| File name: | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe |
| Full analysis: | https://app.any.run/tasks/00e61a6c-7546-4277-a5b3-b837f8f22809 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | May 21, 2022, 04:24:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 88687C7DC456C49C92E1C108D2E9C742 |
| SHA1: | 07441F02634480B05714CE7A4D8194681C76EBCC |
| SHA256: | 5E4990AF033733F53D7B03D5F63184239A7C7D000763B53DA20147750144598D |
| SSDEEP: | 3072:7BdoKA9aCWuUHslgAsUXk5yOi8fExgwOULiQHtZIaH/hiPbkaR2EF7o:7Bd2aCgHUgQXzORygw/icZB/naBo |
MALICIOUS
Changes the autorun value in the registry
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Drops executable file immediately after starts
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
GandCrab detected
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
SUSPICIOUS
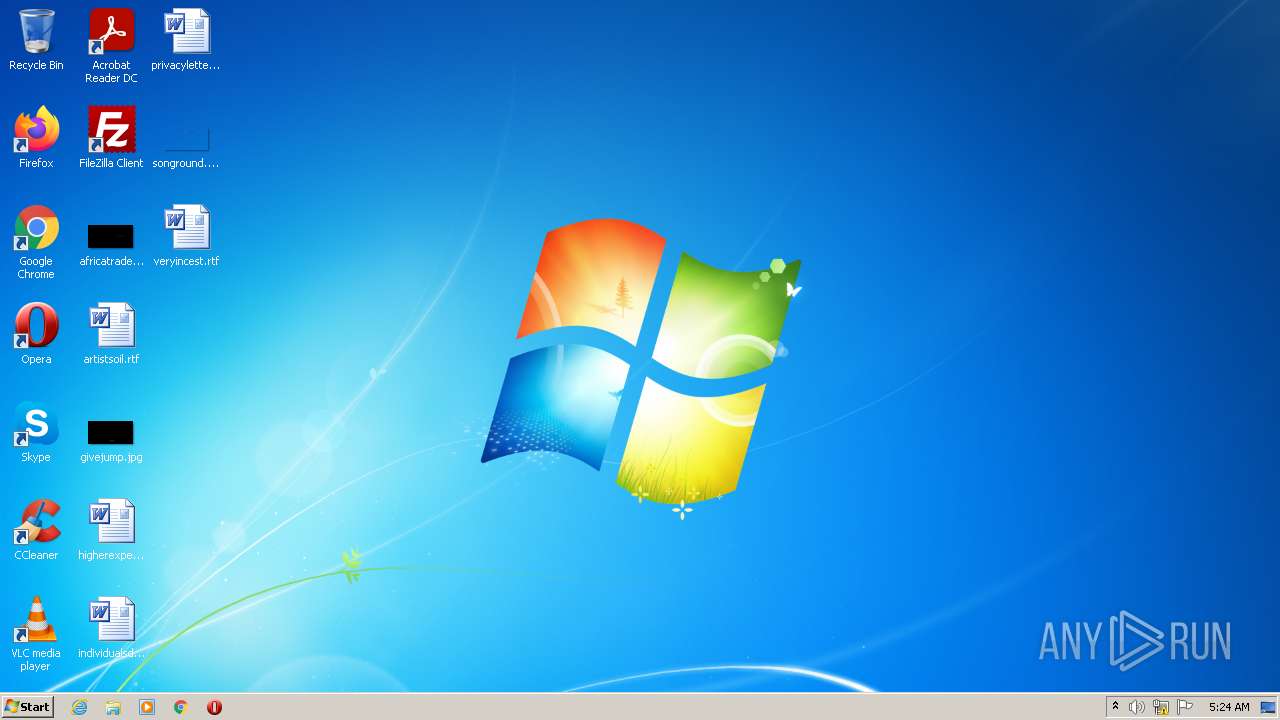
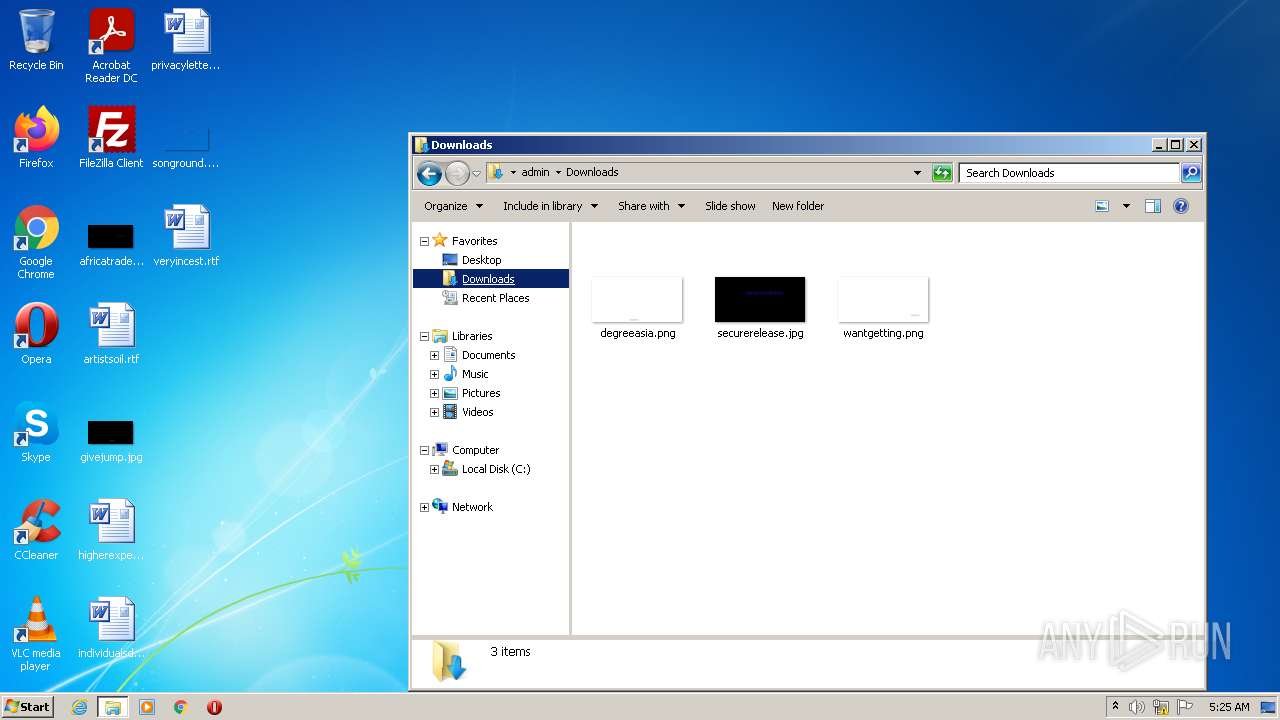
Creates files in the user directory
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Checks supported languages
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Reads the computer name
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Executable content was dropped or overwritten
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Reads Environment values
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Drops a file with a compile date too recent
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
Reads CPU info
- 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe (PID: 2916)
INFO
Checks supported languages
- nslookup.exe (PID: 3260)
- nslookup.exe (PID: 3780)
- nslookup.exe (PID: 3232)
- nslookup.exe (PID: 2668)
- nslookup.exe (PID: 1604)
- nslookup.exe (PID: 3144)
- nslookup.exe (PID: 3516)
- nslookup.exe (PID: 1796)
- nslookup.exe (PID: 940)
- WINWORD.EXE (PID: 732)
- nslookup.exe (PID: 3472)
- nslookup.exe (PID: 2288)
- nslookup.exe (PID: 2612)
- nslookup.exe (PID: 3744)
- nslookup.exe (PID: 3664)
- nslookup.exe (PID: 3136)
- nslookup.exe (PID: 2012)
- nslookup.exe (PID: 3860)
- nslookup.exe (PID: 2420)
- nslookup.exe (PID: 1192)
- nslookup.exe (PID: 2076)
- nslookup.exe (PID: 128)
- nslookup.exe (PID: 3368)
- nslookup.exe (PID: 3188)
- nslookup.exe (PID: 1168)
- explorer.exe (PID: 2004)
- nslookup.exe (PID: 348)
- nslookup.exe (PID: 3024)
- nslookup.exe (PID: 1152)
- nslookup.exe (PID: 4064)
- nslookup.exe (PID: 2976)
- nslookup.exe (PID: 2428)
- nslookup.exe (PID: 2272)
- nslookup.exe (PID: 2968)
- nslookup.exe (PID: 2500)
- nslookup.exe (PID: 1888)
- nslookup.exe (PID: 3972)
- nslookup.exe (PID: 2940)
- WINWORD.EXE (PID: 4020)
- nslookup.exe (PID: 3808)
- nslookup.exe (PID: 3952)
- nslookup.exe (PID: 2800)
- nslookup.exe (PID: 2100)
- nslookup.exe (PID: 1280)
- nslookup.exe (PID: 3296)
- nslookup.exe (PID: 2852)
- nslookup.exe (PID: 872)
- nslookup.exe (PID: 2432)
- nslookup.exe (PID: 2948)
- nslookup.exe (PID: 1252)
- nslookup.exe (PID: 3524)
- nslookup.exe (PID: 2016)
- nslookup.exe (PID: 2912)
- nslookup.exe (PID: 1872)
Reads the computer name
- nslookup.exe (PID: 3260)
- nslookup.exe (PID: 3780)
- nslookup.exe (PID: 3232)
- nslookup.exe (PID: 2668)
- nslookup.exe (PID: 1604)
- nslookup.exe (PID: 3144)
- nslookup.exe (PID: 1796)
- nslookup.exe (PID: 3516)
- nslookup.exe (PID: 940)
- WINWORD.EXE (PID: 732)
- nslookup.exe (PID: 2288)
- nslookup.exe (PID: 3472)
- nslookup.exe (PID: 128)
- nslookup.exe (PID: 2612)
- nslookup.exe (PID: 3744)
- nslookup.exe (PID: 3136)
- nslookup.exe (PID: 3664)
- nslookup.exe (PID: 3860)
- nslookup.exe (PID: 2012)
- nslookup.exe (PID: 2420)
- nslookup.exe (PID: 2076)
- nslookup.exe (PID: 1192)
- nslookup.exe (PID: 3188)
- nslookup.exe (PID: 3368)
- explorer.exe (PID: 2004)
- nslookup.exe (PID: 348)
- nslookup.exe (PID: 1152)
- nslookup.exe (PID: 3024)
- nslookup.exe (PID: 4064)
- nslookup.exe (PID: 2976)
- nslookup.exe (PID: 2428)
- nslookup.exe (PID: 2968)
- nslookup.exe (PID: 3972)
- nslookup.exe (PID: 2940)
- nslookup.exe (PID: 2500)
- nslookup.exe (PID: 1168)
- nslookup.exe (PID: 2272)
- nslookup.exe (PID: 1888)
- nslookup.exe (PID: 3952)
- nslookup.exe (PID: 2800)
- nslookup.exe (PID: 3808)
- WINWORD.EXE (PID: 4020)
- nslookup.exe (PID: 2432)
- nslookup.exe (PID: 872)
- nslookup.exe (PID: 3296)
- nslookup.exe (PID: 2852)
- nslookup.exe (PID: 1280)
- nslookup.exe (PID: 2100)
- nslookup.exe (PID: 2948)
- nslookup.exe (PID: 1252)
- nslookup.exe (PID: 3524)
- nslookup.exe (PID: 2016)
- nslookup.exe (PID: 1872)
- nslookup.exe (PID: 2912)
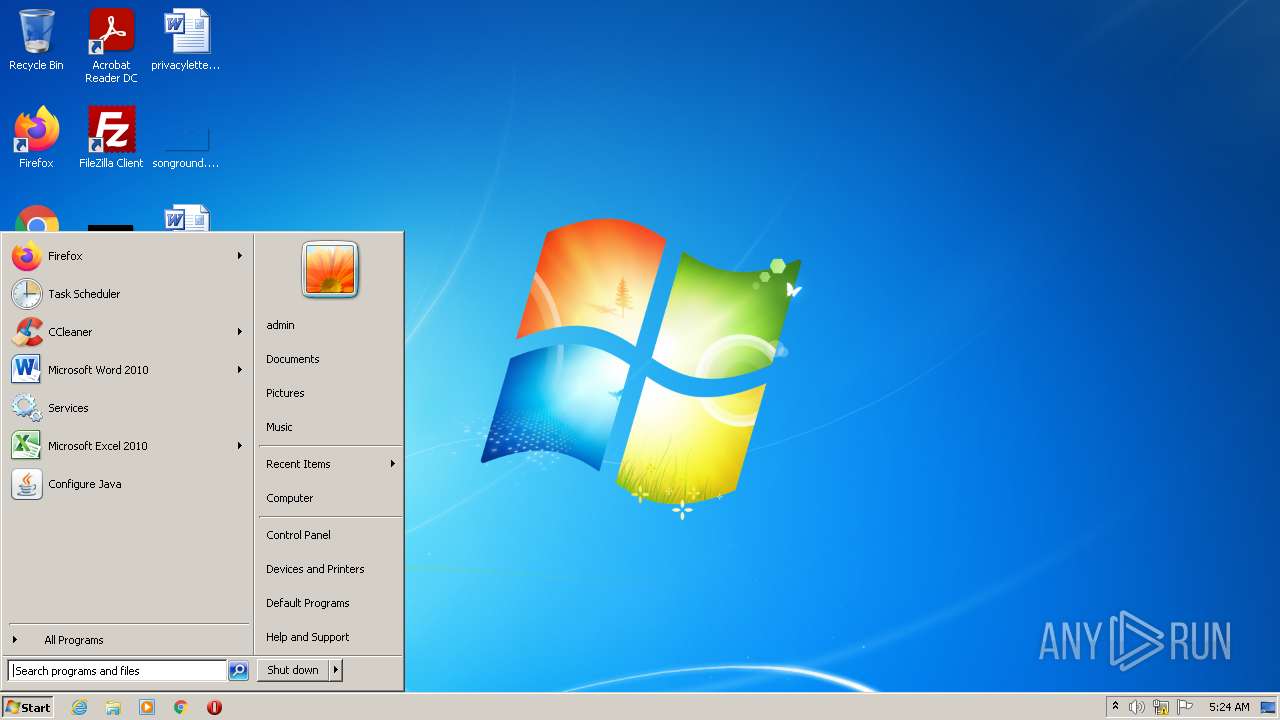
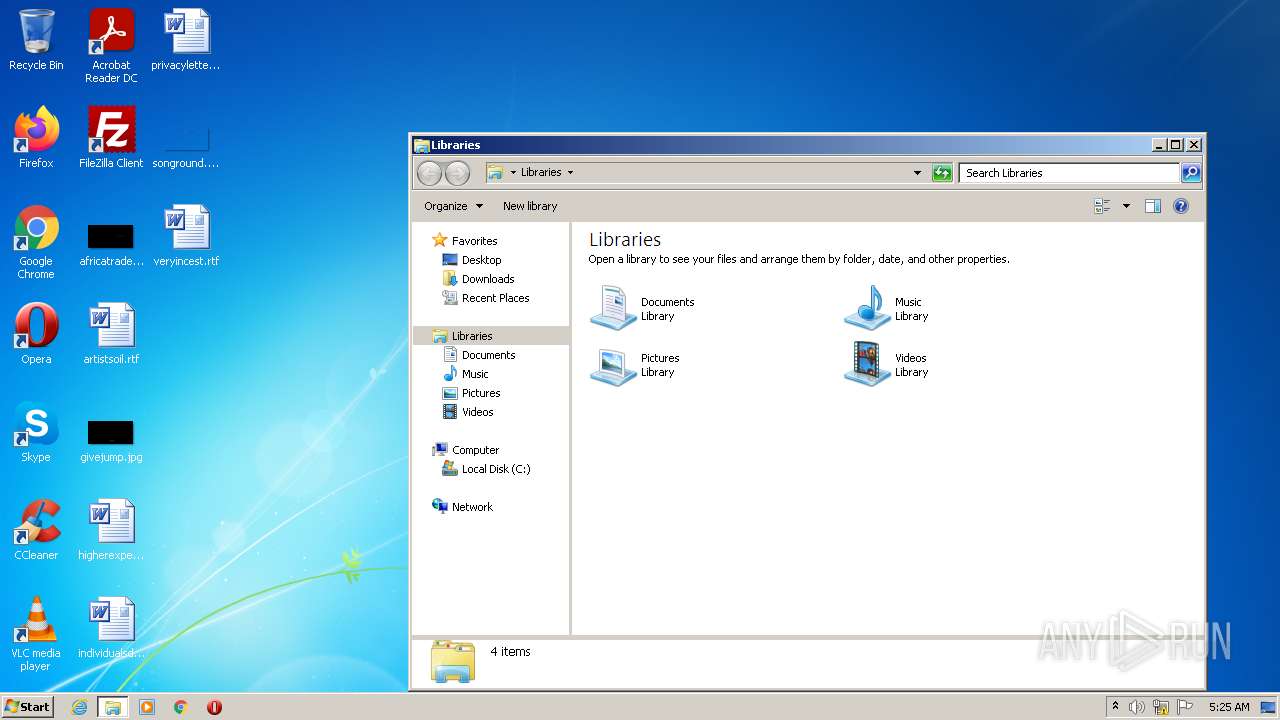
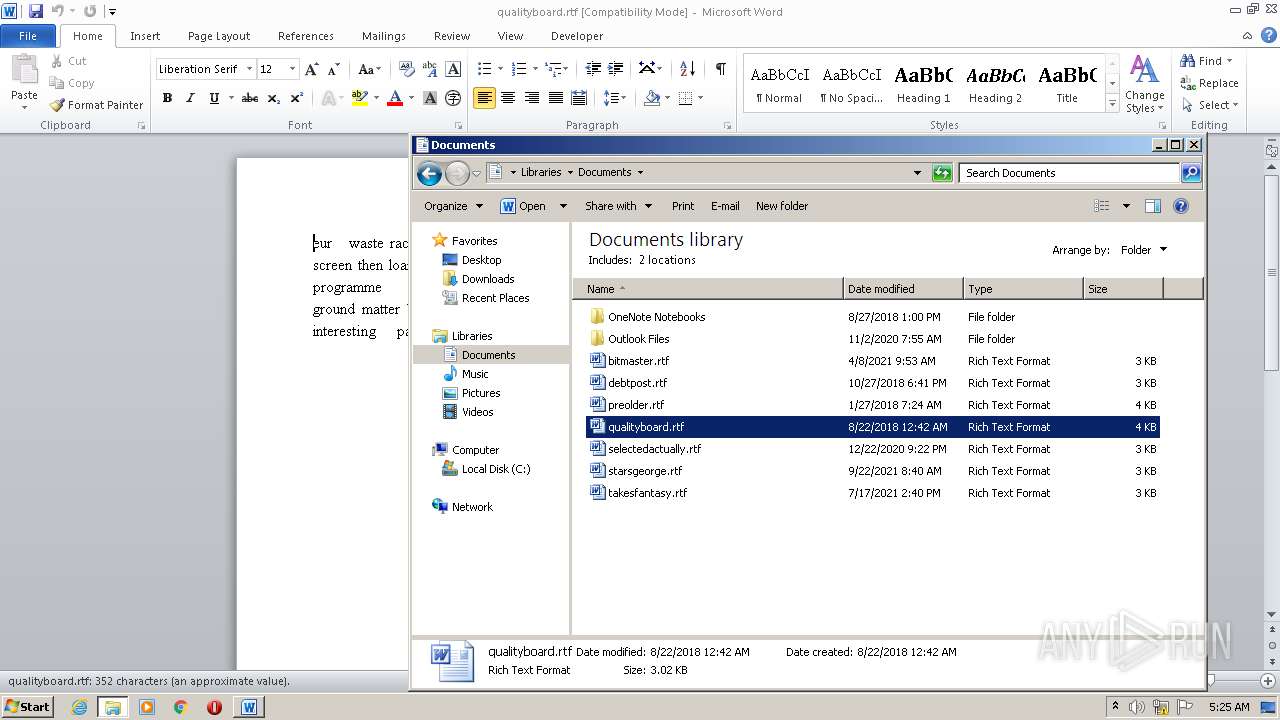
Manual execution by user
- WINWORD.EXE (PID: 732)
- explorer.exe (PID: 2004)
- WINWORD.EXE (PID: 4020)
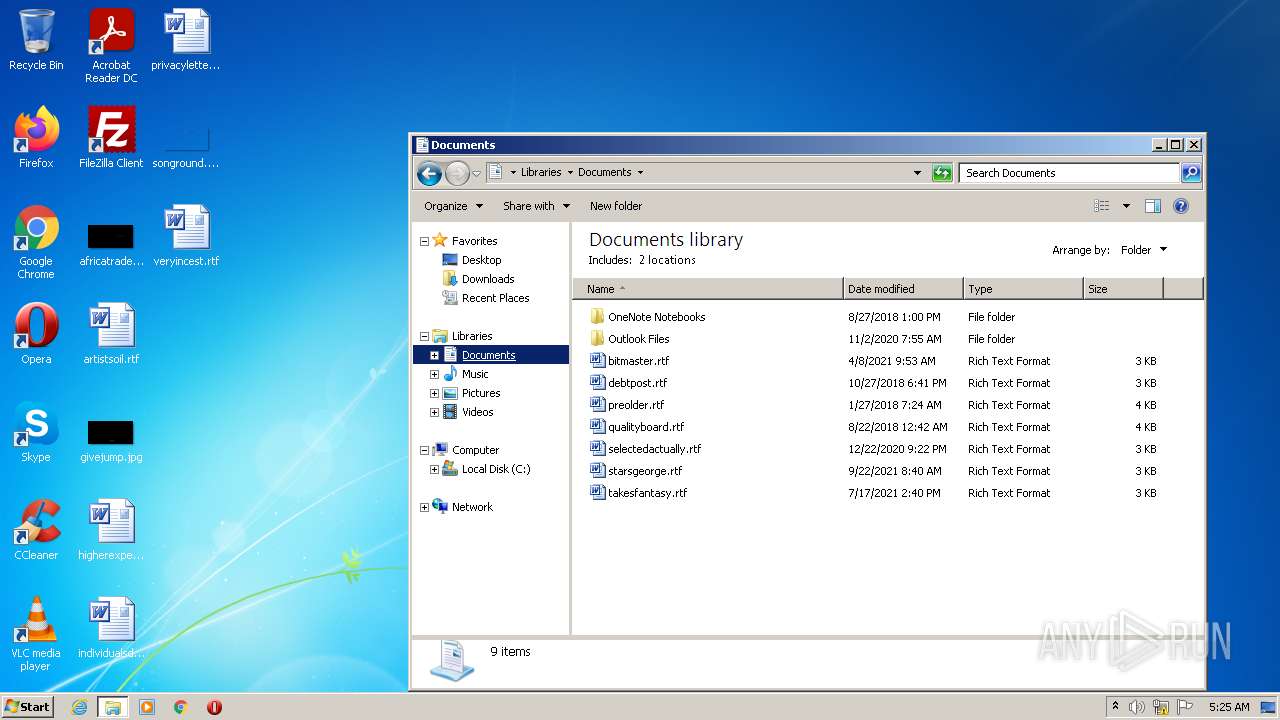
Creates files in the user directory
- WINWORD.EXE (PID: 732)
- WINWORD.EXE (PID: 4020)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 732)
- WINWORD.EXE (PID: 4020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .dll | | | Win32 Dynamic Link Library (generic) (43.5) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (29.8) |
| .exe | | | Generic Win/DOS Executable (13.2) |
| .exe | | | DOS Executable Generic (13.2) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x4de7 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 6154240 |
| CodeSize: | 83456 |
| LinkerVersion: | 9 |
| PEType: | PE32 |
| TimeStamp: | 2018:04:22 20:26:27+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Apr-2018 18:26:27 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 22-Apr-2018 18:26:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001446C | 0x00014600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60922 |
.rdata | 0x00016000 | 0x000045E8 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.34328 |
.data | 0x0001B000 | 0x005B0A68 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.49829 |
.rsrc | 0x005CC000 | 0x00024DF6 | 0x00024E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.56893 |
.reloc | 0x005F1000 | 0x0000550E | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.015 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.77887 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 6.67163 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 2.72308 | 192 | UNKNOWN | UNKNOWN | RT_STRING |
8 | 2.1371 | 76 | UNKNOWN | UNKNOWN | RT_STRING |
9 | 2.39676 | 114 | UNKNOWN | UNKNOWN | RT_STRING |
10 | 3.01564 | 272 | UNKNOWN | UNKNOWN | RT_STRING |
11 | 3.05985 | 382 | UNKNOWN | UNKNOWN | RT_STRING |
13 | 2.8616 | 256 | UNKNOWN | UNKNOWN | RT_STRING |
14 | 2.98259 | 336 | UNKNOWN | UNKNOWN | RT_STRING |
15 | 2.98468 | 346 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.dll |
KERNEL32.dll |
USER32.dll |
ole32.dll |
Total processes
145
Monitored processes
55
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | nslookup zonealarm.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | nslookup zonealarm.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
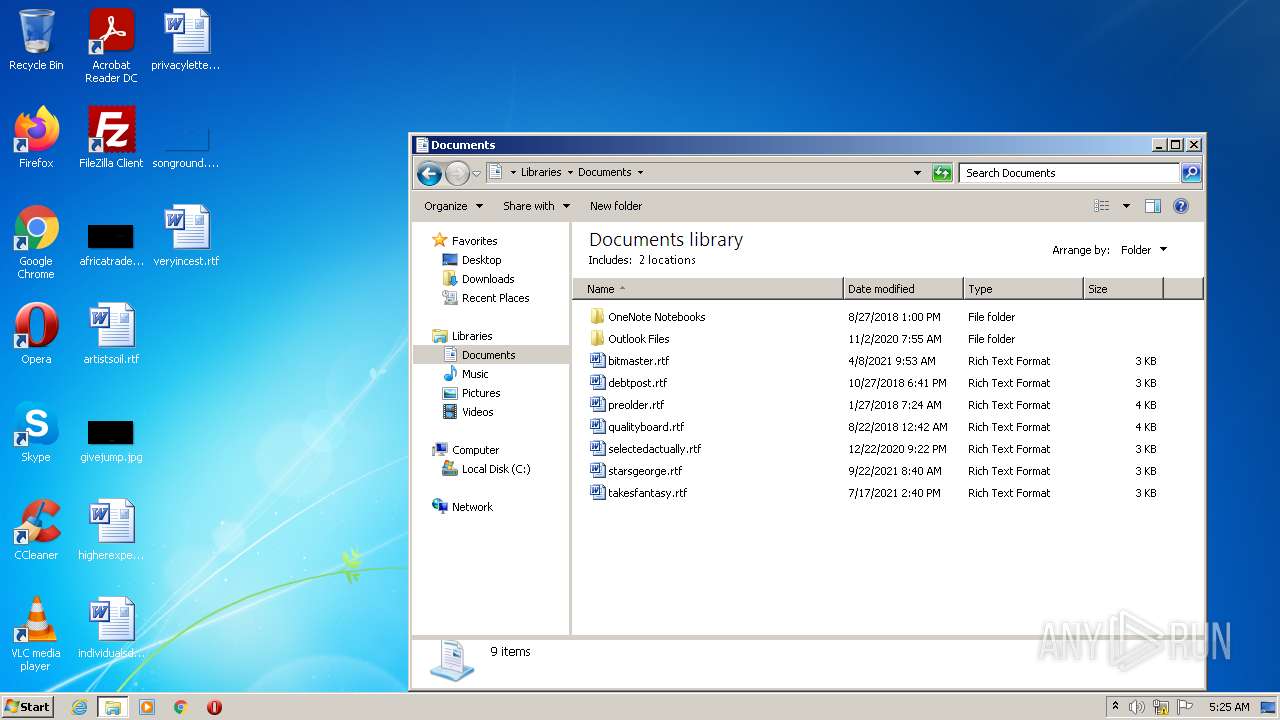
| 732 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\veryincest.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 872 | nslookup ransomware.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 940 | nslookup zonealarm.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | nslookup ransomware.bit ns2.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1168 | nslookup zonealarm.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1192 | nslookup zonealarm.bit ns1.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1252 | nslookup zonealarm.bit ns2.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1280 | nslookup ransomware.bit ns2.corp-servers.ru | C:\Windows\system32\nslookup.exe | — | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 056
Read events
14 438
Write events
323
Delete events
295
Modification events
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | nafndjfayxb |
Value: "C:\Users\admin\AppData\Roaming\Microsoft\eekiqy.exe" | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2916) 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
1
Suspicious files
2
Text files
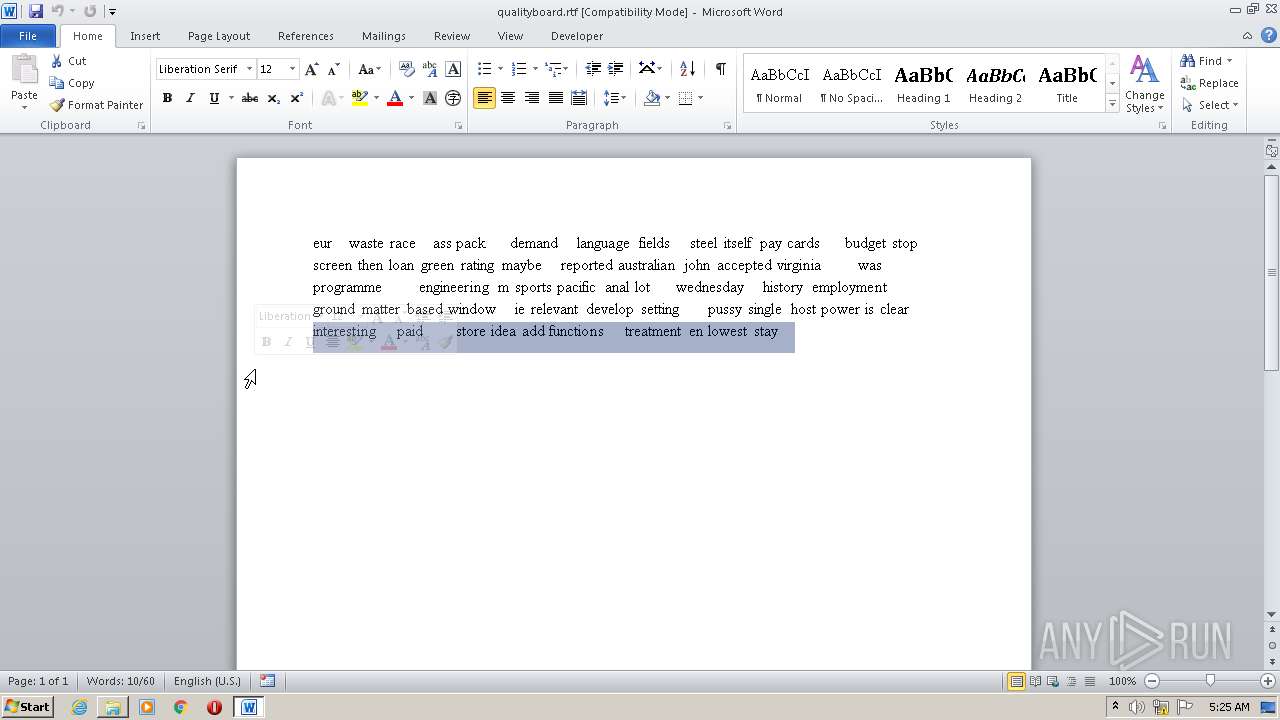
1
Unknown types
13
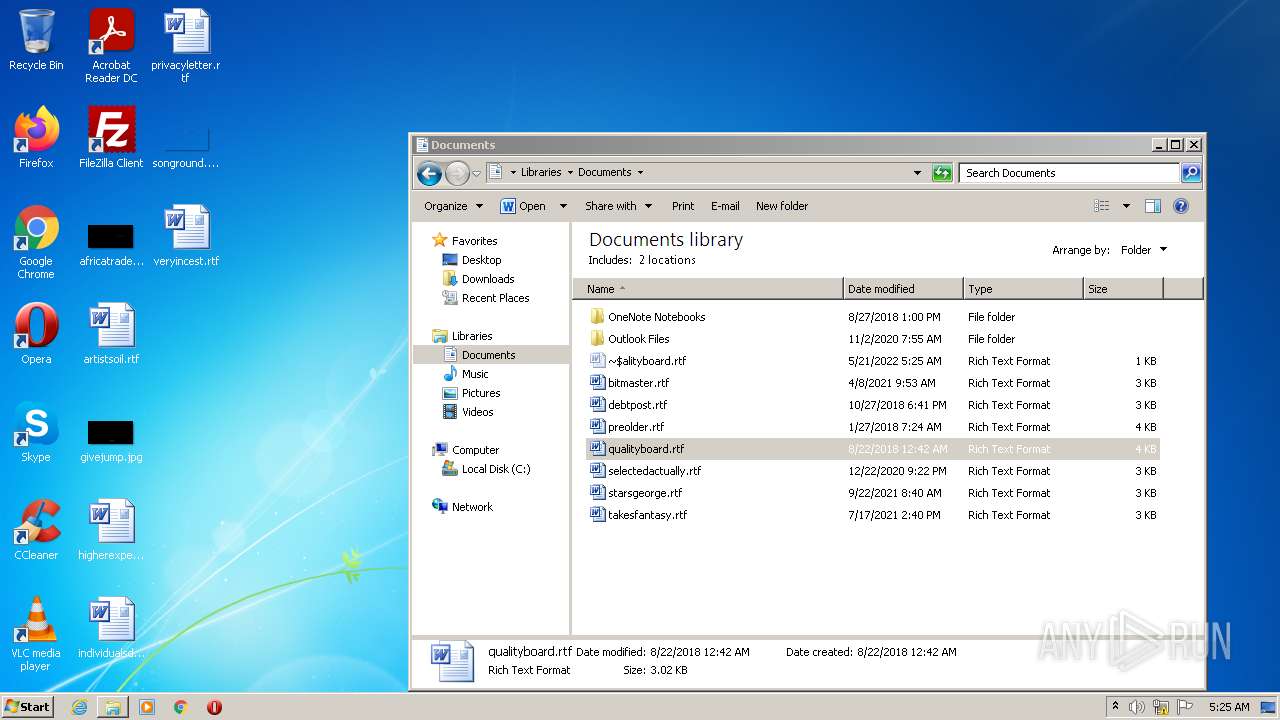
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFDCF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7273.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2916 | 5e4990af033733f53d7b03d5f63184239a7c7d000763b53da20147750144598d.exe | C:\Users\admin\AppData\Roaming\Microsoft\eekiqy.exe | executable | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | ini | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\Desktop\~$ryincest.rtf | pgc | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\veryincest.rtf.LNK | lnk | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C7276F09-7E19-4D4F-9E5A-A7158311F996}.tmp | dbf | |
MD5:— | SHA256:— | |||
| 732 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{1A635D46-2698-44E7-BB27-A5583F808B63}.tmp | binary | |
MD5:— | SHA256:— | |||
| 4020 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
215
Threats
166
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
ipv4bot.whatismyipaddress.com |
| shared |
ns1.corp-servers.ru |
| unknown |
2.100.168.192.in-addr.arpa |
| whitelisted |
zonealarm.bit |
| malicious |
ns2.corp-servers.ru |
| unknown |
ransomware.bit |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | ET TROJAN Observed GandCrab Ransomware Domain (zonealarm .bit in DNS Lookup) |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | A Network Trojan was detected | ET TROJAN Observed GandCrab Ransomware Domain (ransomware .bit in DNS Lookup) |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |
— | — | Potentially Bad Traffic | ET INFO DNS Query Domain .bit |