| download: | dwagent_x86.exe |
| Full analysis: | https://app.any.run/tasks/b282f471-a155-4953-b420-03e4b18d9e1d |
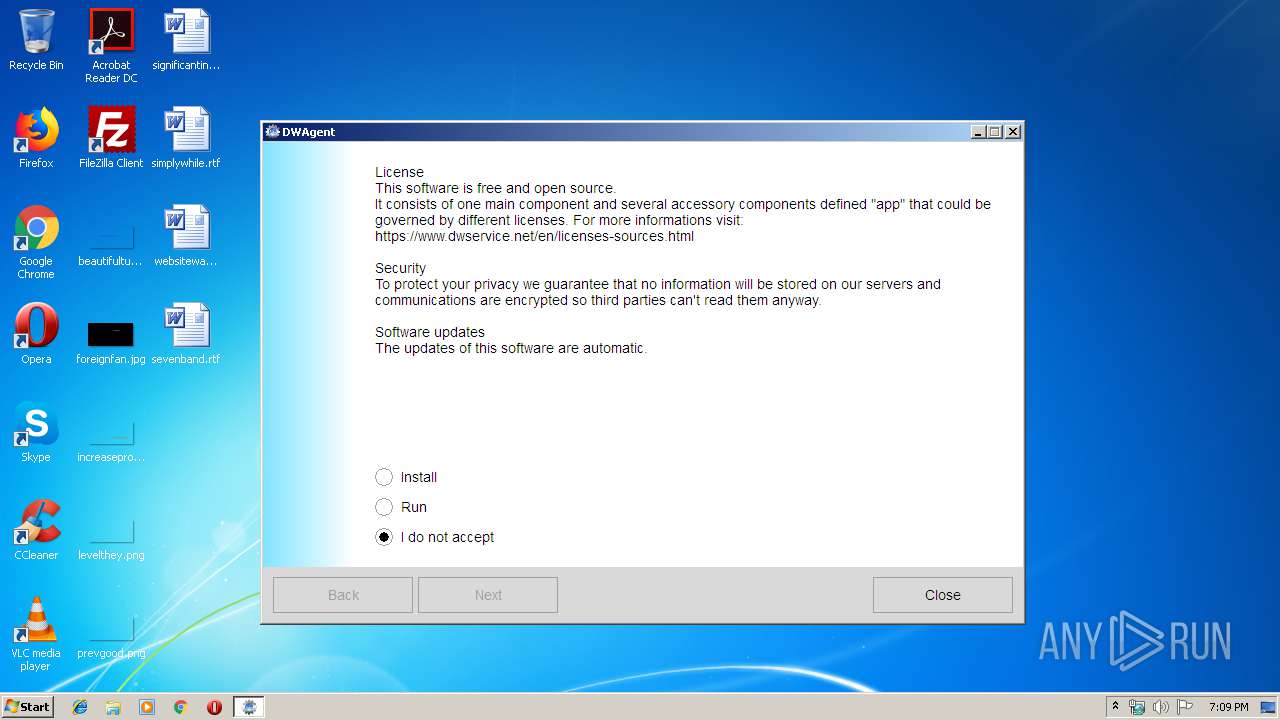
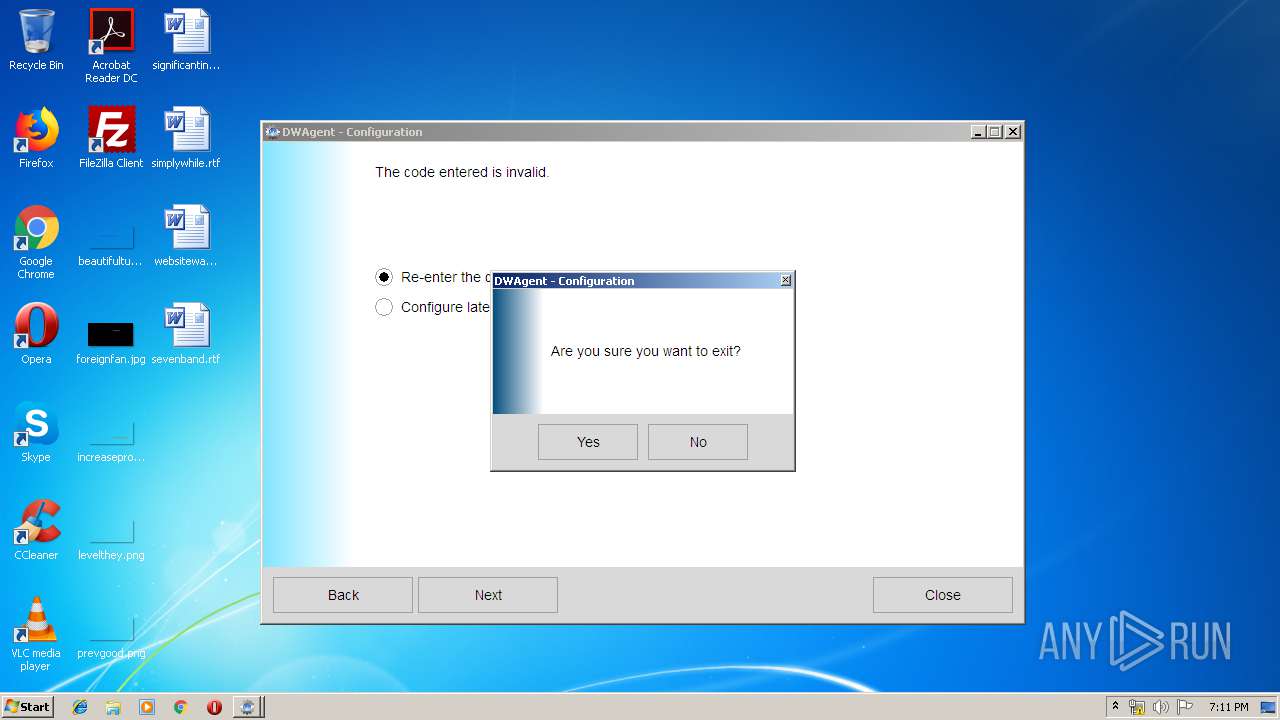
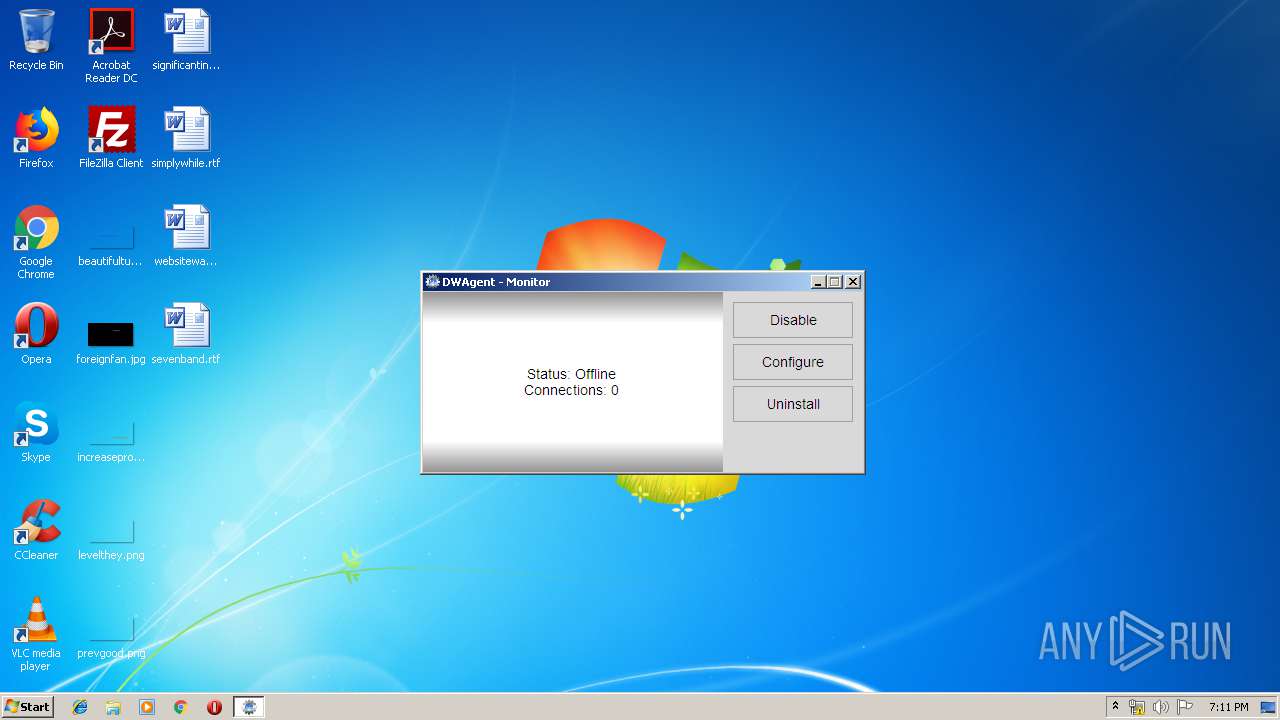
| Verdict: | Malicious activity |
| Analysis date: | August 15, 2019, 18:09:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 4E9623C200DEFF2B48D7D524CD1EA994 |
| SHA1: | FFBE86FC72A776719D9C143DDD118388002B1436 |
| SHA256: | 5E65E5A8E3C427FA516428BA07042812A1CCB4EE312B0D685EE80E92DE38E5D1 |
| SSDEEP: | 196608:Ly+se+OAKnJAlQykoqHE9TwIYTa2LkooGZ2SBRMZb9rPEhhkl:L5XnK6yLft/YTzL7ouMZWhhkl |
MALICIOUS
Loads dropped or rewritten executable
- dwagent.exe (PID: 2056)
- dwagent.exe (PID: 2388)
- dwagent.exe (PID: 2644)
- dwagent.exe (PID: 3220)
- dwagent.exe (PID: 1968)
- dwagent.exe (PID: 3520)
Application was dropped or rewritten from another process
- dwagsvc.exe (PID: 2844)
- dwagsvc.exe (PID: 3904)
- dwagent.exe (PID: 2644)
- dwagsvc.exe (PID: 3940)
- dwagent.exe (PID: 3220)
- dwagsvc.exe (PID: 3552)
- dwagsvc.exe (PID: 2980)
- dwagsvc.exe (PID: 2184)
- dwagsvc.exe (PID: 3688)
- dwagent.exe (PID: 1968)
- dwagent.exe (PID: 2056)
- dwaglnc.exe (PID: 3056)
- dwagent.exe (PID: 2388)
- dwaglnc.exe (PID: 3036)
- dwagent.exe (PID: 3520)
- dwagsvc.exe (PID: 2828)
- dwagsvc.exe (PID: 3380)
- dwaglnc.exe (PID: 3472)
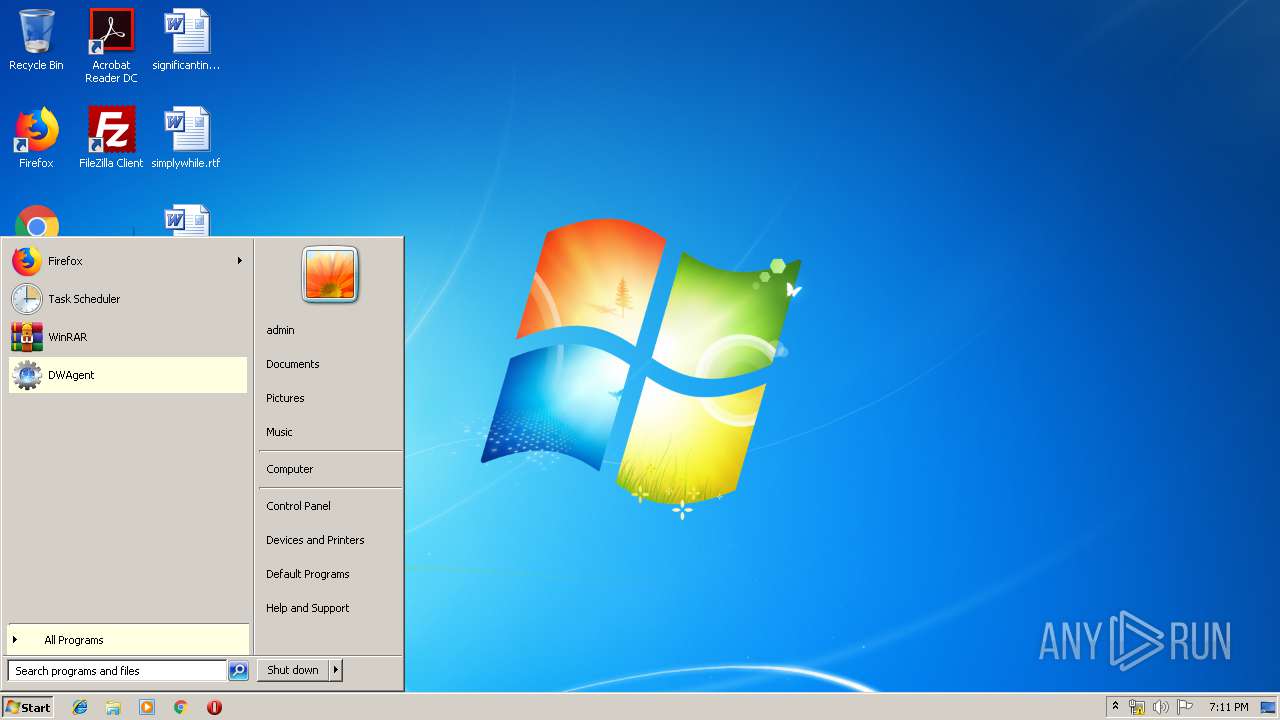
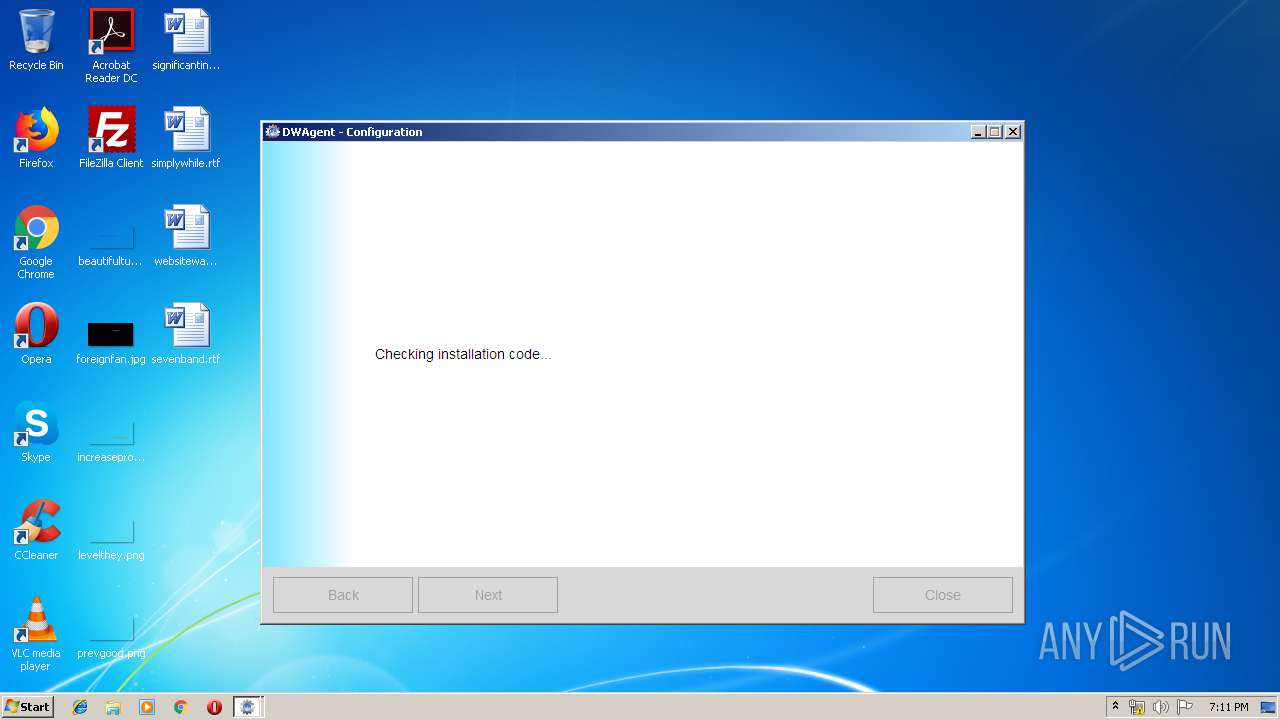
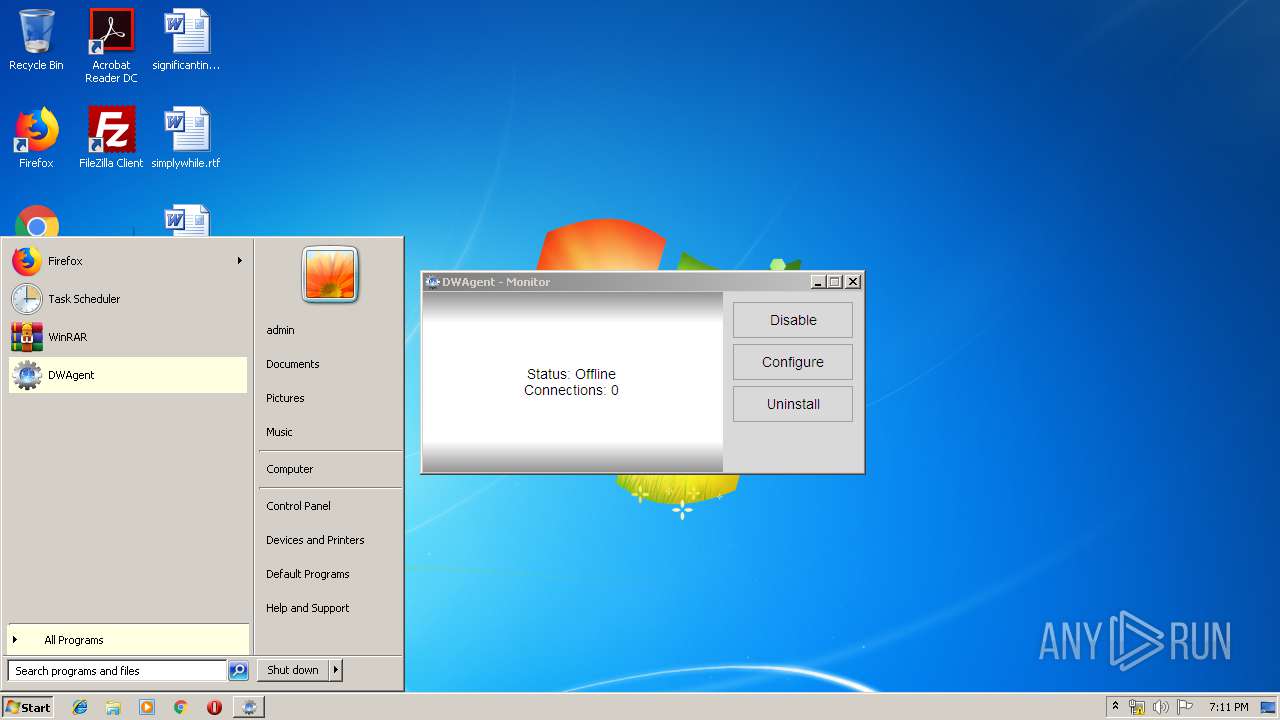
Changes the autorun value in the registry
- dwagsvc.exe (PID: 3552)
SUSPICIOUS
Application launched itself
- dwagent_x86.exe (PID: 3152)
Executable content was dropped or overwritten
- dwagent.exe (PID: 2388)
- dwagent_x86.exe (PID: 3152)
Creates files in the program directory
- dwagsvc.exe (PID: 2184)
- dwagent.exe (PID: 2644)
- dwagent.exe (PID: 2388)
- dwagent.exe (PID: 3220)
- dwagsvc.exe (PID: 3380)
Loads Python modules
- dwagent.exe (PID: 2644)
- dwagent.exe (PID: 2056)
- dwagent.exe (PID: 2388)
- dwagent.exe (PID: 3220)
- dwagent.exe (PID: 1968)
- dwagent.exe (PID: 3520)
Starts CMD.EXE for commands execution
- dwagent.exe (PID: 2388)
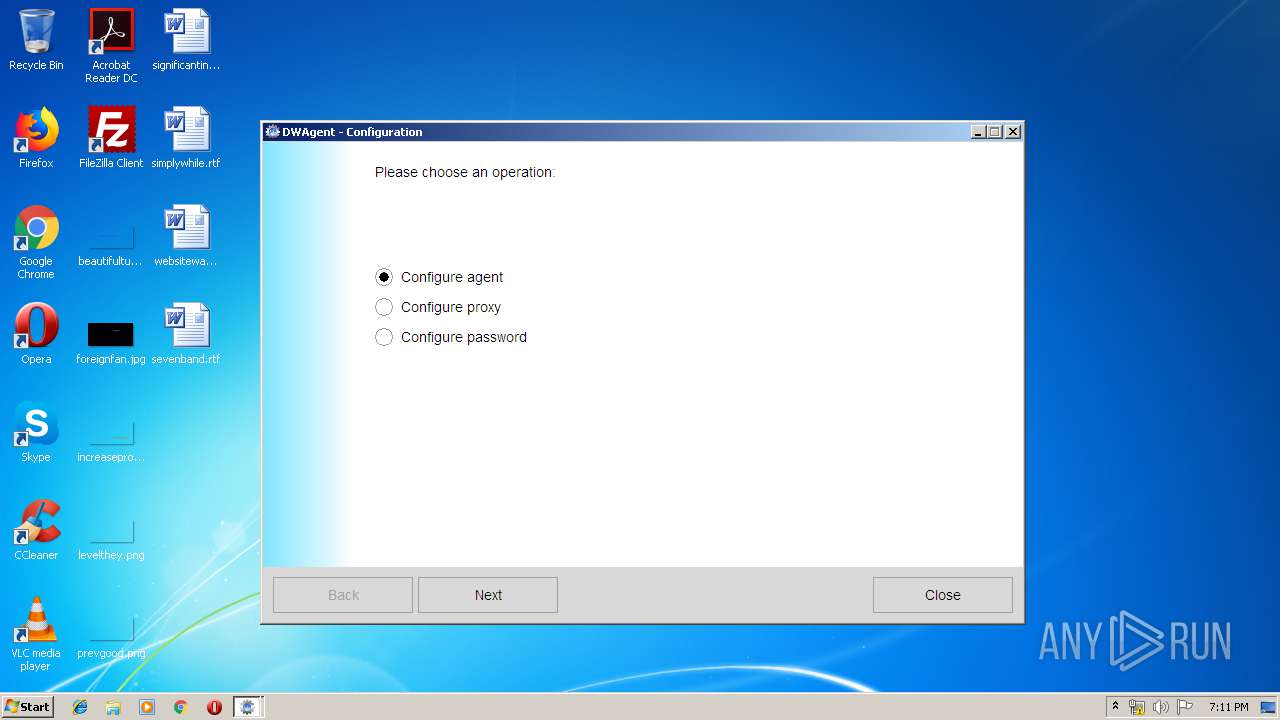
Creates a software uninstall entry
- dwagsvc.exe (PID: 3380)
Executed as Windows Service
- dwagsvc.exe (PID: 2184)
INFO
Dropped object may contain Bitcoin addresses
- dwagent_x86.exe (PID: 3152)
- dwagent.exe (PID: 2388)
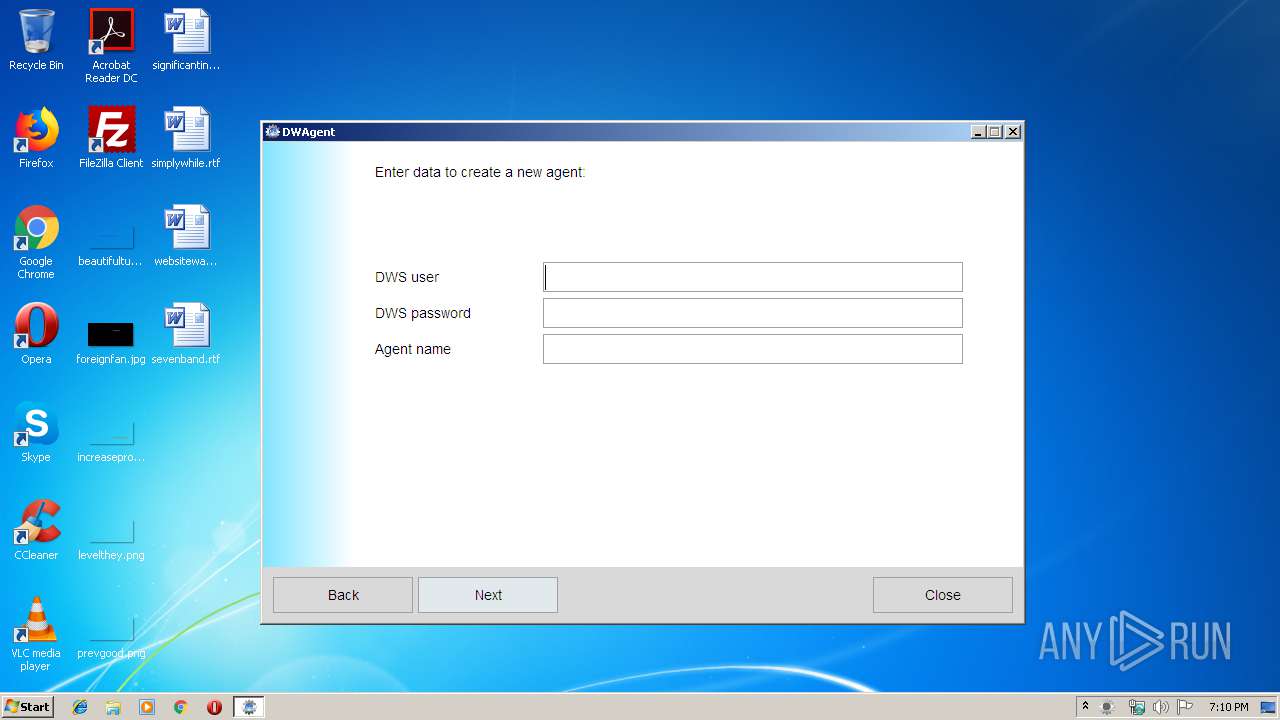
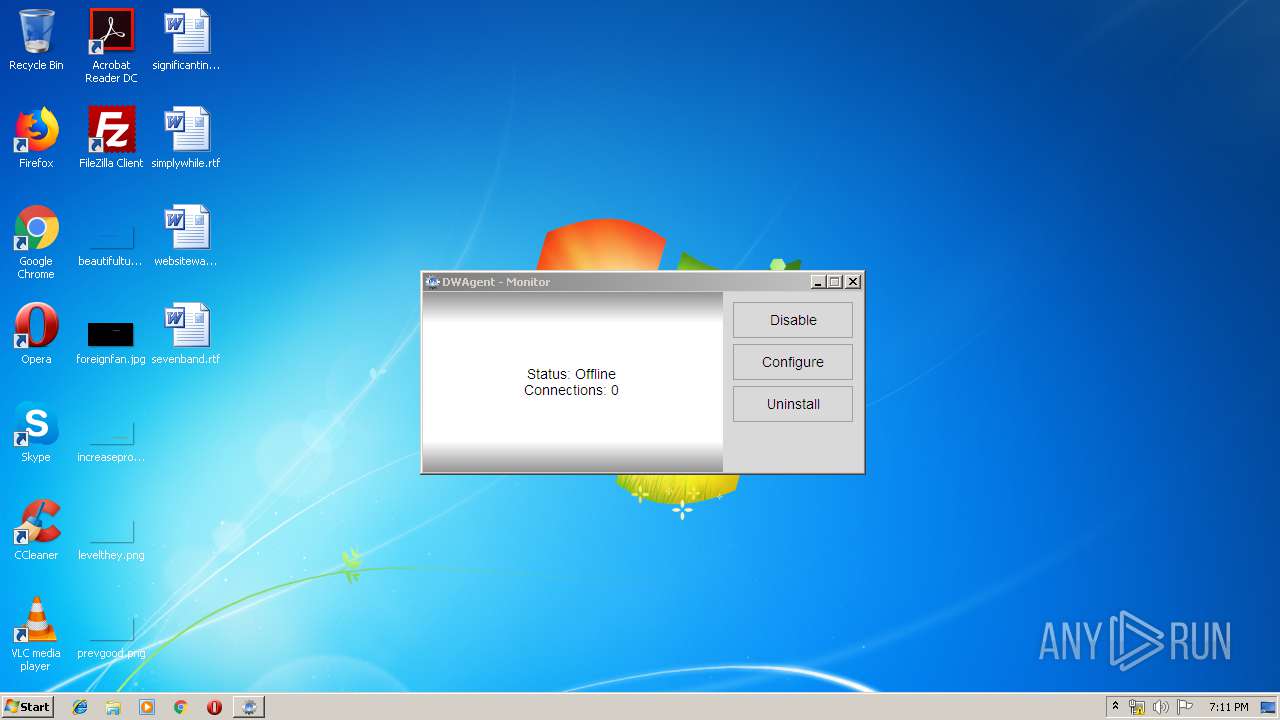
Manual execution by user
- dwaglnc.exe (PID: 3056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:25 17:48:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.3 |
| CodeSize: | 289792 |
| InitializedDataSize: | 351744 |
| UninitializedDataSize: | 26112 |
| EntryPoint: | 0x1490 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jan-2019 16:48:46 |
| Detected languages: |
|
| TLS Callbacks: | 2 callback(s) detected. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 25-Jan-2019 16:48:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00046BD4 | 0x00046C00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.16635 |
.data | 0x00048000 | 0x000000AC | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.21924 |
.rdata | 0x00049000 | 0x00004140 | 0x00004200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.56509 |
.bss | 0x0004E000 | 0x00006588 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00055000 | 0x000014A8 | 0x00001600 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.16995 |
.CRT | 0x00057000 | 0x00000034 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.262518 |
.tls | 0x00058000 | 0x00000008 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00059000 | 0x00009208 | 0x00009400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.29315 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.2684 | 296 | UNKNOWN | English - United States | RT_ICON |
2 | 5.07571 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 6.10549 | 872 | UNKNOWN | English - United States | RT_ICON |
4 | 3.74743 | 744 | UNKNOWN | English - United States | RT_ICON |
5 | 6.23414 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.96389 | 3240 | UNKNOWN | English - United States | RT_ICON |
7 | 3.28585 | 1640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.35345 | 3752 | UNKNOWN | English - United States | RT_ICON |
9 | 4.94859 | 7336 | UNKNOWN | English - United States | RT_ICON |
10 | 5.55446 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
msvcrt.dll |
Total processes
77
Monitored processes
29
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
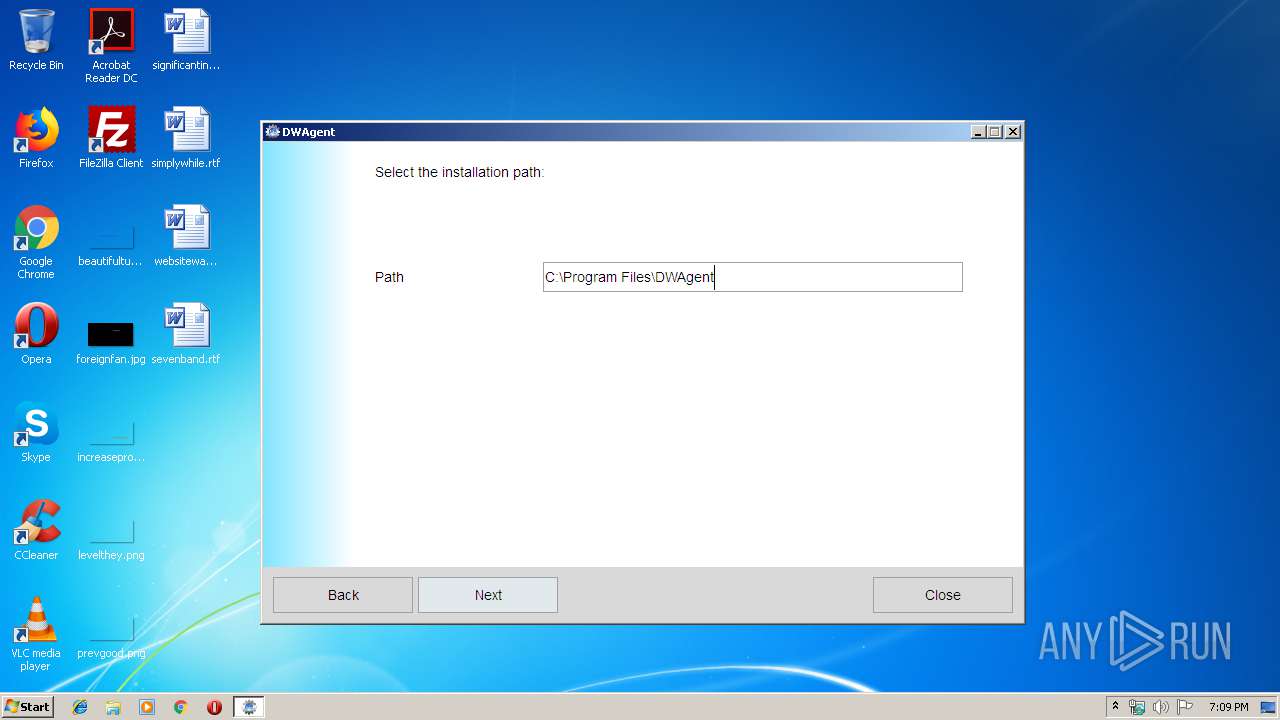
| 1968 | "C:\Program Files\DWAgent\runtime\dwagent.exe" -S -m monitor window | C:\Program Files\DWAgent\runtime\dwagent.exe | — | dwaglnc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2056 | "C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\dwagent.exe" -S -m installer | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\dwagent.exe | — | dwagent_x86.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\DWAgent\native\dwagsvc.exe" run | C:\Program Files\DWAgent\native\dwagsvc.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2276 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\DWAgent\native\dwagsvc.exe" installShortcuts" | C:\Windows\system32\cmd.exe | — | dwagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2332 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\DWAgent\native\dwagsvc.exe" stopService" | C:\Windows\system32\cmd.exe | — | dwagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\dwagent.exe" -S -m installer gotoopt=install | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\dwagent.exe | dwagent_x86.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2428 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\DWAgent\native\dwagsvc.exe" installService" | C:\Windows\system32\cmd.exe | — | dwagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2500 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\DWAgent\native\dwagsvc.exe" startService" | C:\Windows\system32\cmd.exe | — | dwagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | "C:\Program Files\DWAgent\runtime\dwagent.exe" -S -m agent -filelog | C:\Program Files\DWAgent\runtime\dwagent.exe | dwagsvc.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2688 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\DWAgent\native\dwagsvc.exe" installAutoRun" | C:\Windows\system32\cmd.exe | — | dwagent.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 123
Read events
1 098
Write events
25
Delete events
0
Modification events
| (PID) Process: | (3152) dwagent_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3152) dwagent_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3024) dwagent_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3024) dwagent_x86.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3472) dwaglnc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3472) dwaglnc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3552) dwagsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | DWAgentMon |
Value: "C:\Program Files\DWAgent\native\dwaglnc.exe" systray | |||
| (PID) Process: | (3380) dwagsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DWAgent |
| Operation: | write | Name: | DisplayName |
Value: DWAgent | |||
| (PID) Process: | (3380) dwagsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DWAgent |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\DWAgent\ui\images\logo.ico | |||
| (PID) Process: | (3380) dwagsvc.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\DWAgent |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\DWAgent | |||
Executable files
59
Suspicious files
0
Text files
41
Unknown types
1 082
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\win.7z | — | |
MD5:— | SHA256:— | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\_ctypes_test.pyd | executable | |
MD5:— | SHA256:— | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\pyexpat.pyd | executable | |
MD5:5DDC2E0F87C91172CA93E1CBEA27D78D | SHA256:8AB94B0A8811C6365D0A5B4509E4B628666D45133C432B3B244619F24E5C1A81 | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\winsound.pyd | executable | |
MD5:— | SHA256:— | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\DLLs\_ctypes.pyd | executable | |
MD5:F1134B690B2DC0E6AA0F31BE1ED9B05F | SHA256:030BF1AAFF316DFBB1B424D91B1340B331C2E38F3E874AE532284C6170D93E7E | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\_ctypes.pyd | executable | |
MD5:14A00D260C8DD3C05ACD2AEE92C80497 | SHA256:14DF3E276E4AB33AEC0731201DD6CD571BAFF1B7F21430CC1E4E0D36251475BE | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\DLLs\select.pyd | executable | |
MD5:BDC7B944B9319F9708AF1949B42BAE4B | SHA256:83B5C76D938BC50E58C851D56EF8CBC1001D2E81A1E1F8F5DFED2245244C1472 | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\Microsoft.VC90.CRT.manifest | xml | |
MD5:CFDFB365D8F581E80292124EEB97854F | SHA256:F20BC224A6E3EF391C67FD91378E2EC9734E450EA30AC1D6B84E5ACB4AC9A087 | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\_elementtree.pyd | executable | |
MD5:2ED01DAEBCA0BC27F7CF8B6262F85011 | SHA256:8A8809692D397DA8E3D673B925F1575937D300A422EEDC99FF2D86D9FC7573B5 | |||
| 3152 | dwagent_x86.exe | C:\Users\admin\AppData\Local\Temp\dwagent_x8620190815180935\runtime\bit64\DLLs\_socket.pyd | executable | |
MD5:98C84771B43613B5F2E7F402488CABD2 | SHA256:E7AADAD889CD73E8B83315E4C26CE6BFEFE3695E0CEF43E73BE4141D7DE9A6EB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | dwagent.exe | 51.89.4.88:443 | www.dwservice.net | — | GB | unknown |
2644 | dwagent.exe | 51.89.4.88:443 | www.dwservice.net | — | GB | unknown |
2388 | dwagent.exe | 54.38.139.233:443 | node443189.dwservice.net | OVH SAS | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dwservice.net |
| unknown |
node443189.dwservice.net |
| unknown |