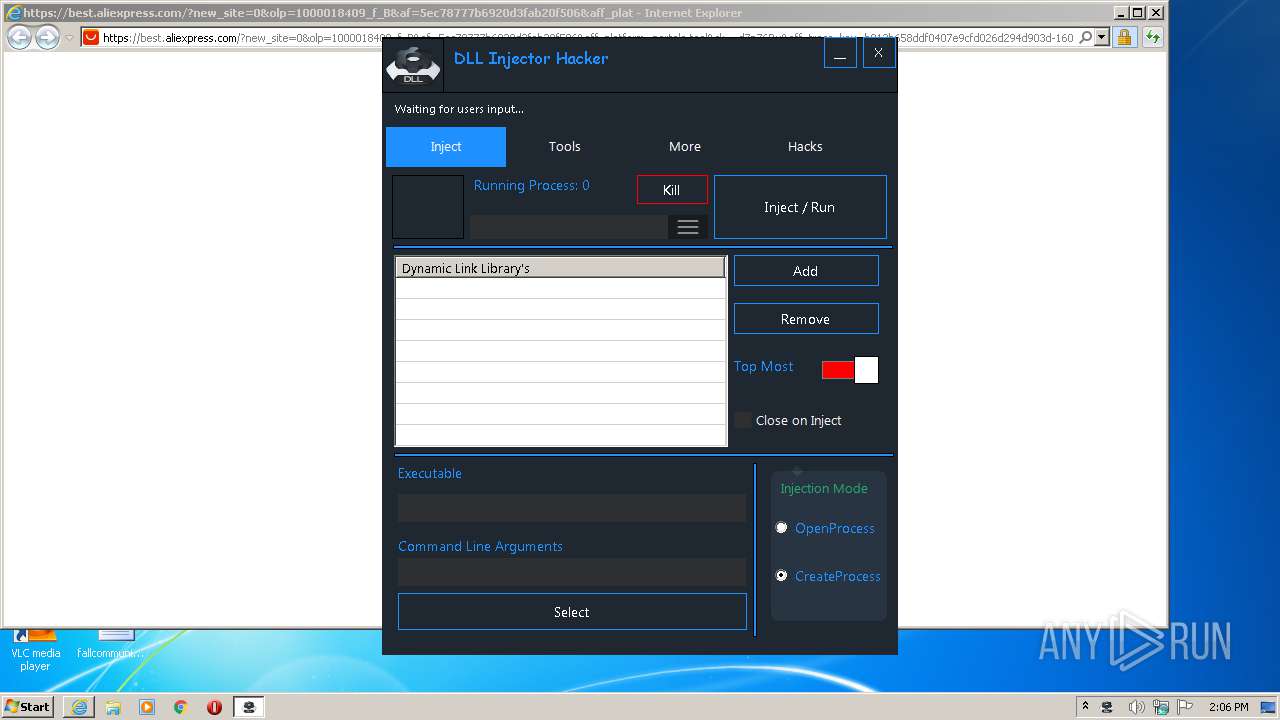
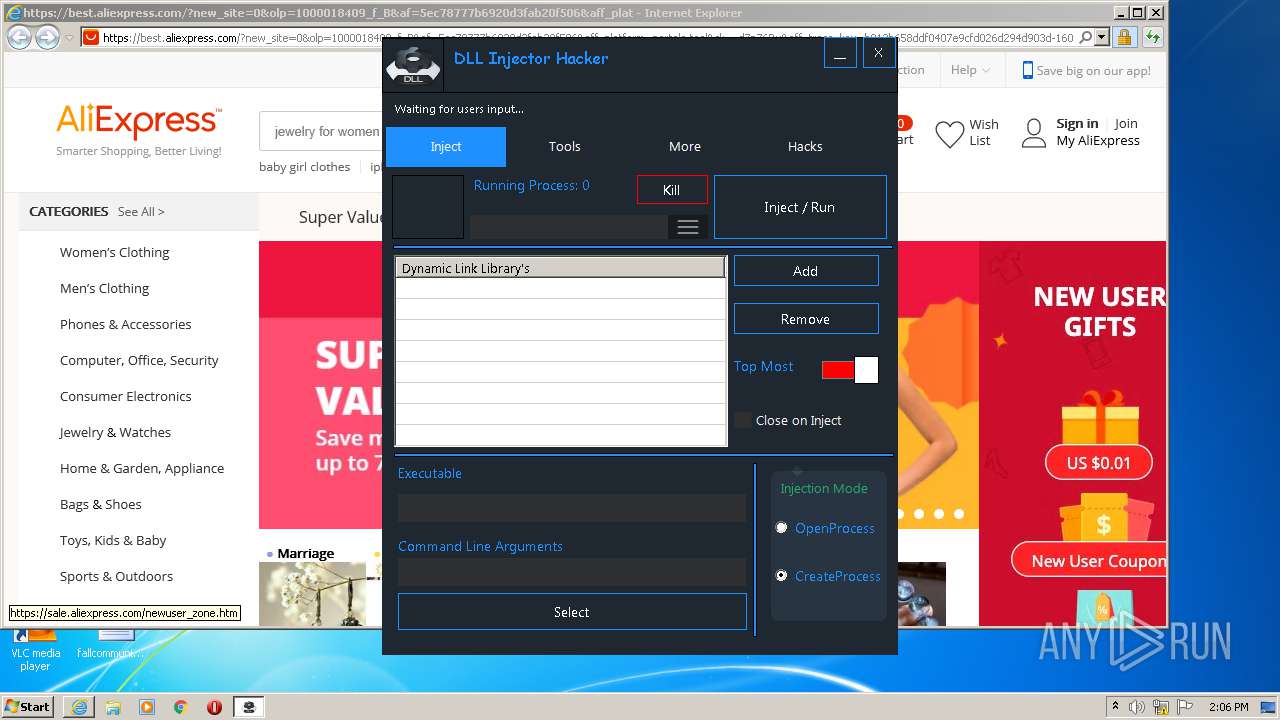
| download: | dll-injector-hacker_0.6.6.exe |
| Full analysis: | https://app.any.run/tasks/62b3458f-afef-4659-85ee-6e14d2807a7d |
| Verdict: | Malicious activity |
| Analysis date: | September 27, 2020, 13:05:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | ACDB662BC94B29B863BBB25C68F8842D |
| SHA1: | 2CD50241C42B7C708B8602A25DB5DF985DE76BDB |
| SHA256: | 5EA8A99442382FFBF757B88931B2AE817A3EA4365ADB54AD2C13C4308F77CF13 |
| SSDEEP: | 24576:3P6zpA1nczaKWg4y1OppRoX3sUYKK7C7IYA02PC2ed9NNCsBCMKnx74ulIxA:3N1q5kRyKmMvedEsBk4ulI6 |
MALICIOUS
Changes settings of System certificates
- dll-injector-hacker_0.6.6.exe (PID: 3064)
SUSPICIOUS
Reads Environment values
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Reads Internet Cache Settings
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Changes IE settings (feature browser emulation)
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Adds / modifies Windows certificates
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Creates files in the user directory
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Reads internet explorer settings
- dll-injector-hacker_0.6.6.exe (PID: 3064)
Executed via COM
- iexplore.exe (PID: 3620)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3620)
Reads internet explorer settings
- iexplore.exe (PID: 1920)
Reads settings of System Certificates
- dll-injector-hacker_0.6.6.exe (PID: 3064)
- iexplore.exe (PID: 1920)
- iexplore.exe (PID: 3620)
Application launched itself
- iexplore.exe (PID: 3620)
Creates files in the user directory
- iexplore.exe (PID: 1920)
- iexplore.exe (PID: 3620)
Reads Internet Cache Settings
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 1920)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1920)
Changes settings of System certificates
- iexplore.exe (PID: 1920)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:09 18:31:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1733632 |
| InitializedDataSize: | 153600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a92ae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.6.4.6 |
| ProductVersionNumber: | 0.6.4.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| ProductName: | DLL Injector Hacker |
| FileDescription: | DLL Injector Hacker |
| CompanyName: | none |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | DLL Injector Hacker |
| Comments: | Inject your DLLs into games, etc. |
| FileVersion: | 0.6.4.6 |
| ProductVersion: | 0.6.4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Apr-2019 16:31:05 |
| Detected languages: |
|
| ProductName: | DLL Injector Hacker |
| FileDescription: | DLL Injector Hacker |
| CompanyName: | none |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | DLL Injector Hacker |
| Comments: | Inject your DLLs into games, etc. |
| FileVersion: | 0.6.4.6 |
| ProductVersion: | 0.6.4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 09-Apr-2019 16:31:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x001A72B4 | 0x001A7400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.85428 |
.rsrc | 0x001AA000 | 0x00025600 | 0x00025600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.78116 |
.reloc | 0x001D0000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.9039 | 2461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 7.98004 | 46751 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.01669 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.11498 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.38792 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.35826 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 4.58366 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.59271 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
32512 | 2.94489 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
44
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 560 | "C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6.exe" | C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1920 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3620 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3064 | "C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6.exe" | C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3620 | "C:\Program Files\Internet Explorer\iexplore.exe" -startmediumtab -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 159
Read events
970
Write events
186
Delete events
3
Modification events
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 11001 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_AJAX_CONNECTIONEVENTS |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 1 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_ENABLE_CLIPCHILDREN_OPTIMIZATION |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 1 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_MANAGE_SCRIPT_CIRCULAR_REFS |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 1 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_DOMSTORAGE |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 1 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_GPU_RENDERING |
| Operation: | write | Name: | dll-injector-hacker_0.6.6.exe |
Value: 1 | |||
| (PID) Process: | (3064) dll-injector-hacker_0.6.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
44
Text files
167
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\600WXRZJ.txt | — | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\550XINSM.txt | — | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\RU9Z88J8.txt | — | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Local\Temp\CabF6DF.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Local\Temp\TarF6E0.tmp | — | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\adfly_7[1].css | text | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CFE86DBBE02D859DC92F1E17E0574EE8_46766FC45507C0B9E264E4C18BC7288B | der | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\BxPw[1].htm | html | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\view111[1].js | text | |
MD5:— | SHA256:— | |||
| 3064 | dll-injector-hacker_0.6.6.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\2GIW396N.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
76
DNS requests
39
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3064 | dll-injector-hacker_0.6.6.exe | GET | 301 | 185.60.216.35:80 | http://www.facebook.com/plugins/like.php?href=https%3A%2F%2Fwww.facebook.com%2Fx19ltd.adfly&width=150&fb_source=unshorten&layout=button_count&action=like&show_faces=false&share=true&height=21&appId=399141353502152 | IE | — | — | whitelisted |
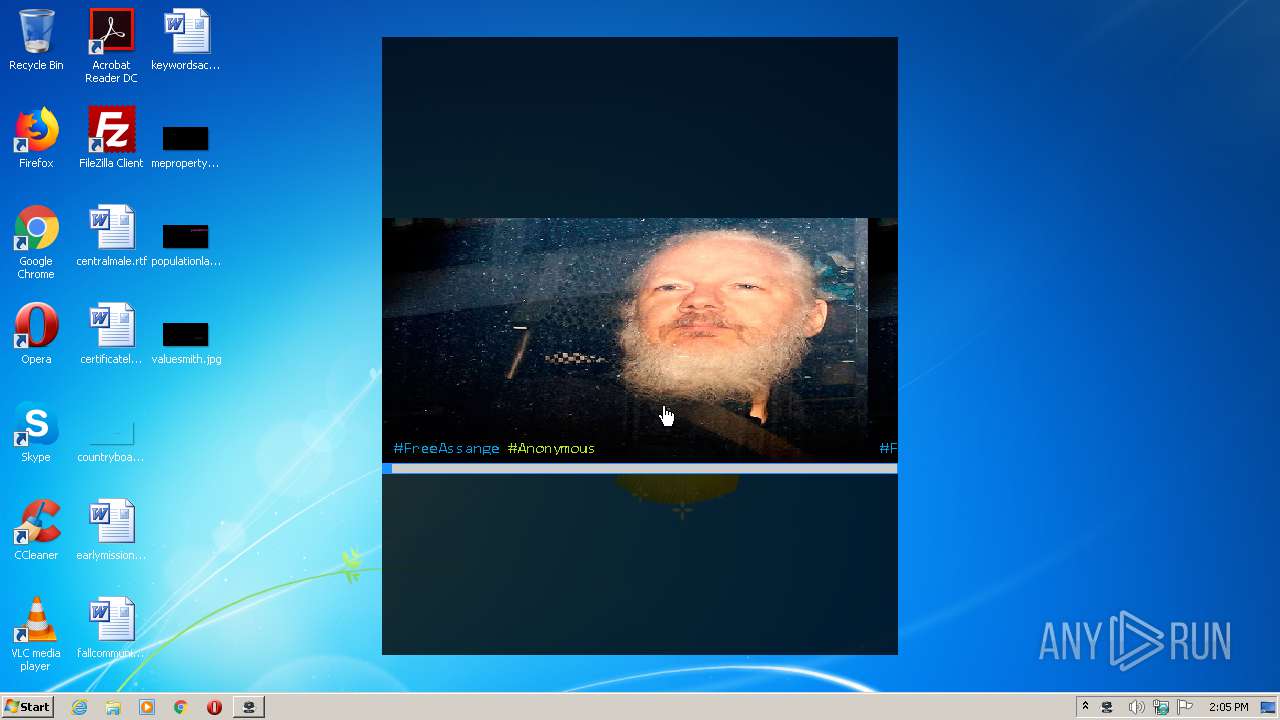
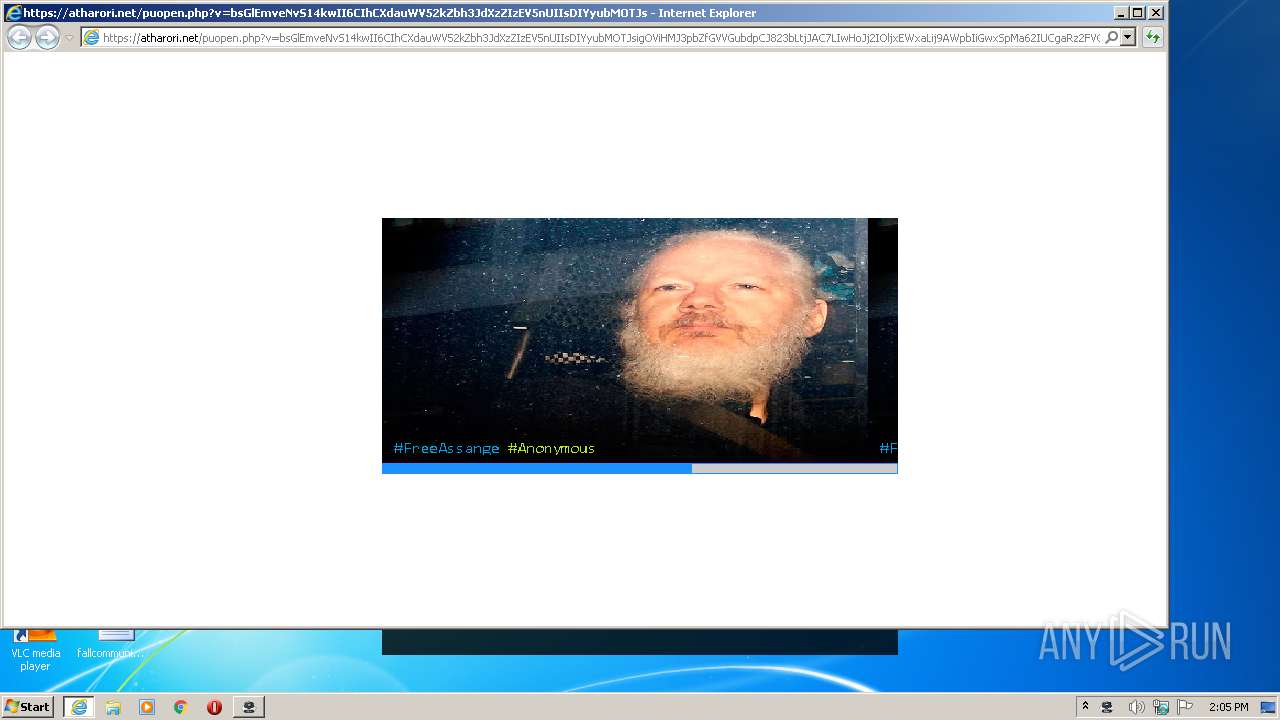
3064 | dll-injector-hacker_0.6.6.exe | GET | 301 | 104.26.0.230:80 | http://j.gs/BxPw | US | — | — | malicious |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.64.105.28:80 | http://cdn.atharori.net/static/css/adfly_7.css | US | text | 869 b | shared |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.64.105.28:80 | http://cdn.atharori.net/static/js/b64.js | US | text | 1.07 Kb | shared |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.64.105.28:80 | http://cdn.atharori.net/static/js/main.js | US | text | 667 b | shared |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.64.105.28:80 | http://cdn.atharori.net/static/js/view111.js | US | text | 28.1 Kb | shared |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.217.18.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDqXuNQ97mPtAIAAAAAektt | US | der | 472 b | whitelisted |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3064 | dll-injector-hacker_0.6.6.exe | GET | 200 | 172.64.105.28:80 | http://cdn.atharori.net/static/js/amvn.js | US | text | 90.2 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3064 | dll-injector-hacker_0.6.6.exe | 172.67.165.44:443 | hax4ever.com | — | US | suspicious |
3064 | dll-injector-hacker_0.6.6.exe | 104.26.0.230:80 | j.gs | Cloudflare Inc | US | suspicious |
3064 | dll-injector-hacker_0.6.6.exe | 172.64.104.28:80 | atharori.net | Cloudflare Inc | US | shared |
3064 | dll-injector-hacker_0.6.6.exe | 104.23.98.190:443 | pastebin.com | Cloudflare Inc | US | malicious |
3064 | dll-injector-hacker_0.6.6.exe | 51.210.112.129:443 | i.ibb.co | — | GB | unknown |
3064 | dll-injector-hacker_0.6.6.exe | 172.64.105.28:80 | atharori.net | Cloudflare Inc | US | shared |
3064 | dll-injector-hacker_0.6.6.exe | 172.217.18.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3064 | dll-injector-hacker_0.6.6.exe | 13.35.253.190:80 | d1nmxiiewlx627.cloudfront.net | — | US | unknown |
3064 | dll-injector-hacker_0.6.6.exe | 172.217.18.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3064 | dll-injector-hacker_0.6.6.exe | 172.64.104.28:443 | atharori.net | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hax4ever.com |
| unknown |
j.gs |
| malicious |
atharori.net |
| unknown |
pastebin.com |
| malicious |
i.ibb.co |
| shared |
ajax.googleapis.com |
| whitelisted |
cdn.atharori.net |
| unknown |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
www.google-analytics.com |
| whitelisted |
Threats
4 ETPRO signatures available at the full report