| URL: | yy.yy |
| Full analysis: | https://app.any.run/tasks/368b182d-0075-4c75-8f71-780d5ef0fa4d |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
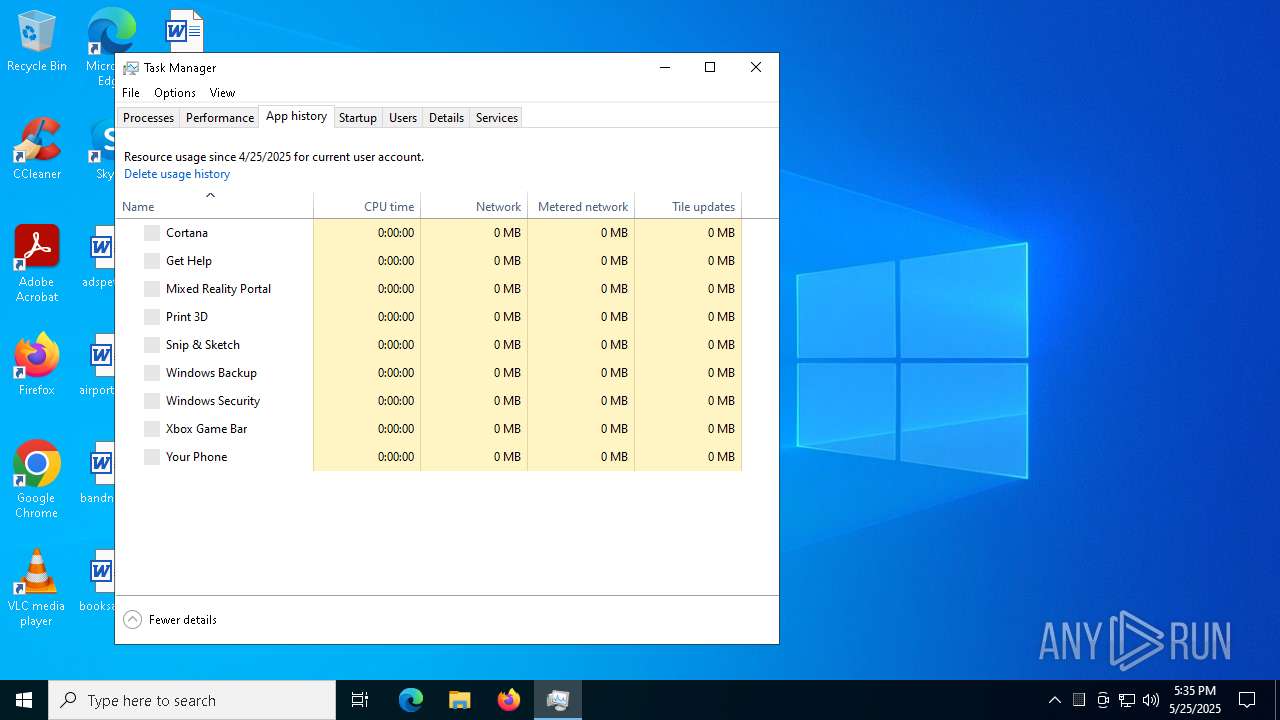
| Analysis date: | May 25, 2025, 17:34:32 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4440F1D9A236C0A36953A4F56ECF754C |
| SHA1: | A49802C31F94BEED9DC82AFFBD7EC8576466A571 |
| SHA256: | 5E7FDEC1152FF5F0D8E5E7F67B4DB180B3408B5DF3D2499675407248473D33E6 |
| SSDEEP: | 3:tBn:fn |
MALICIOUS
Changes the login/logoff helper path in the registry
- des1.exe (PID: 6372)
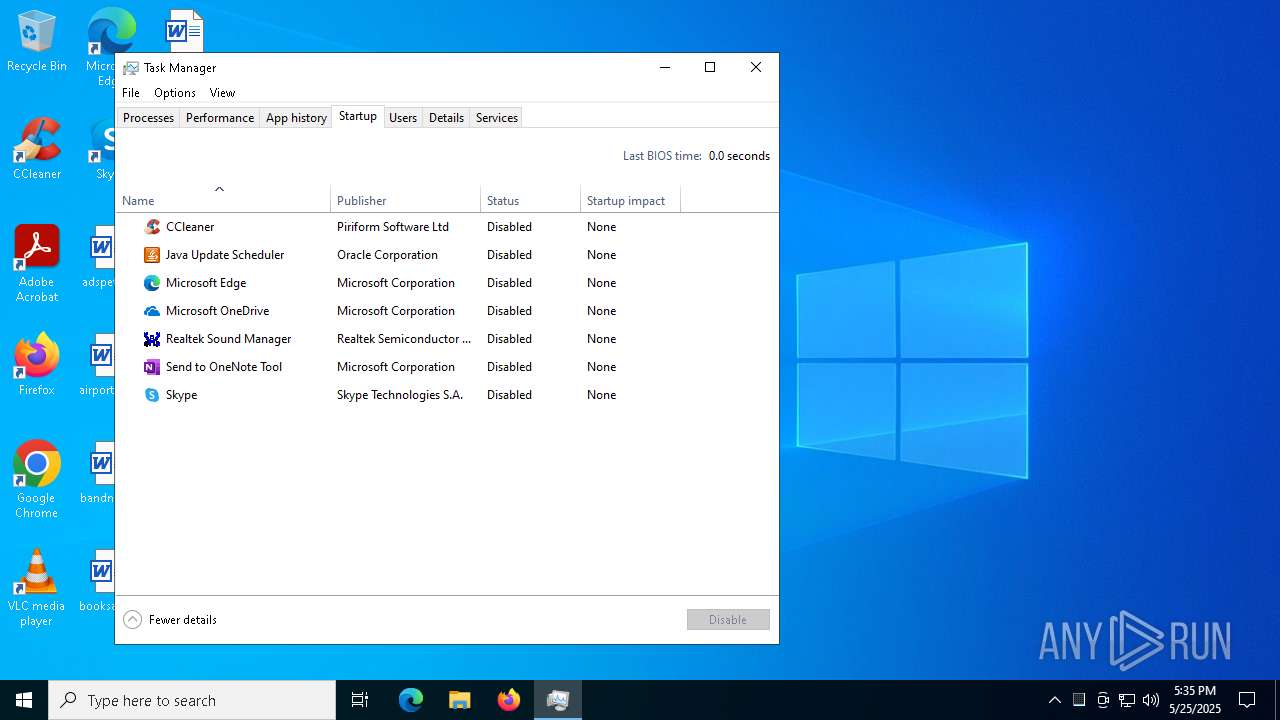
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 6576)
DARKCRYSTAL has been detected (SURICATA)
- des1.exe (PID: 6372)
- destrio.exe (PID: 4136)
PURELOGS has been detected (SURICATA)
- des1.exe (PID: 6372)
- destrio.exe (PID: 4136)
Connects to the CnC server
- des1.exe (PID: 6372)
- destrio.exe (PID: 4136)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1240)
SHEETRAT has been detected (SURICATA)
- destrio.exe (PID: 4136)
- des1.exe (PID: 6372)
SUSPICIOUS
Reads the date of Windows installation
- des1.exe (PID: 1164)
Reads security settings of Internet Explorer
- des1.exe (PID: 1164)
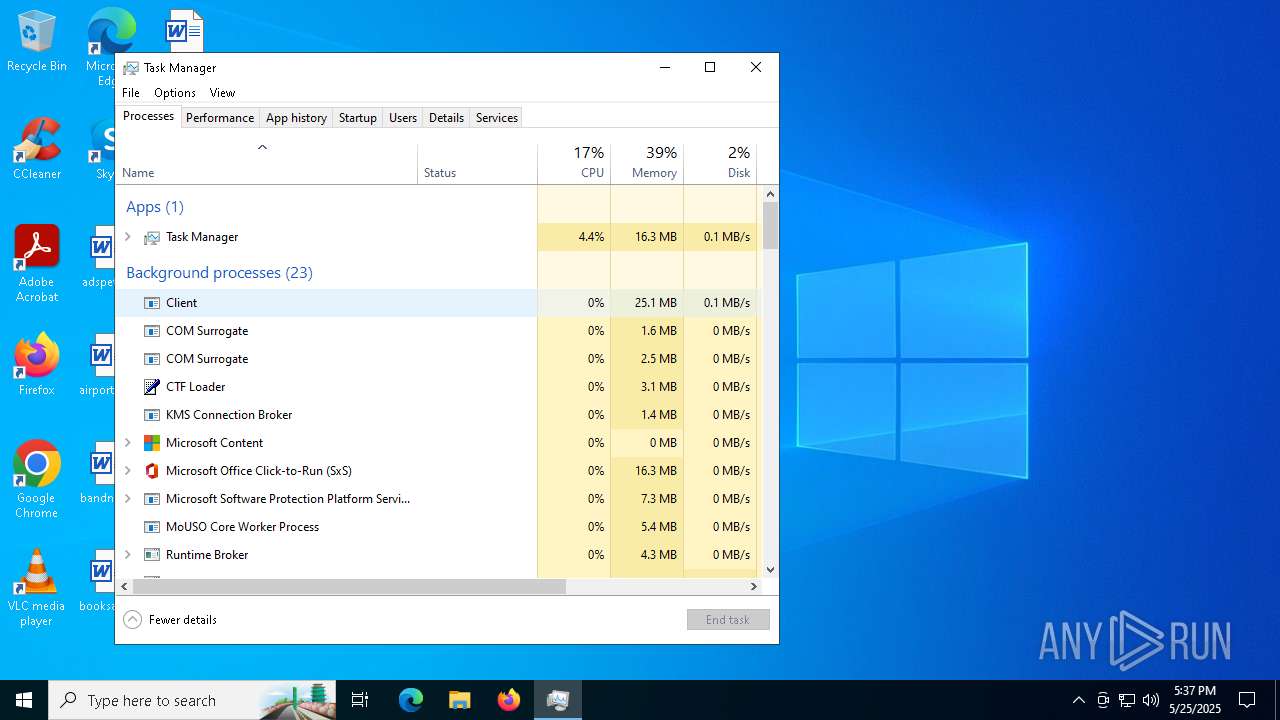
Application launched itself
- des1.exe (PID: 1164)
Executable content was dropped or overwritten
- des1.exe (PID: 6372)
Starts CMD.EXE for commands execution
- des1.exe (PID: 6372)
- destrio.exe (PID: 4584)
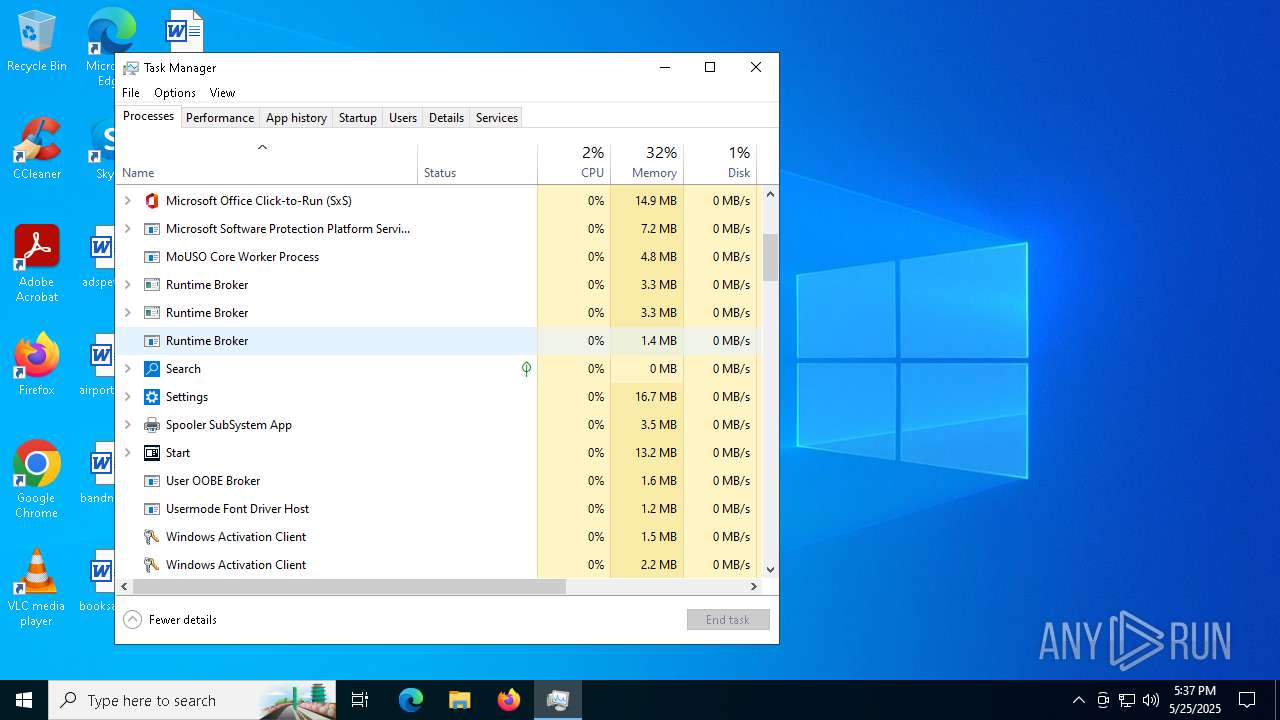
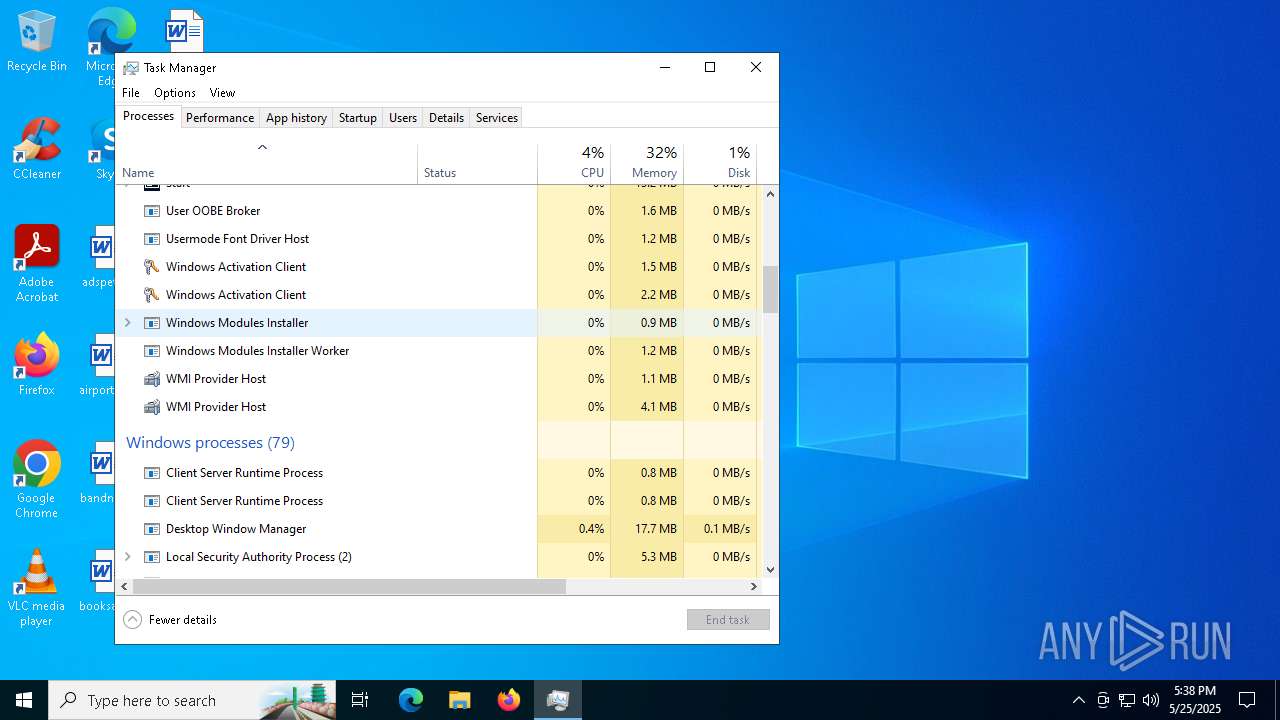
Executes as Windows Service
- WmiApSrv.exe (PID: 7440)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
- svchost.exe (PID: 2164)
The process checks if it is being run in the virtual environment
- des1.exe (PID: 6372)
Connects to unusual port
- des1.exe (PID: 6372)
- destrio.exe (PID: 4136)
The process executes via Task Scheduler
- destrio.exe (PID: 4136)
- destrio.exe (PID: 6784)
- PLUGScheduler.exe (PID: 4128)
Contacting a server suspected of hosting an CnC
- destrio.exe (PID: 4136)
- des1.exe (PID: 6372)
INFO
Application launched itself
- msedge.exe (PID: 4776)
- msedge.exe (PID: 2236)
Reads Environment values
- identity_helper.exe (PID: 2852)
- identity_helper.exe (PID: 7620)
Checks supported languages
- identity_helper.exe (PID: 7620)
- identity_helper.exe (PID: 2852)
- des1.exe (PID: 1164)
- des1.exe (PID: 6372)
Reads the computer name
- identity_helper.exe (PID: 2852)
- identity_helper.exe (PID: 7620)
- des1.exe (PID: 1164)
- des1.exe (PID: 6372)
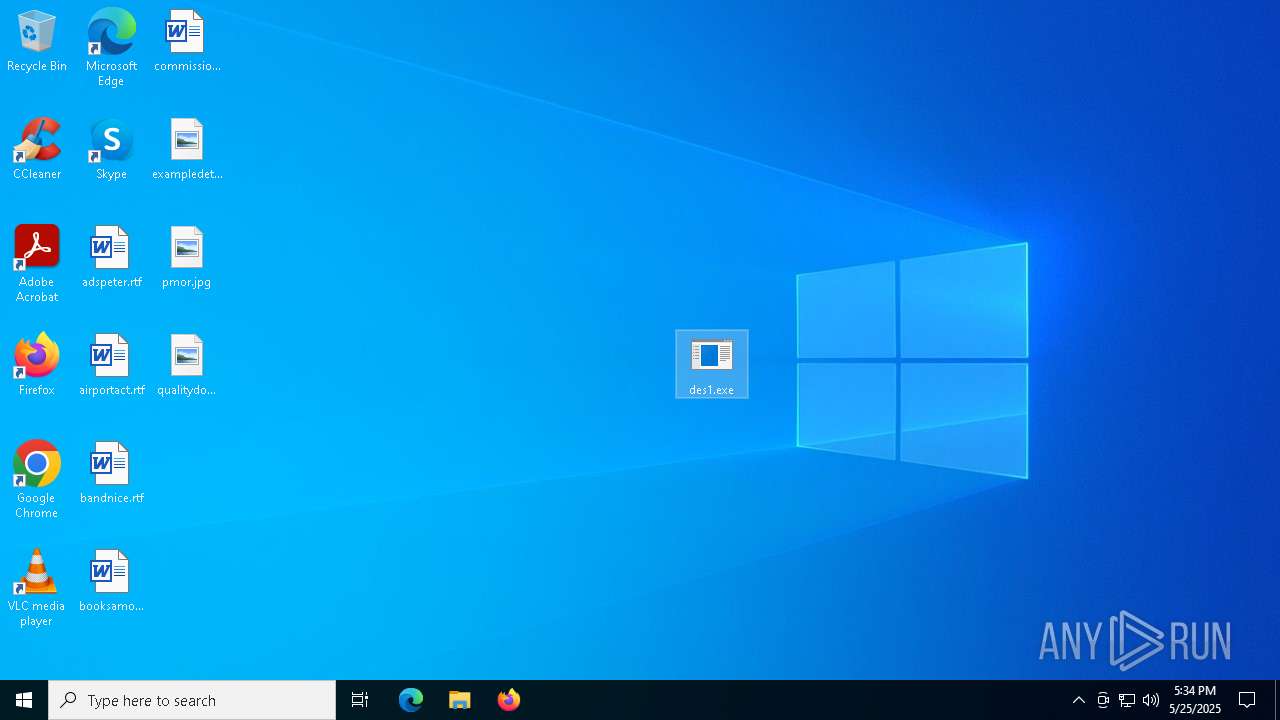
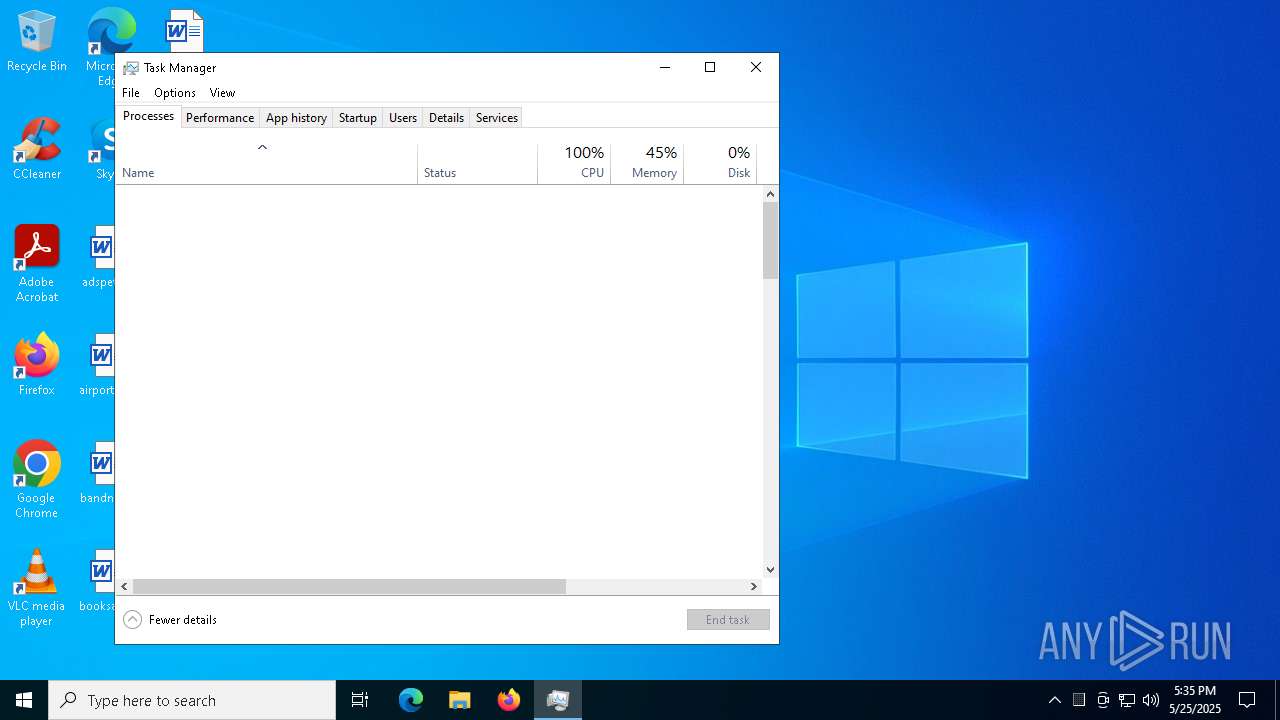
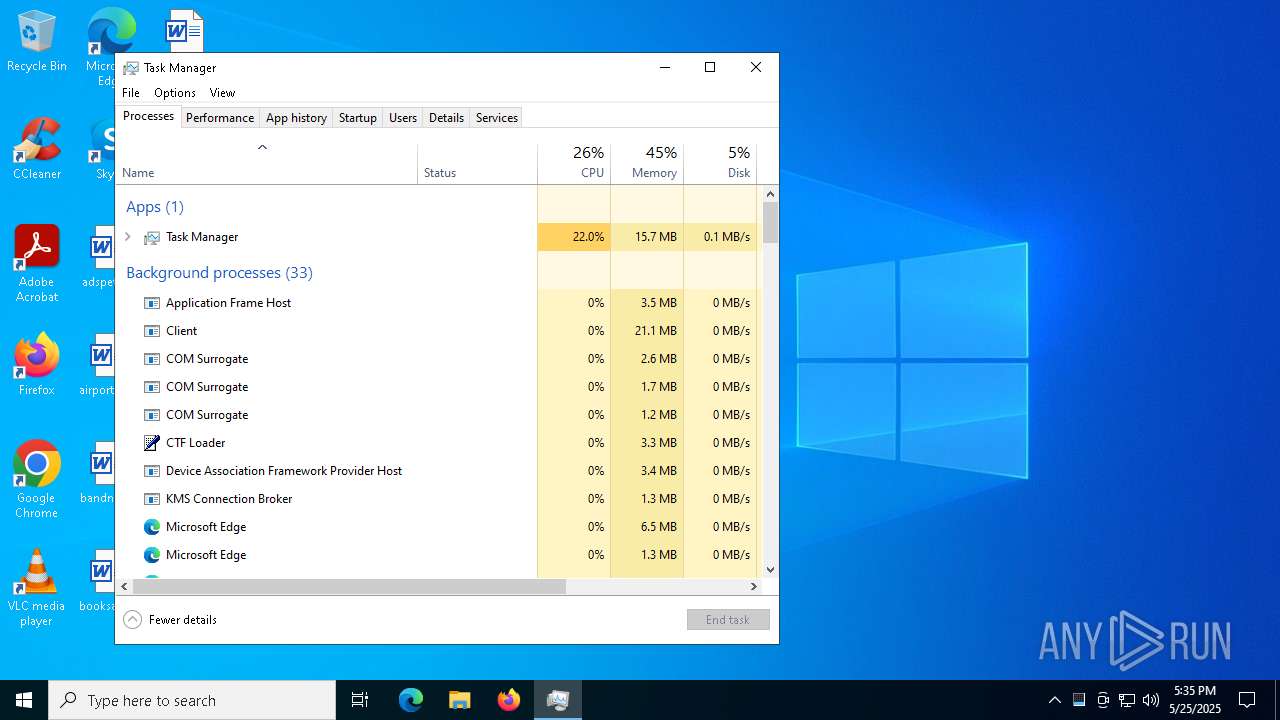
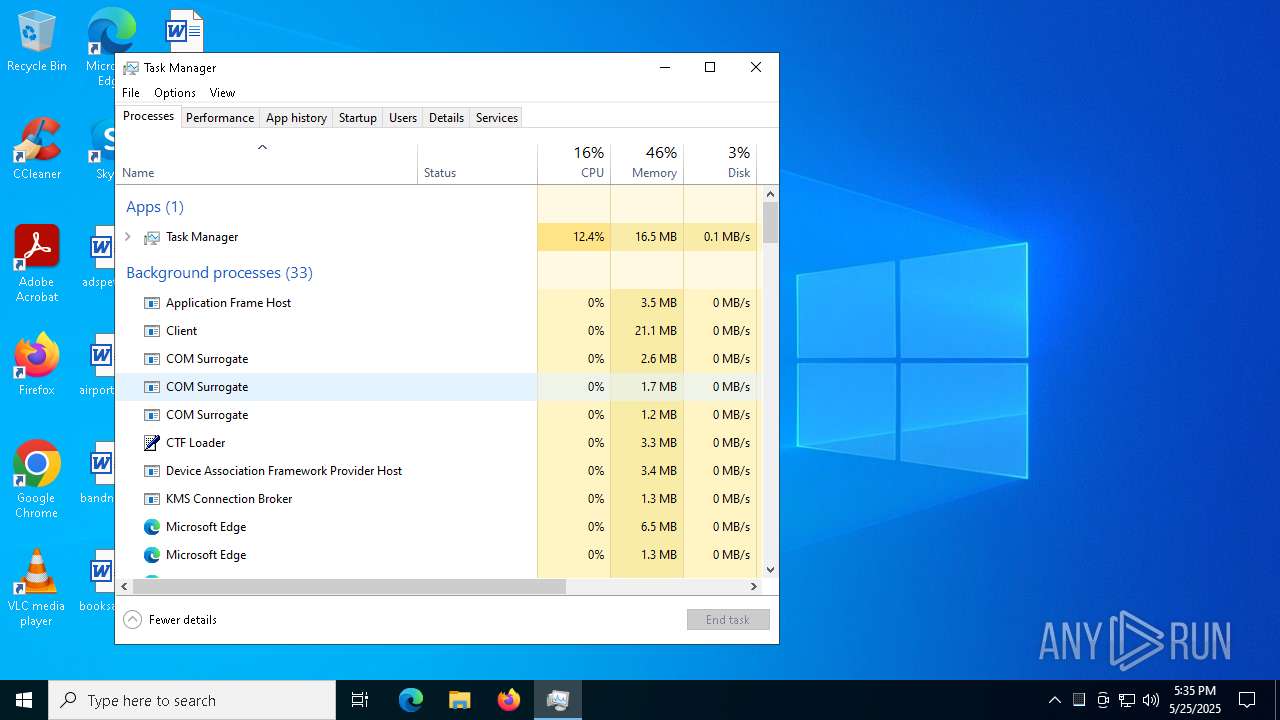
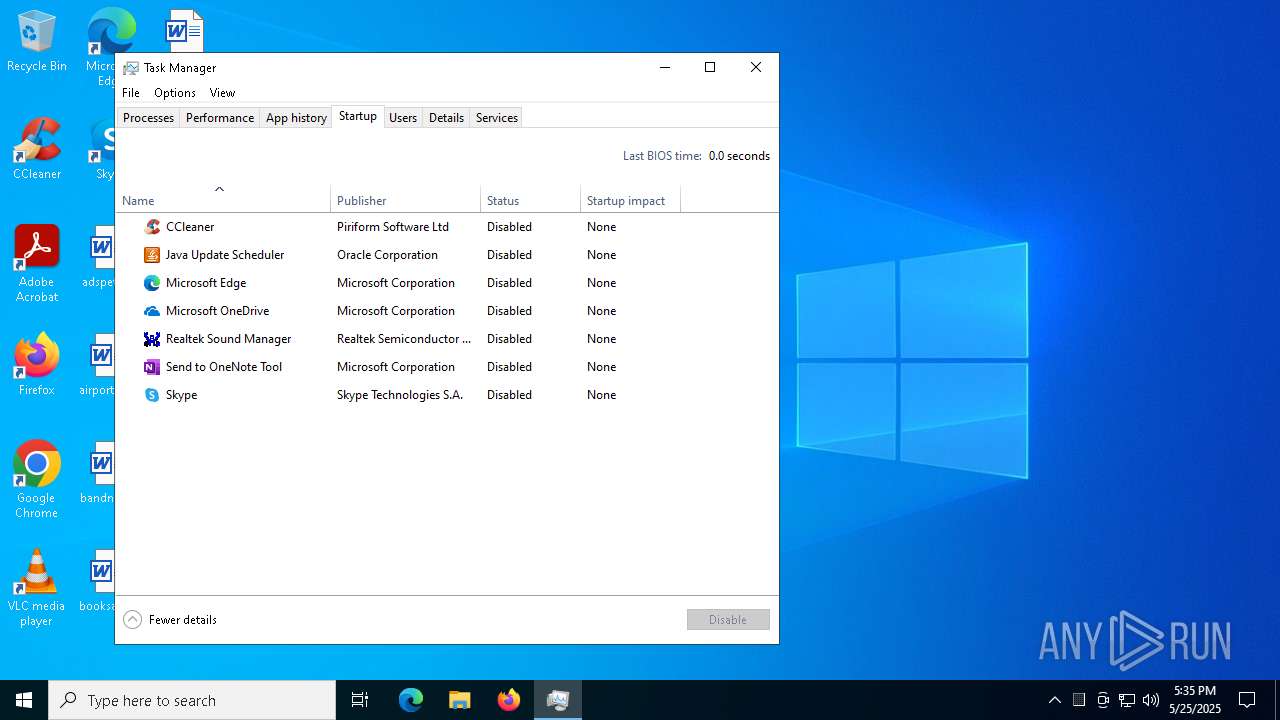
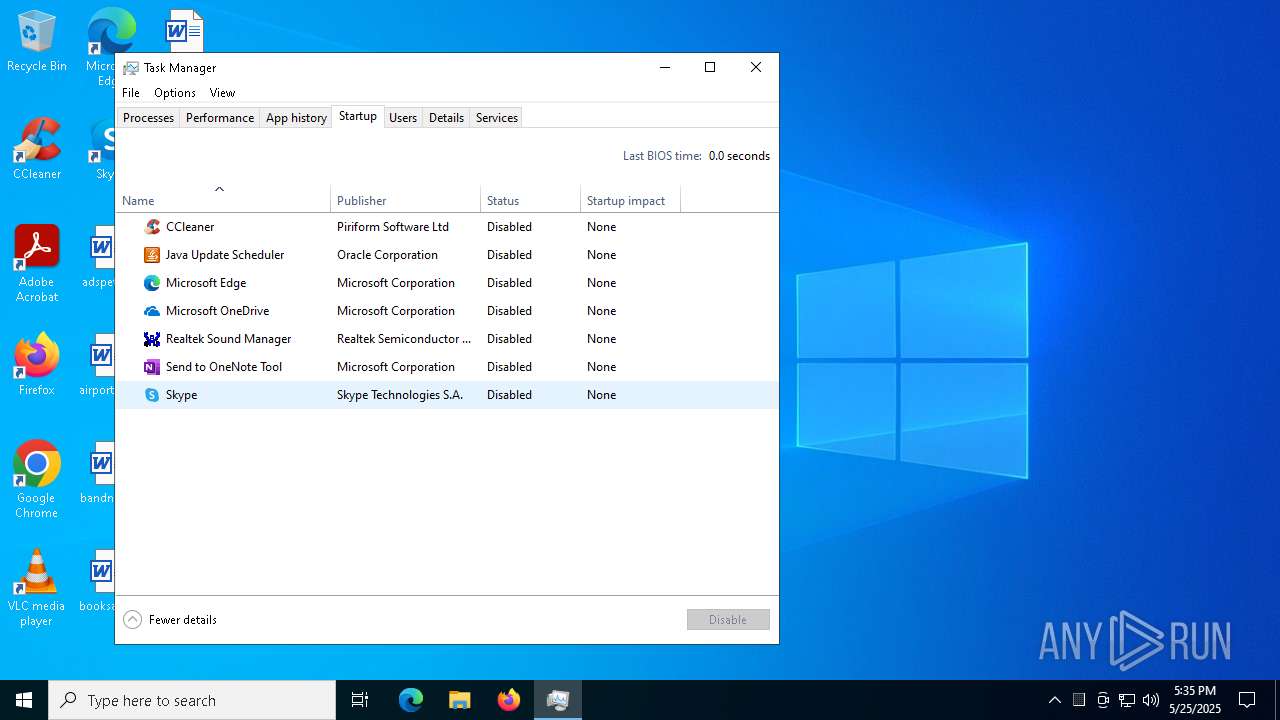
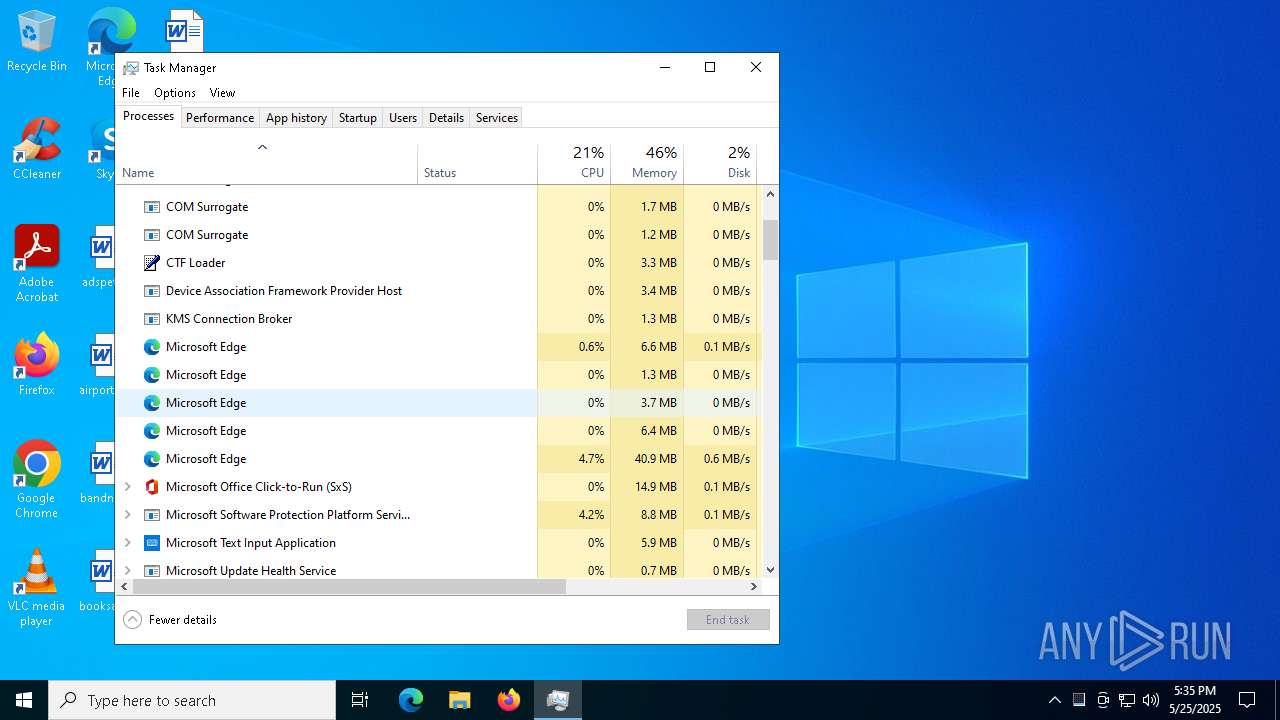
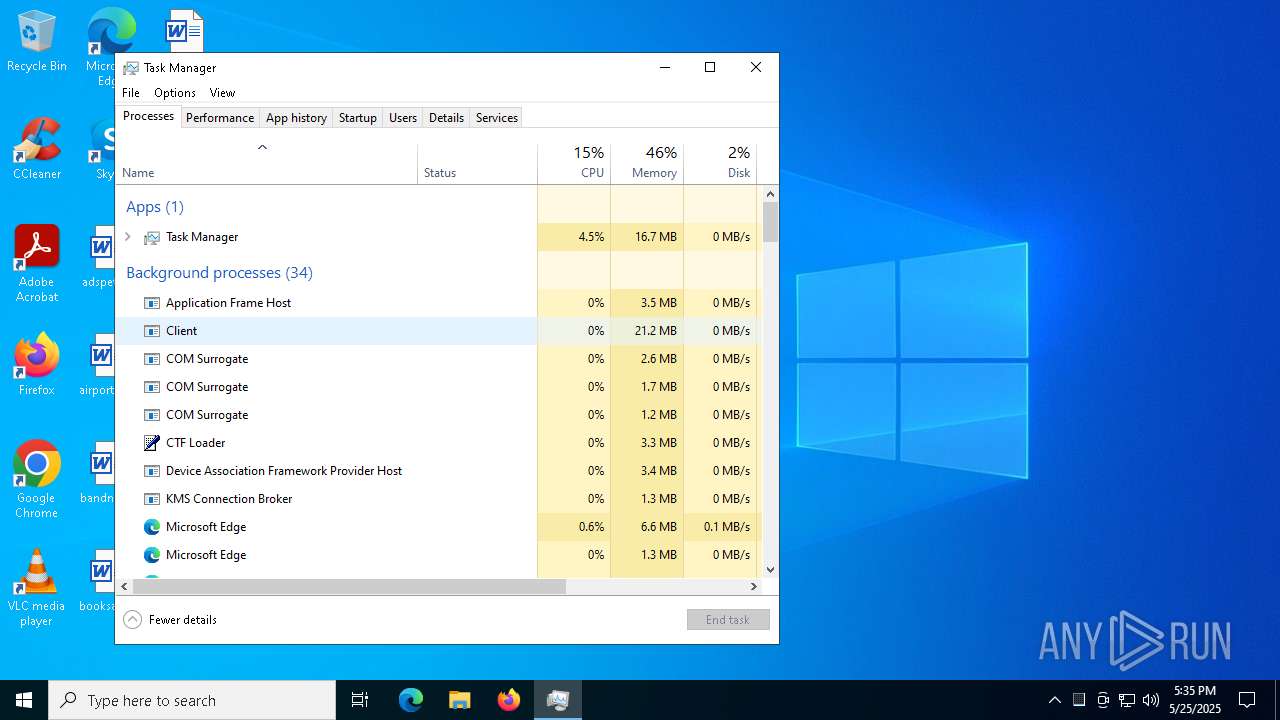
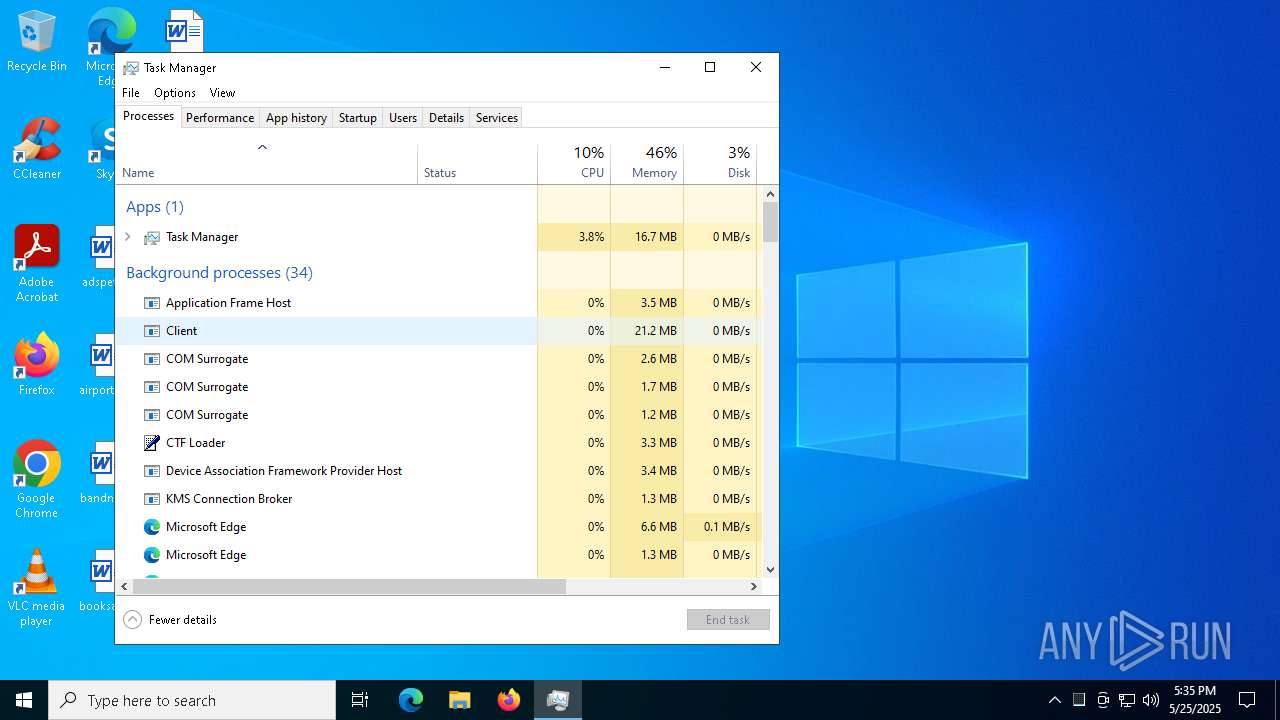
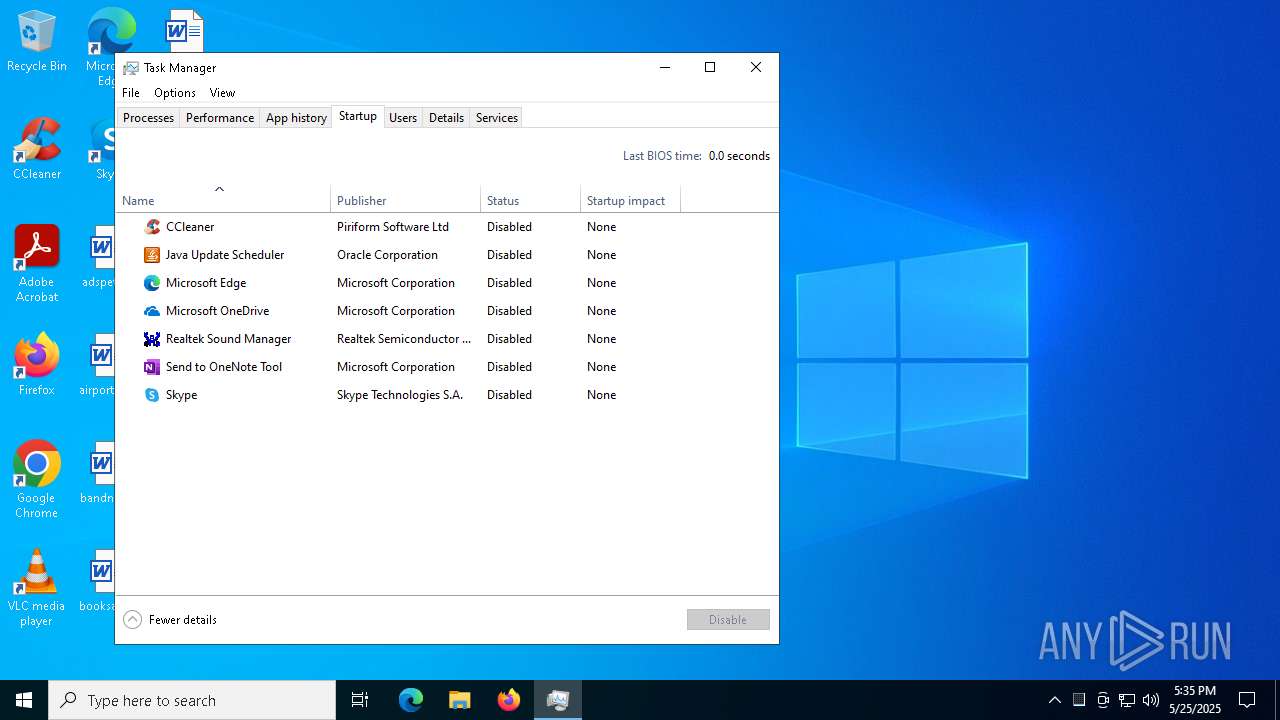
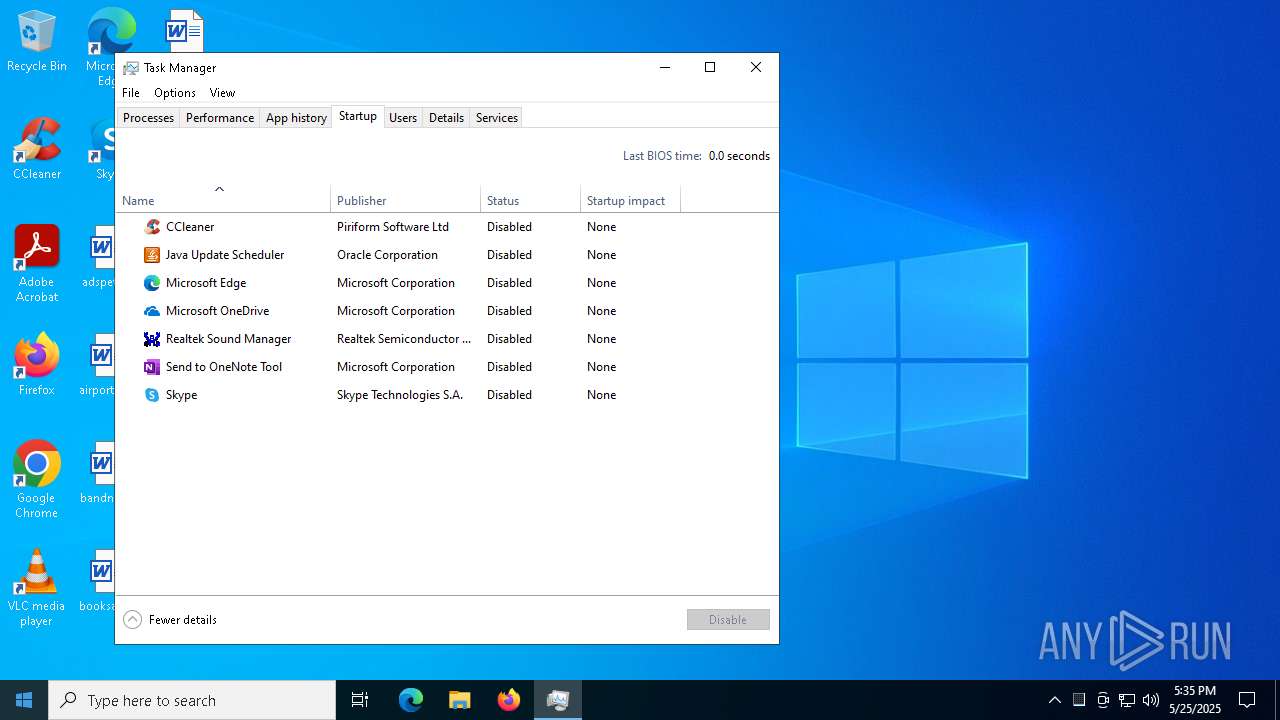
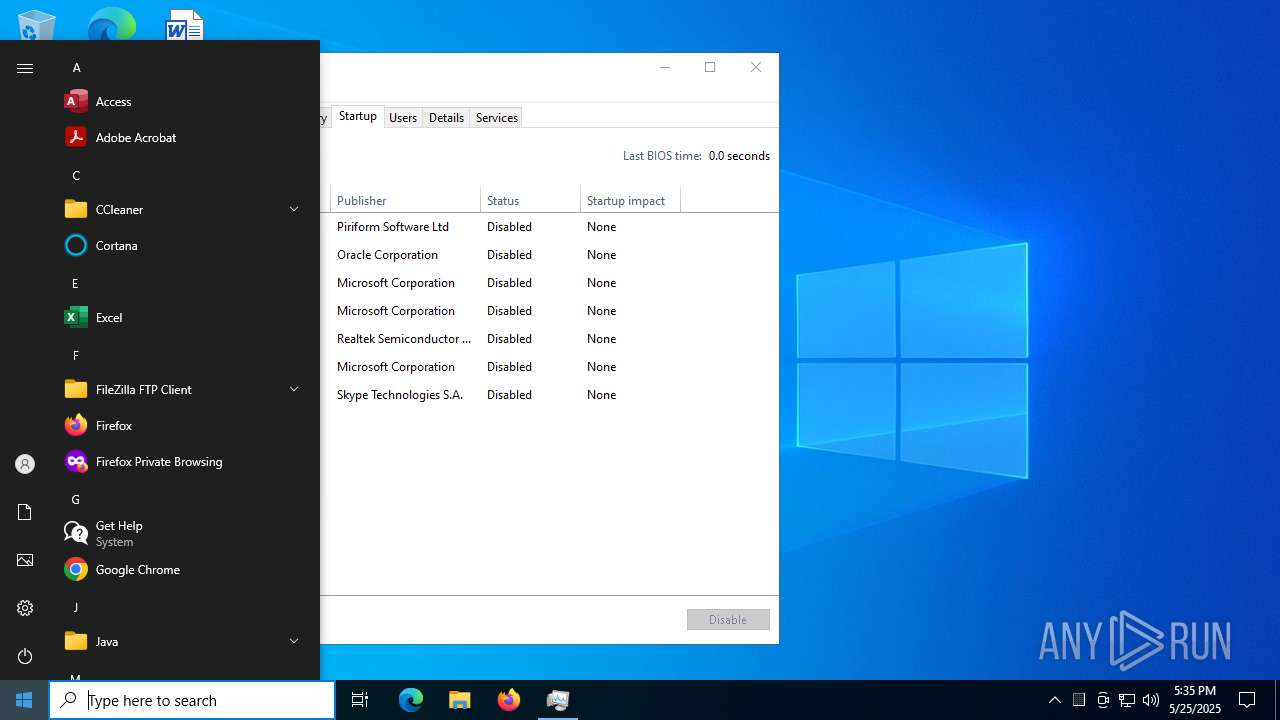
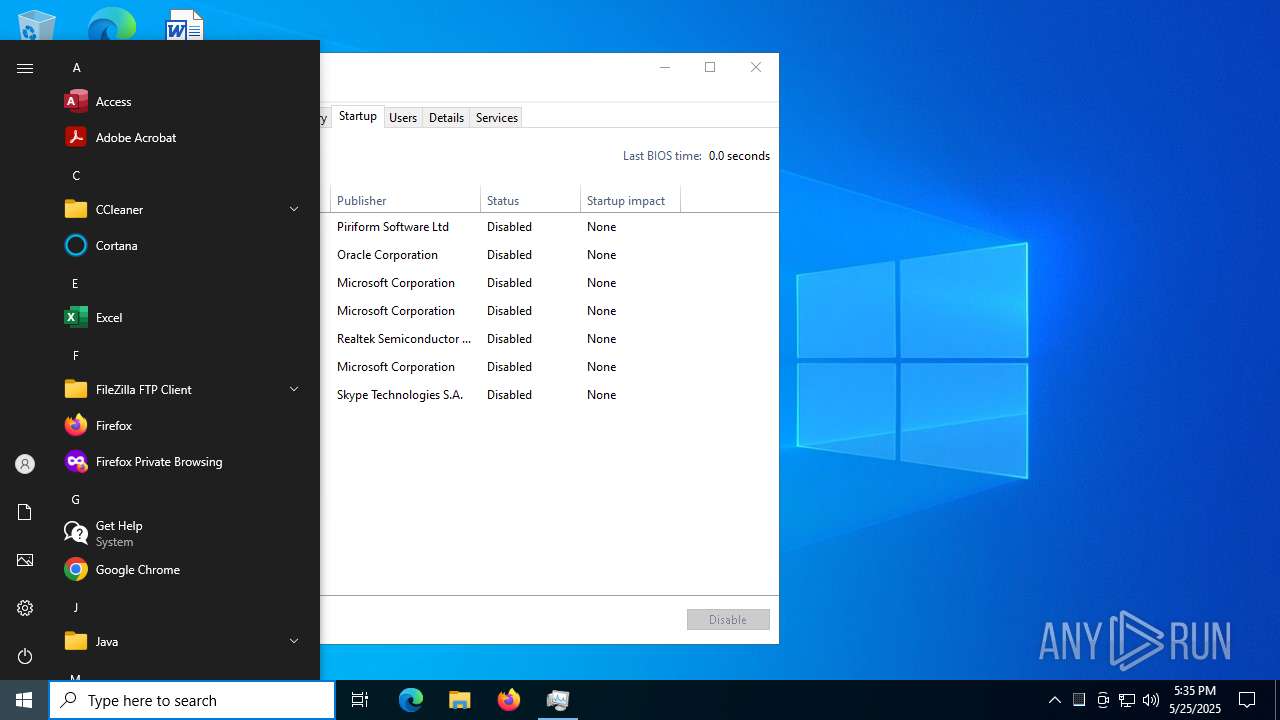
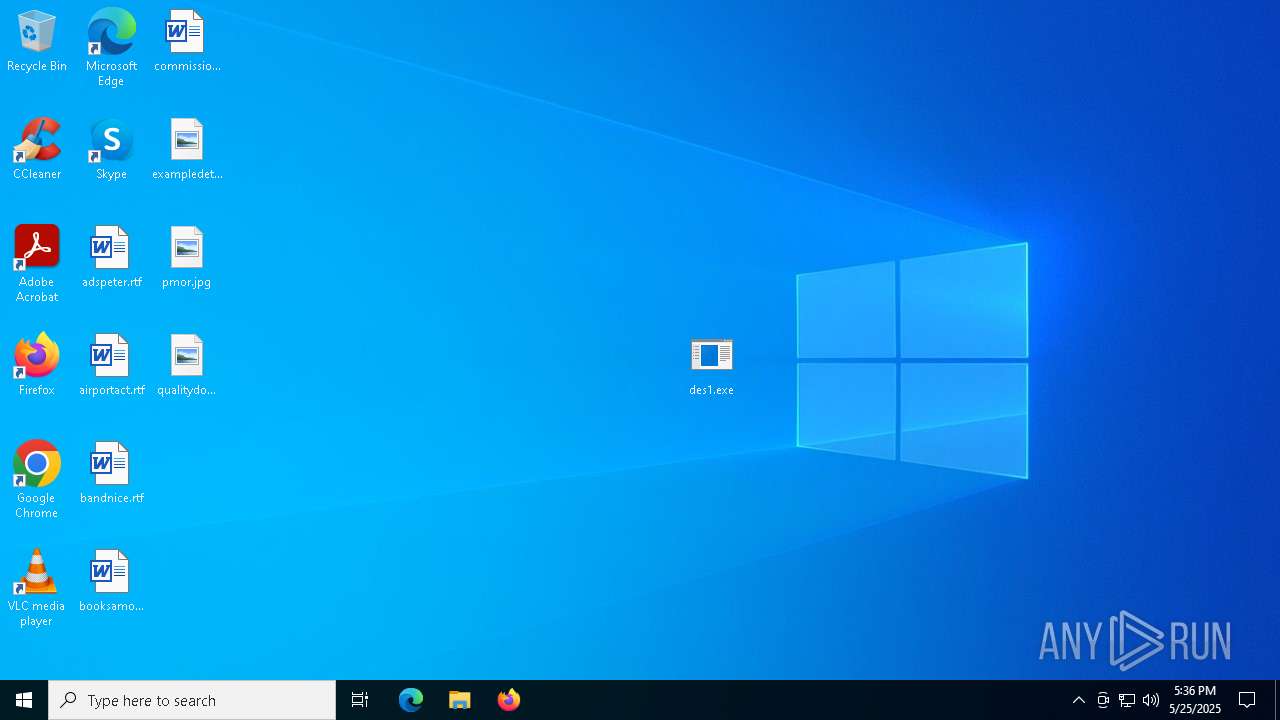
Manual execution by a user
- des1.exe (PID: 1164)
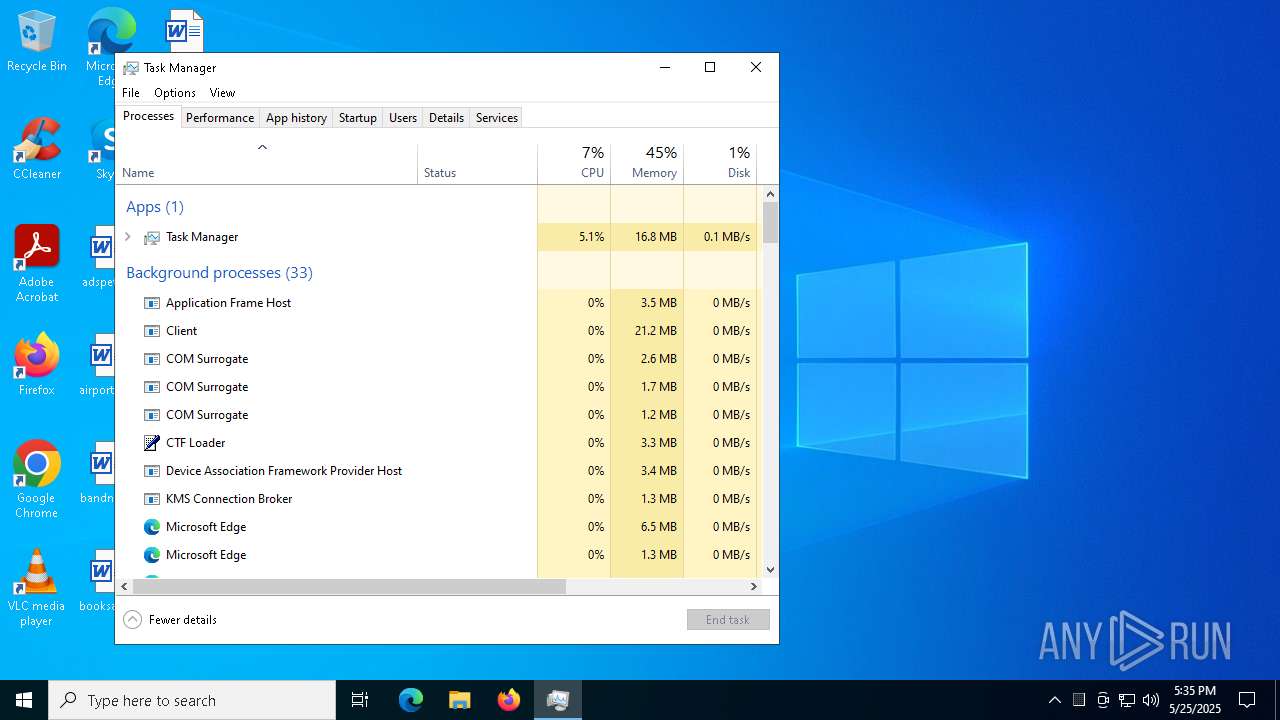
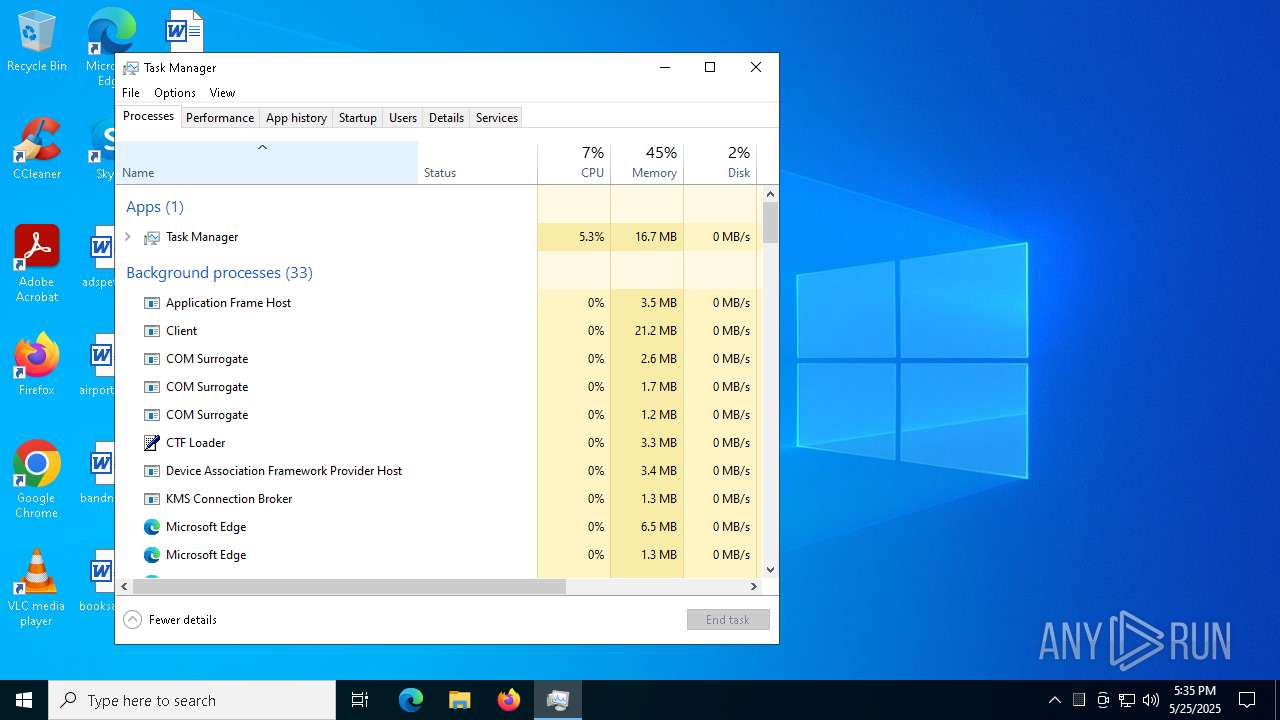
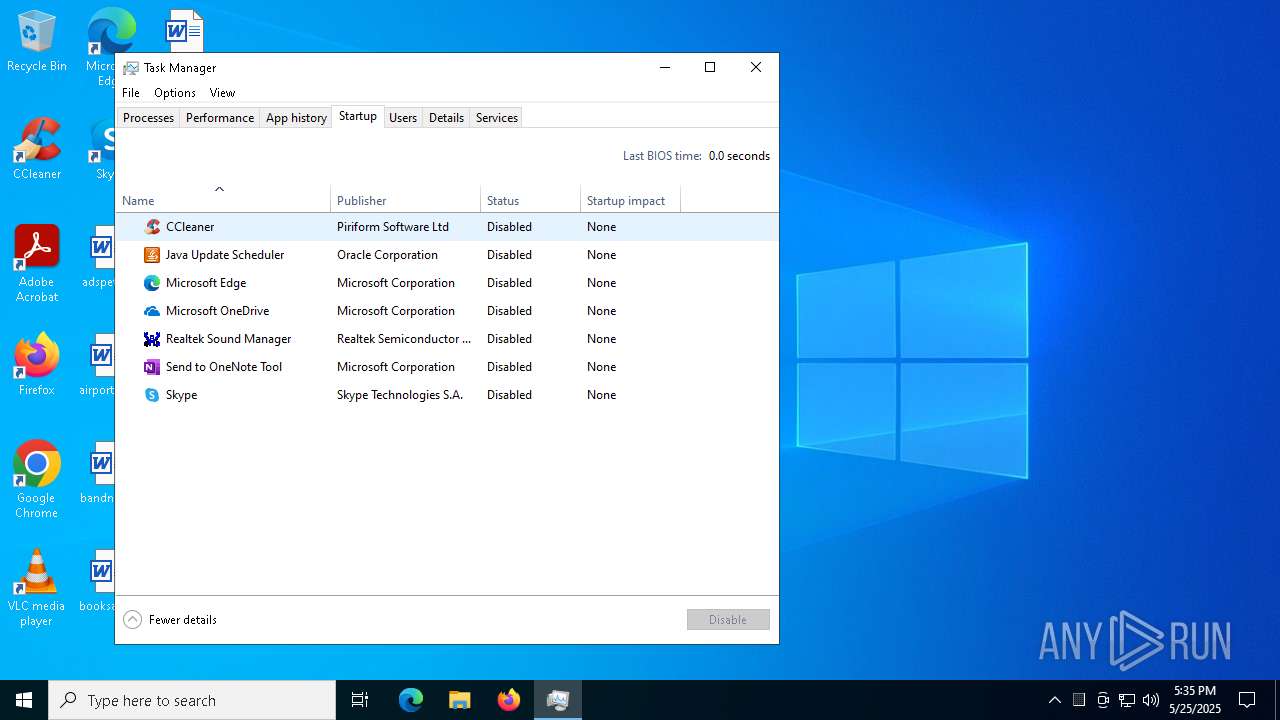
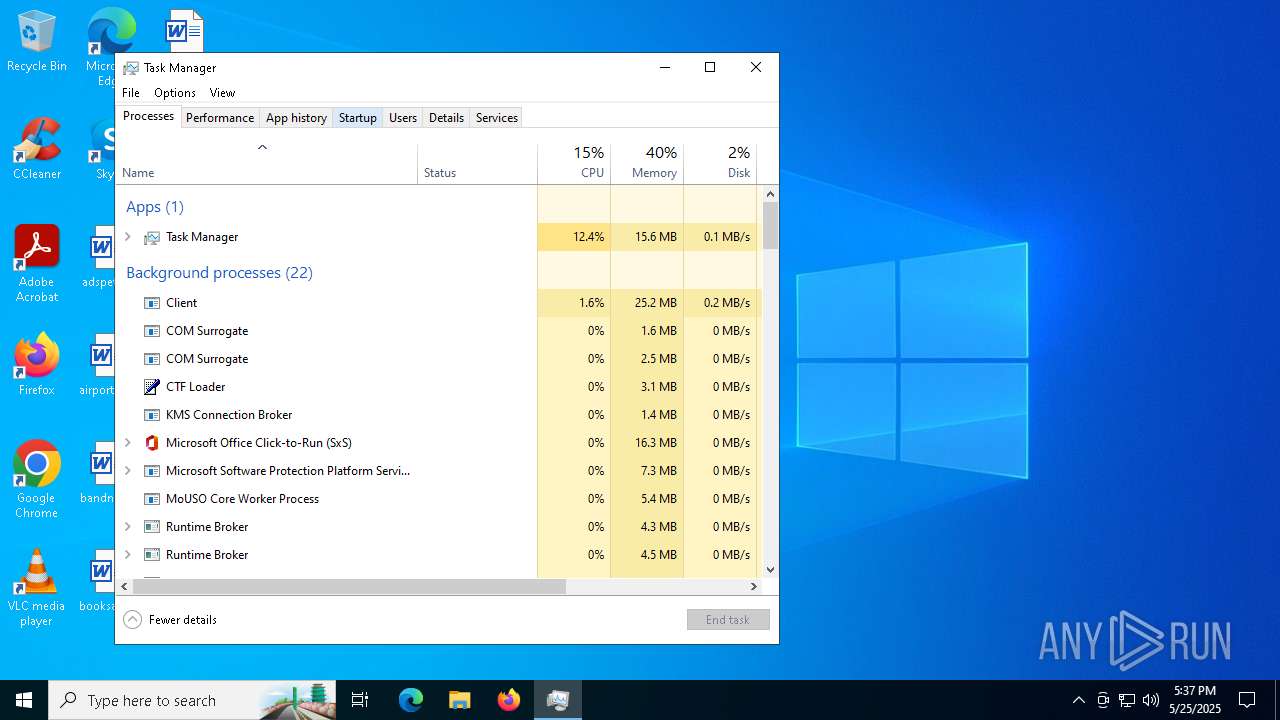
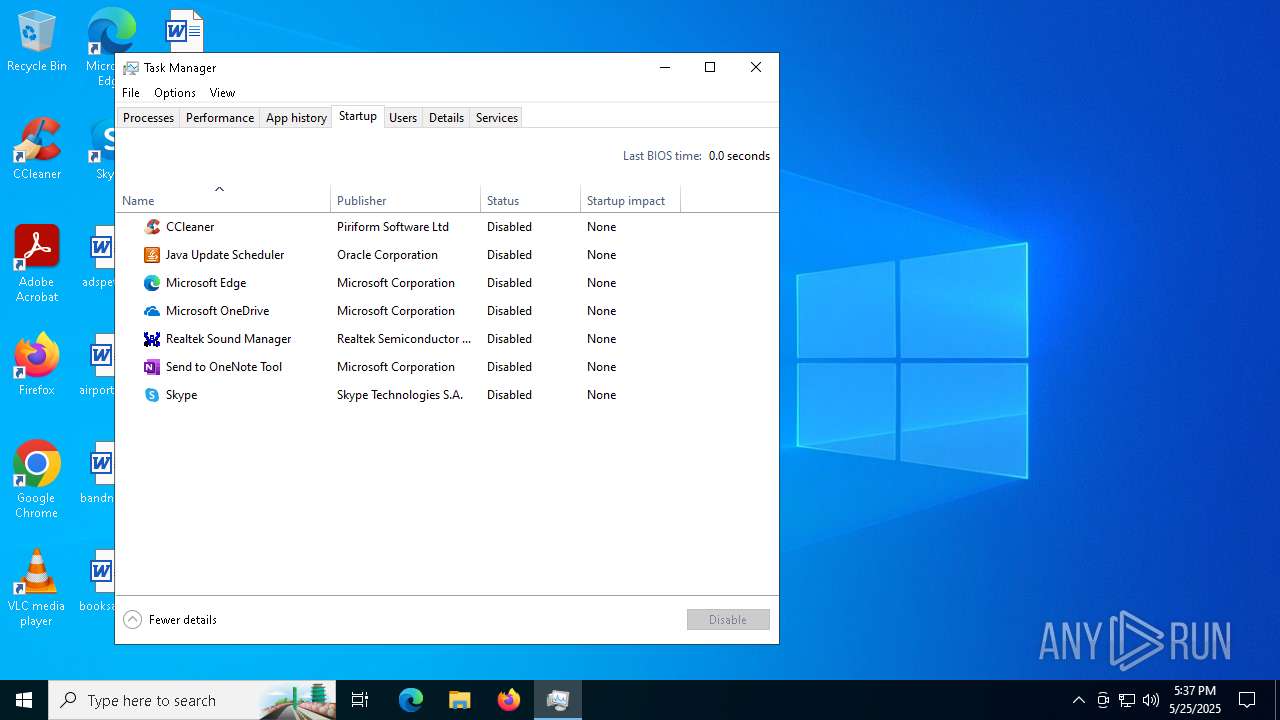
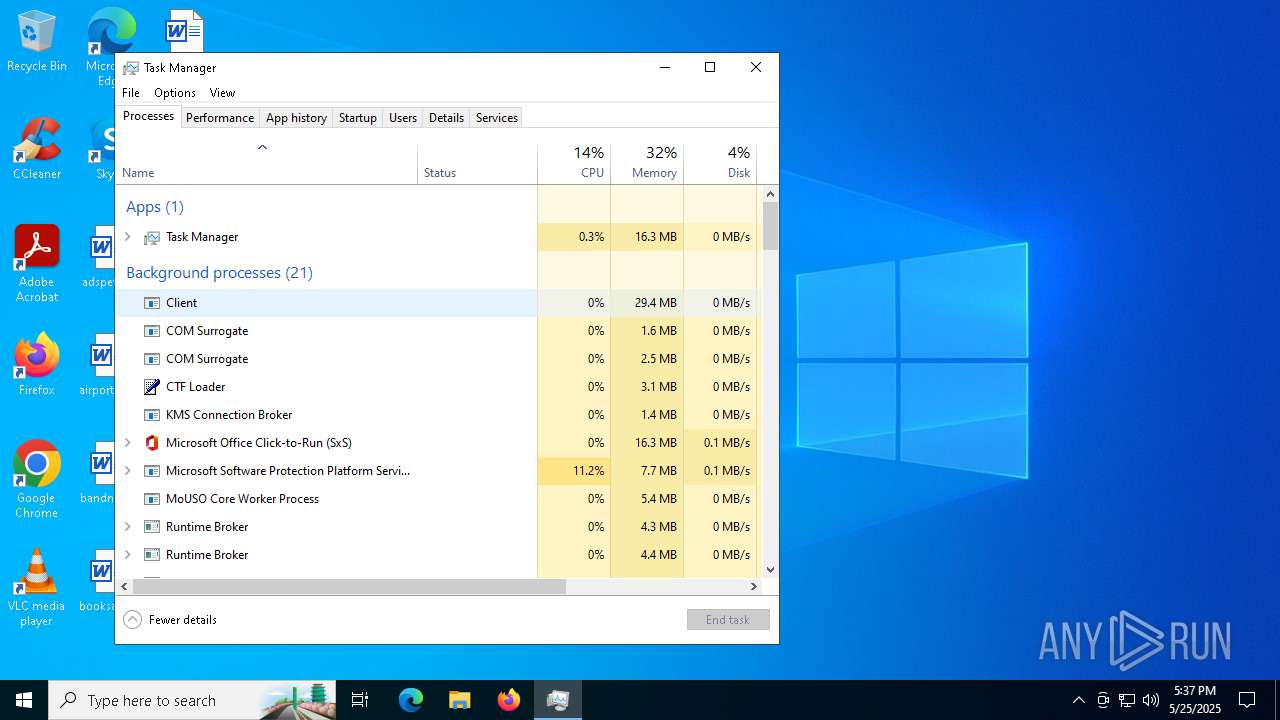
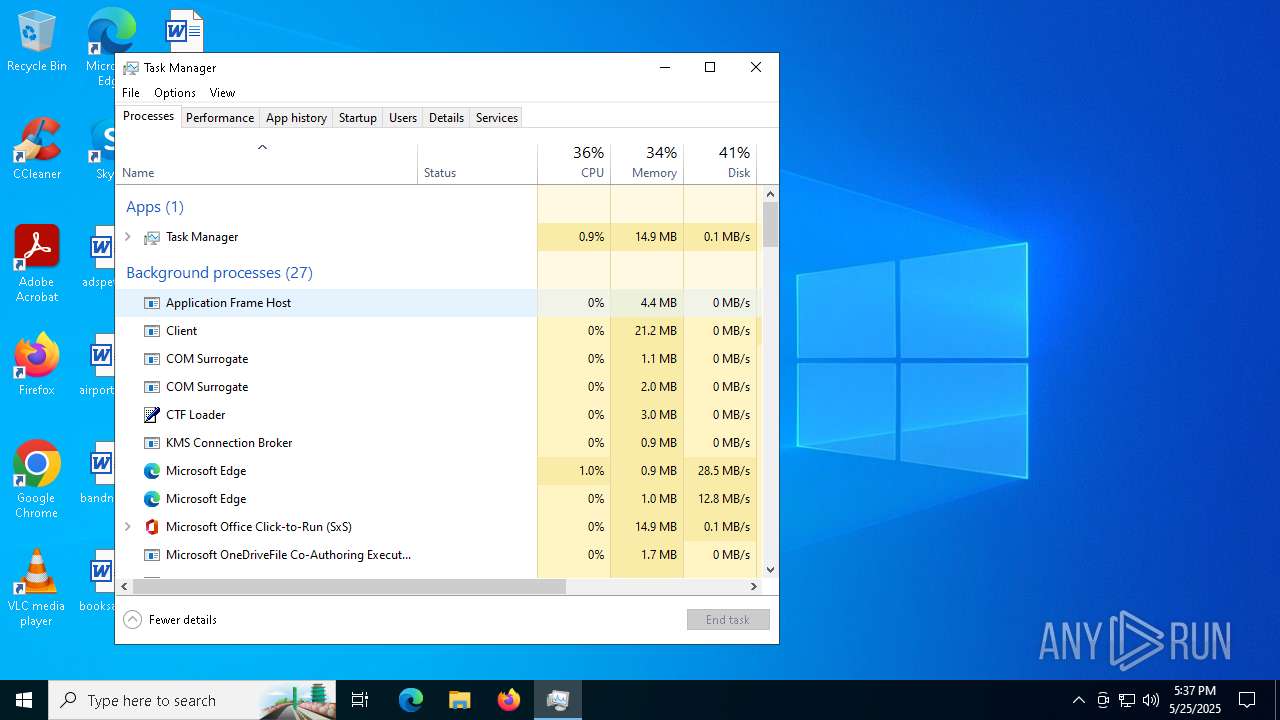
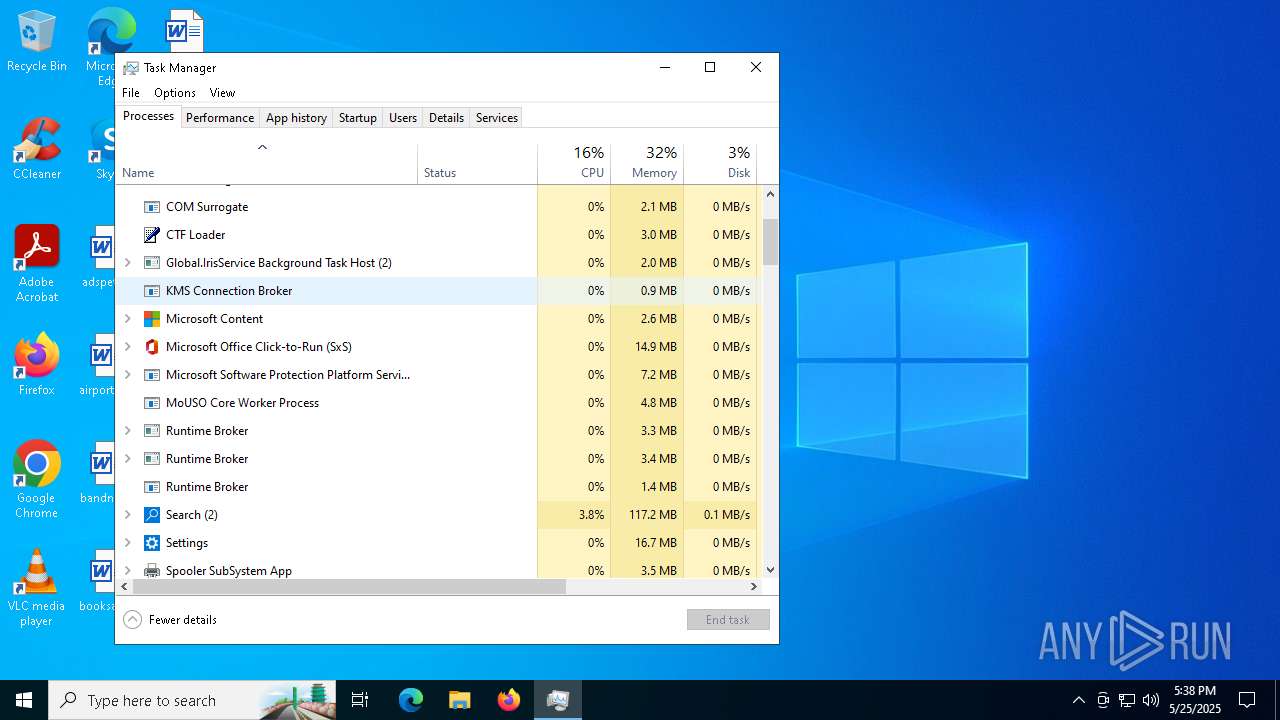
- Taskmgr.exe (PID: 7324)
- Taskmgr.exe (PID: 7240)
- Taskmgr.exe (PID: 6000)
- Taskmgr.exe (PID: 6220)
Reads the machine GUID from the registry
- des1.exe (PID: 1164)
- des1.exe (PID: 6372)
Process checks computer location settings
- des1.exe (PID: 1164)
Creates files or folders in the user directory
- des1.exe (PID: 6372)
Reads the time zone
- des1.exe (PID: 6372)
Reads CPU info
- des1.exe (PID: 6372)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 7324)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
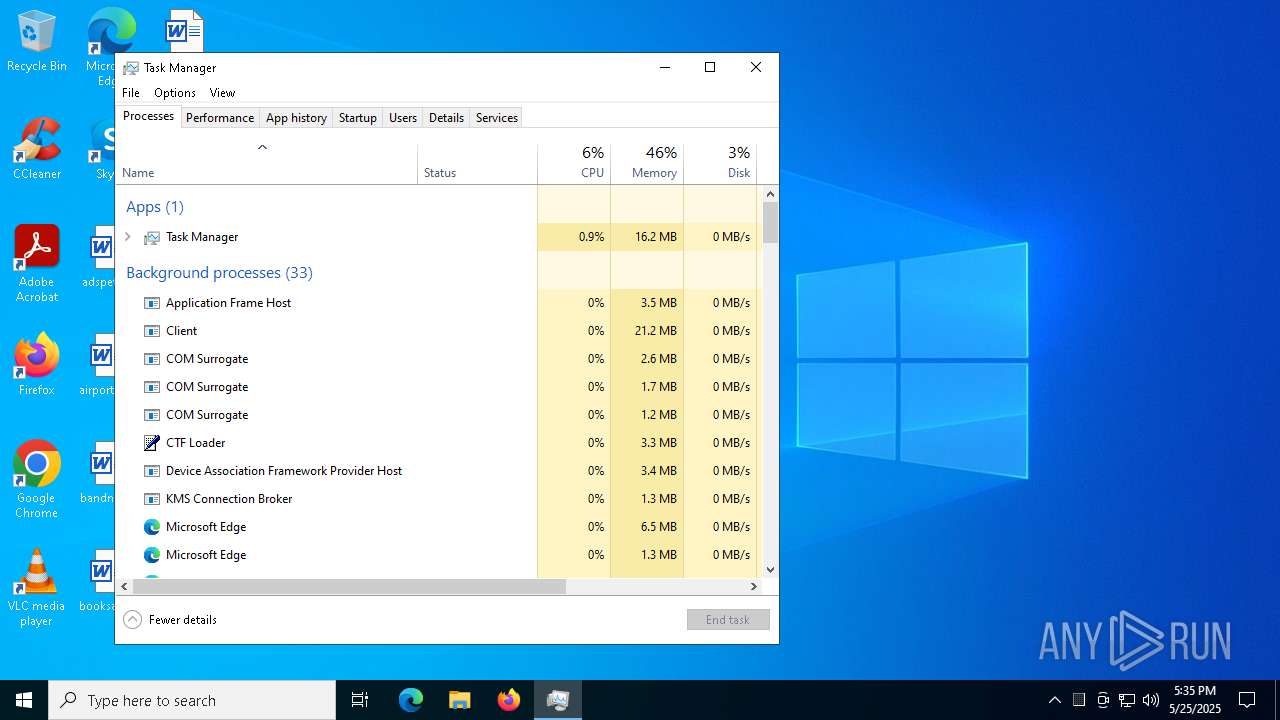
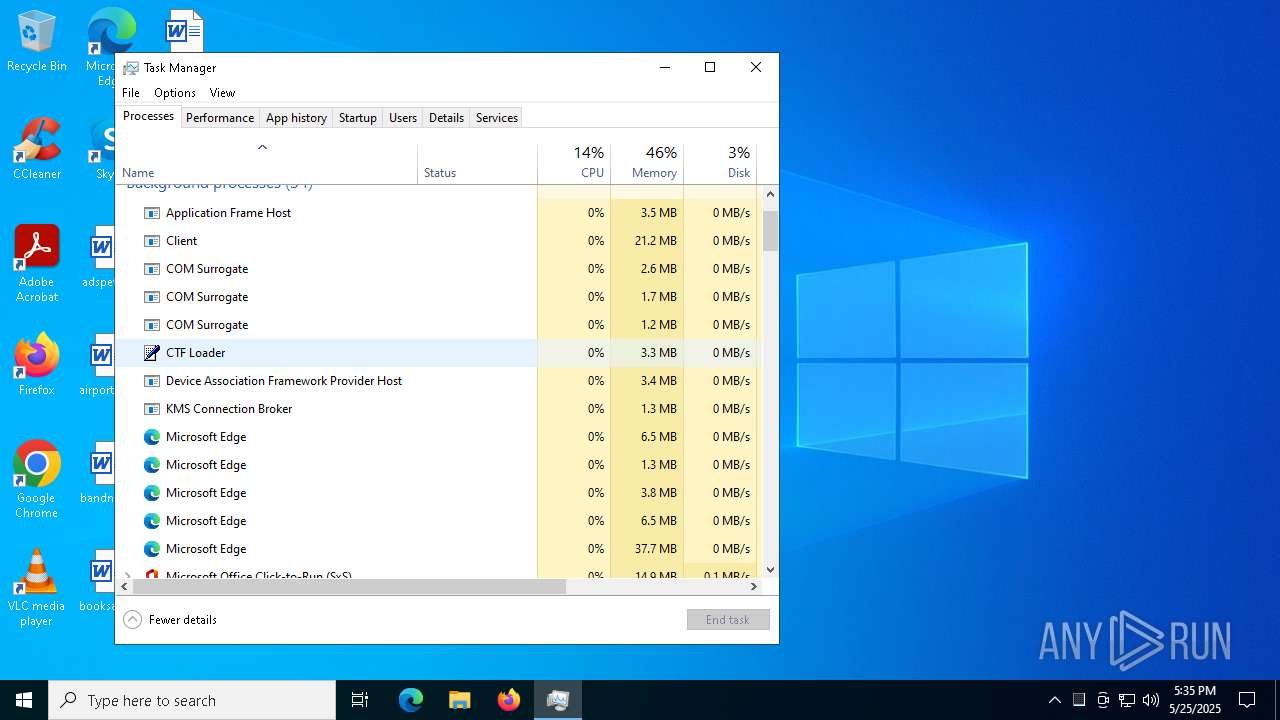
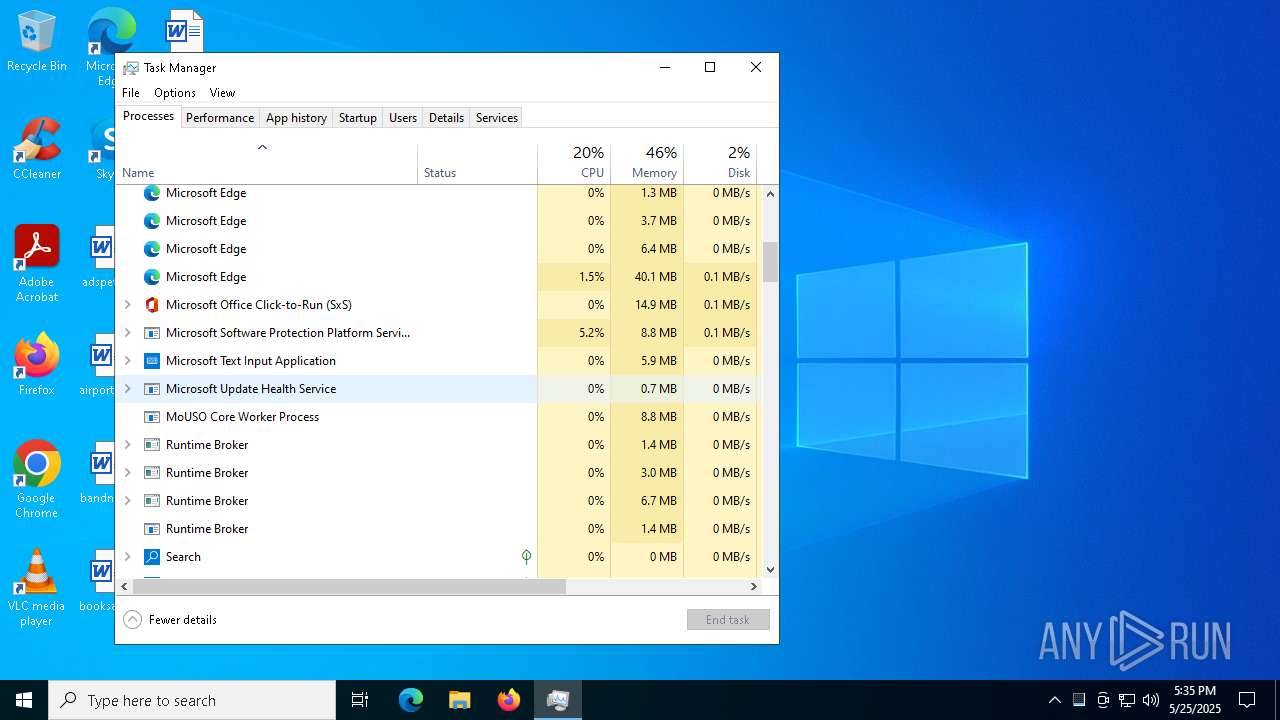
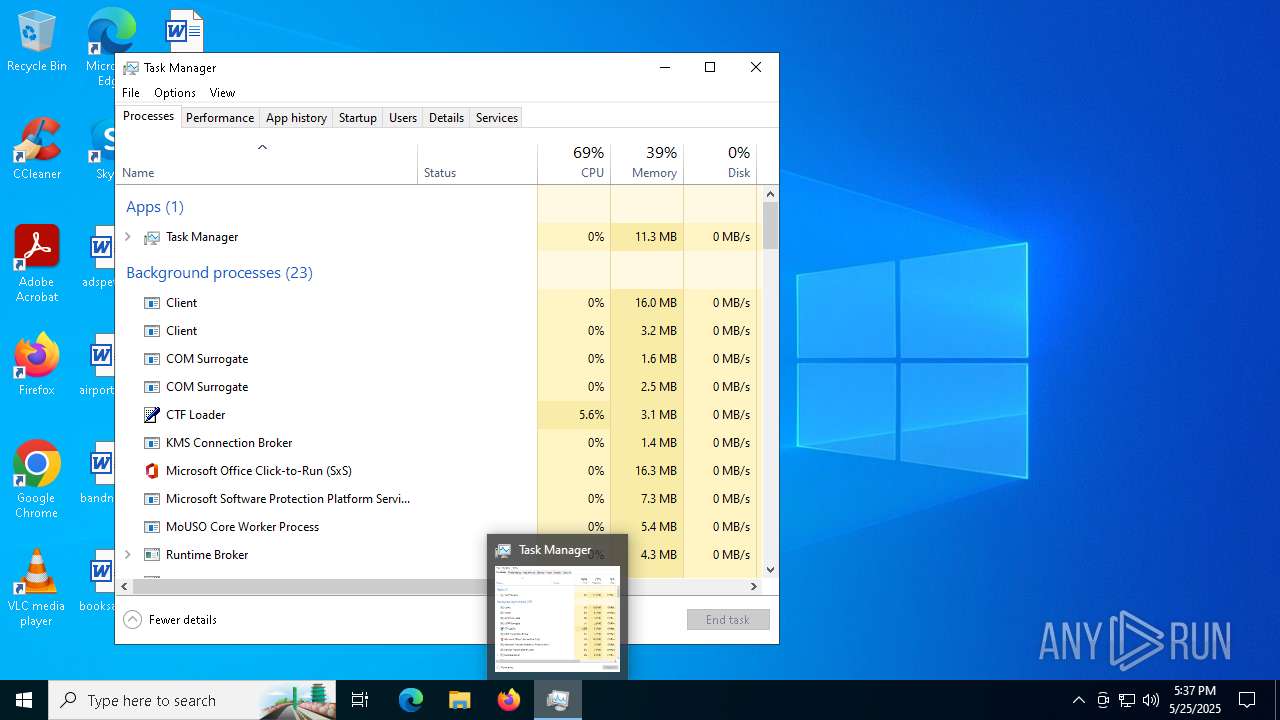
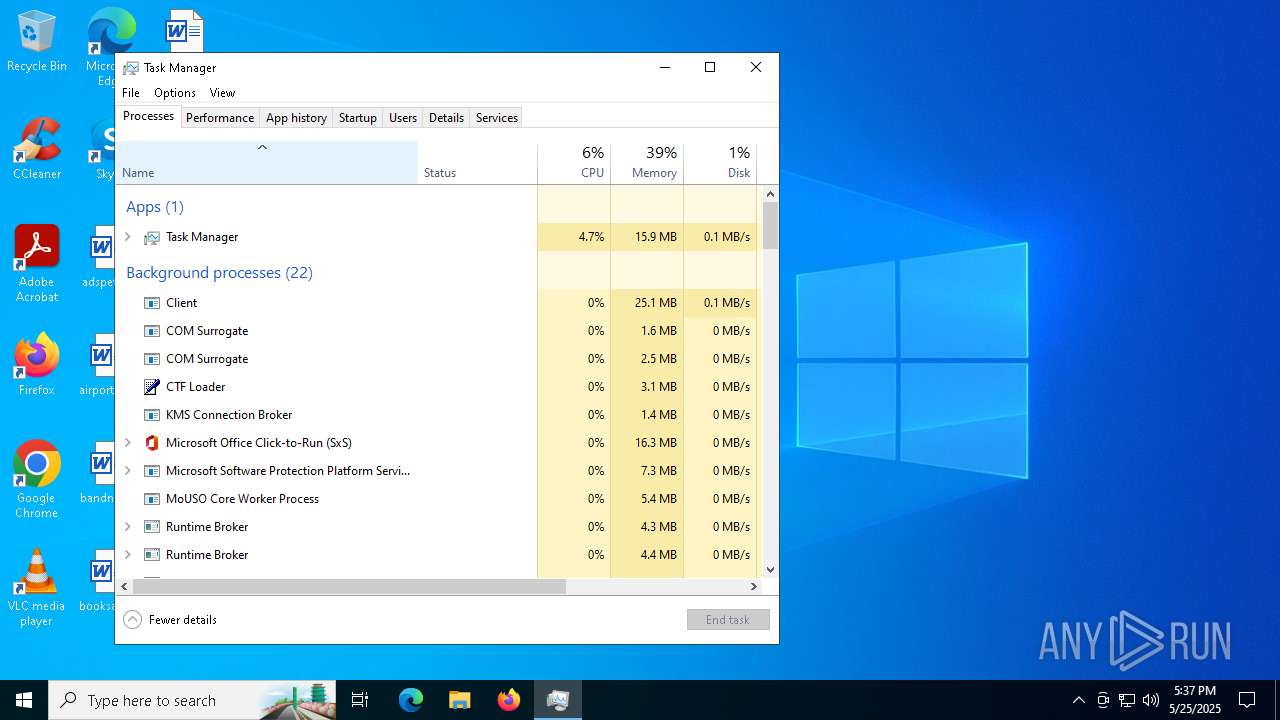
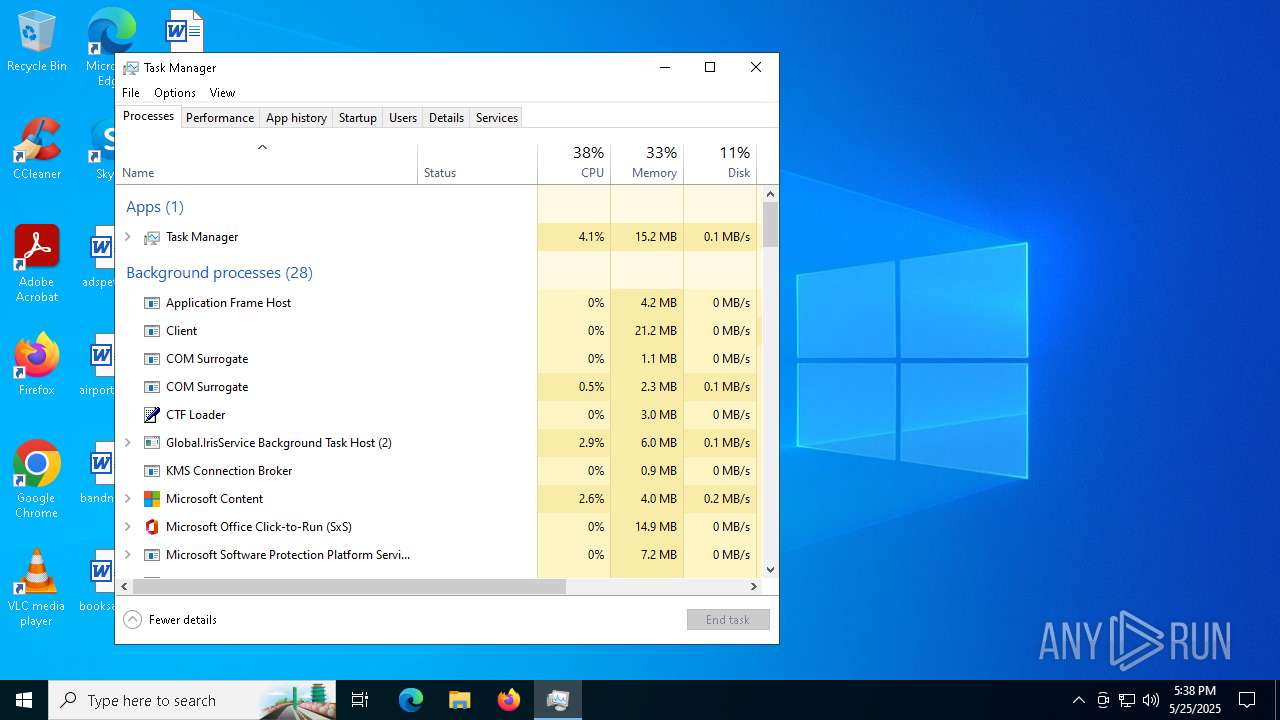
Total processes
342
Monitored processes
58
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x290,0x294,0x298,0x288,0x2a0,0x7ffc88825fd8,0x7ffc88825fe4,0x7ffc88825ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4936 --field-trial-handle=2364,i,10482584891400636031,16380011895499382635,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1164 | "C:\Users\admin\Desktop\des1.exe" | C:\Users\admin\Desktop\des1.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Client Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1240 | "CMD" /c SchTaSKs /create /f /sc minute /mo -1 /tn "destrio" /tr "C:\Users\admin\AppData\Roaming\destrio.exe" /RL HIGHEST & exit | C:\Windows\System32\cmd.exe | — | des1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2147500037 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2164 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2852 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=4628 --field-trial-handle=2292,i,6507424637954320137,1392518003872652189,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3300 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=2712 --field-trial-handle=2364,i,10482584891400636031,16380011895499382635,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4128 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 051
Read events
20 994
Write events
55
Delete events
2
Modification events
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 2A1087878F942F00 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197212 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {833E8285-B563-4830-BBEE-8A93207DCCE4} | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197212 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E11D259F-C6BD-4DA3-B4E9-5FCCCF5AB723} | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 3E4A7D878F942F00 | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (4776) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 1 | |||
Executable files
14
Suspicious files
157
Text files
65
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bf2b.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bf4a.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bf5a.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bf5a.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bf6a.TMP | — | |
MD5:— | SHA256:— | |||
| 4776 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
102
DNS requests
76
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.29:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3096 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8120 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748536276&P2=404&P3=2&P4=jNimNWYP08u0LxnoaUK2guS25hh%2fBhnhP2PyqqU5bbmUzdT%2b8iZpO%2bhwzt2HoWXEV9%2bOn%2b4DSKq64QyvgWlzwg%3d%3d | unknown | — | — | whitelisted |
3096 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8120 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748536276&P2=404&P3=2&P4=jNimNWYP08u0LxnoaUK2guS25hh%2fBhnhP2PyqqU5bbmUzdT%2b8iZpO%2bhwzt2HoWXEV9%2bOn%2b4DSKq64QyvgWlzwg%3d%3d | unknown | — | — | whitelisted |
8120 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748536276&P2=404&P3=2&P4=jNimNWYP08u0LxnoaUK2guS25hh%2fBhnhP2PyqqU5bbmUzdT%2b8iZpO%2bhwzt2HoWXEV9%2bOn%2b4DSKq64QyvgWlzwg%3d%3d | unknown | — | — | whitelisted |
8120 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748536276&P2=404&P3=2&P4=jNimNWYP08u0LxnoaUK2guS25hh%2fBhnhP2PyqqU5bbmUzdT%2b8iZpO%2bhwzt2HoWXEV9%2bOn%2b4DSKq64QyvgWlzwg%3d%3d | unknown | — | — | whitelisted |
8120 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2ef98485-cbad-4d99-b4c2-cd4abac73fb4?P1=1748536276&P2=404&P3=2&P4=jNimNWYP08u0LxnoaUK2guS25hh%2fBhnhP2PyqqU5bbmUzdT%2b8iZpO%2bhwzt2HoWXEV9%2bOn%2b4DSKq64QyvgWlzwg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.216.77.29:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4776 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7328 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7328 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
yy.yy |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE DcRAT/Sheet RAT CnC Checkin Using MessagePack |
6372 | des1.exe | Malware Command and Control Activity Detected | REMOTE [ANY.RUN] SheetRat (Ping) |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Server GZIP C2 Traffic |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |
6372 | des1.exe | A Network Trojan was detected | ET MALWARE PureLogs Backdoor Client GZIP C2 Traffic |