| File name: | eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe |
| Full analysis: | https://app.any.run/tasks/89d8aa2d-430c-4c3b-80d8-df17b69a5fc3 |
| Verdict: | Malicious activity |
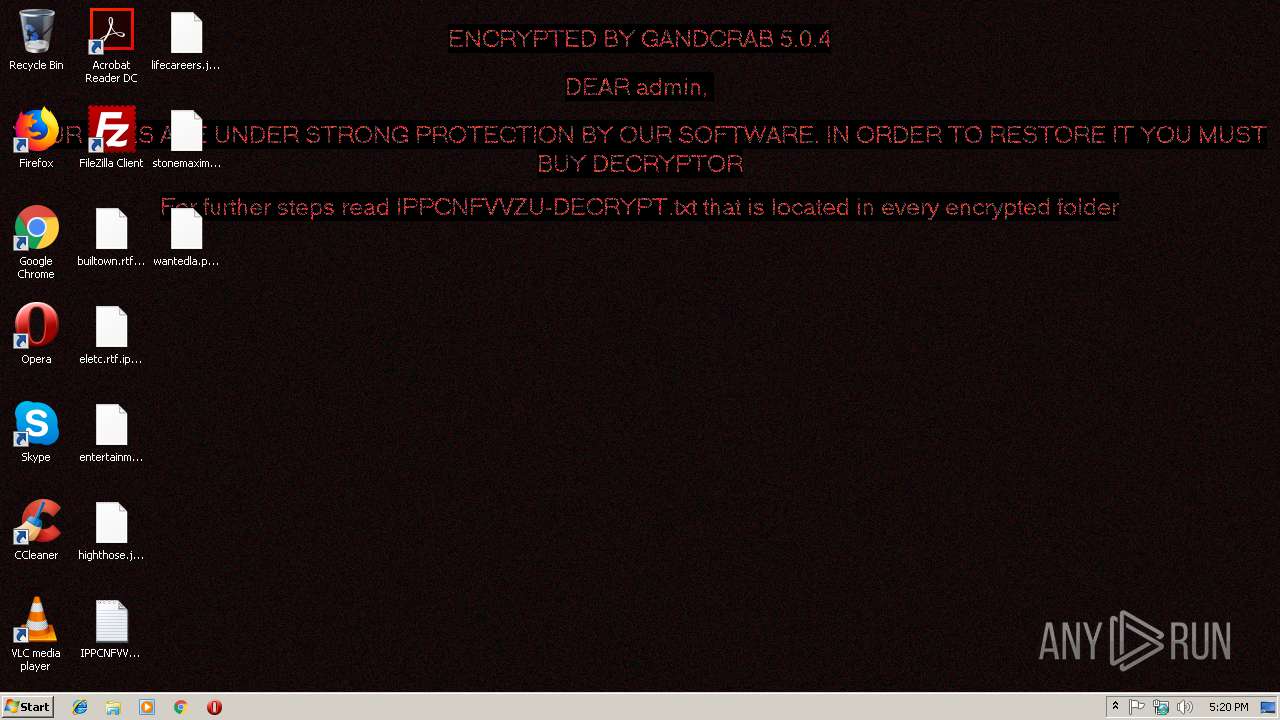
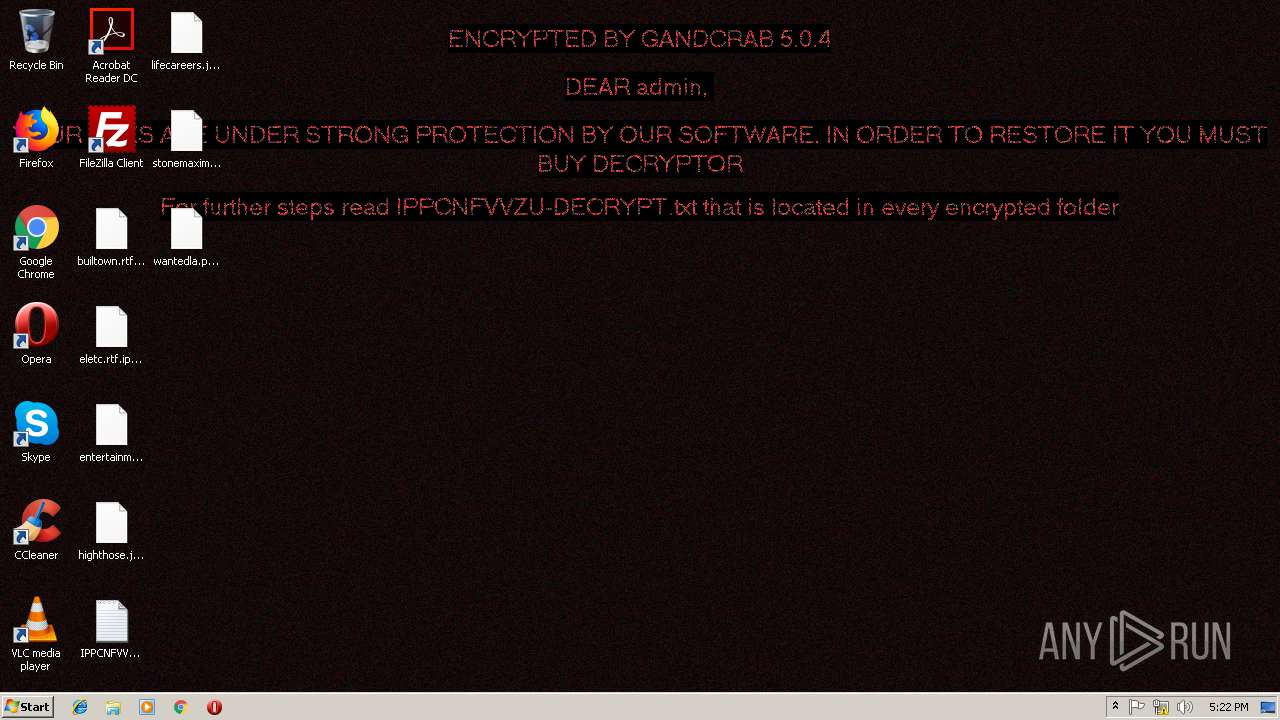
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | January 10, 2019, 17:19:15 |
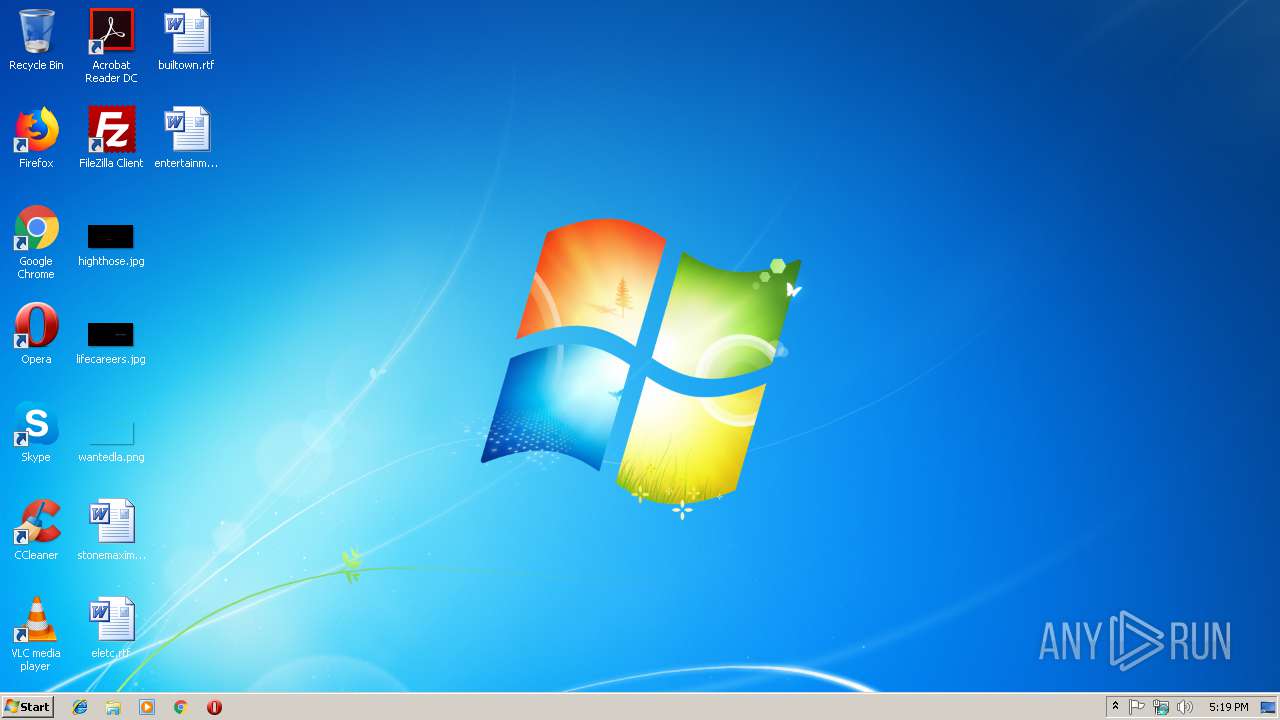
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3ABB1F4A8F2FDEB302985911BFEFD6BF |
| SHA1: | EADC3C11FD66AFD716E8E4F20BE2B9F6048DDC0B |
| SHA256: | 5E901677DAD76C0DC21DA659115B4D08E1E27C279C1CD038518AE1518646C306 |
| SSDEEP: | 192:piKixqK606vbxjowPrfpfh9A/dWhgUP1oynaUTG8tu8W1:pimAar2/dWhg610UTG8k8 |
MALICIOUS
Application was dropped or rewritten from another process
- winsvcs.exe (PID: 2968)
- 4223939108.exe (PID: 364)
- 2281337220.exe (PID: 3760)
- wincfg32svc.exe (PID: 3744)
- 3002915575.exe (PID: 1140)
- 2288140680.exe (PID: 2144)
- 4230842568.exe (PID: 3704)
- 3967628476.exe (PID: 2776)
- 3072135814.exe (PID: 912)
- 2504038984.exe (PID: 2372)
- 2095425148.exe (PID: 3344)
- 1437331526.exe (PID: 3460)
- 3998820812.exe (PID: 1964)
Changes the autorun value in the registry
- 4223939108.exe (PID: 364)
- 2281337220.exe (PID: 3760)
- eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe (PID: 2976)
Downloads executable files from the Internet
- winsvcs.exe (PID: 3952)
GandCrab keys found
- 3002915575.exe (PID: 1140)
Actions looks like stealing of personal data
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Disables Windows Defender Real-time monitoring
- winsvcs.exe (PID: 2968)
Disables Windows System Restore
- winsvcs.exe (PID: 2968)
Changes Security Center notification settings
- winsvcs.exe (PID: 2968)
Writes file to Word startup folder
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Downloads executable files from IP
- winsvcs.exe (PID: 3952)
Dropped file may contain instructions of ransomware
- 3002915575.exe (PID: 1140)
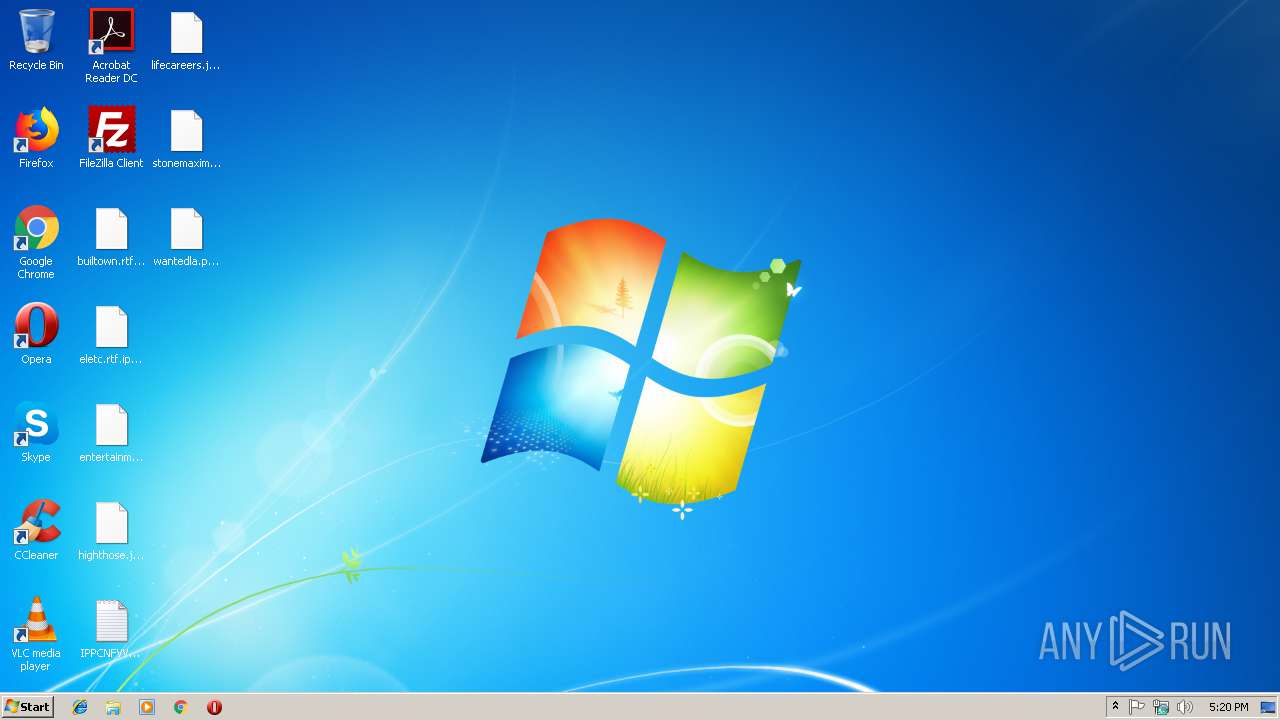
Renames files like Ransomware
- 3002915575.exe (PID: 1140)
Deletes shadow copies
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Changes settings of System certificates
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Connects to CnC server
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
GANDCRAB was detected
- 3072135814.exe (PID: 912)
SUSPICIOUS
Creates files in the user directory
- winsvcs.exe (PID: 3952)
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Executable content was dropped or overwritten
- winsvcs.exe (PID: 3952)
- 2281337220.exe (PID: 3760)
- 4223939108.exe (PID: 364)
- eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe (PID: 2976)
- winsvcs.exe (PID: 2968)
Starts itself from another location
- eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe (PID: 2976)
- 2281337220.exe (PID: 3760)
- 4223939108.exe (PID: 364)
- winsvcs.exe (PID: 2968)
Creates files in the program directory
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Connects to SMTP port
- wincfg32svc.exe (PID: 3744)
Reads the cookies of Mozilla Firefox
- 3002915575.exe (PID: 1140)
Creates files like Ransomware instruction
- 3002915575.exe (PID: 1140)
Reads Internet Cache Settings
- 3002915575.exe (PID: 1140)
Starts CMD.EXE for commands execution
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
Adds / modifies Windows certificates
- 3002915575.exe (PID: 1140)
- 3072135814.exe (PID: 912)
INFO
Dropped object may contain TOR URL's
- 3002915575.exe (PID: 1140)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:10 17:08:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 7168 |
| InitializedDataSize: | 7168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1030 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 10-Jan-2019 16:08:41 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 10-Jan-2019 16:08:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00001B2F | 0x00001C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.56902 |
.rdata | 0x00003000 | 0x00001244 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.07414 |
.data | 0x00005000 | 0x00000050 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00006000 | 0x000001B4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.09798 |
.reloc | 0x00007000 | 0x0000025C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.83187 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
Imports
ADVAPI32.dll |
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
SHLWAPI.dll |
WININET.dll |
urlmon.dll |
Total processes
58
Monitored processes
21
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 364 | C:\Users\admin\AppData\Local\Temp\4223939108.exe | C:\Users\admin\AppData\Local\Temp\4223939108.exe | winsvcs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 912 | C:\Users\admin\AppData\Local\Temp\3072135814.exe | C:\Users\admin\AppData\Local\Temp\3072135814.exe | winsvcs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1140 | C:\Users\admin\AppData\Local\Temp\3002915575.exe | C:\Users\admin\AppData\Local\Temp\3002915575.exe | winsvcs.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1620 | "C:\Windows\System32\cmd.exe" /c timeout -c 5 & del "C:\Users\admin\AppData\Local\Temp\3072135814.exe" /f /q | C:\Windows\System32\cmd.exe | — | 3072135814.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1708 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | 3072135814.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | timeout -c 5 | C:\Windows\system32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: timeout - pauses command processing Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1964 | C:\Users\admin\AppData\Local\Temp\3998820812.exe | C:\Users\admin\AppData\Local\Temp\3998820812.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2144 | C:\Users\admin\AppData\Local\Temp\2288140680.exe | C:\Users\admin\AppData\Local\Temp\2288140680.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2192 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | — | 3002915575.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2372 | C:\Users\admin\AppData\Local\Temp\2504038984.exe | C:\Users\admin\AppData\Local\Temp\2504038984.exe | — | winsvcs.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
485
Read events
347
Write events
125
Delete events
13
Modification events
| (PID) Process: | (2976) eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Microsoft Windows Services |
Value: C:\Users\admin\495030305060\winsvcs.exe | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3952) winsvcs.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\winsvcs_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
17
Suspicious files
270
Text files
258
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1140 | 3002915575.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | — | |
MD5:— | SHA256:— | |||
| 1140 | 3002915575.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\IPPCNFVVZU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3952 | winsvcs.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\2[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2976 | eadc3c11fd66afd716e8e4f20be2b9f6048ddc0b.exe | C:\Users\admin\495030305060\winsvcs.exe | executable | |
MD5:— | SHA256:— | |||
| 364 | 4223939108.exe | C:\Users\admin\4950606094303050\wincfg32svc.exe | executable | |
MD5:— | SHA256:— | |||
| 1140 | 3002915575.exe | C:\Users\admin\657607470096780\IPPCNFVVZU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 3952 | winsvcs.exe | C:\Users\admin\AppData\Local\Temp\3002915575.exe | executable | |
MD5:— | SHA256:— | |||
| 1140 | 3002915575.exe | C:\Users\admin\AppData\Roaming\IPPCNFVVZU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
| 1140 | 3002915575.exe | C:\Users\admin\AppData\Roaming\Adobe\Acrobat\DC\JSCache\GlobData | — | |
MD5:— | SHA256:— | |||
| 1140 | 3002915575.exe | C:\Users\admin\AppData\Local\VirtualStore\IPPCNFVVZU-DECRYPT.txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
312
TCP/UDP connections
509
DNS requests
205
Threats
263
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3952 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/1.exe | RU | — | — | malicious |
3952 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | — | — | malicious |
3952 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://92.63.197.48/m/1.exe | RU | — | — | malicious |
2968 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://92.63.197.48/2.exe | RU | — | — | malicious |
2968 | winsvcs.exe | GET | 304 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | — | — | malicious |
2968 | winsvcs.exe | GET | — | 92.63.197.48:80 | http://92.63.197.48/1.exe | RU | — | — | malicious |
3952 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/1.exe | RU | executable | 261 Kb | malicious |
3952 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://92.63.197.48/m/1.exe | RU | executable | 247 Kb | malicious |
3952 | winsvcs.exe | GET | 200 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/2.exe | RU | executable | 258 Kb | malicious |
3952 | winsvcs.exe | GET | 404 | 92.63.197.48:80 | http://slpsrgpsrhojifdij.ru/3.exe | RU | html | 178 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3952 | winsvcs.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
3744 | wincfg32svc.exe | 98.137.159.25:25 | mta5.am0.yahoodns.net | Yahoo | US | unknown |
2968 | winsvcs.exe | 92.63.197.48:80 | slpsrgpsrhojifdij.ru | — | RU | malicious |
1140 | 3002915575.exe | 78.46.77.98:80 | www.2mmotorsport.biz | Hetzner Online GmbH | DE | suspicious |
1140 | 3002915575.exe | 138.201.162.99:80 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
1140 | 3002915575.exe | 138.201.162.99:443 | www.fliptray.biz | Hetzner Online GmbH | DE | malicious |
1140 | 3002915575.exe | 74.220.215.73:80 | www.bizziniinfissi.com | Unified Layer | US | malicious |
1140 | 3002915575.exe | 136.243.13.215:80 | www.holzbock.biz | Hetzner Online GmbH | DE | suspicious |
1140 | 3002915575.exe | 192.185.159.253:80 | www.pizcam.com | CyrusOne LLC | US | malicious |
1140 | 3002915575.exe | 192.185.159.253:443 | www.pizcam.com | CyrusOne LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
slpsrgpsrhojifdij.ru |
| malicious |
yahoo.com |
| whitelisted |
mta5.am0.yahoodns.net |
| unknown |
osheoufhusheoghuesd.ru |
| malicious |
www.2mmotorsport.biz |
| unknown |
ofheofosugusghuhush.ru |
| unknown |
www.haargenau.biz |
| unknown |
www.bizziniinfissi.com |
| malicious |
www.holzbock.biz |
| unknown |
www.fliptray.biz |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | A Network Trojan was detected | ET TROJAN Single char EXE direct download likely trojan (multiple families) |
3952 | winsvcs.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |