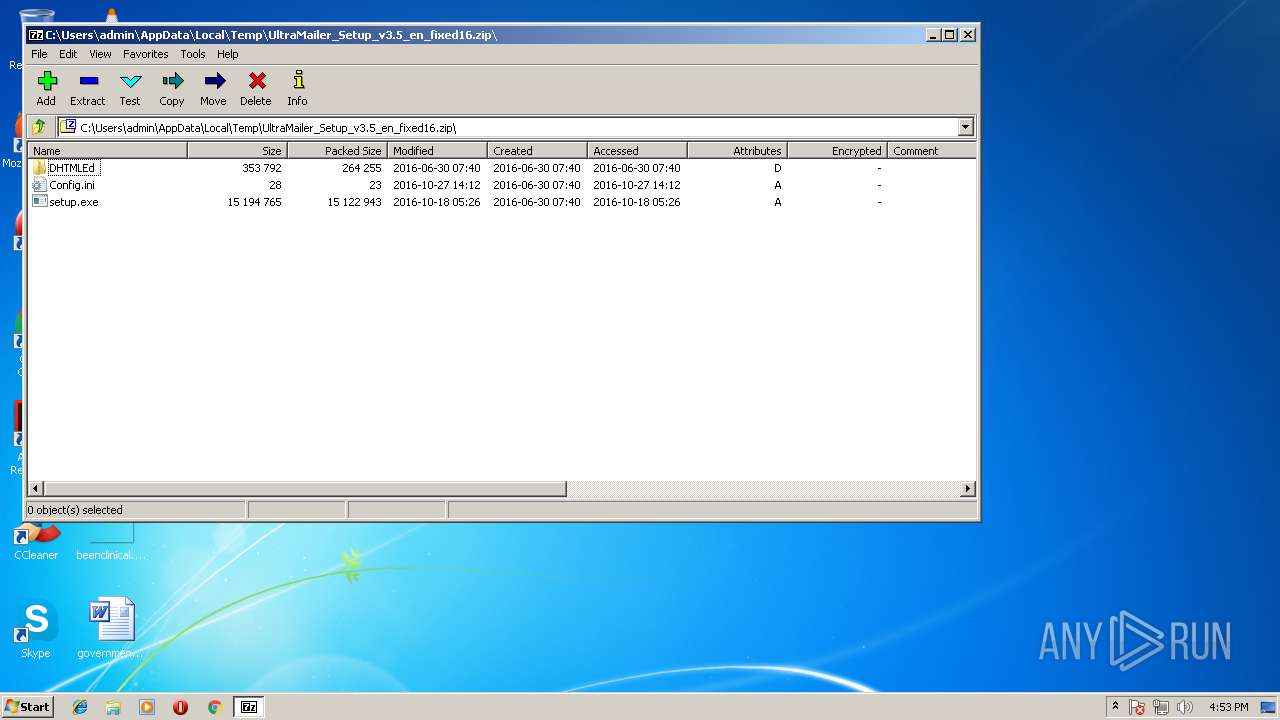
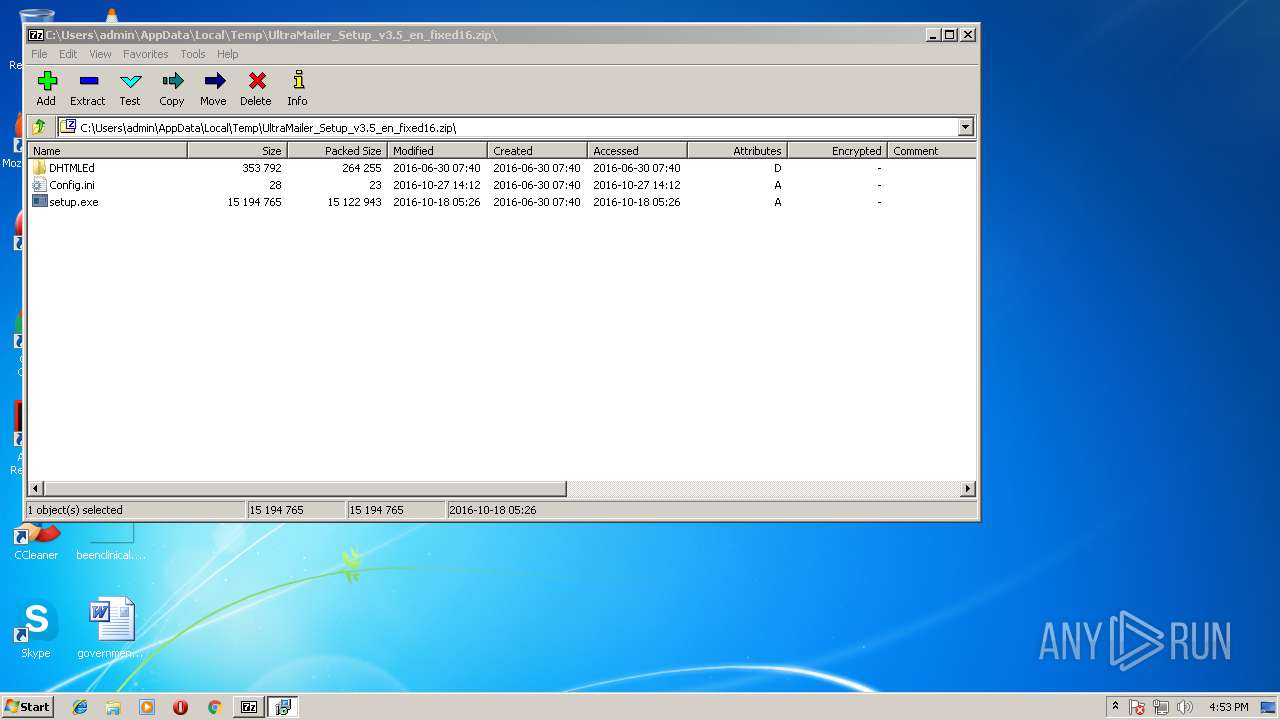
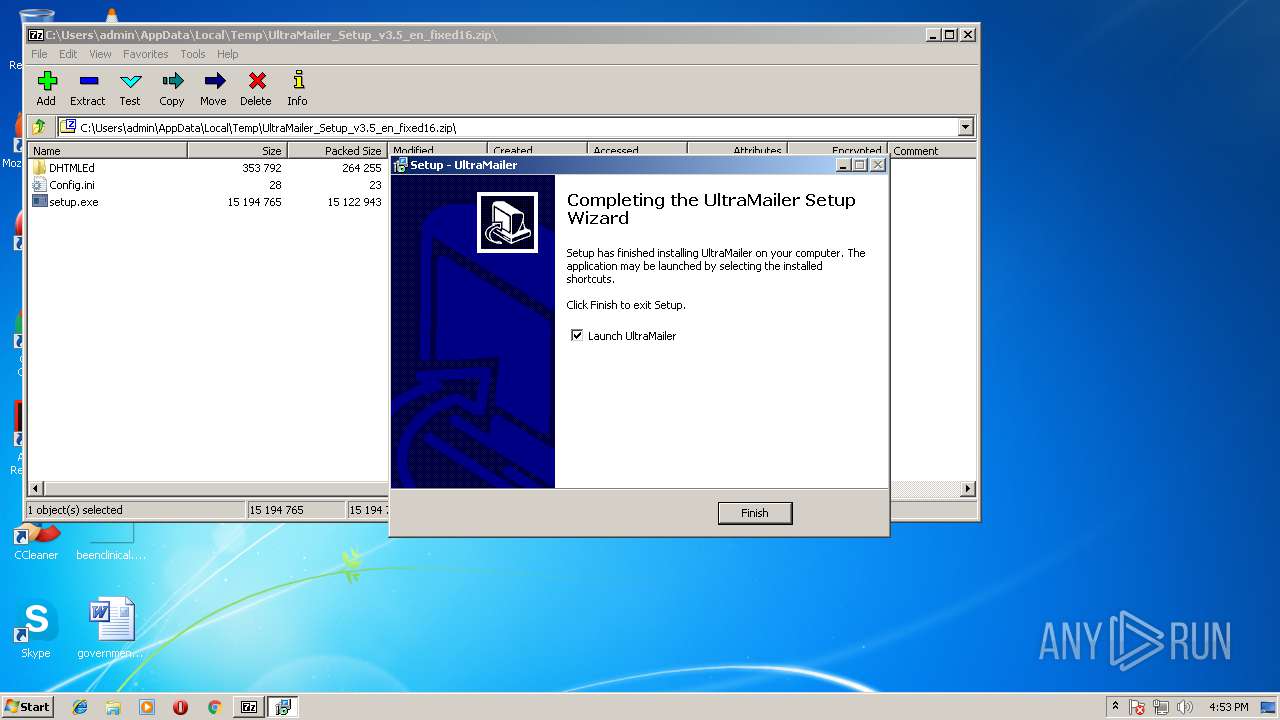
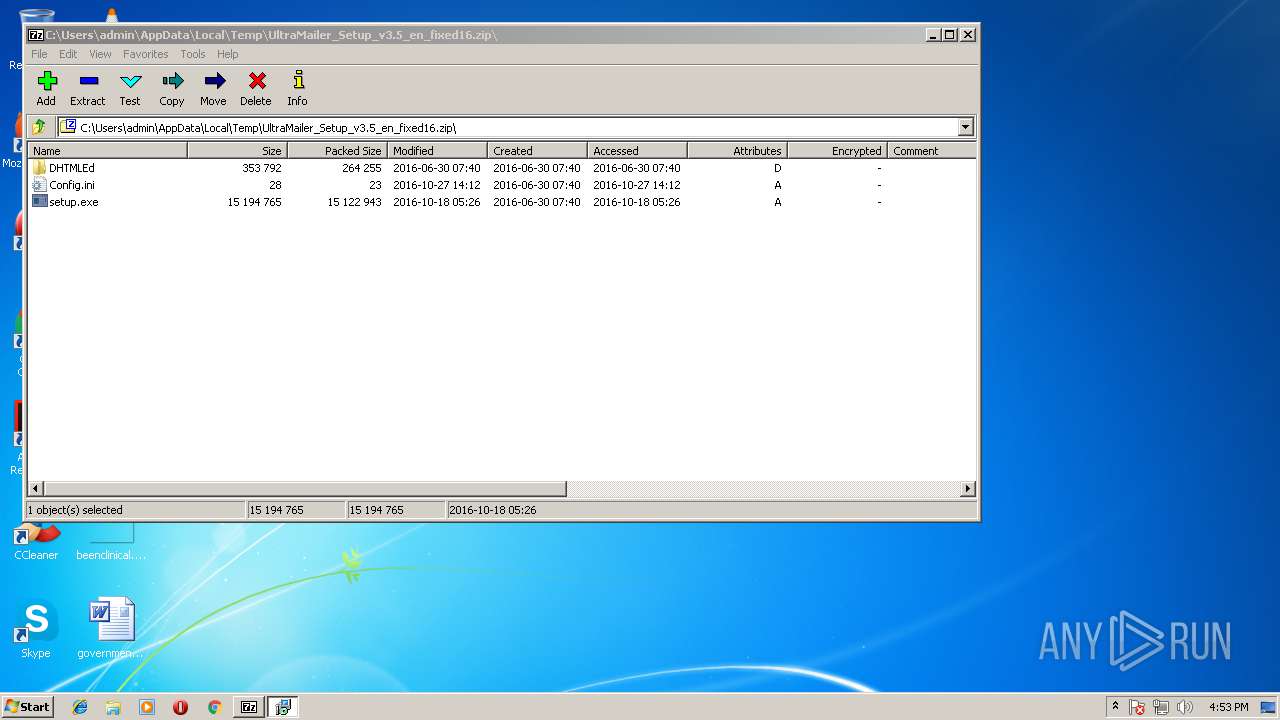
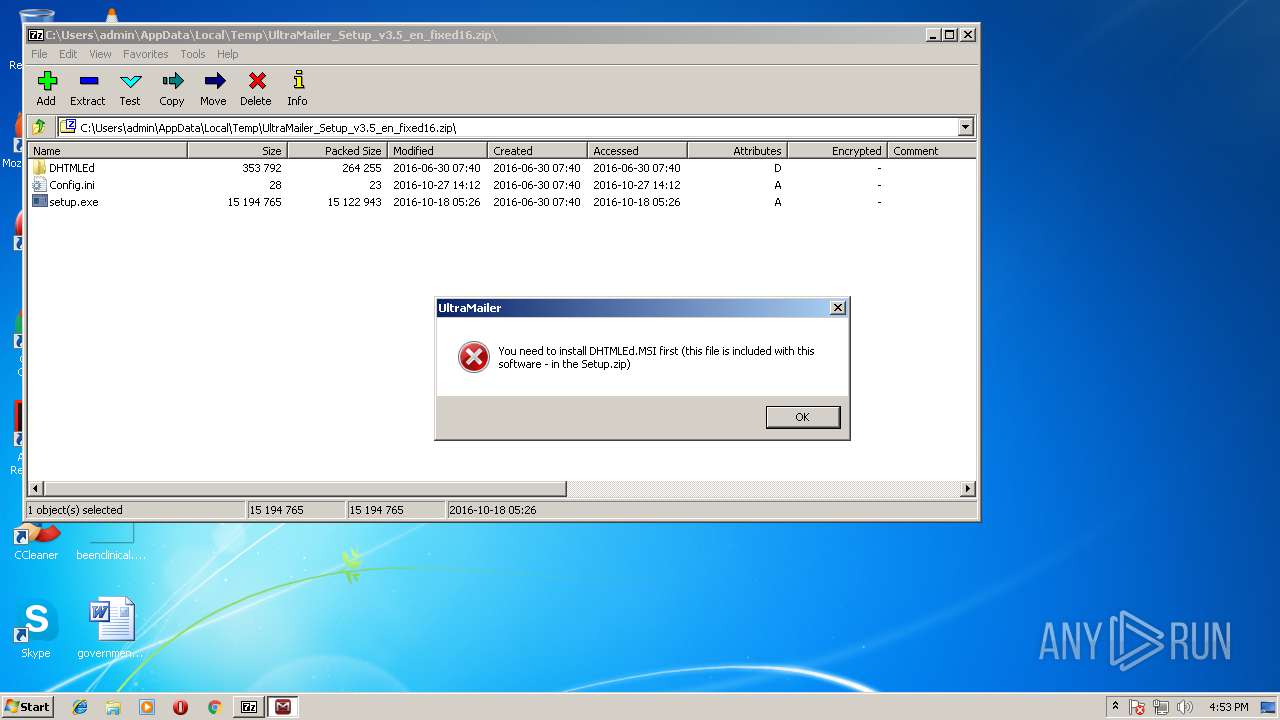
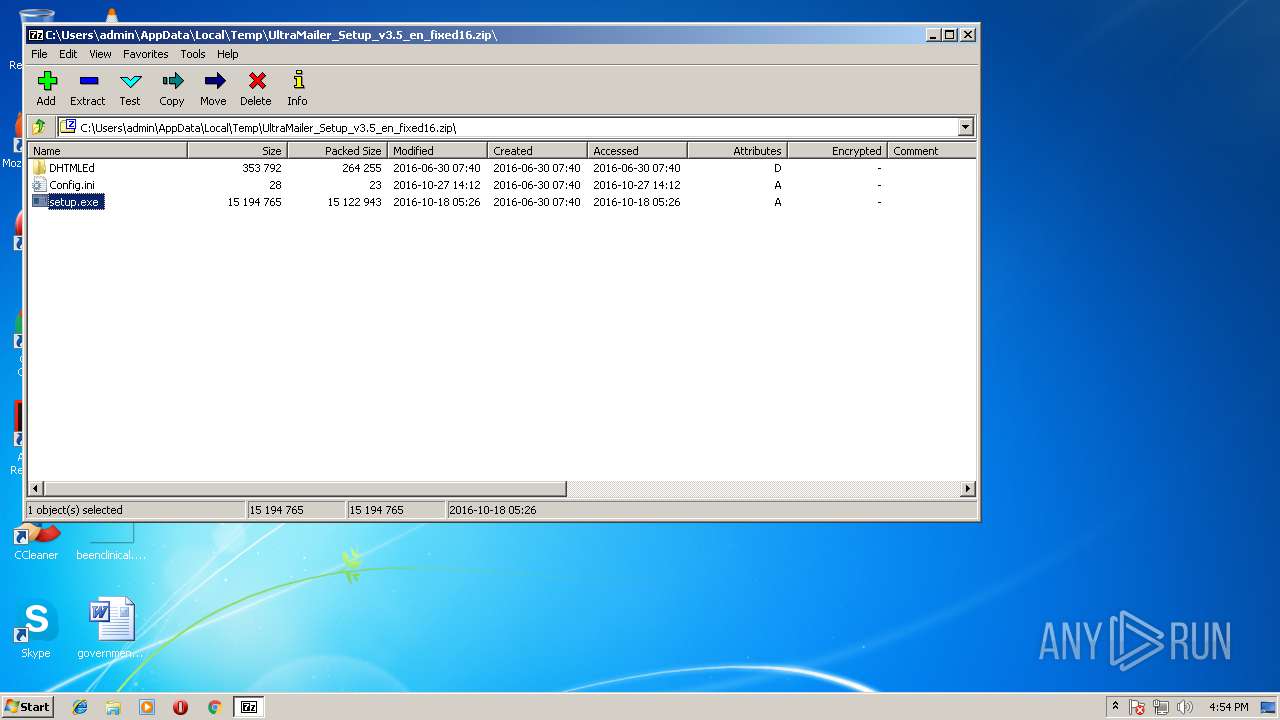
| File name: | UltraMailer_Setup_v3.5_en_fixed16.zip |
| Full analysis: | https://app.any.run/tasks/607b68d4-8c7d-453f-9646-8c7fc6ddfd55 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2018, 15:52:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7809B4A0BD8463C023372E51061378B6 |
| SHA1: | 0F82C2C7BACE443369411478C67DD5842E668C05 |
| SHA256: | 5E8AA83B6818D9685173597C1A50051E0DEB7EF4812F5EFF92B610A4DD9C8600 |
| SSDEEP: | 393216:sy0OryjV8f4489Vn+IsnFvZflmOn94nAqITJoeDoxhy9P05XN:syZiT48Dnjst9n9s7Ipb9w9 |
MALICIOUS
Application was dropped or rewritten from another process
- setup.exe (PID: 2580)
- setup.exe (PID: 3644)
- UltraMailerActiveX.exe (PID: 2016)
- Ultra Mailer.exe (PID: 888)
- Ultra Mailer.exe (PID: 3612)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1540)
- regsvr32.exe (PID: 1376)
- regsvr32.exe (PID: 2692)
- regsvr32.exe (PID: 4024)
- regsvr32.exe (PID: 2896)
- regsvr32.exe (PID: 2576)
- regsvr32.exe (PID: 3496)
- UltraMailerActiveX.exe (PID: 2016)
- regasm.exe (PID: 2188)
- regasm.exe (PID: 3292)
- regasm.exe (PID: 3888)
- regasm.exe (PID: 1524)
- Ultra Mailer.exe (PID: 888)
- Ultra Mailer.exe (PID: 3612)
Registers / Runs the DLL via REGSVR32.EXE
- setup.tmp (PID: 1220)
SUSPICIOUS
Executable content was dropped or overwritten
- 7zFM.exe (PID: 2676)
- setup.exe (PID: 3644)
- setup.tmp (PID: 1220)
- setup.exe (PID: 2580)
- msiexec.exe (PID: 3168)
Reads the Windows organization settings
- setup.tmp (PID: 1220)
Reads Windows owner settings
- setup.tmp (PID: 1220)
Creates COM task schedule object
- regsvr32.exe (PID: 2896)
- regsvr32.exe (PID: 2576)
- regasm.exe (PID: 3292)
- regasm.exe (PID: 1524)
- msiexec.exe (PID: 3168)
- regasm.exe (PID: 3888)
- regasm.exe (PID: 2188)
Creates files in the program directory
- regasm.exe (PID: 2188)
- regasm.exe (PID: 3292)
- regasm.exe (PID: 3888)
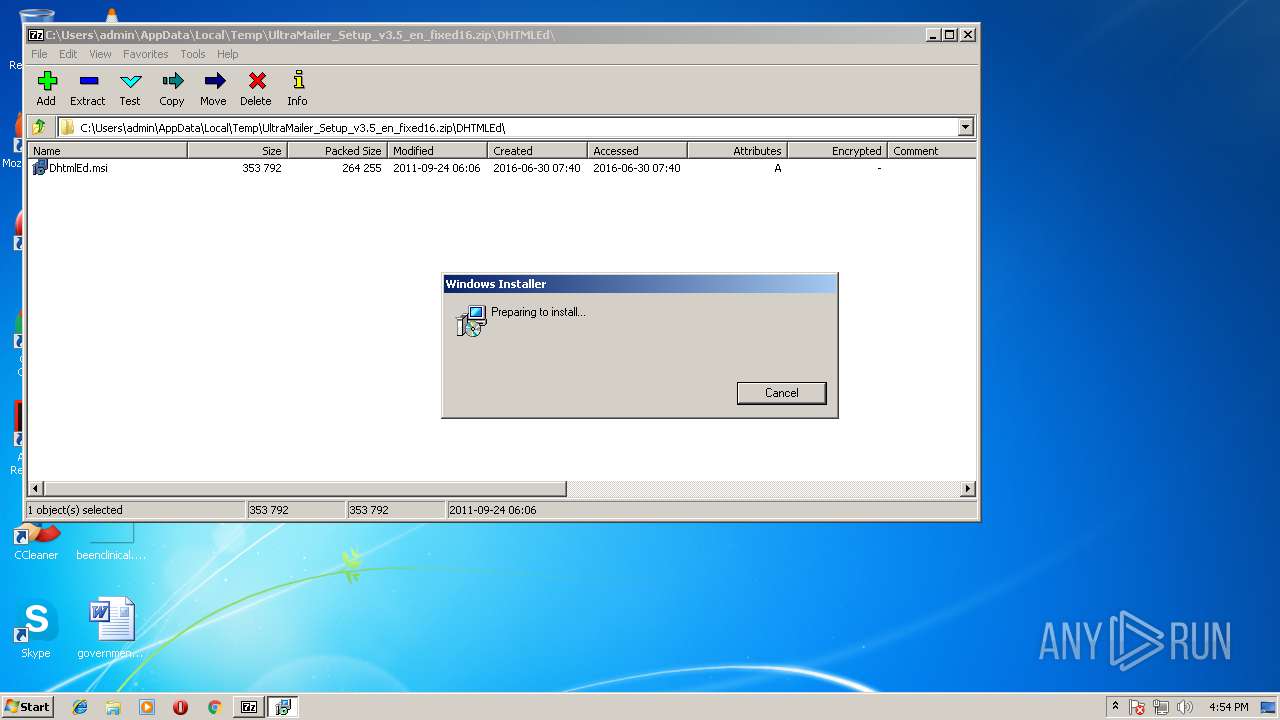
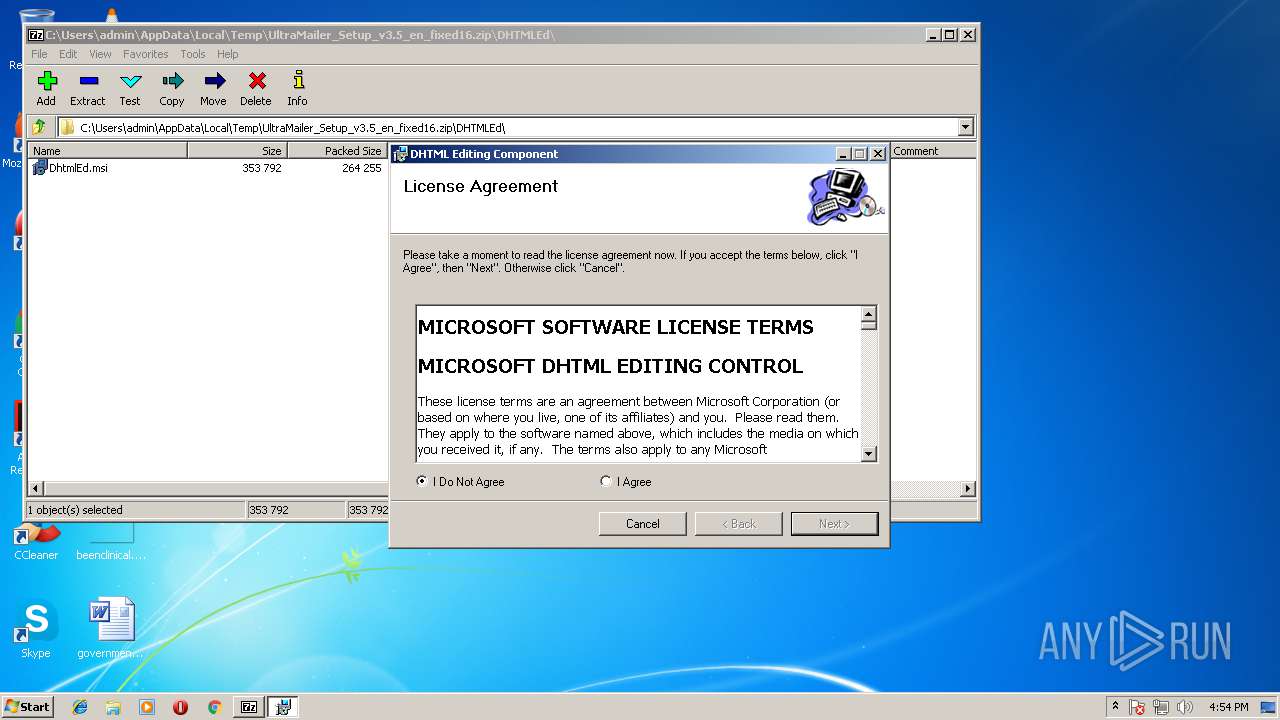
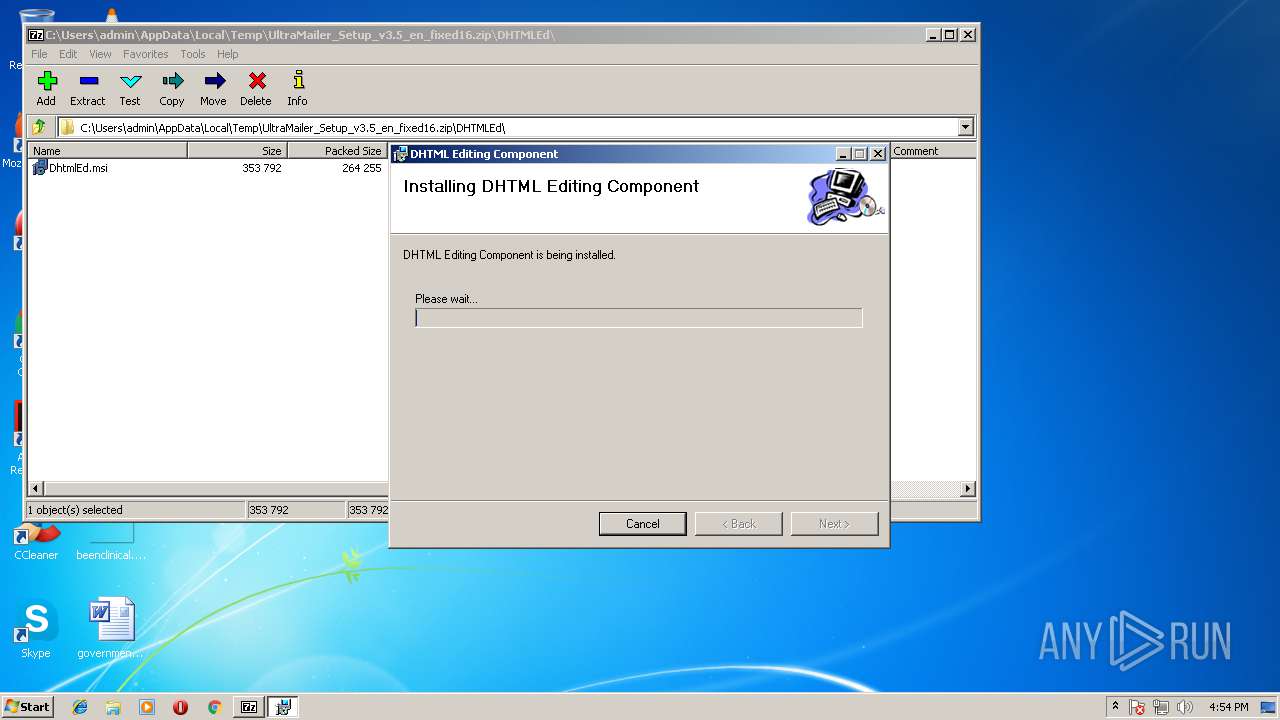
Starts Microsoft Installer
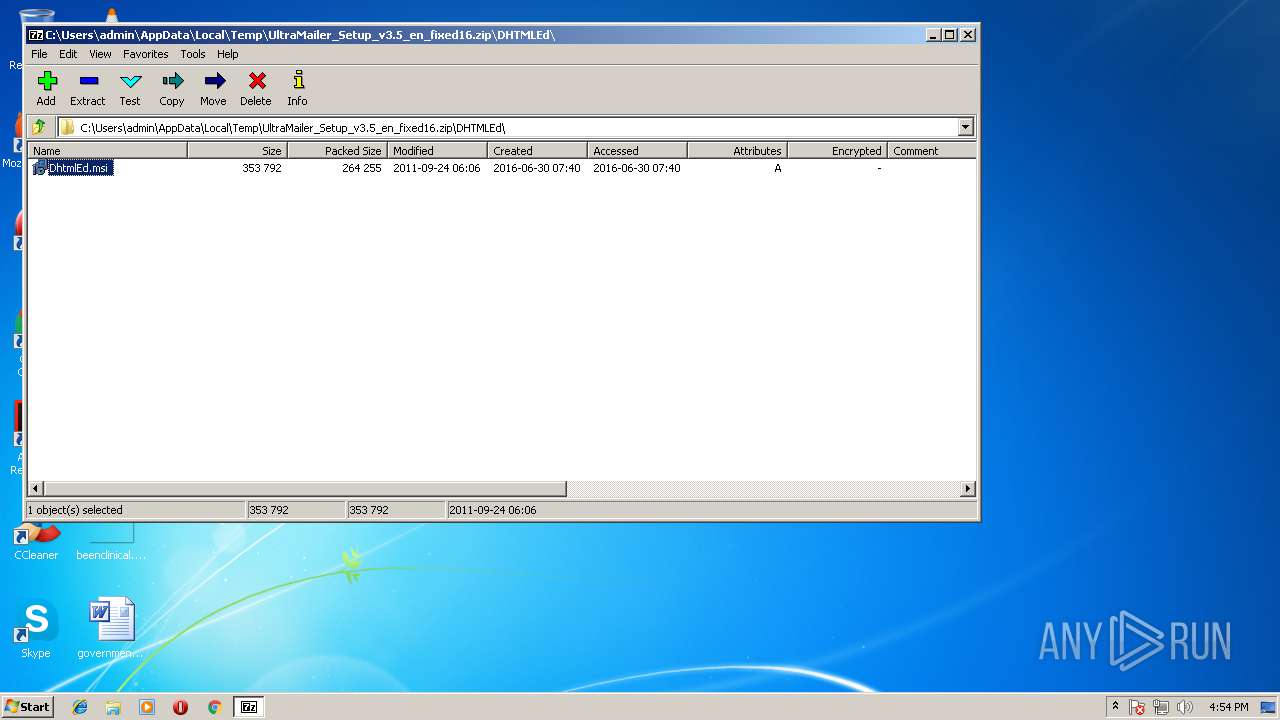
- 7zFM.exe (PID: 2676)
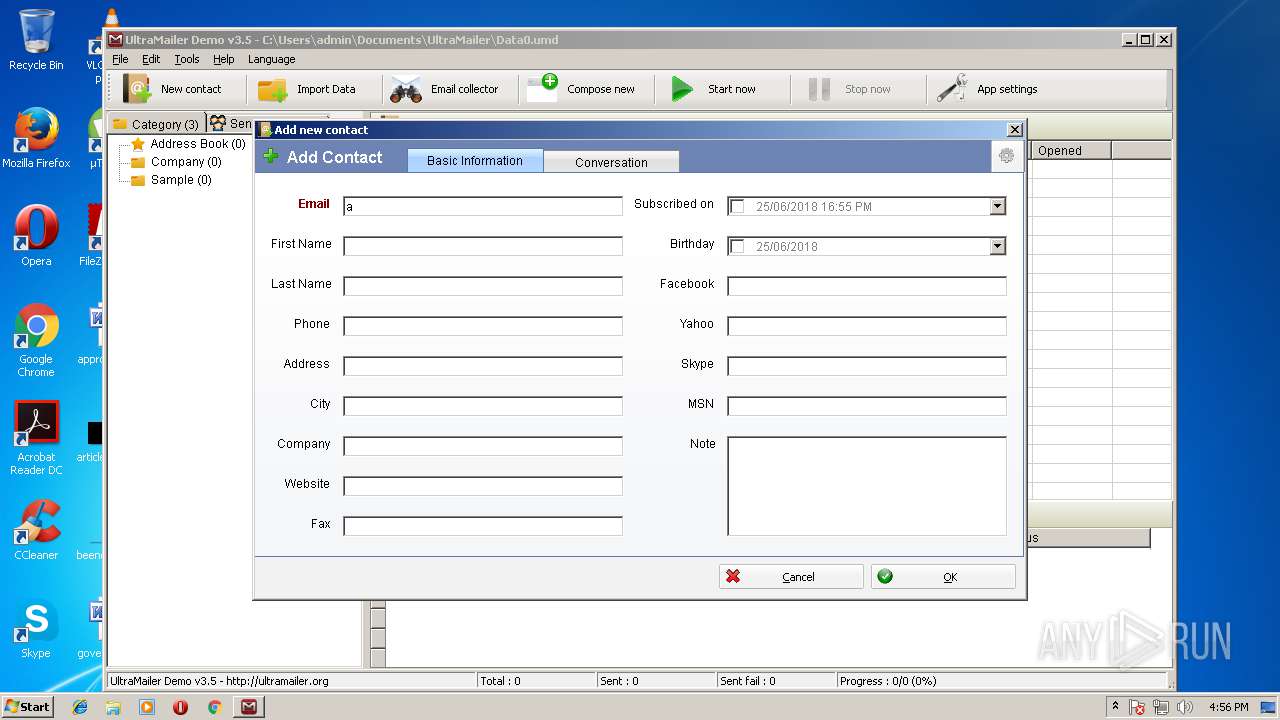
Creates files in the user directory
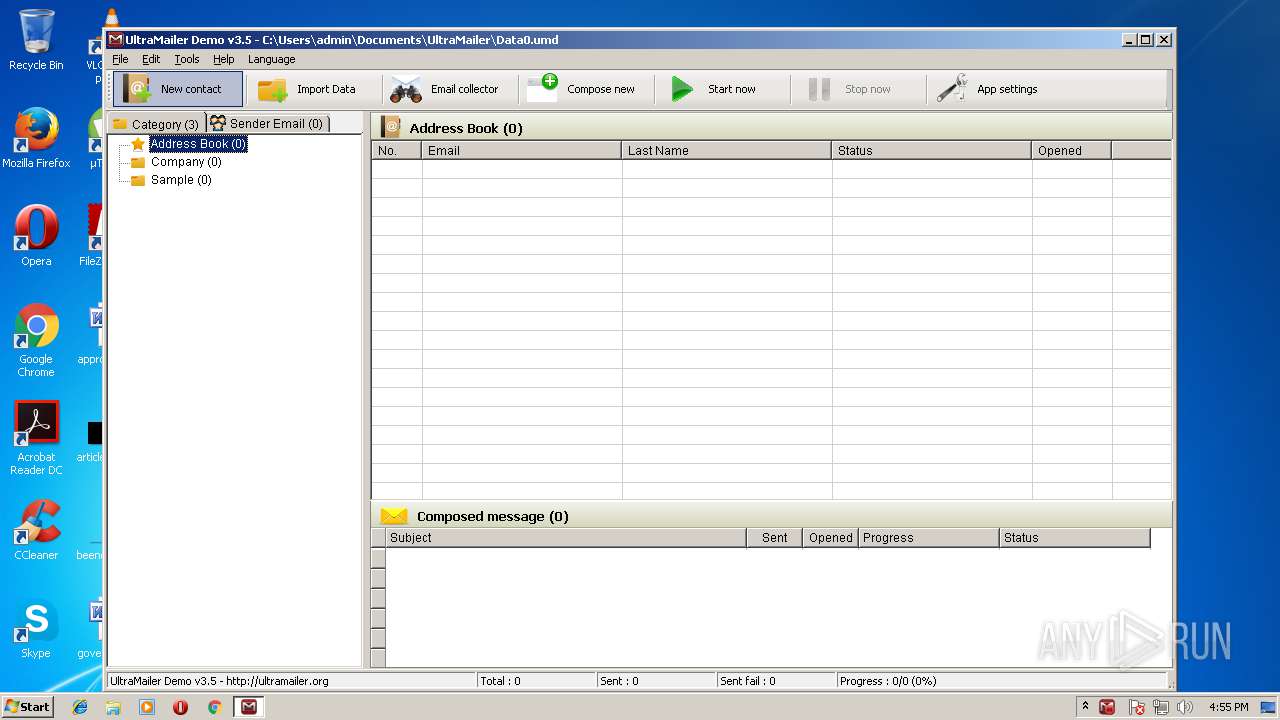
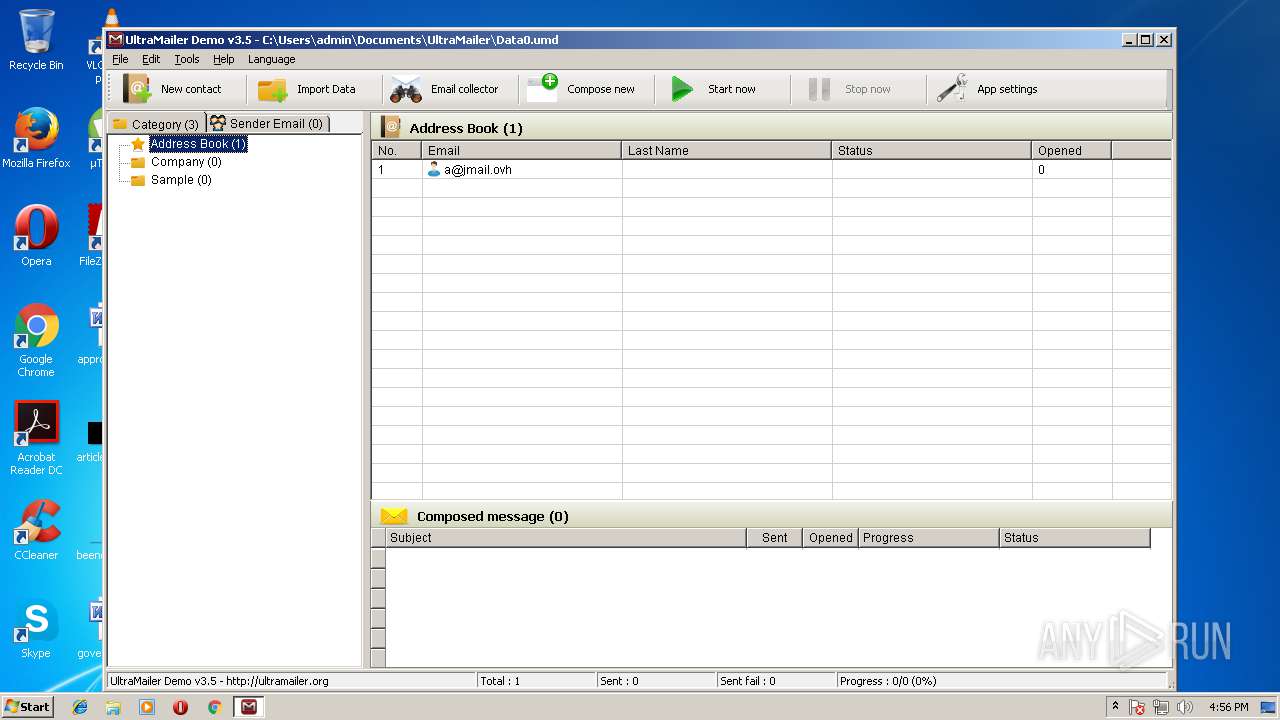
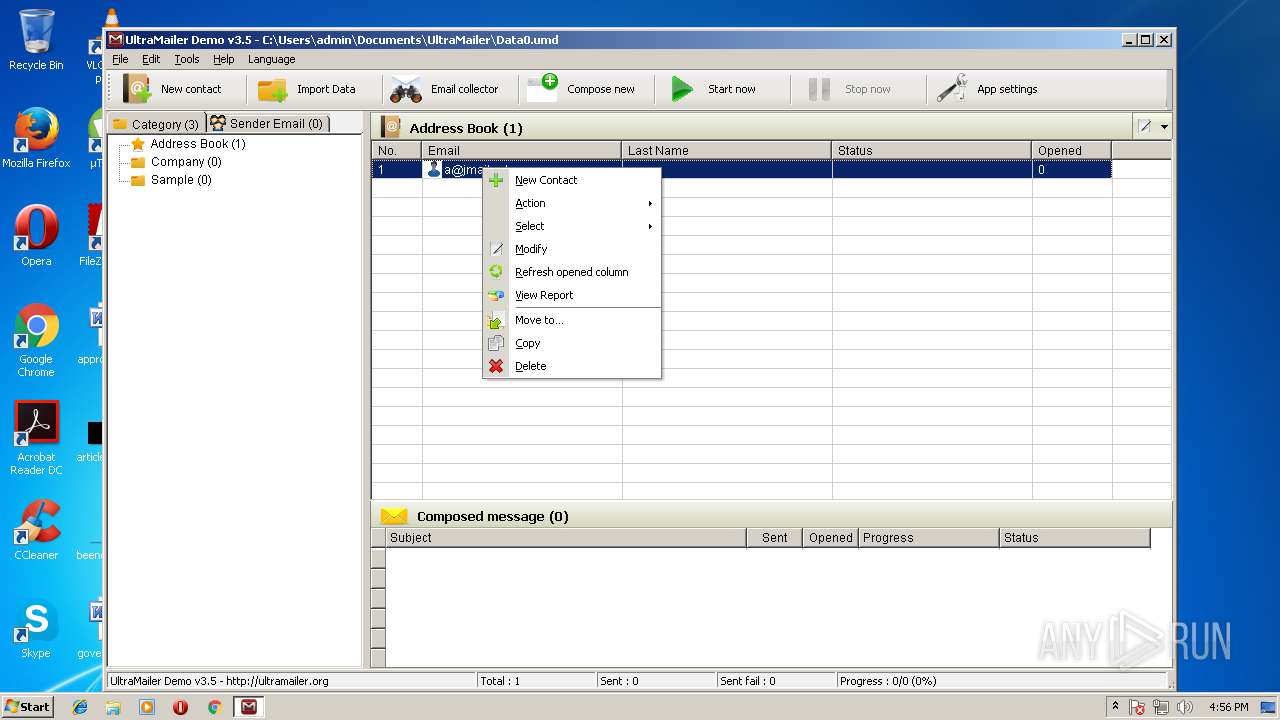
- Ultra Mailer.exe (PID: 3612)
Reads Internet Cache Settings
- Ultra Mailer.exe (PID: 3612)
Reads internet explorer settings
- Ultra Mailer.exe (PID: 3612)
Application launched itself
- software_reporter_tool.exe (PID: 2856)
INFO
Application was dropped or rewritten from another process
- setup.tmp (PID: 1220)
- setup.tmp (PID: 2312)
Loads dropped or rewritten executable
- setup.tmp (PID: 1220)
Creates a software uninstall entry
- setup.tmp (PID: 1220)
- msiexec.exe (PID: 3168)
Dropped object may contain URL's
- 7zFM.exe (PID: 2676)
- msiexec.exe (PID: 3168)
- setup.tmp (PID: 1220)
- Ultra Mailer.exe (PID: 3612)
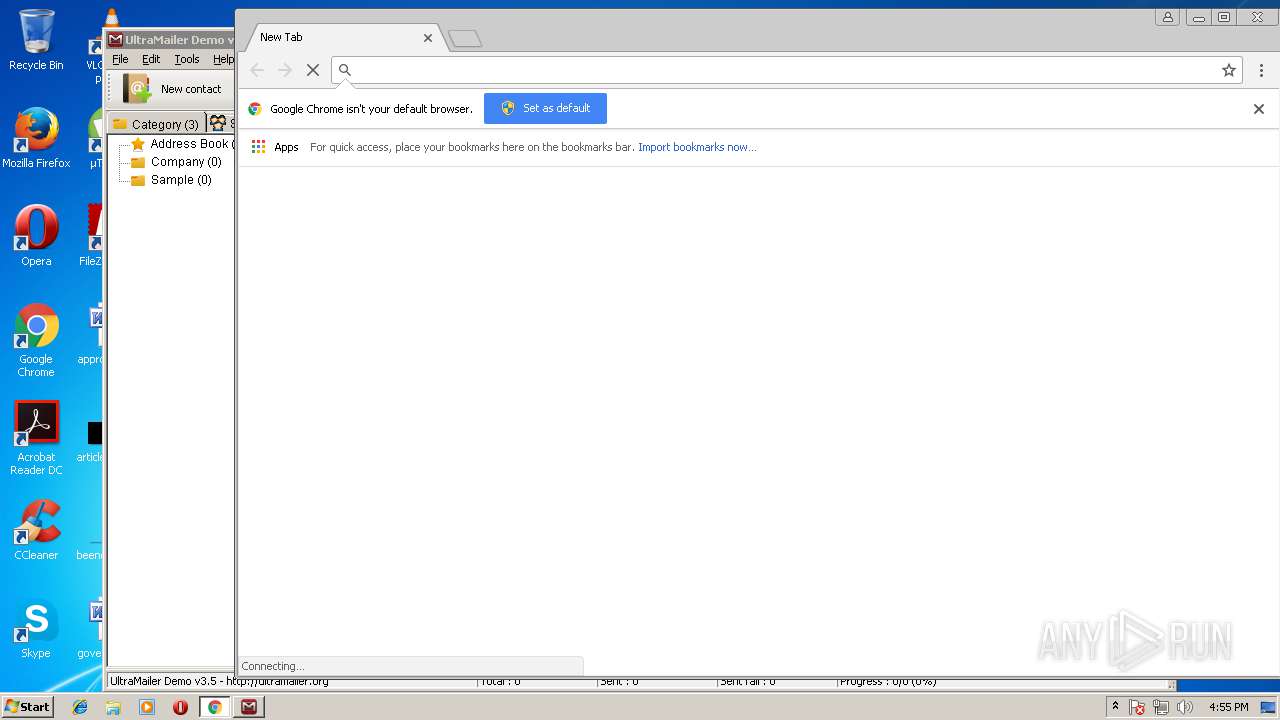
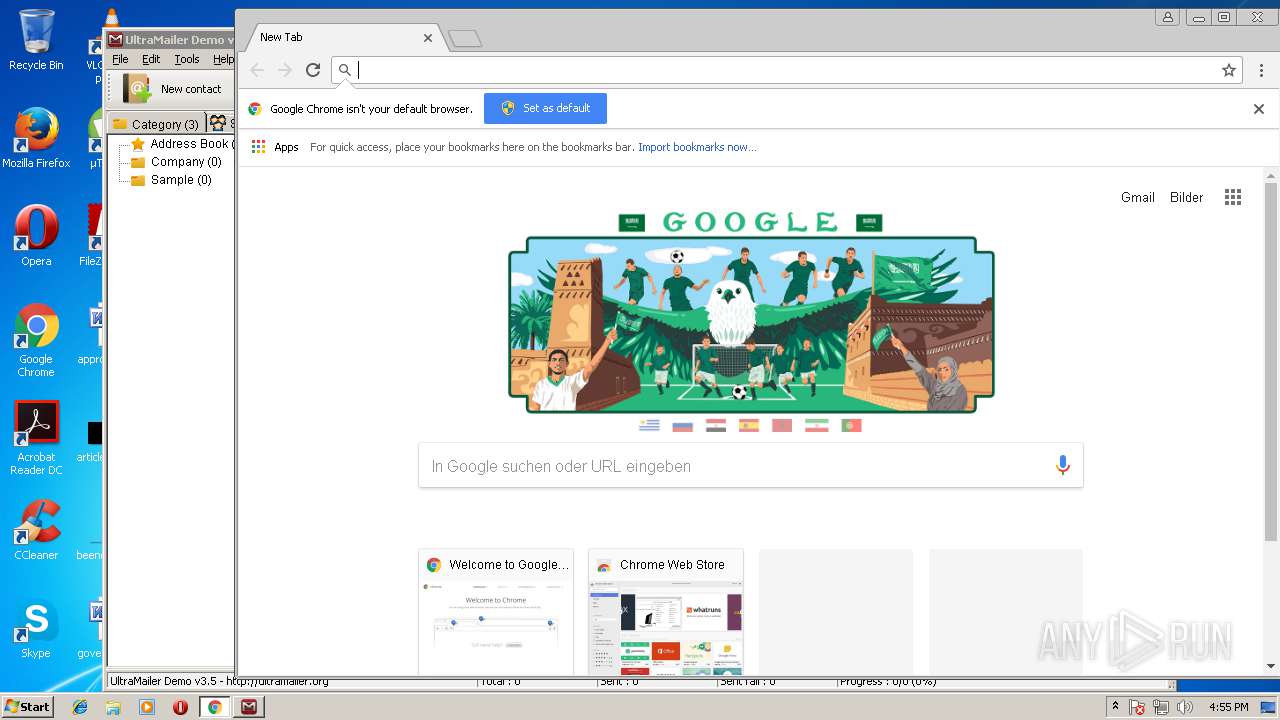
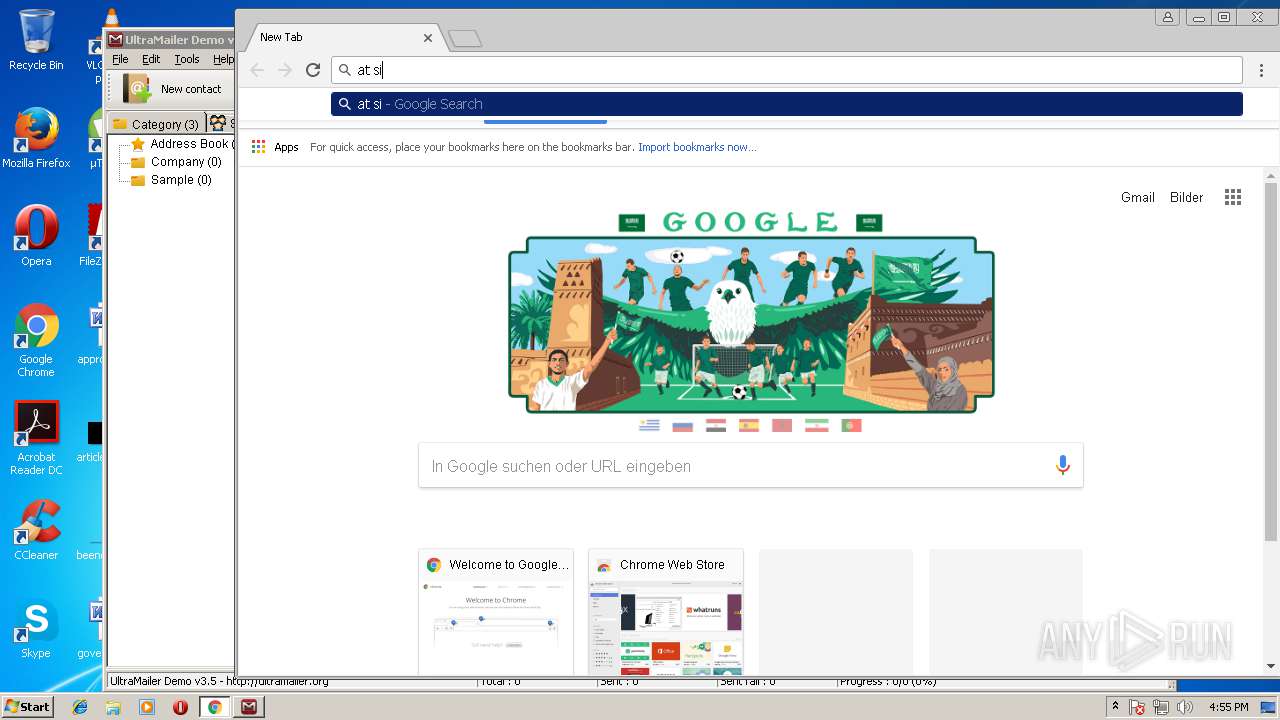
- chrome.exe (PID: 1388)
Creates or modifies windows services
- msiexec.exe (PID: 3168)
- vssvc.exe (PID: 3532)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3532)
Dropped object may contain Bitcoin addresses
- setup.tmp (PID: 1220)
Creates files in the program directory
- msiexec.exe (PID: 3168)
- setup.tmp (PID: 1220)
Application launched itself
- chrome.exe (PID: 1388)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 2856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2016:10:18 11:26:15 |
| ZipCRC: | 0x83a52f90 |
| ZipCompressedSize: | 15122943 |
| ZipUncompressedSize: | 15194765 |
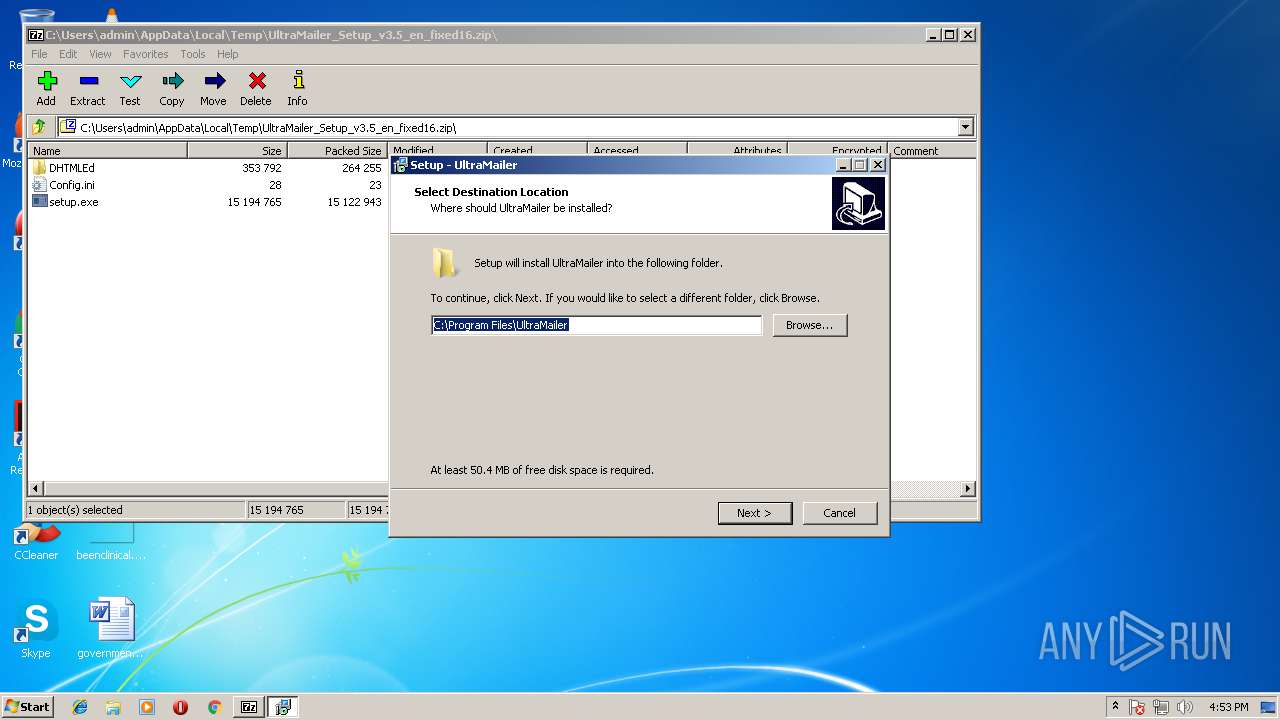
| ZipFileName: | setup.exe |
Total processes
76
Monitored processes
31
Malicious processes
12
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1588,16314126072747967548,8602994449583200051,131072 --service-pipe-token=B90664C3C737DB933E90954F911D69C8 --lang=en-US --extension-process --disable-client-side-phishing-detection --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=B90664C3C737DB933E90954F911D69C8 --renderer-client-id=2 --mojo-platform-channel-handle=1756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
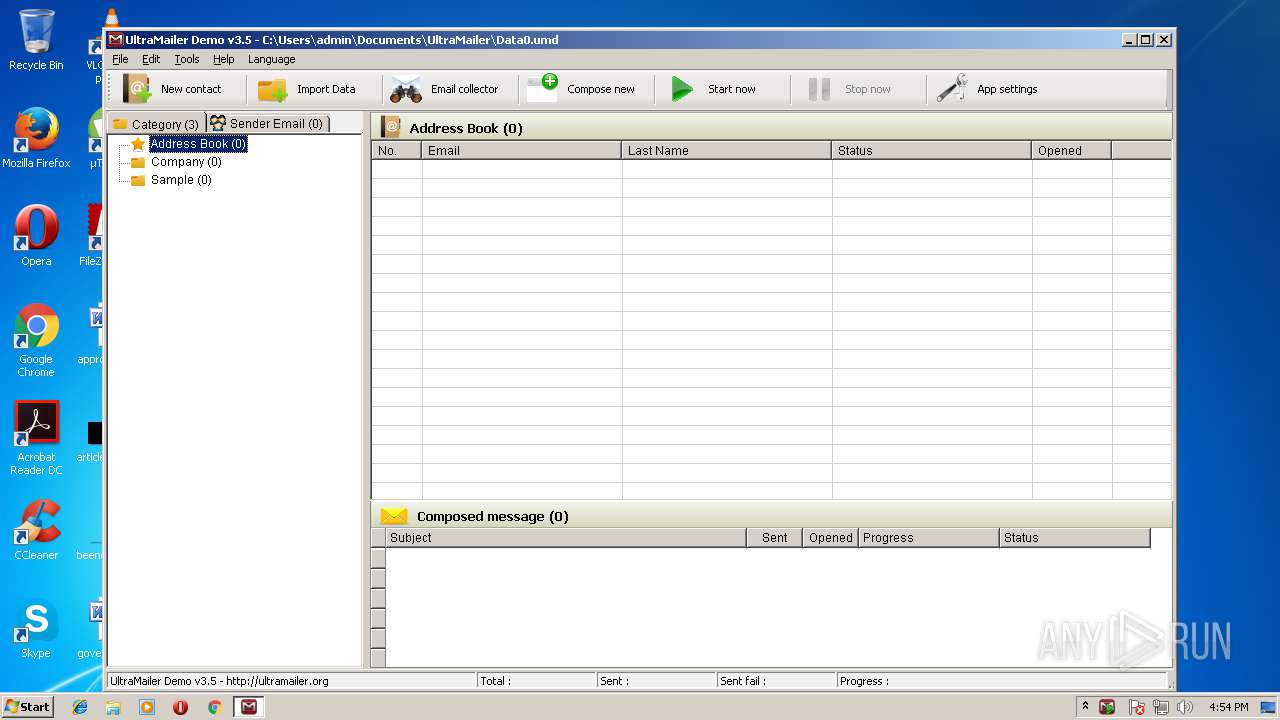
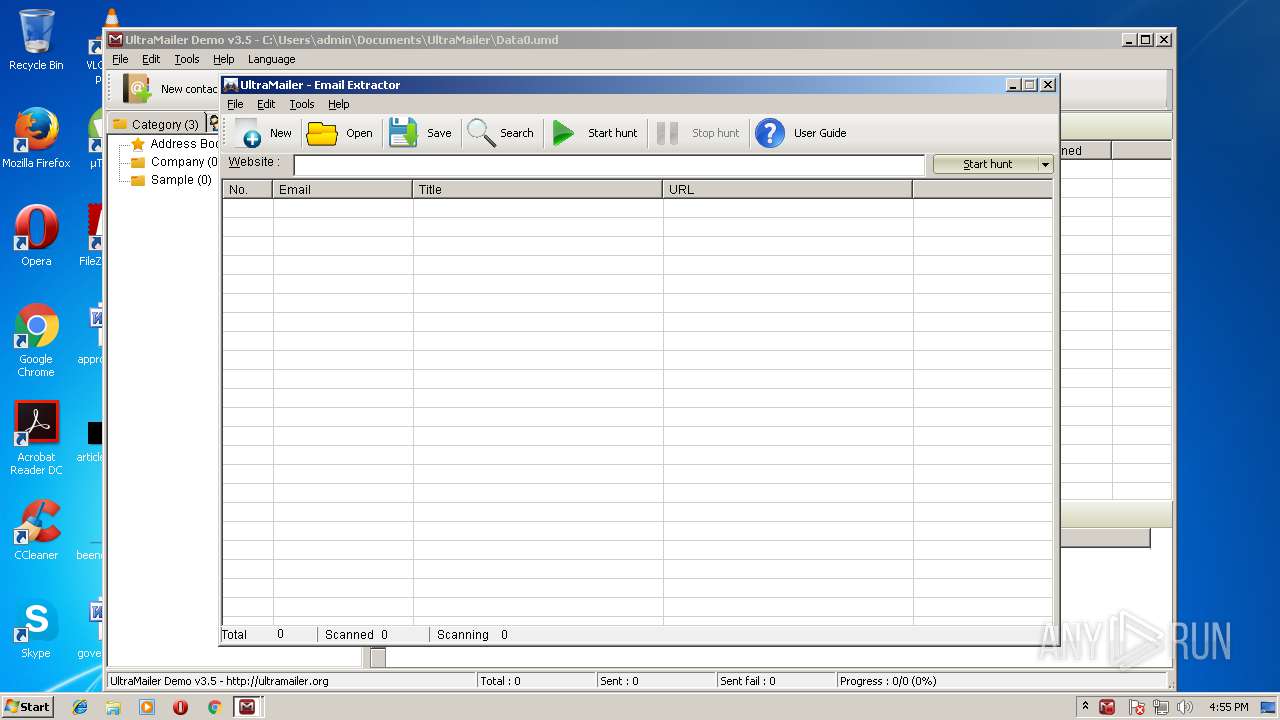
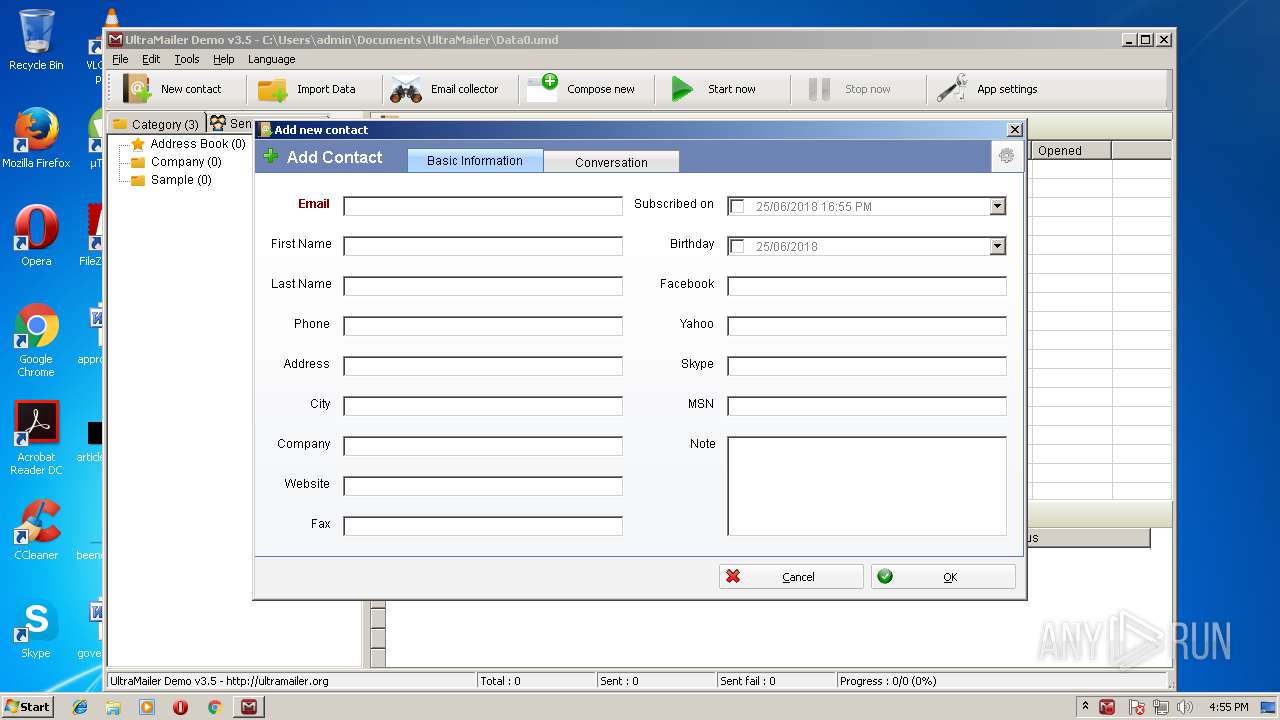
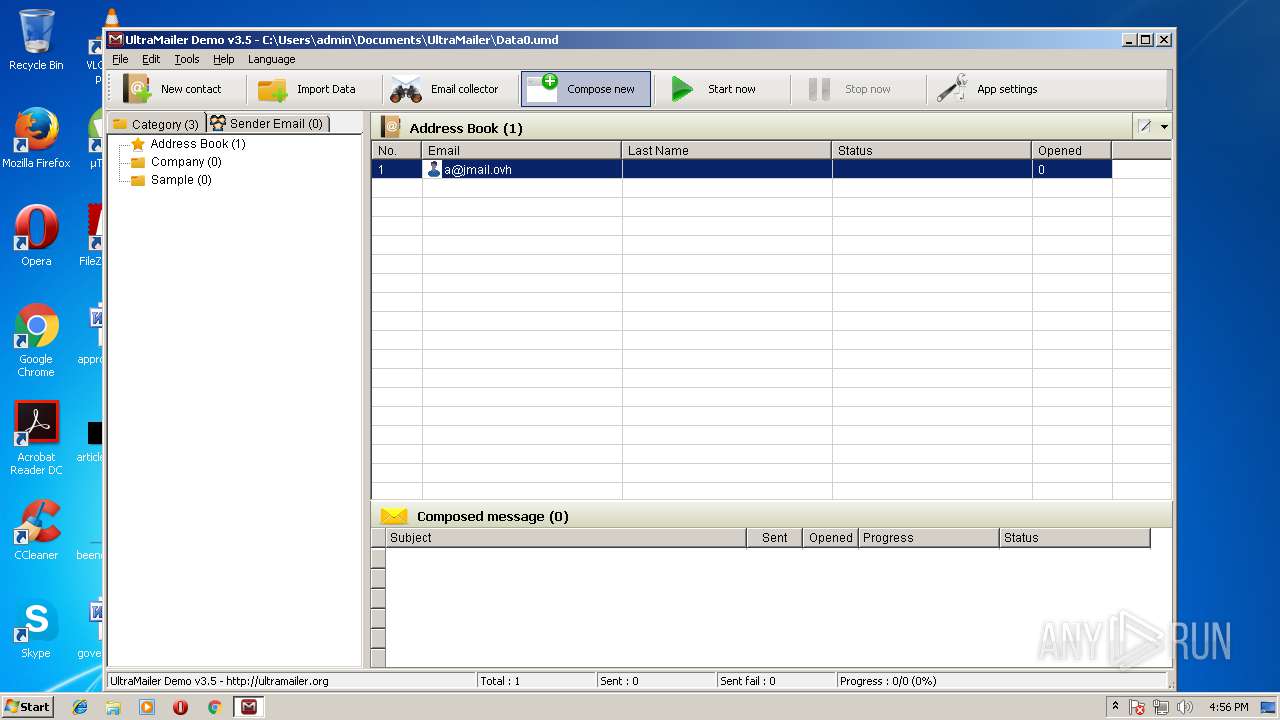
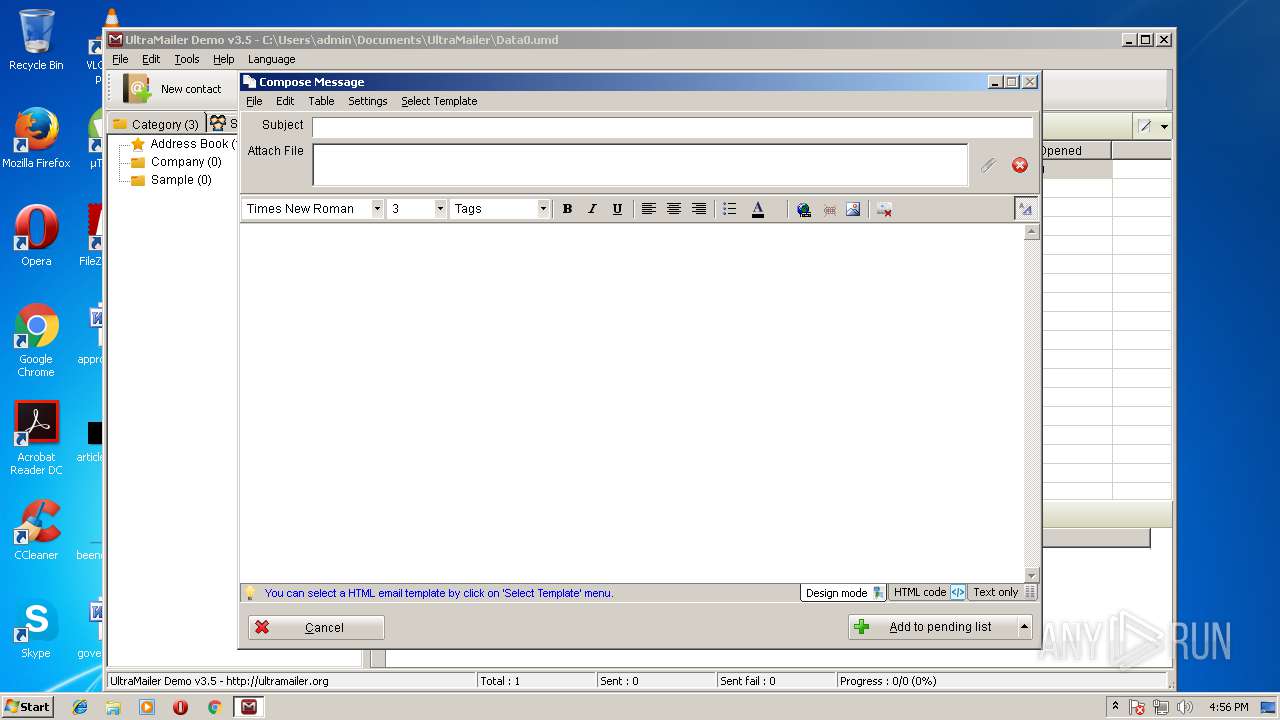
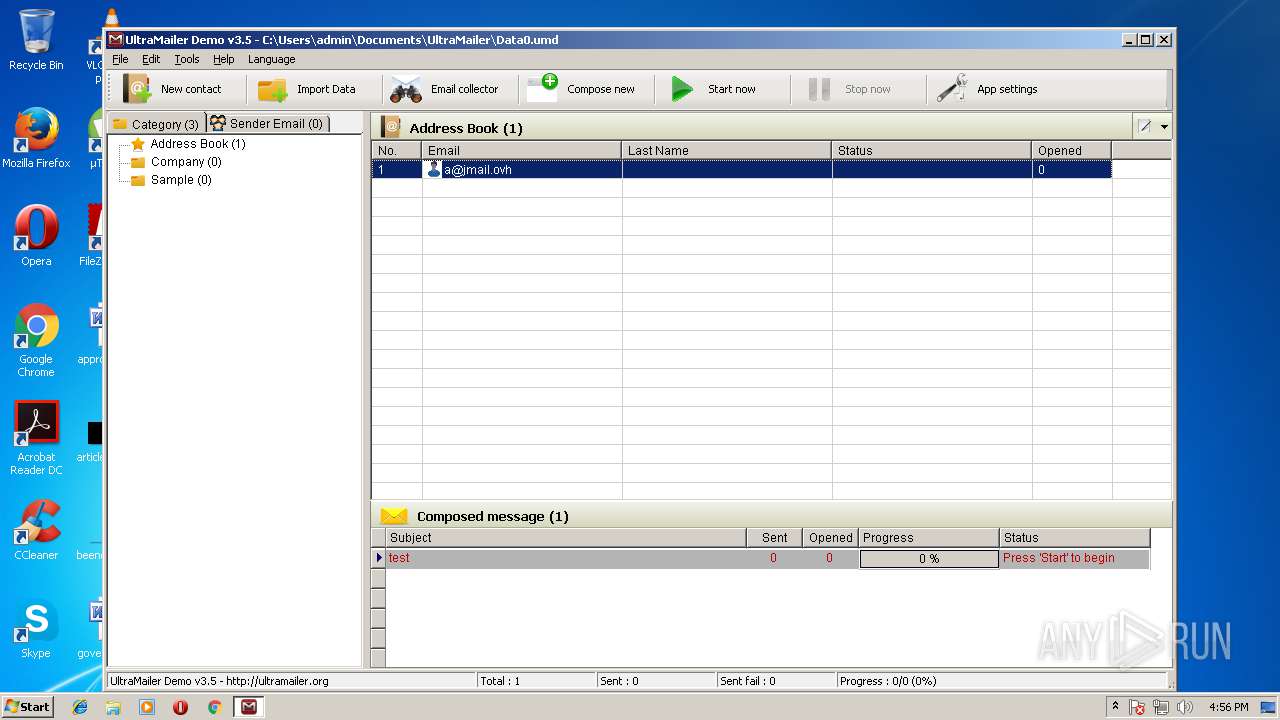
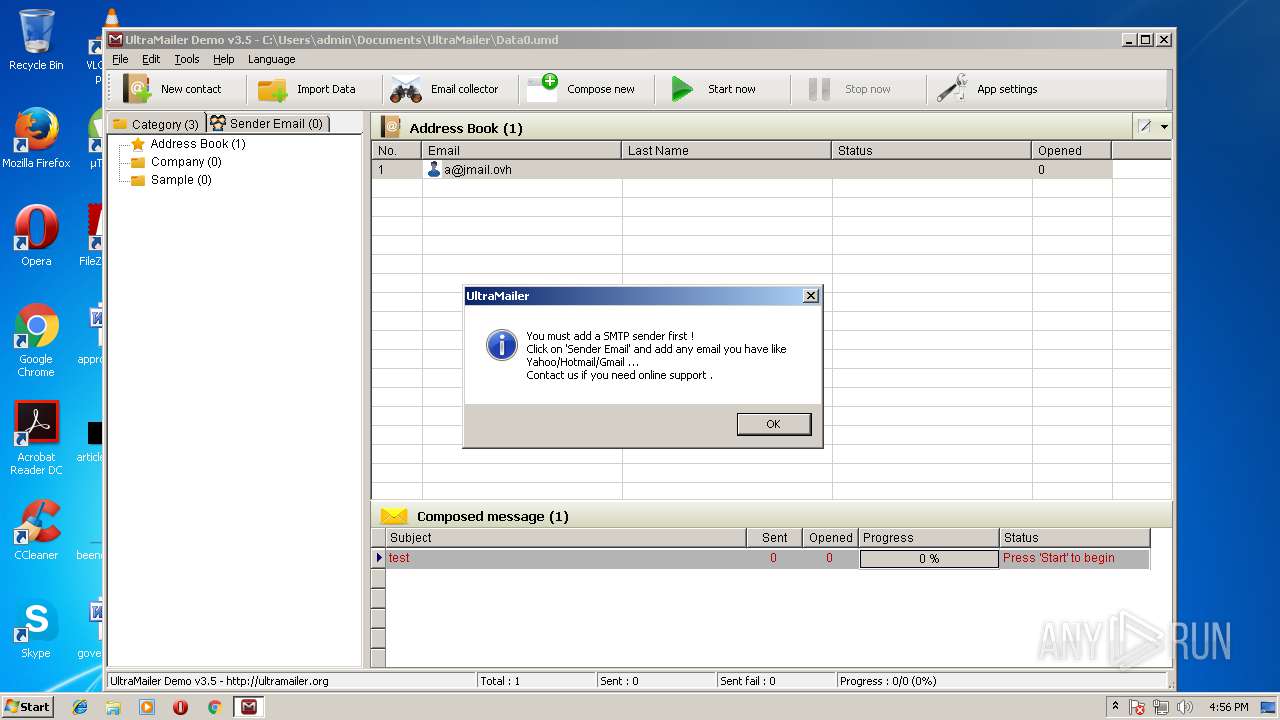
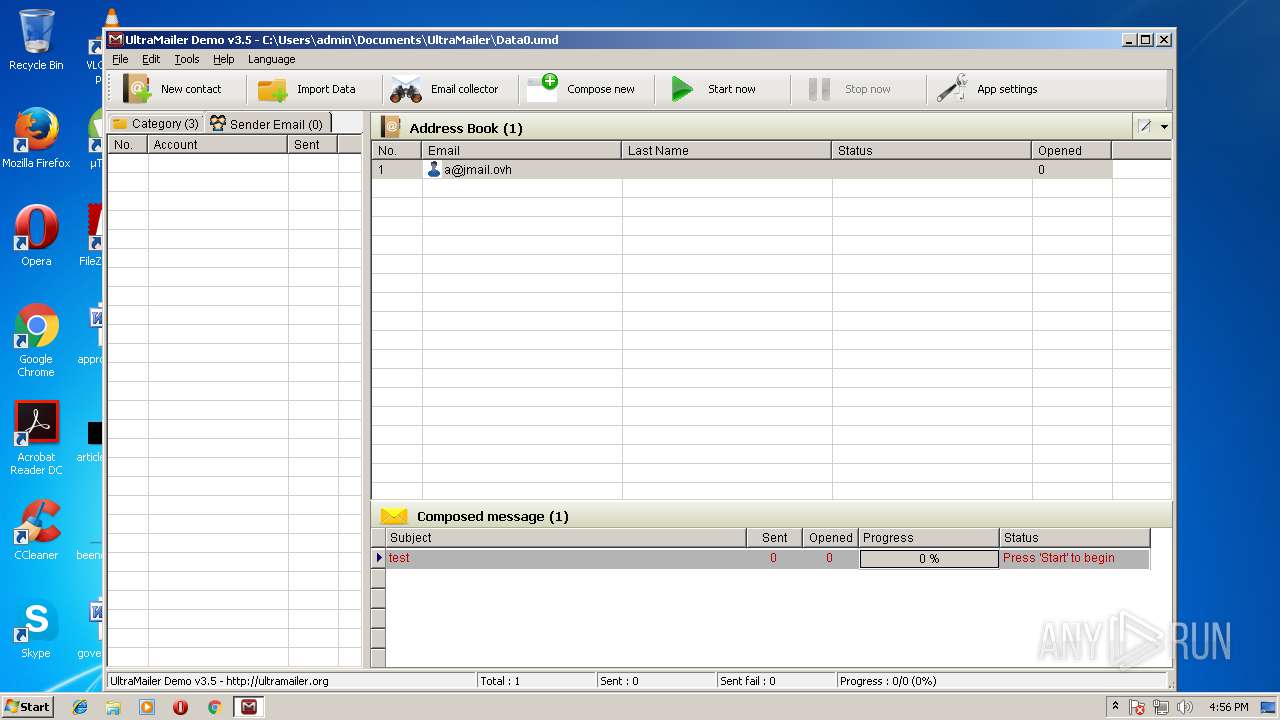
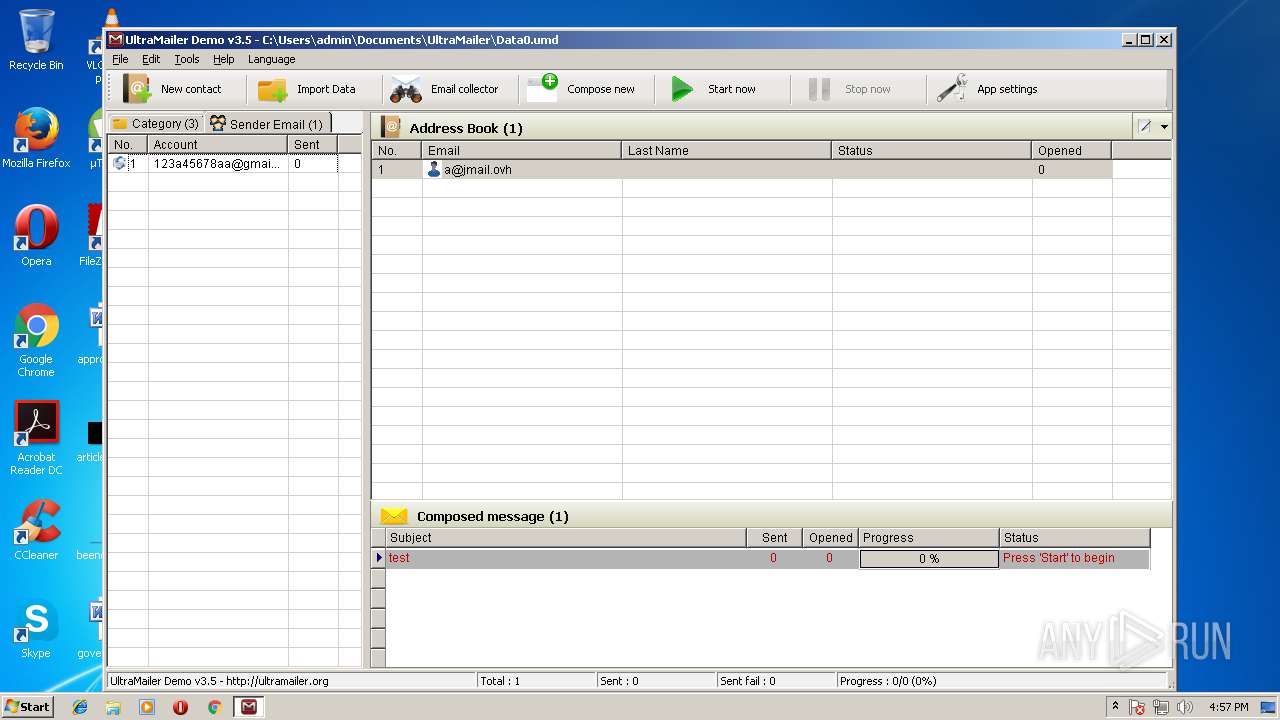
| 888 | "C:\Program Files\UltraMailer\Ultra Mailer.exe" | C:\Program Files\UltraMailer\Ultra Mailer.exe | — | setup.tmp | |||||||||||
User: admin Company: UltraSoft Coporation Integrity Level: MEDIUM Description: http://ultramailer.org Exit code: 0 Version: 2.08 Modules
| |||||||||||||||
| 1220 | "C:\Users\admin\AppData\Local\Temp\is-RVCSA.tmp\setup.tmp" /SL5="$D01F2,14772106,121344,C:\Users\admin\AppData\Local\Temp\7zO47AD53EA\setup.exe" /SPAWNWND=$D01C0 /NOTIFYWND=$B024C | C:\Users\admin\AppData\Local\Temp\is-RVCSA.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1376 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\UltraMailer\UnicodeFullControl.ocx" | C:\Windows\system32\regsvr32.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1588,16314126072747967548,8602994449583200051,131072 --service-pipe-token=5D727FCCD46BEE3DEACB1C86748FC90E --lang=en-US --disable-client-side-phishing-detection --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --enable-pinch --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --content-image-texture-target=0,0,3553;0,1,3553;0,2,3553;0,3,3553;0,4,3553;0,5,3553;0,6,3553;0,7,3553;0,8,3553;0,9,3553;0,10,3553;0,11,3553;0,12,3553;0,13,3553;0,14,3553;0,15,3553;0,16,3553;0,17,3553;1,0,3553;1,1,3553;1,2,3553;1,3,3553;1,4,3553;1,5,3553;1,6,3553;1,7,3553;1,8,3553;1,9,3553;1,10,3553;1,11,3553;1,12,3553;1,13,3553;1,14,3553;1,15,3553;1,16,3553;1,17,3553;2,0,3553;2,1,3553;2,2,3553;2,3,3553;2,4,3553;2,5,3553;2,6,3553;2,7,3553;2,8,3553;2,9,3553;2,10,3553;2,11,3553;2,12,3553;2,13,3553;2,14,3553;2,15,3553;2,16,3553;2,17,3553;3,0,3553;3,1,3553;3,2,3553;3,3,3553;3,4,3553;3,5,3553;3,6,3553;3,7,3553;3,8,3553;3,9,3553;3,10,3553;3,11,3553;3,12,3553;3,13,3553;3,14,3553;3,15,3553;3,16,3553;3,17,3553;4,0,3553;4,1,3553;4,2,3553;4,3,3553;4,4,3553;4,5,3553;4,6,3553;4,7,3553;4,8,3553;4,9,3553;4,10,3553;4,11,3553;4,12,3553;4,13,3553;4,14,3553;4,15,3553;4,16,3553;4,17,3553 --disable-accelerated-video-decode --disable-gpu-compositing --enable-gpu-async-worker-context --service-request-channel-token=5D727FCCD46BEE3DEACB1C86748FC90E --renderer-client-id=4 --mojo-platform-channel-handle=1600 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 61.0.3163.100 Modules
| |||||||||||||||
| 1524 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe" "C:\Program Files\UltraMailer\DFunction.dll" /tlb | C:\Windows\Microsoft.NET\Framework\v2.0.50727\regasm.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1540 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\UltraMailer\HookMenu.ocx" | C:\Windows\system32\regsvr32.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2016 | "C:\Program Files\UltraMailer\ActiveX\UltraMailerActiveX.exe" /regserver | C:\Program Files\UltraMailer\ActiveX\UltraMailerActiveX.exe | — | setup.tmp | |||||||||||
User: admin Company: UltraMailer Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2176 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\UltraMailer\MSCOMCTL.OCX" | C:\Windows\system32\regsvr32.exe | — | setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
11 777
Read events
3 415
Write events
8 271
Delete events
91
Modification events
| (PID) Process: | (2676) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2676) 7zFM.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: C404000006E4BFA99C0CD401 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: E6306886252352F0441845F12A509ECC2680404CEC1F0A5389F6E095F58BE118 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\UltraMailer\Ultra Mailer.exe | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 9C161363AFD209904592A9EFB7307B0337F808AD3DAF923EEFC7124025525B21 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\UltraMailer\COMCTL32.OCX |
Value: 2 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\UltraMailer\HookMenu.ocx |
Value: 2 | |||
| (PID) Process: | (1220) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\UltraMailer\MSCOMCTL.OCX |
Value: 2 | |||
Executable files
42
Suspicious files
53
Text files
1 210
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-A0P88.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-O39HC.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-ETK88.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-9NG8T.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-JU4JE.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-V8RCA.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-AQAU0.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-9QL0M.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-9QT1E.tmp | — | |
MD5:— | SHA256:— | |||
| 1220 | setup.tmp | C:\Program Files\UltraMailer\is-VGP5D.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
18
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3612 | Ultra Mailer.exe | GET | 200 | 123.30.240.133:80 | http://functions.ultramailer.org/license_check/InitAPIKey.asp?APIKey=rgh6vsww0&APIPass=gl27fmjcm | VN | — | — | suspicious |
3612 | Ultra Mailer.exe | GET | 200 | 123.30.240.133:80 | http://functions.ultramailer.org/license_check/InitAPIKey.asp?APIKey=fouzcxb3m&APIPass=6s8rhoijx | VN | — | — | suspicious |
3612 | Ultra Mailer.exe | GET | 200 | 123.30.240.133:80 | http://functions.ultramailer.org/license_check/InitAPIKey.asp?APIKey=tl2lsxgnm&APIPass=0298q85qw | VN | — | — | suspicious |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/portal.css | VN | text | 5.94 Kb | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/skin.css | VN | text | 7.02 Kb | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/images/HBTong.css | VN | text | 7.89 Kb | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/images/Right.gif | VN | image | 70 b | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/images/Left.gif | VN | image | 83 b | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/images/HeadLeft.gif | VN | image | 266 b | unknown |
3612 | Ultra Mailer.exe | GET | 200 | 27.0.12.43:80 | http://phanmemguimailhangloat.com/Default.aspx_files/images/Bottom.gif | VN | image | 59 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3612 | Ultra Mailer.exe | 123.30.240.133:80 | functions.ultramailer.org | VNPT Corp | VN | suspicious |
3612 | Ultra Mailer.exe | 27.0.12.43:80 | phanmemguimailhangloat.com | SUPERDATA | VN | unknown |
1388 | chrome.exe | 216.58.206.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.22.14:443 | apis.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 216.58.205.227:443 | id.google.ru | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.23.131:443 | id.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
1388 | chrome.exe | 172.217.22.34:443 | adservice.google.ru | Google Inc. | US | whitelisted |
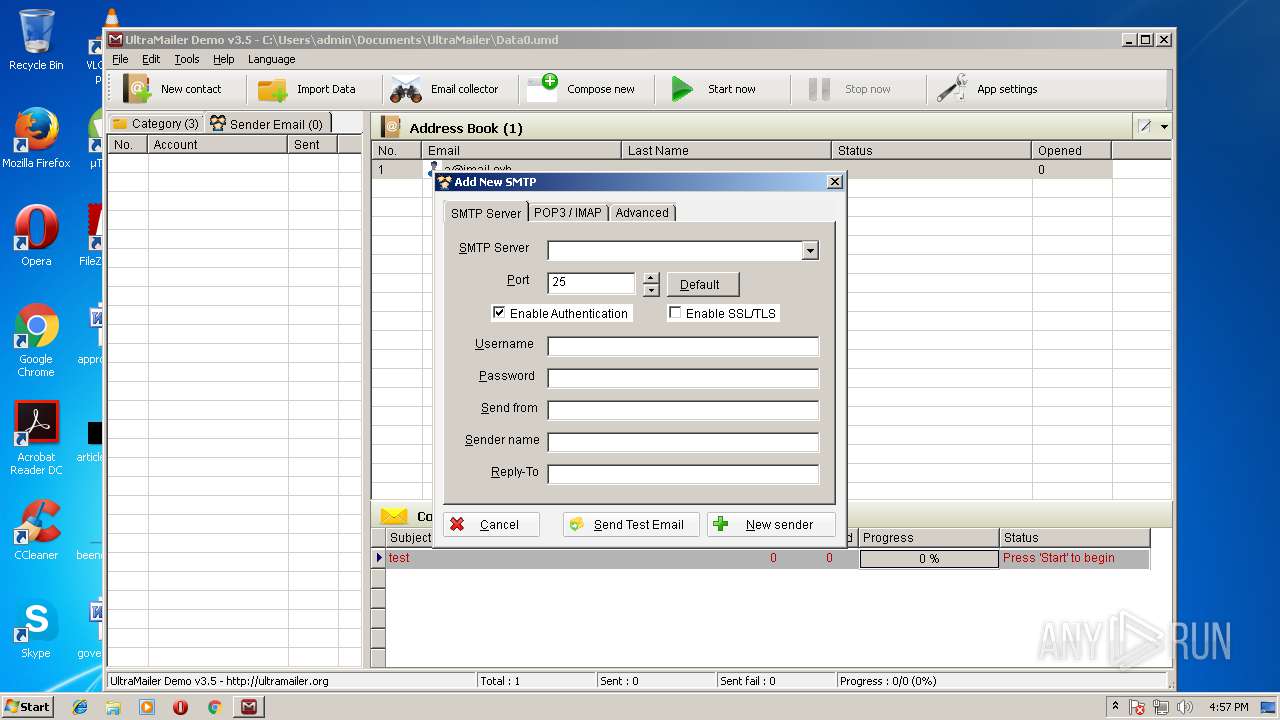
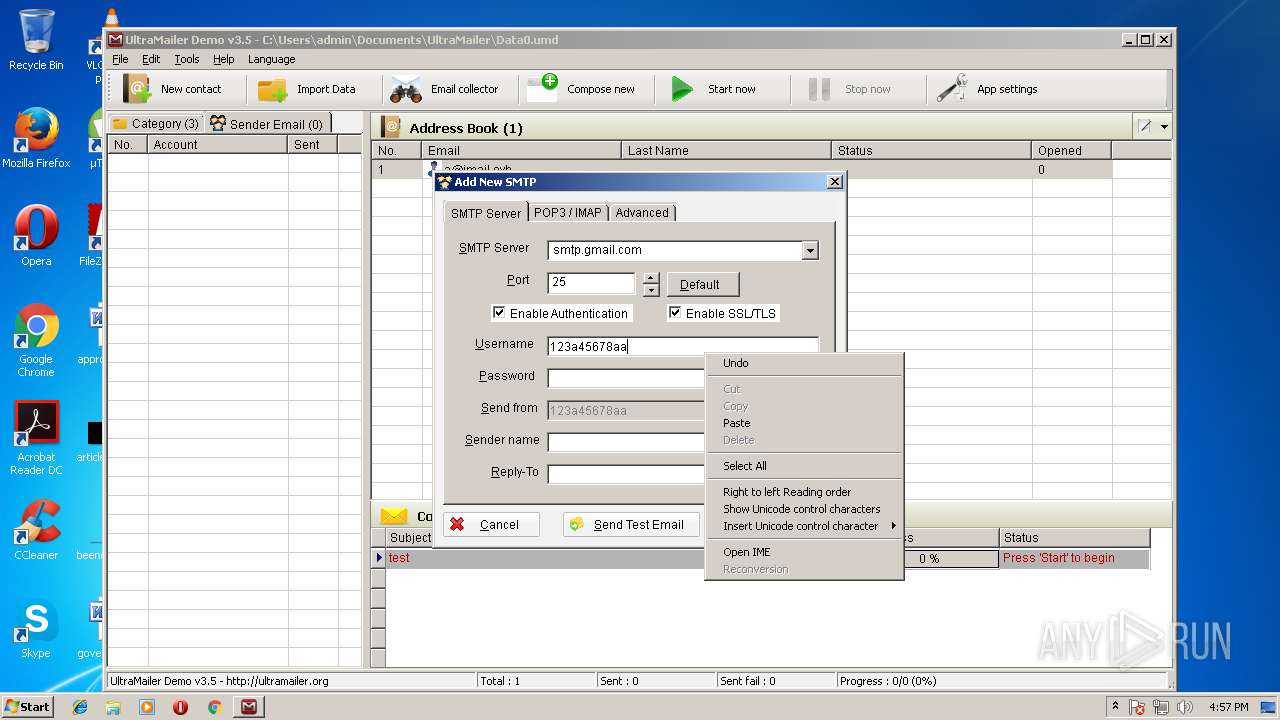
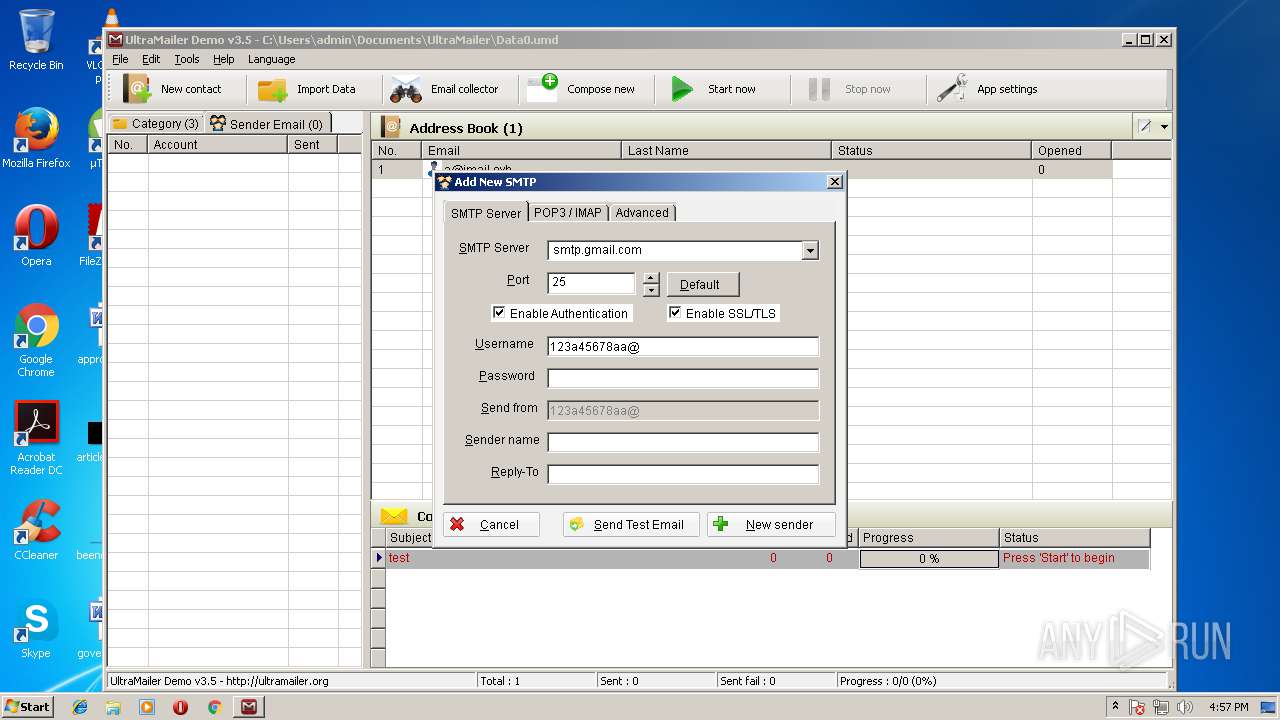
3612 | Ultra Mailer.exe | 64.233.166.108:25 | smtp.gmail.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
functions.ultramailer.org |
| suspicious |
phanmemguimailhangloat.com |
| unknown |
en.ultramailer.org |
| suspicious |
opi.yahoo.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
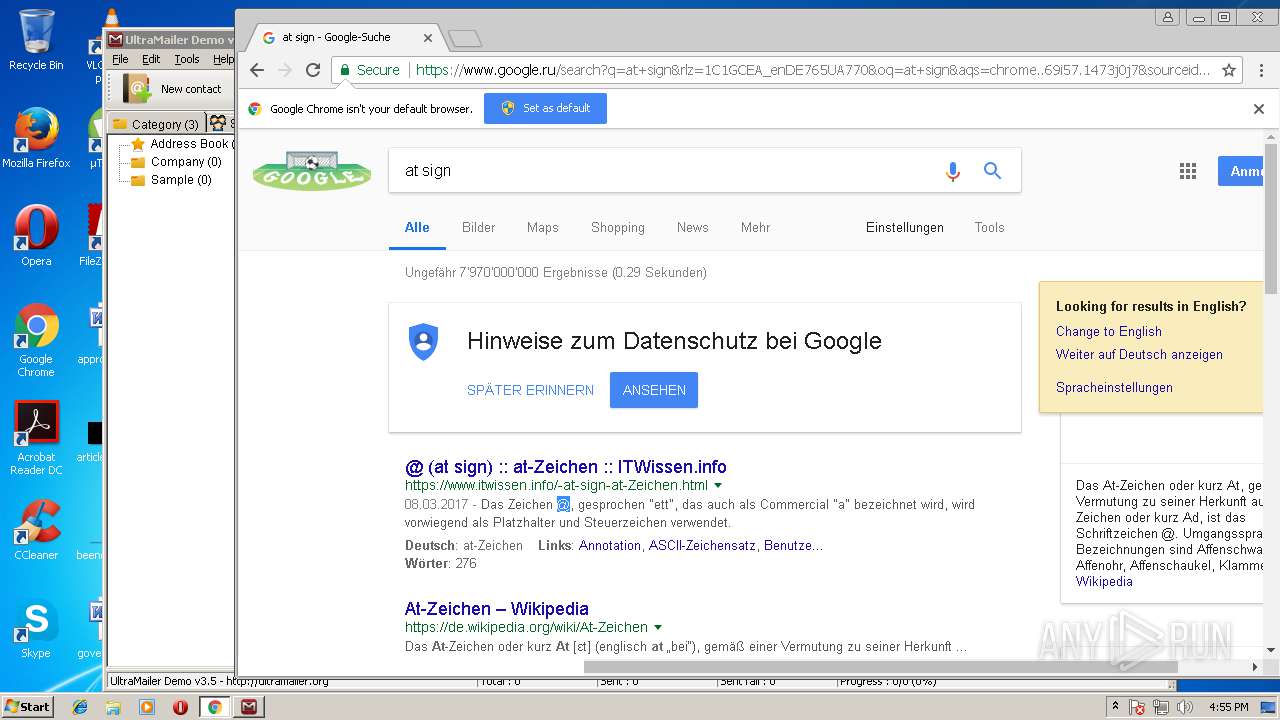
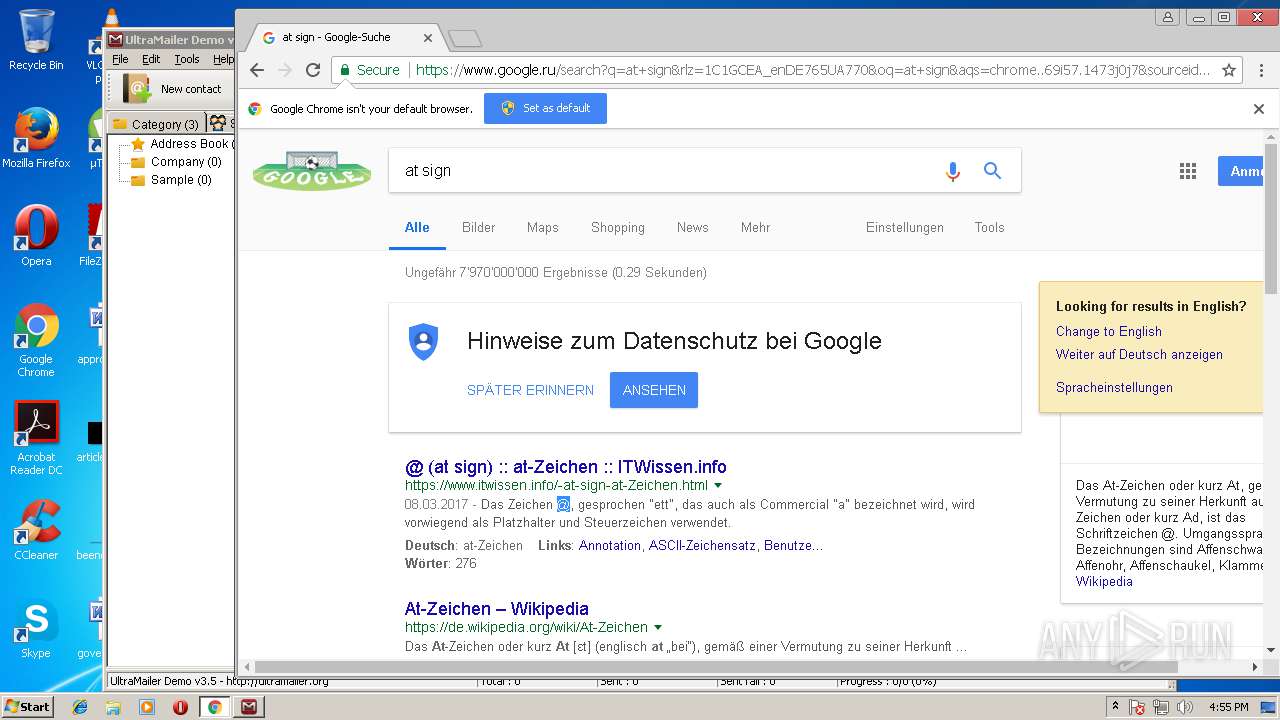
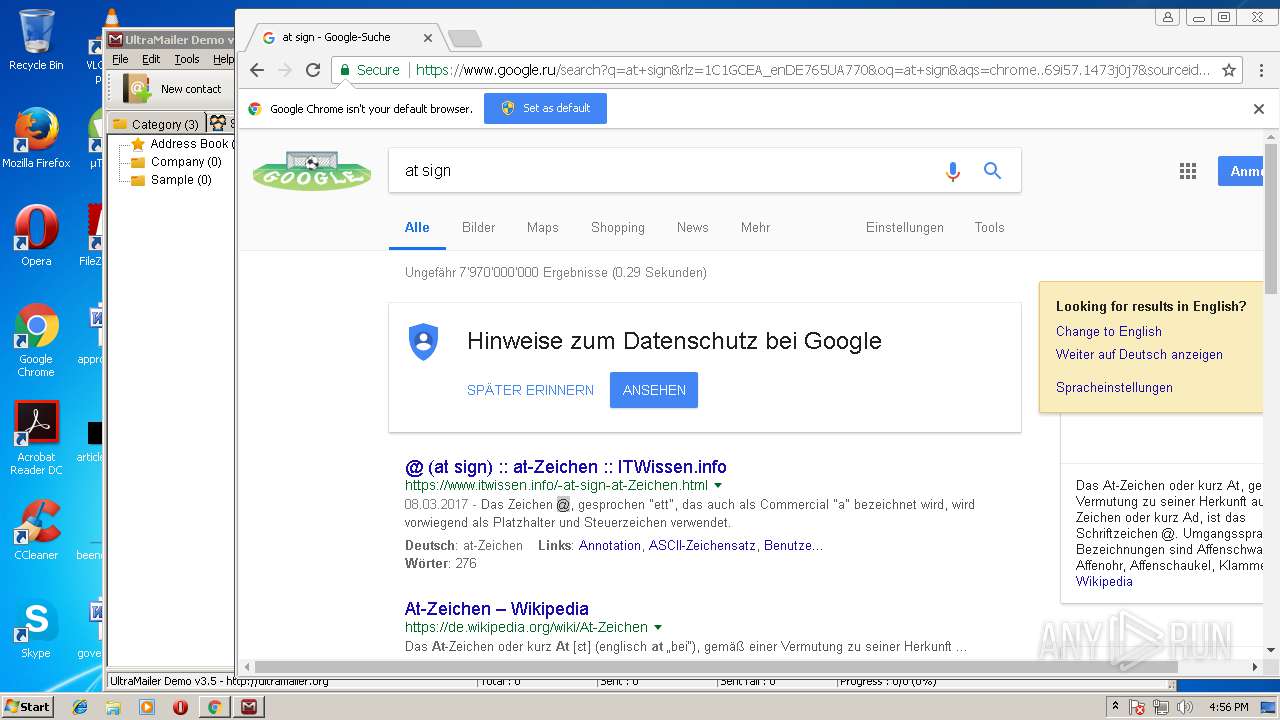
www.google.ru |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
consent.google.com |
| shared |