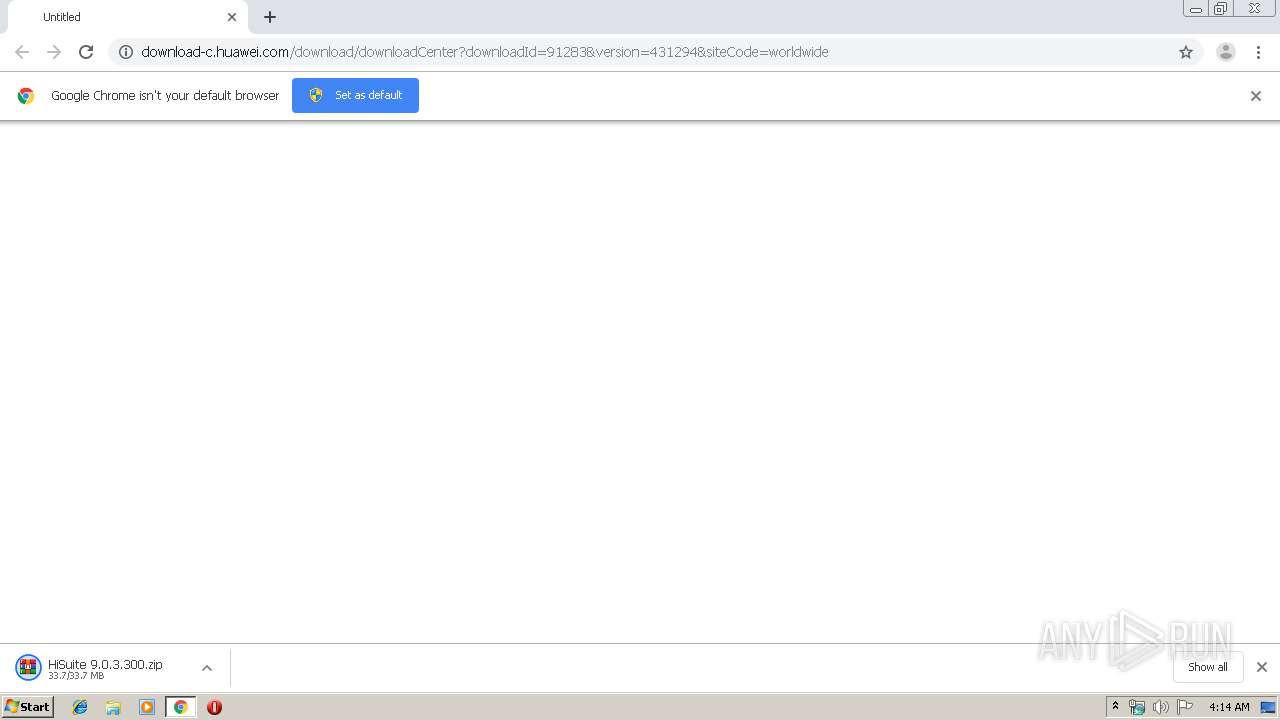
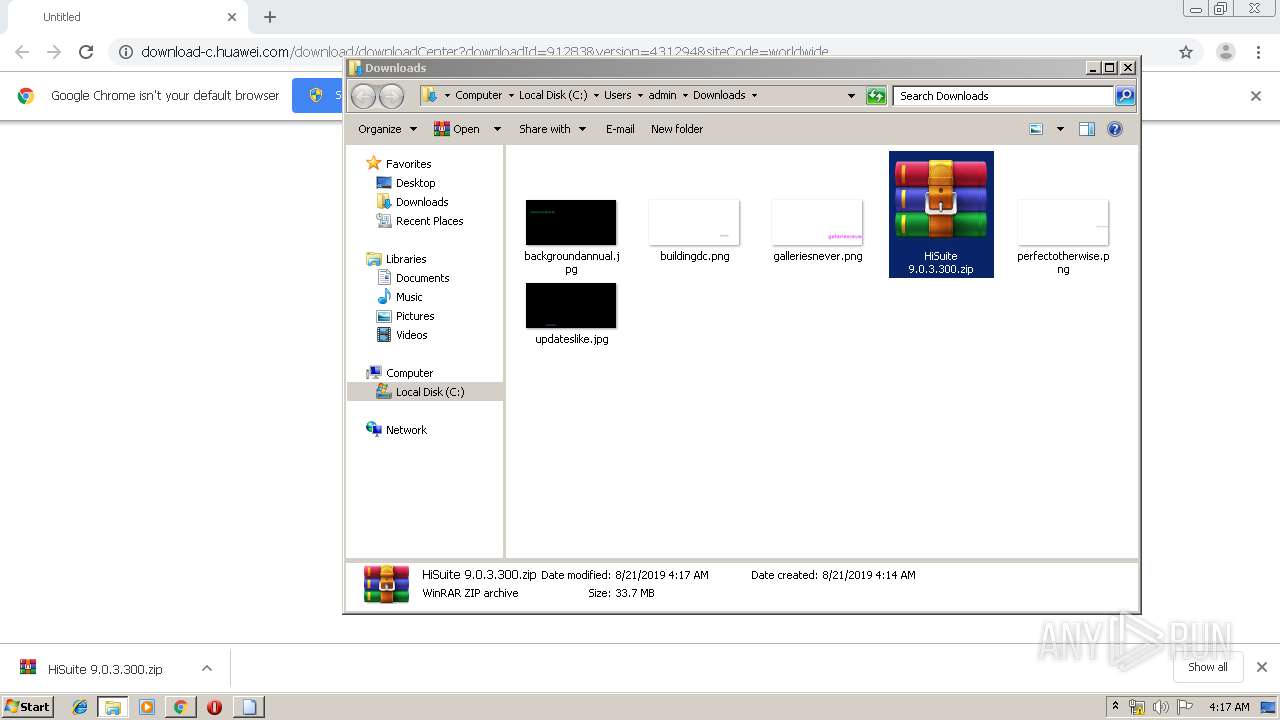
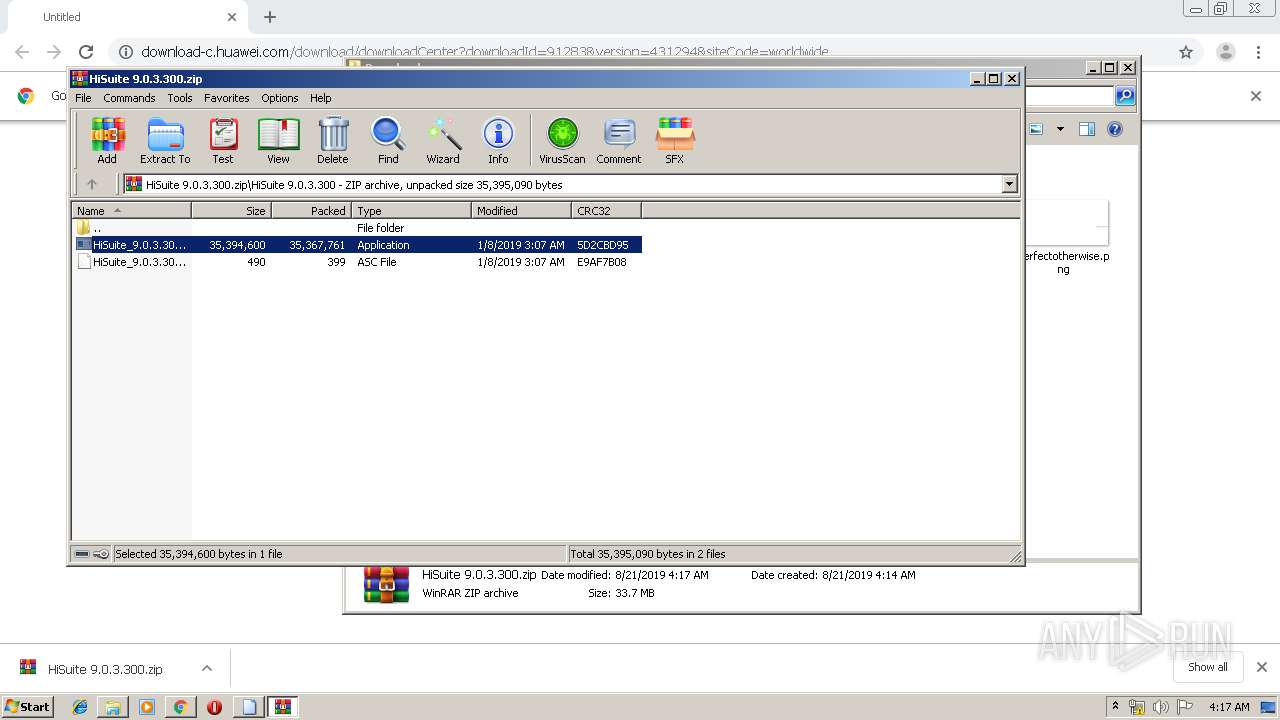
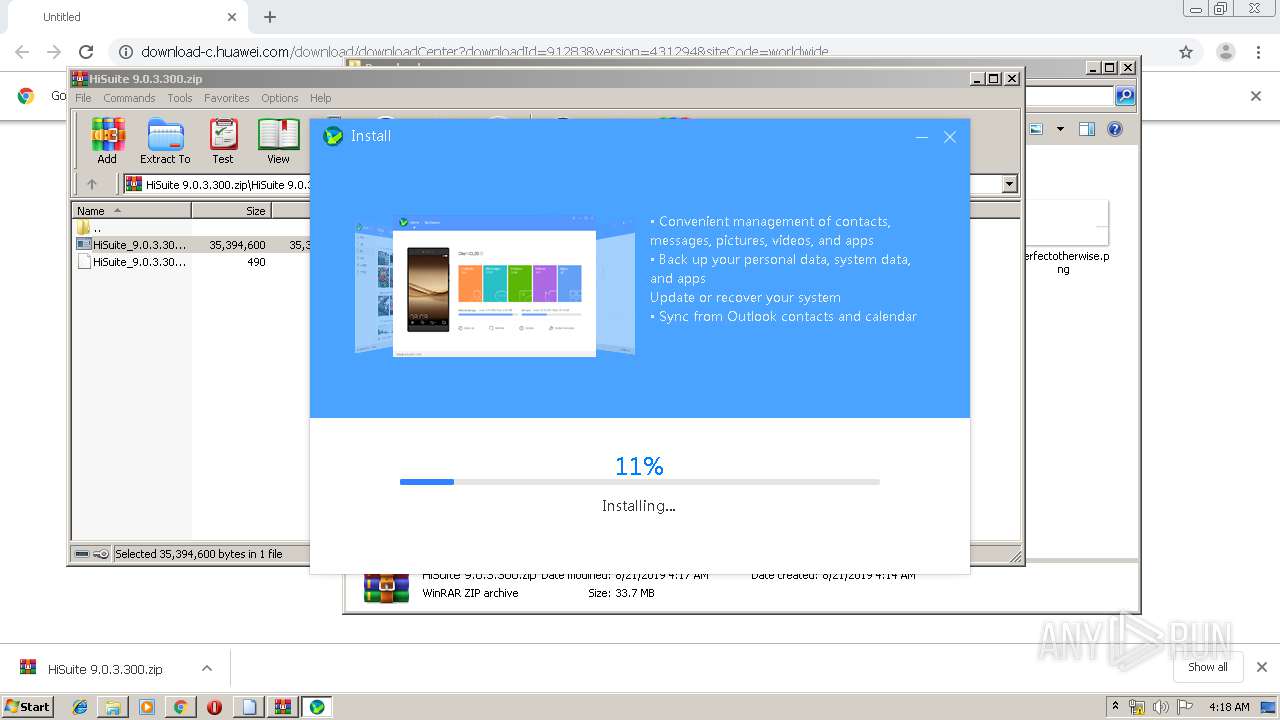
| URL: | http://download-c.huawei.com/download/downloadCenter?downloadId=91283&version=431294&siteCode=worldwide |
| Full analysis: | https://app.any.run/tasks/99f13716-f39b-4067-8210-1855ca1cea90 |
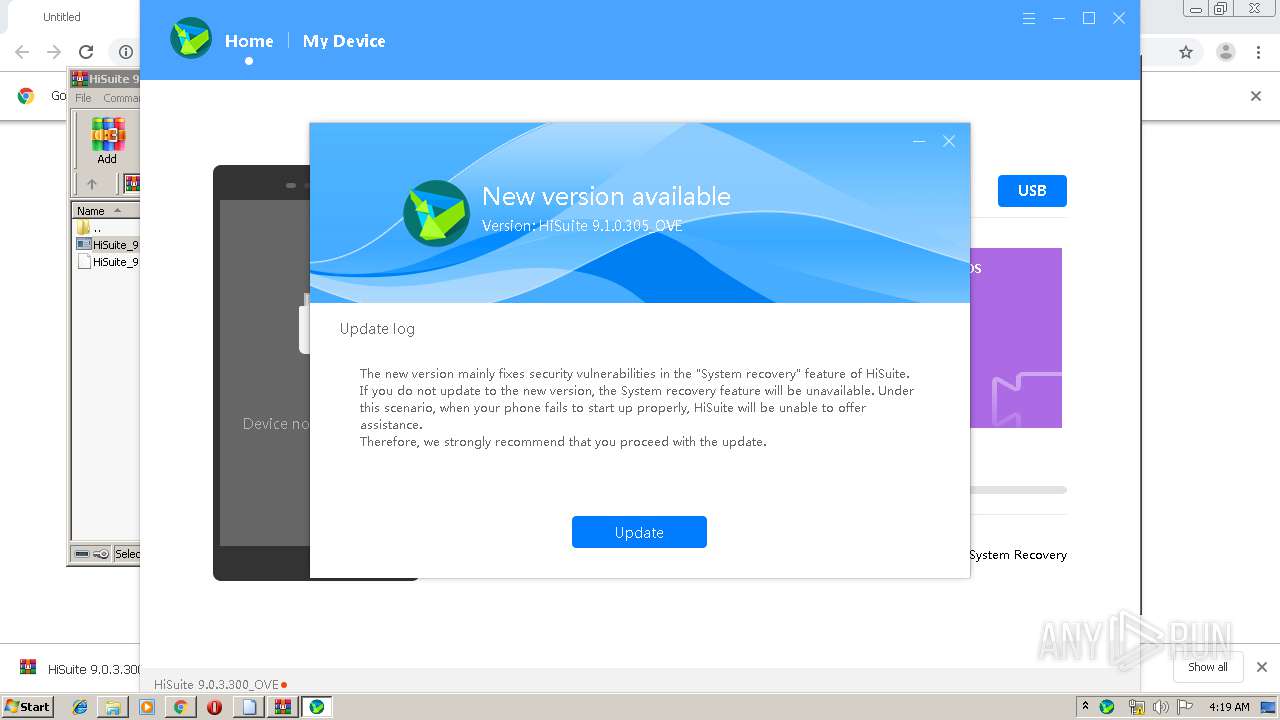
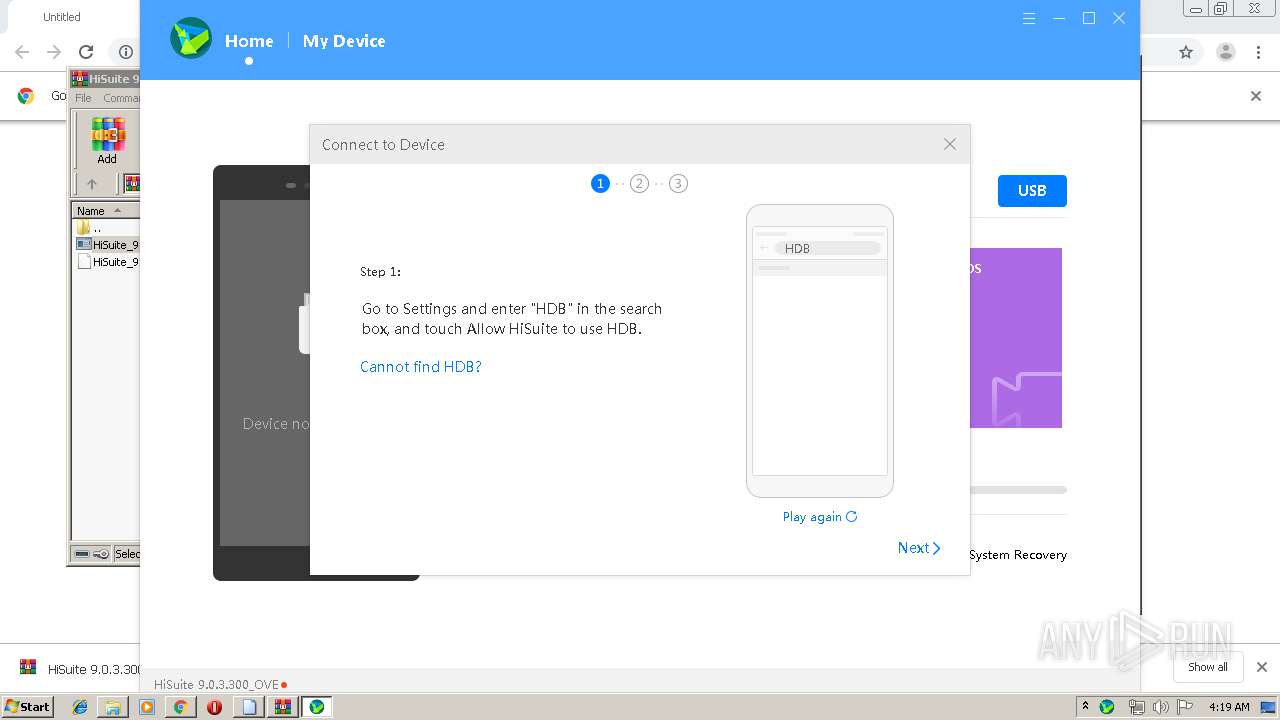
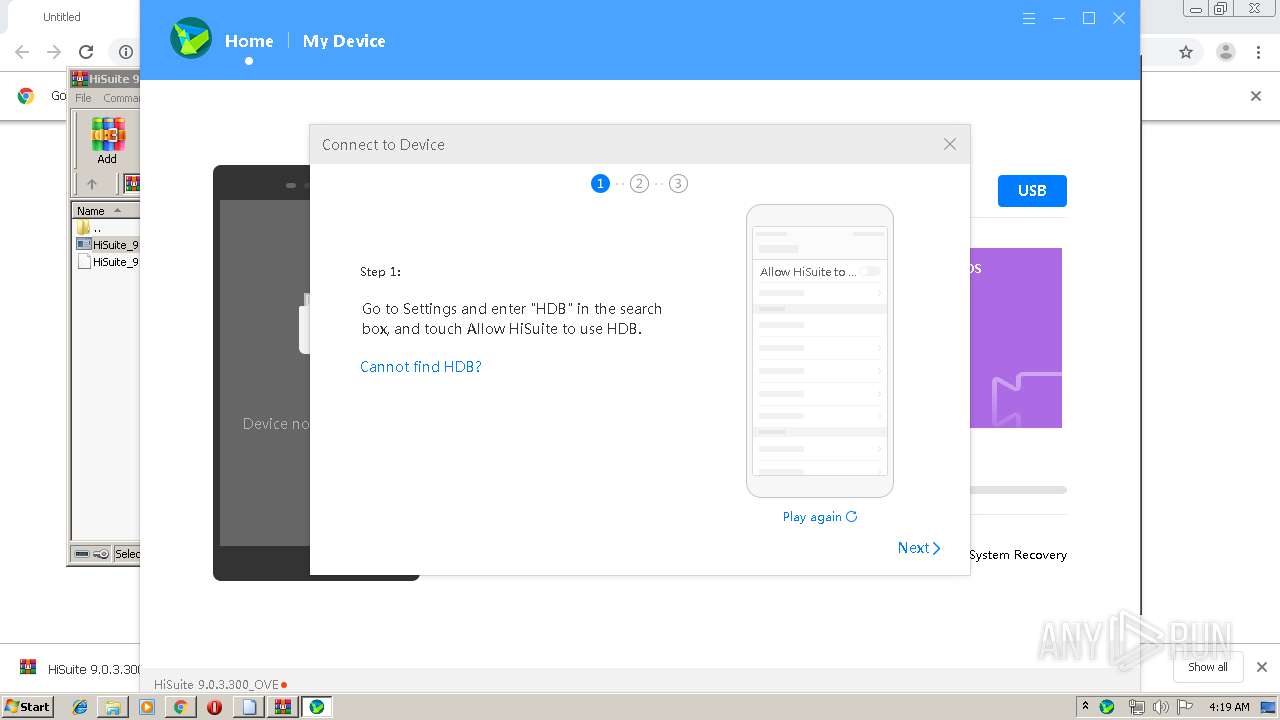
| Verdict: | Malicious activity |
| Analysis date: | August 21, 2019, 03:14:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
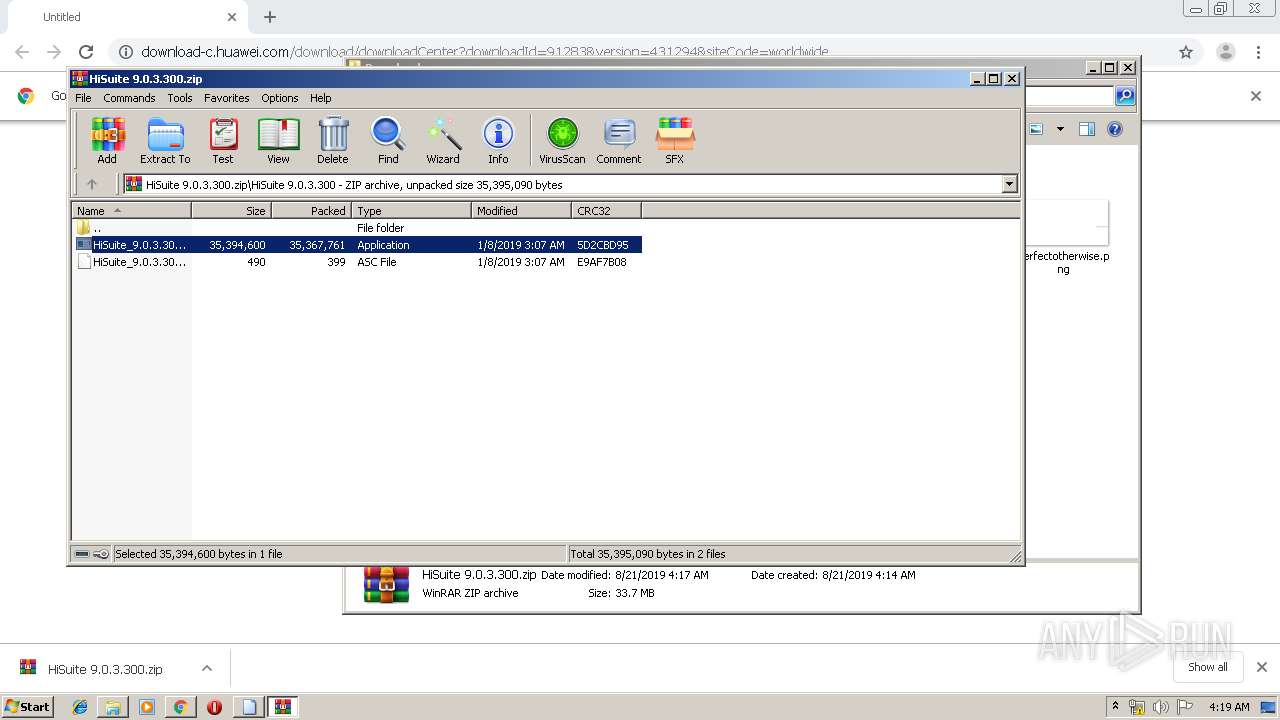
| MD5: | 838CA5A4D96187A83E45CCFCA4A2A094 |
| SHA1: | ED4DF0CDF19110B083606CF7673804F1C6C97100 |
| SHA256: | 5E6D62390CE0787CF27E575B701320A8612800EEF537094297BEA6186F05293C |
| SSDEEP: | 3:N1KaKEmGr88LXJIeySoxBSXYtsRWOgXgAQE:Catrf7s4YGb/e |
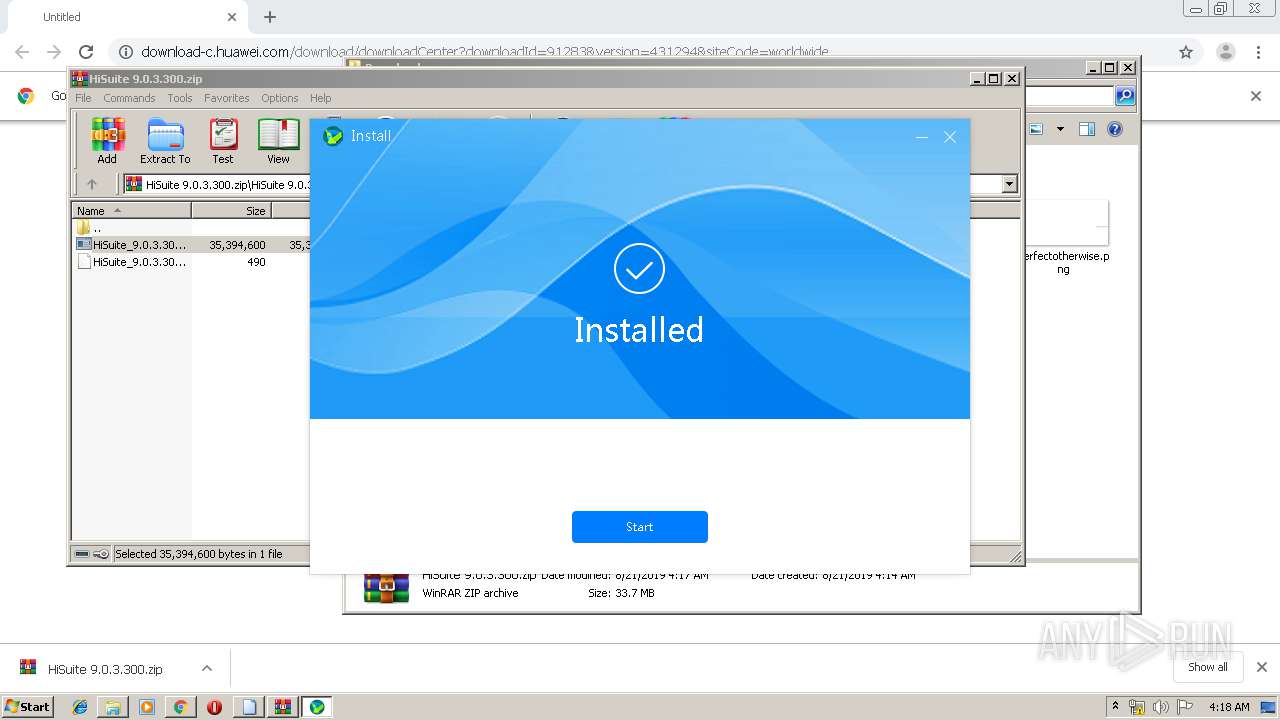
MALICIOUS
Application was dropped or rewritten from another process
- DriverSetup.exe (PID: 3116)
- devsetup32.exe (PID: 3972)
- ns60F2.tmp (PID: 4048)
- RIconTool.exe (PID: 3180)
- HuaweiHiSuiteService.exe (PID: 3492)
- HiSuite.exe (PID: 2916)
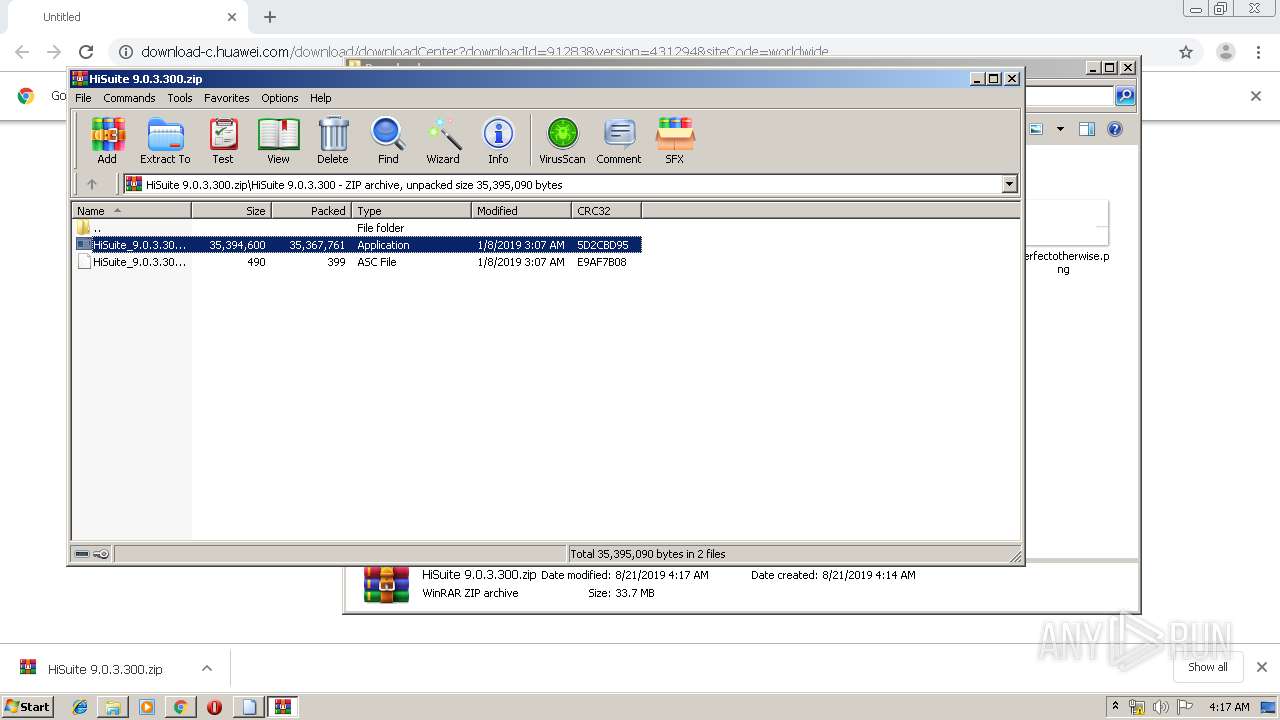
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
- HiSuite_9.0.3.300_OVE.exe (PID: 3688)
- HSService.exe (PID: 1536)
- HuaweiHiSuiteService.exe (PID: 4020)
Loads dropped or rewritten executable
- DriverSetup.exe (PID: 3116)
- HiSuite.exe (PID: 2916)
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
SUSPICIOUS
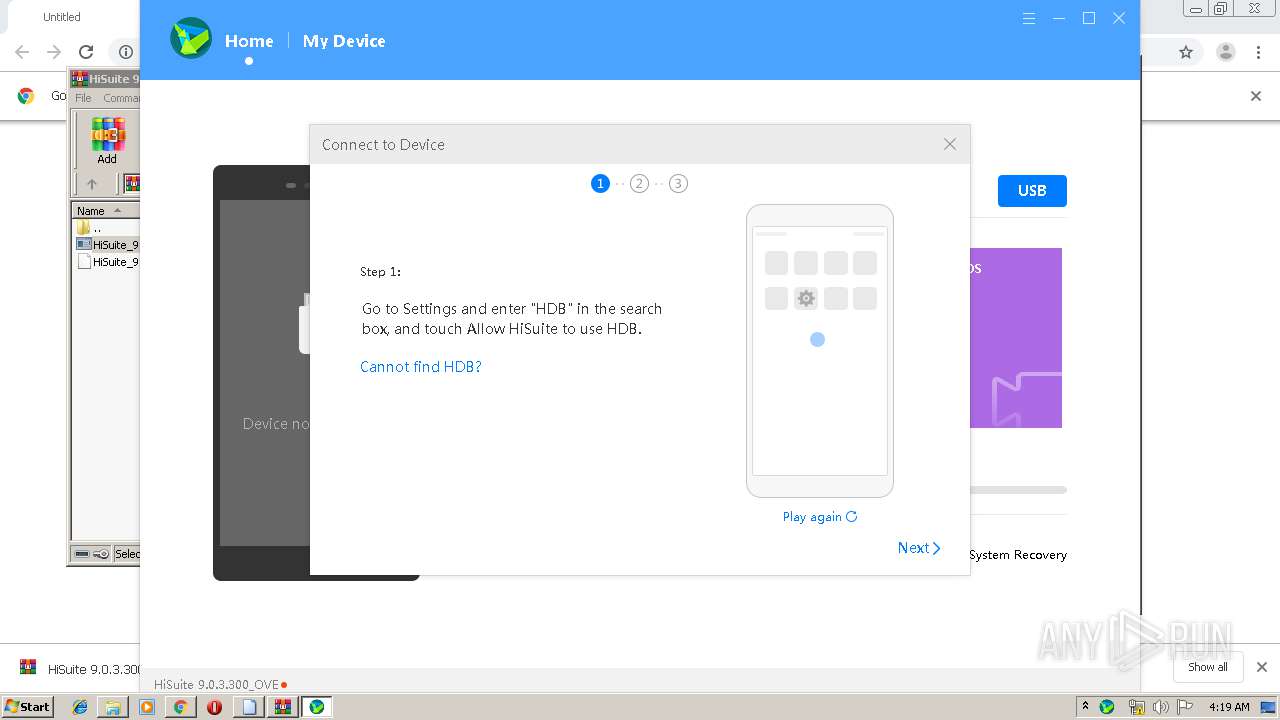
Starts SC.EXE for service management
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
Creates files in the program directory
- DriverSetup.exe (PID: 3116)
- devsetup32.exe (PID: 3972)
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
- HuaweiHiSuiteService.exe (PID: 4020)
- HuaweiHiSuiteService.exe (PID: 3492)
- HSService.exe (PID: 1536)
Executed via COM
- DrvInst.exe (PID: 2348)
- DrvInst.exe (PID: 1688)
- DrvInst.exe (PID: 3436)
- DrvInst.exe (PID: 3944)
- DrvInst.exe (PID: 1792)
- DrvInst.exe (PID: 3052)
- DrvInst.exe (PID: 3776)
- DrvInst.exe (PID: 1728)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 3776)
Executable content was dropped or overwritten
- devsetup32.exe (PID: 3972)
- DrvInst.exe (PID: 2348)
- DrvInst.exe (PID: 1688)
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
- DrvInst.exe (PID: 3776)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 4076)
Removes files from Windows directory
- DrvInst.exe (PID: 2348)
- DrvInst.exe (PID: 1688)
- DrvInst.exe (PID: 3944)
- DrvInst.exe (PID: 1792)
- DrvInst.exe (PID: 1728)
- DrvInst.exe (PID: 3052)
- DrvInst.exe (PID: 3436)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3776)
- DrvInst.exe (PID: 3776)
Starts application with an unusual extension
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
Creates files in the driver directory
- DrvInst.exe (PID: 2348)
- DrvInst.exe (PID: 1688)
- DrvInst.exe (PID: 3944)
- DrvInst.exe (PID: 1792)
- DrvInst.exe (PID: 3436)
- DrvInst.exe (PID: 1728)
- DrvInst.exe (PID: 3052)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3776)
- DrvInst.exe (PID: 3776)
- devsetup32.exe (PID: 3972)
Creates files in the Windows directory
- DrvInst.exe (PID: 2348)
- DrvInst.exe (PID: 1688)
- DrvInst.exe (PID: 1792)
- DrvInst.exe (PID: 3436)
- DrvInst.exe (PID: 3944)
- DrvInst.exe (PID: 1728)
- DrvInst.exe (PID: 3052)
- DrvInst.exe (PID: 1860)
- DrvInst.exe (PID: 4076)
- DrvInst.exe (PID: 3776)
- DrvInst.exe (PID: 3776)
- devsetup32.exe (PID: 3972)
Creates or modifies windows services
- devsetup32.exe (PID: 3972)
Creates a software uninstall entry
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
- HiSuite.exe (PID: 2916)
Modifies the open verb of a shell class
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
- HiSuite.exe (PID: 2916)
Executed as Windows Service
- HuaweiHiSuiteService.exe (PID: 3492)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3544)
INFO
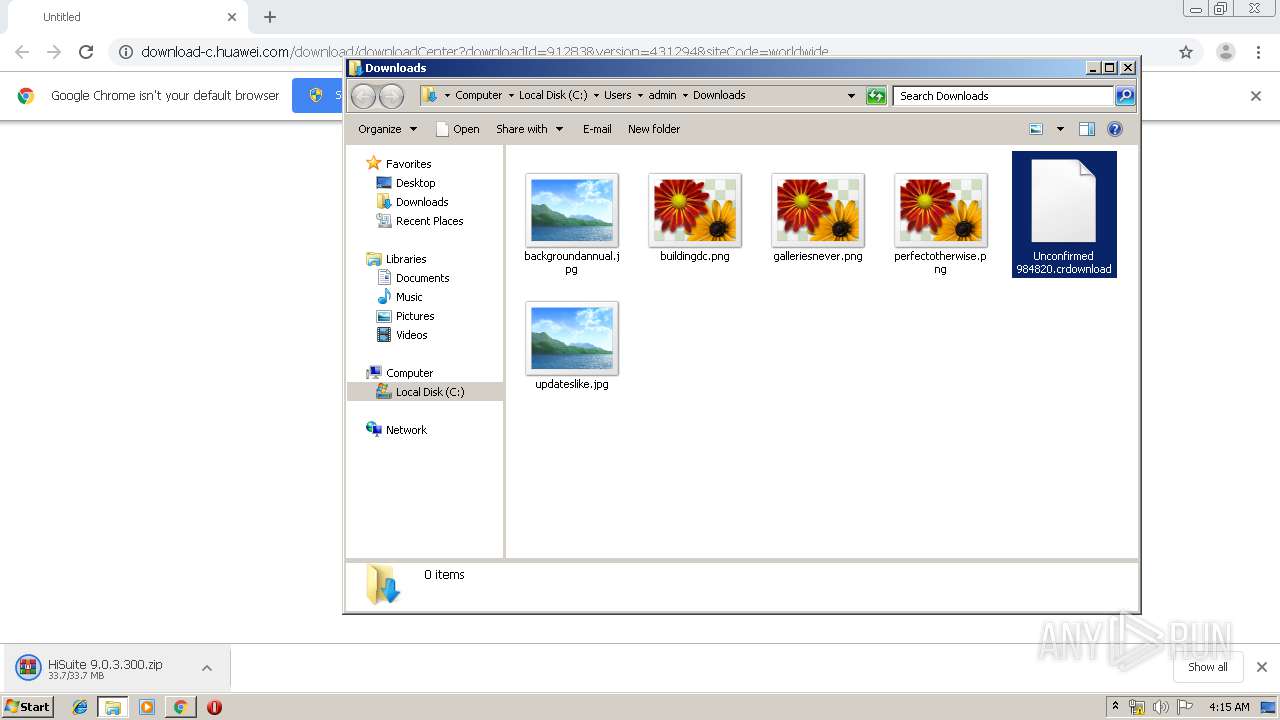
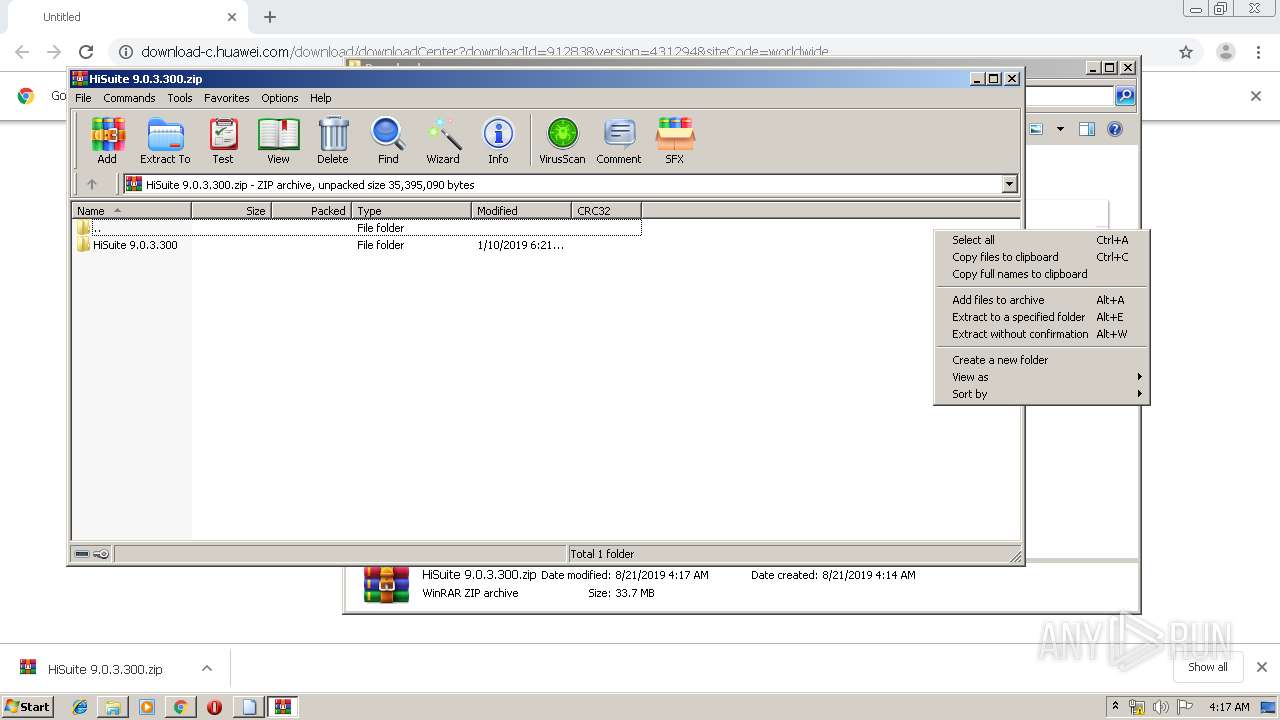
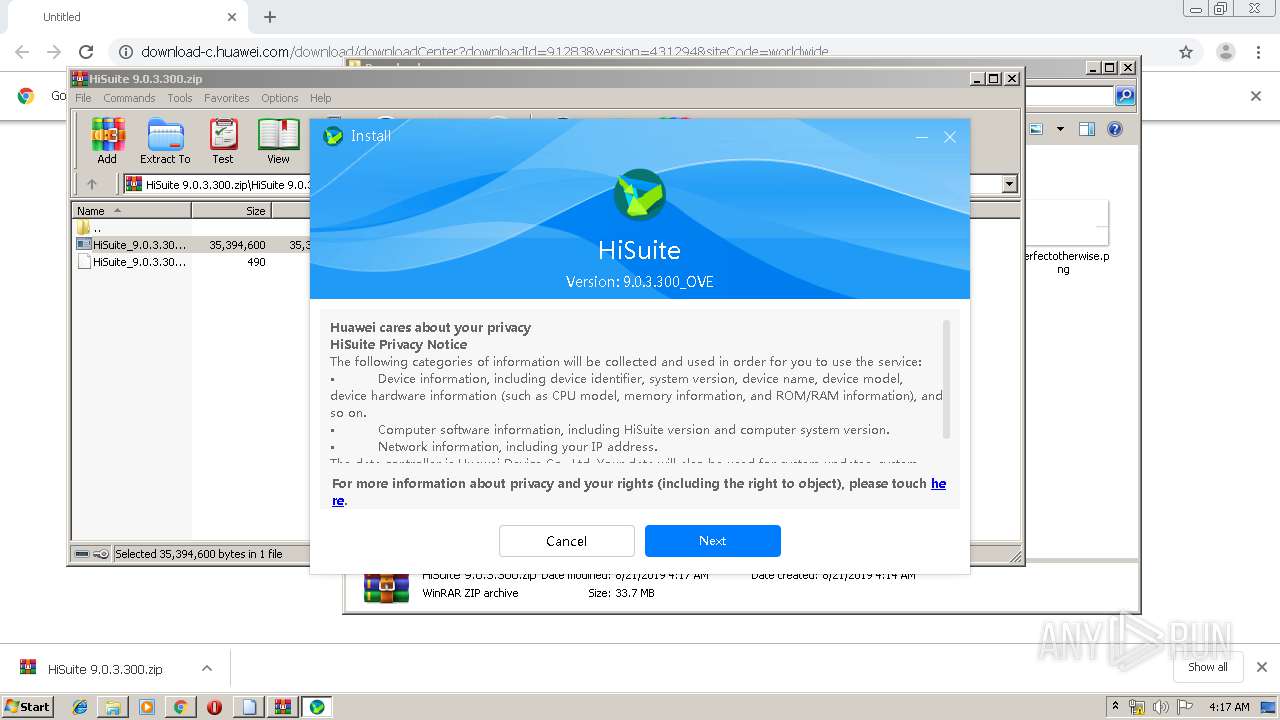
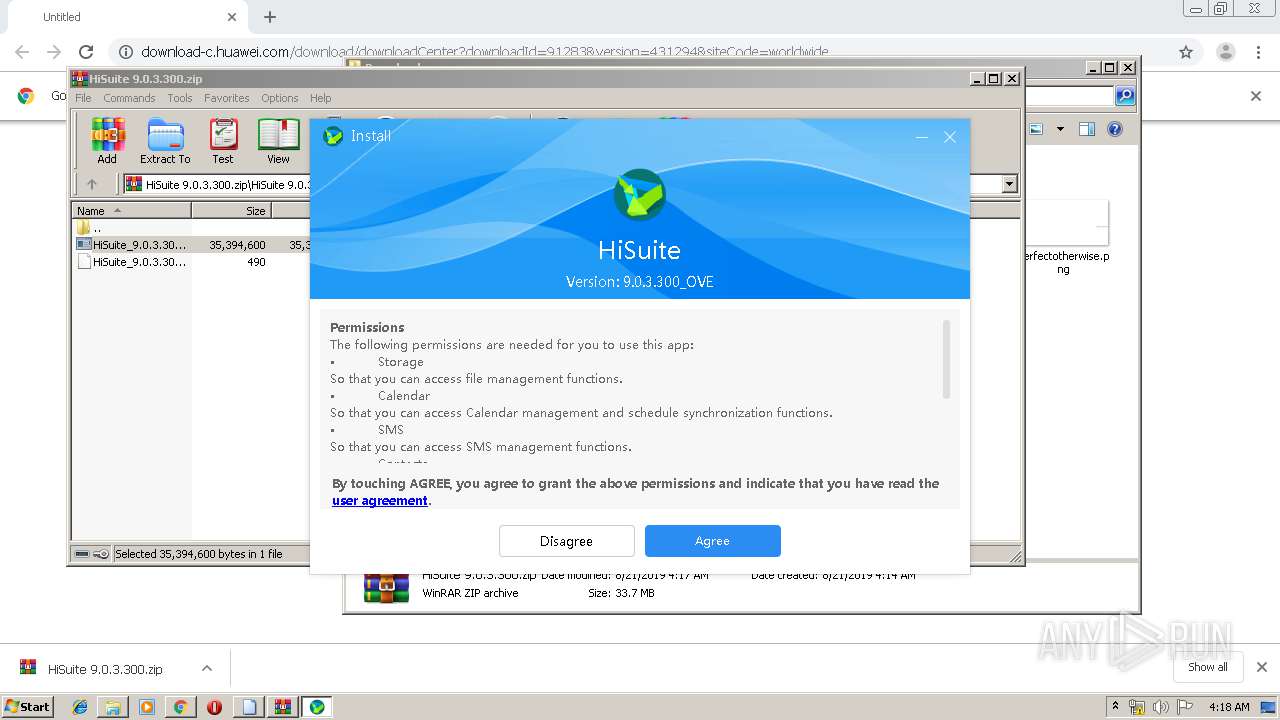
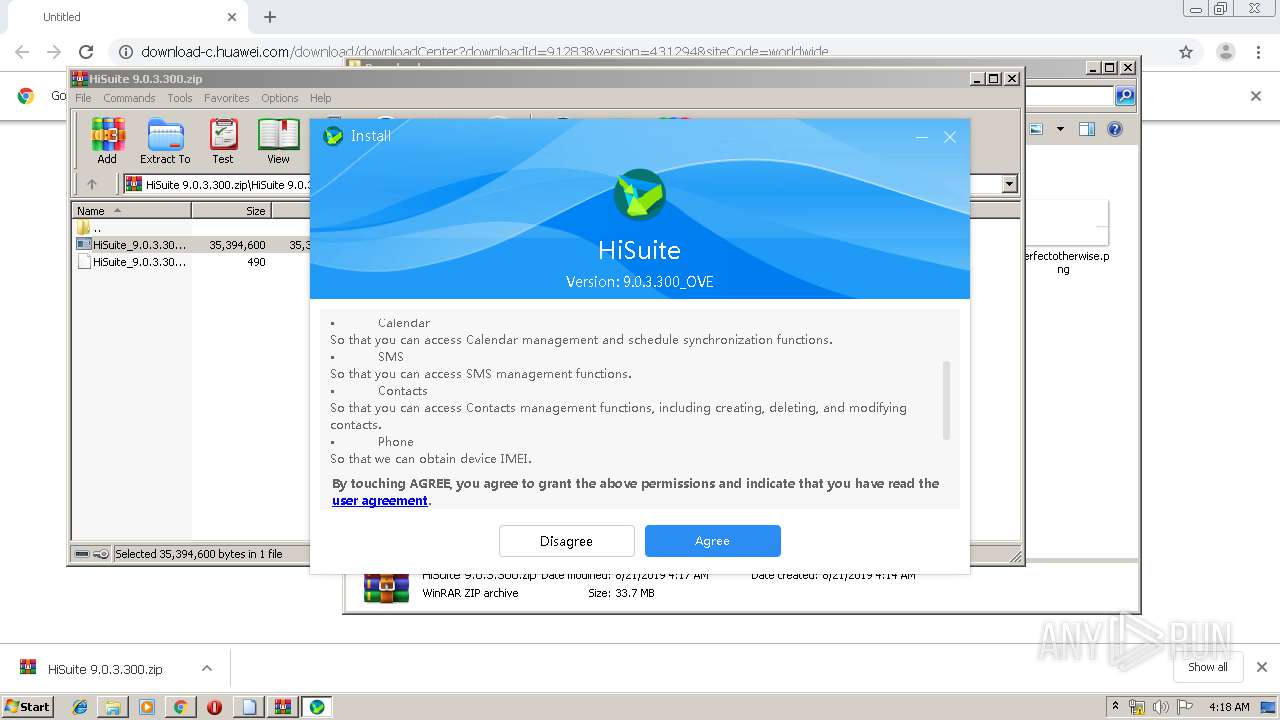
Manual execution by user
- rundll32.exe (PID: 848)
- WinRAR.exe (PID: 2876)
Application launched itself
- chrome.exe (PID: 3544)
Dropped object may contain Bitcoin addresses
- HiSuite_9.0.3.300_OVE.exe (PID: 2752)
Reads Internet Cache Settings
- chrome.exe (PID: 3544)
Reads settings of System Certificates
- chrome.exe (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
94
Monitored processes
47
Malicious processes
19
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,601706055650148795,15325482702228934603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12842504474250412078 --mojo-platform-channel-handle=2952 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,601706055650148795,15325482702228934603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5169544915307485863 --renderer-client-id=20 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4052 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 848 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\Unconfirmed 984820.crdownload | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 924 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,601706055650148795,15325482702228934603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12192461516763770487 --mojo-platform-channel-handle=3796 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1536 | "C:\Program Files\HiSuite\HandSetService\HSService.exe" -install | C:\Program Files\HiSuite\HandSetService\HSService.exe | — | HiSuite_9.0.3.300_OVE.exe | |||||||||||
User: admin Integrity Level: HIGH Description: RunDCSer 应用程序 Exit code: 0 Version: 22.0.0.3 Modules
| |||||||||||||||
| 1676 | "C:\Windows\System32\sc.exe" delete HuaweiHiSuiteService64.exe | C:\Windows\System32\sc.exe | — | HiSuite_9.0.3.300_OVE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{7f3d1376-0257-5bcd-99d5-950b2eb3aa6f}\hw_quser.inf" "0" "67561b49f" "000004D8" "WinSta0\Default" "000003AC" "208" "C:\Program Files\HiSuite\driver\all\Driver\X86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1728 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4688b520-514c-7ba7-fb30-6a5474b09512}\hw_quusbnet.inf" "0" "601ee2f0b" "000004D8" "WinSta0\Default" "000003AC" "208" "C:\Program Files\HiSuite\driver\all\Driver\X86" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4bf6a599-f312-09be-99d5-950bdb7fad2c}\hw_goadb.inf" "0" "6b10a7187" "0000054C" "WinSta0\Default" "000003B0" "208" "C:\Program Files\HiSuite\driver\all\Driver\X86" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1860 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{7e2435b3-412e-4505-fe24-1375f75aa828}\hw_cdcacm.inf" "0" "6a58486ff" "000003B0" "WinSta0\Default" "000004D8" "208" "C:\Program Files\HiSuite\driver\all\Driver\X86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 256
Read events
1 963
Write events
287
Delete events
6
Modification events
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3544-13210830865341125 |
Value: 259 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3544) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3544-13210830865341125 |
Value: 259 | |||
Executable files
145
Suspicious files
150
Text files
2 093
Unknown types
81
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\93cce119-3bcb-43ae-b847-f587fbe3c4ef.tmp | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:911B244E4A362B56F2478647D2D61A40 | SHA256:3A5AEC1EA537D8841E604D0AA4CD5F9241C805A3D4EB4E372CFB7EEB3678A361 | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF169c73.TMP | text | |
MD5:A519780ED0A2F4336DB4F5651D79C369 | SHA256:DA5B71BD0075B55757BF757BF5F4D4A1DCBCF0762CDA5B31B28680963E068C75 | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169c25.TMP | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:C4D6CBB269C626168A5D6D0D8CCE6C30 | SHA256:B62CDBB758278A0C2E50593357390119441D8DE09428EB29027F3DFD1332E348 | |||
| 3544 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
20
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2916 | HiSuite.exe | GET | 200 | 203.205.224.29:8180 | http://update.hicloud.com:8180/TDS/data/files/p3/s27/G56/g0/v292520/f1/full/filelist.xml | CN | xml | 677 b | suspicious |
2916 | HiSuite.exe | GET | 200 | 203.205.224.29:8180 | http://update.hicloud.com:8180/TDS/data/files/p3/s27/G56/g0/v292520/f1/full/changelog.xml | CN | xml | 1.61 Kb | suspicious |
2840 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 514 b | whitelisted |
2840 | chrome.exe | GET | 200 | 2.16.106.169:80 | http://download-c.huawei.com/download/downloadCenter?downloadId=91283&version=431294&siteCode=worldwide | unknown | compressed | 33.7 Mb | malicious |
2916 | HiSuite.exe | GET | 200 | 203.205.224.29:8180 | http://update.hicloud.com:8180/TDS/data/files/p3/s27/G56/g0/v292520/f1/full/changelog.xml | CN | xml | 1.61 Kb | suspicious |
2840 | chrome.exe | GET | 200 | 173.194.183.166:80 | http://r1---sn-aigl6ney.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.92.25.193&mm=28&mn=sn-aigl6ney&ms=nvh&mt=1566357374&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2840 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.16.131:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.22.33:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 173.194.183.166:80 | r1---sn-aigl6ney.gvt1.com | Google Inc. | US | whitelisted |
2840 | chrome.exe | 216.58.206.14:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
download-c.huawei.com |
| malicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2840 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |
Process | Message |
|---|---|
HuaweiHiSuiteService.exe | InstallService Start |