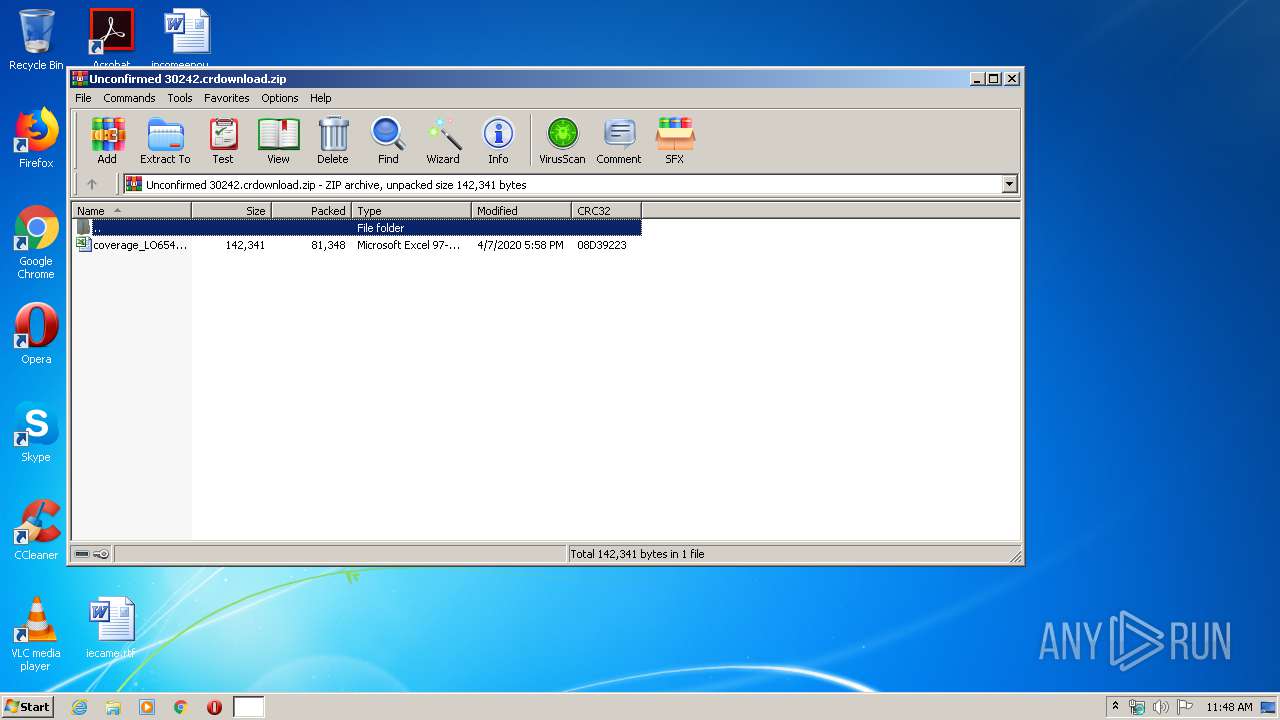
| File name: | Unconfirmed 30242.crdownload |
| Full analysis: | https://app.any.run/tasks/86815d71-e246-47e6-9fcb-30b2a90ae2b9 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 15, 2020, 10:48:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C8B0F289A656B829F10B8B743A8EB621 |
| SHA1: | 5CE9D3C11C09EC6564795997C8EBD28080F7A2AF |
| SHA256: | 5E714F3D4F154A0AE4FDEB10A9609029E196B6FDD7569AFCE4603E4AE635C121 |
| SSDEEP: | 1536:zlaWTYni/0FcKcEaCI70FDU3fNlEKmCcQubzt34voM:zonvcKNaZAFcf7FchogM |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- regsvr32.exe (PID: 2676)
Connects to CnC server
- svchost.exe (PID: 3176)
HANCITOR was detected
- svchost.exe (PID: 3176)
Executable content was dropped or overwritten
- EXCEL.EXE (PID: 3992)
Registers / Runs the DLL via REGSVR32.EXE
- EXCEL.EXE (PID: 3992)
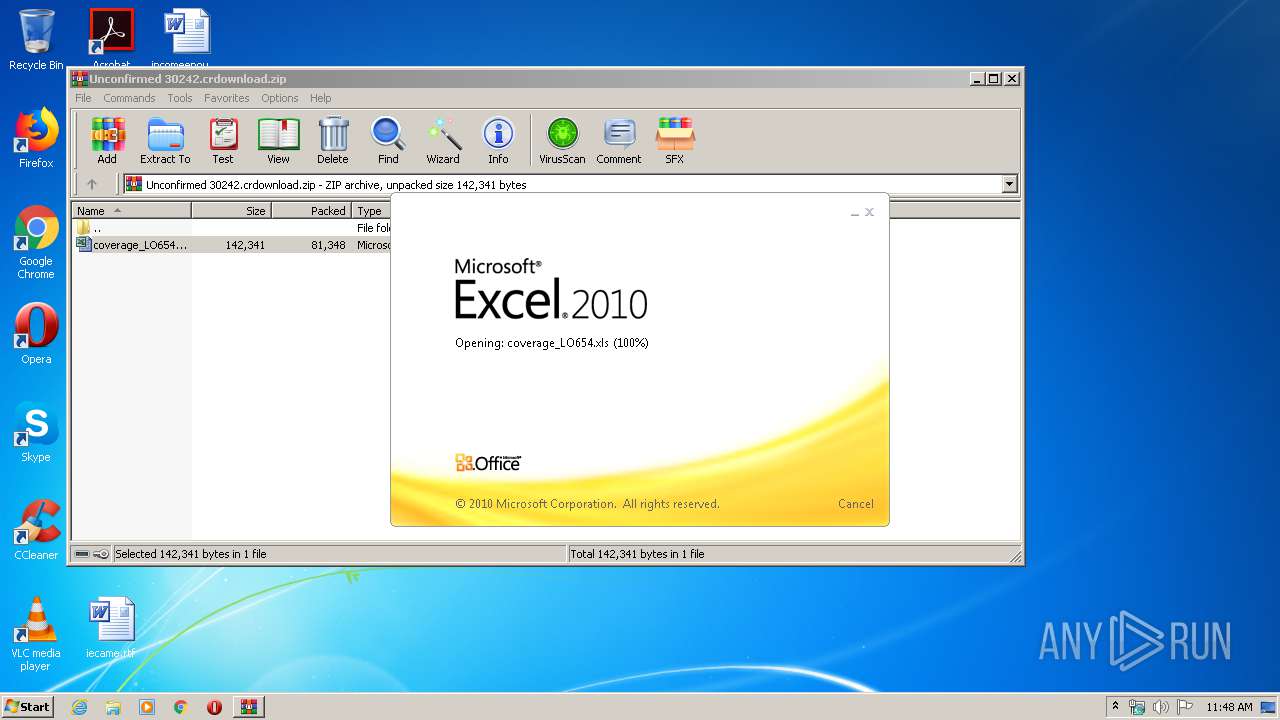
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3992)
Requests a remote executable file from MS Office
- EXCEL.EXE (PID: 3992)
SUSPICIOUS
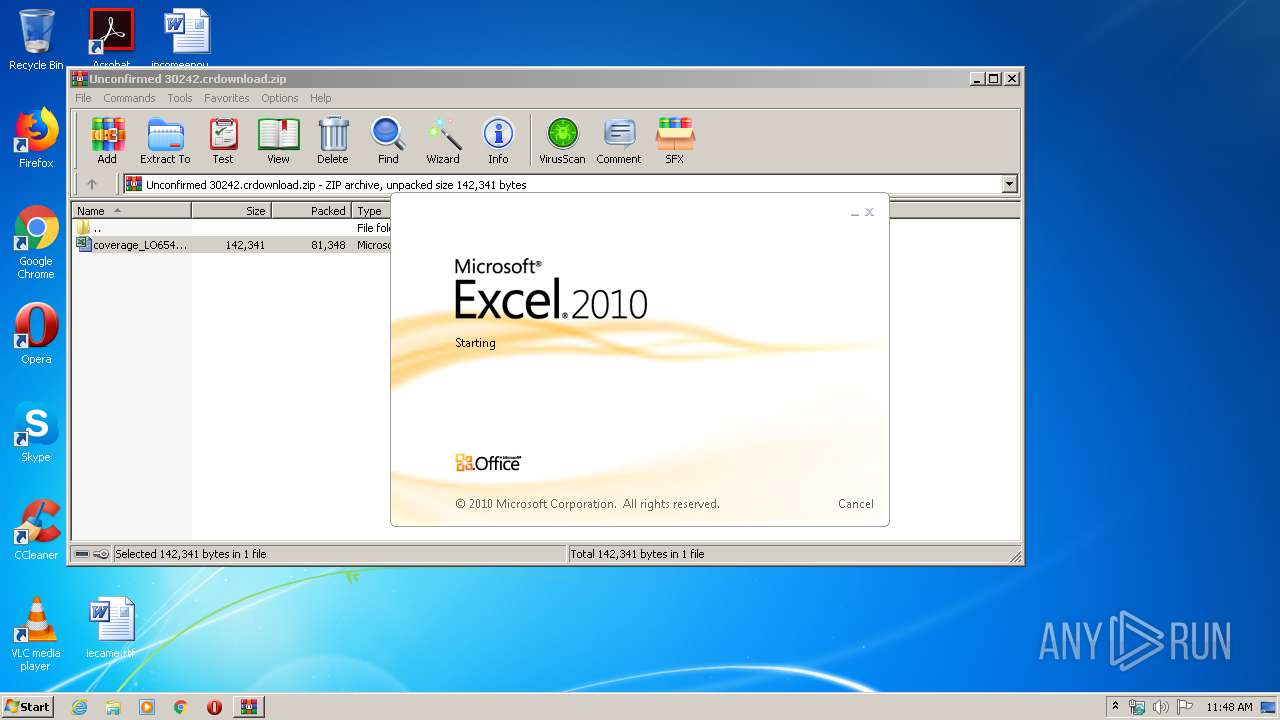
Starts Microsoft Office Application
- WinRAR.exe (PID: 3664)
Reads Internet Cache Settings
- svchost.exe (PID: 3176)
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 3992)
Creates files in the program directory
- EXCEL.EXE (PID: 3992)
Checks for external IP
- svchost.exe (PID: 3176)
INFO
Reads Internet Cache Settings
- EXCEL.EXE (PID: 3992)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0002 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:04:07 17:58:23 |
| ZipCRC: | 0x08d39223 |
| ZipCompressedSize: | 81348 |
| ZipUncompressedSize: | 142341 |
| ZipFileName: | coverage_LO654.xls |
Total processes
38
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2676 | "C:\Windows\System32\regsvr32.exe" /s /i C:\ProgramData\tpeyoft.ocx | C:\Windows\System32\regsvr32.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 4 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3176 | C:\Windows\System32\svchost.exe | C:\Windows\System32\svchost.exe | regsvr32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Unconfirmed 30242.crdownload.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3992 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 090
Read events
1 023
Write events
56
Delete events
11
Modification events
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Unconfirmed 30242.crdownload.zip | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3664) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3992) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | !j5 |
Value: 216A3500980F0000010000000000000000000000 | |||
| (PID) Process: | (3992) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRF601.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3664 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3664.5200\coverage_LO654.xls | document | |
MD5:— | SHA256:— | |||
| 3992 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\b[1].ocx | executable | |
MD5:— | SHA256:— | |||
| 3992 | EXCEL.EXE | C:\ProgramData\tpeyoft.ocx | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
7
DNS requests
7
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3992 | EXCEL.EXE | GET | 200 | 47.254.92.217:80 | http://clarityupstate.com/b.ocx | US | executable | 82.5 Kb | suspicious |
3176 | svchost.exe | GET | 200 | 23.21.213.140:80 | http://api.ipify.org/ | US | text | 12 b | shared |
3176 | svchost.exe | POST | — | 51.254.58.126:80 | http://hoagoomde.com/4/forum.php | PT | — | — | malicious |
3176 | svchost.exe | POST | — | 51.254.58.126:80 | http://ationsopors.com/4/forum.php | PT | — | — | malicious |
3176 | svchost.exe | POST | 200 | 77.120.123.206:80 | http://ardstiobek.com/4/forum.php | UA | text | 12 b | malicious |
3176 | svchost.exe | POST | 200 | 77.120.123.206:80 | http://ardstiobek.com/4/forum.php | UA | text | 12 b | malicious |
3176 | svchost.exe | POST | 200 | 77.120.123.206:80 | http://ardstiobek.com/4/forum.php | UA | text | 12 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3992 | EXCEL.EXE | 47.254.92.217:80 | clarityupstate.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
3176 | svchost.exe | 23.21.213.140:80 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
3176 | svchost.exe | 51.254.58.126:80 | ationsopors.com | OVH SAS | PT | malicious |
3176 | svchost.exe | 77.120.123.206:80 | ardstiobek.com | Volia | UA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clarityupstate.com |
| suspicious |
api.ipify.org |
| shared |
ationsopors.com |
| malicious |
hoagoomde.com |
| malicious |
ardstiobek.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3992 | EXCEL.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3992 | EXCEL.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
3176 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |
3176 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3992 | EXCEL.EXE | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
3176 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3176 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3176 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
3176 | svchost.exe | A Network Trojan was detected | MALWARE [PTsecurity] Hancitor POST Data send |
5 ETPRO signatures available at the full report