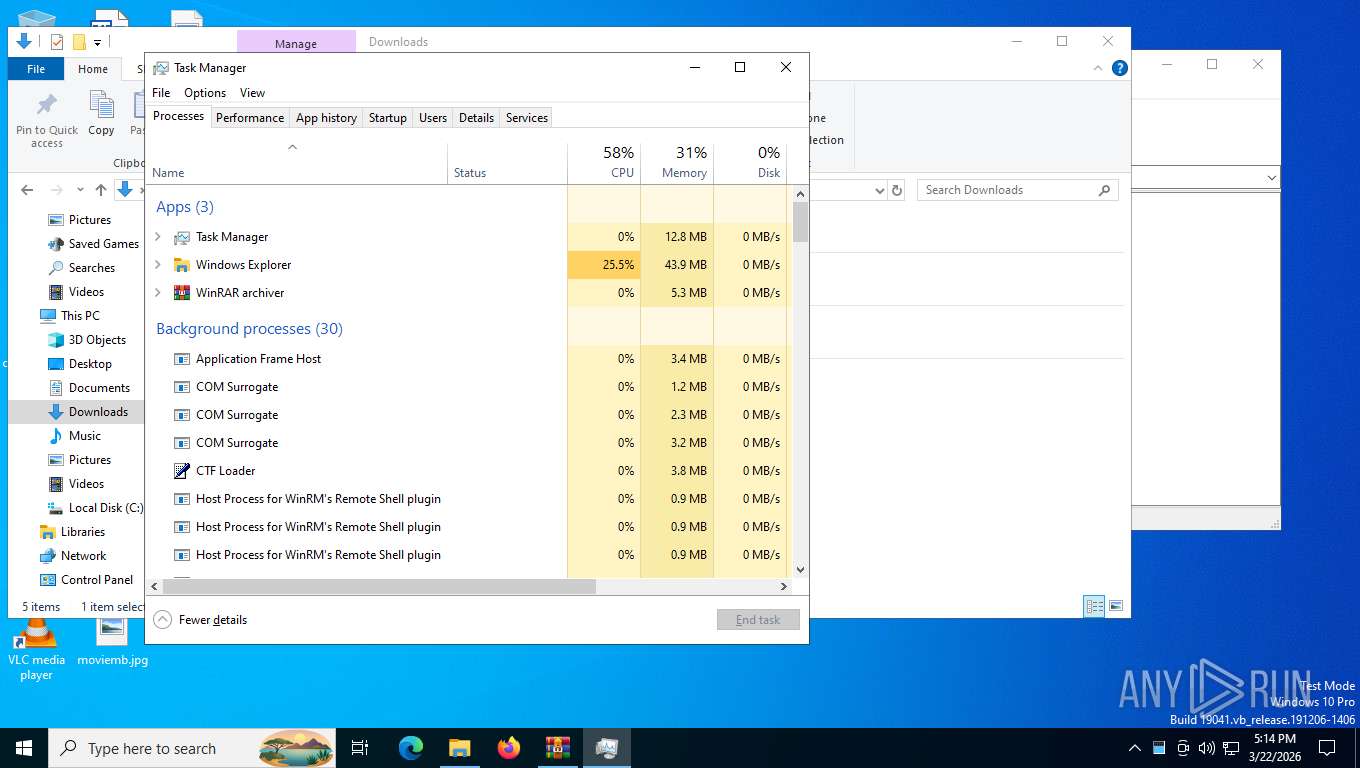
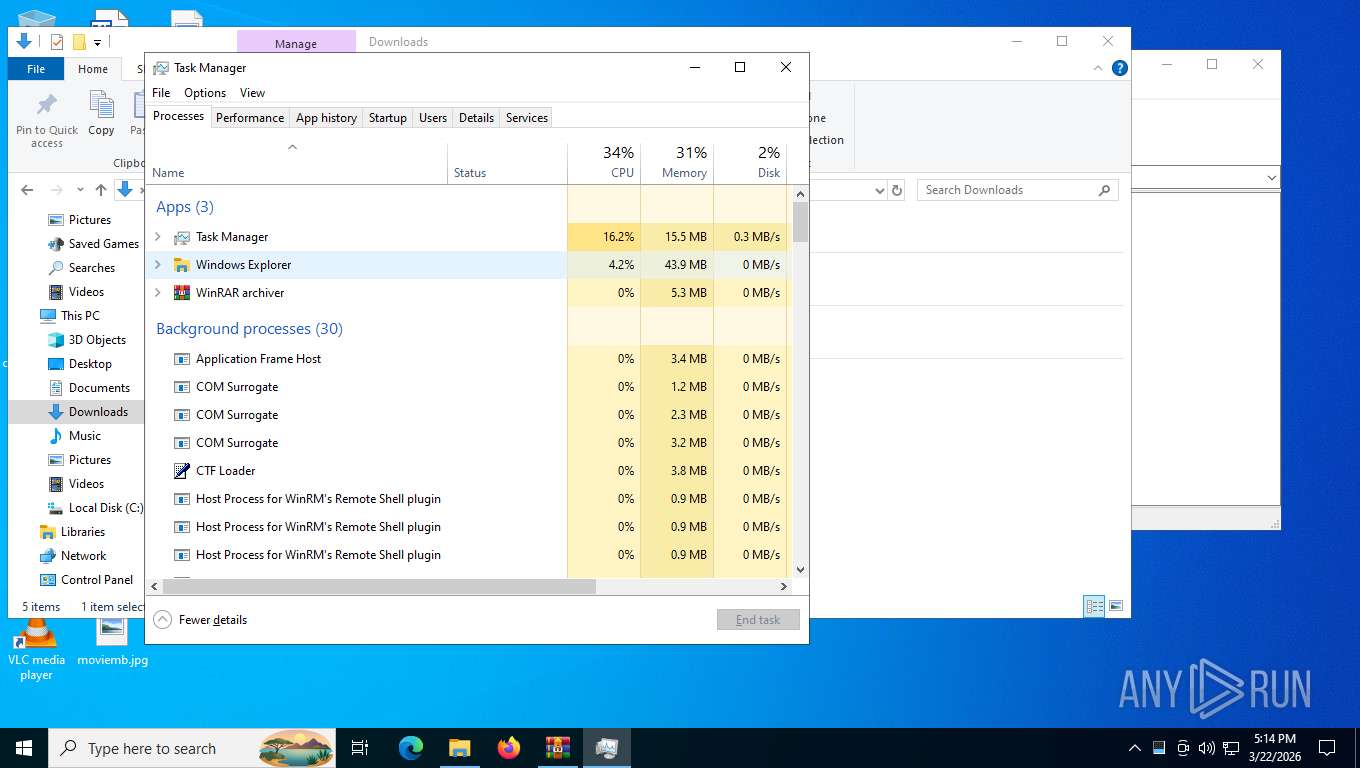
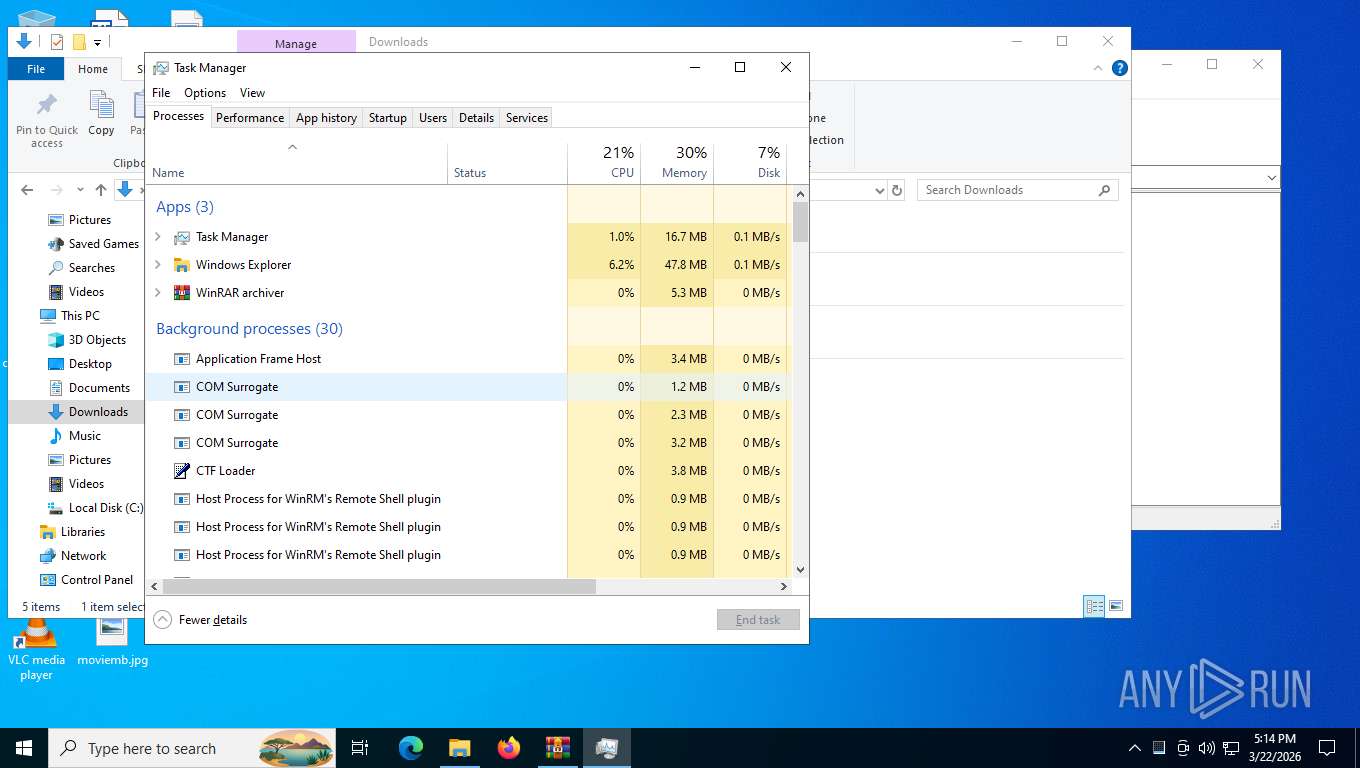
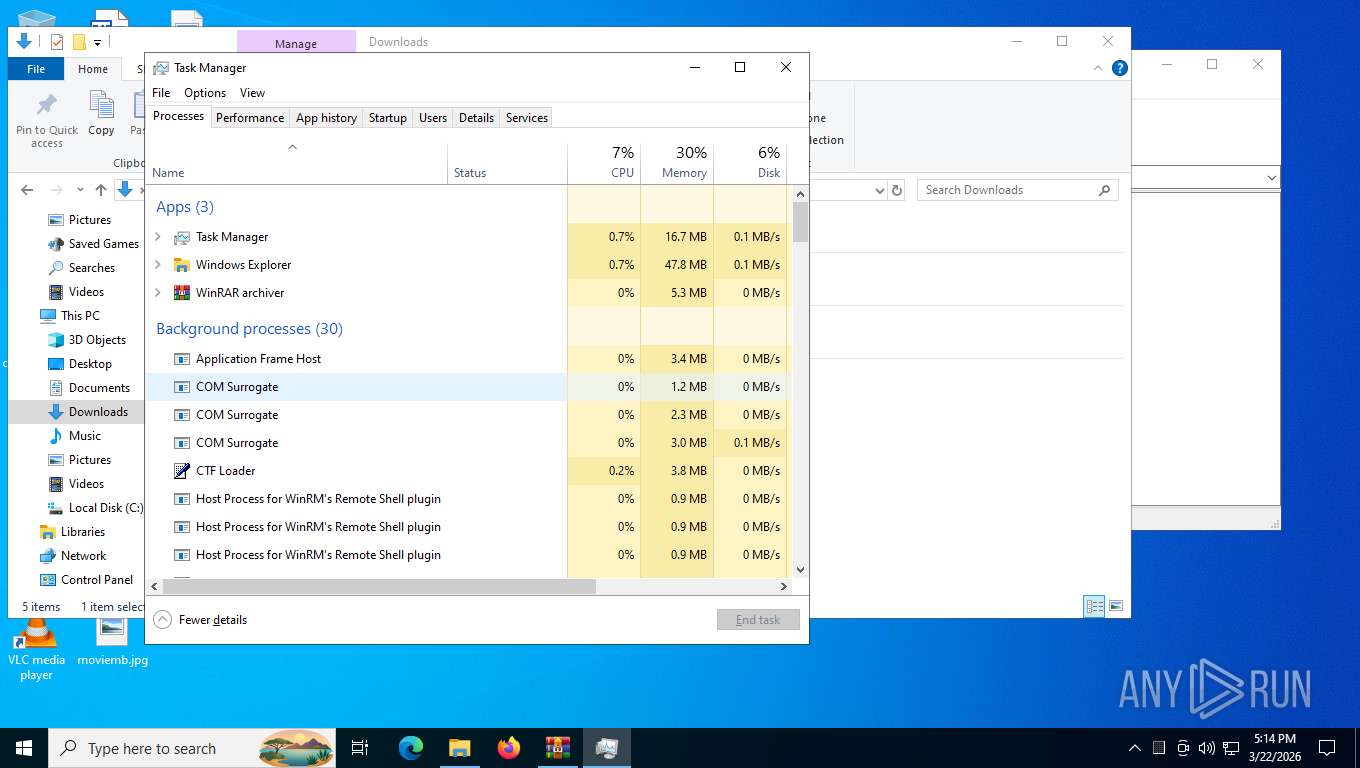
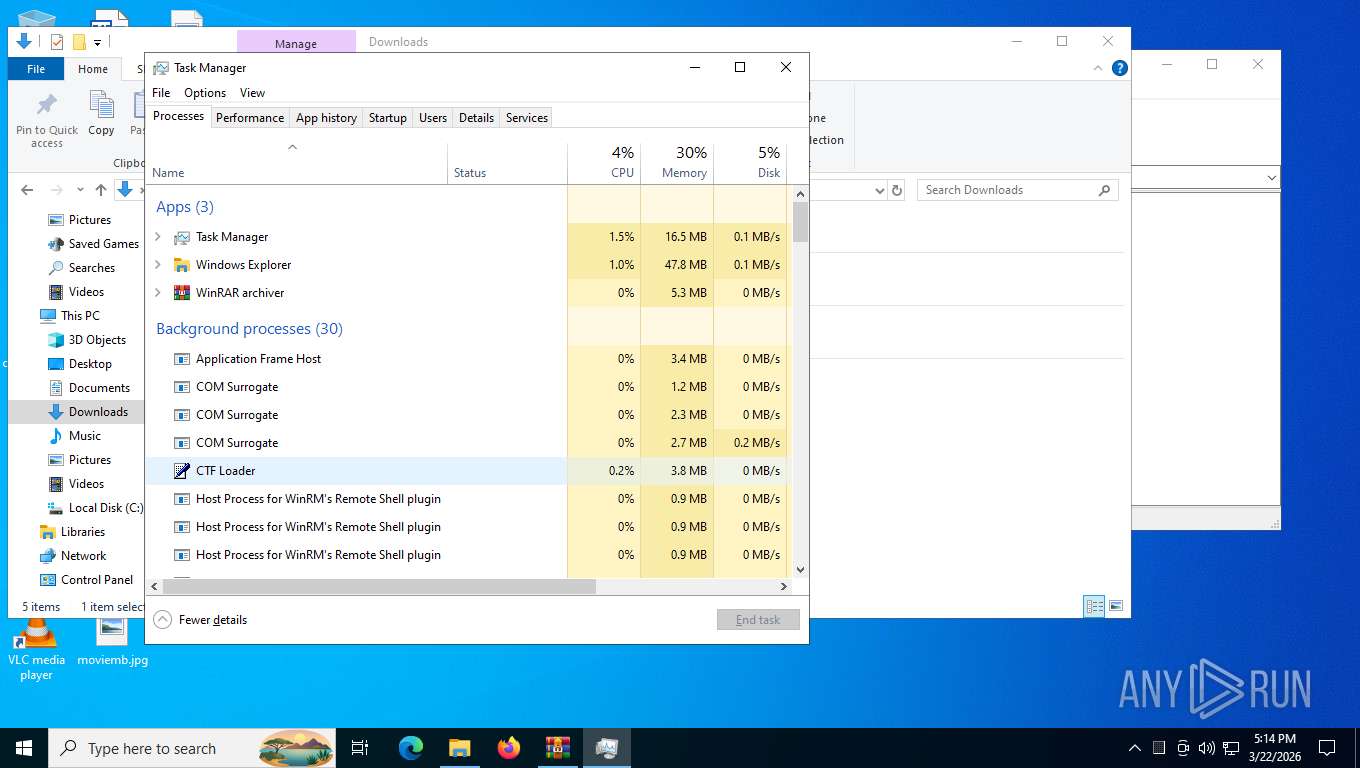
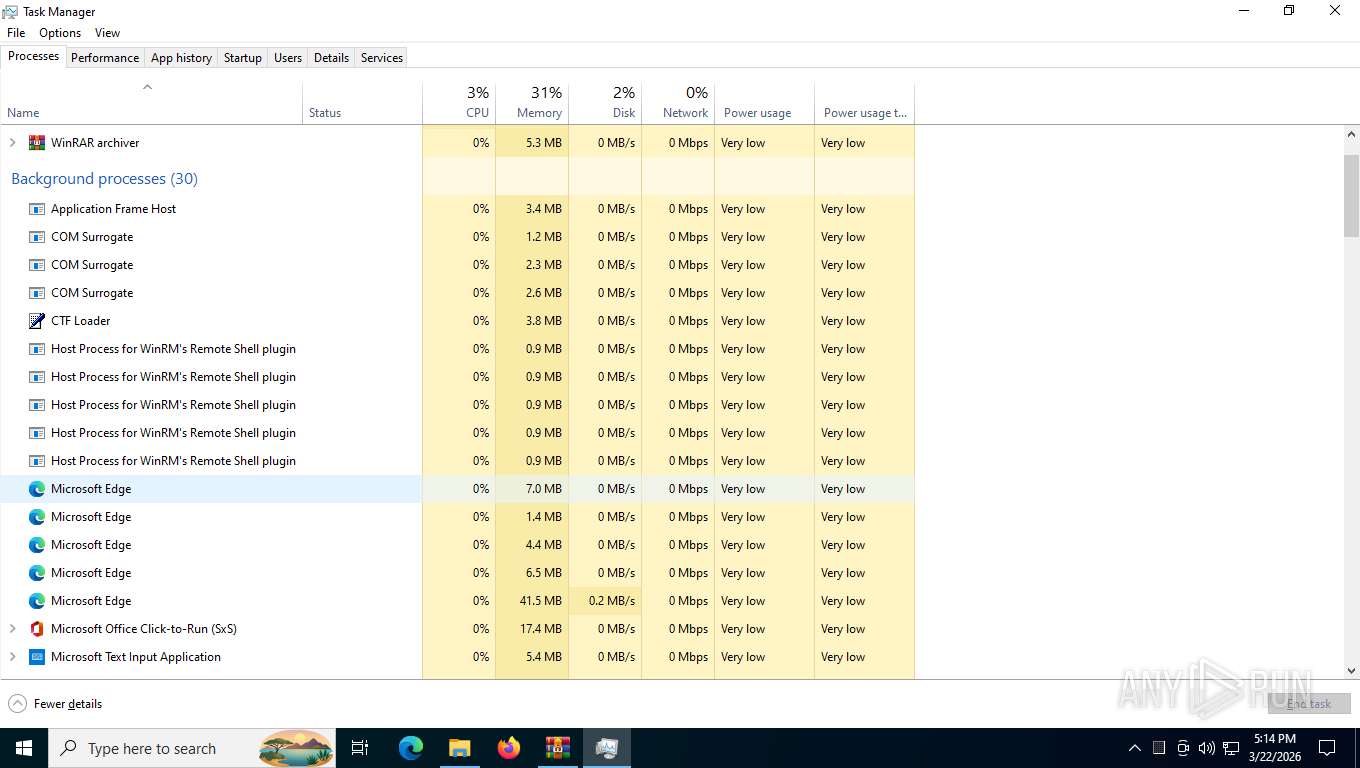
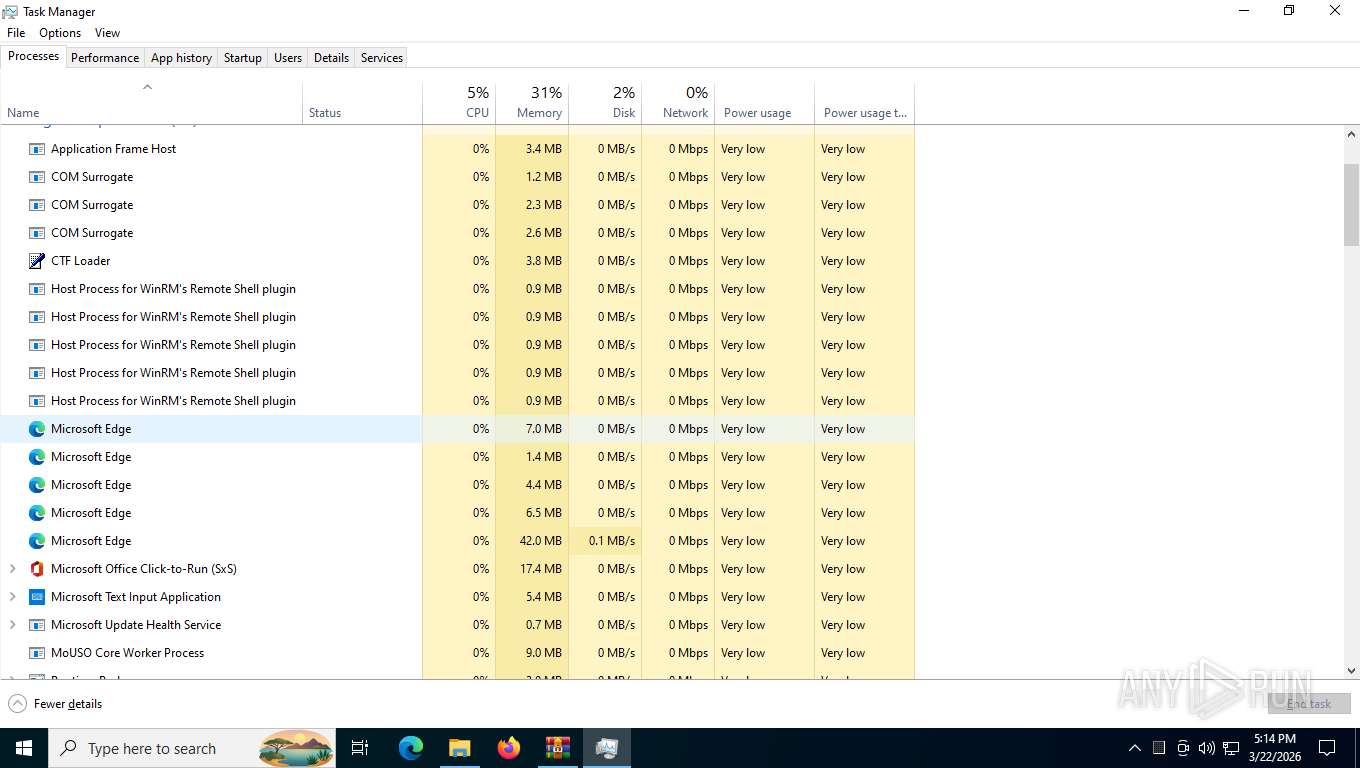
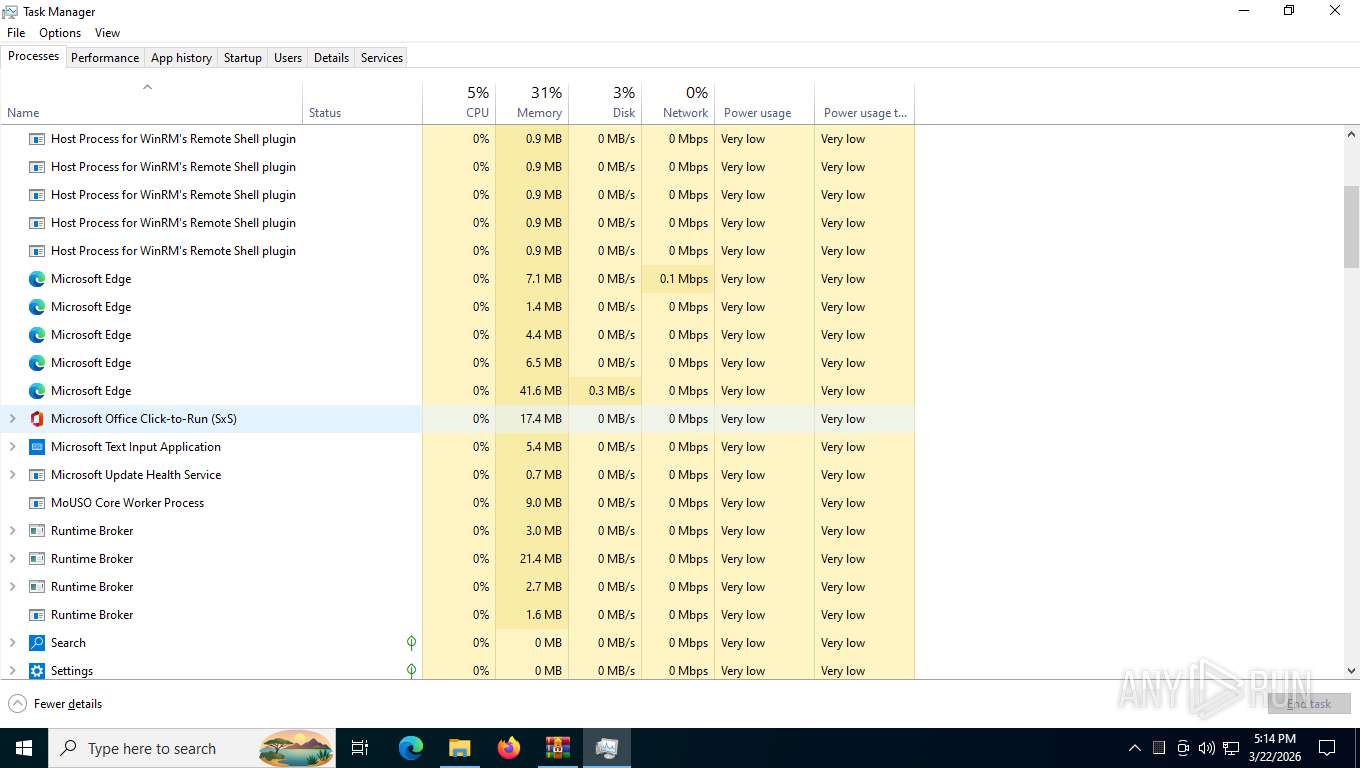
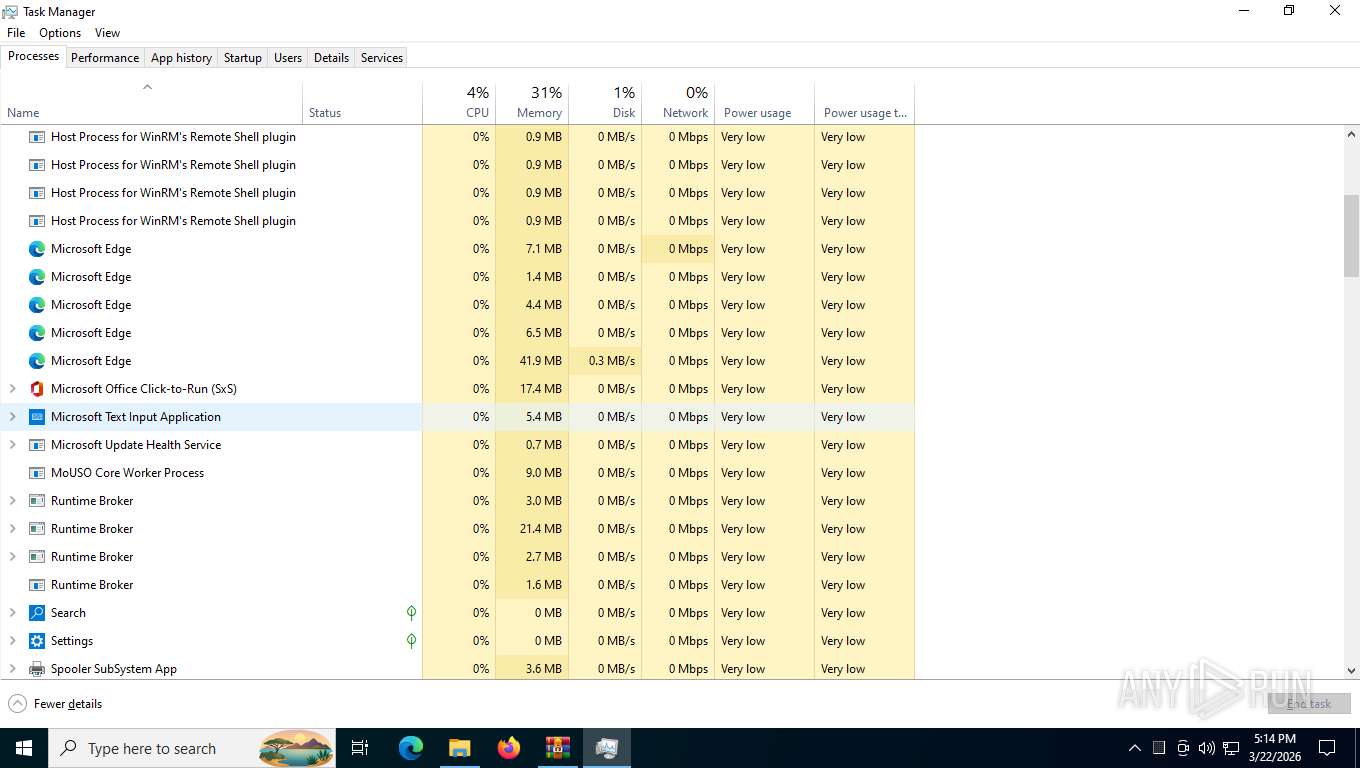
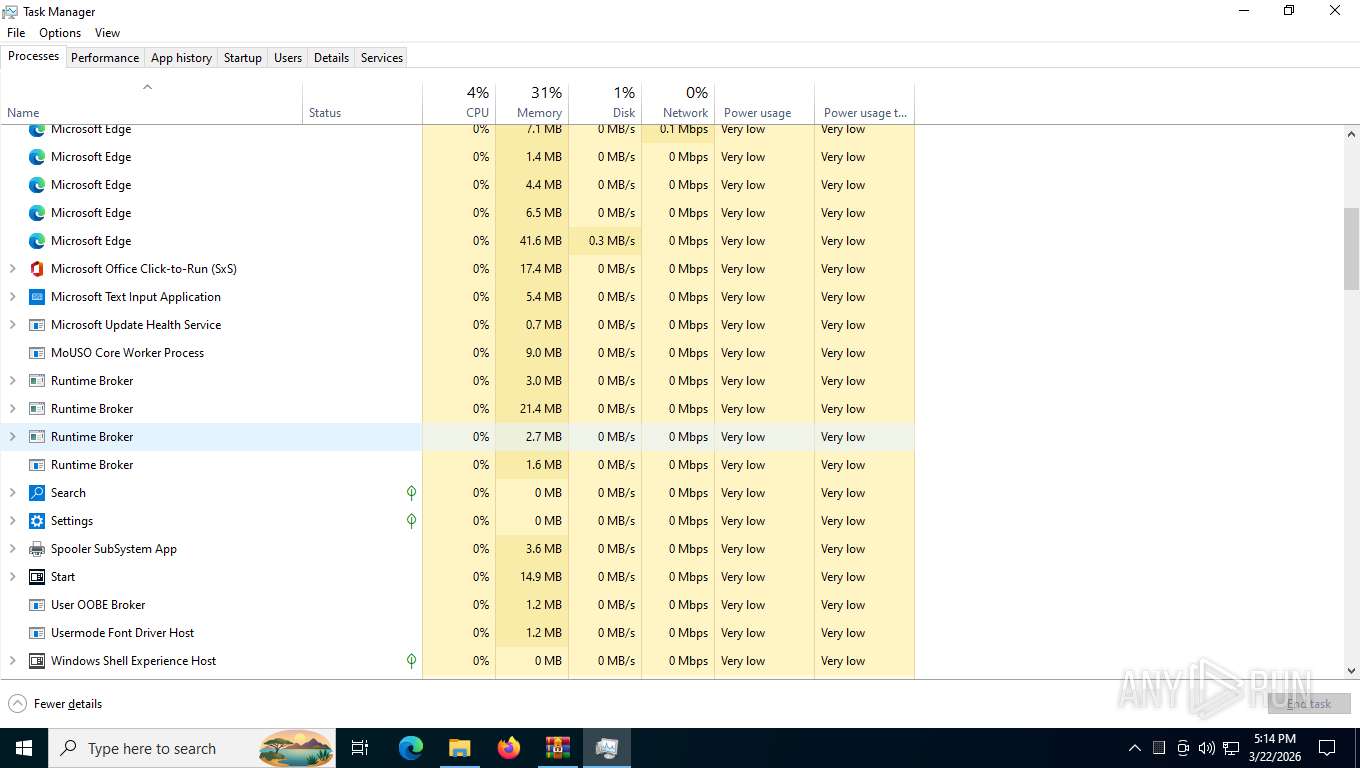
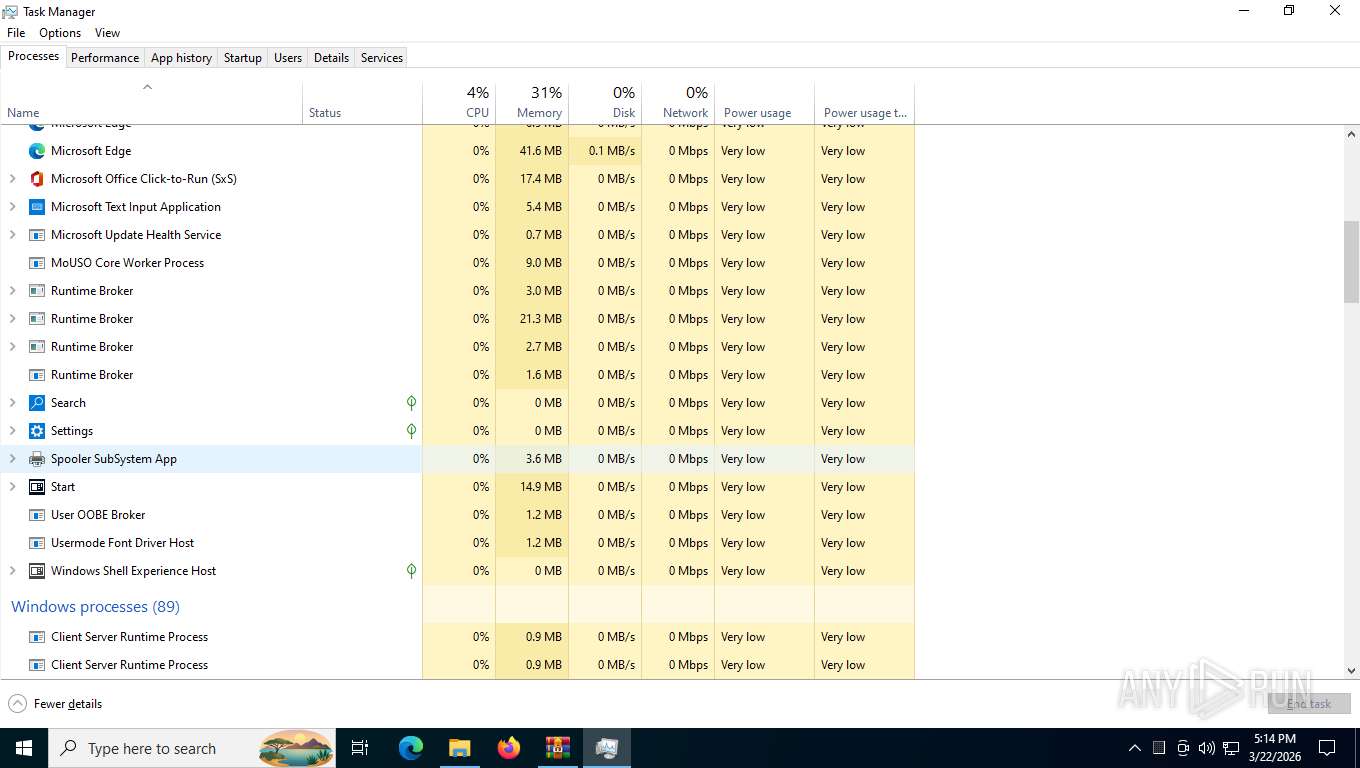
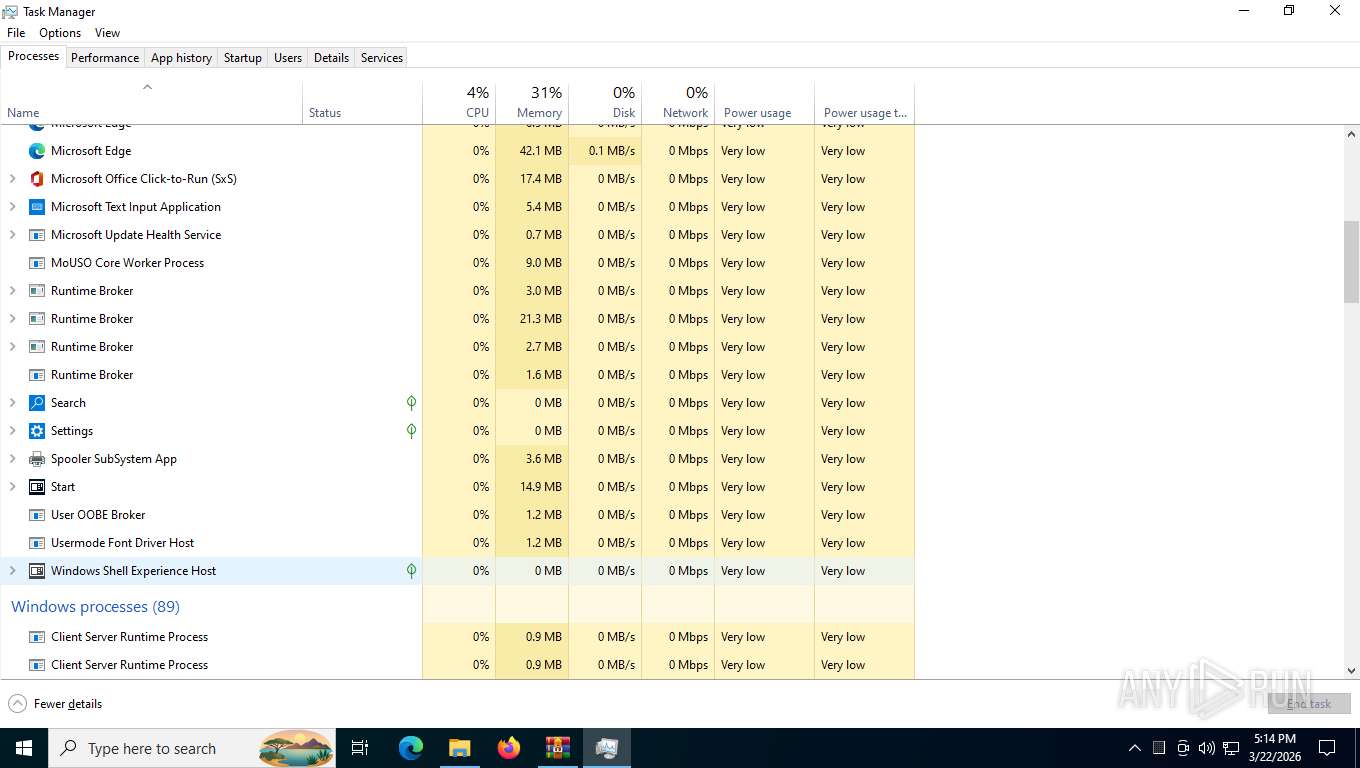
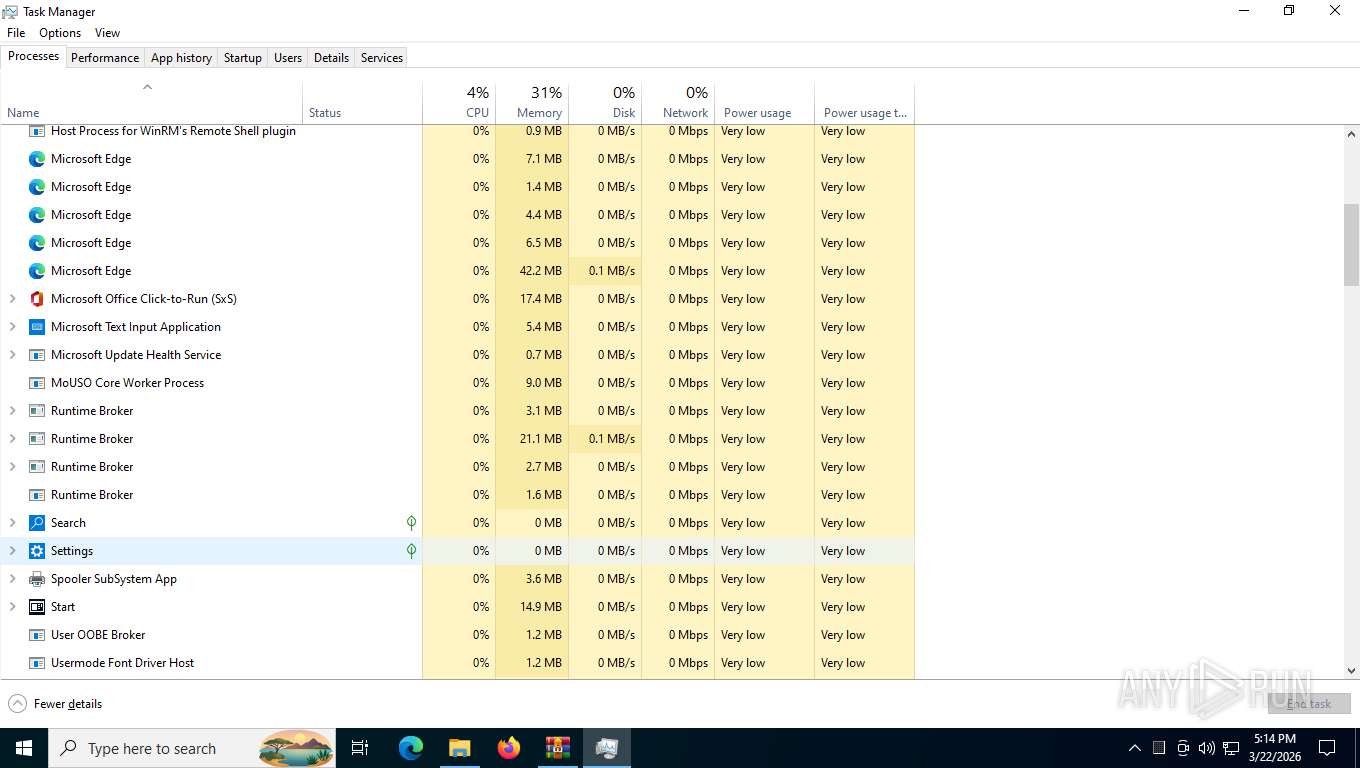
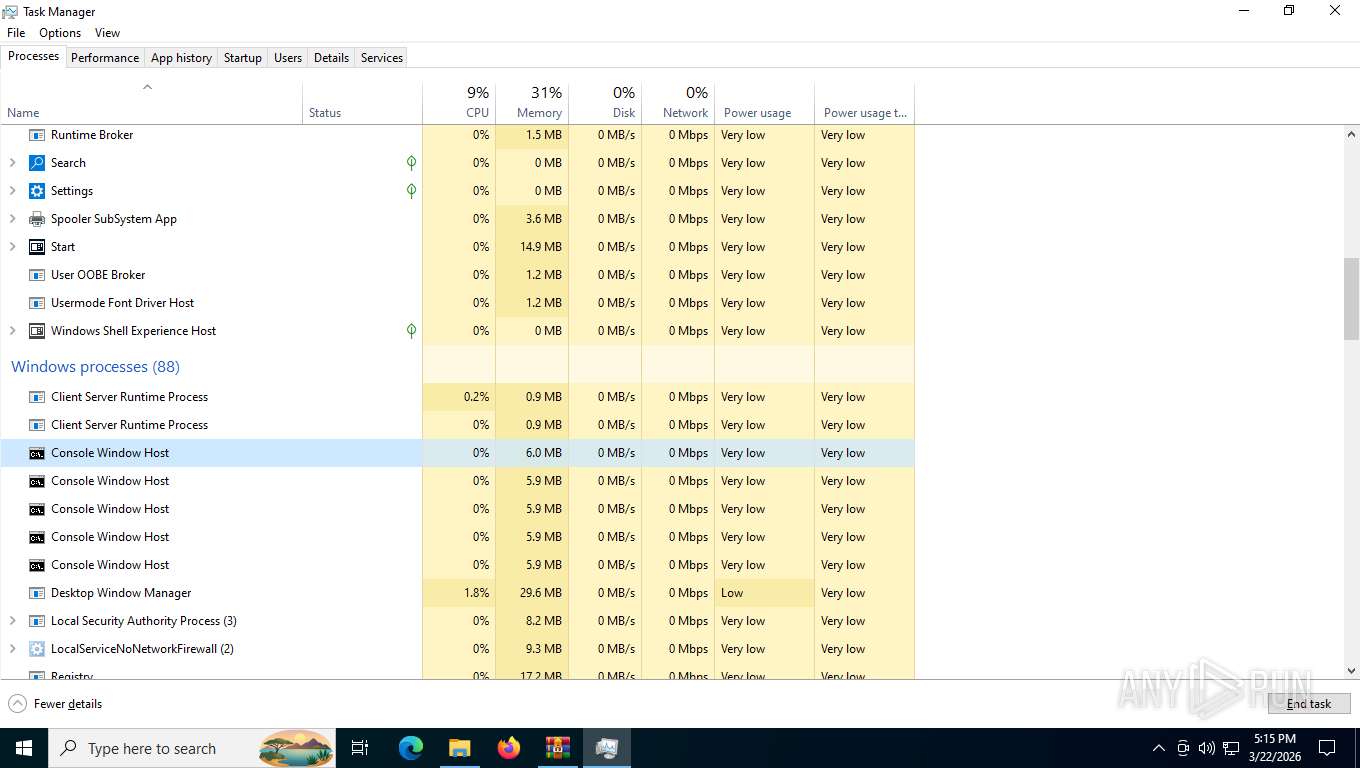
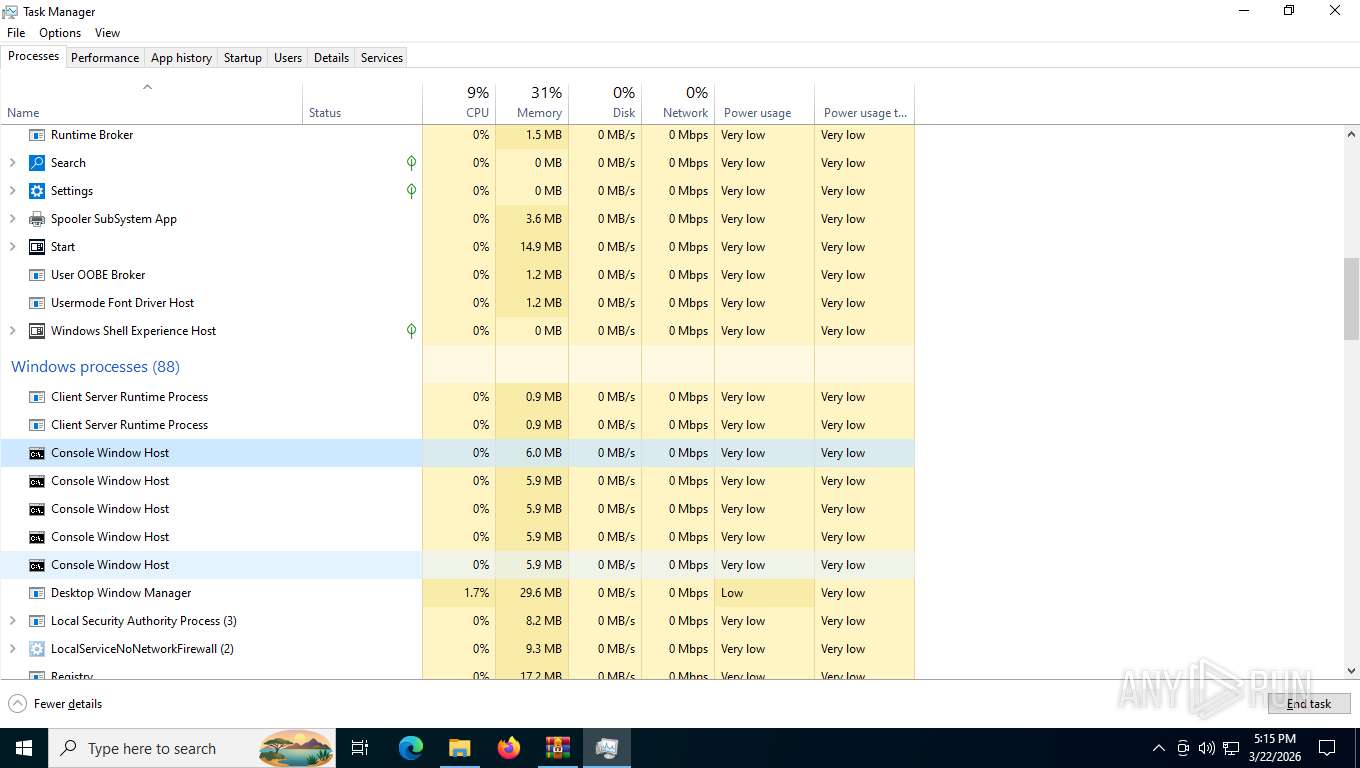
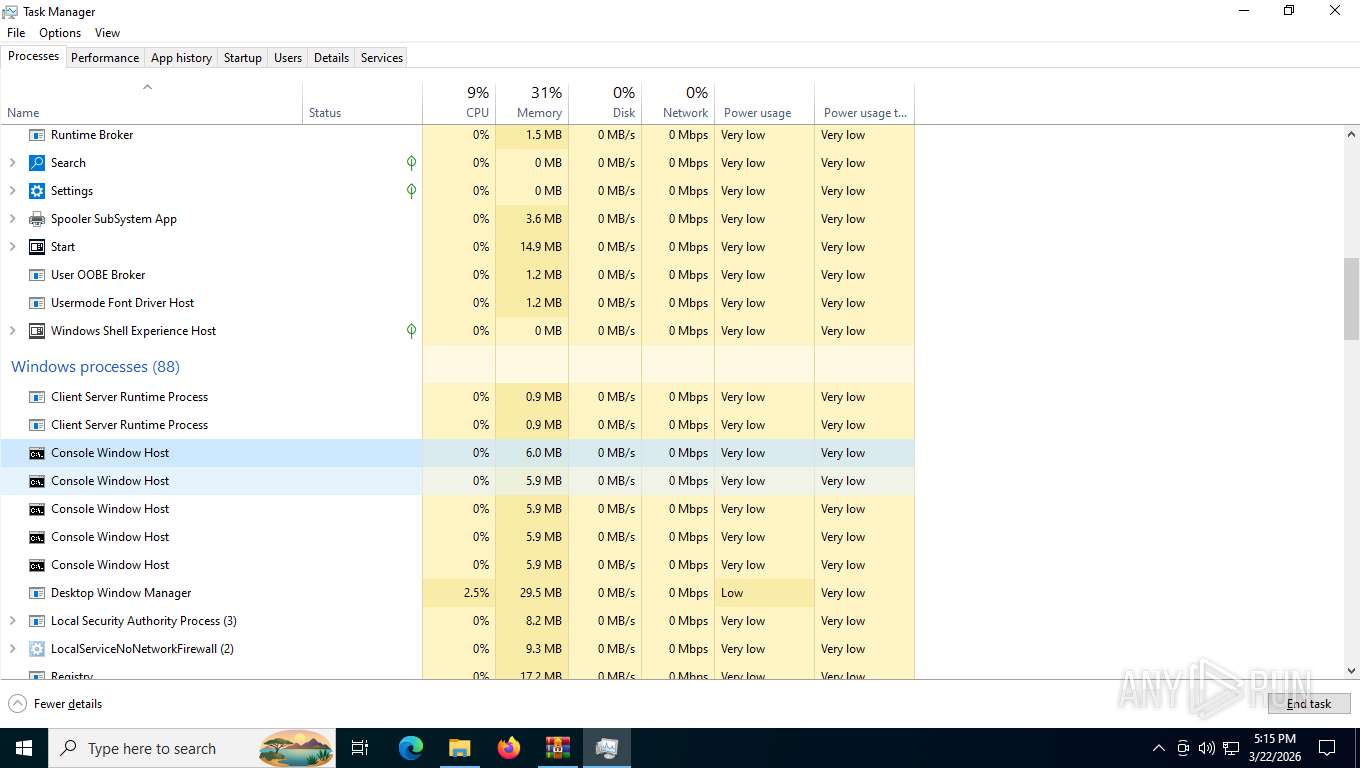
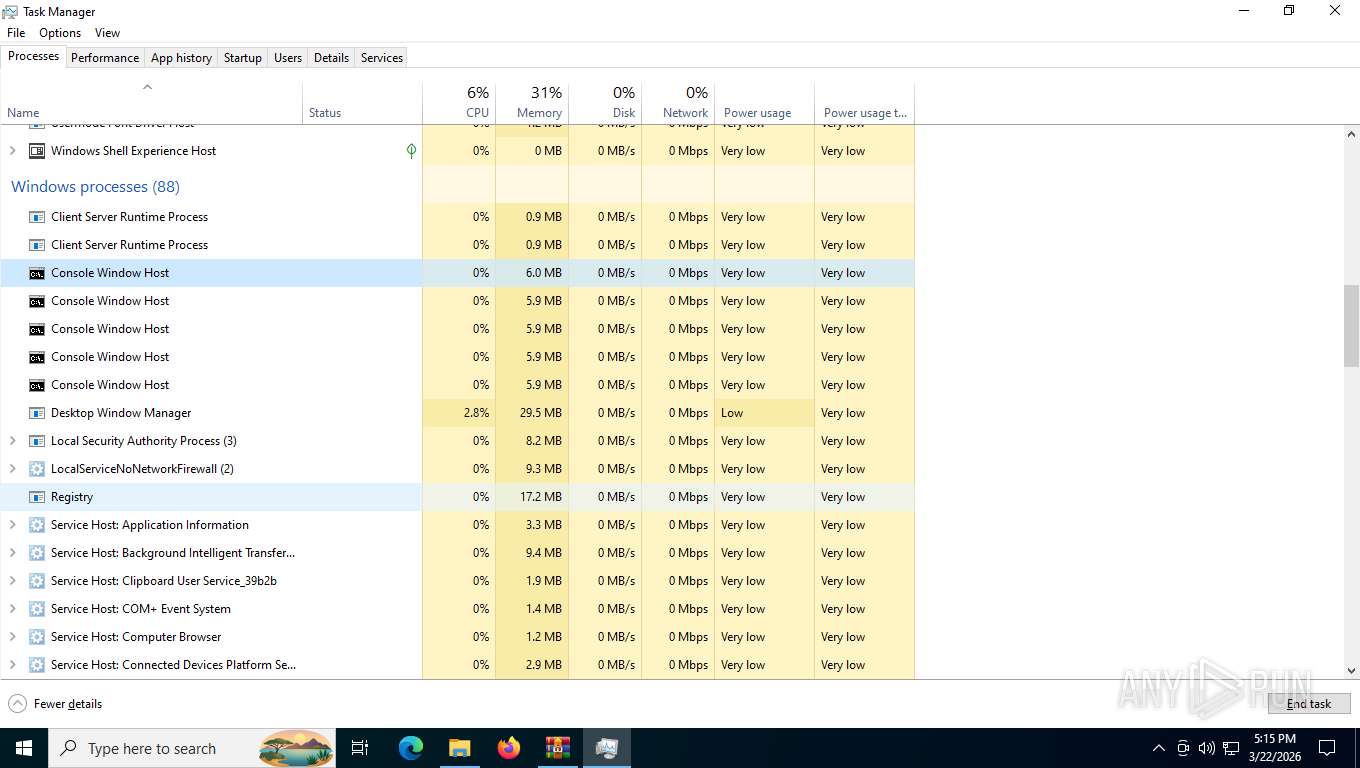
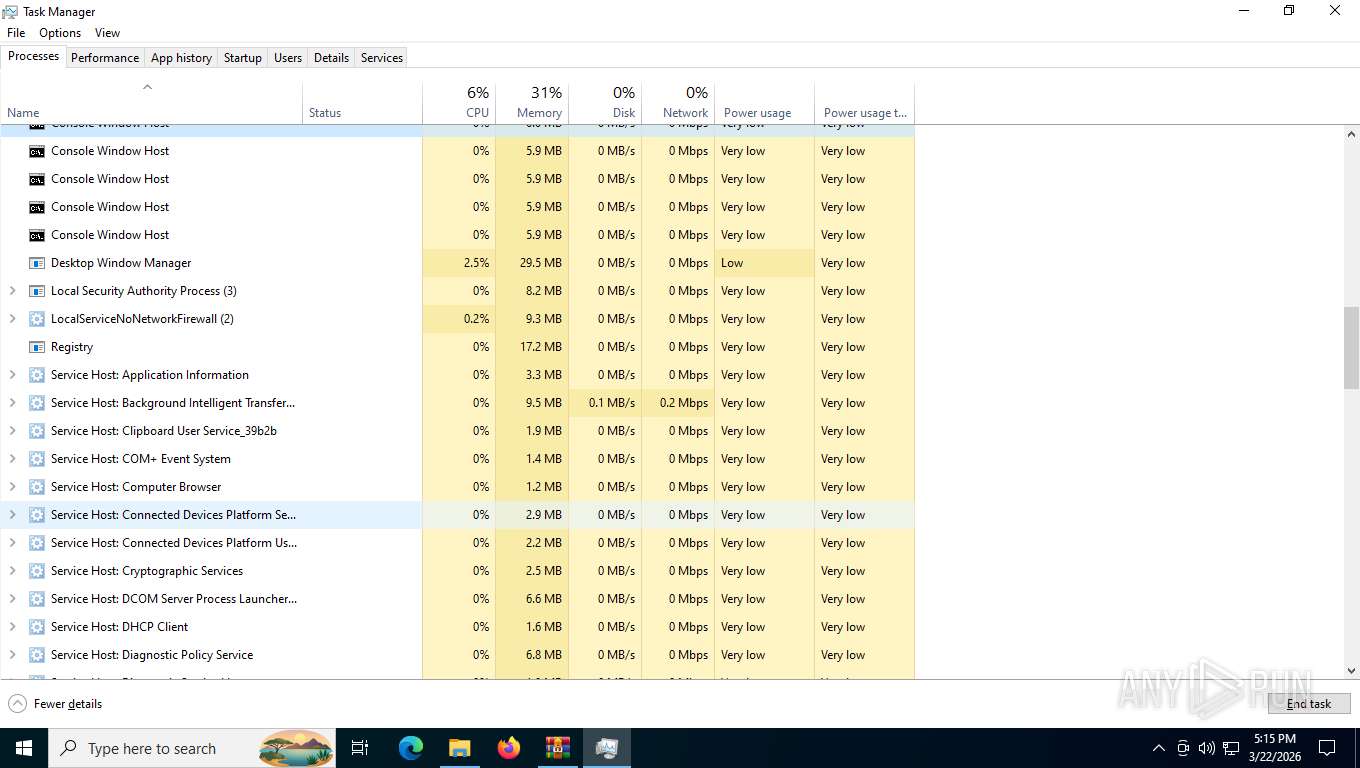
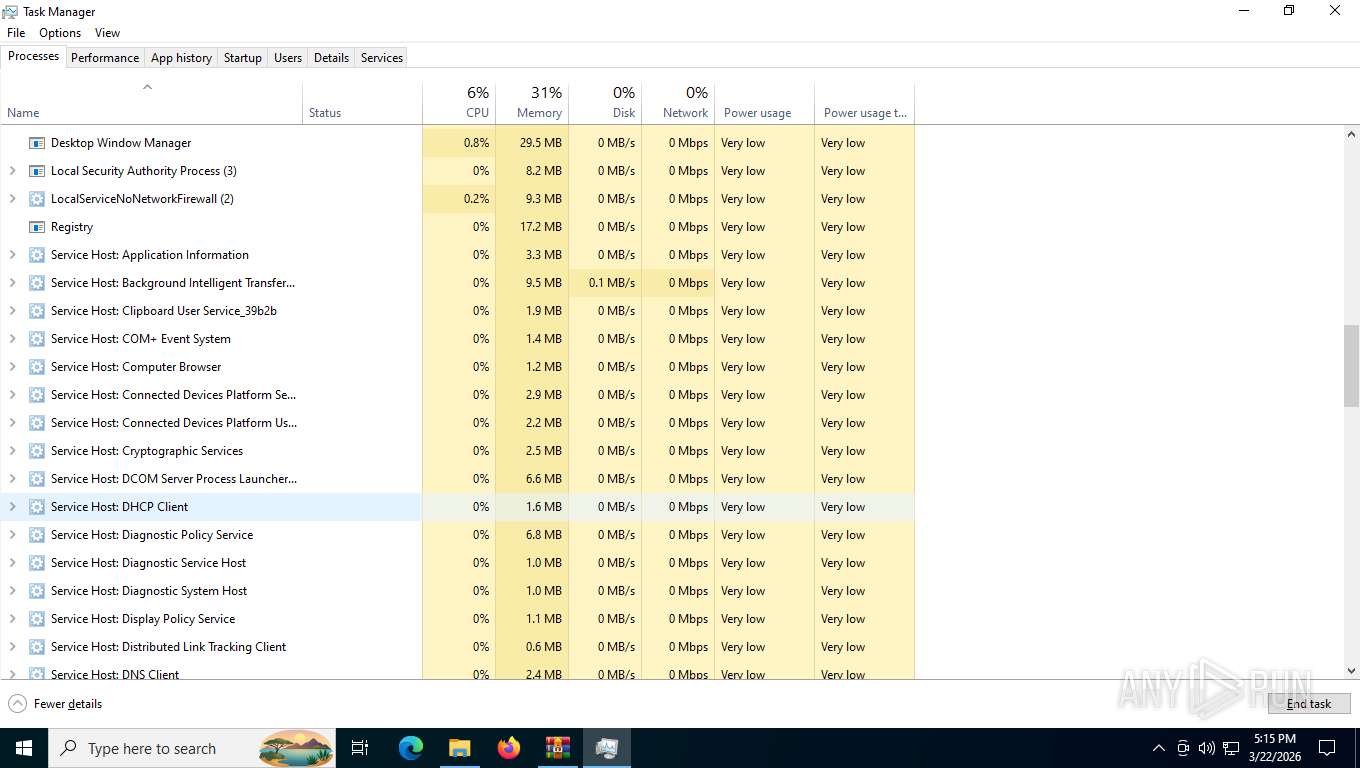
Total processes
210
Monitored processes
61
Malicious processes
6
Suspicious processes
0
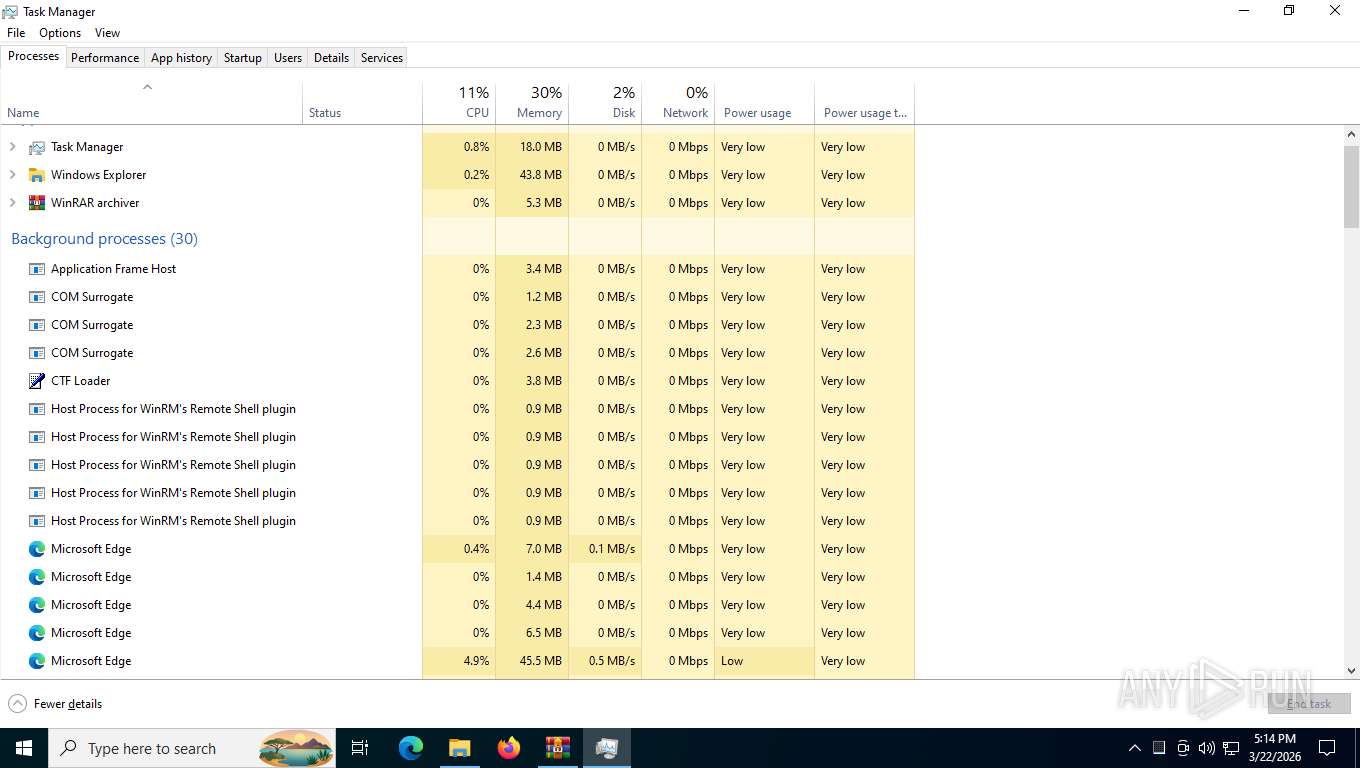
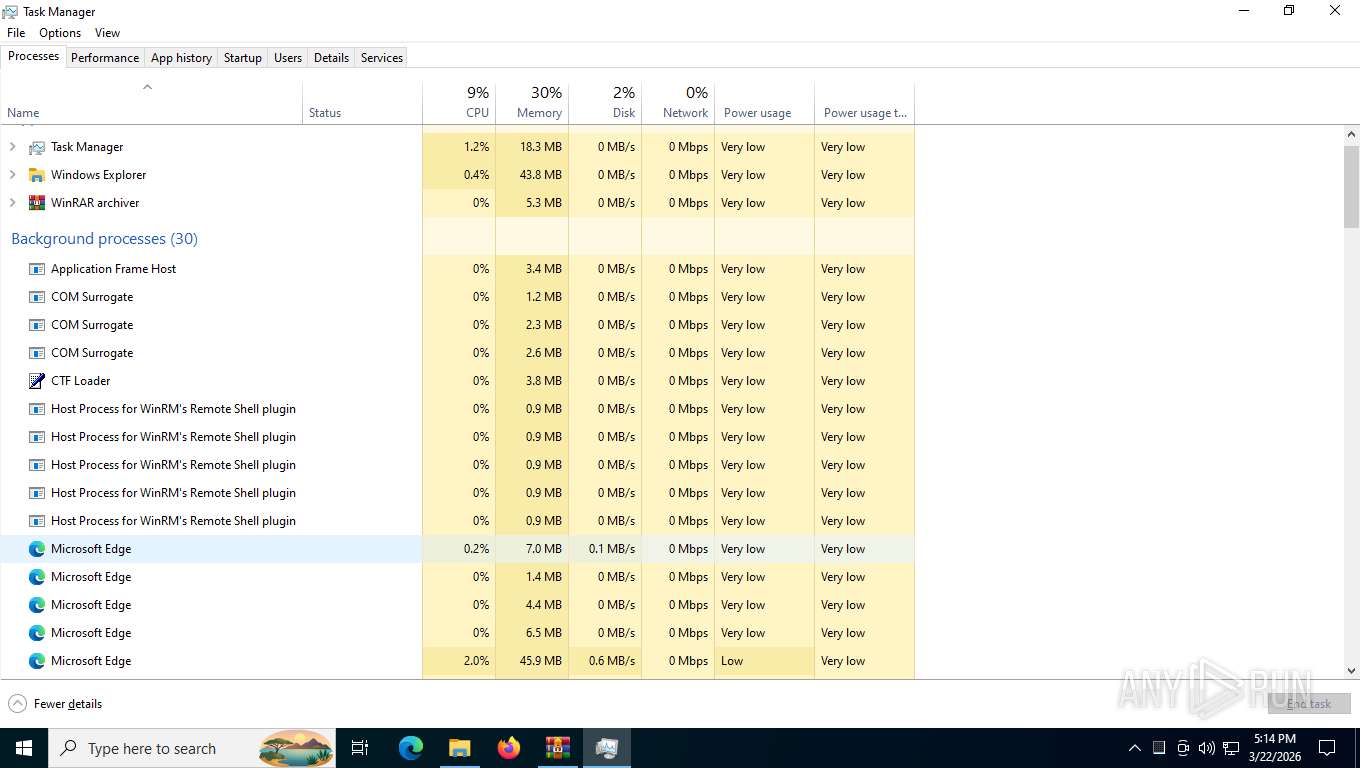
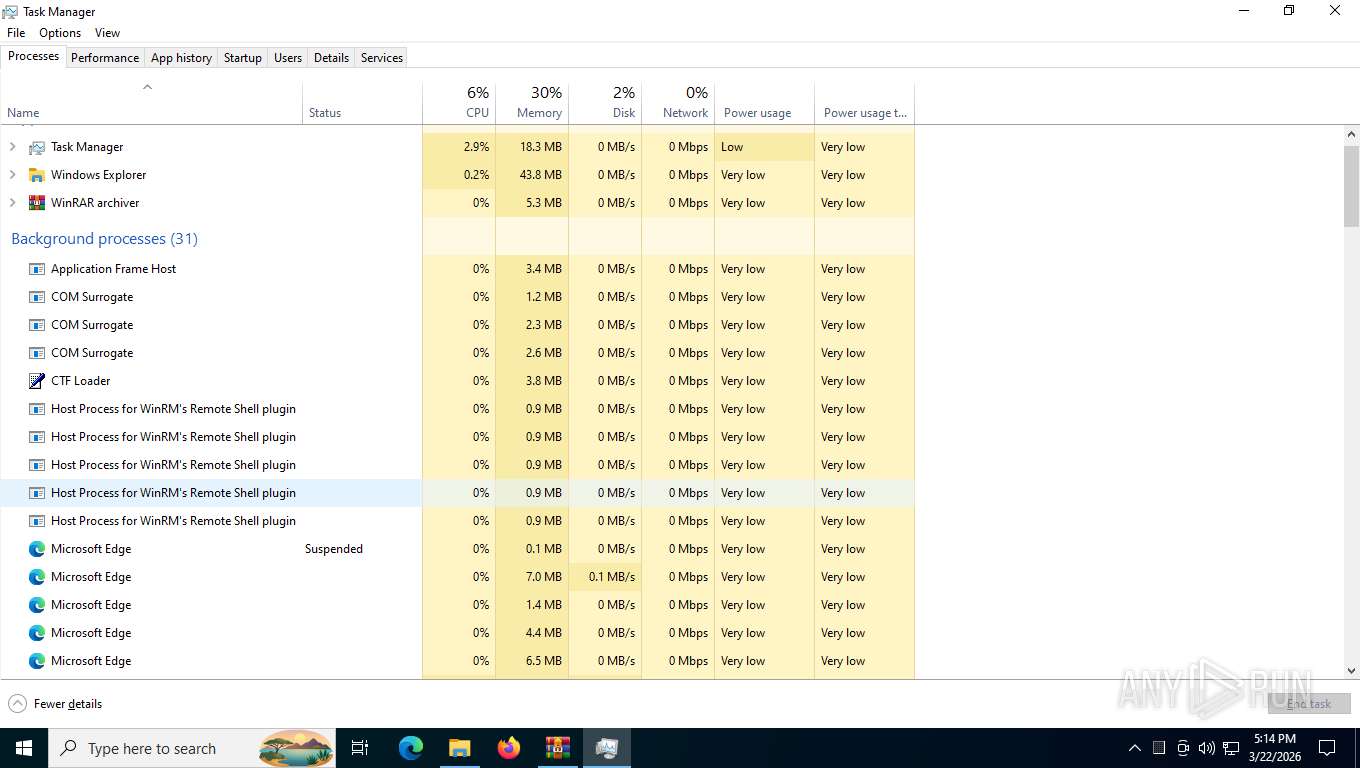
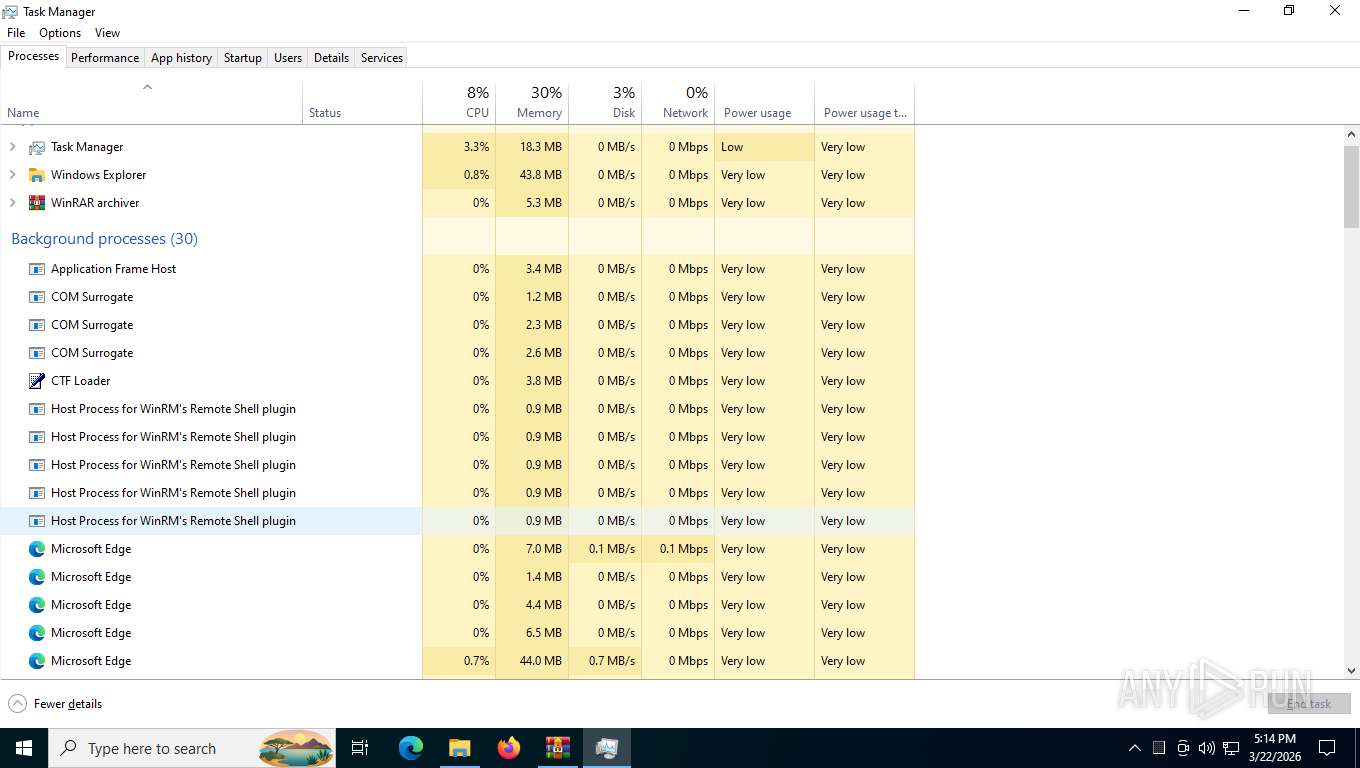
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1116 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=4900,i,13282863435181508812,18434466595966297094,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5272 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
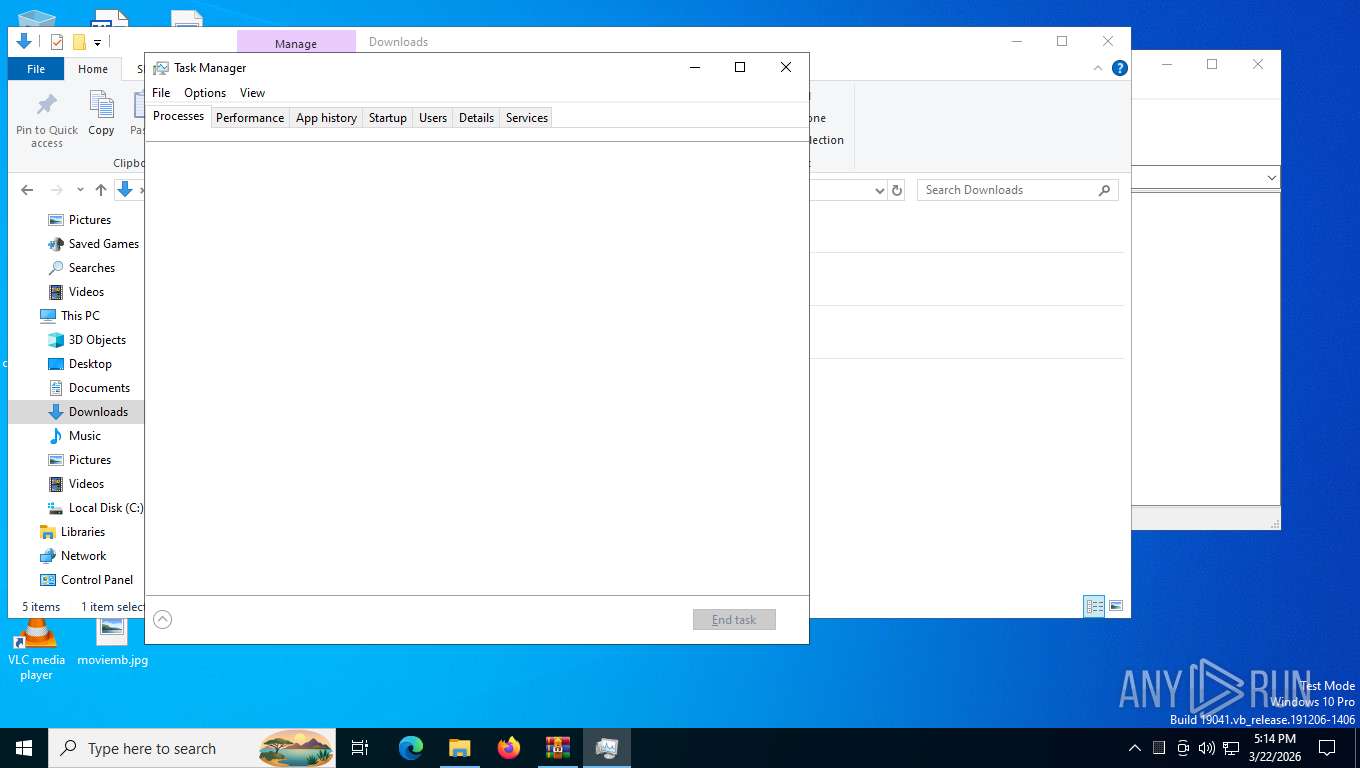
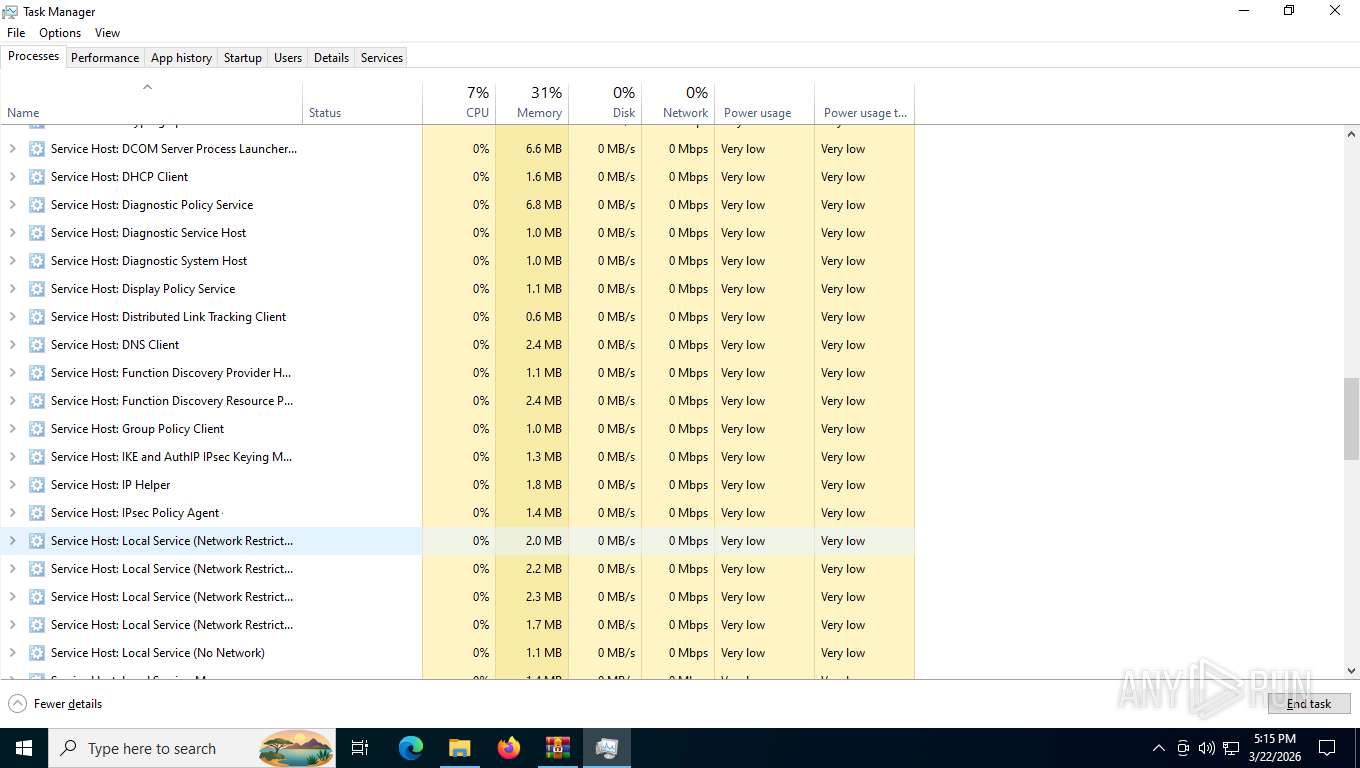
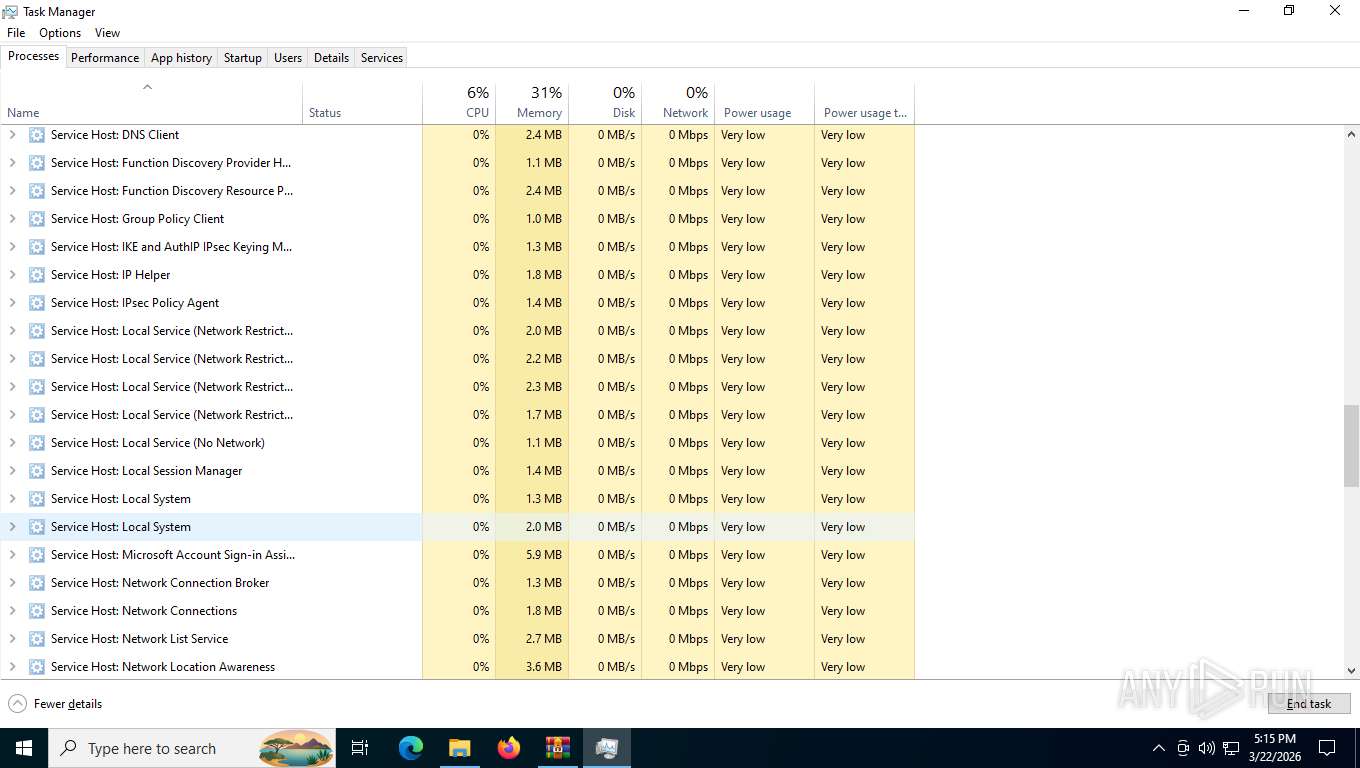
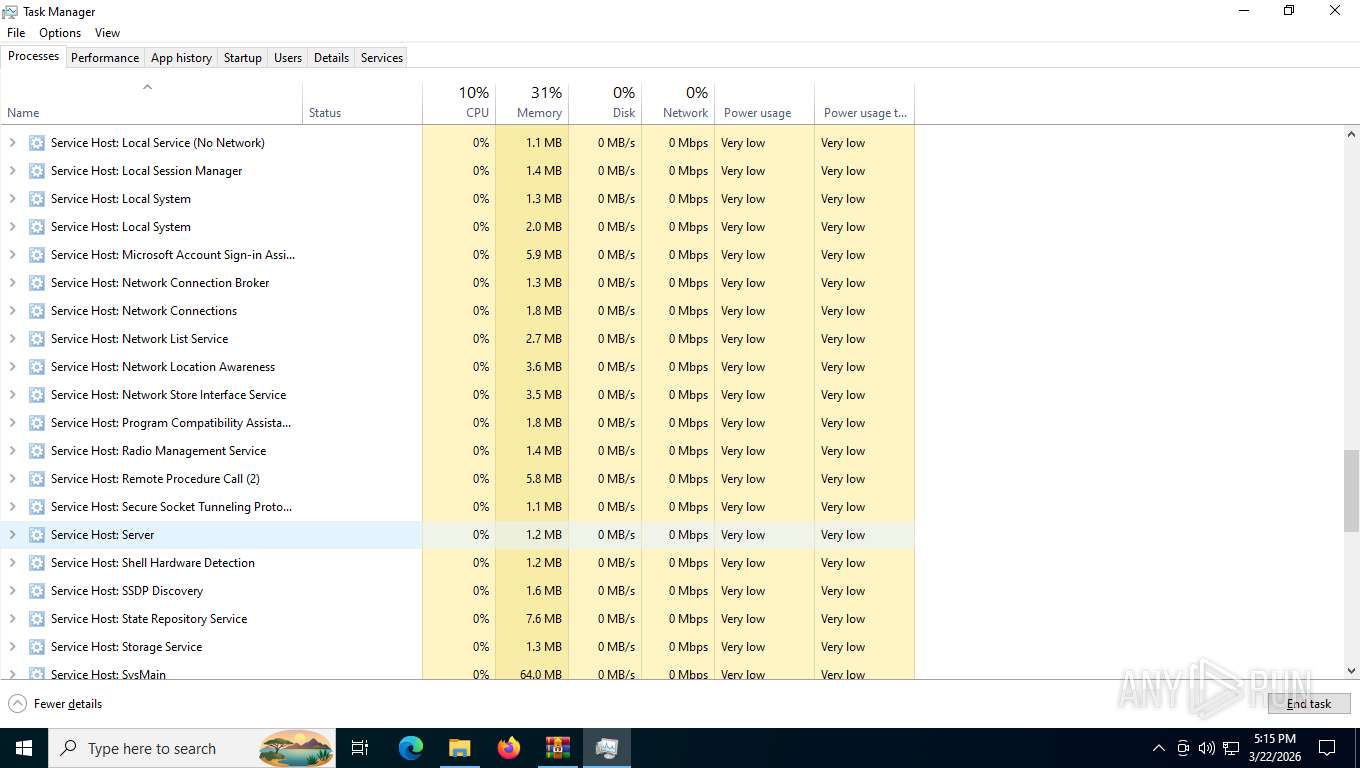
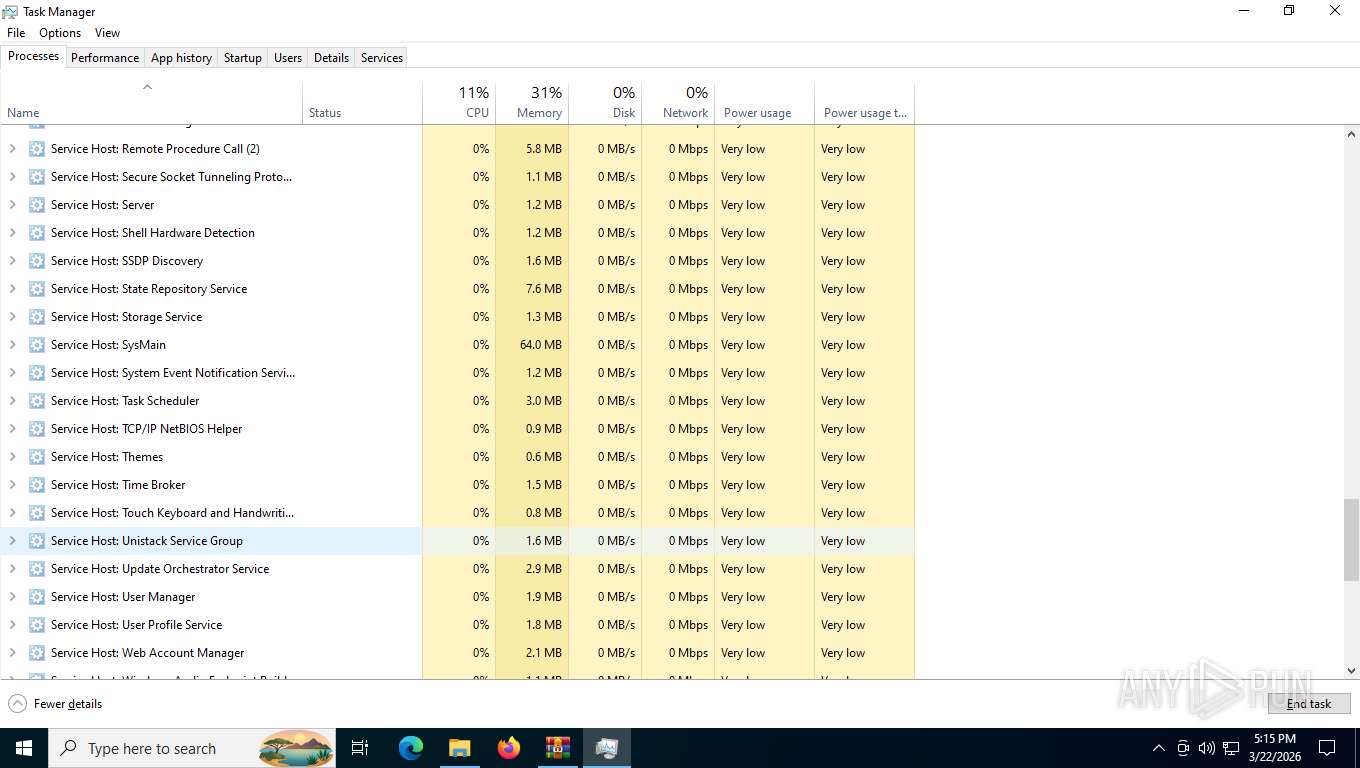
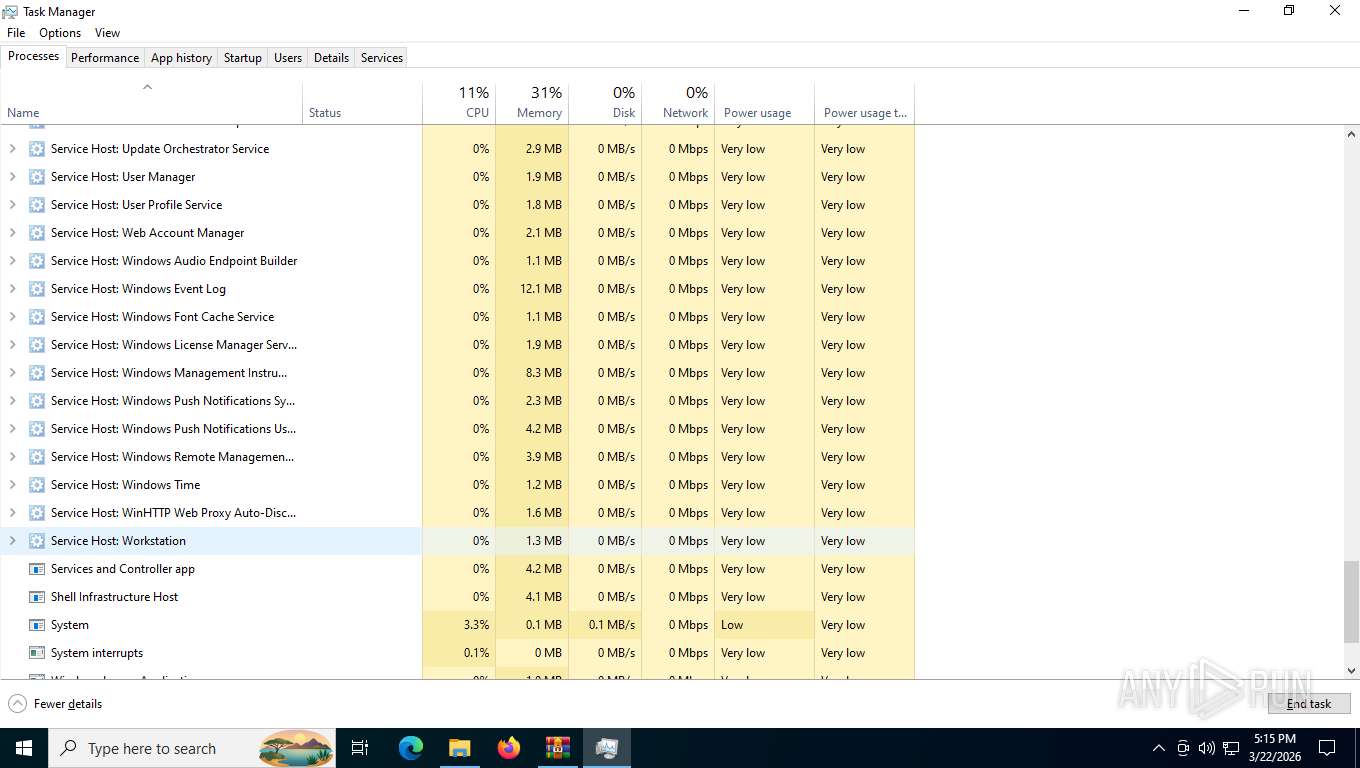
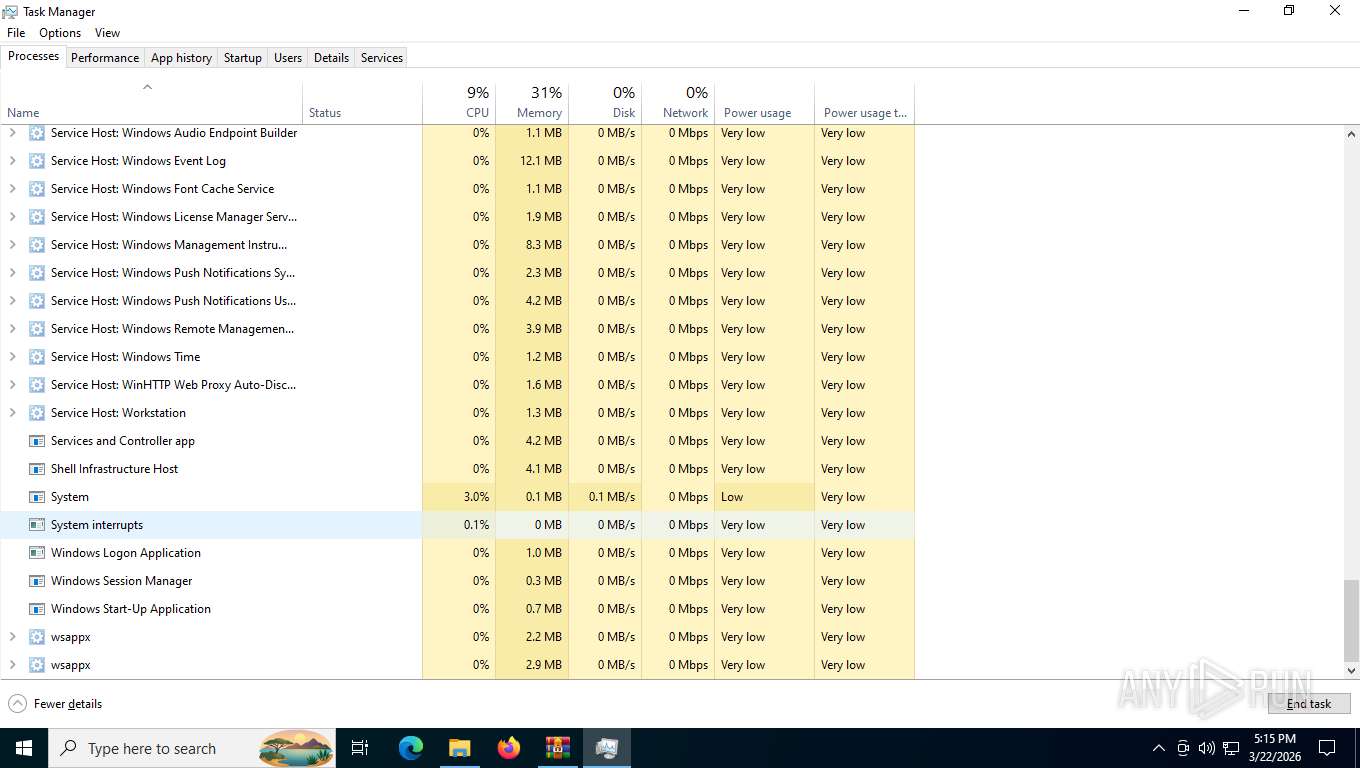
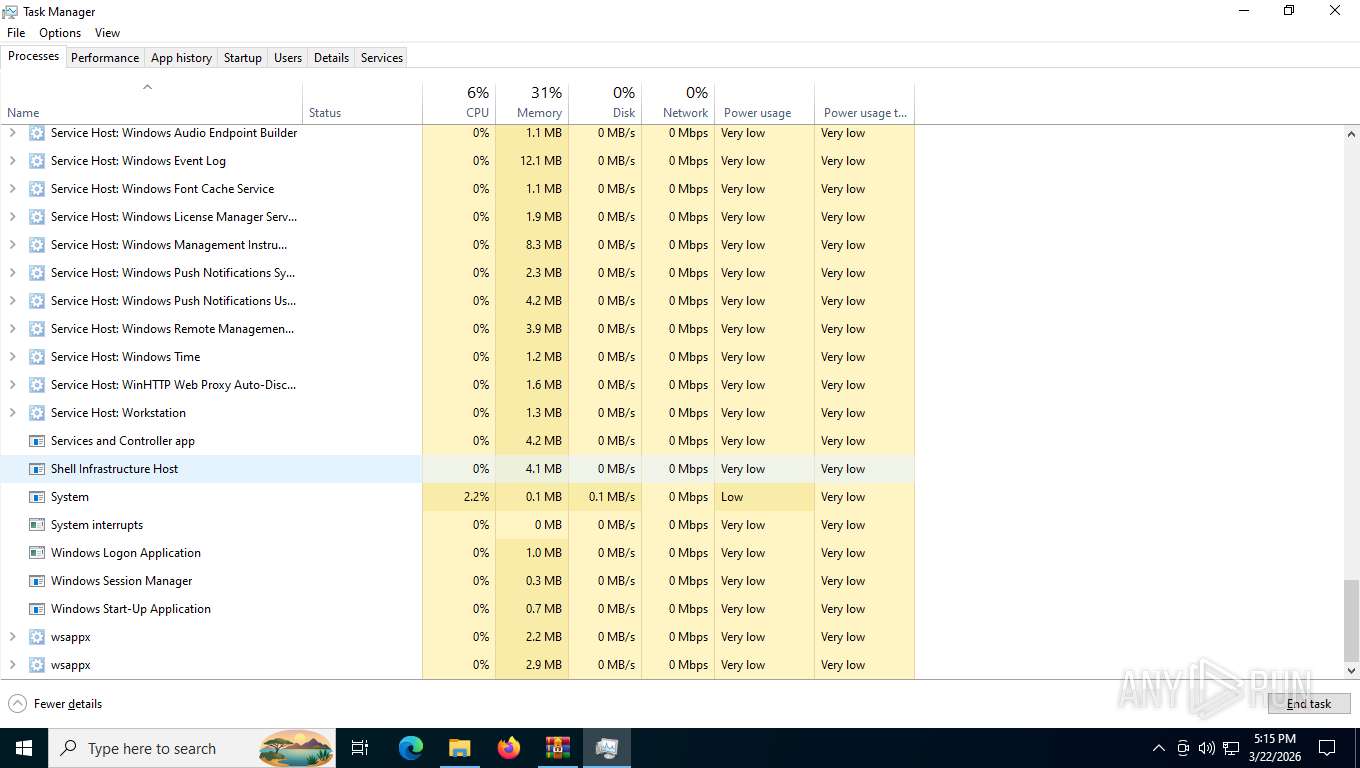
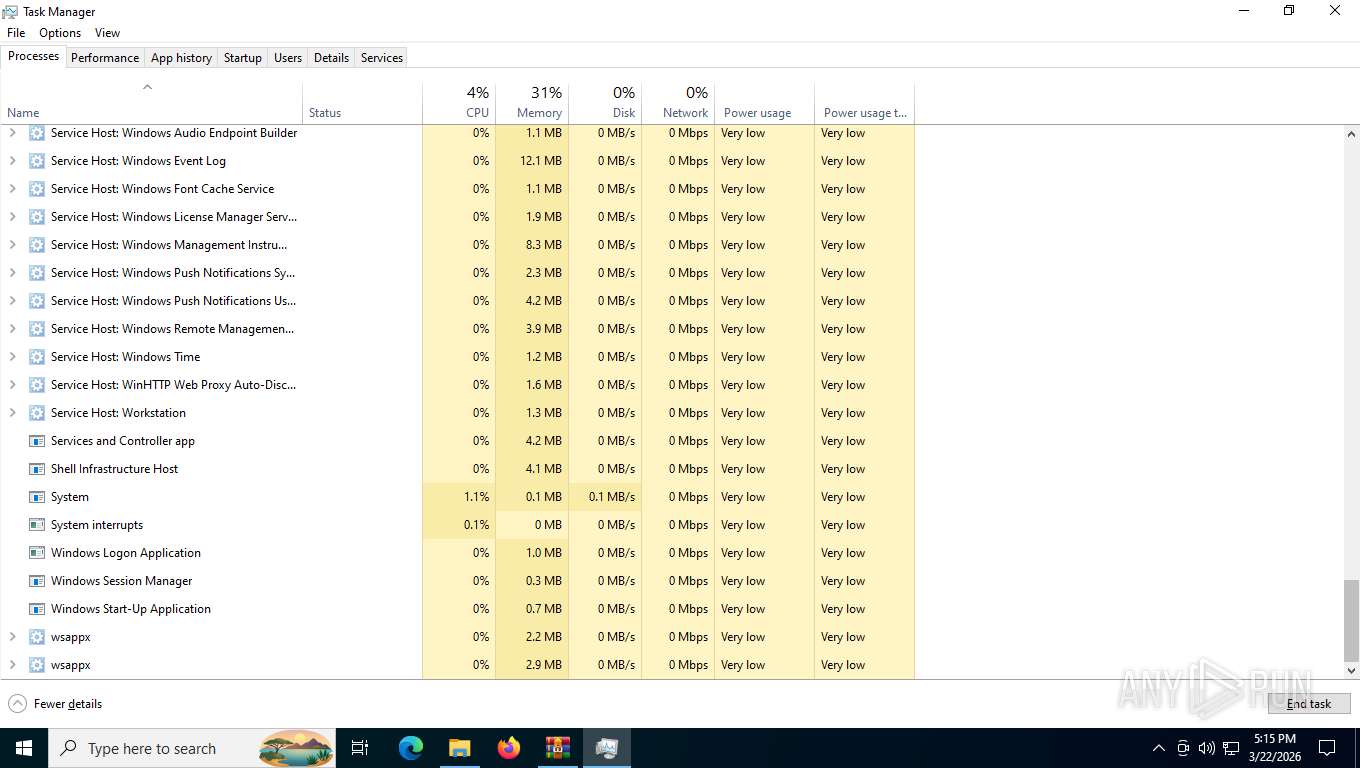
| 1132 | "C:\WINDOWS\system32\taskmgr.exe" /7 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1268 | "C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\python\builds\python-3.14.3-embed-win32\pythonw.exe" -x "C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\license.txt" | C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\python\builds\python-3.14.3-embed-win32\pythonw.exe | traffic3.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 0 Version: 3.14.3 Modules
| |||||||||||||||
| 2304 | "C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\python\builds\python-3.14.3-embed-win32\pythonw.exe" -x "C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\license.txt" | C:\Users\admin\AppData\Local\Temp\fe7efe75-f982-4d90-818b-ddfd62cdeafa\python\builds\python-3.14.3-embed-win32\pythonw.exe | traffic3.exe | ||||||||||||
User: admin Company: Python Software Foundation Integrity Level: MEDIUM Description: Python Exit code: 3221225477 Version: 3.14.3 Modules
| |||||||||||||||
| 2304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5508,i,696066090788721624,15952903084957980498,262144 --variations-seed-version --mojo-platform-channel-handle=5280 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2368 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=6216,i,13282863435181508812,18434466595966297094,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6484 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4492,i,696066090788721624,15952903084957980498,262144 --variations-seed-version --mojo-platform-channel-handle=3776 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2664 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3976,i,696066090788721624,15952903084957980498,262144 --variations-seed-version --mojo-platform-channel-handle=5284 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
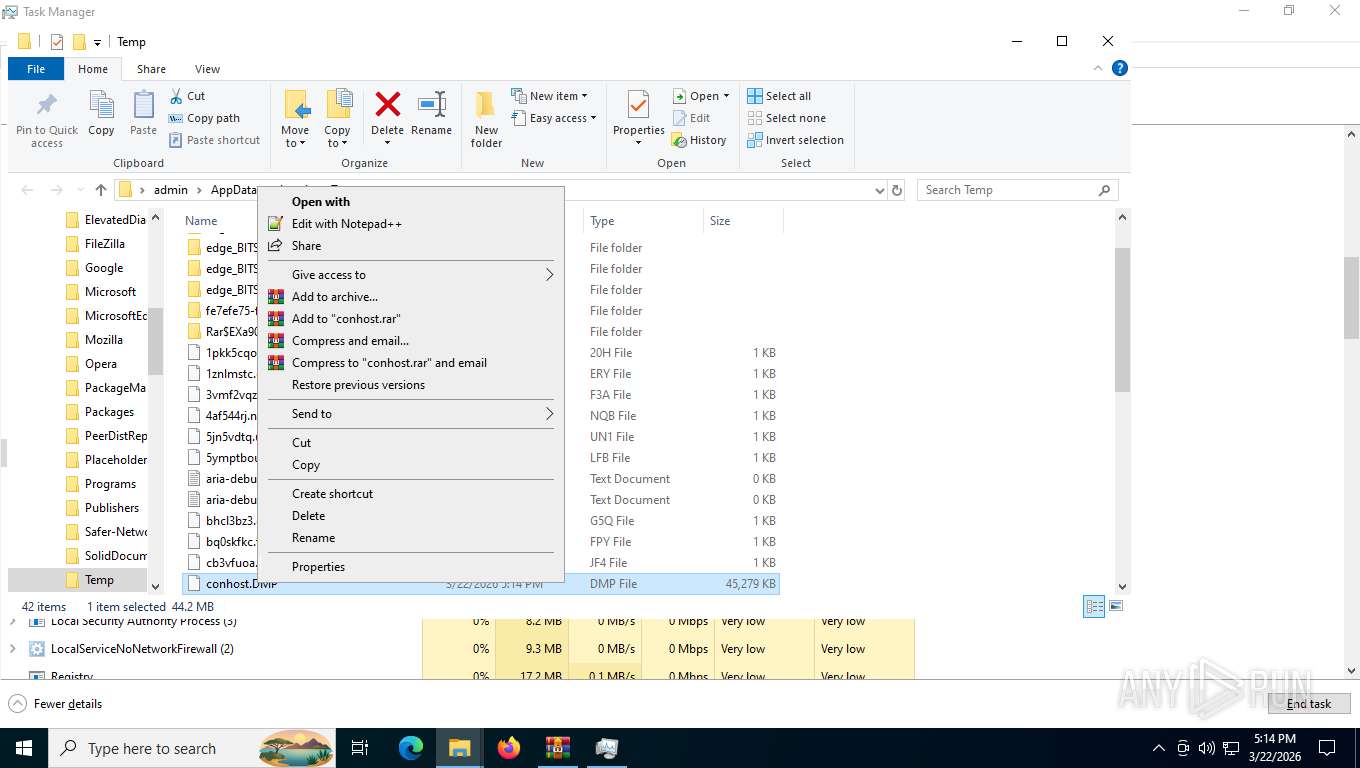
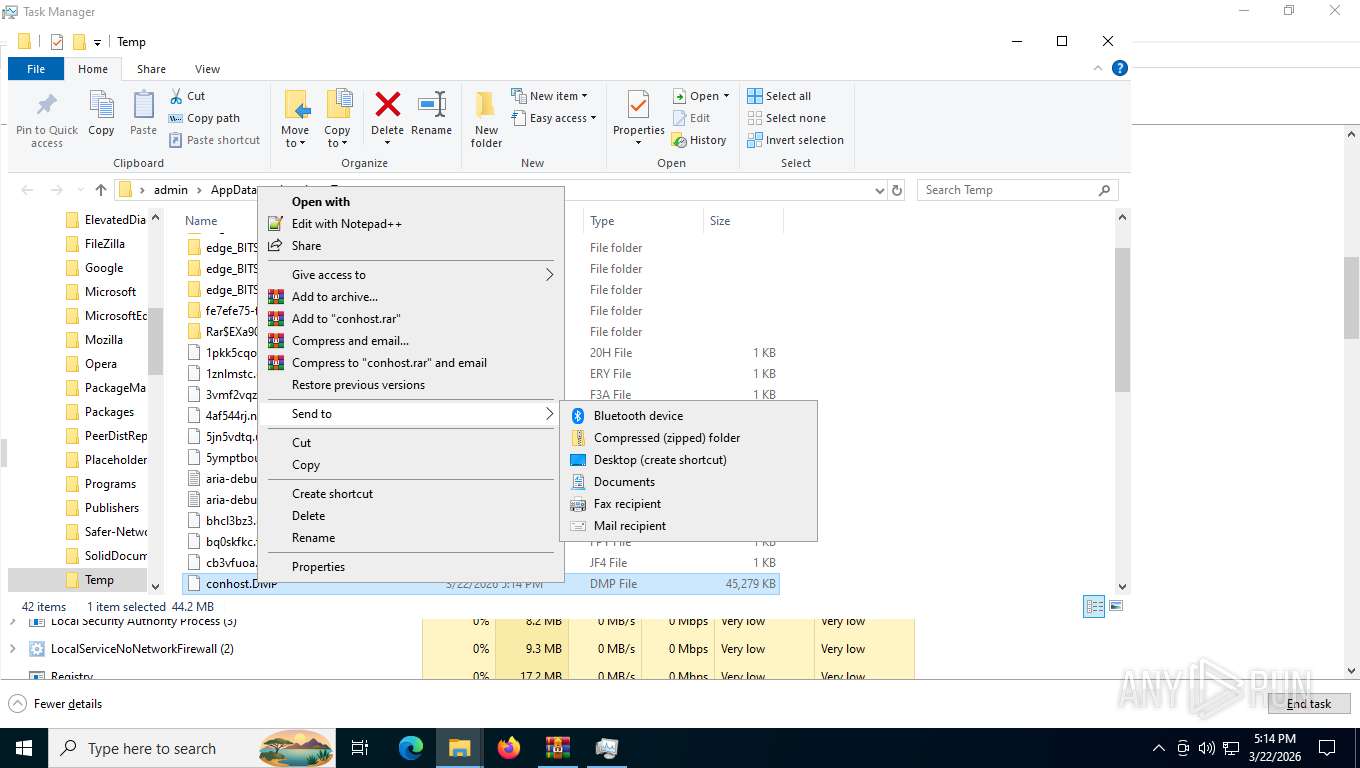
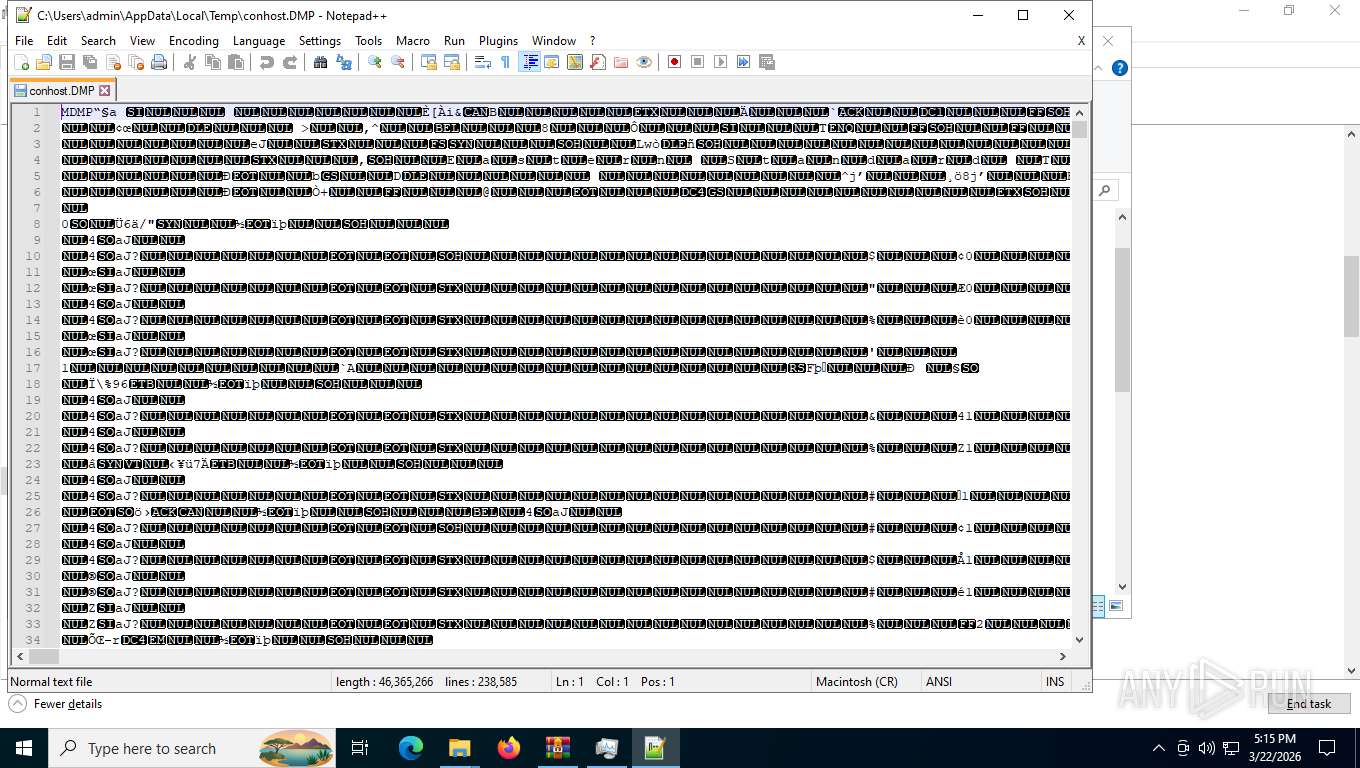
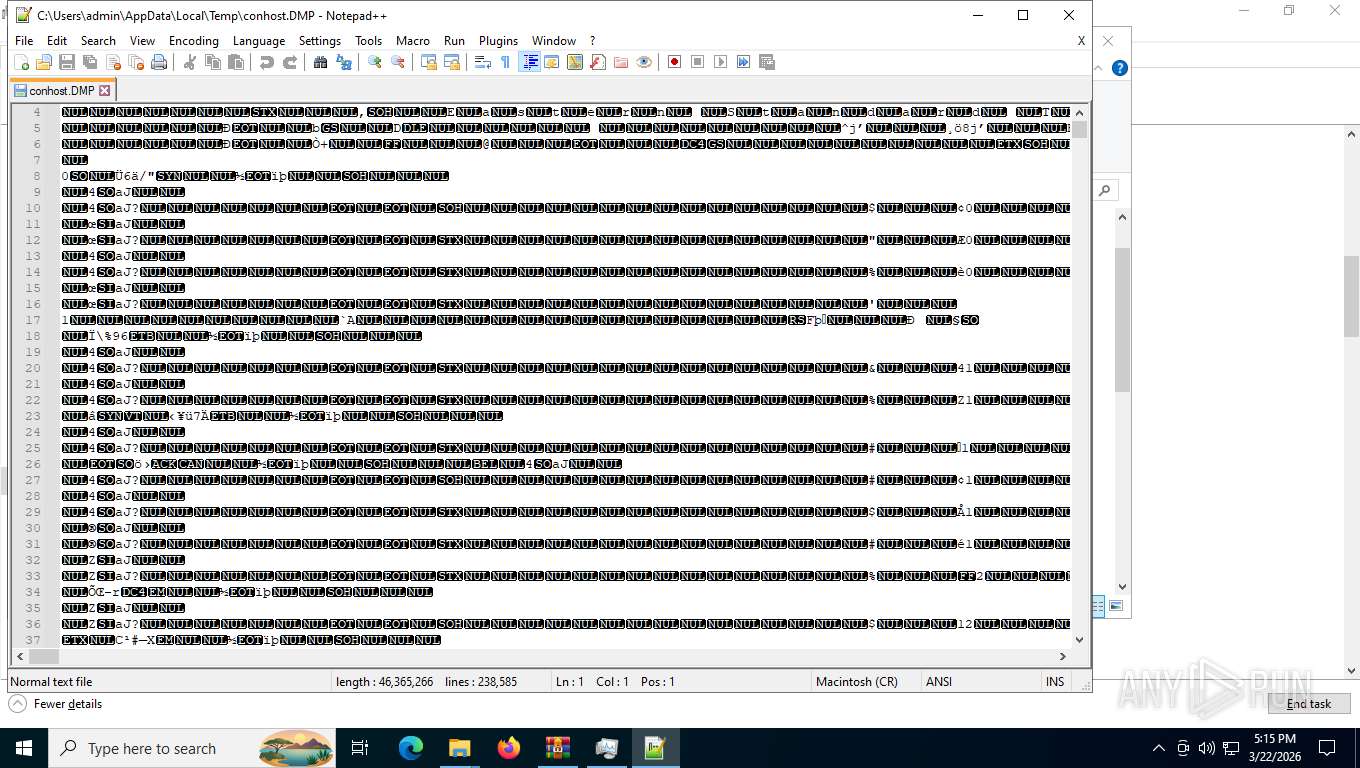
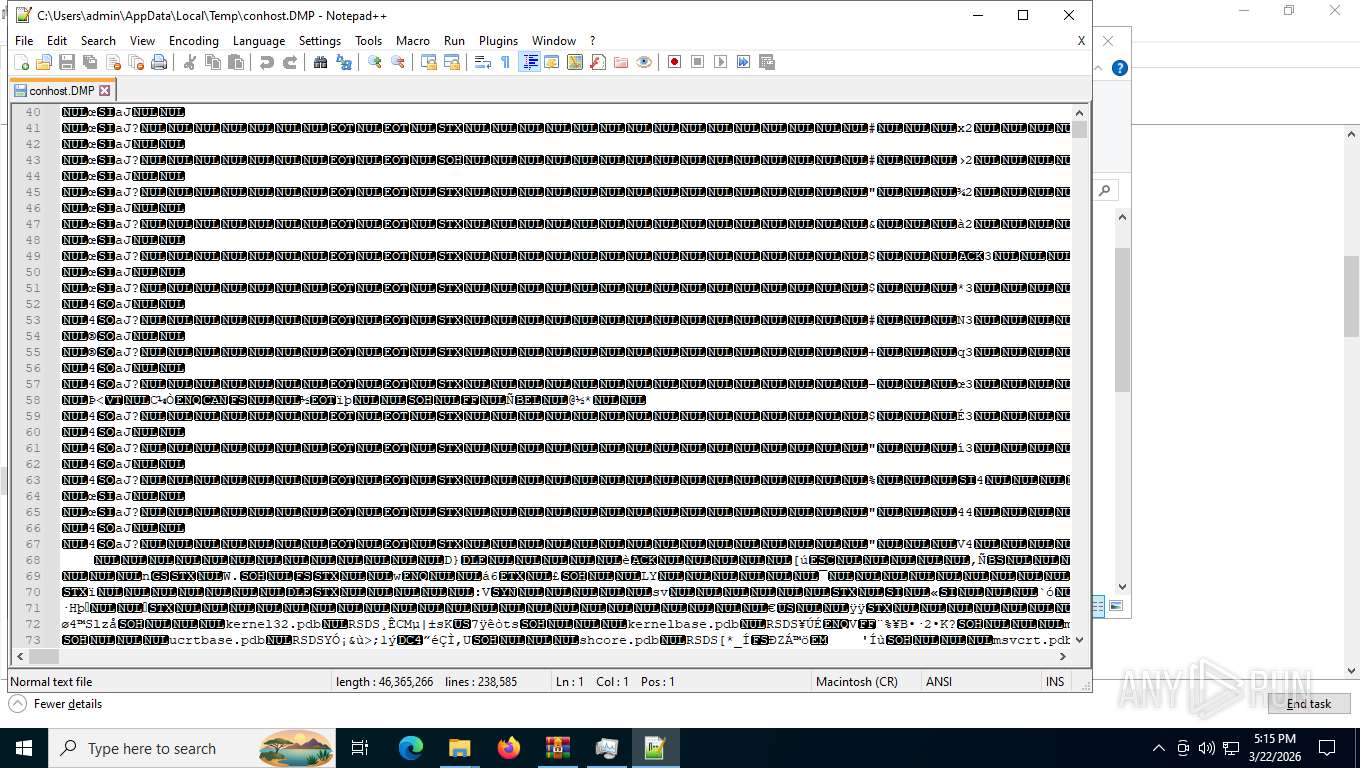
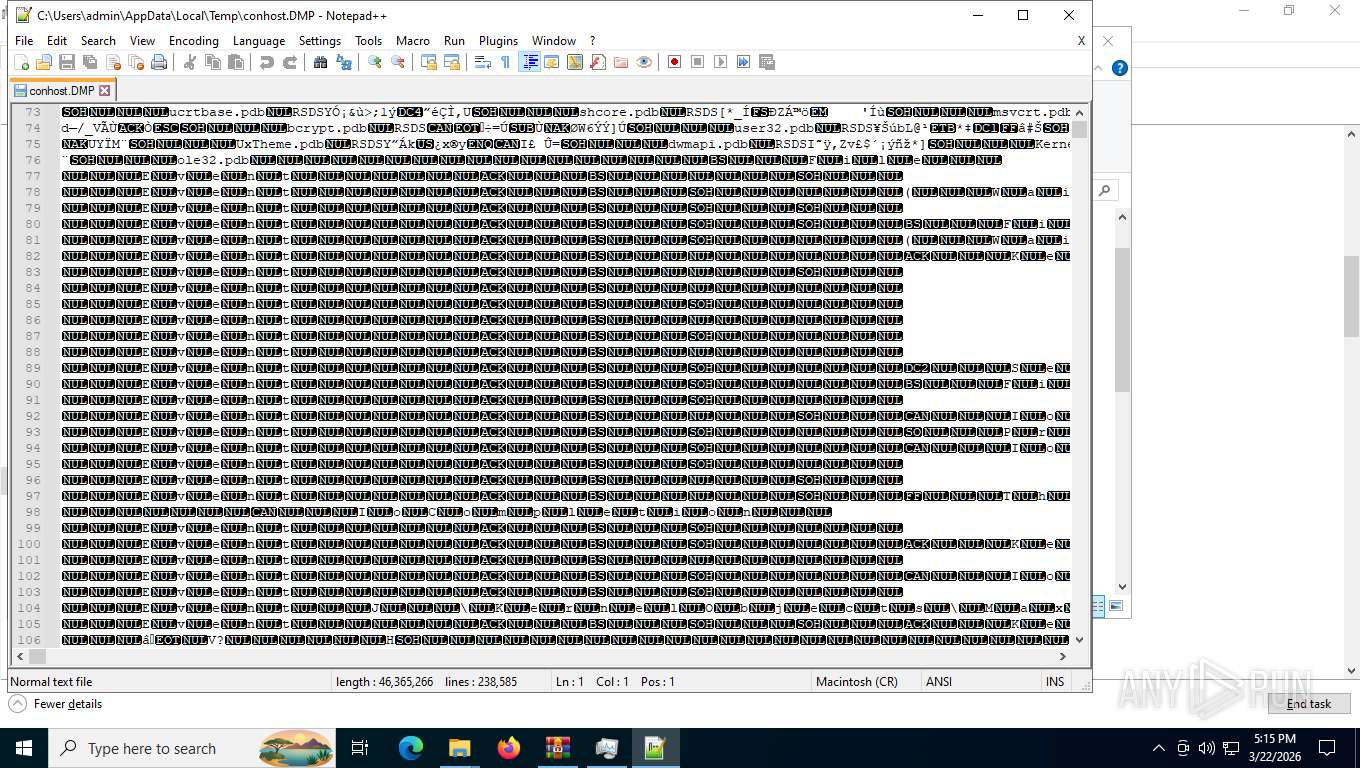
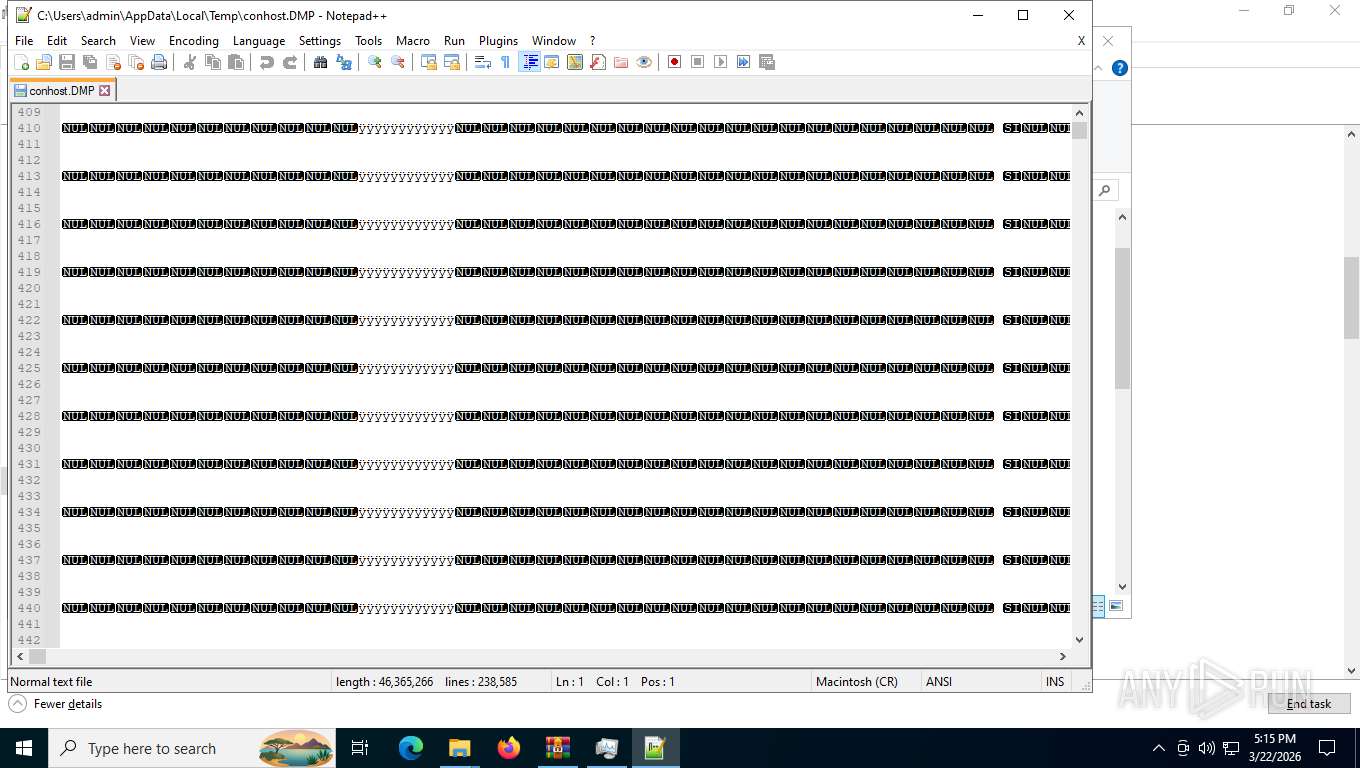
| 2960 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\AppData\Local\Temp\conhost.DMP" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.91 Modules
| |||||||||||||||
| 3420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffe2392f208,0x7ffe2392f214,0x7ffe2392f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
18 774
Read events
18 752
Write events
21
Delete events
1
Modification events
| (PID) Process: | (8400) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Downloads\chromium_build 1.zip | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\traffic3.zip | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (9036) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2304) pythonw.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
0
Suspicious files
18
Text files
61
Unknown types
448
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RFdffad.TMP | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RFdffbd.TMP | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RFdffcd.TMP | — | |
MD5:— | SHA256:— | |||
| 5784 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RFdffdc.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
300
TCP/UDP connections
99
DNS requests
106
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4136 | msedge.exe | GET | — | 38.146.27.206:443 | https://tuoqunt.com/traffic3.zip | US | — | — | unknown |
4136 | msedge.exe | GET | 304 | 150.171.28.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
4136 | msedge.exe | GET | 200 | 52.123.243.221:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=67&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | binary | 4.59 Kb | whitelisted |
4136 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:xs4UiBgEK1O7ORobyUKwXjQ-vRk_7TwYHRFJk4WkjM4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | binary | 97 b | whitelisted |
4136 | msedge.exe | GET | 200 | 13.107.246.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
4136 | msedge.exe | POST | 200 | 142.250.201.67:443 | https://update.googleapis.com/service/update2/json?cup2key=14:CssMci_wORfuVRJhGkpvsIT8J64p3JM6Zm48u4K66PU&cup2hreq=09581d1bc3d3e428ea824763f60098b0a81f33f0235f7f9a34f166fecd5091dd | US | binary | 349 b | whitelisted |
4136 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | binary | 465 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 304 | 51.104.136.2:443 | https://settings-win.data.microsoft.com/settings/v3.0/OneSettings/Client?OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&LocalDeviceID=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&FlightRing=Retail&AttrDataVer=186&OSUILocale=en-US&OSSkuId=48&App=WOSC&AppVer=&IsFlightingEnabled=0&TelemetryLevel=1&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
4136 | msedge.exe | GET | 200 | 104.18.22.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
4136 | msedge.exe | GET | 200 | 150.171.27.11:443 | https://edge.microsoft.com/entityextractiontemplates/api/v1/assets/find-assets?name=domains_config_gz&version=3.*.*&channel=stable&key=d414dd4f9db345fa8003e32adc81b362 | US | binary | 267 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
4212 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8028 | slui.exe | 48.192.1.65:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
4136 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4136 | msedge.exe | 52.123.243.221:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4136 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4136 | msedge.exe | 38.146.27.206:443 | tuoqunt.com | COGENT-174 | US | unknown |
4136 | msedge.exe | 13.107.246.44:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
tuoqunt.com |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4136 | msedge.exe | Domain Observed Used for C2 Detected | PAYLOAD [ANY.RUN] PowerShell Payload Delivery Domain (tuoqunt .com) |
4136 | msedge.exe | Domain Observed Used for C2 Detected | PAYLOAD [ANY.RUN] PowerShell Payload Delivery Domain (tuoqunt .com) |
4212 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: error while getting certificate informations
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\updater\gup.exe
|