| File name: | EH Typing Product 2019 U1.17.exe |
| Full analysis: | https://app.any.run/tasks/56850d3c-f194-4414-a099-2d9fc147c286 |
| Verdict: | Malicious activity |
| Analysis date: | March 02, 2019, 07:01:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 33D93B887D584C4E8D6A341EBF46E0AE |
| SHA1: | 714E766632BF370DA0590B274254C69DD8204E67 |
| SHA256: | 5E2F7656AD403BF477F87C4700B3F2DB779B58496AB0952FBA5725B75DDDD945 |
| SSDEEP: | 98304:vUWEwD838rle1CbgkuBLXjtM5xVTFc3F1mMXbInQr7El+5f:vUWEG834epdBLXjtM/VT4F1mGMnQr7E+ |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 1636)
- regsvr32.exe (PID: 3372)
- regsvr32.exe (PID: 2652)
- regsvr32.exe (PID: 3912)
- regsvr32.exe (PID: 3072)
- TypingTutor.exe (PID: 3648)
Registers / Runs the DLL via REGSVR32.EXE
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Application was dropped or rewritten from another process
- TypingTutor.exe (PID: 3648)
SUSPICIOUS
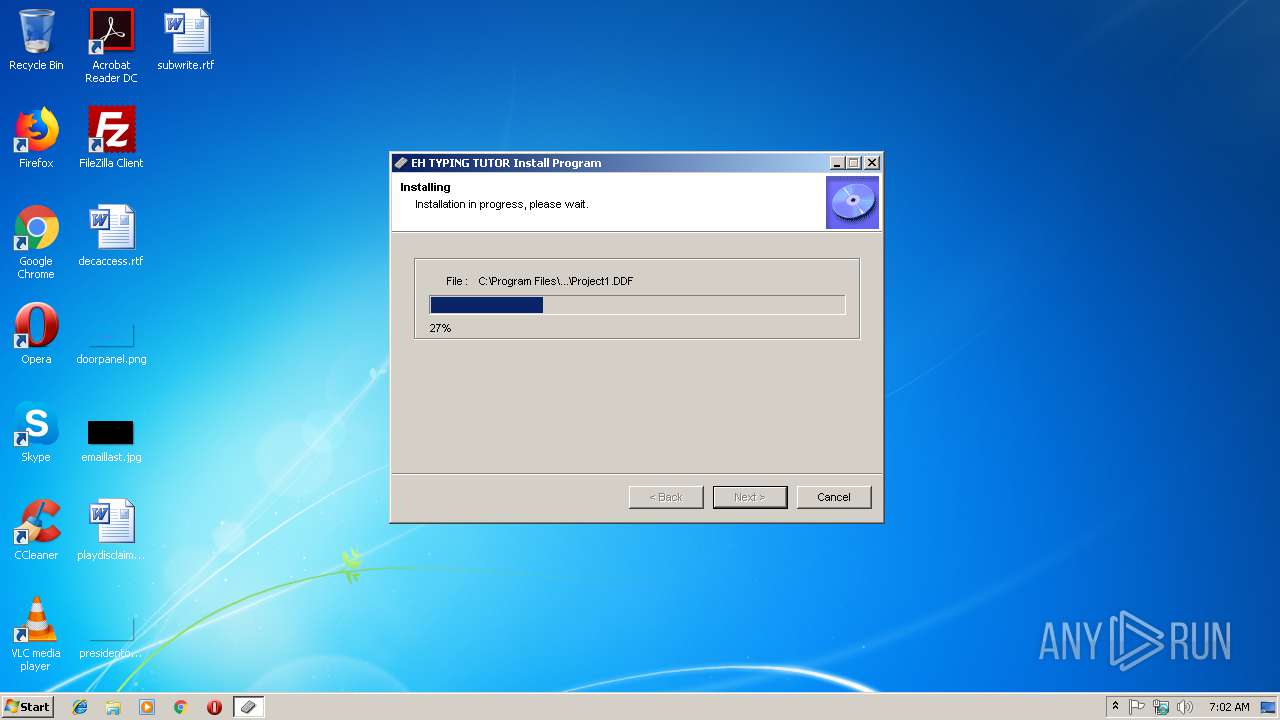
Executable content was dropped or overwritten
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Creates files in the Windows directory
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Creates COM task schedule object
- regsvr32.exe (PID: 3912)
Creates files in the user directory
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Creates a software uninstall entry
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Creates files in the program directory
- EH Typing Product 2019 U1.17.exe (PID: 3620)
INFO
Dropped object may contain Bitcoin addresses
- EH Typing Product 2019 U1.17.exe (PID: 3620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:10:27 13:26:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 94208 |
| InitializedDataSize: | 135168 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13eec |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.41 |
| ProductVersionNumber: | 2.0.0.41 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 2, 0, 0, 41 |
| InternalName: | - |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | - |
| PrivateBuild: | - |
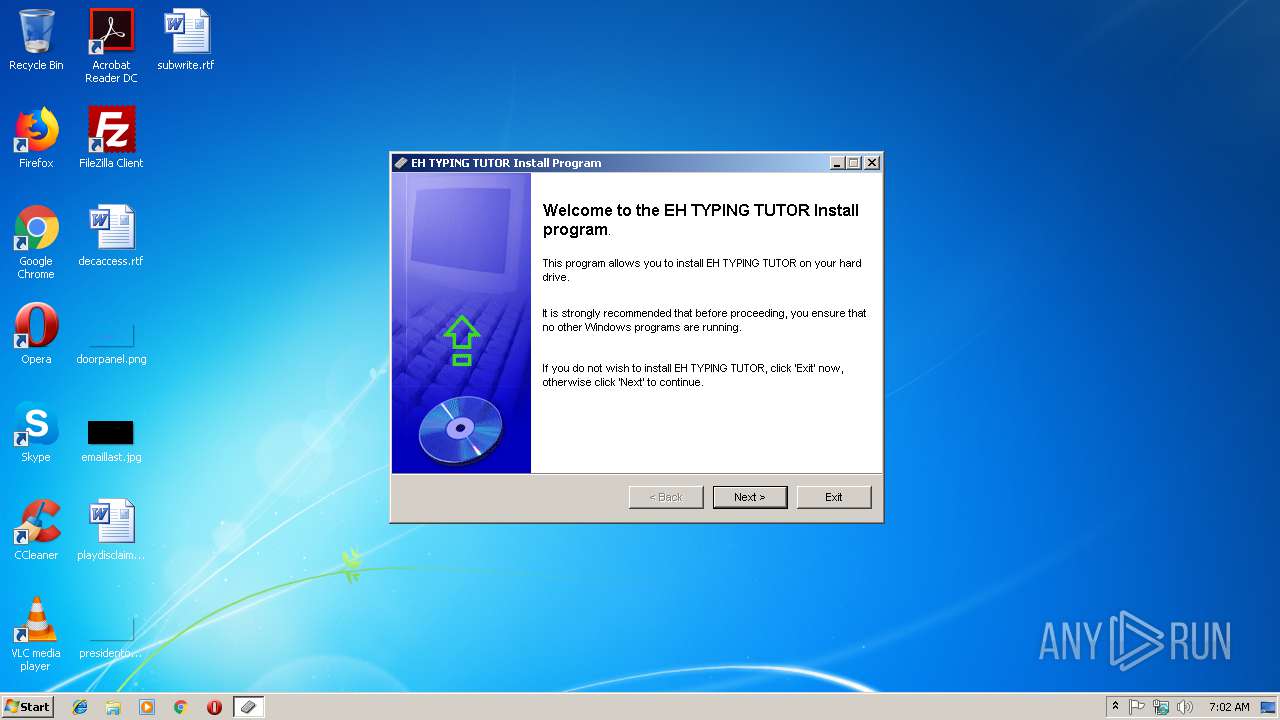
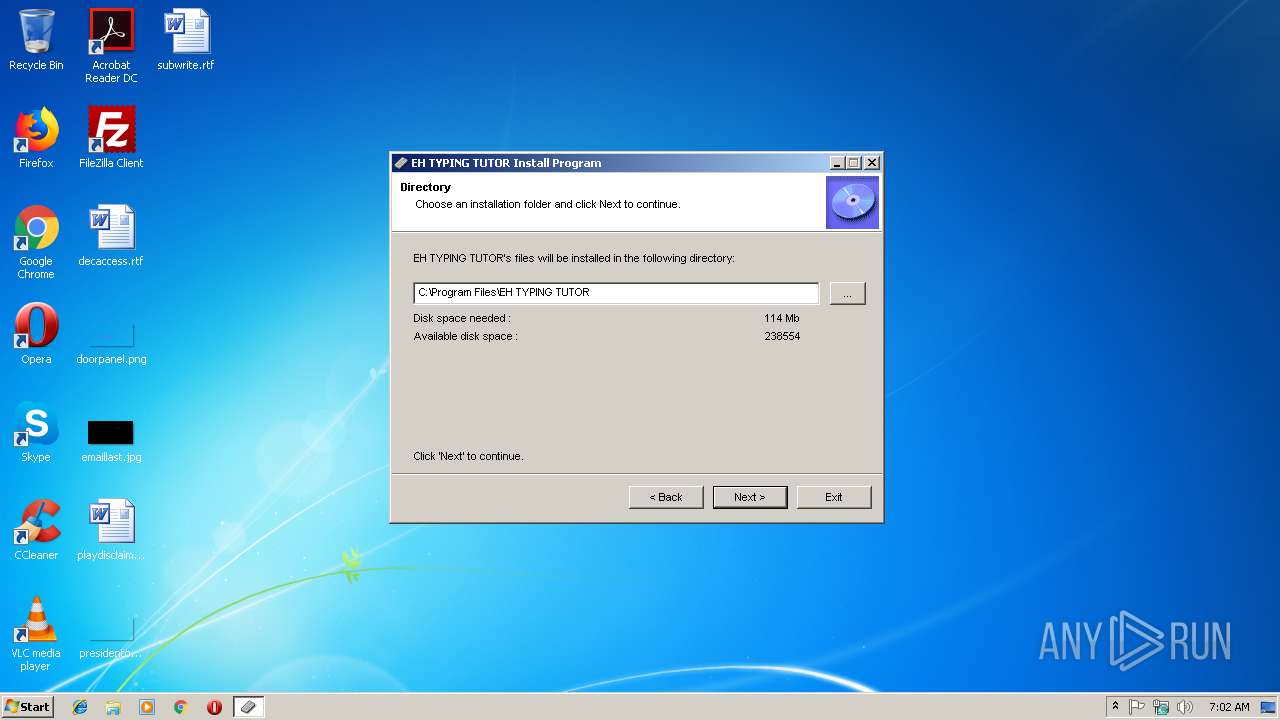
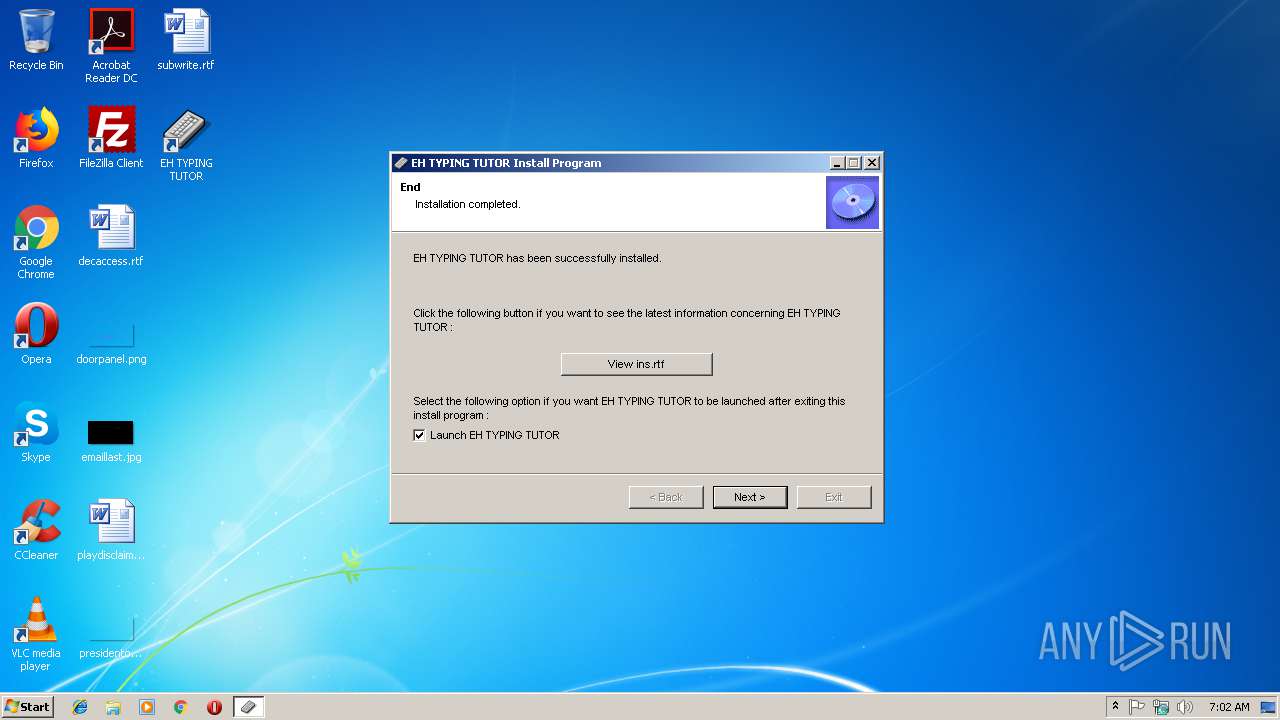
| ProductName: | EH TYPING TUTOR Install Program |
| ProductVersion: | 2, 0, 0, 41 |
| SpecialBuild: | - |
Total processes
41
Monitored processes
9
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1636 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\COMCAT.DLL" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\RICHTX32.OCX" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2652 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\MSADODC.OCX" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3072 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\MSWINSCK.OCX" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3124 | "C:\Users\admin\AppData\Local\Temp\EH Typing Product 2019 U1.17.exe" | C:\Users\admin\AppData\Local\Temp\EH Typing Product 2019 U1.17.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 2, 0, 0, 41 Modules
| |||||||||||||||
| 3372 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\COMDLG32.OCX" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3620 | "C:\Users\admin\AppData\Local\Temp\EH Typing Product 2019 U1.17.exe" | C:\Users\admin\AppData\Local\Temp\EH Typing Product 2019 U1.17.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2, 0, 0, 41 Modules
| |||||||||||||||
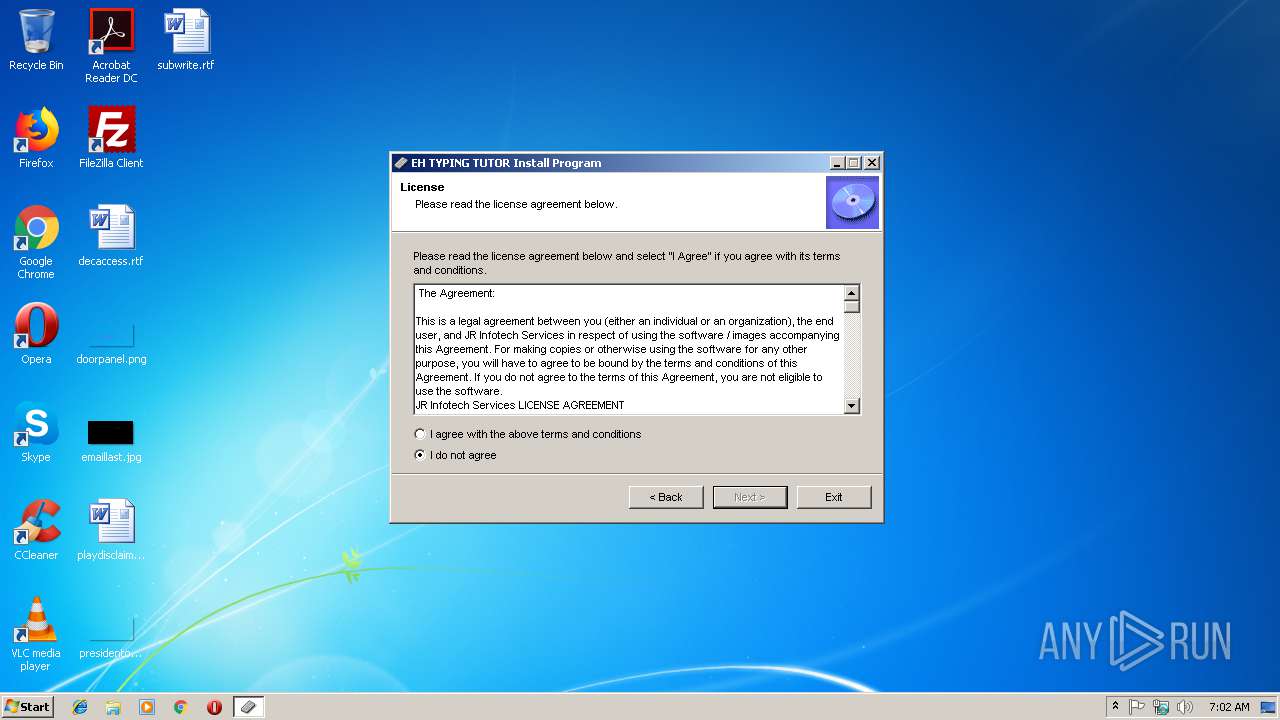
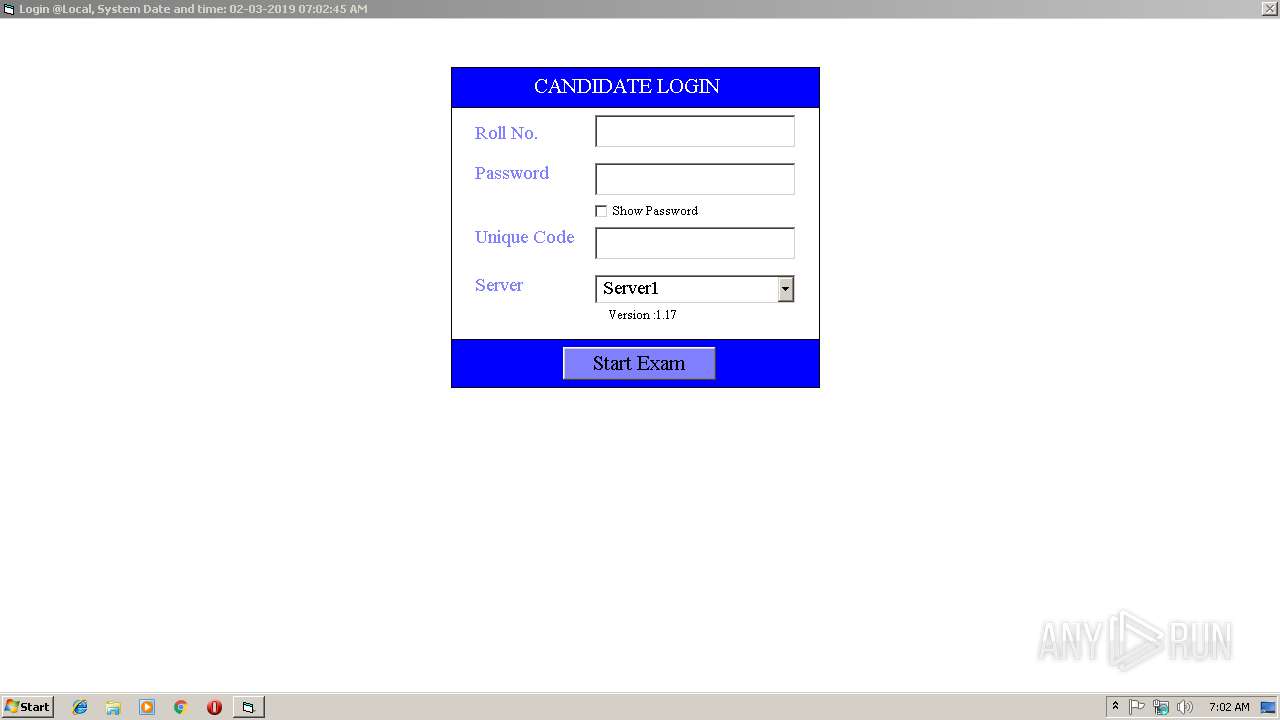
| 3648 | "C:\Program Files\EH TYPING TUTOR\TypingTutor.exe" | C:\Program Files\EH TYPING TUTOR\TypingTutor.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: JR Infotech Services(R) Integrity Level: HIGH Exit code: 0 Version: 4.02.0314 Modules
| |||||||||||||||
| 3912 | "C:\Windows\system32\regsvr32" /s "C:\Program Files\EH TYPING TUTOR\MSSTDFMT.DLL" | C:\Windows\system32\regsvr32.exe | — | EH Typing Product 2019 U1.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
434
Read events
164
Write events
248
Delete events
22
Modification events
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\asycfilt.dll |
Value: 1 | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Code 128 (TrueType) |
Value: code128.ttf | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | DevLys 010 (TrueType) |
Value: DevLys 010.ttf | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Kruti Dev 160 (TrueType) |
Value: k160.ttf | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Kruti Dev 014 (TrueType) |
Value: Kruti Dev 014.TTF | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Kruti Dev 016 (TrueType) |
Value: Kruti Dev 016.TTF | |||
| (PID) Process: | (3620) EH Typing Product 2019 U1.17.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Fonts |
| Operation: | write | Name: | Kruti Dev 010 (TrueType) |
Value: KurtiDev.TTF | |||
| (PID) Process: | (1636) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Component Categories\{40FC6ED3-2438-11CF-A3DB-080036F12502} |
| Operation: | write | Name: | 409 |
Value: Embeddable Objects | |||
| (PID) Process: | (1636) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Component Categories\{40FC6ED4-2438-11CF-A3DB-080036F12502} |
| Operation: | write | Name: | 409 |
Value: Controls | |||
| (PID) Process: | (1636) regsvr32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Component Categories\{40FC6ED5-2438-11CF-A3DB-080036F12502} |
| Operation: | write | Name: | 409 |
Value: Automation Objects | |||
Executable files
28
Suspicious files
1
Text files
241
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\Uninstal.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\oleaut32.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\olepro32.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\stdole2.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\msvbvm60.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\colPhysicalMedia.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\cPhysicalMedia.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\temp\Database.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\DATAFILE.$A | — | |
MD5:— | SHA256:— | |||
| 3620 | EH Typing Product 2019 U1.17.exe | C:\Program Files\EH TYPING TUTOR\DBLOGIN.$A | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report