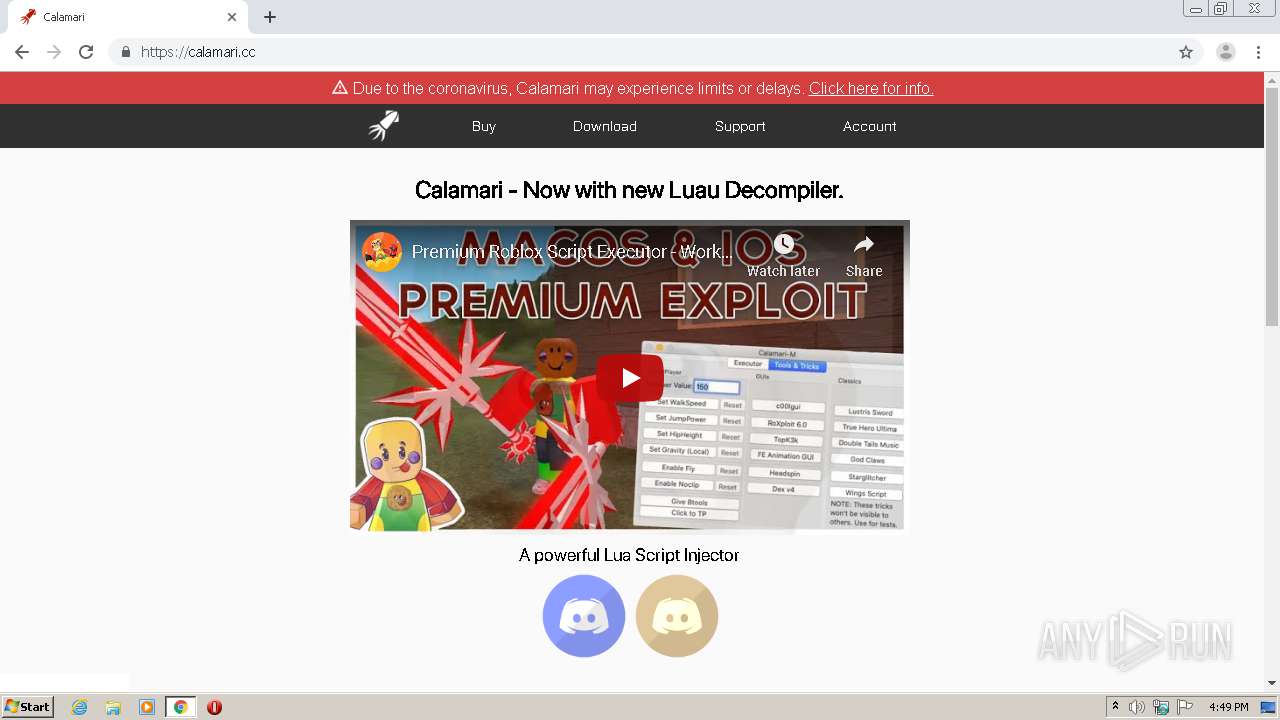
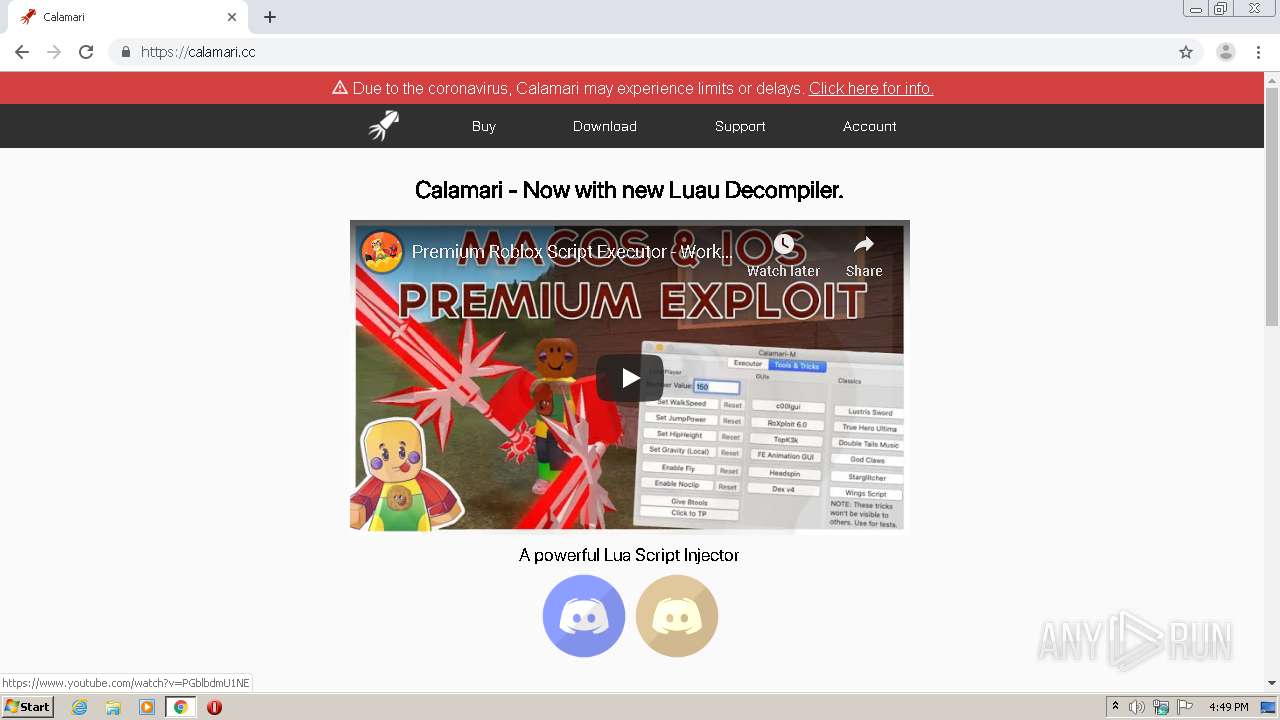
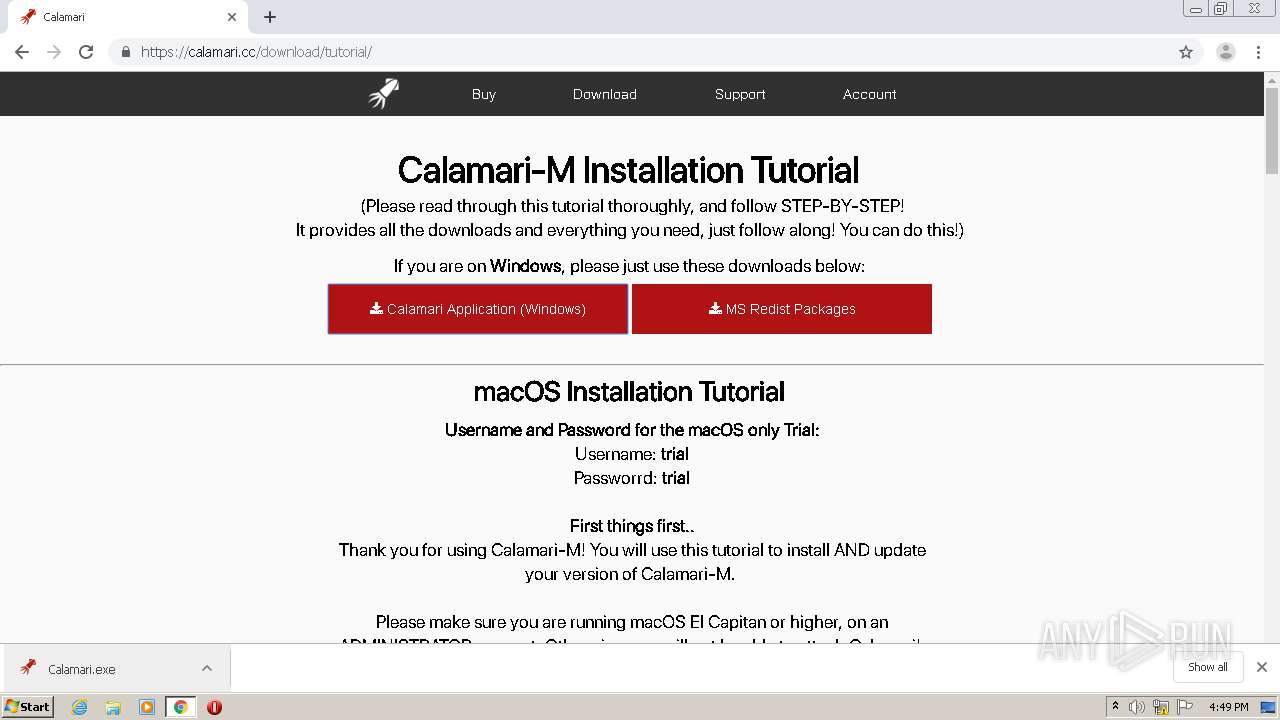
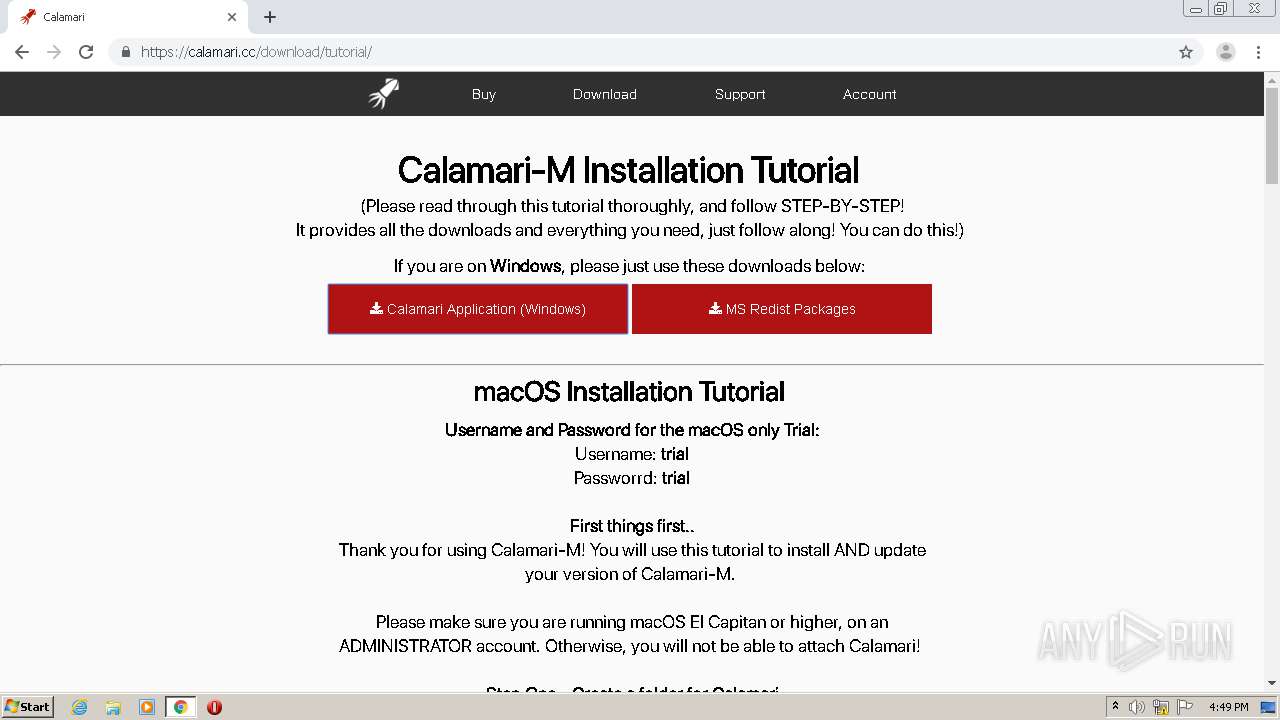
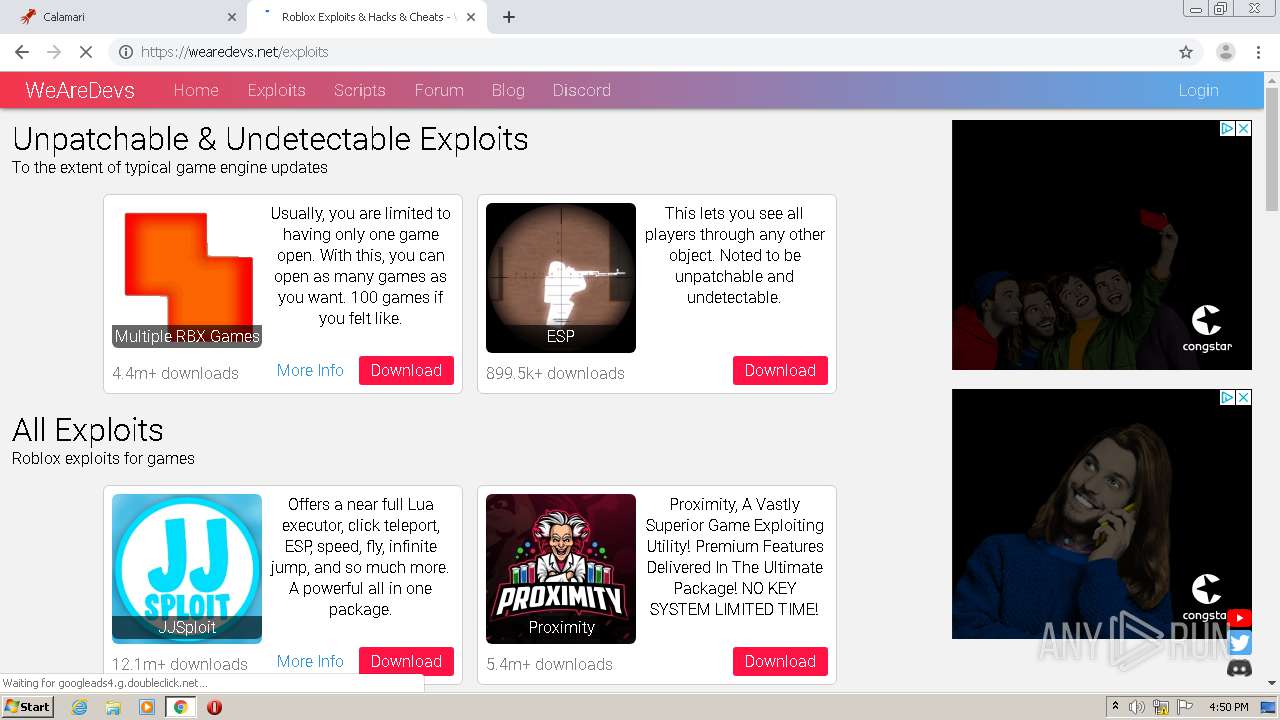
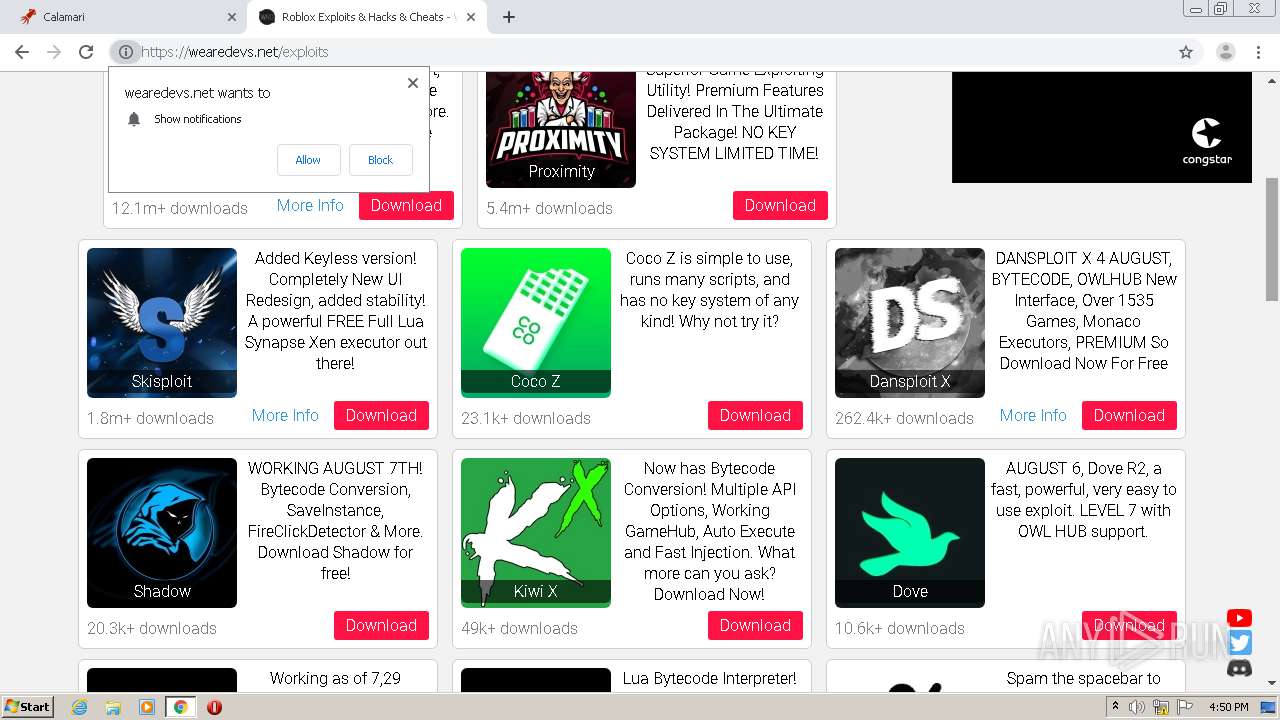
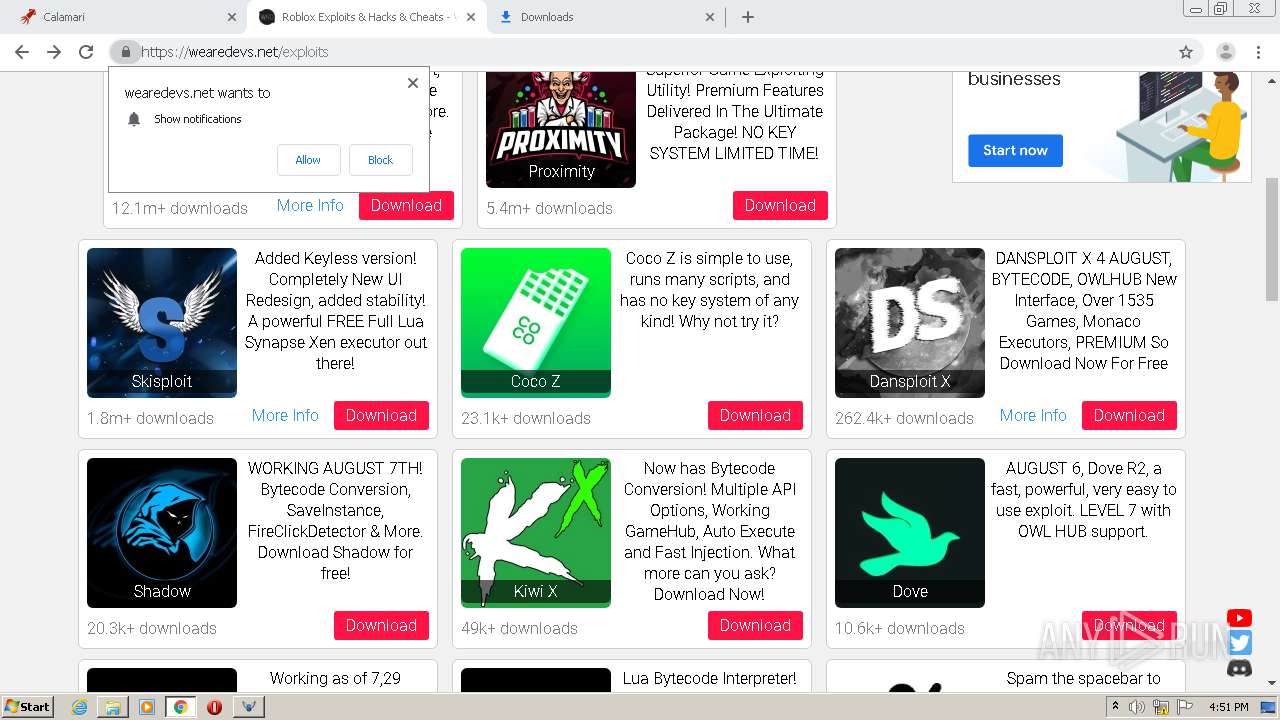
| URL: | https://calamari.cc/ |
| Full analysis: | https://app.any.run/tasks/f7eb96e1-99ae-4c37-8905-17ddacfeecce |
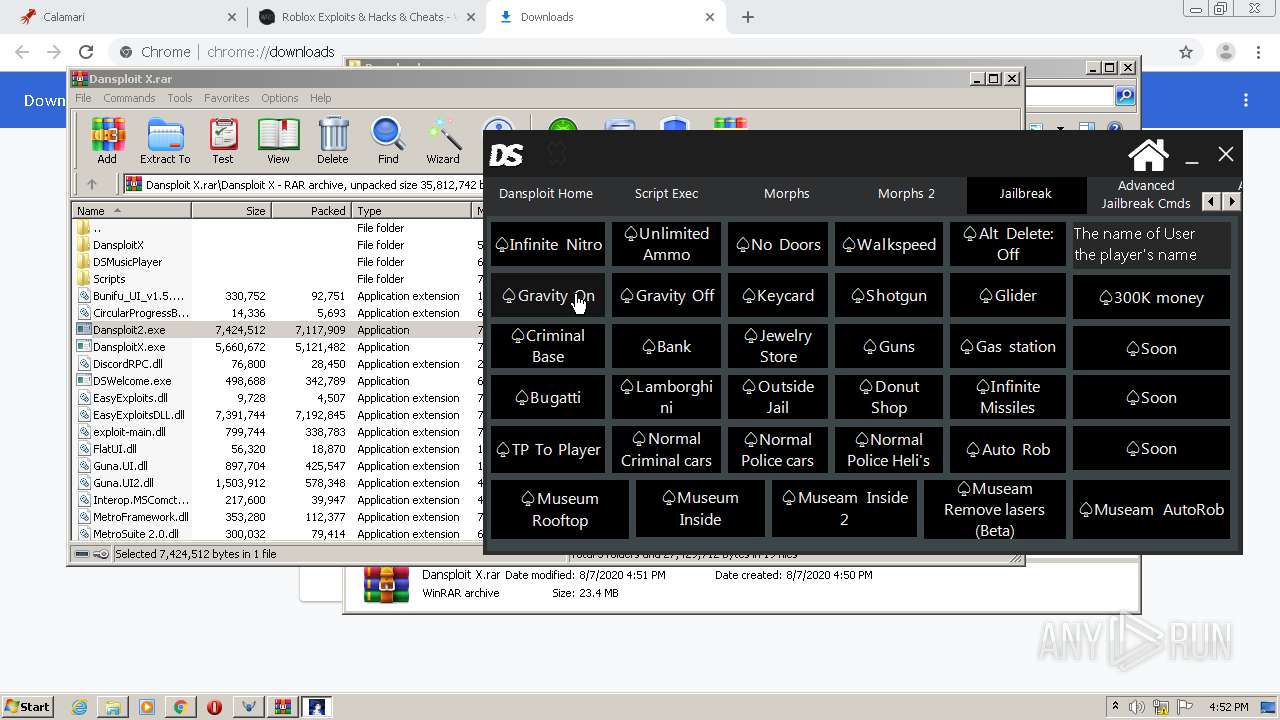
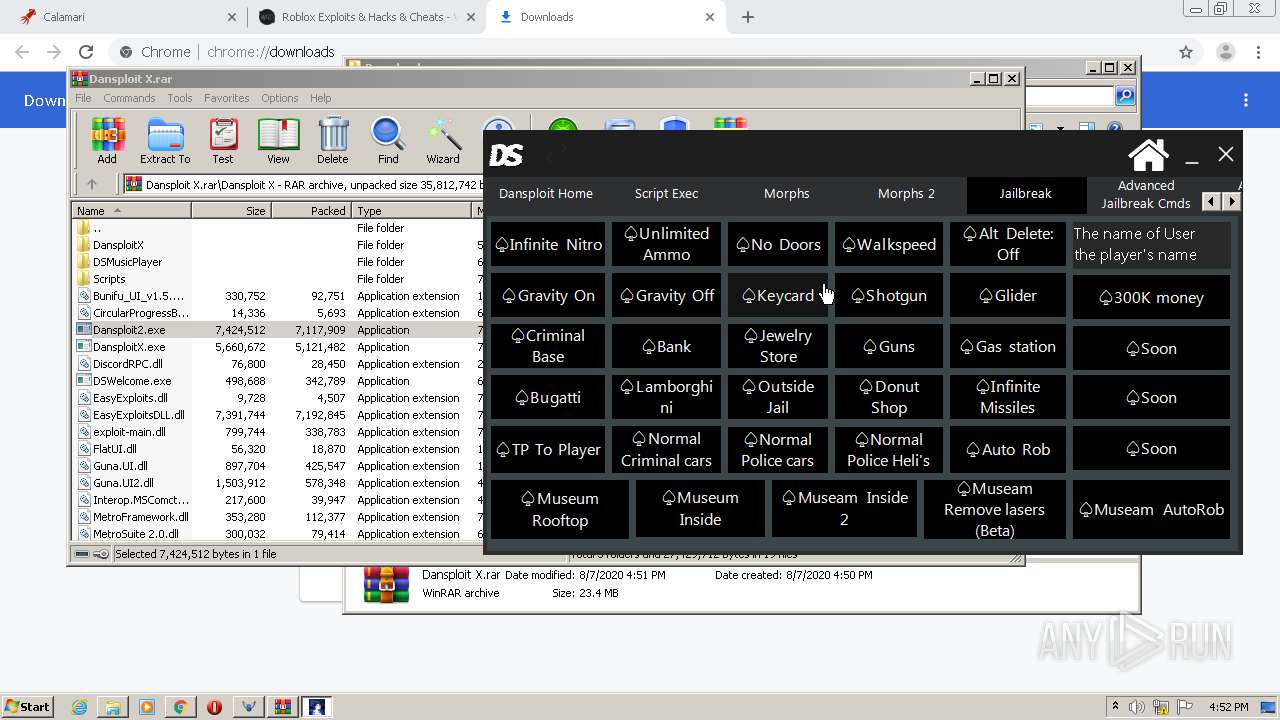
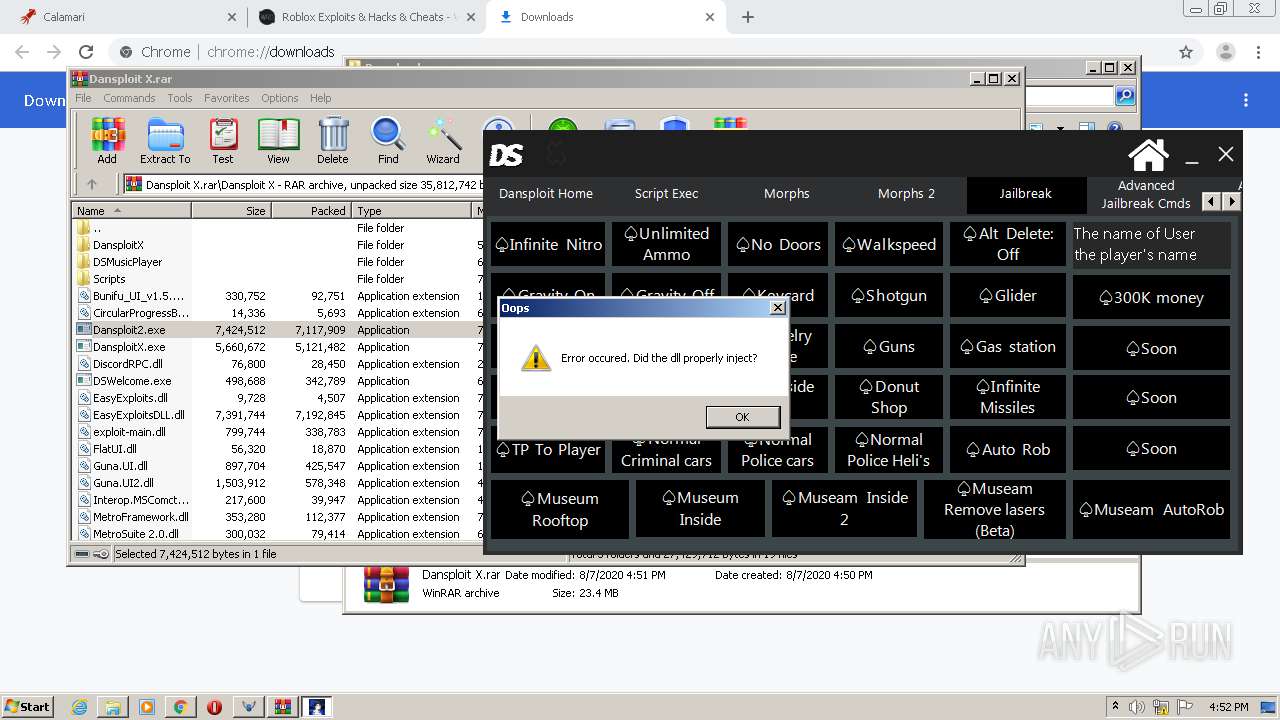
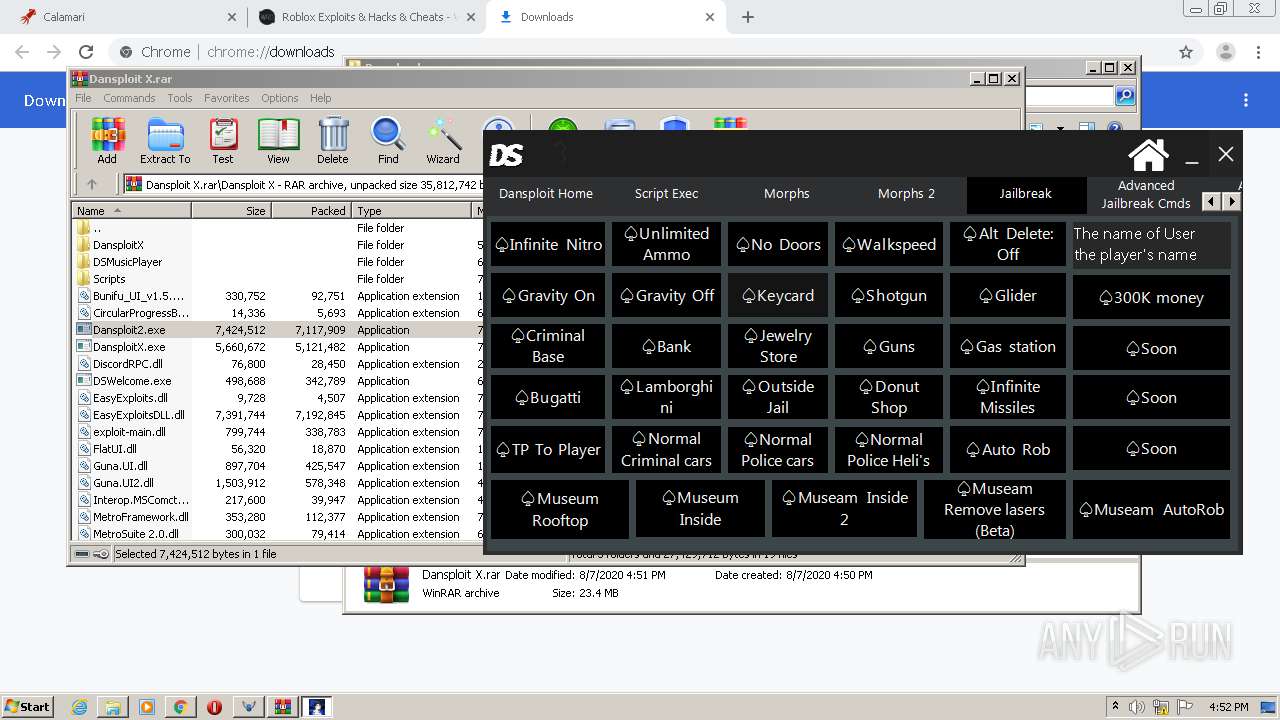
| Verdict: | Malicious activity |
| Analysis date: | August 07, 2020, 15:48:21 |
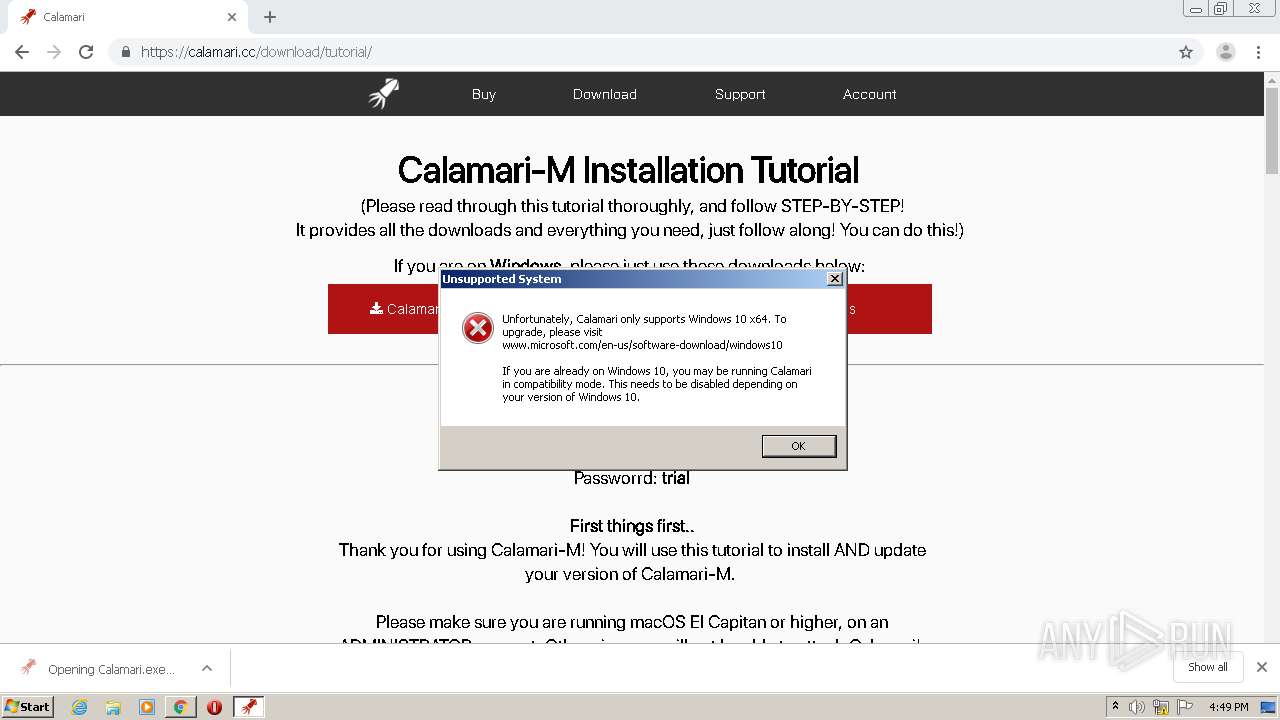
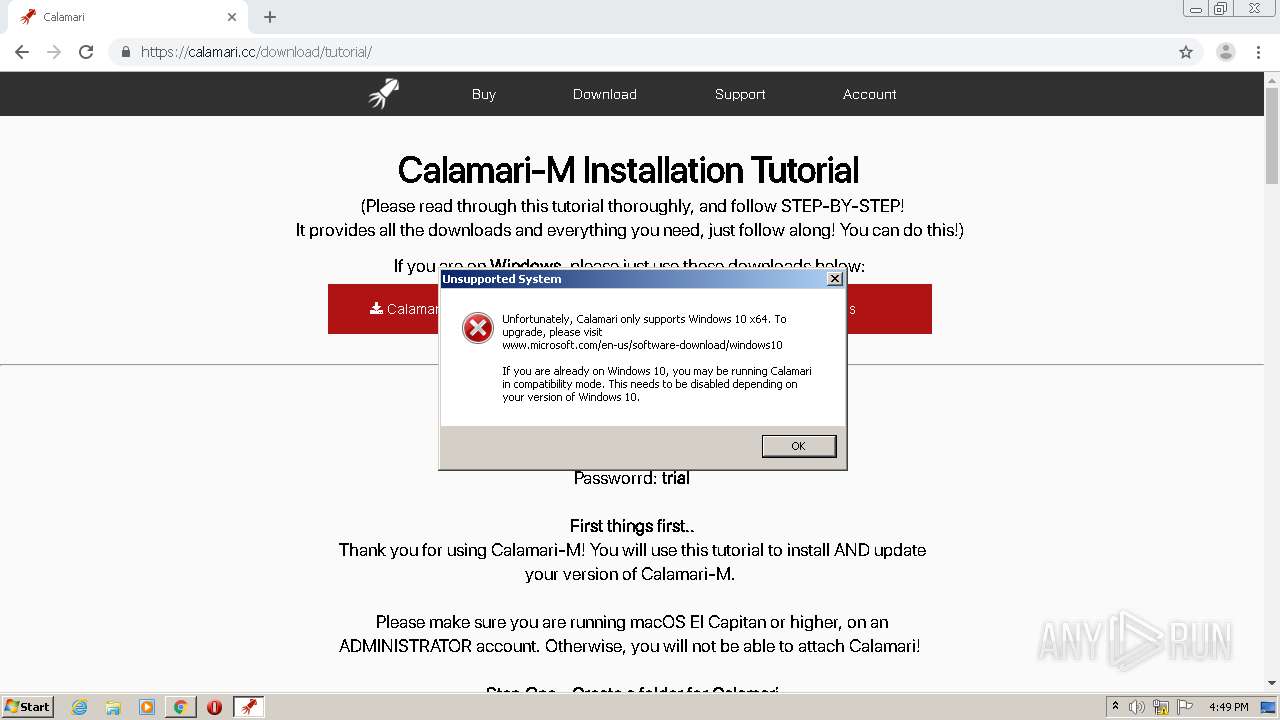
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | D5E63E0351CE04938C0A3F99D8BFD897 |
| SHA1: | C1343B76B64DA5FB9BD97F6E7210A434B51A912B |
| SHA256: | 5E8BDB970C4E29B57A9BB111C3744E7CC7A47B4CE48868B8F412F68DDFD9EE68 |
| SSDEEP: | 3:N8ZJhEXKGd:2CXKs |
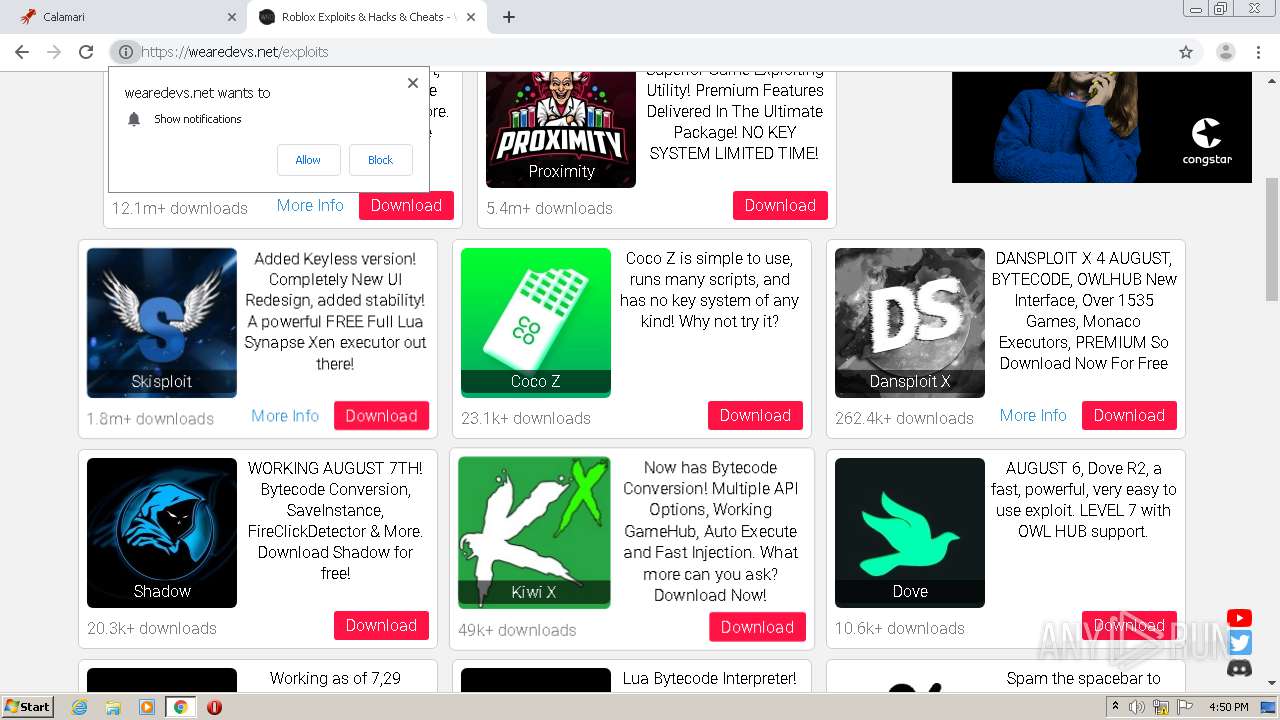
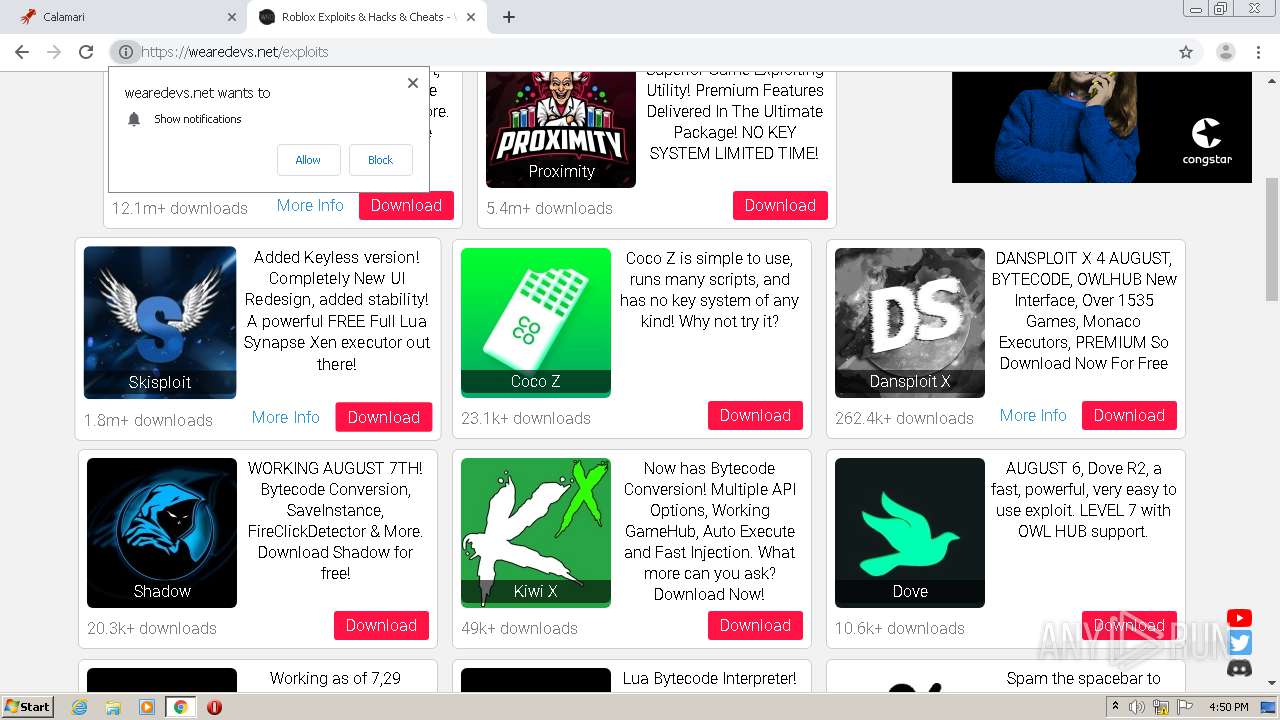
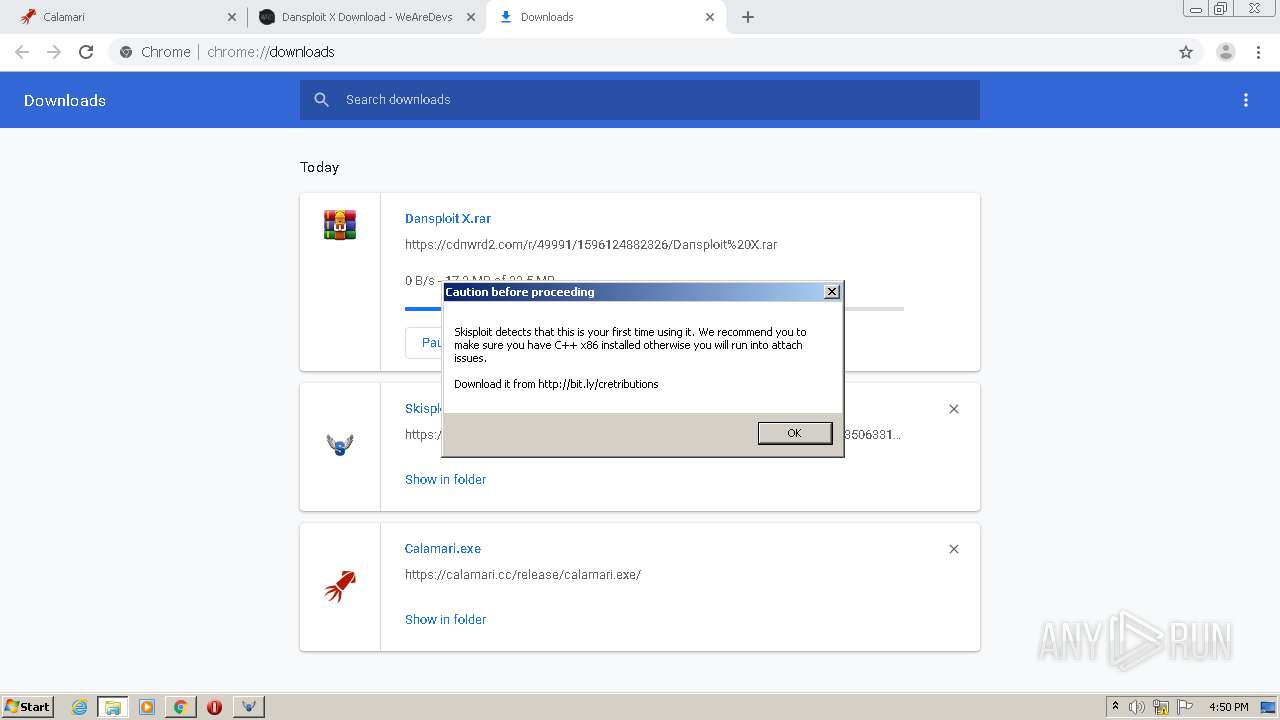
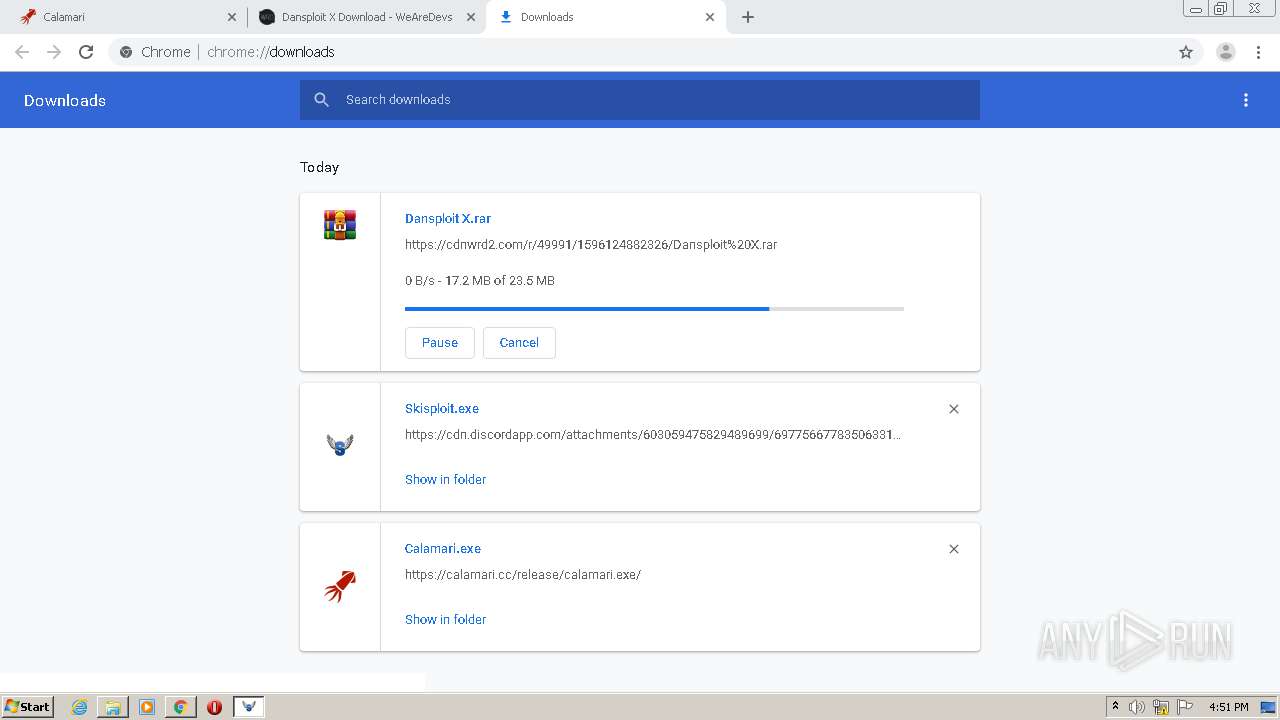
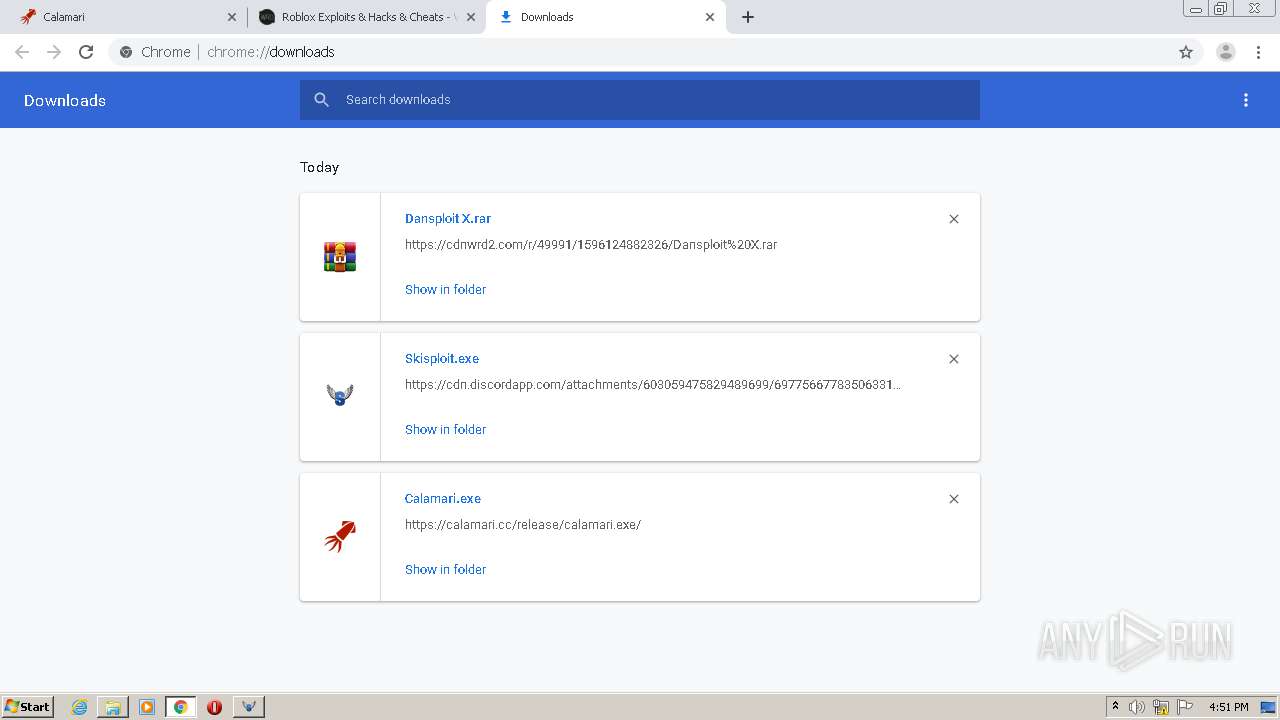
MALICIOUS
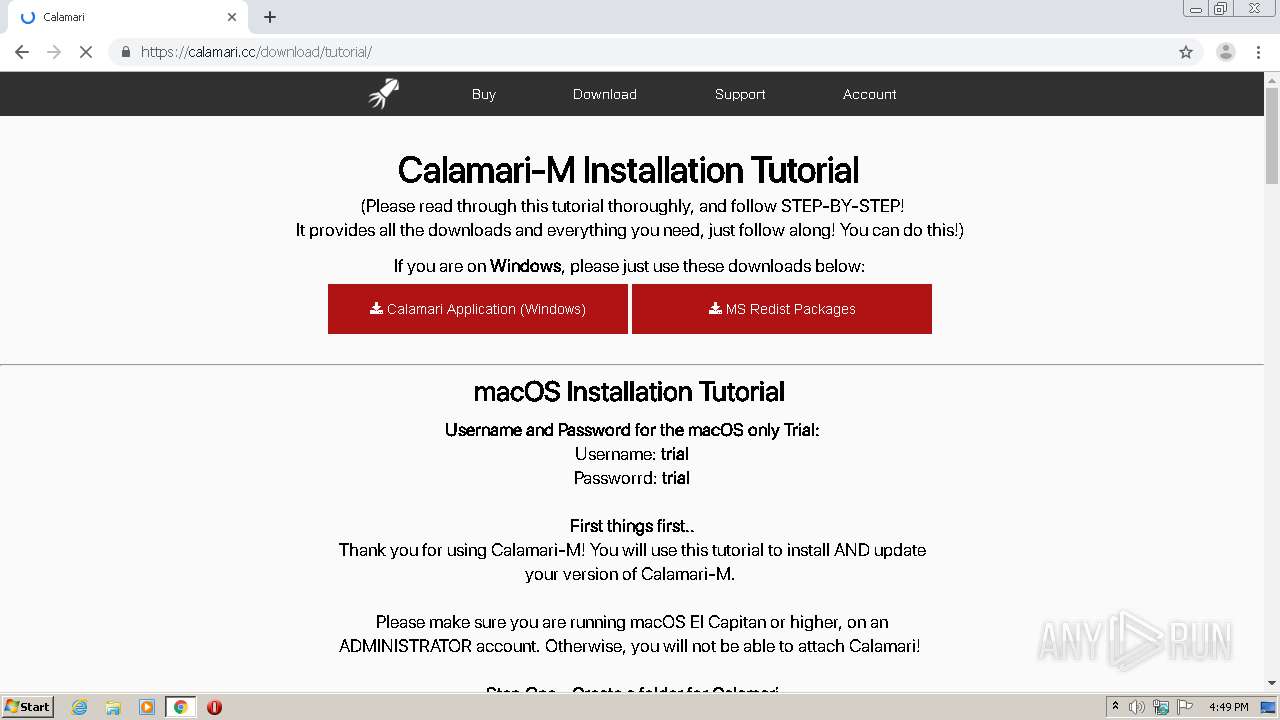
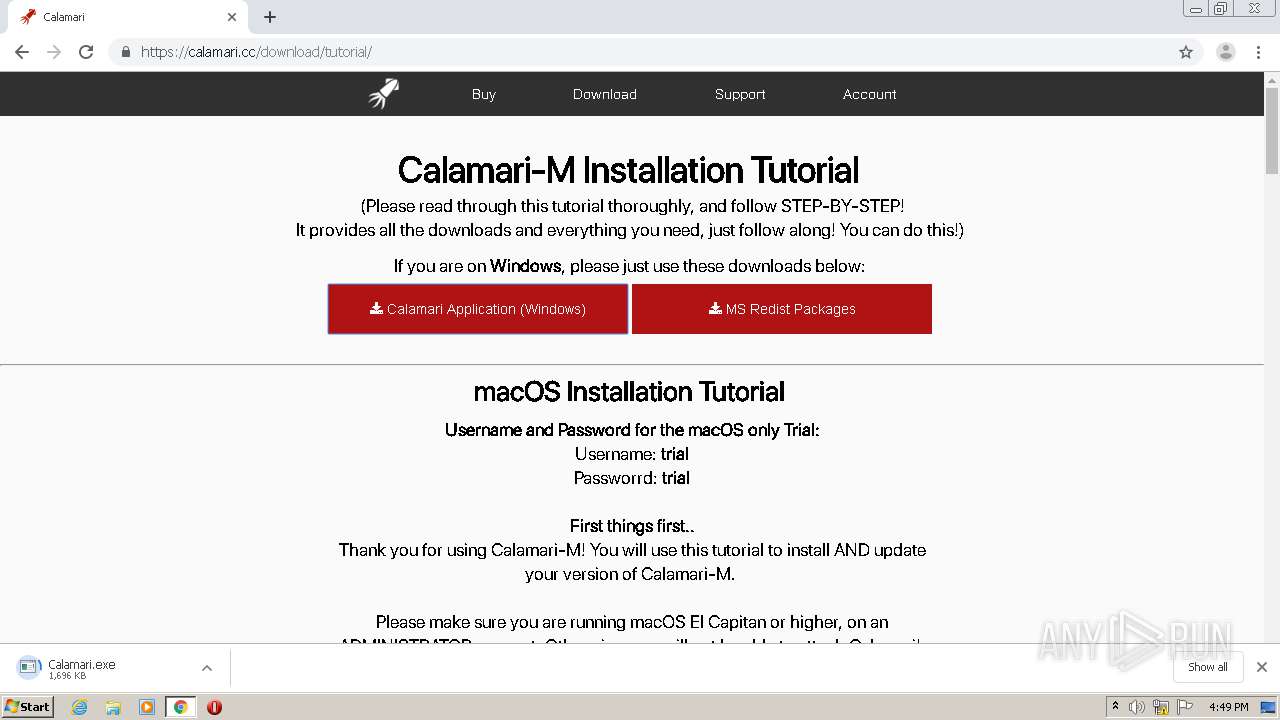
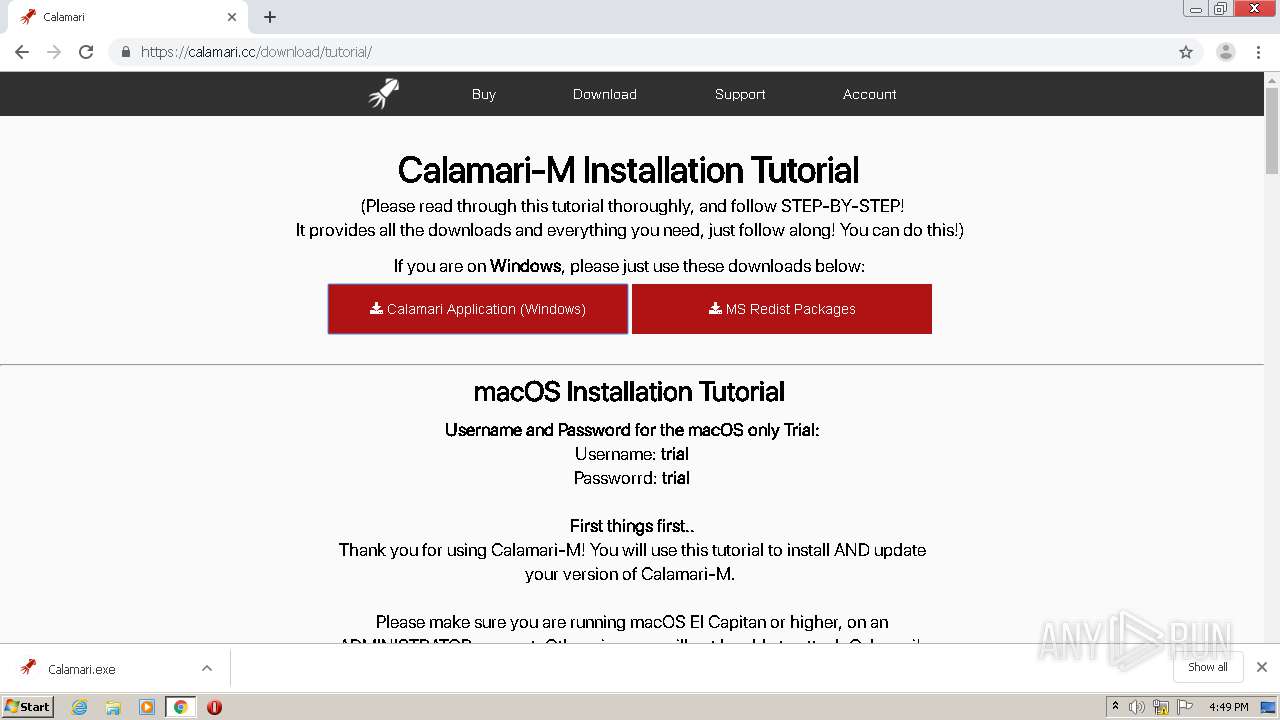
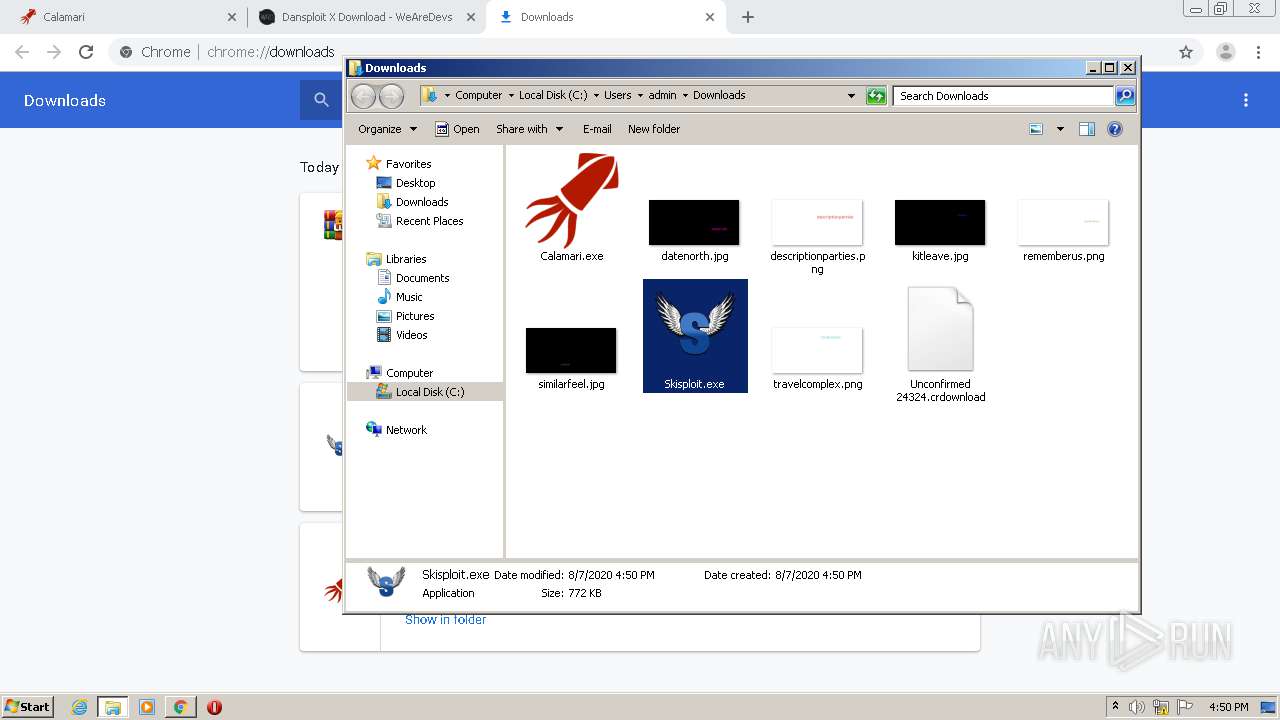
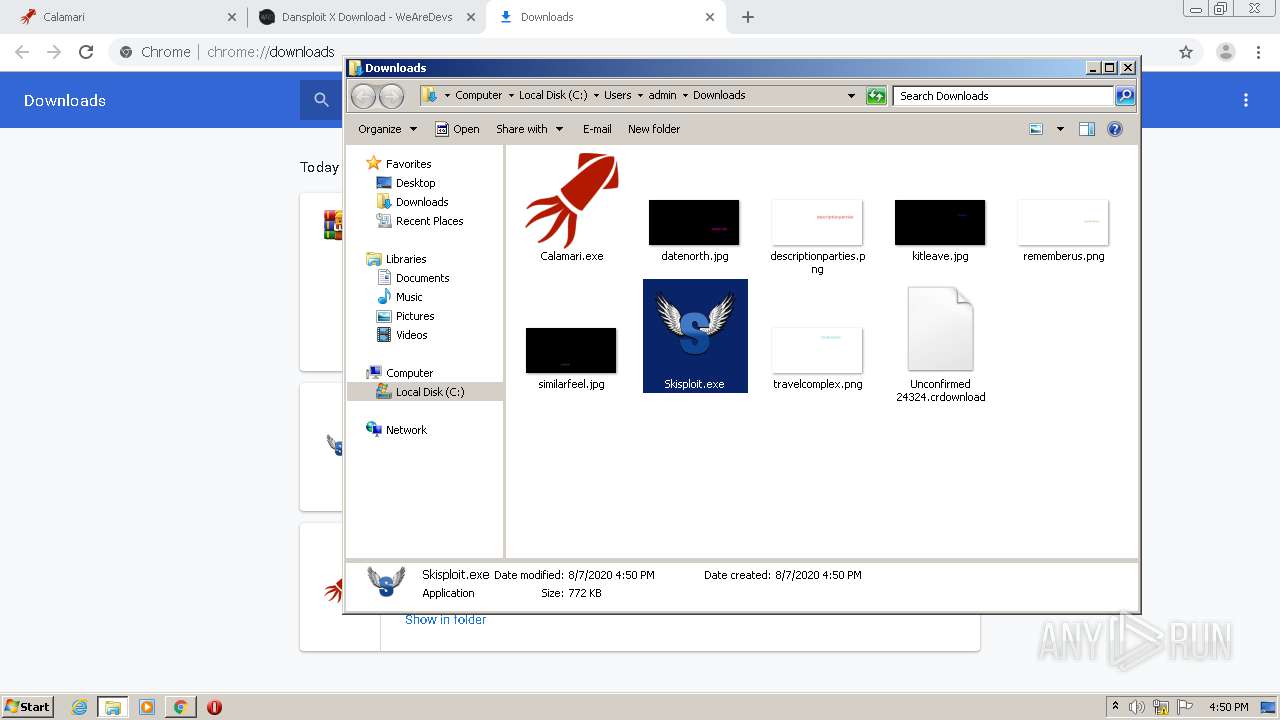
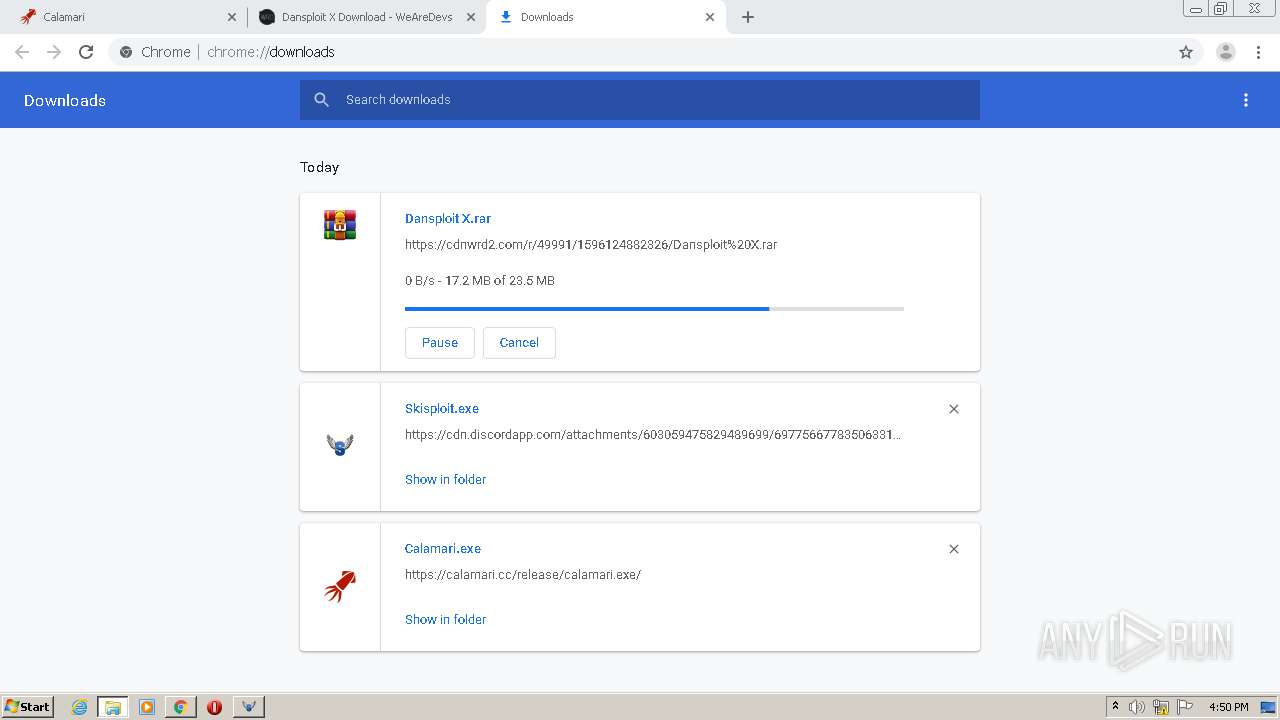
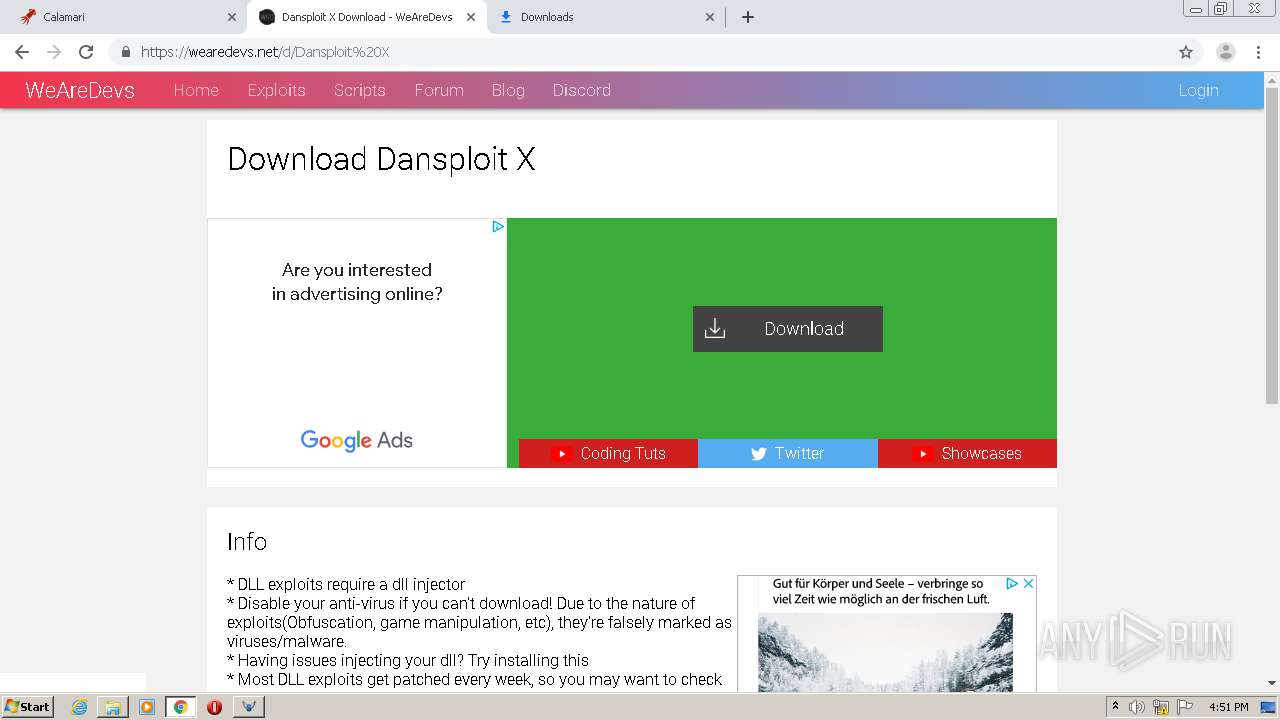
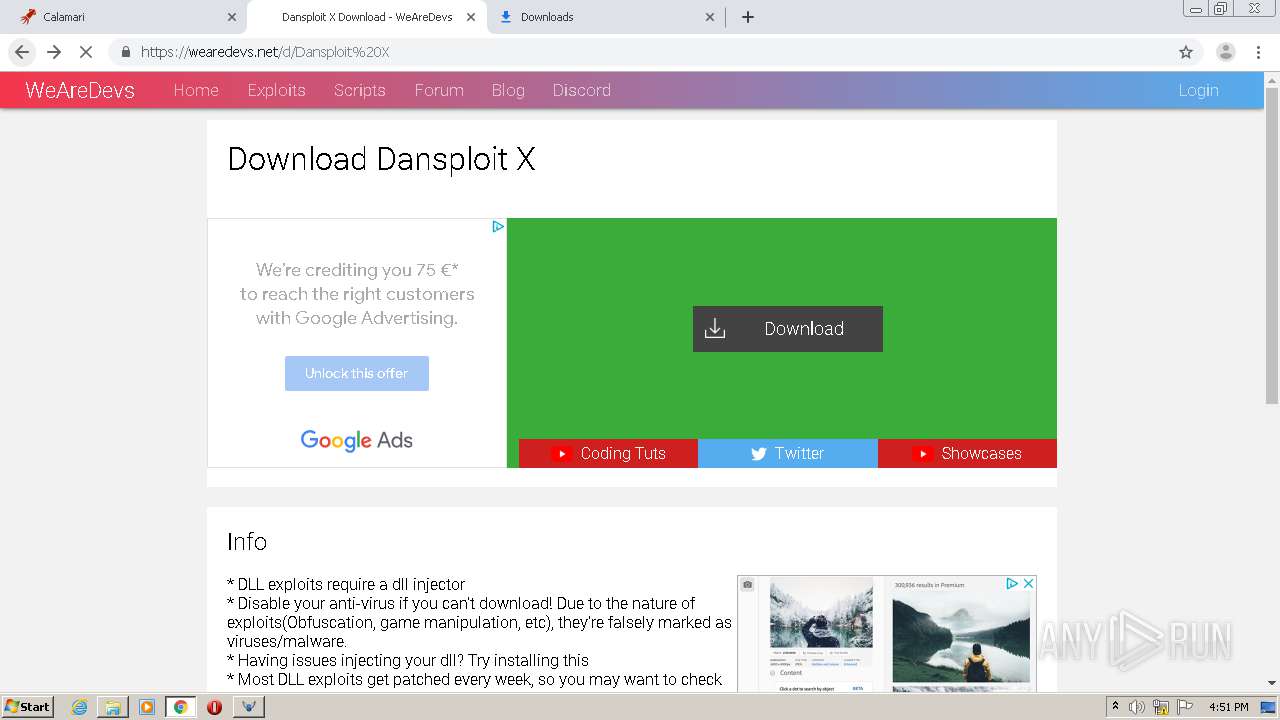
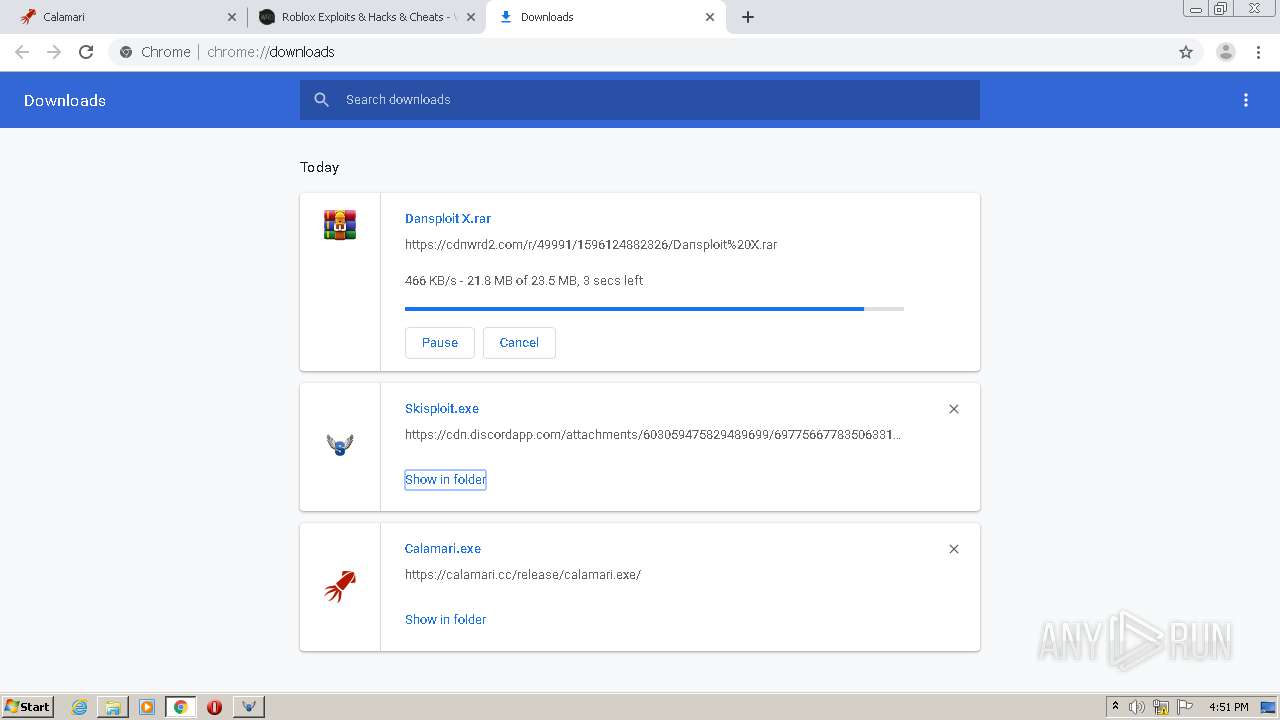
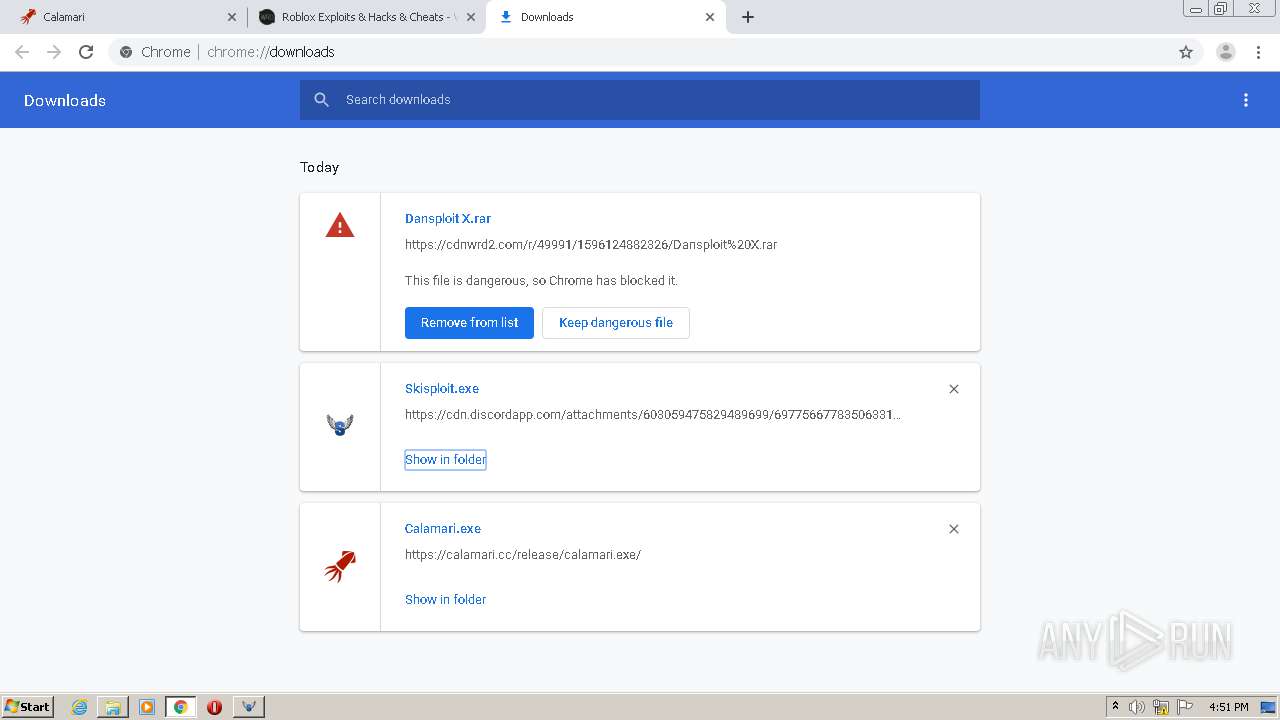
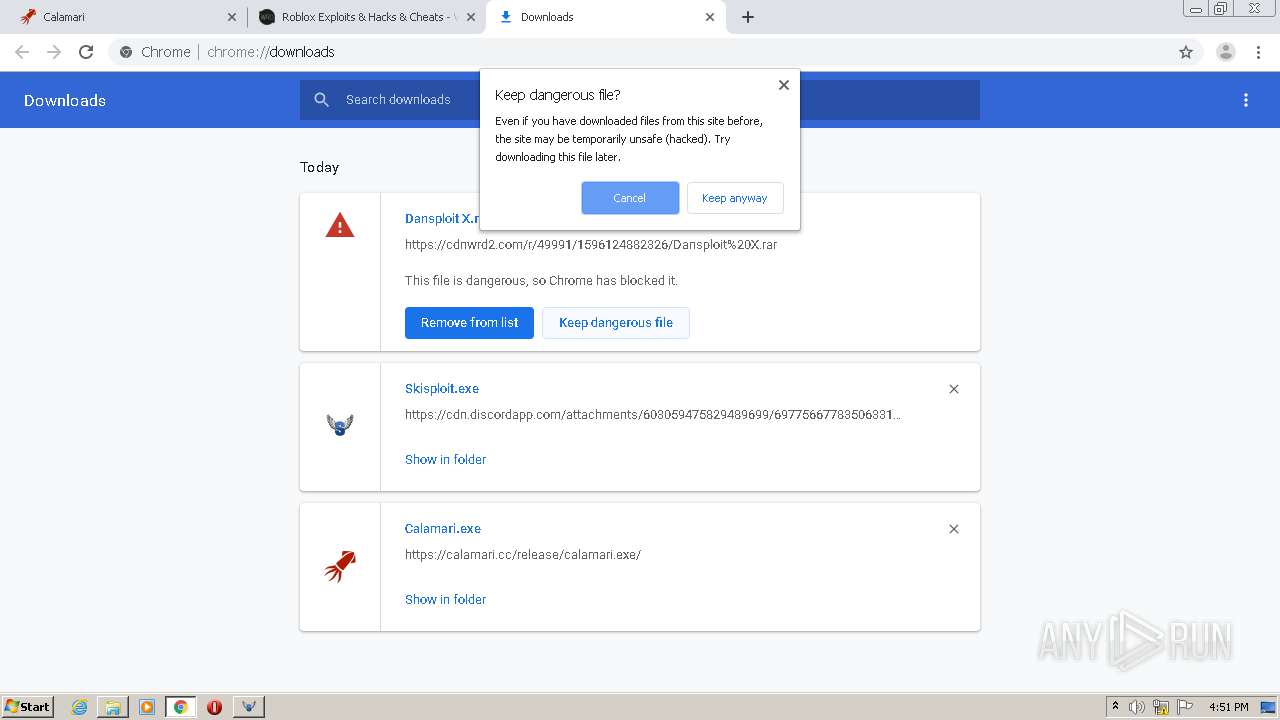
Application was dropped or rewritten from another process
- Skisploit.exe (PID: 1252)
- Calamari.exe (PID: 2108)
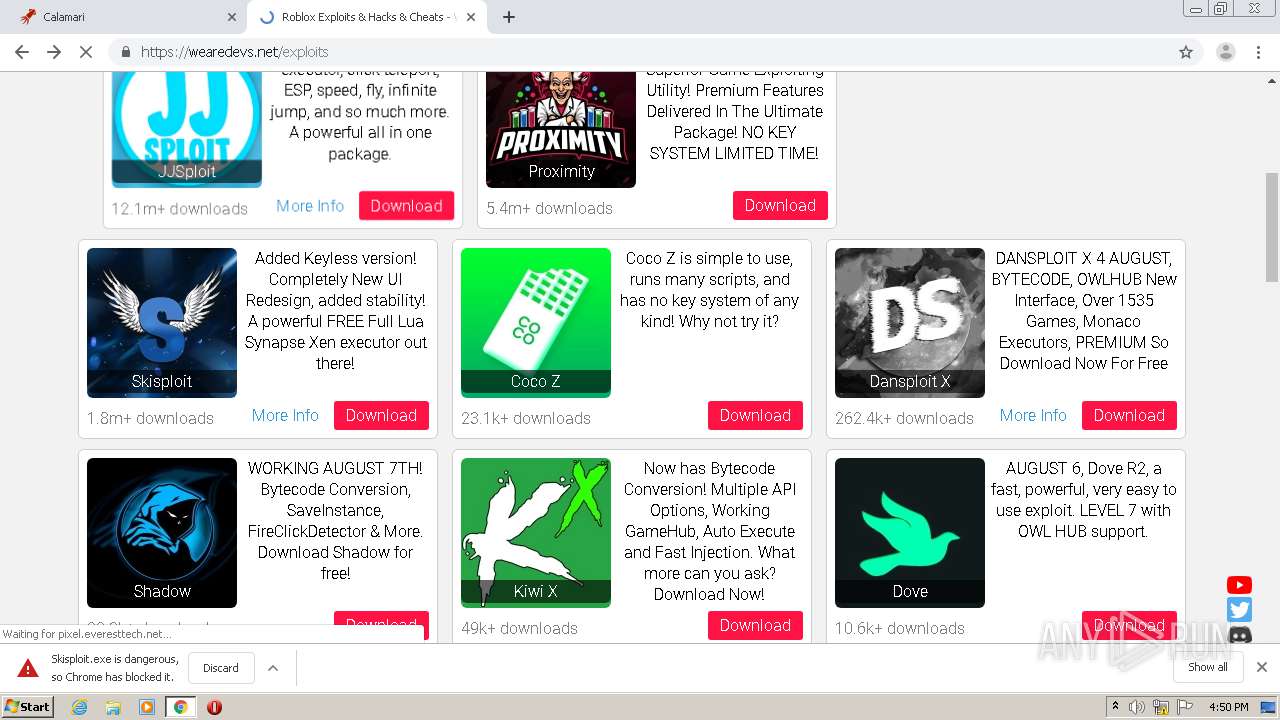
- Dansploit2.exe (PID: 576)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3464)
- Dansploit2.exe (PID: 576)
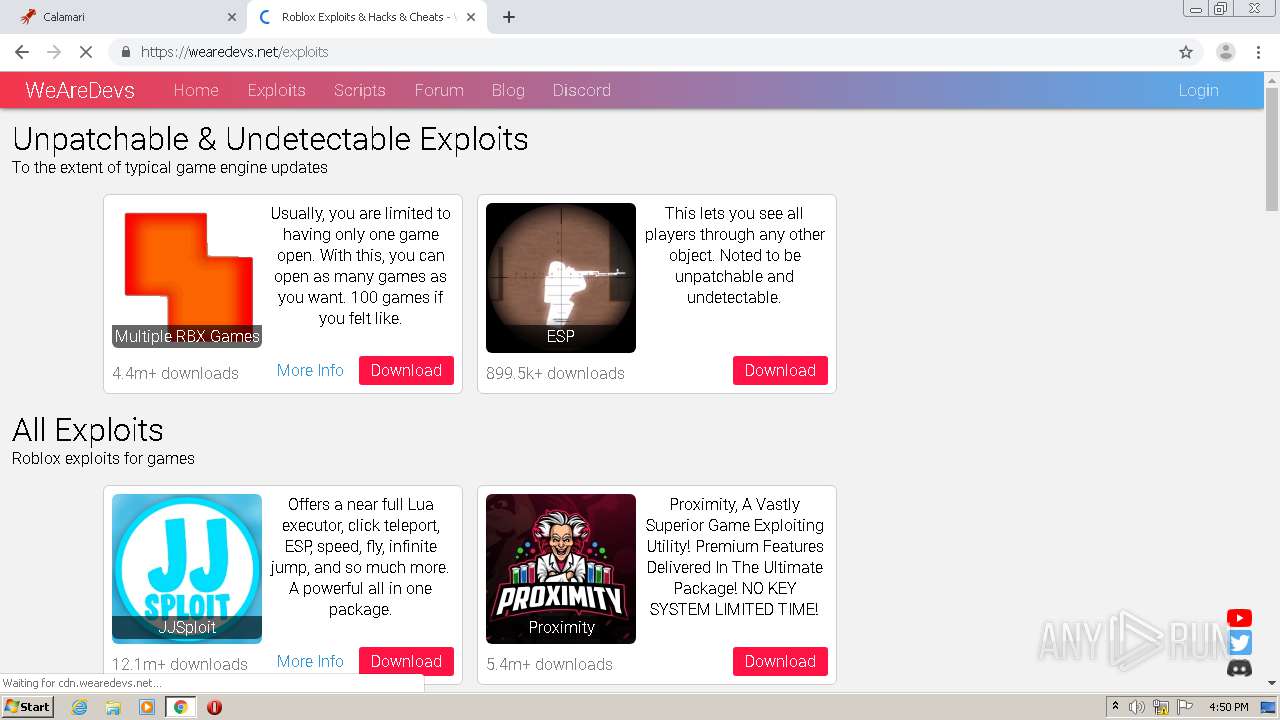
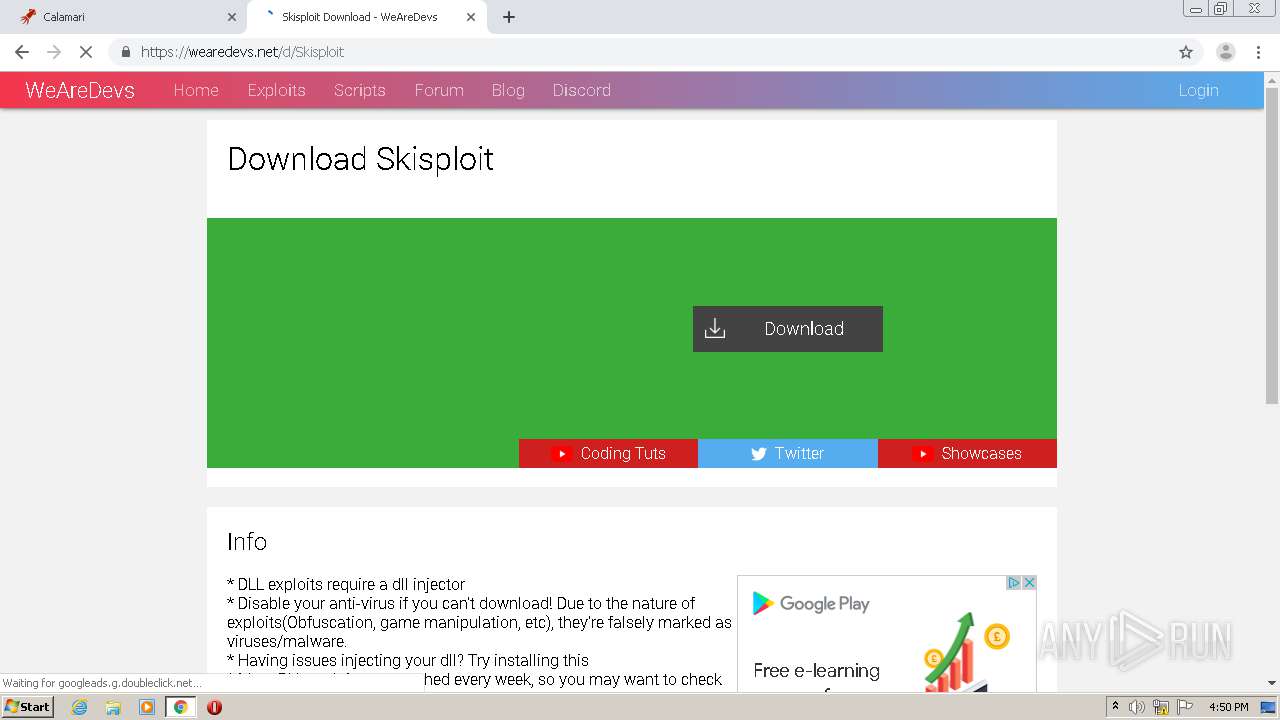
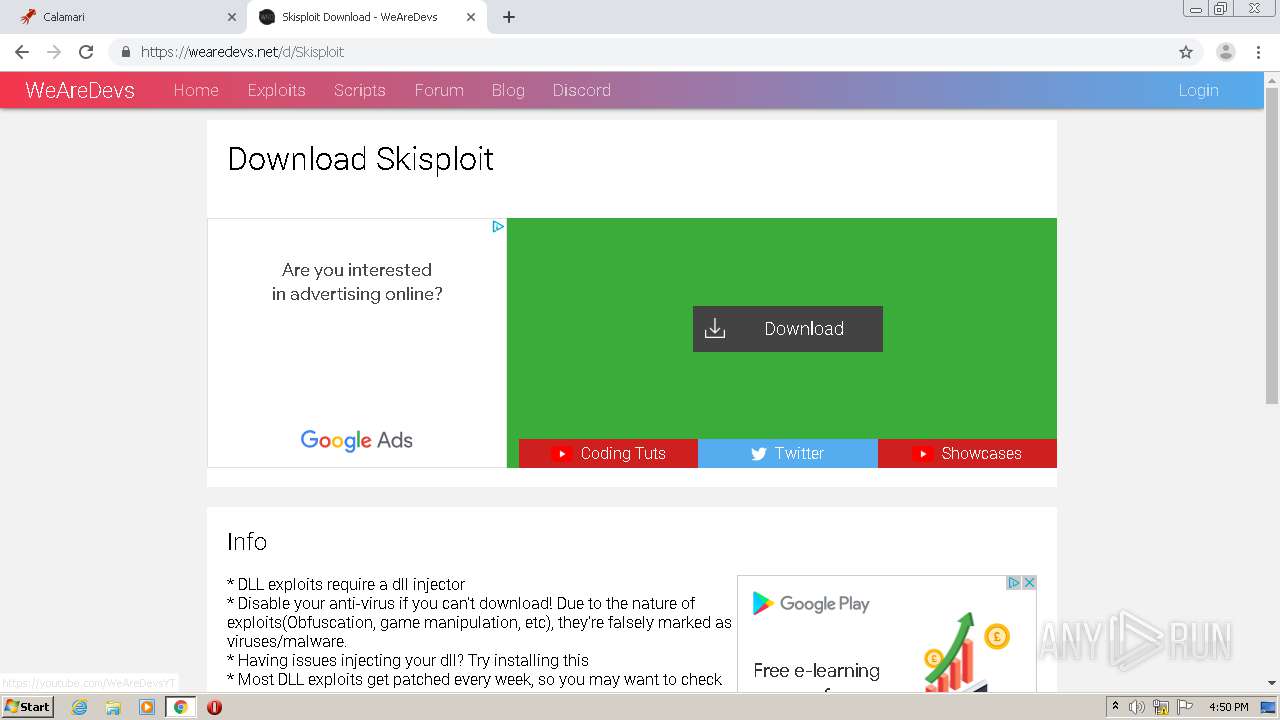
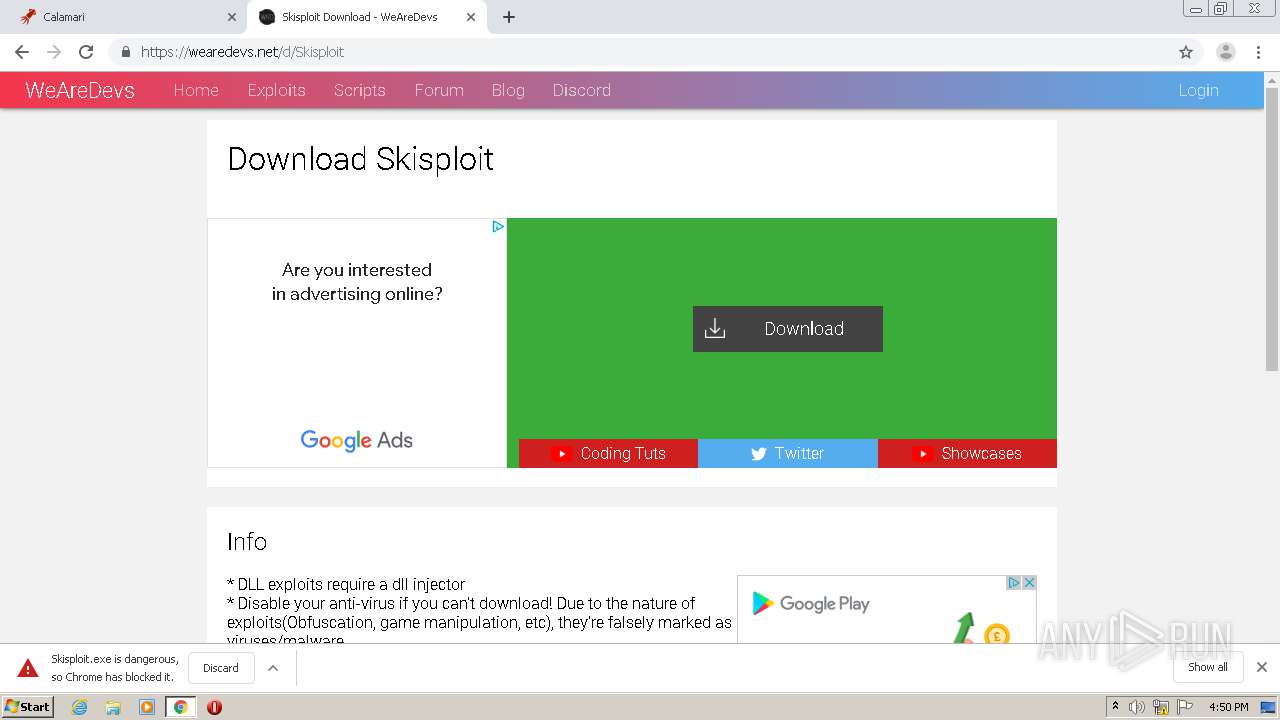
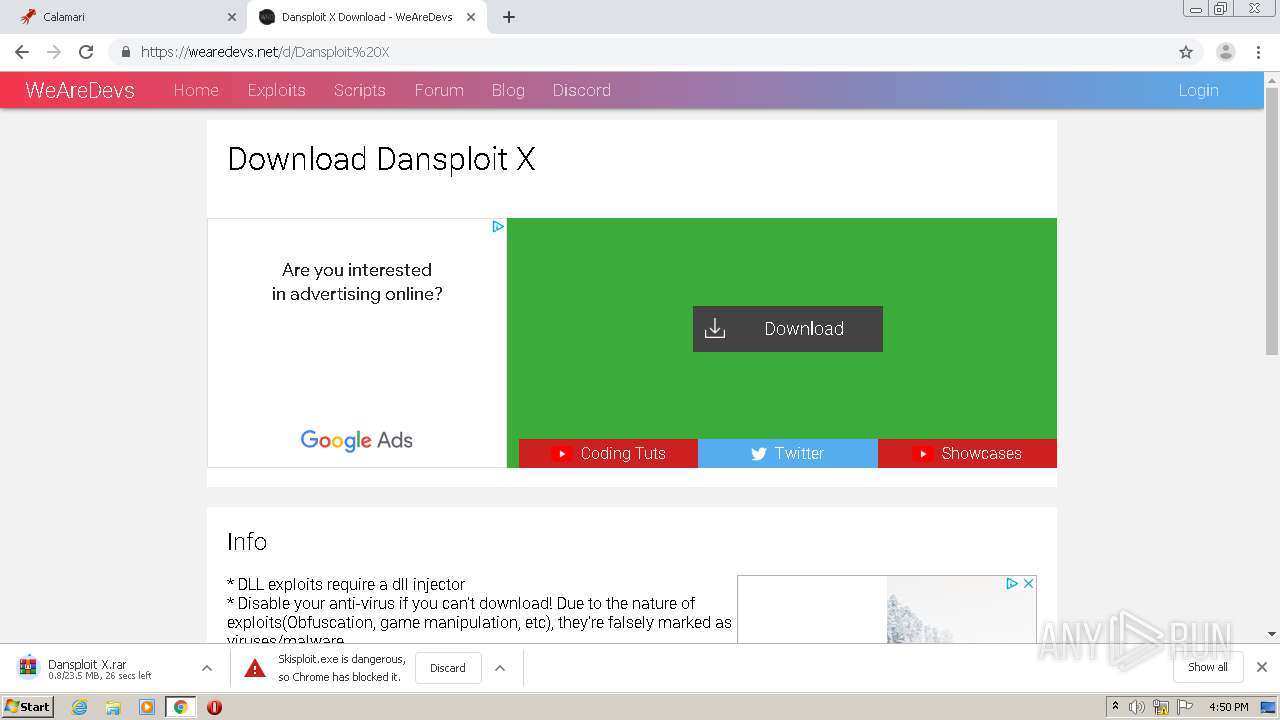
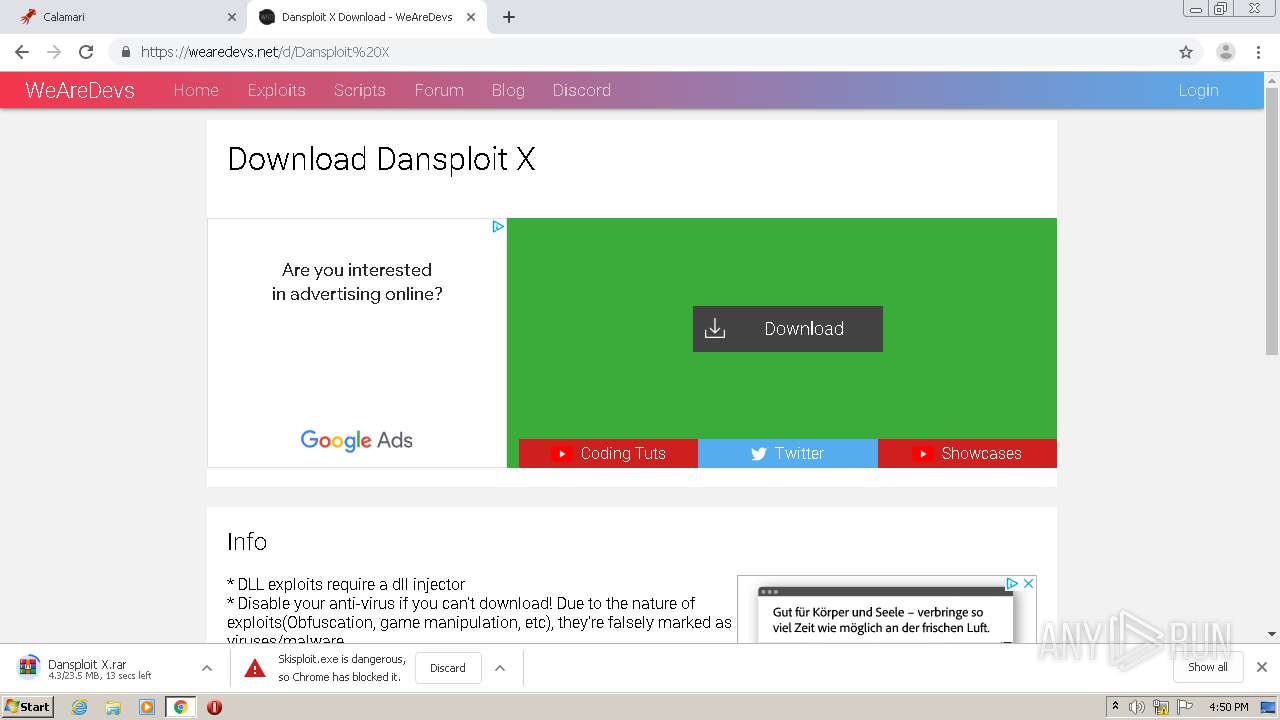
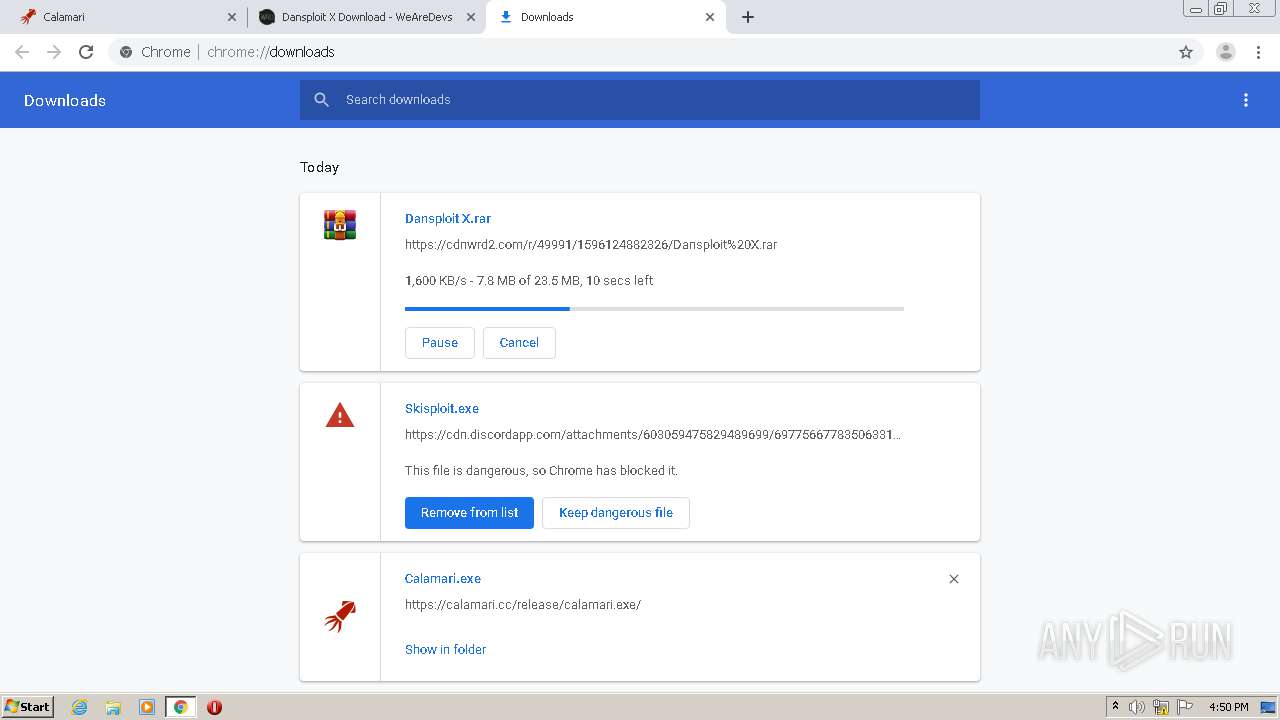
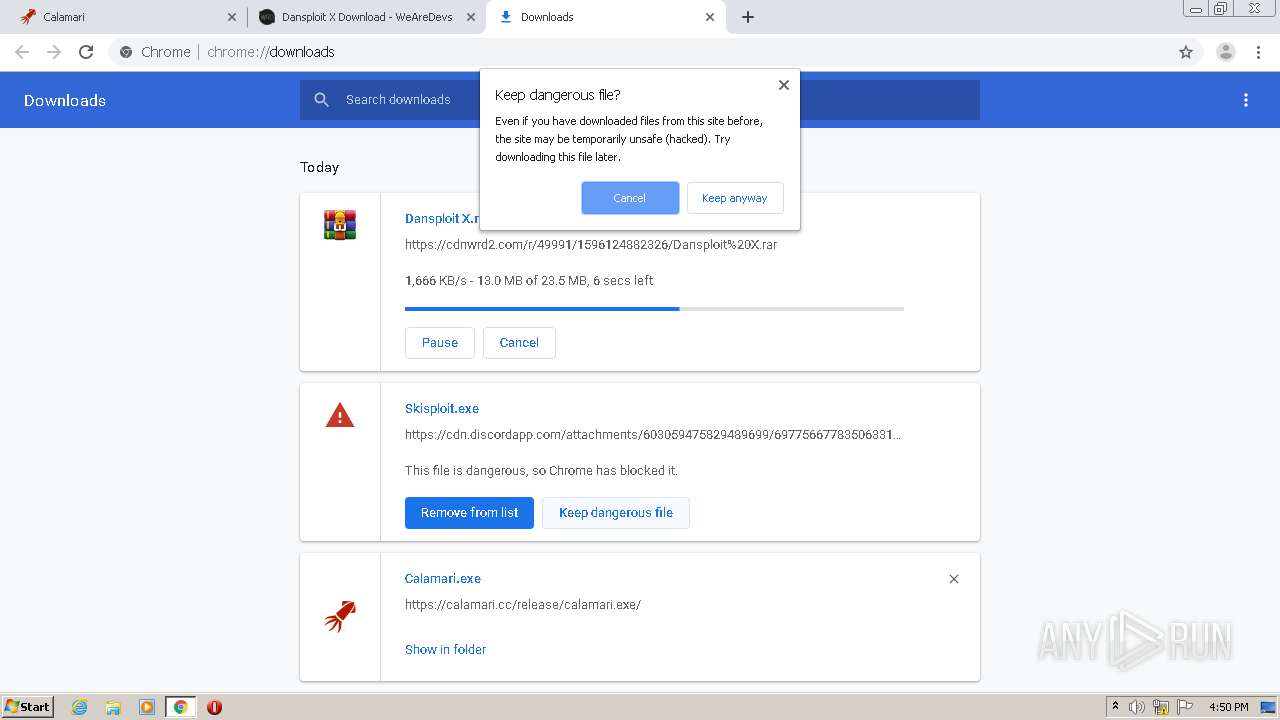
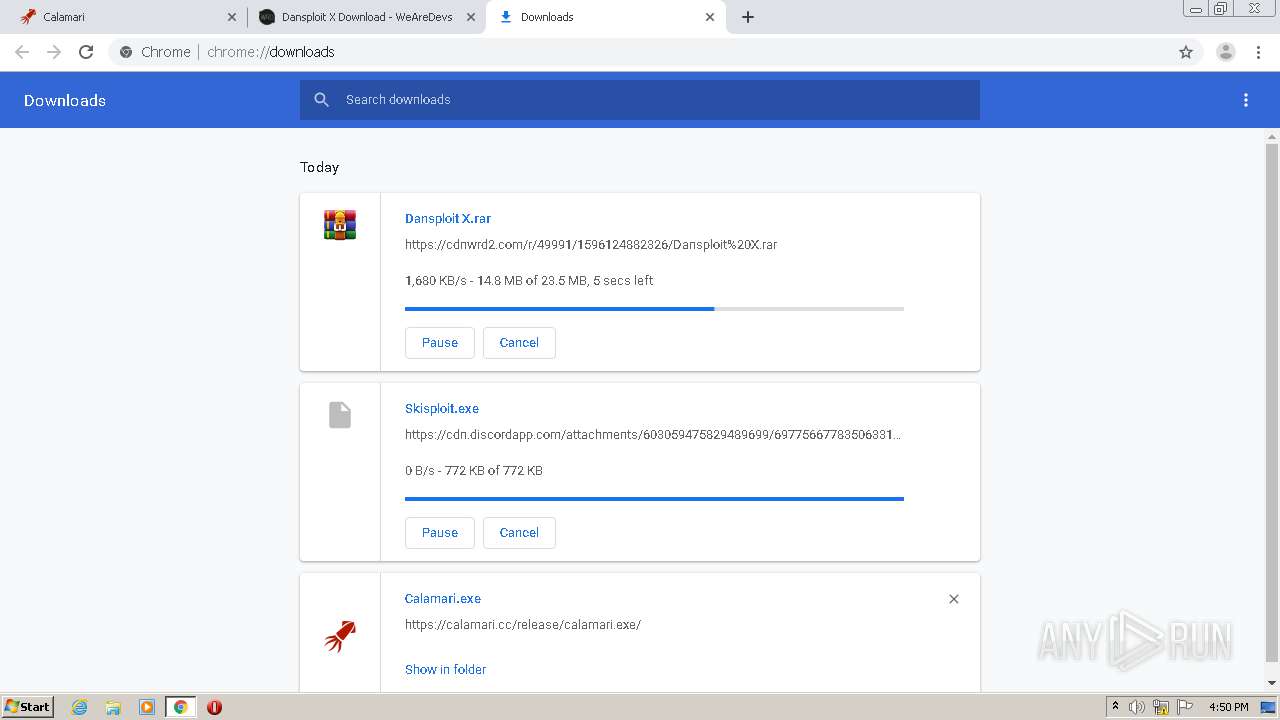
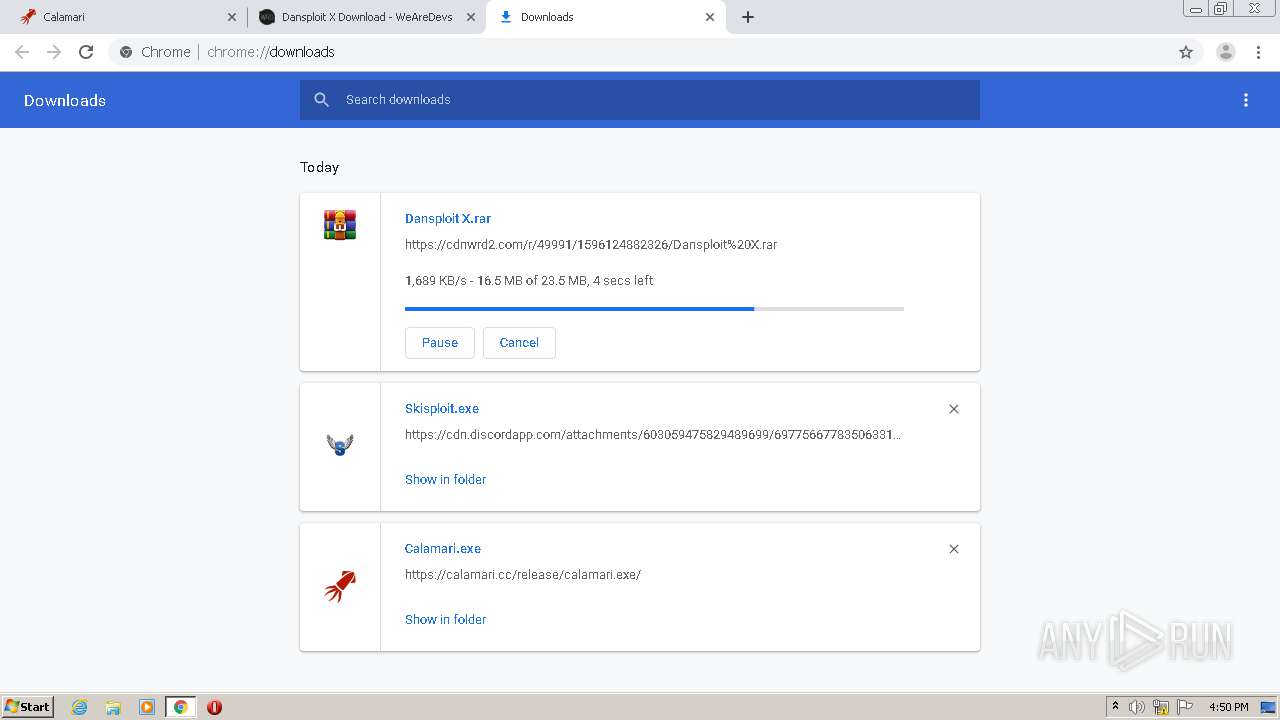
Downloads executable files from the Internet
- Skisploit.exe (PID: 1252)
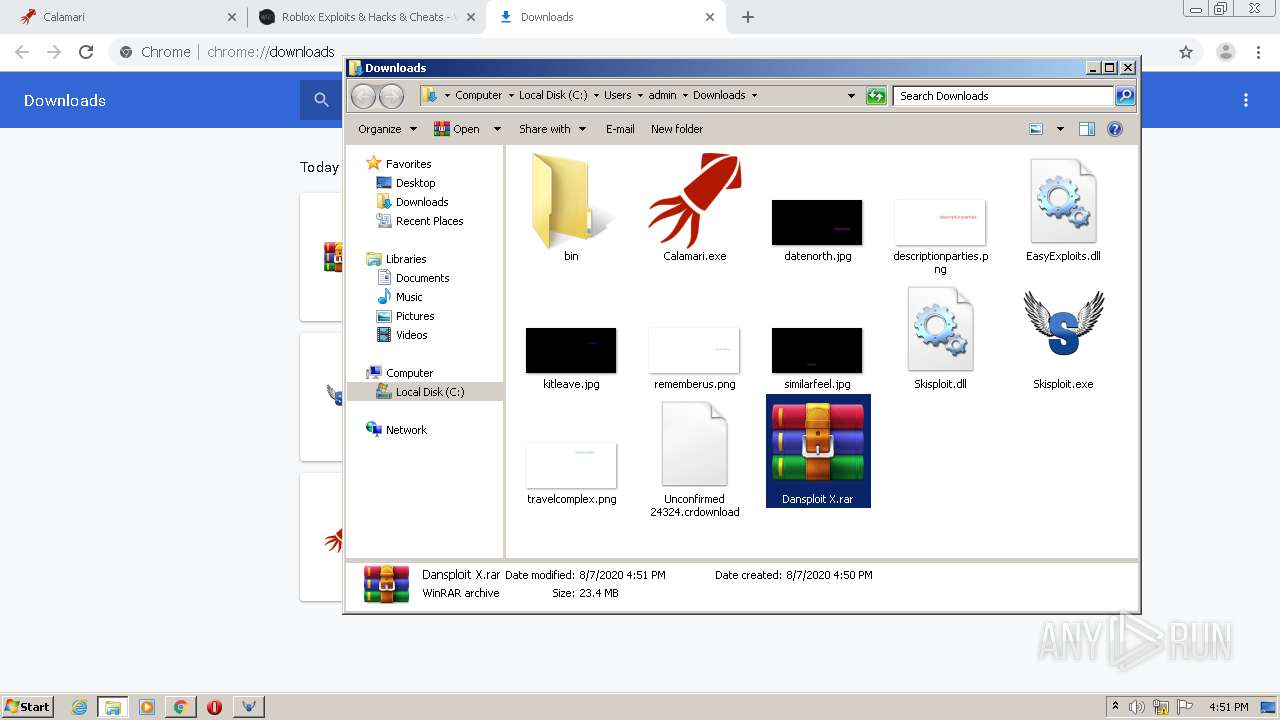
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2792)
- chrome.exe (PID: 2812)
- Skisploit.exe (PID: 1252)
- WinRAR.exe (PID: 3652)
Reads Environment values
- Skisploit.exe (PID: 1252)
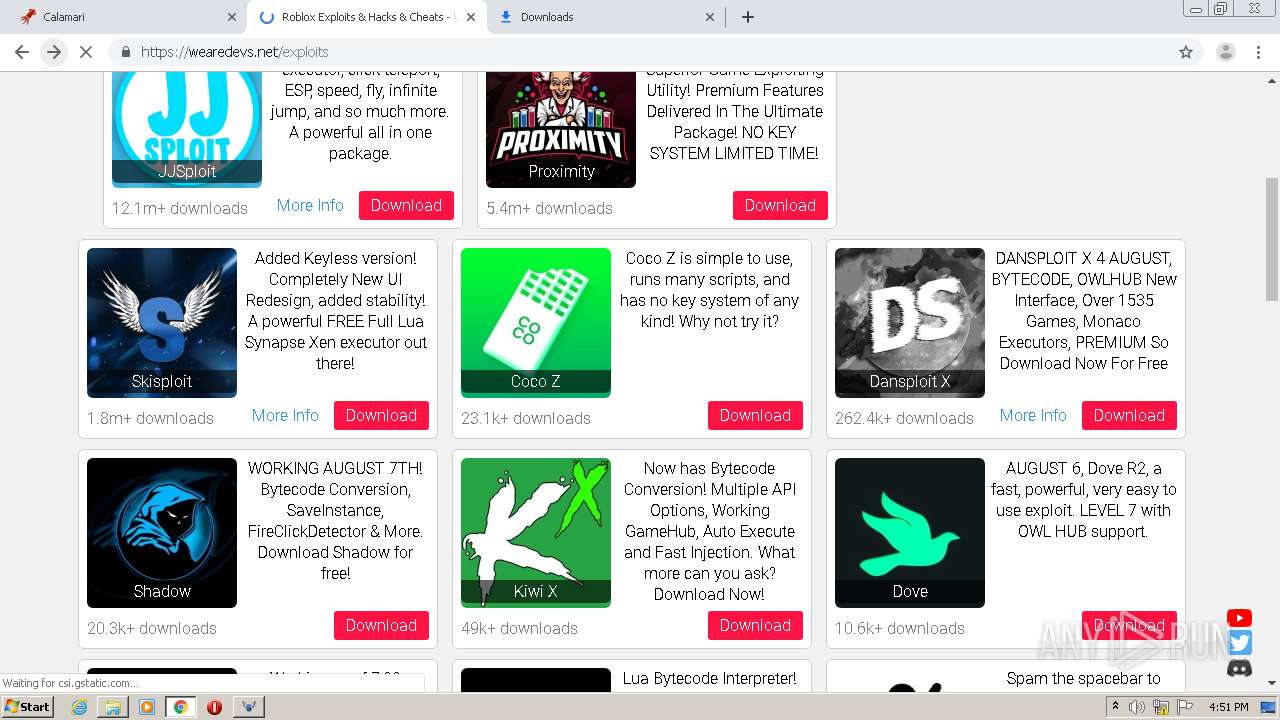
Starts Internet Explorer
- Skisploit.exe (PID: 1252)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 2200)
- iexplore.exe (PID: 780)
Reads the hosts file
- chrome.exe (PID: 2812)
- chrome.exe (PID: 2792)
Application launched itself
- iexplore.exe (PID: 2200)
- chrome.exe (PID: 2812)
Changes internet zones settings
- iexplore.exe (PID: 2200)
Creates files in the user directory
- chrome.exe (PID: 2812)
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2200)
Reads settings of System Certificates
- iexplore.exe (PID: 780)
- iexplore.exe (PID: 2200)
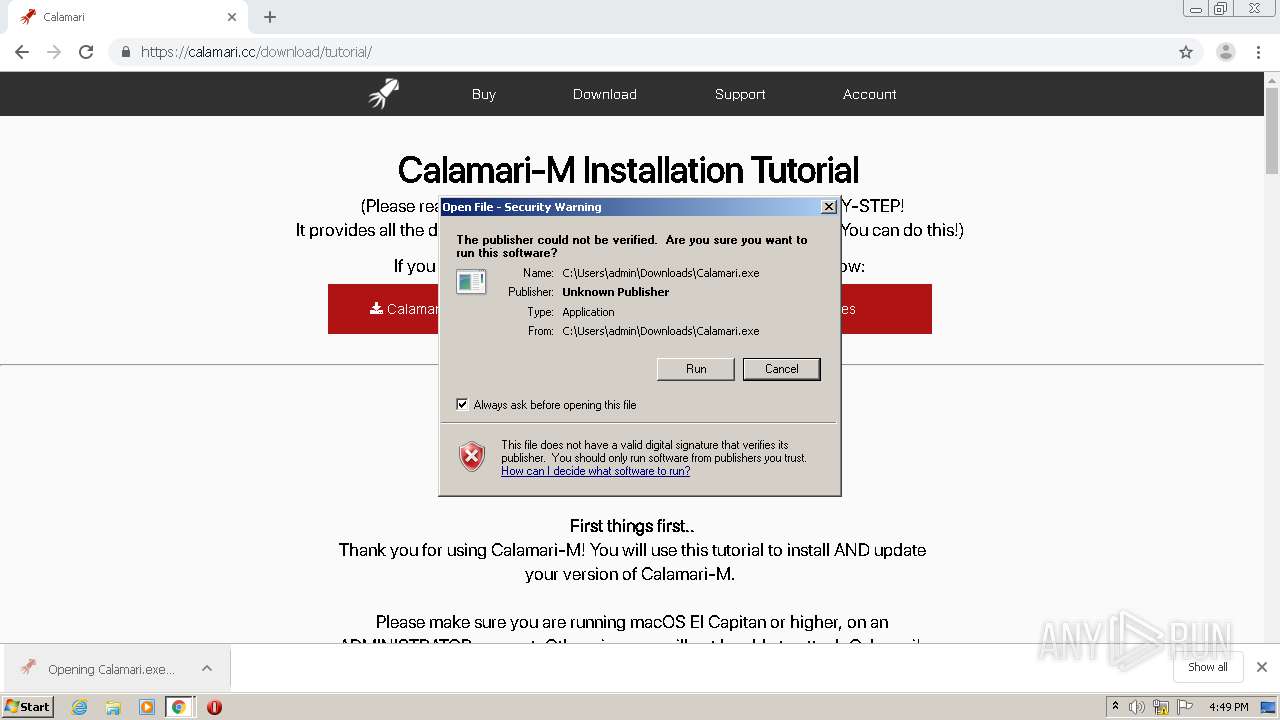
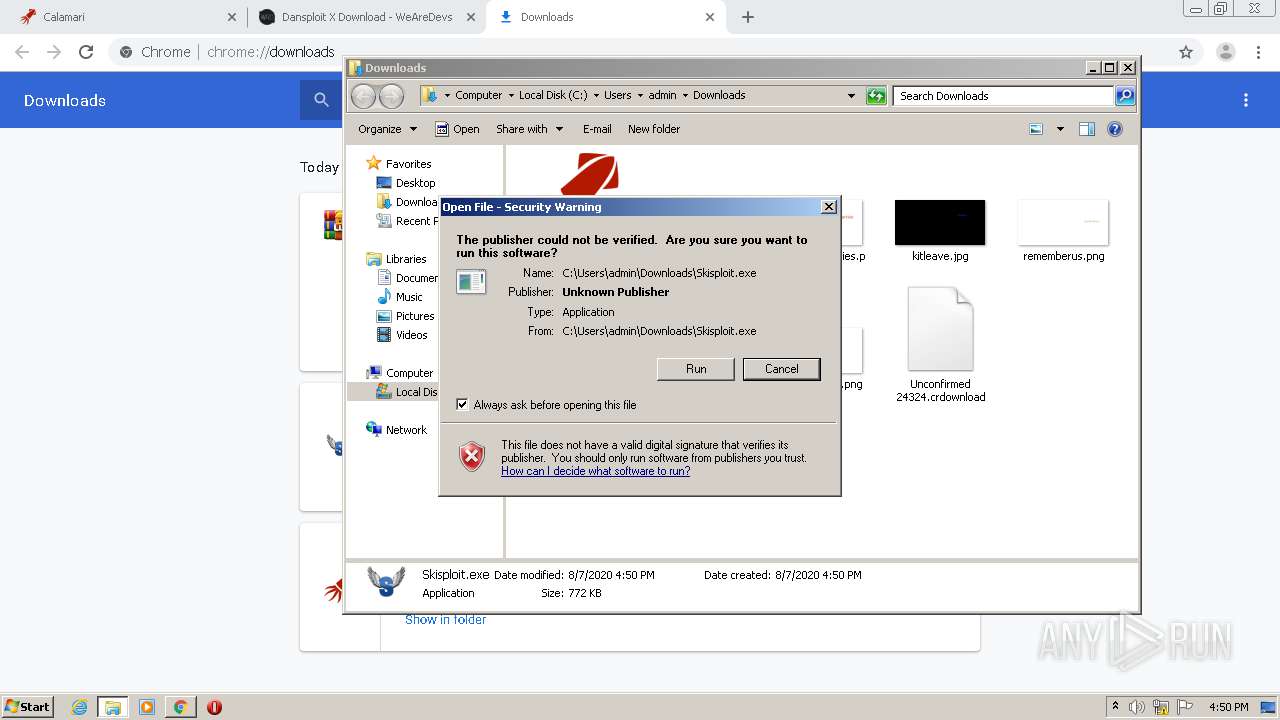
Manual execution by user
- Skisploit.exe (PID: 1252)
- WinRAR.exe (PID: 3652)
Reads internet explorer settings
- iexplore.exe (PID: 780)
Changes settings of System certificates
- iexplore.exe (PID: 2200)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2200)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 780)
- WinRAR.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
61
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=2787593850810927153 --mojo-platform-channel-handle=3500 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=13676244829203652017 --mojo-platform-channel-handle=3480 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14057907937369300170 --mojo-platform-channel-handle=4372 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
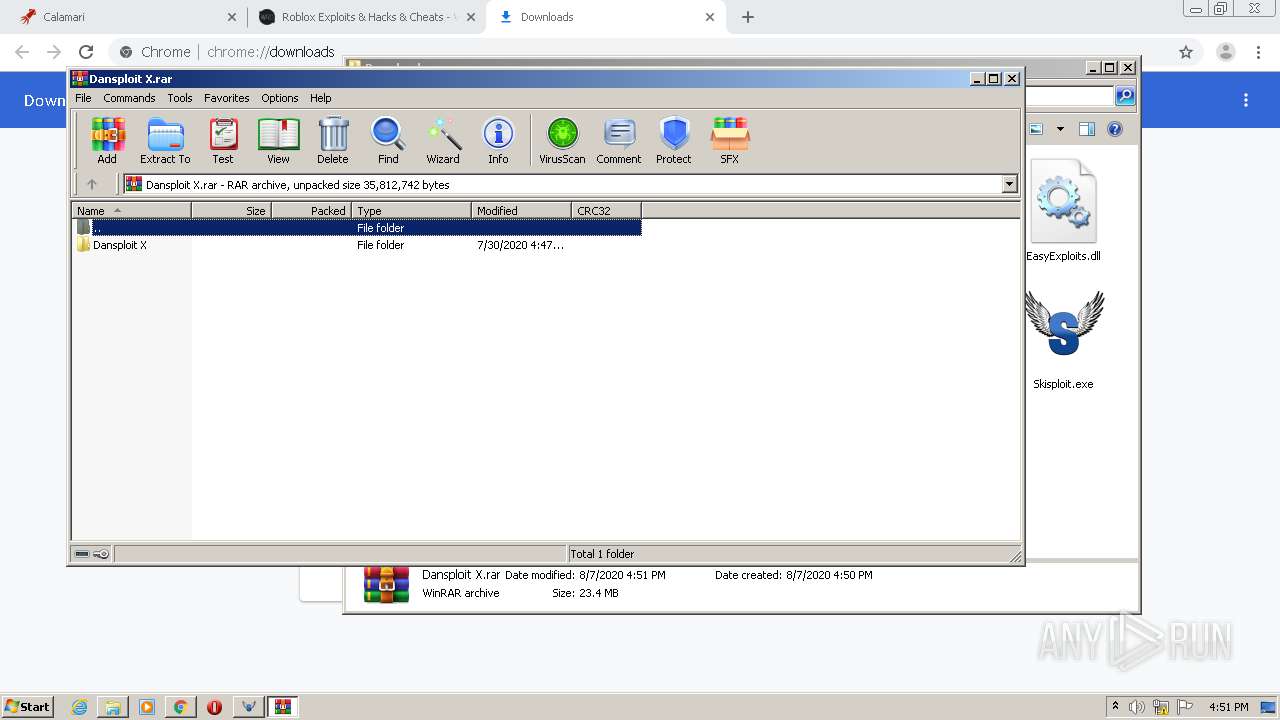
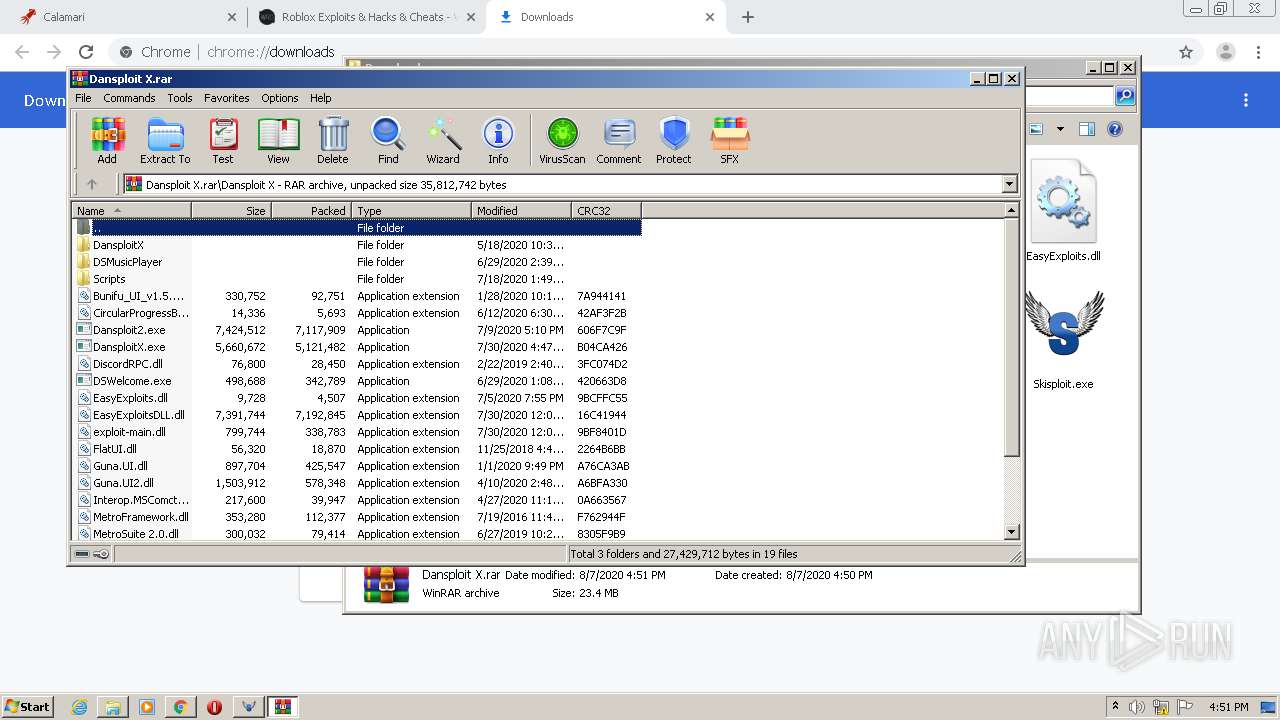
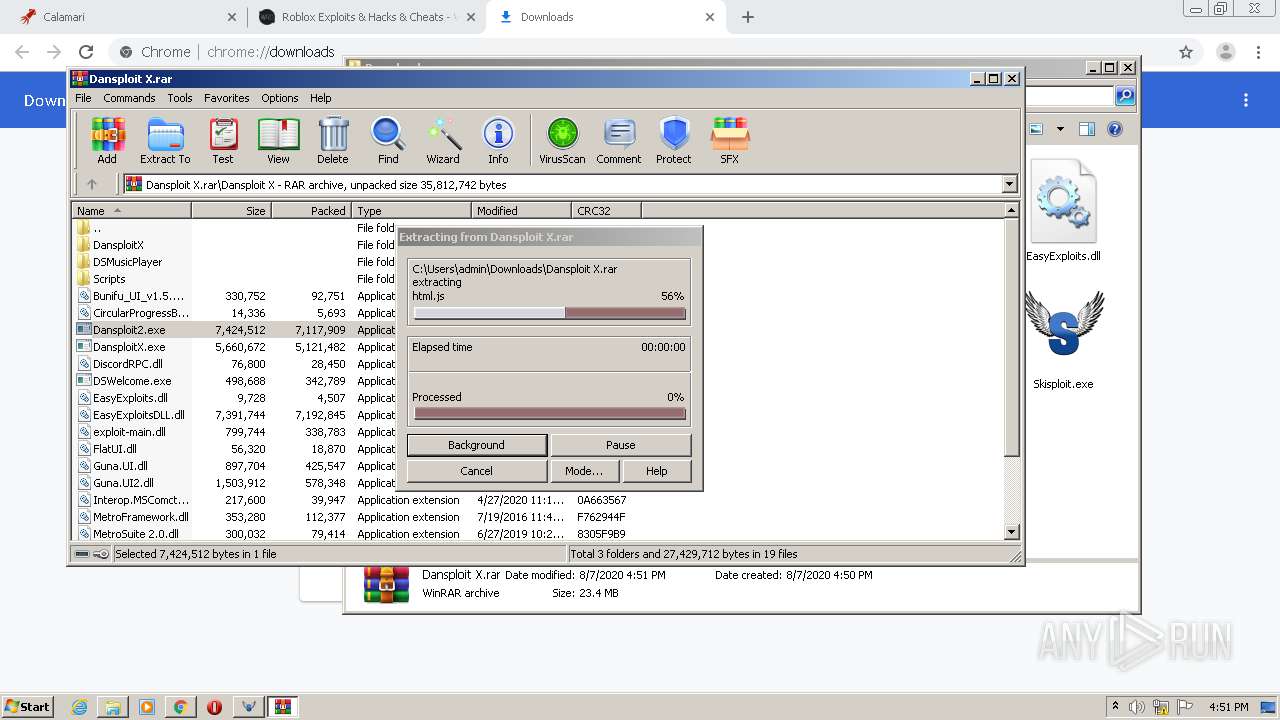
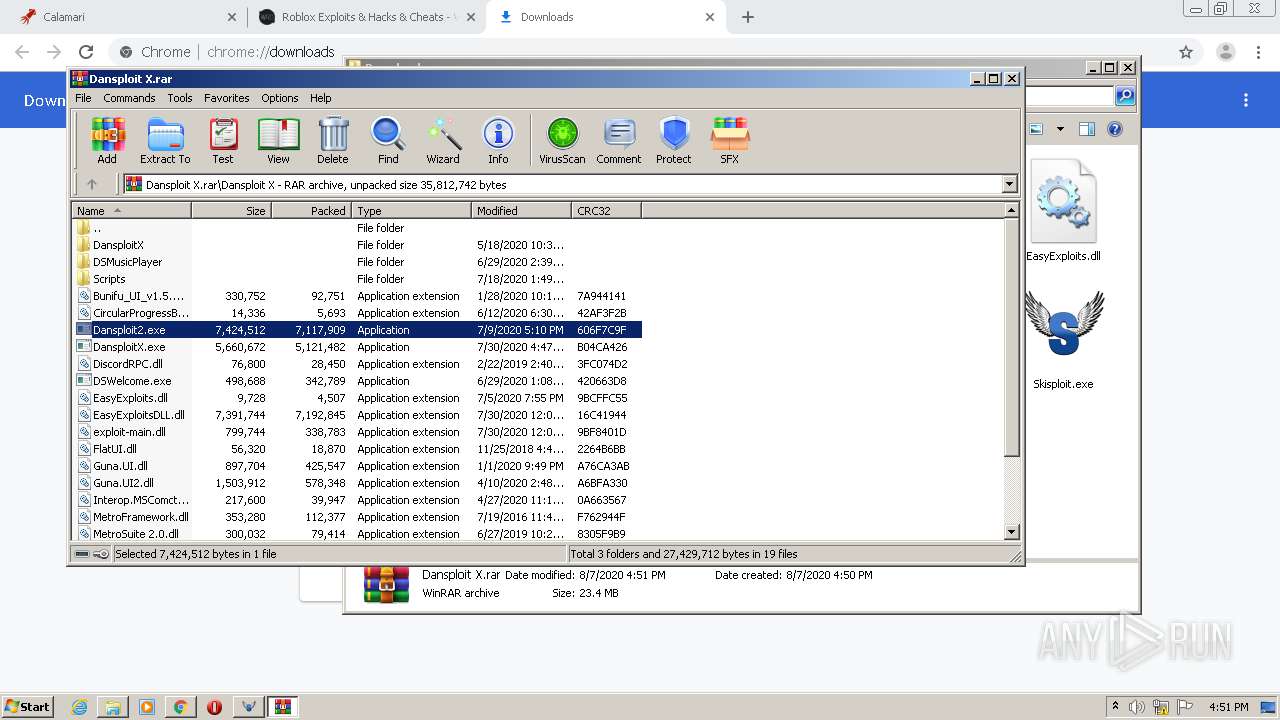
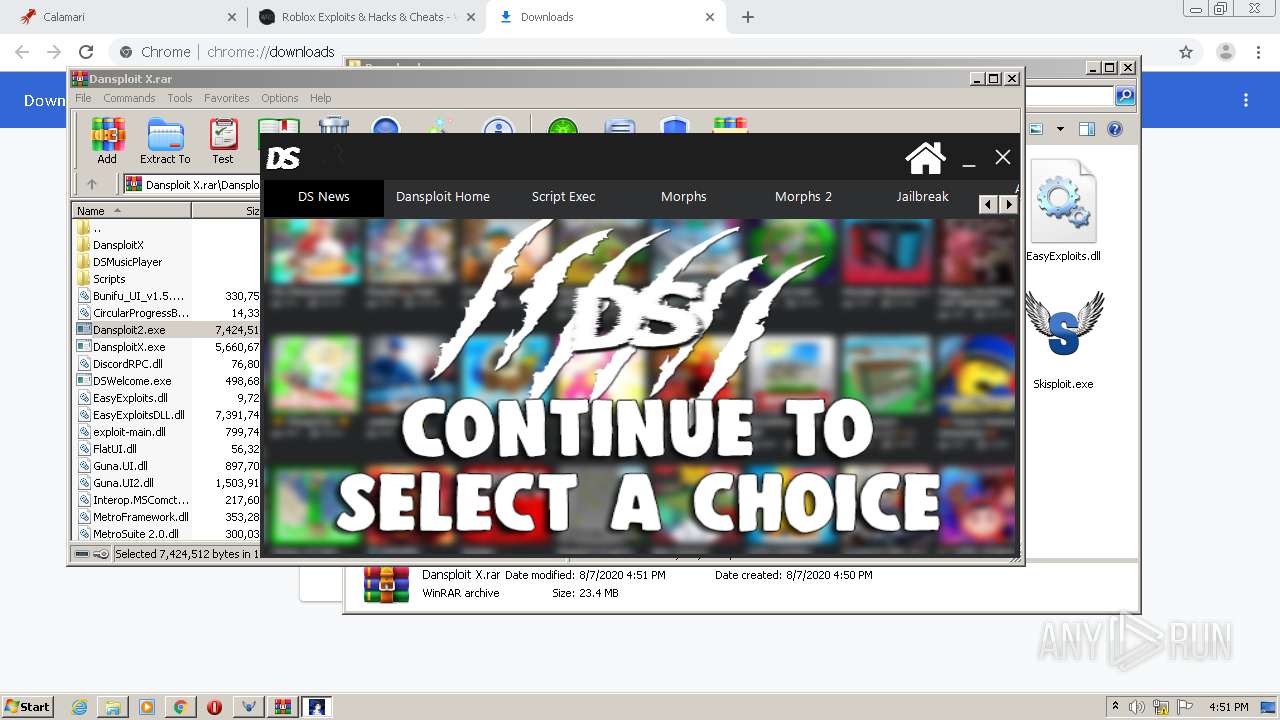
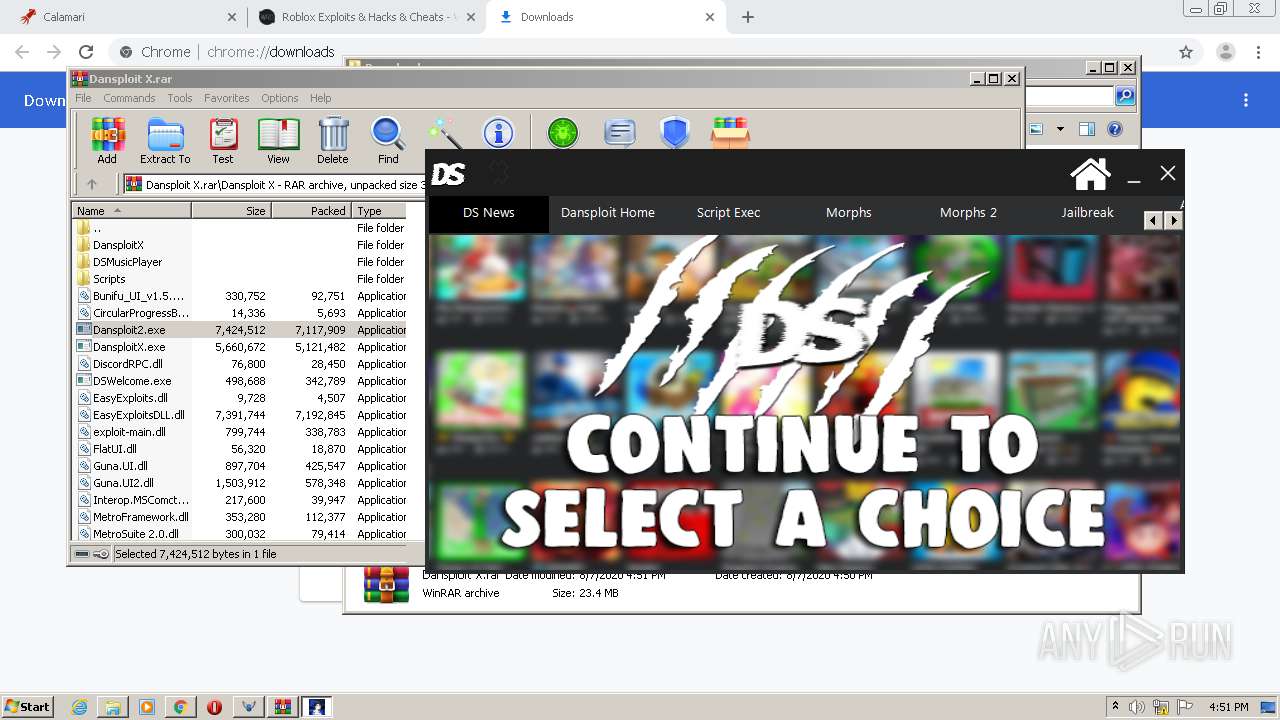
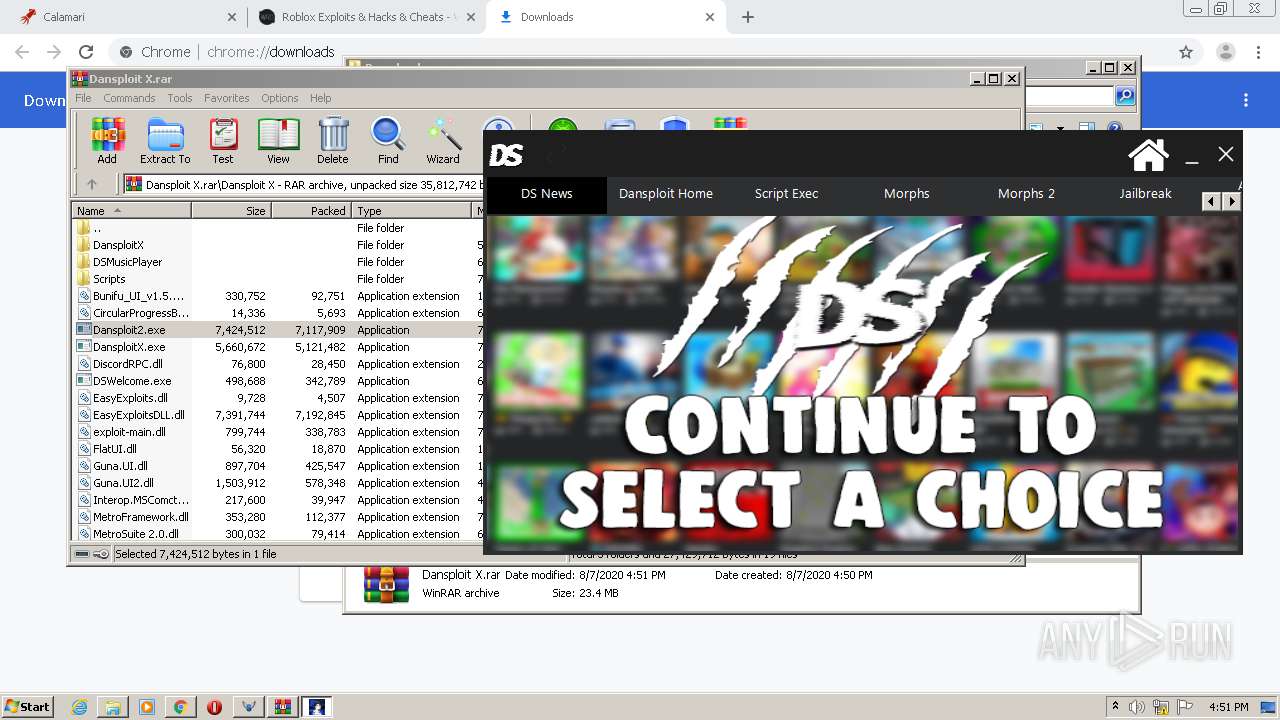
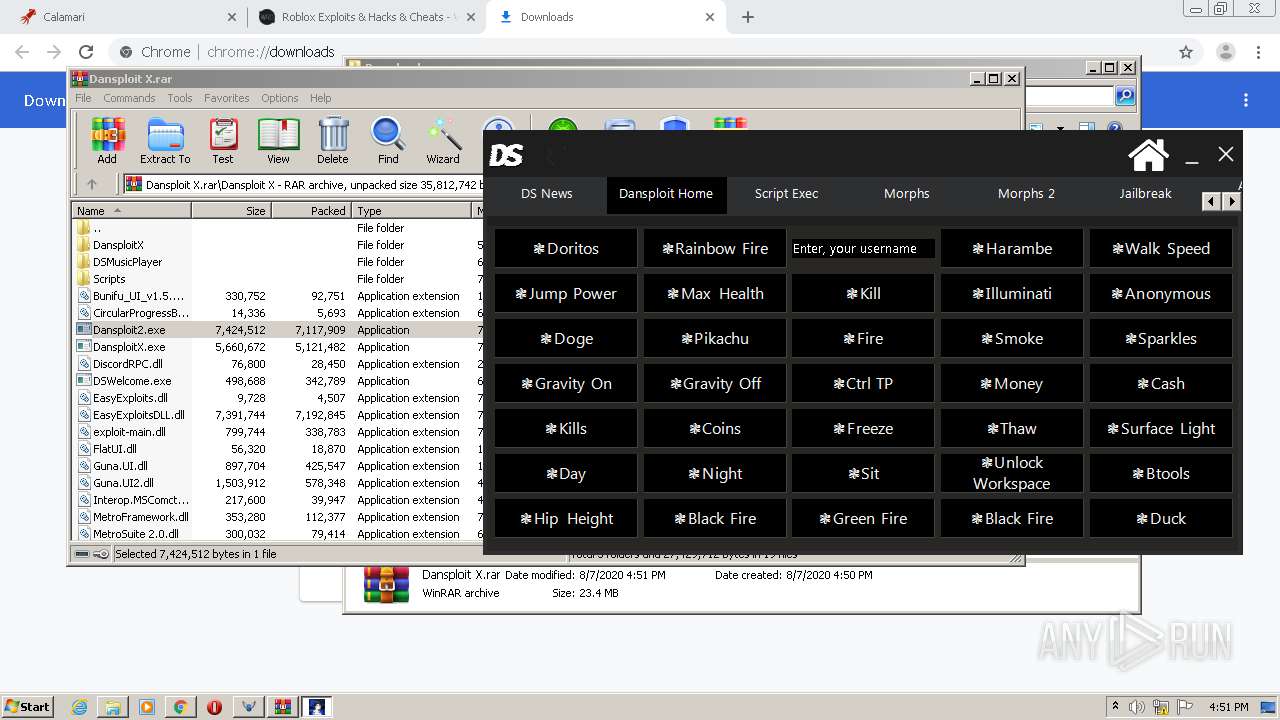
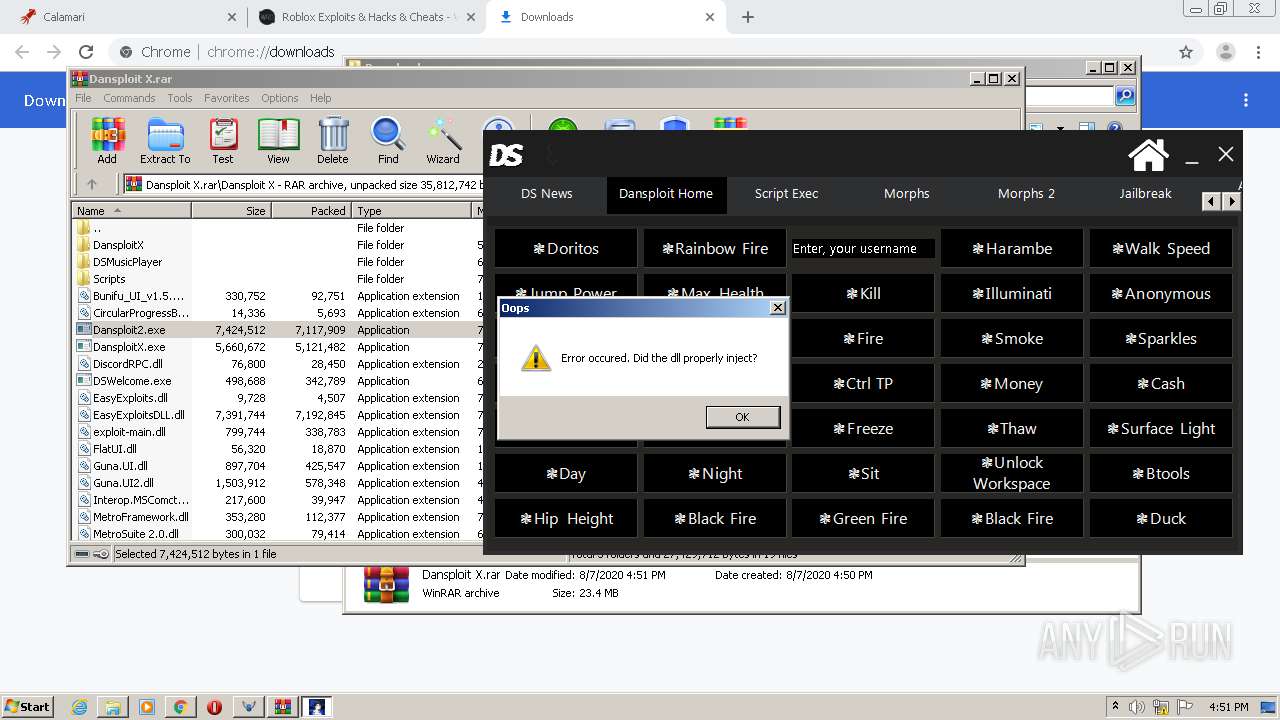
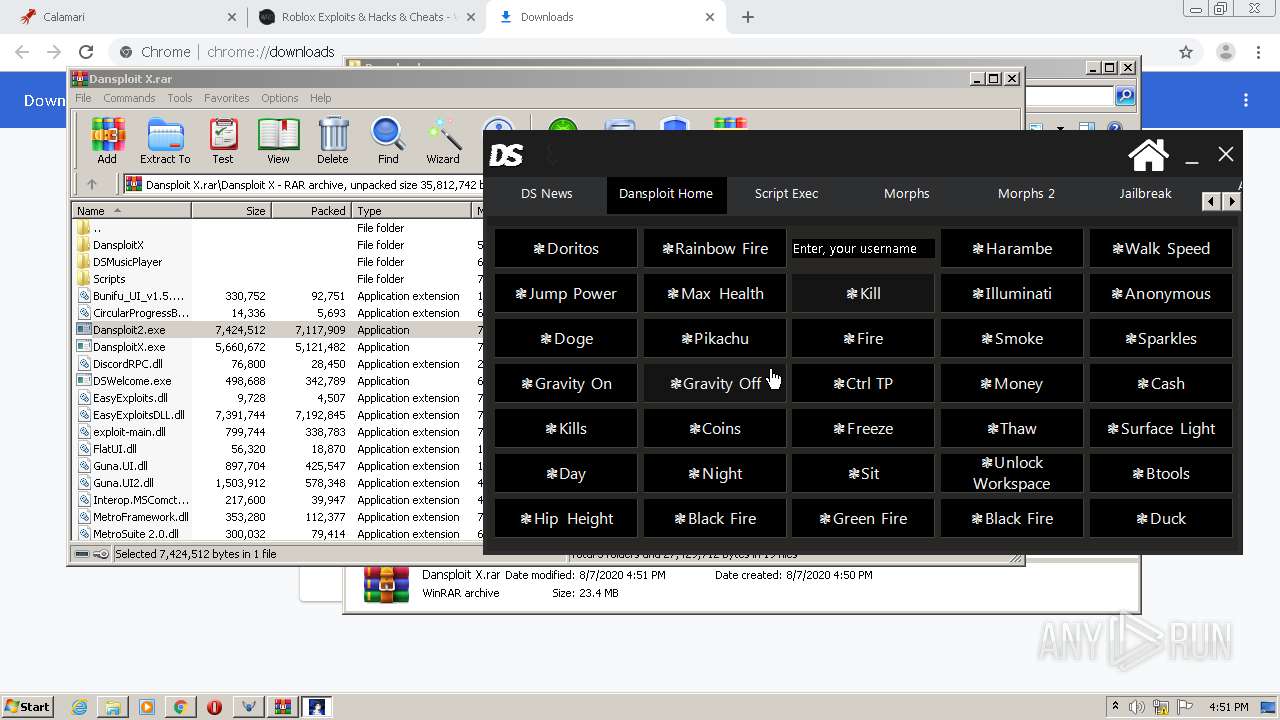
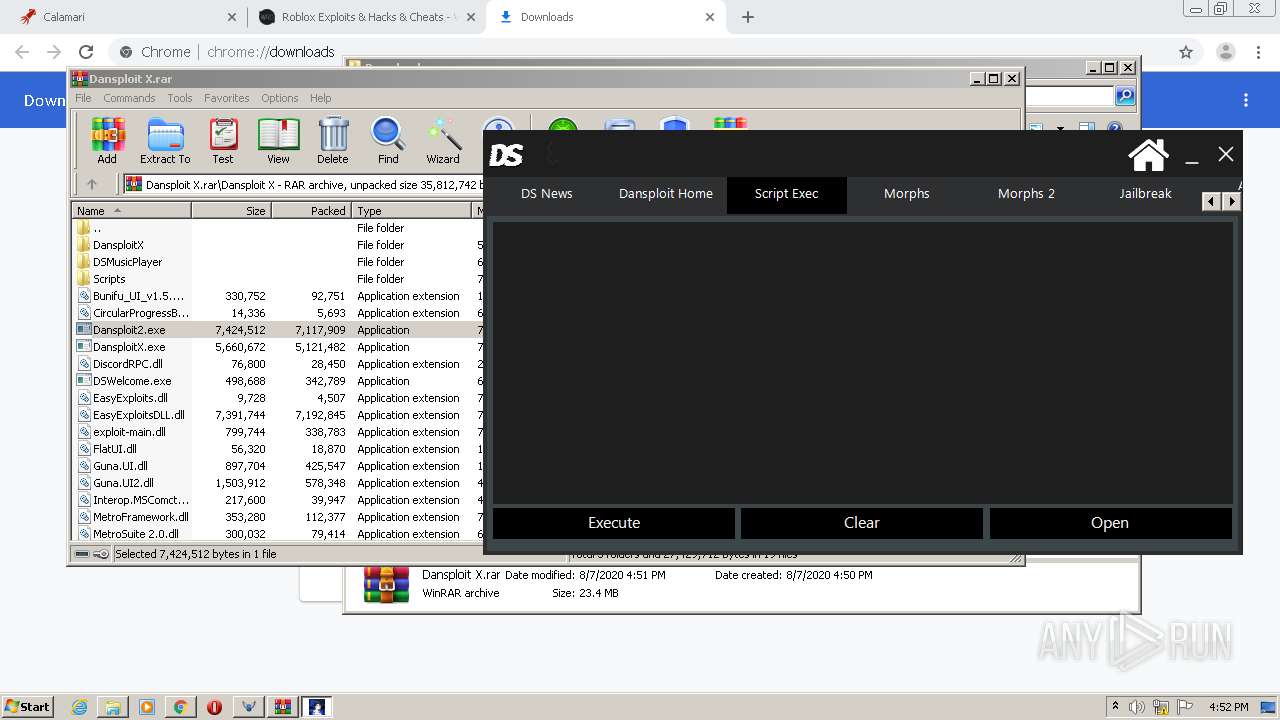
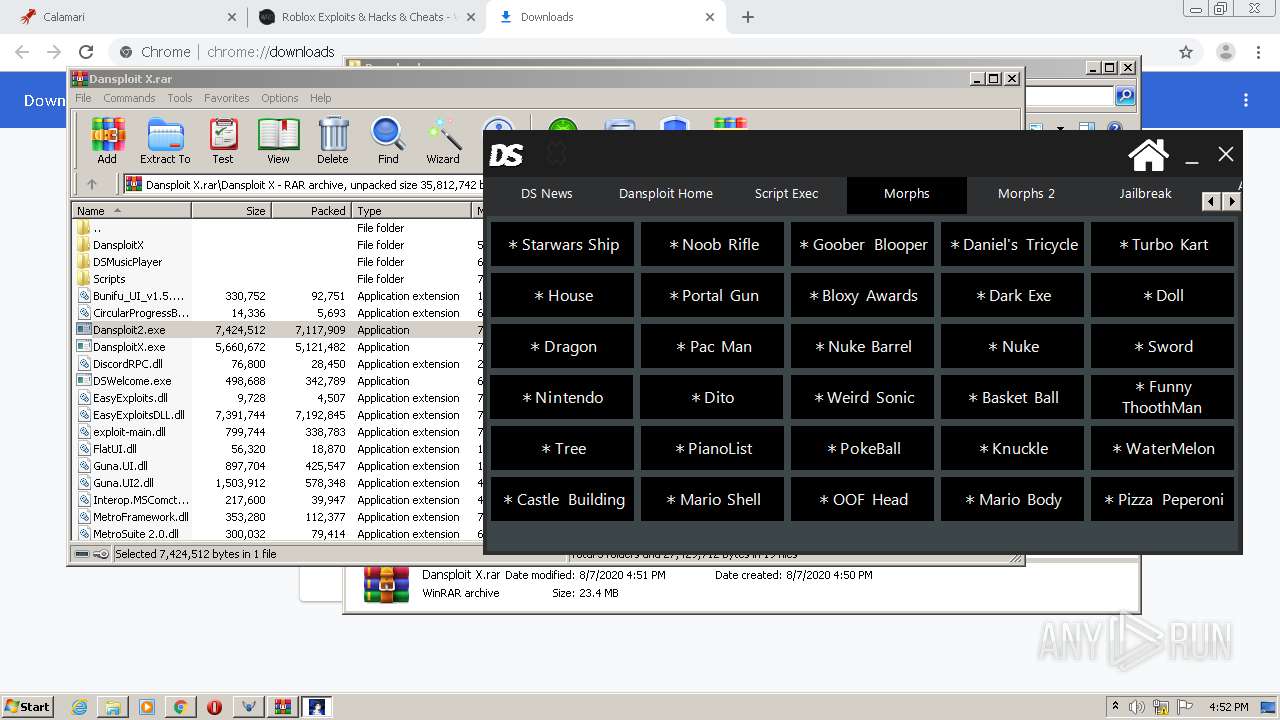
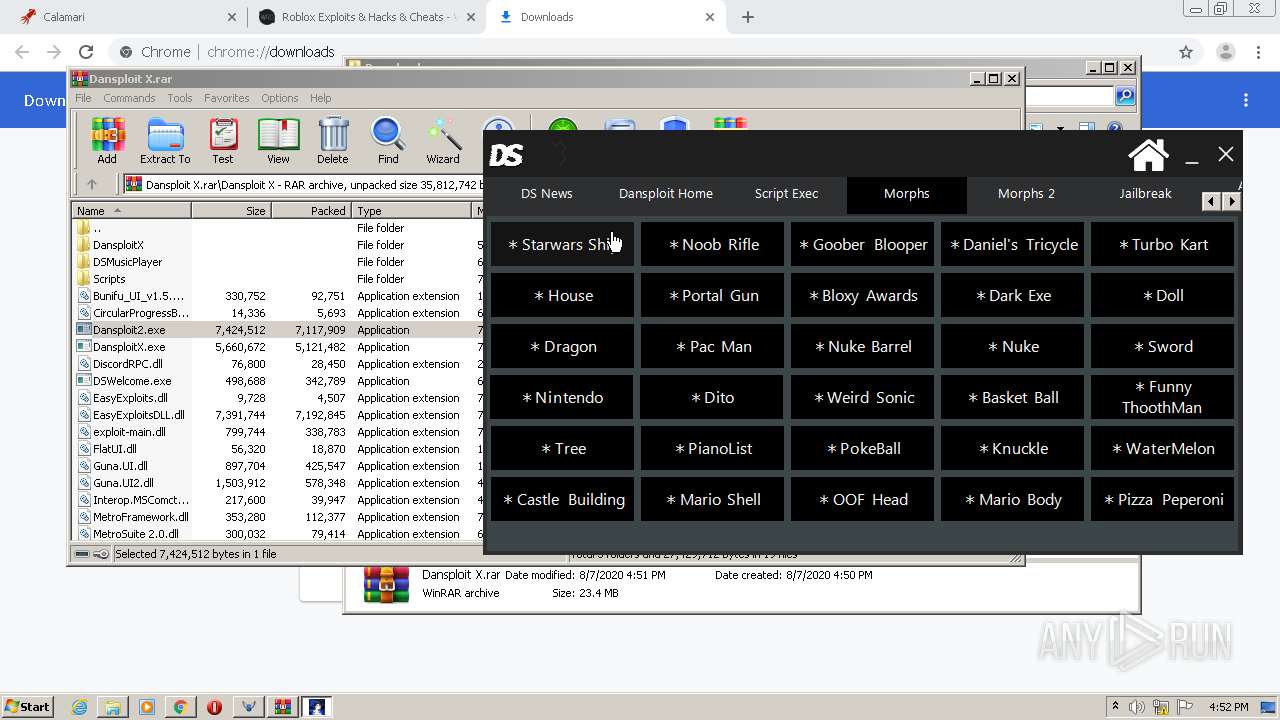
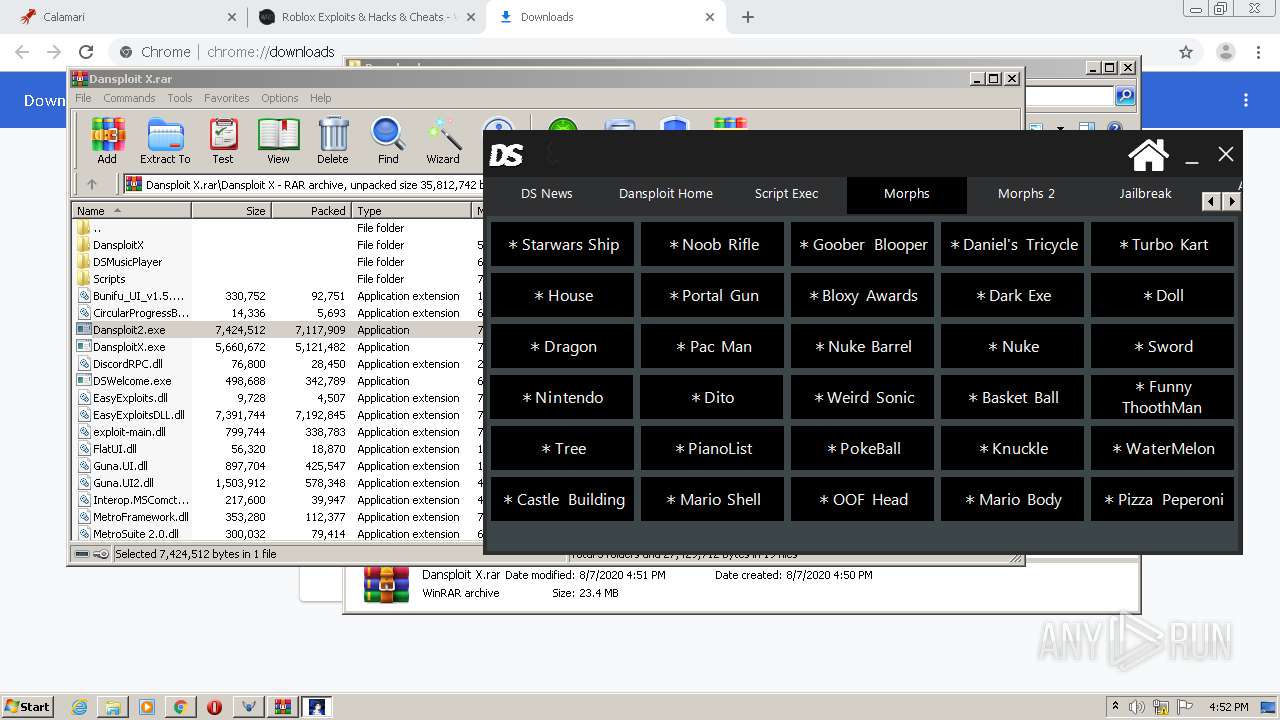
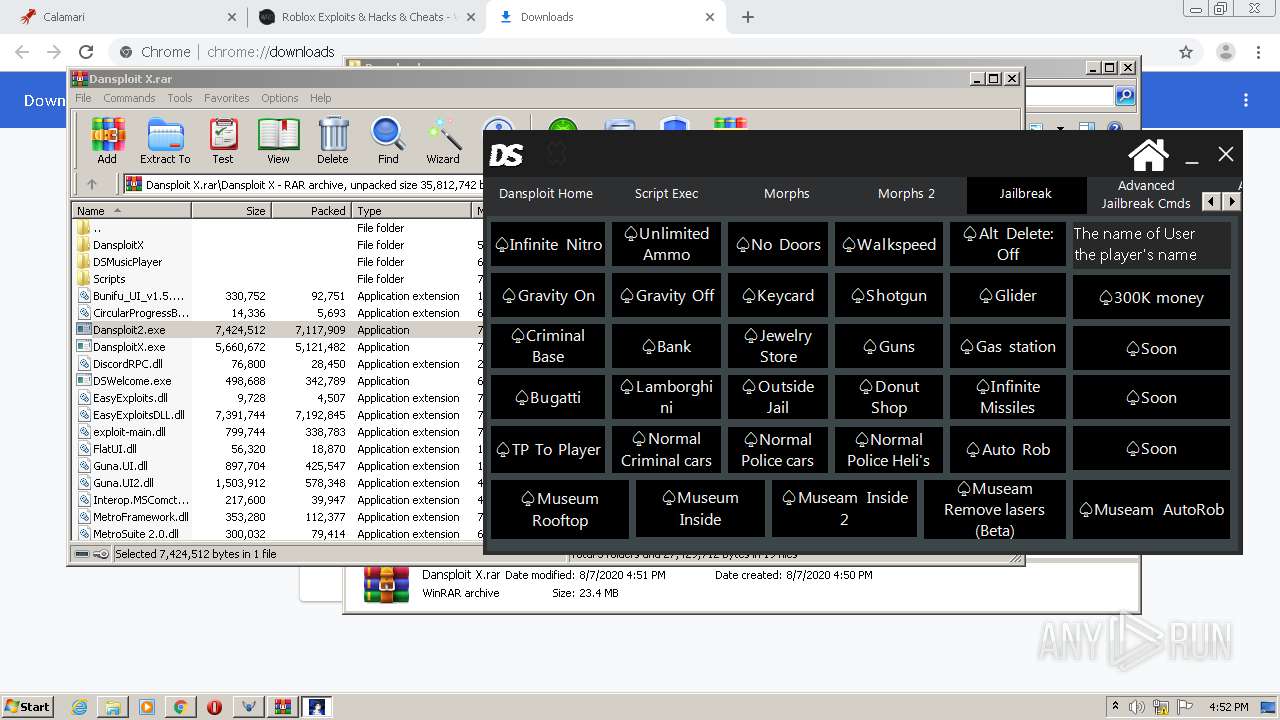
| 576 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.32826\Dansploit X\Dansploit2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3652.32826\Dansploit X\Dansploit2.exe | — | WinRAR.exe | |||||||||||
User: admin Company: DanielNiewold© Integrity Level: MEDIUM Description: Dansploit X Old Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14530798610180477172 --renderer-client-id=42 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2116 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13223652866547090176 --renderer-client-id=35 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3860 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2200 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=6412644190914822028 --mojo-platform-channel-handle=2440 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6976849621846467478 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,4060687638392183371,6448867932895760529,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9128384355998637522 --mojo-platform-channel-handle=1908 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 601
Read events
2 320
Write events
270
Delete events
11
Modification events
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2812-13241288917422625 |
Value: 259 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
33
Suspicious files
237
Text files
247
Unknown types
33
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\23f64408-0c41-4907-a890-4fb3ec869b3c.tmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:D11C35B3D5258F594933332C11C6F0F2 | SHA256:DC2EB16E16FA3FB258AC31A481F817208CF0C917AF4224F2832588D3A64ADD05 | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:AFDDC99E148FD40EED8086EE532B61C4 | SHA256:3F1C412561D08C113C1561C9D273FBA00DAB5481B4AC1428FCC91D9285BA7E1E | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe0933.TMP | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:0CE1FA0314D44178816BA5E7133E07DD | SHA256:8D81EC8C4EFED885A0FF9267B0B388FB53316938EEDCDFABDC697E3610883714 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
161
DNS requests
107
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1252 | Skisploit.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/loadingtips.txt | US | text | 523 b | malicious |
1252 | Skisploit.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/downloads/EasyExploits.dll | US | executable | 9.50 Kb | malicious |
— | — | GET | 302 | 172.217.18.98:80 | http://cm.g.doubleclick.net/pixel?google_nid=spotxchange_dbm&google_hm=YWMwYjg0NjUtZDhjNS0xMWVhLWJkY2YtMTdjYTg5MzAyMTA2 | US | html | 321 b | whitelisted |
1252 | Skisploit.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/version.txt | US | text | 7 b | malicious |
1252 | Skisploit.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/dlldownload.txt | US | text | 90 b | malicious |
1252 | Skisploit.exe | GET | 200 | 104.24.106.9:80 | http://api.thundermods.com/updatemessage.txt | US | text | 240 b | malicious |
780 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
780 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEATXi7Ndo9ER0%2FY0D5NxnyM%3D | US | der | 278 b | whitelisted |
780 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEBblhnjgcJQ5S9%2FbTvymO98%3D | US | der | 471 b | whitelisted |
780 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca4.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTOpjOEf6LG1z52jqAxwDlTxoaOCgQUQAlhZ%2FC8g3FP3hIILG%2FU1Ct2PZYCEDsJGKKiFxWJllawuNqPxXw%3D | US | der | 279 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2792 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 216.58.212.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 172.67.185.52:443 | calamari.cc | — | US | suspicious |
2792 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 104.31.95.162:443 | calamari.cc | Cloudflare Inc | US | shared |
2792 | chrome.exe | 172.217.23.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 172.217.22.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 216.58.206.2:443 | adservice.google.com | Google Inc. | US | whitelisted |
2792 | chrome.exe | 216.58.205.226:443 | adservice.google.de | Google Inc. | US | whitelisted |
2792 | chrome.exe | 172.217.21.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
calamari.cc |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
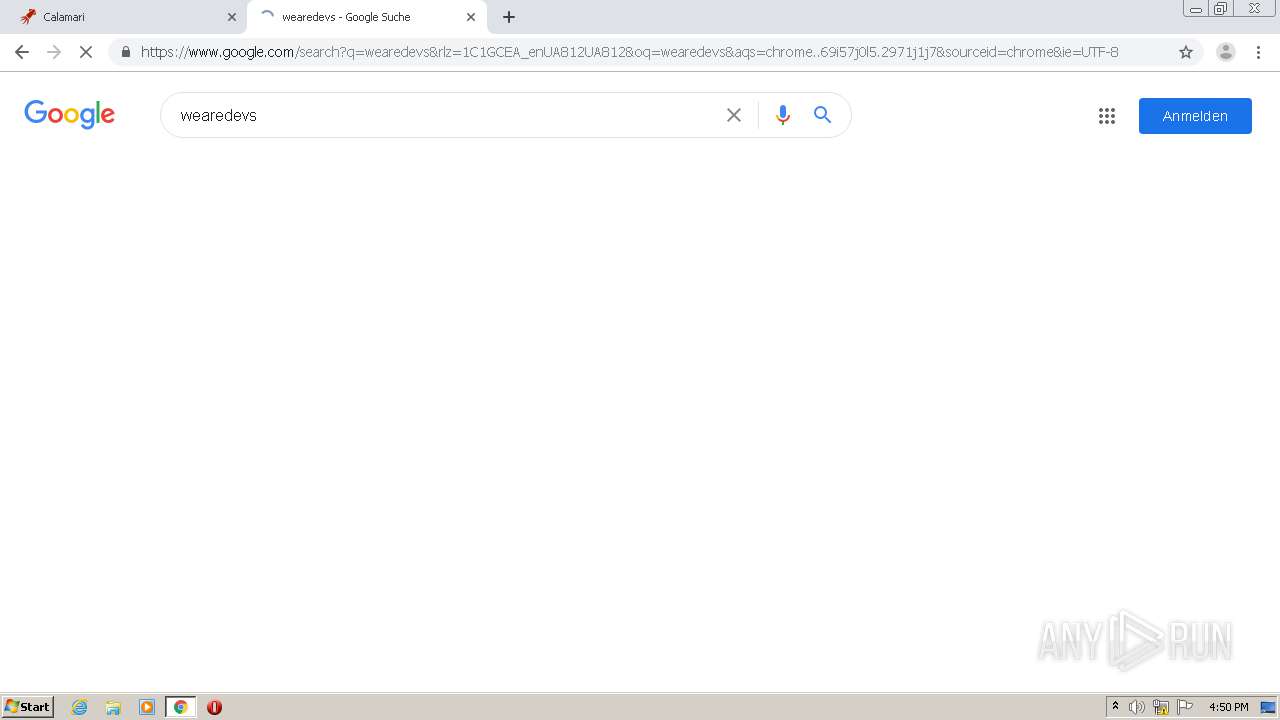
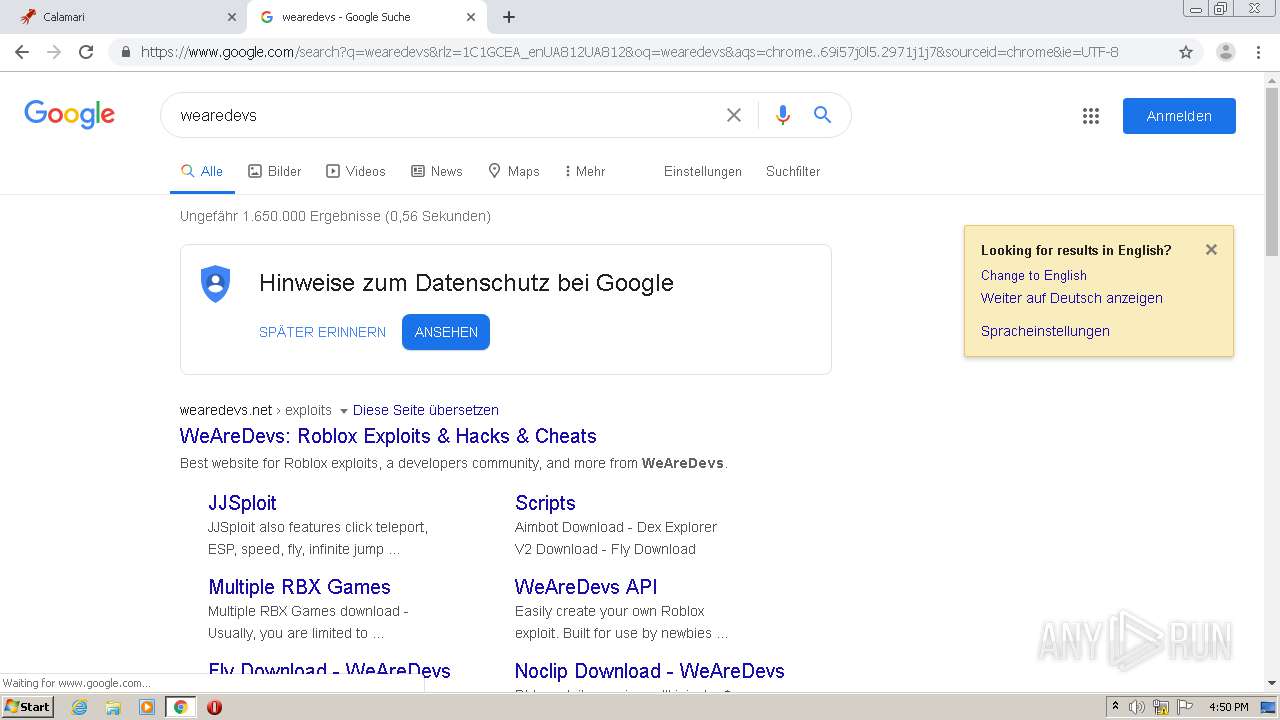
www.google.com |
| malicious |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
www.youtube.com |
| whitelisted |
adservice.google.de |
| whitelisted |
adservice.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1252 | Skisploit.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1252 | Skisploit.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1 ETPRO signatures available at the full report