| URL: | yy.yy |
| Full analysis: | https://app.any.run/tasks/561208b1-66a9-447f-b7b4-497f1bef4f3f |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
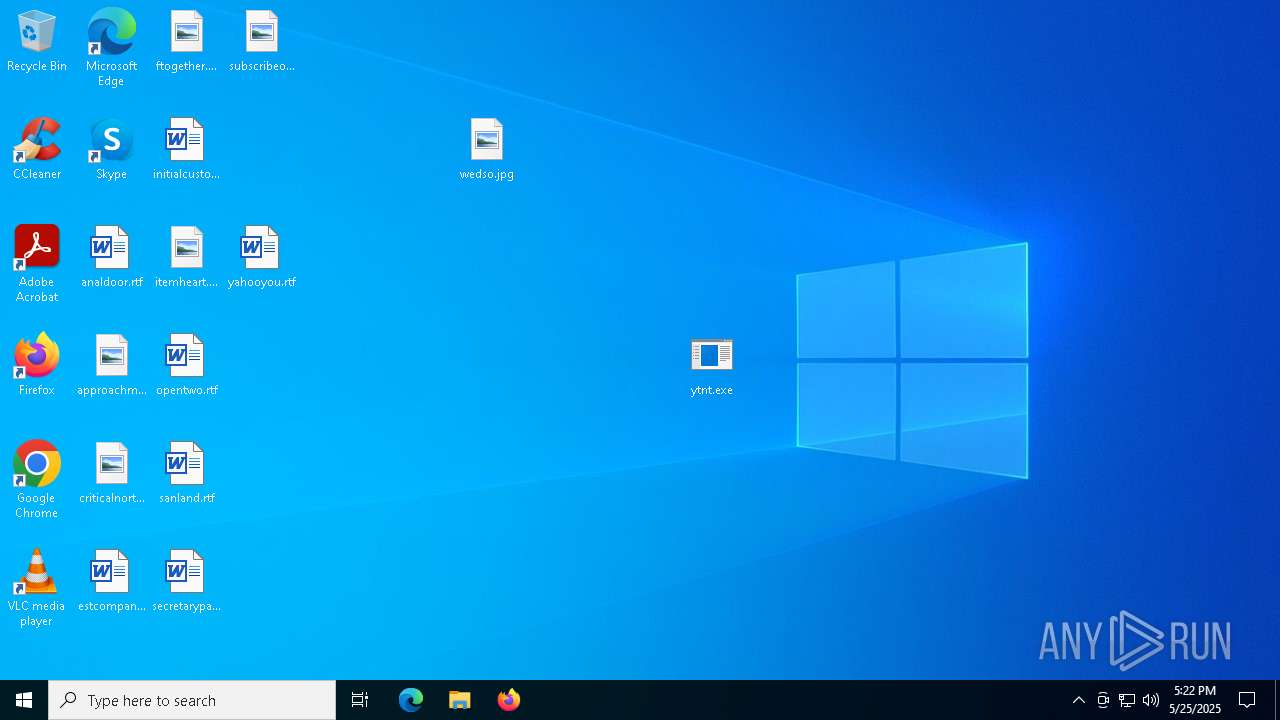
| Analysis date: | May 25, 2025, 17:19:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4440F1D9A236C0A36953A4F56ECF754C |
| SHA1: | A49802C31F94BEED9DC82AFFBD7EC8576466A571 |
| SHA256: | 5E7FDEC1152FF5F0D8E5E7F67B4DB180B3408B5DF3D2499675407248473D33E6 |
| SSDEEP: | 3:tBn:fn |
MALICIOUS
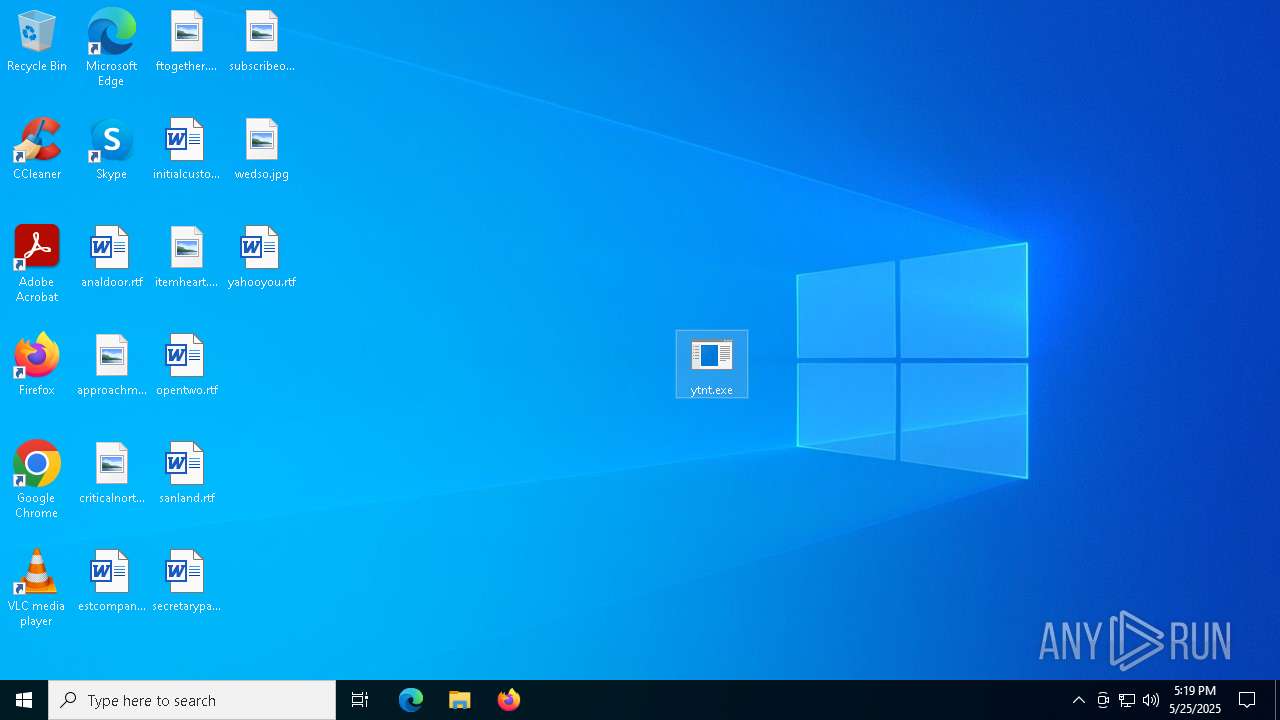
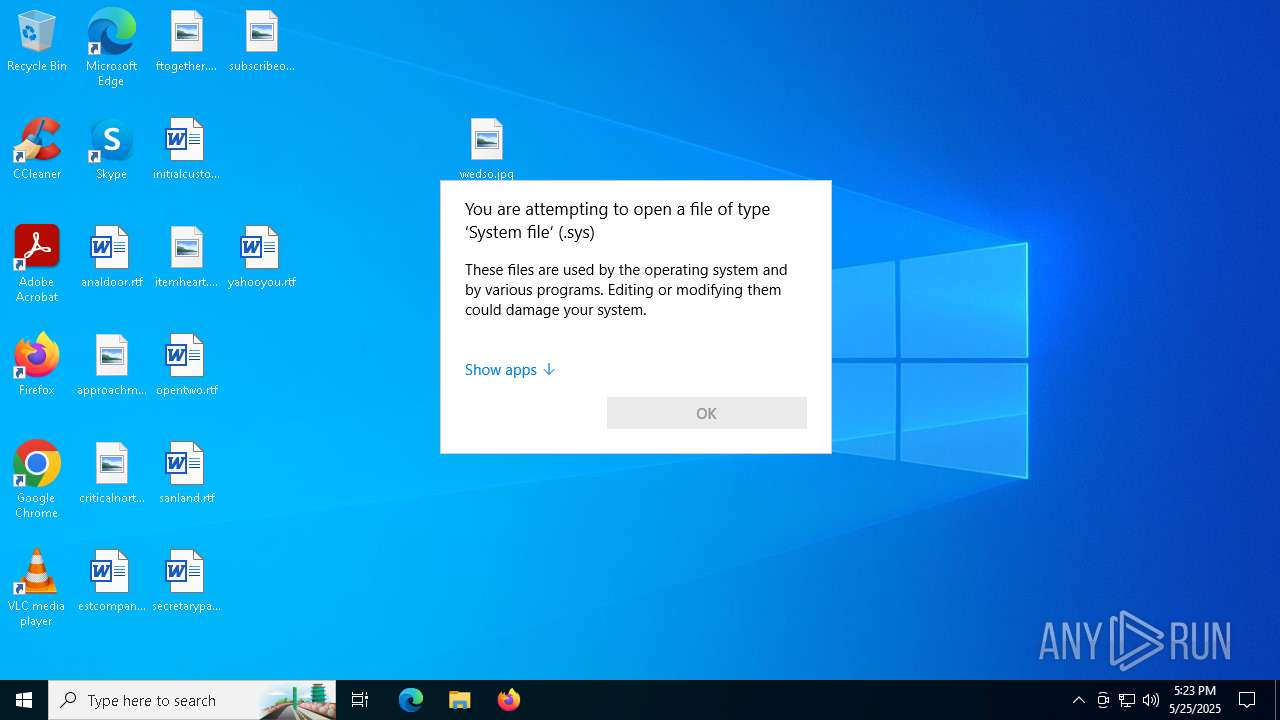
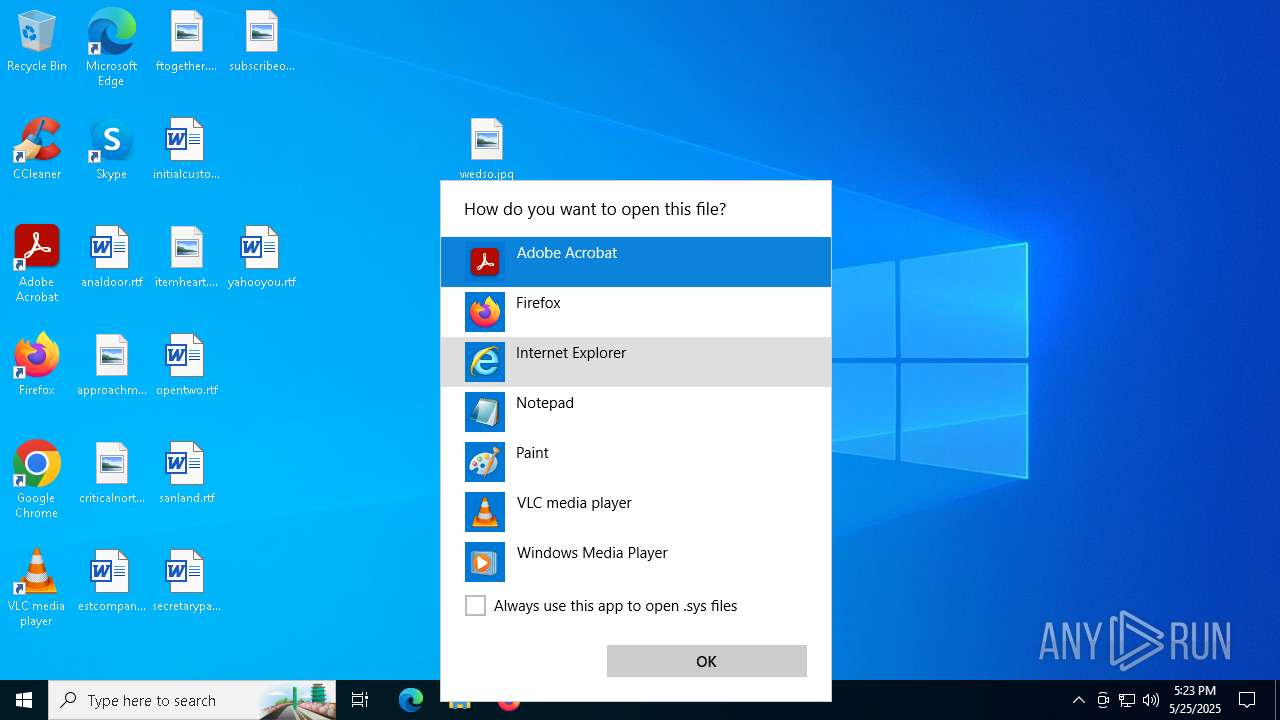
Executing a file with an untrusted certificate
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
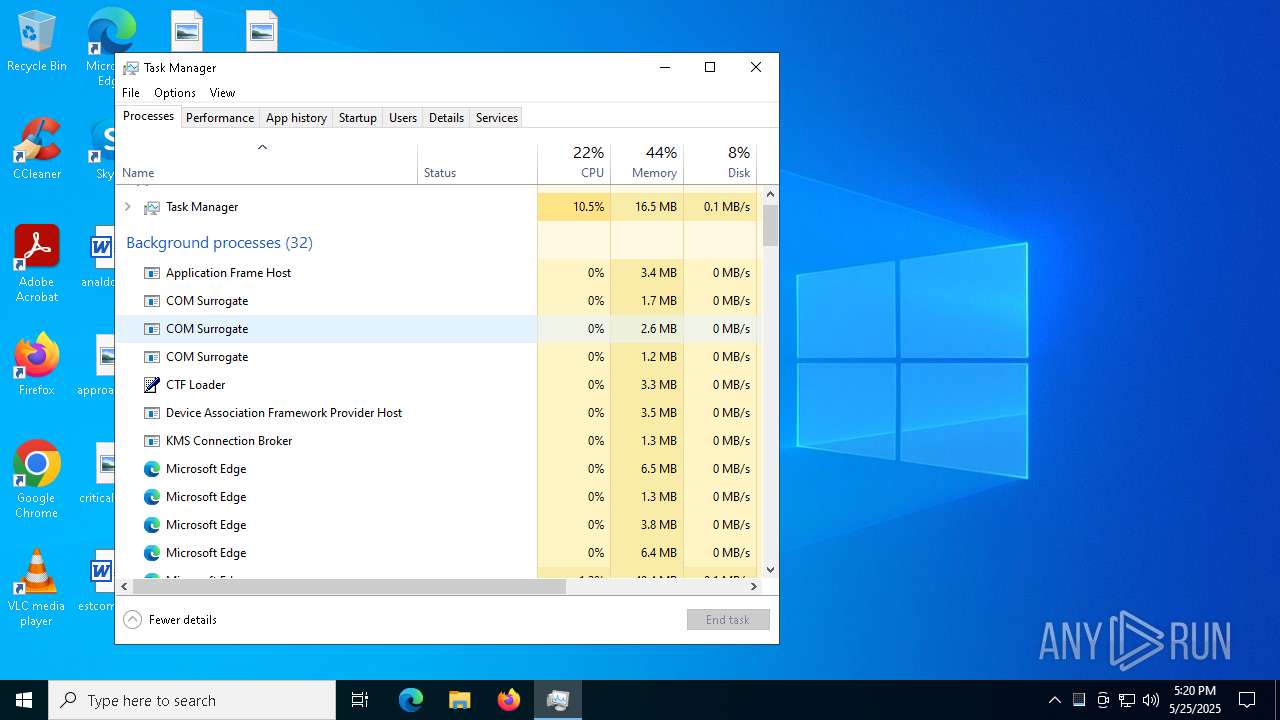
Uses Task Scheduler to run other applications
- cmd.exe (PID: 7964)
- cmd.exe (PID: 5364)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 1116)
- cmd.exe (PID: 3900)
- cmd.exe (PID: 1184)
- cmd.exe (PID: 1568)
- cmd.exe (PID: 5760)
- cmd.exe (PID: 2772)
- cmd.exe (PID: 1300)
- cmd.exe (PID: 5776)
- cmd.exe (PID: 4932)
- cmd.exe (PID: 7272)
- cmd.exe (PID: 7716)
- cmd.exe (PID: 2904)
- cmd.exe (PID: 5744)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 7964)
- cmd.exe (PID: 6068)
- cmd.exe (PID: 6476)
- cmd.exe (PID: 6964)
- cmd.exe (PID: 7548)
- cmd.exe (PID: 5344)
- cmd.exe (PID: 900)
- cmd.exe (PID: 3268)
- cmd.exe (PID: 7228)
- cmd.exe (PID: 8016)
- cmd.exe (PID: 7520)
- cmd.exe (PID: 6592)
- cmd.exe (PID: 6916)
- cmd.exe (PID: 4372)
- cmd.exe (PID: 6928)
- cmd.exe (PID: 2584)
- cmd.exe (PID: 2136)
- cmd.exe (PID: 6564)
- cmd.exe (PID: 7076)
- cmd.exe (PID: 428)
Changes the login/logoff helper path in the registry
- ytnt.exe (PID: 5984)
Changes the AppInit_DLLs value (autorun option)
- ytnt.exe (PID: 5984)
Changes the autorun value in the registry
- ytnt.exe (PID: 5984)
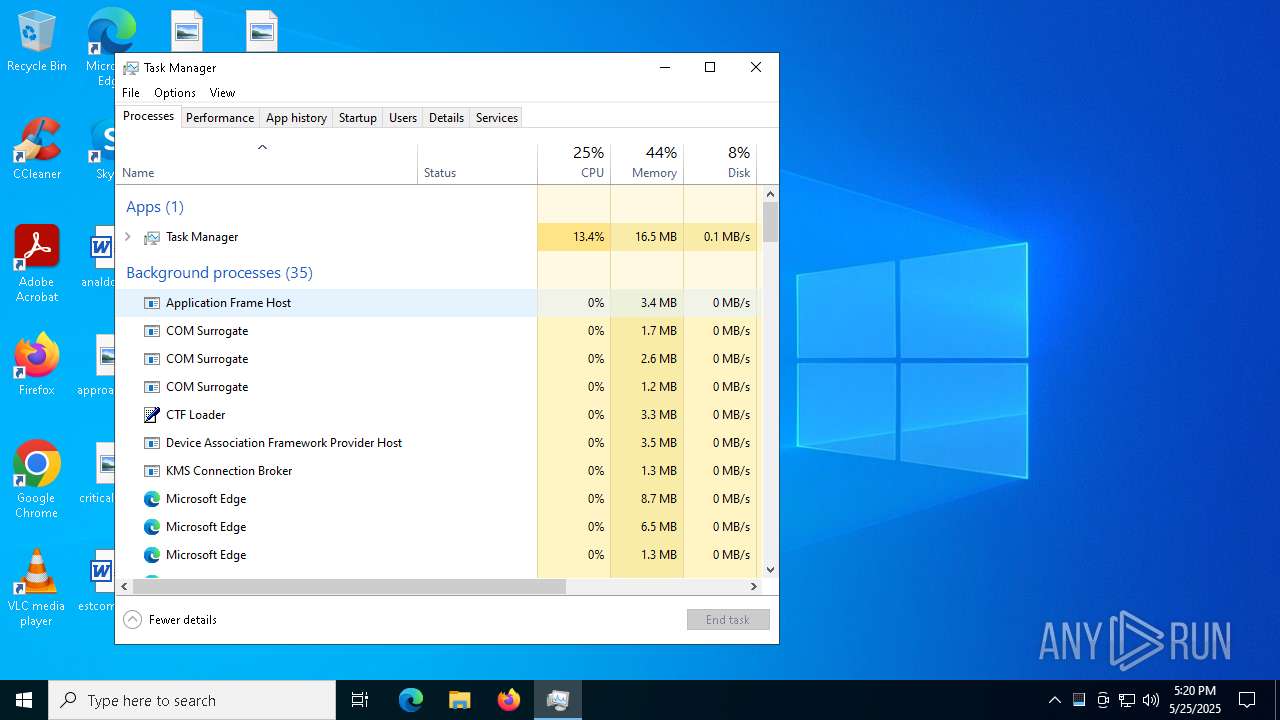
Connects to the CnC server
- ytnt.exe (PID: 5984)
- COM Surrogate (PID: 4508)
PURELOGS has been detected (SURICATA)
- ytnt.exe (PID: 5984)
- COM Surrogate (PID: 4508)
DARKCRYSTAL has been detected (SURICATA)
- ytnt.exe (PID: 5984)
- COM Surrogate (PID: 4508)
SHEETRAT has been detected (SURICATA)
- ytnt.exe (PID: 5984)
SUSPICIOUS
Executable content was dropped or overwritten
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
Starts CMD.EXE for commands execution
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
- COM Surrogate (PID: 4508)
Reads security settings of Internet Explorer
- ytnt.exe (PID: 7288)
Reads the date of Windows installation
- ytnt.exe (PID: 7288)
Application launched itself
- ytnt.exe (PID: 7288)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
- svchost.exe (PID: 2168)
Connects to unusual port
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
- COM Surrogate (PID: 4508)
Executes as Windows Service
- WmiApSrv.exe (PID: 7400)
Contacting a server suspected of hosting an CnC
- ytnt.exe (PID: 5984)
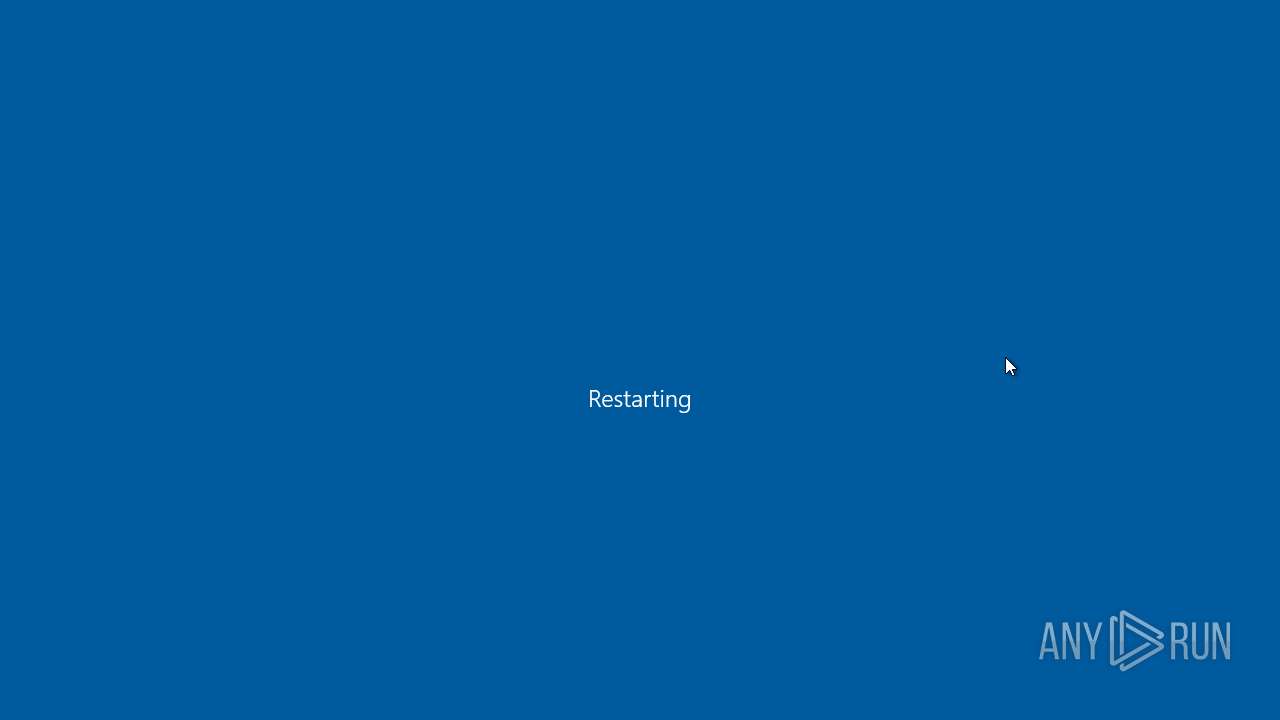
The system shut down or reboot
- cmd.exe (PID: 5452)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4104)
INFO
Checks supported languages
- identity_helper.exe (PID: 7372)
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
Application launched itself
- msedge.exe (PID: 4428)
- msedge.exe (PID: 1228)
Reads the computer name
- identity_helper.exe (PID: 7372)
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
Reads Environment values
- identity_helper.exe (PID: 7372)
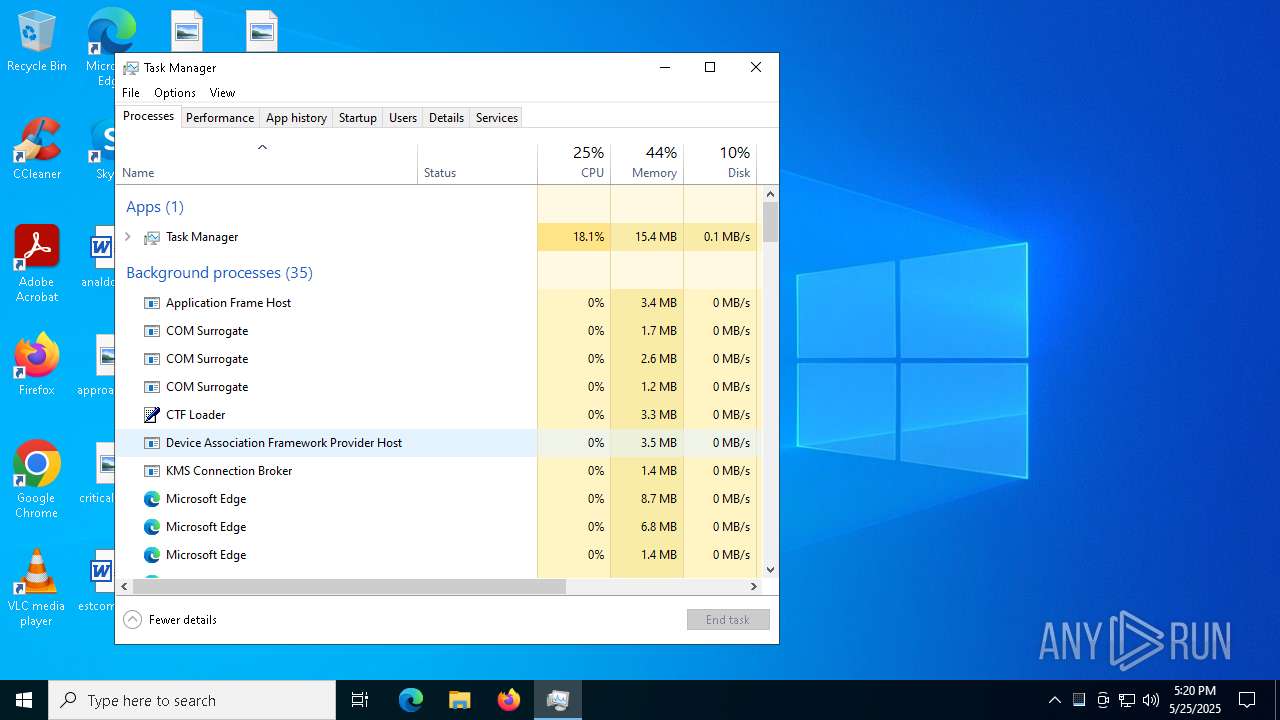
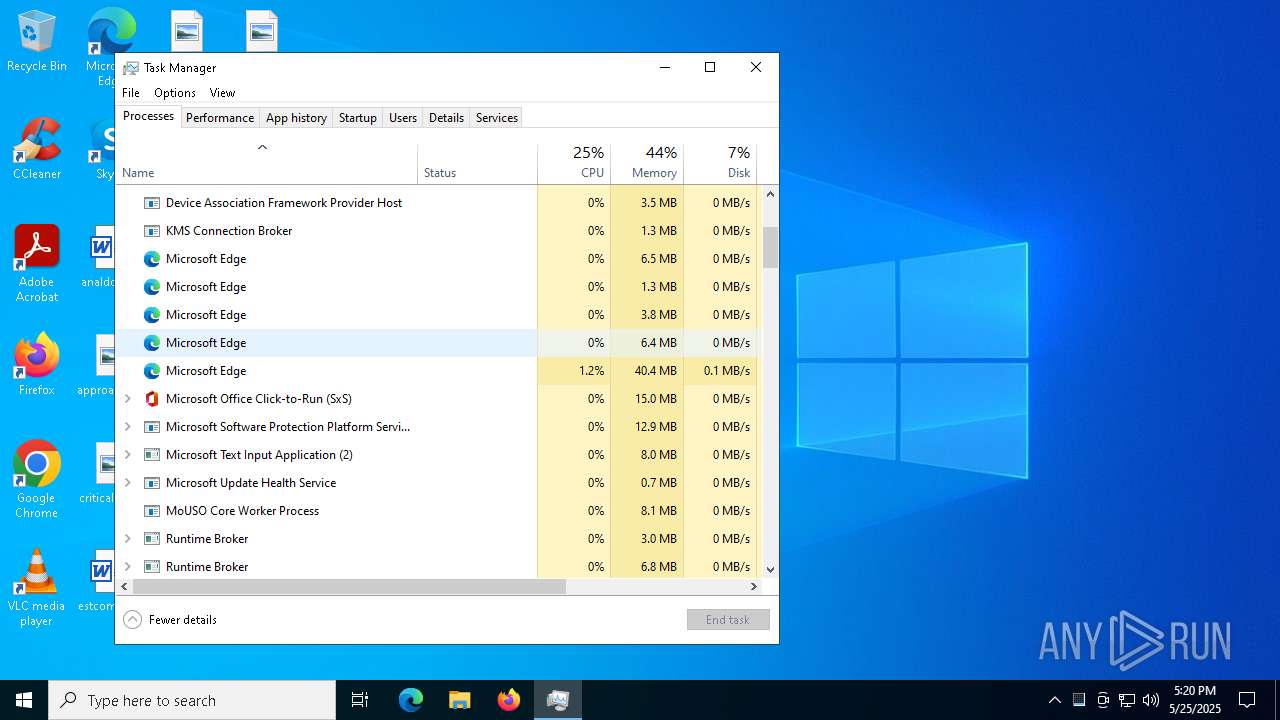
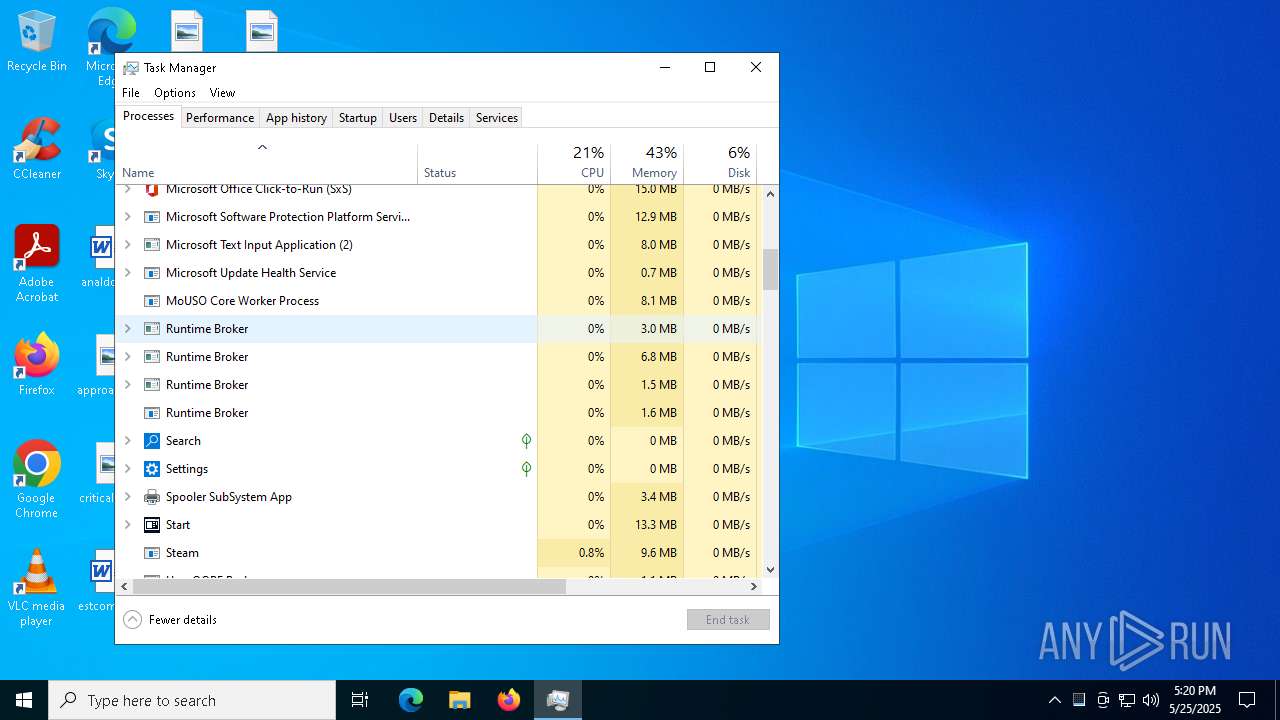
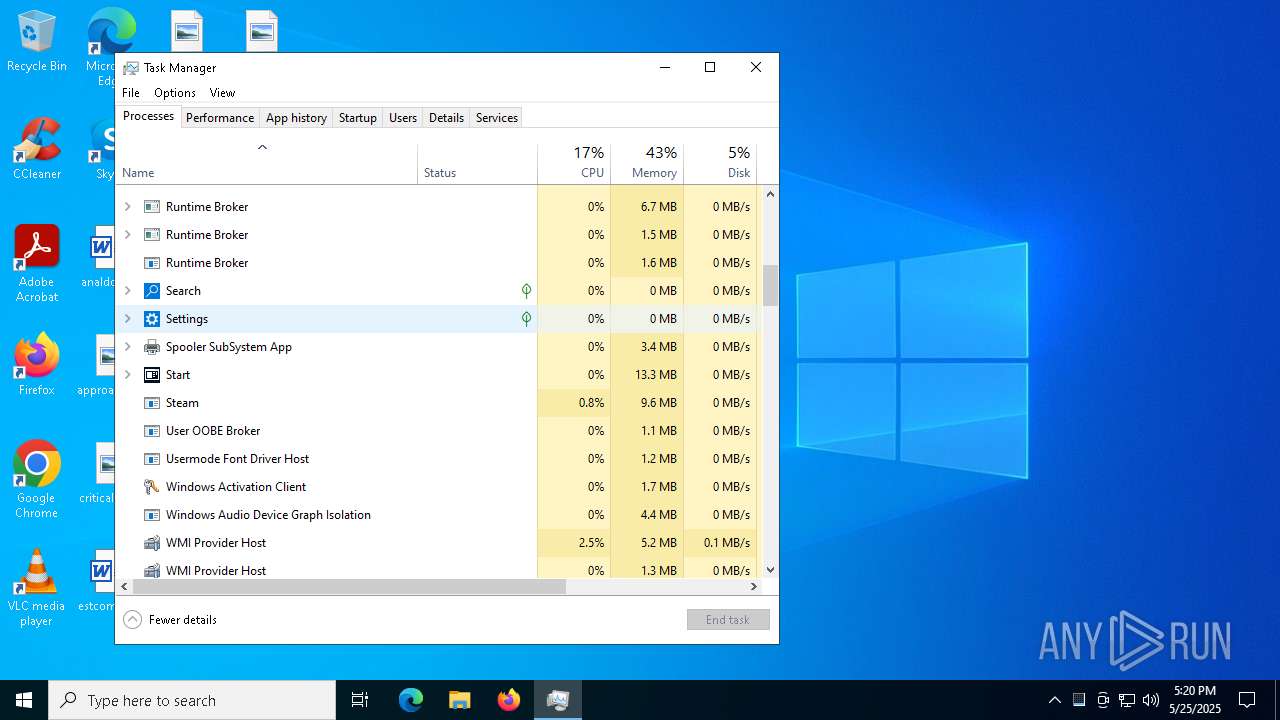
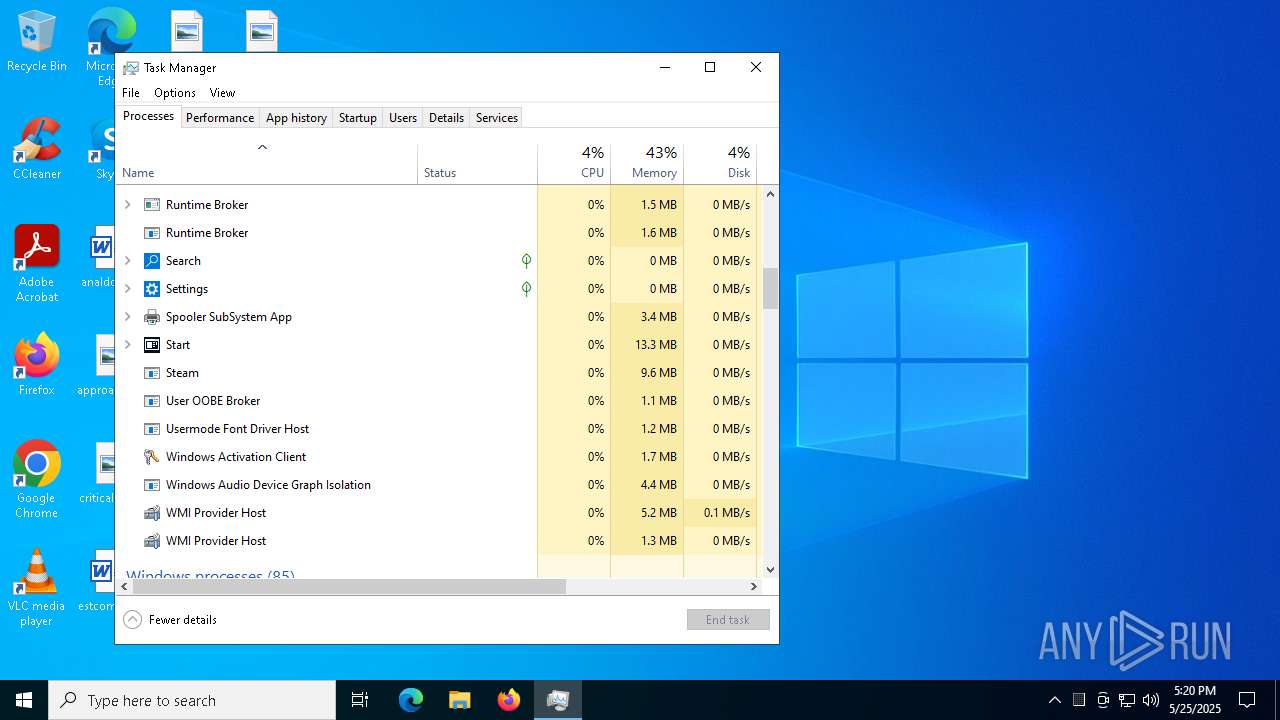
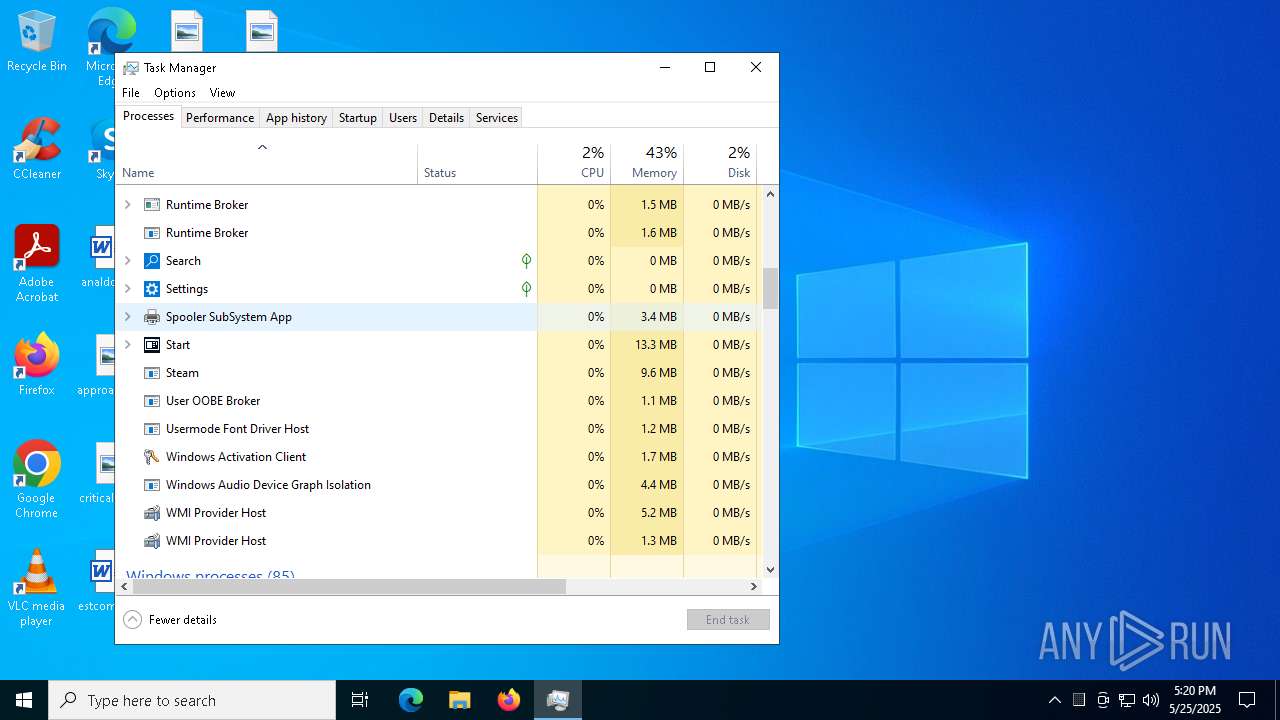
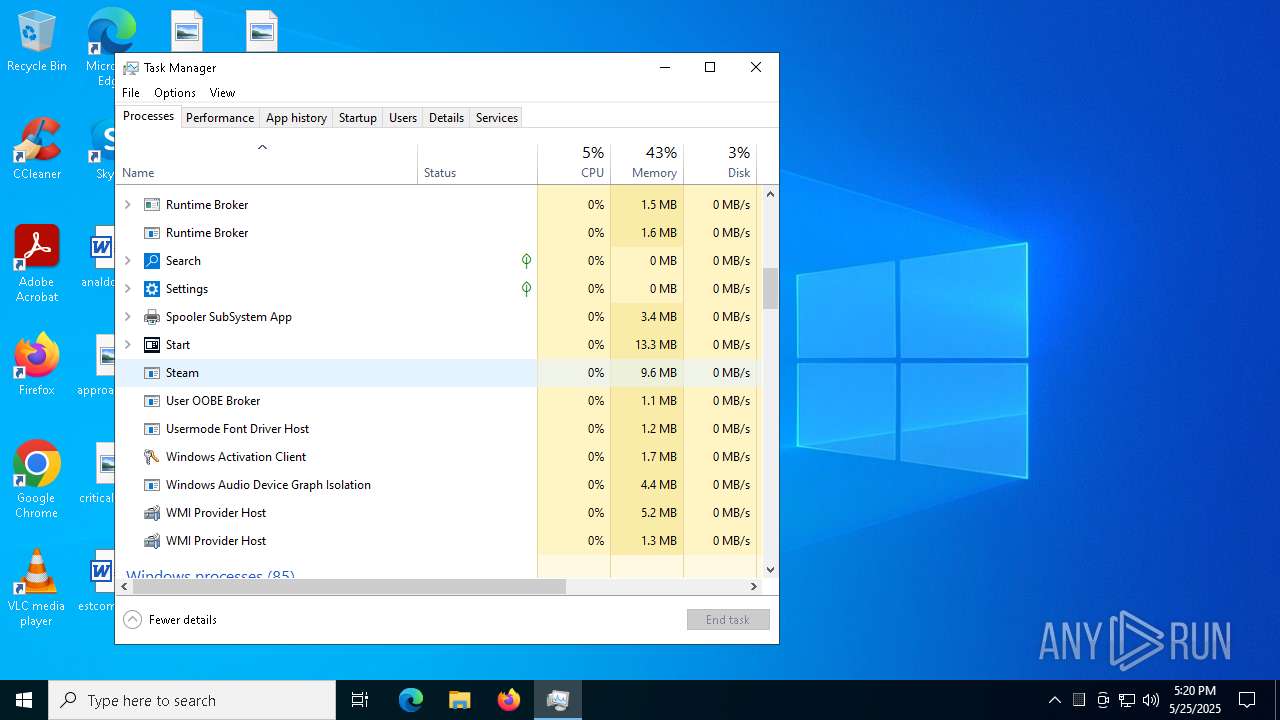
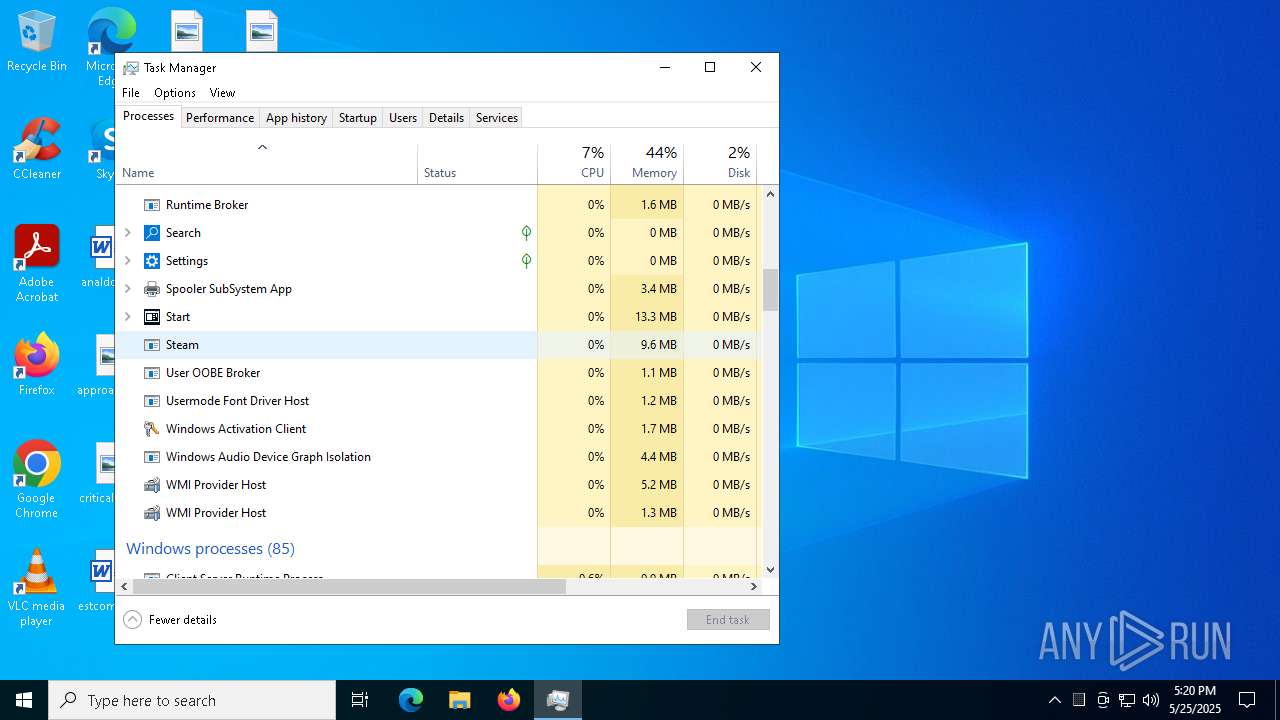
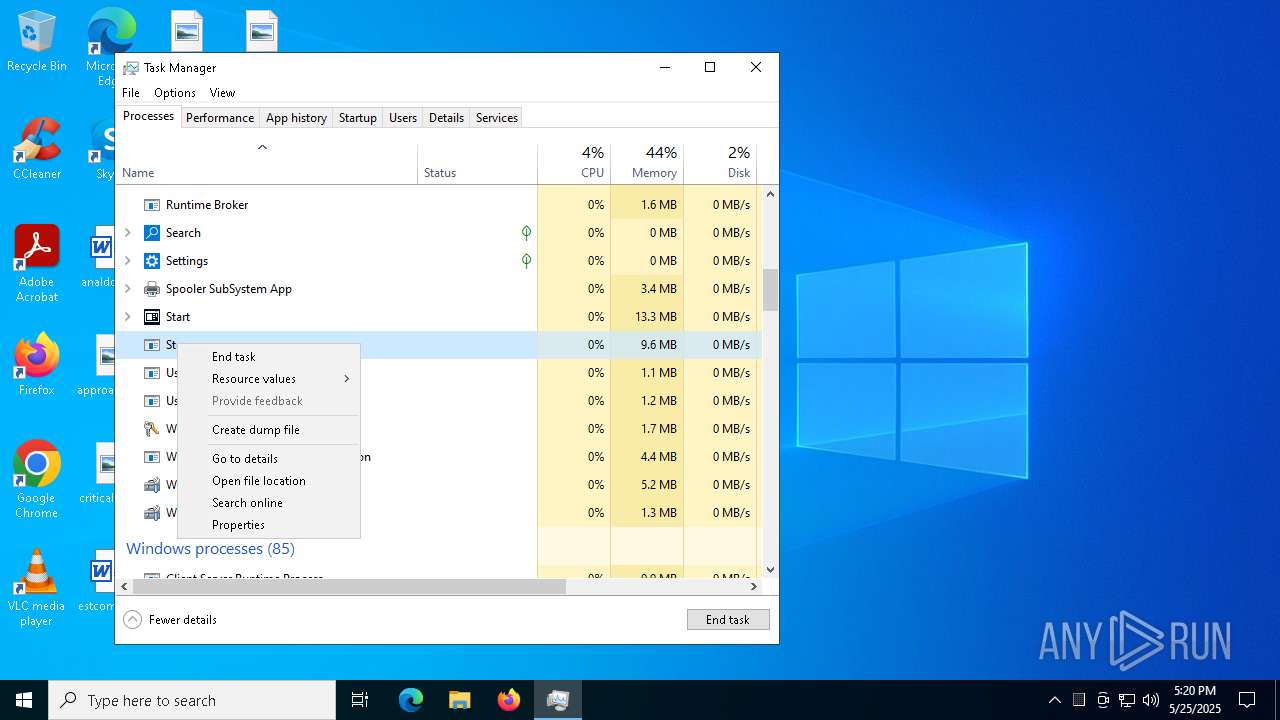
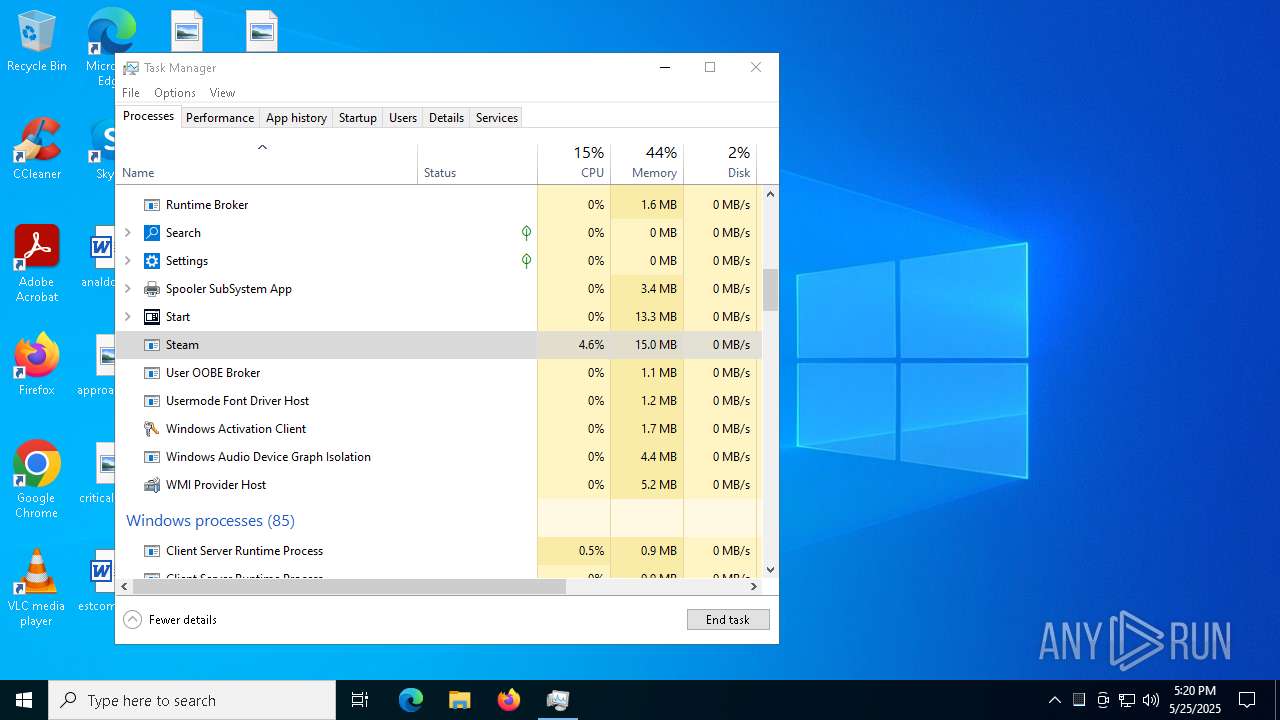
Manual execution by a user
- ytnt.exe (PID: 7288)
- Taskmgr.exe (PID: 3268)
- Taskmgr.exe (PID: 1196)
Reads the machine GUID from the registry
- ytnt.exe (PID: 7288)
- ytnt.exe (PID: 5984)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 1196)
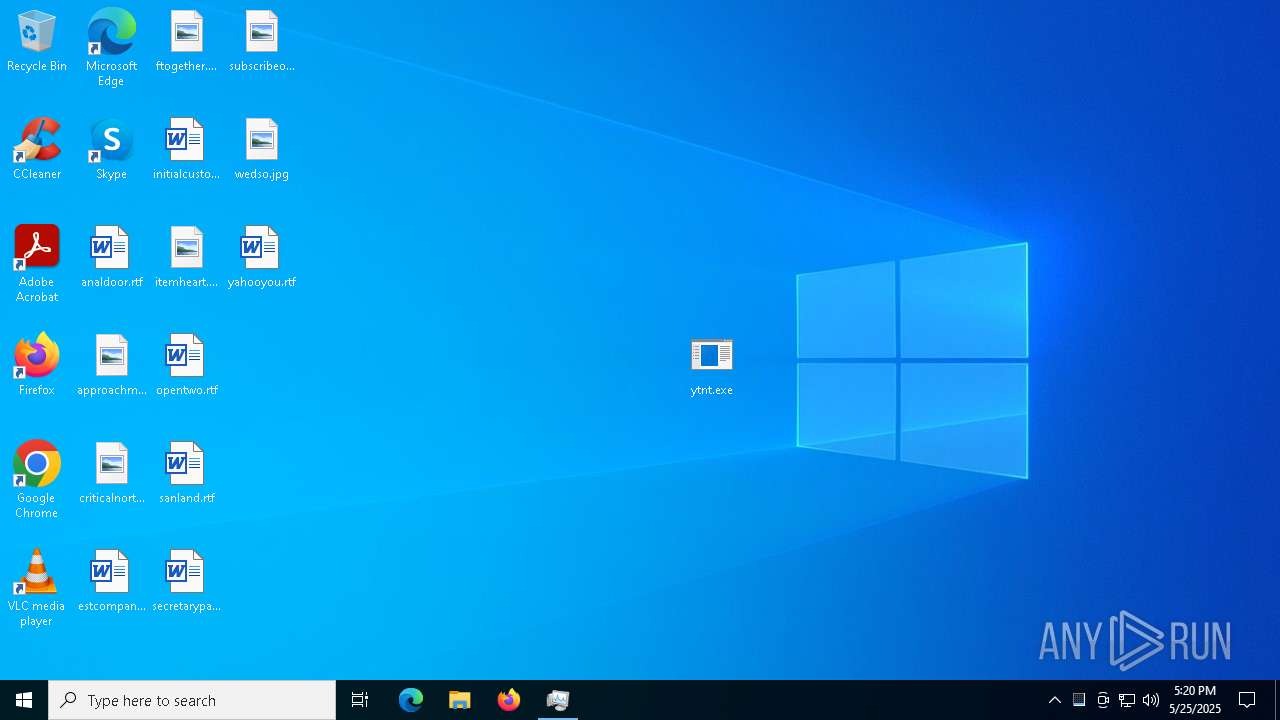
Creates files or folders in the user directory
- ytnt.exe (PID: 7288)
Process checks computer location settings
- ytnt.exe (PID: 7288)
Reads the software policy settings
- slui.exe (PID: 2284)
Reads CPU info
- ytnt.exe (PID: 5984)
Reads the time zone
- ytnt.exe (PID: 5984)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
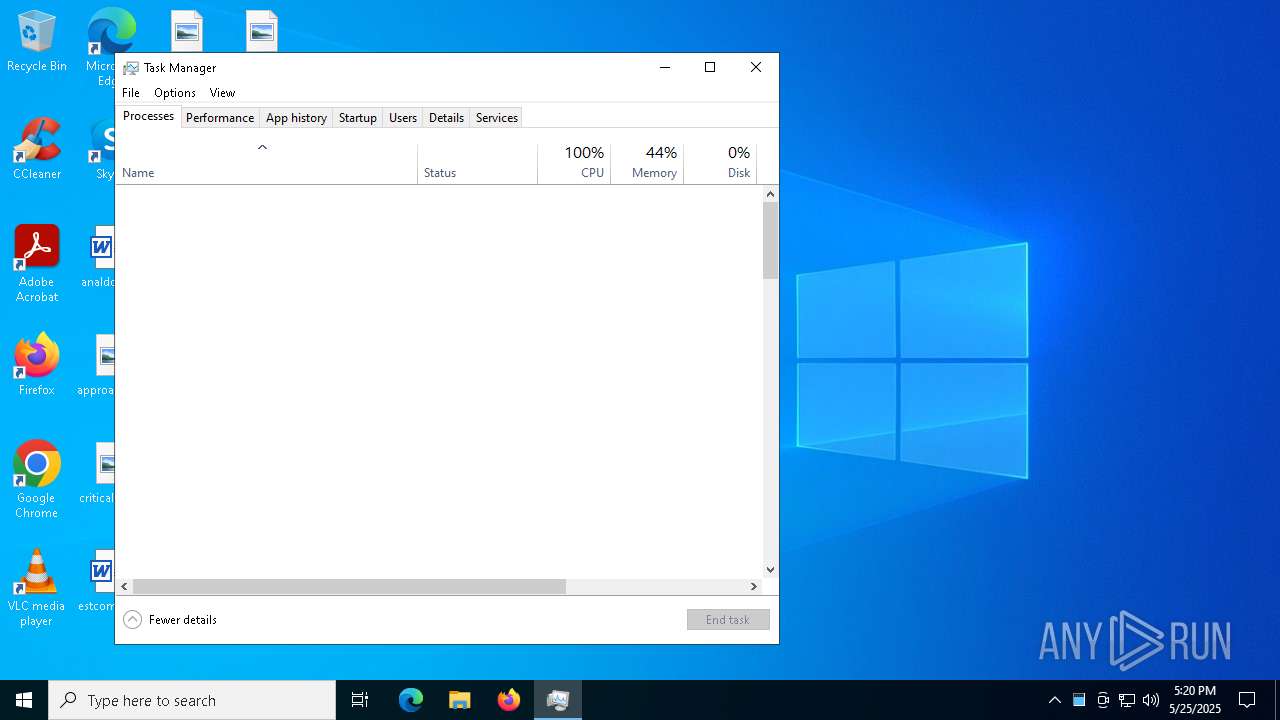
Total processes
434
Monitored processes
169
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 428 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" & exit | C:\Windows\System32\cmd.exe | — | COM Surrogate |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 504 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5856 --field-trial-handle=2452,i,9647966365564444842,9055281422117302329,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 660 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 736 | SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 856 | SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" /RL HIGHEST | C:\Windows\System32\schtasks.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 900 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | ytnt.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1116 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | ytnt.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1184 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "destrio4" /tr "C:\Users\admin\AppData\Local\Microsoft\Windows\INetCookies\COM Surrogate" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | ytnt.exe |
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
17
Suspicious files
231
Text files
63
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a48f.TMP | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a49e.TMP | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a49e.TMP | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a49e.TMP | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10a4ec.TMP | — | |
MD5:— | SHA256:— | |||
| 1228 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
165
DNS requests
65
Threats
41
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5796 | svchost.exe | GET | 200 | 23.216.77.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.8:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7732 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748295846&P2=404&P3=2&P4=bAjUCGEMzkcYH4tjrSostth%2bAiKds7QSE4jVLijkpVVtu2qQwyY9wSbMVQLnAXwVWsvcHoVKKCQ3ebKWpfOZKg%3d%3d | unknown | — | — | whitelisted |
7300 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7732 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748295846&P2=404&P3=2&P4=bAjUCGEMzkcYH4tjrSostth%2bAiKds7QSE4jVLijkpVVtu2qQwyY9wSbMVQLnAXwVWsvcHoVKKCQ3ebKWpfOZKg%3d%3d | unknown | — | — | whitelisted |
7732 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748295846&P2=404&P3=2&P4=bAjUCGEMzkcYH4tjrSostth%2bAiKds7QSE4jVLijkpVVtu2qQwyY9wSbMVQLnAXwVWsvcHoVKKCQ3ebKWpfOZKg%3d%3d | unknown | — | — | whitelisted |
7732 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748295846&P2=404&P3=2&P4=bAjUCGEMzkcYH4tjrSostth%2bAiKds7QSE4jVLijkpVVtu2qQwyY9wSbMVQLnAXwVWsvcHoVKKCQ3ebKWpfOZKg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6700 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5796 | svchost.exe | 23.216.77.8:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5796 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7228 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7228 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
yy.yy |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Server GZIP C2 Traffic |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
5984 | ytnt.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |