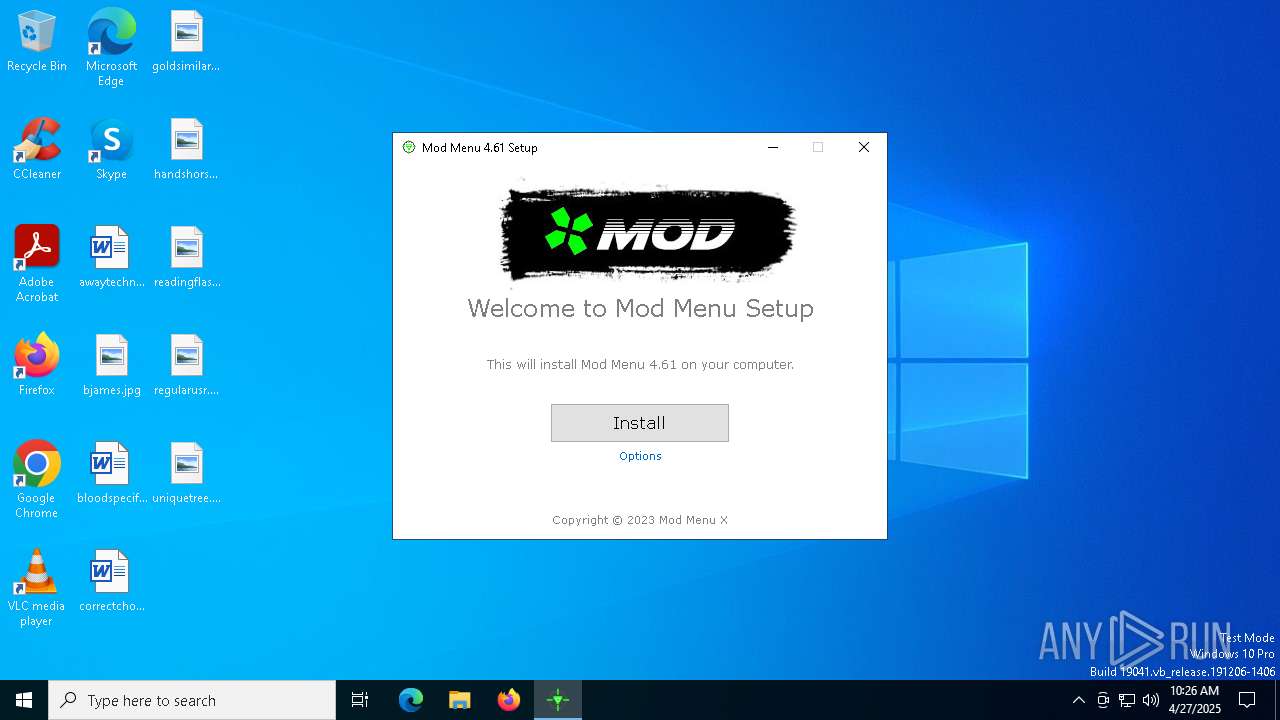
| File name: | Mod Menu.exe |
| Full analysis: | https://app.any.run/tasks/01db5cd2-582a-45e9-bf38-fac1ebed2d93 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2025, 10:25:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 11 sections |
| MD5: | 31F4B9BC75FCA596D7F0A38786665BC4 |
| SHA1: | 85B6813F398C89E897C2AFF0298EA53D030E96EF |
| SHA256: | 5E7761B435A3CD803A547332BA35D8C9E98DC7D47A4FCFBBACBA179748861B33 |
| SSDEEP: | 1572864:HgcyVmf84VC6kJMSefHBg9g54qDbpHFGny:Hiwk4Vb4vsh7dF9 |
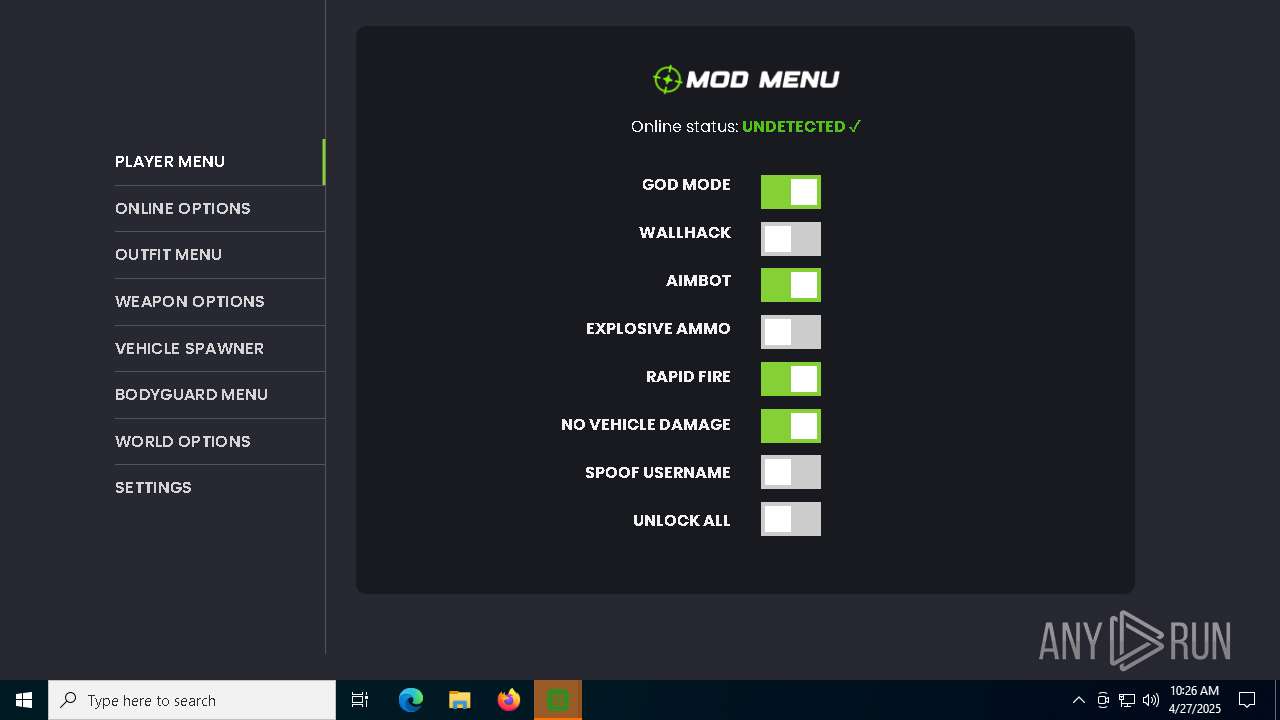
MALICIOUS
Changes the autorun value in the registry
- Mod Menu.exe (PID: 7408)
SUSPICIOUS
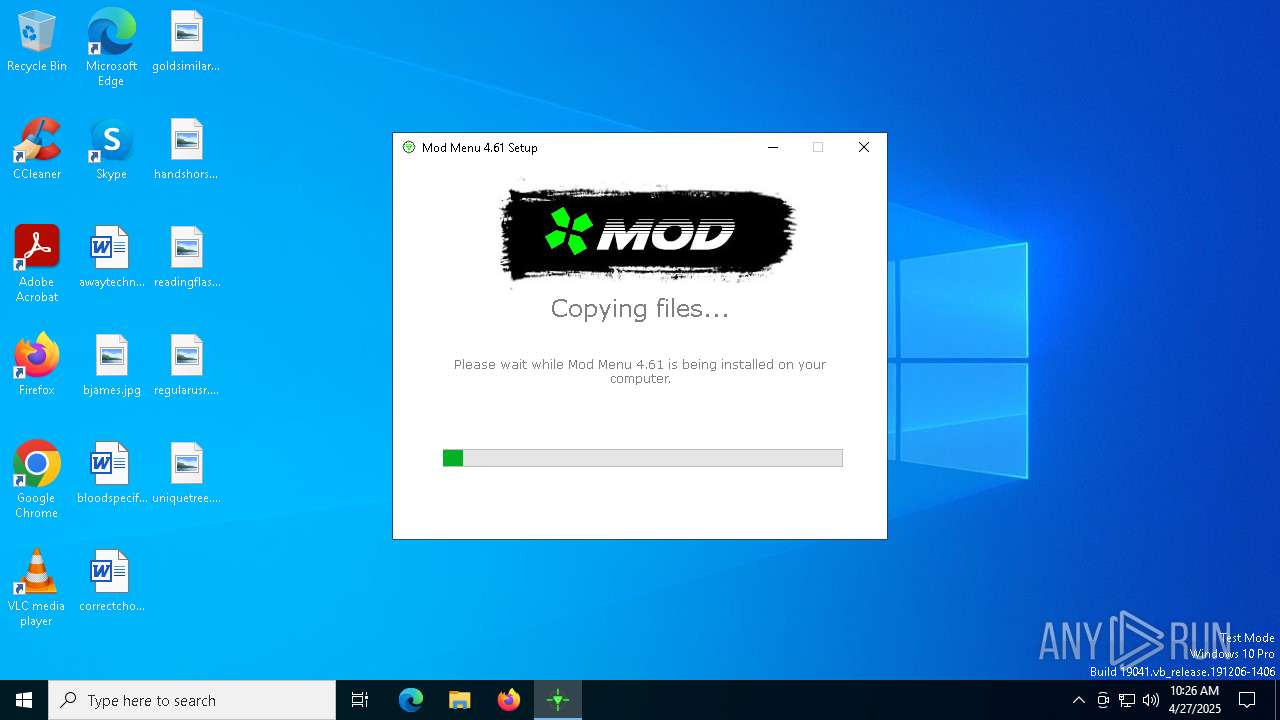
Executable content was dropped or overwritten
- Mod Menu.exe (PID: 7408)
There is functionality for taking screenshot (YARA)
- Mod Menu.exe (PID: 7408)
Reads security settings of Internet Explorer
- Mod Menu.exe (PID: 7408)
Process drops legitimate windows executable
- Mod Menu.exe (PID: 7408)
Application launched itself
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 7836)
INFO
The sample compiled with english language support
- Mod Menu.exe (PID: 7408)
Reads the computer name
- Mod Menu.exe (PID: 7408)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 8116)
- XModz Mod Menu.exe (PID: 8060)
- XModz Mod Menu.exe (PID: 8108)
- XModz Mod Menu.exe (PID: 8168)
- XModz Mod Menu.exe (PID: 7904)
Creates files or folders in the user directory
- Mod Menu.exe (PID: 7408)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 8116)
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 8168)
Checks supported languages
- Mod Menu.exe (PID: 7408)
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 8060)
- XModz Mod Menu.exe (PID: 8116)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 8108)
- XModz Mod Menu.exe (PID: 8168)
- XModz Mod Menu.exe (PID: 8152)
- XModz Mod Menu.exe (PID: 7244)
- XModz Mod Menu.exe (PID: 7280)
- XModz Mod Menu.exe (PID: 1276)
Create files in a temporary directory
- Mod Menu.exe (PID: 7408)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7904)
Auto-launch of the file from Registry key
- Mod Menu.exe (PID: 7408)
Compiled with Borland Delphi (YARA)
- Mod Menu.exe (PID: 7408)
Process checks computer location settings
- Mod Menu.exe (PID: 7408)
- XModz Mod Menu.exe (PID: 8152)
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7244)
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 7280)
- XModz Mod Menu.exe (PID: 1276)
Manual execution by a user
- XModz Mod Menu.exe (PID: 7836)
Reads Environment values
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 7244)
- XModz Mod Menu.exe (PID: 8152)
Reads product name
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 8152)
- XModz Mod Menu.exe (PID: 7244)
Checks proxy server information
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7904)
- slui.exe (PID: 7204)
Reads the machine GUID from the registry
- XModz Mod Menu.exe (PID: 7904)
- XModz Mod Menu.exe (PID: 7836)
Reads the software policy settings
- XModz Mod Menu.exe (PID: 7836)
- XModz Mod Menu.exe (PID: 7904)
- slui.exe (PID: 7204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:07:02 10:01:56+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 2515456 |
| InitializedDataSize: | 448000 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x267ce0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Unknown |
| FileDescription: | Installation |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | (c) |
| ProductName: | Setup |
| ProductVersion: | 1.0.0.0 |
| ProgramID: | com.embarcadero.Setup |
Total processes
133
Monitored processes
12
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1276 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --app-user-model-id=xmodz-mod-menu-nativefier-e5a4a8 --app-path="C:\Users\admin\AppData\Roaming\Mod Menu\resources\app" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3092 --field-trial-handle=1708,i,5654625046800358066,17791464386488778389,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 7204 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7244 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --app-user-model-id=xmodz-mod-menu-nativefier-e5a4a8 --app-path="C:\Users\admin\AppData\Roaming\Mod Menu\resources\app" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2340 --field-trial-handle=1768,i,9184608708985635750,13540456011334339739,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 7280 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --app-user-model-id=xmodz-mod-menu-nativefier-e5a4a8 --app-path="C:\Users\admin\AppData\Roaming\Mod Menu\resources\app" --enable-sandbox --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3108 --field-trial-handle=1768,i,9184608708985635750,13540456011334339739,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 7408 | "C:\Users\admin\AppData\Local\Temp\Mod Menu.exe" | C:\Users\admin\AppData\Local\Temp\Mod Menu.exe | explorer.exe | ||||||||||||
User: admin Company: Unknown Integrity Level: MEDIUM Description: Installation Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7836 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | explorer.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 7904 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 8060 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1592 --field-trial-handle=1708,i,5654625046800358066,17791464386488778389,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 8108 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1612 --field-trial-handle=1768,i,9184608708985635750,13540456011334339739,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | — | XModz Mod Menu.exe | |||||||||||
User: admin Company: Jia Hao Integrity Level: LOW Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
| 8116 | "C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\xmodz-mod-menu-nativefier-e5a4a8" --mojo-platform-channel-handle=2044 --field-trial-handle=1708,i,5654625046800358066,17791464386488778389,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | XModz Mod Menu.exe | ||||||||||||
User: admin Company: Jia Hao Integrity Level: MEDIUM Description: XModz Mod Menu Version: 1.0.0 Modules
| |||||||||||||||
Total events
11 267
Read events
11 224
Write events
1
Delete events
42
Modification events
| (PID) Process: | (7408) Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Mod Menu |
Value: C:\Users\admin\AppData\Roaming\Mod Menu\XModz Mod Menu.exe | |||
| (PID) Process: | (7836) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (7836) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (7836) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (7904) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (7904) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (7904) XModz Mod Menu.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
Executable files
7
Suspicious files
150
Text files
19
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Local\Temp\AITMP578\aidatafile.zip | — | |
MD5:— | SHA256:— | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Local\Temp\AITMP578\aisetup.zip | compressed | |
MD5:FB0AE634A9710D2EFEC990845514883E | SHA256:DDD9DA8FDB74D6A2A0B66B30129AA3B17B89F8D2345CFBD8A64C1152E88DDED6 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\locales\cs.pak | binary | |
MD5:DF23ADDC3559428776232B1769BF505E | SHA256:C06AC5459D735F7AC7ED352D9F100C17749FA2A277AF69C25E7AFE0B6954D3C0 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\locales\da.pak | binary | |
MD5:875C8EAA5F2A5DA2D36783024BFF40C7 | SHA256:6EE55E456D12246A4EA677C30BE952ADFB3AB57ACA428516E35056E41E7828B5 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\chrome_100_percent.pak | binary | |
MD5:0CF9DE69DCFD8227665E08C644B9499C | SHA256:D2C299095DBBD3A3CB2B4639E5B3BD389C691397FFD1A681E586F2CFE0E2AB88 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Roaming\Mod Menu\chrome_200_percent.pak | binary | |
MD5:D88936315A5BD83C1550E5B8093EB1E6 | SHA256:F49ABD81E93A05C1E53C1201A5D3A12F2724F52B6971806C8306B512BF66AA25 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Local\Temp\AITMP578\aisetup.ini | text | |
MD5:FB0AE634A9710D2EFEC990845514883E | SHA256:DDD9DA8FDB74D6A2A0B66B30129AA3B17B89F8D2345CFBD8A64C1152E88DDED6 | |||
| 7408 | Mod Menu.exe | C:\Users\admin\AppData\Local\Temp\AITMP578\Englishai.lng | text | |
MD5:AB28EE07335D13FBDEDB1EB31887B5E3 | SHA256:107AE72D54A81096EB7B3D61753F12EA1A1C3C9B17F6D5B7483675E2EC46AD63 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
47
DNS requests
22
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
2104 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
2104 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7608 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2104 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
7608 | SIHClient.exe | 4.175.87.197:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7608 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7608 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
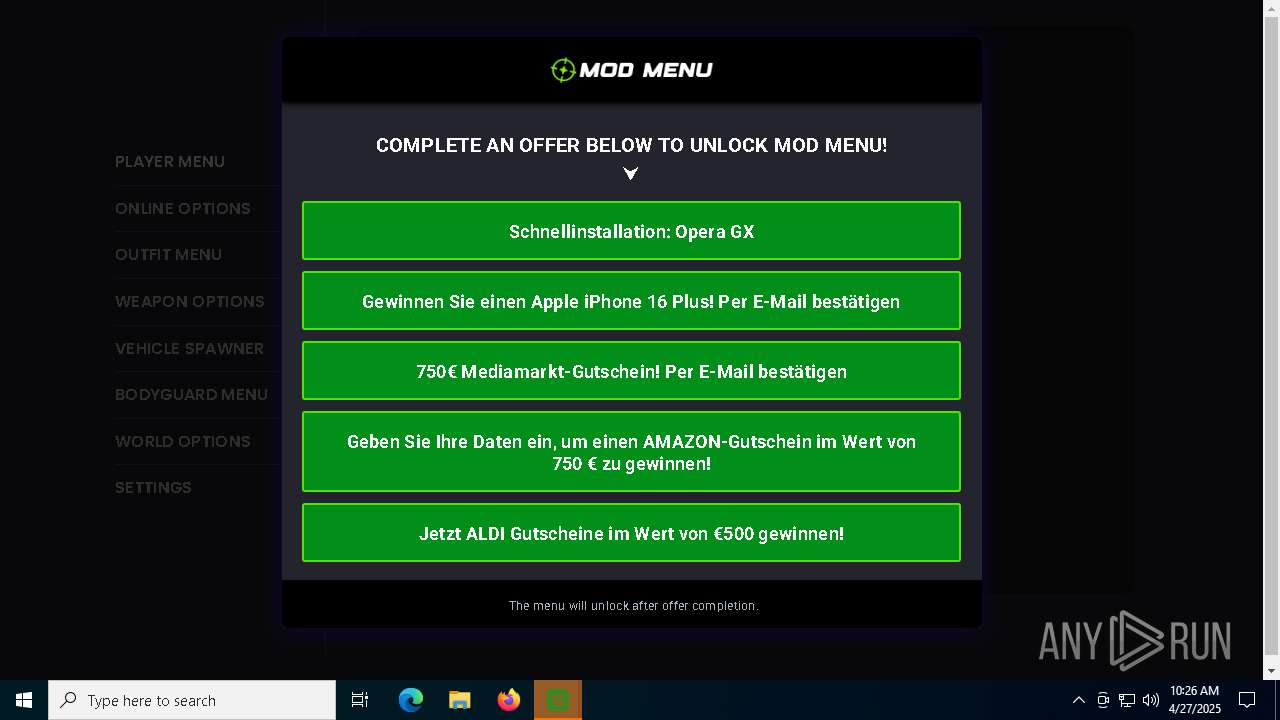
8168 | XModz Mod Menu.exe | 188.114.96.3:443 | modmenu.pages.dev | CLOUDFLARENET | NL | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
modmenu.pages.dev |
| shared |
d3h83s39ga3y3t.cloudfront.net |
| whitelisted |
cdn.jsdelivr.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
8116 | XModz Mod Menu.exe | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |