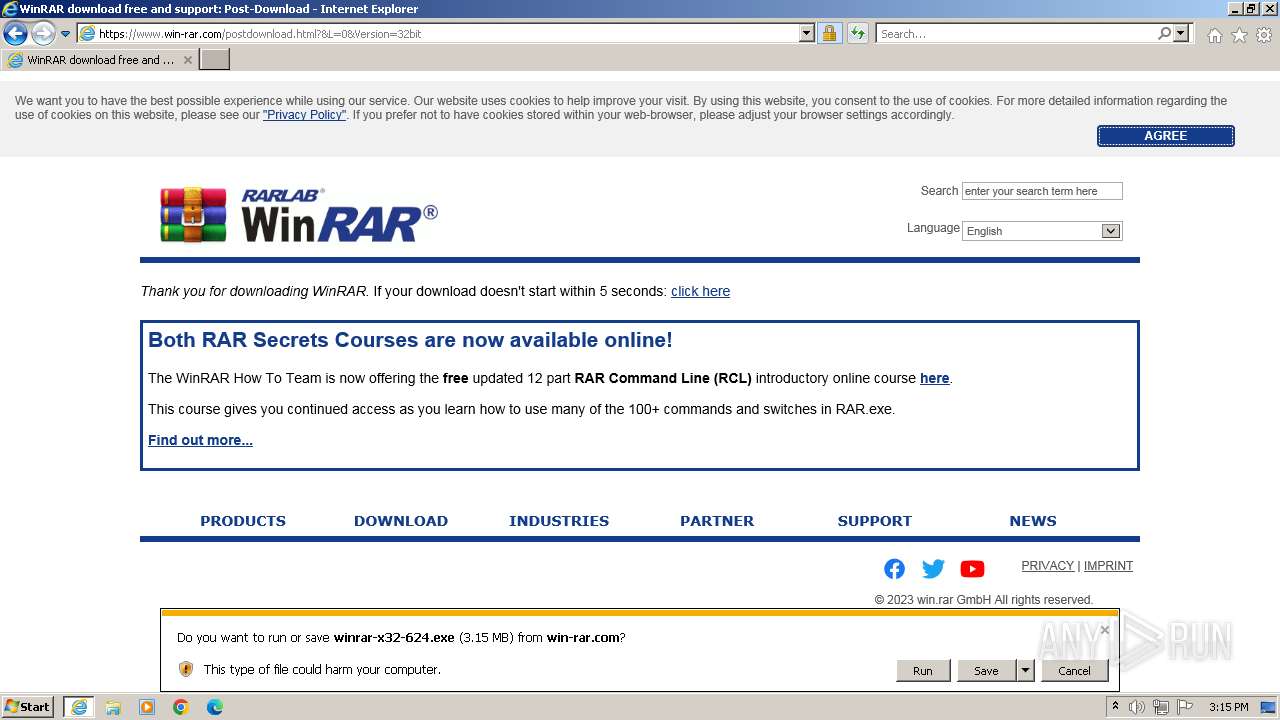
| URL: | https://www.win-rar.com/predownload.html?&L=0&Version=32bit |
| Full analysis: | https://app.any.run/tasks/aec244d9-b7be-4116-9b92-663f313b4bc6 |
| Verdict: | Malicious activity |
| Analysis date: | December 15, 2023, 15:14:52 |
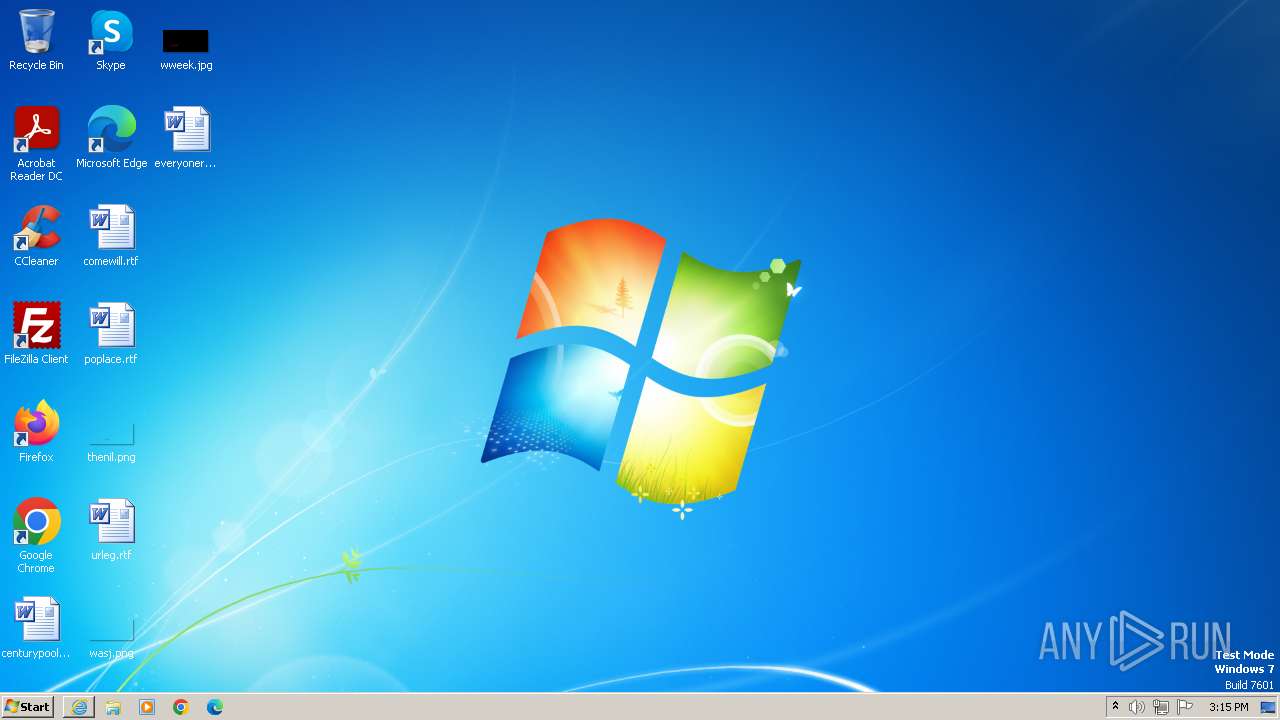
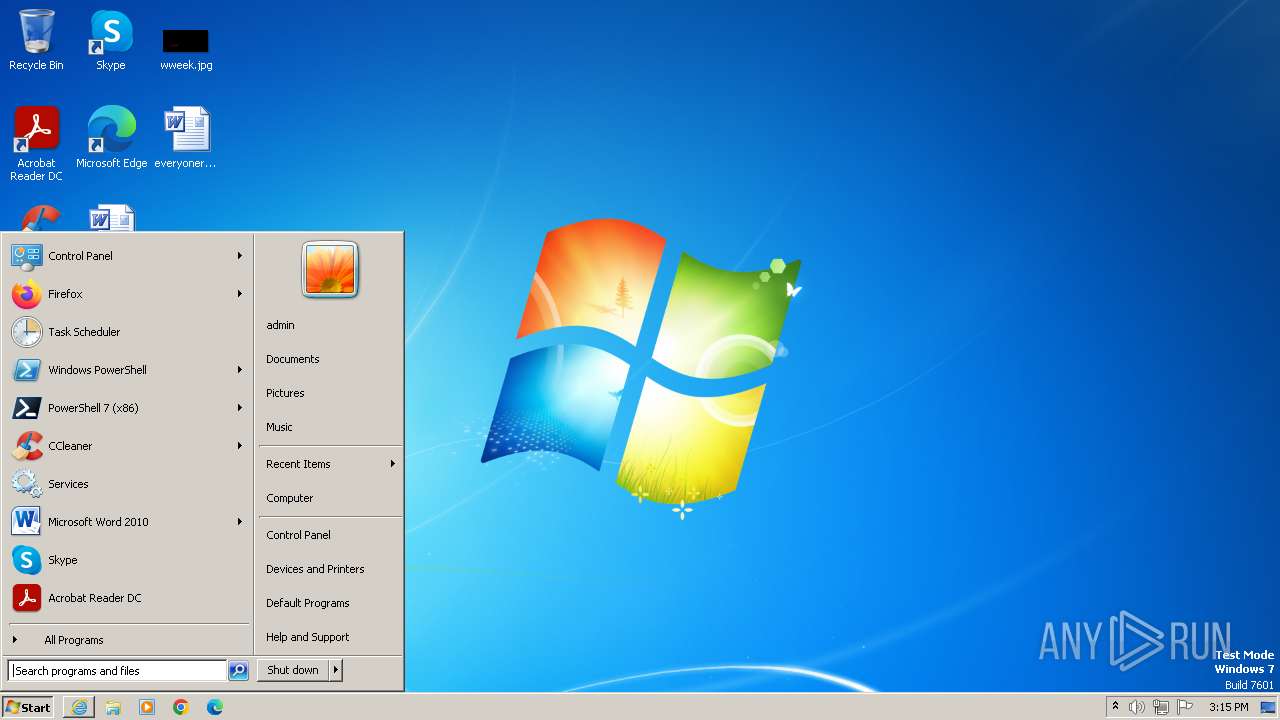
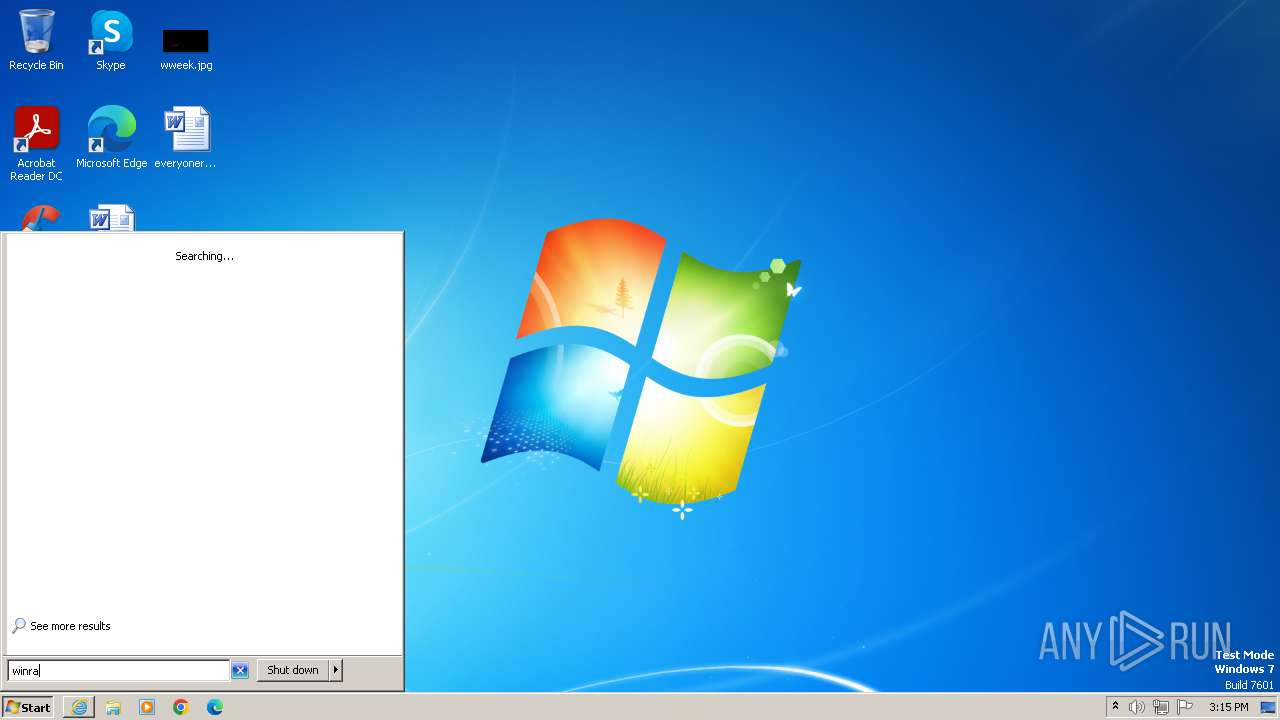
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0553B403DDA11FF32F72A725D800930D |
| SHA1: | 4312DE6C2CC4068E8B84CB162C60683791494FD9 |
| SHA256: | 5E93715796406901F85738B690B0014E71838D577CF3F3DF420F609366A33E4F |
| SSDEEP: | 3:N8DSLUPUDjWqVDxMNWXMRn:2OLUPhqVDxMn |
MALICIOUS
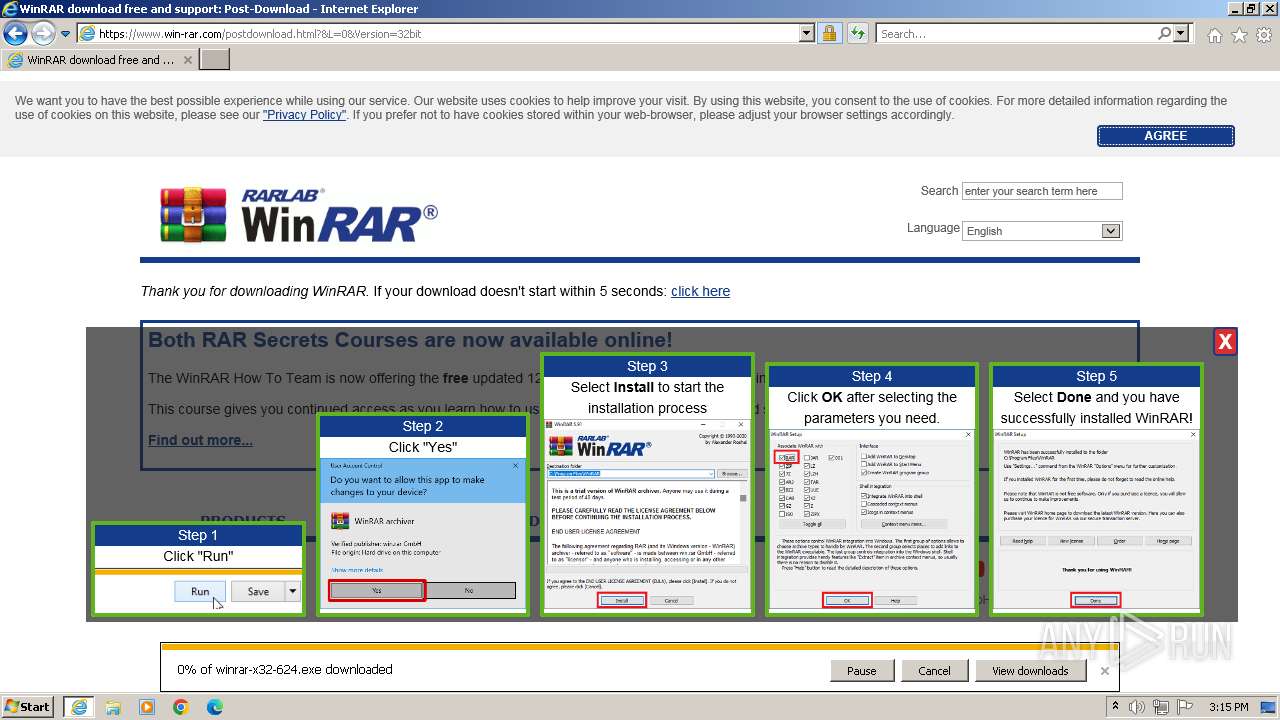
Drops the executable file immediately after the start
- winrar-x32-624.exe (PID: 3116)
SUSPICIOUS
Reads the Internet Settings
- winrar-x32-624.exe (PID: 3116)
Reads Microsoft Outlook installation path
- winrar-x32-624.exe (PID: 3116)
Reads Internet Explorer settings
- winrar-x32-624.exe (PID: 3116)
Drops 7-zip archiver for unpacking
- winrar-x32-624.exe (PID: 3116)
Creates/Modifies COM task schedule object
- uninstall.exe (PID: 3496)
Searches for installed software
- uninstall.exe (PID: 3496)
Creates a software uninstall entry
- uninstall.exe (PID: 3496)
INFO
Application launched itself
- iexplore.exe (PID: 2540)
Reads the computer name
- wmpnscfg.exe (PID: 3856)
- winrar-x32-624.exe (PID: 3116)
- uninstall.exe (PID: 3496)
Manual execution by a user
- wmpnscfg.exe (PID: 3856)
- WinRAR.exe (PID: 2468)
Checks supported languages
- wmpnscfg.exe (PID: 3856)
- winrar-x32-624.exe (PID: 3116)
- uninstall.exe (PID: 3496)
Drops the executable file immediately after the start
- iexplore.exe (PID: 2540)
- iexplore.exe (PID: 1088)
The process uses the downloaded file
- iexplore.exe (PID: 2540)
Checks proxy server information
- winrar-x32-624.exe (PID: 3116)
Reads the machine GUID from the registry
- winrar-x32-624.exe (PID: 3116)
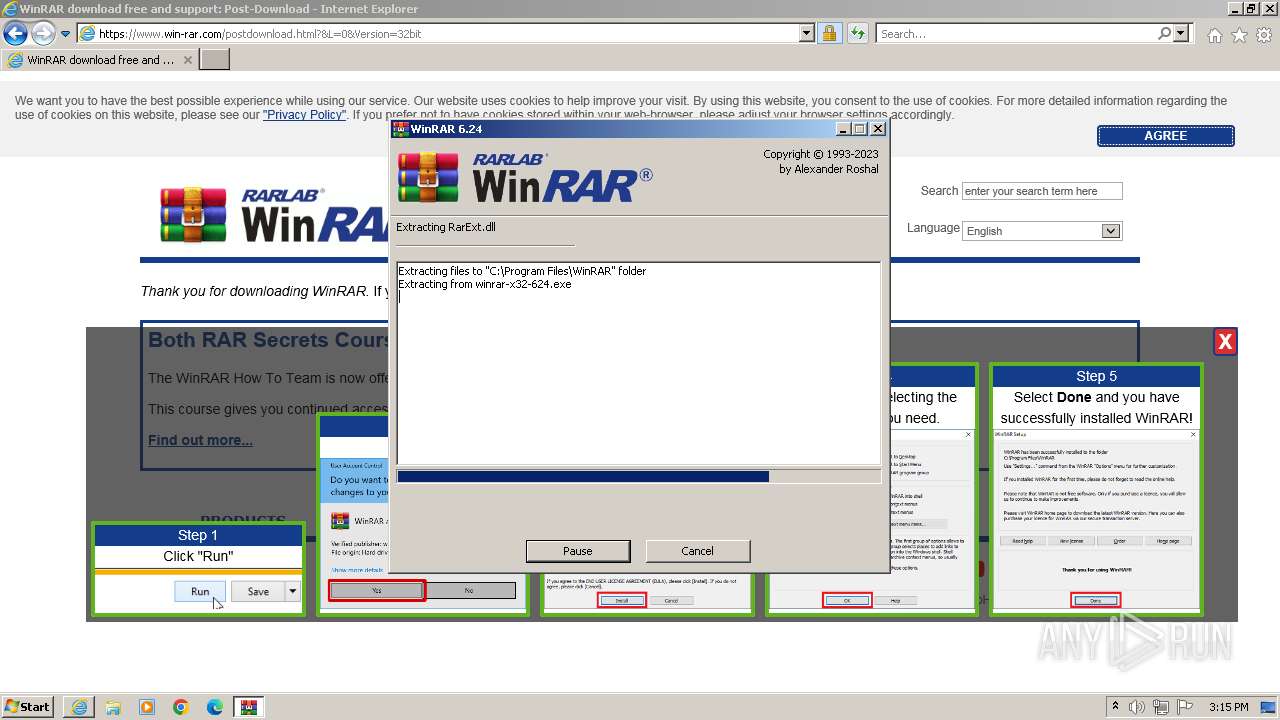
Creates files in the program directory
- winrar-x32-624.exe (PID: 3116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
7
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1088 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2540 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
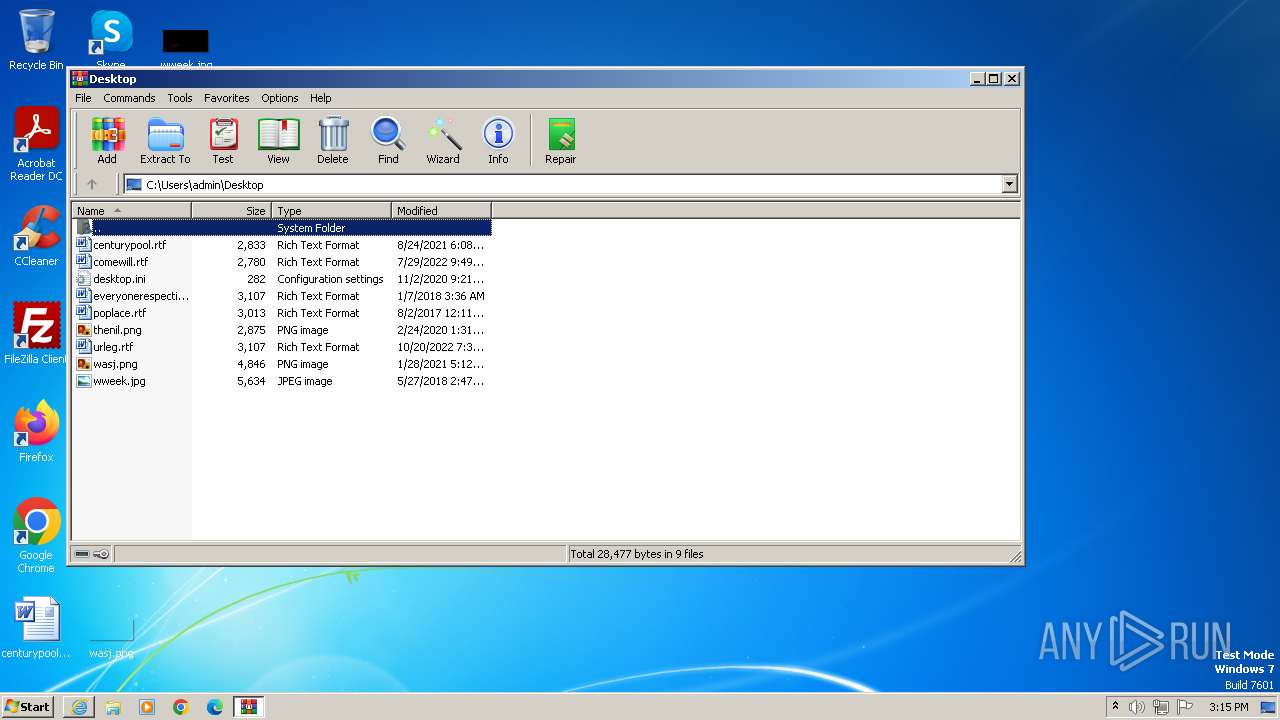
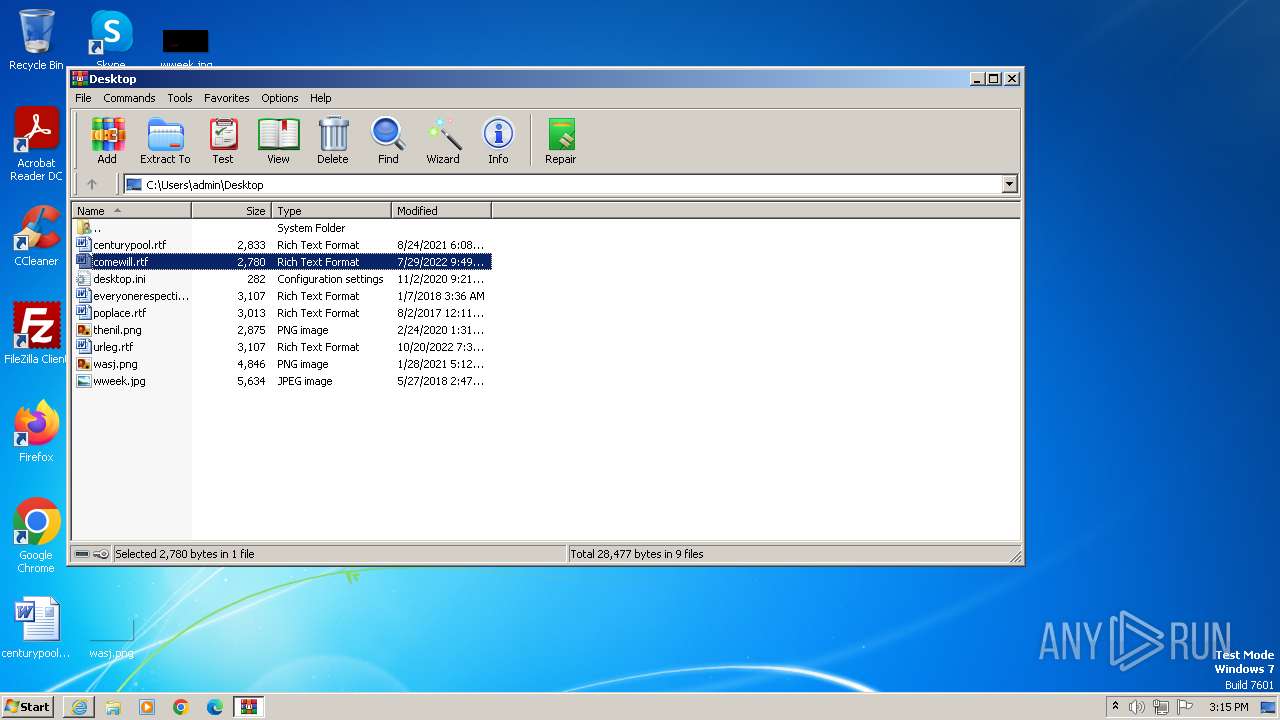
| 2468 | "C:\Program Files\WinRAR\WinRAR.exe" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 6.24.0 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.win-rar.com/predownload.html?&L=0&Version=32bit" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
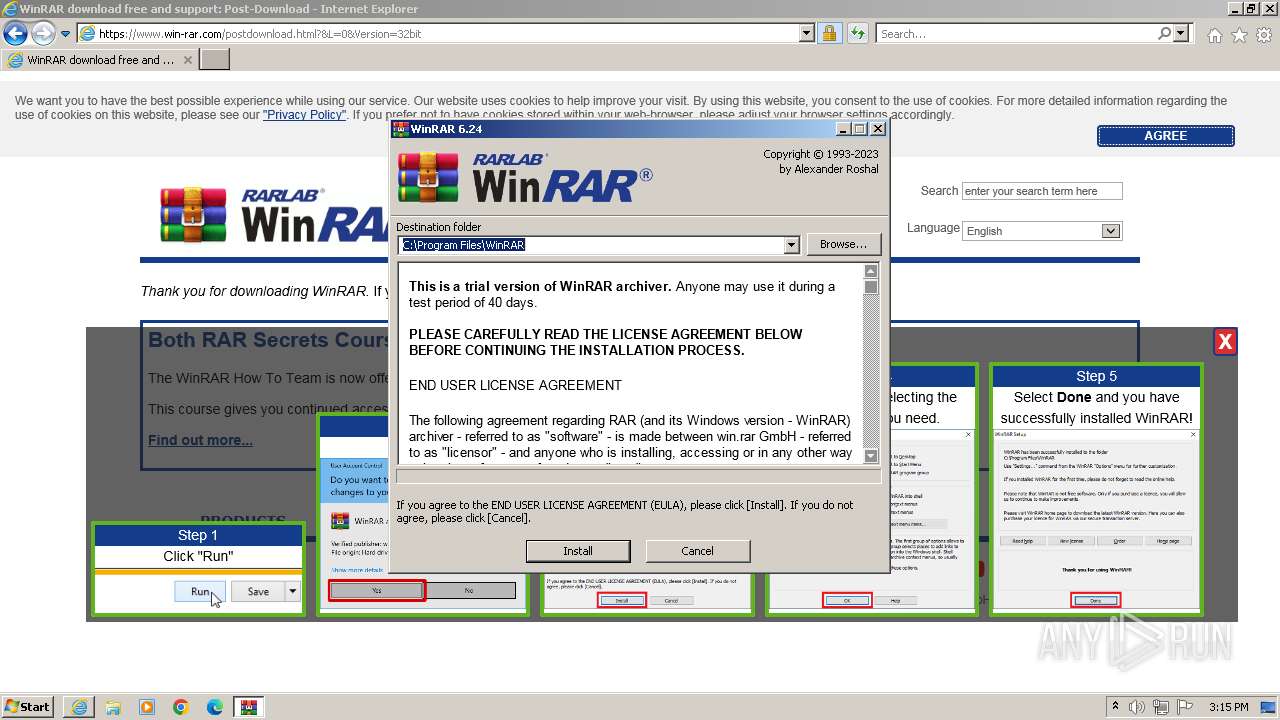
| 3116 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\winrar-x32-624.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\winrar-x32-624.exe | iexplore.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: WinRAR archiver Exit code: 0 Version: 6.24.0 Modules
| |||||||||||||||
| 3436 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\winrar-x32-624.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\winrar-x32-624.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 3221226540 Version: 6.24.0 Modules
| |||||||||||||||
| 3496 | "C:\Program Files\WinRAR\uninstall.exe" /setup | C:\Program Files\WinRAR\uninstall.exe | — | winrar-x32-624.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: HIGH Description: Uninstall WinRAR Exit code: 0 Version: 6.24.0 Modules
| |||||||||||||||
| 3856 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 578
Read events
20 421
Write events
151
Delete events
6
Modification events
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000005A010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2540) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
13
Suspicious files
20
Text files
45
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:E5034468F4C766A164BB3E28D4F0E6C8 | SHA256:C22DF2802E5DA3ECE8D548EE7280F764D7EDB5BA19A3661D0749DD13ACF8F2DB | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA5F.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarA60.tmp | cat | |
MD5:9C0C641C06238516F27941AA1166D427 | SHA256:4276AF3669A141A59388BC56A87F6614D9A9BDDDF560636C264219A7EB11256F | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabA71.tmp | compressed | |
MD5:AC05D27423A85ADC1622C714F2CB6184 | SHA256:C6456E12E5E53287A547AF4103E0397CB9697E466CF75844312DC296D43D144D | |||
| 2540 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:34B3ED26C2428DA8467538A932791184 | SHA256:840EBB8423F409631AE7809F68D406A00BB338757FF8B283238DFB91883B3A75 | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:FEFAEFFF4596EE80FC2A17B62434D78E | SHA256:56F127492098DBD2B9DBE6697119CFC69B7A08D479ACA6045A2D762D819A5829 | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\062FAA989ADCC8896090E4A63FE05E85 | binary | |
MD5:FAB6678B19233E8481E7E421424B708D | SHA256:5E677AA4224E22334F2ACA54911C3B356D1C44B8F5BD97D6052EED0A2D785515 | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:80090388A745FE912DA32DF6C670C625 | SHA256:7C054749AFE4CD626B50E5949534461D833A787B184A4CCD1AFD04A94DA33451 | |||
| 1088 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\predownload[1].htm | html | |
MD5:D5D794FCF00D0B8A4F084AEB96882FA5 | SHA256:B8632BBB2BB0D07EFA44F3ADD8B4D96E8A154999142655472CC6B80F6650F0AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
30
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1088 | iexplore.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?44e705f36e178026 | unknown | compressed | 4.66 Kb | unknown |
1088 | iexplore.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?06cff0cc752c9400 | unknown | compressed | 65.2 Kb | unknown |
1088 | iexplore.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?282a5f2988aaef25 | unknown | compressed | 4.66 Kb | unknown |
1088 | iexplore.exe | GET | 200 | 87.248.205.0:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?028c1e64bf9eff21 | unknown | compressed | 65.2 Kb | unknown |
1088 | iexplore.exe | GET | 200 | 184.24.77.68:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPp2qh%2FNDM3stros4IuzOsfsA%3D%3D | unknown | binary | 503 b | unknown |
1088 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2540 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | binary | 313 b | unknown |
2540 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | iexplore.exe | 51.195.68.163:443 | www.win-rar.com | OVH SAS | FR | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1088 | iexplore.exe | 87.248.205.0:80 | ctldl.windowsupdate.com | LLNW | US | unknown |
1088 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
1088 | iexplore.exe | 184.24.77.68:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
2540 | iexplore.exe | 104.126.37.139:443 | www.bing.com | Akamai International B.V. | DE | unknown |
2540 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.win-rar.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |