| File name: | 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f |
| Full analysis: | https://app.any.run/tasks/67e4b8b1-6f2d-4a8f-90c9-f59989a7bc3a |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2019, 08:25:02 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, MS CAB-Installer self-extracting archive |
| MD5: | A157A168E6EC68743CCD84129958F07B |
| SHA1: | 823957D5D9DEA9C0DA5D92066F447EAE690F78EC |
| SHA256: | 5E2B3771C665C2538CDE7CBD4E5595793044ADEAAAD853AB5A8D9F4260B1460F |
| SSDEEP: | 12288:FGvjp5cj35kDB9hrs3zARBSaJSXi15mN9bFm3LIIh:KukDF4zARUwSXImNZUxh |
MALICIOUS
Changes the autorun value in the registry
- 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe (PID: 3492)
Loads dropped or rewritten executable
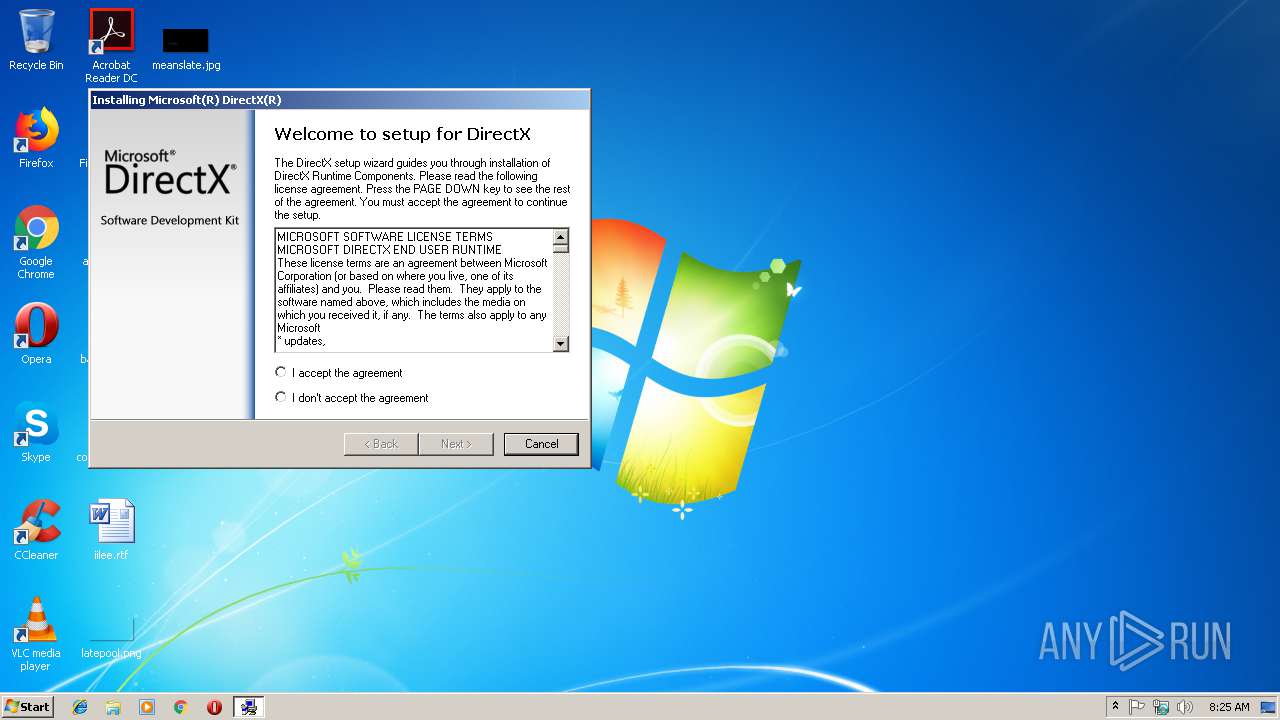
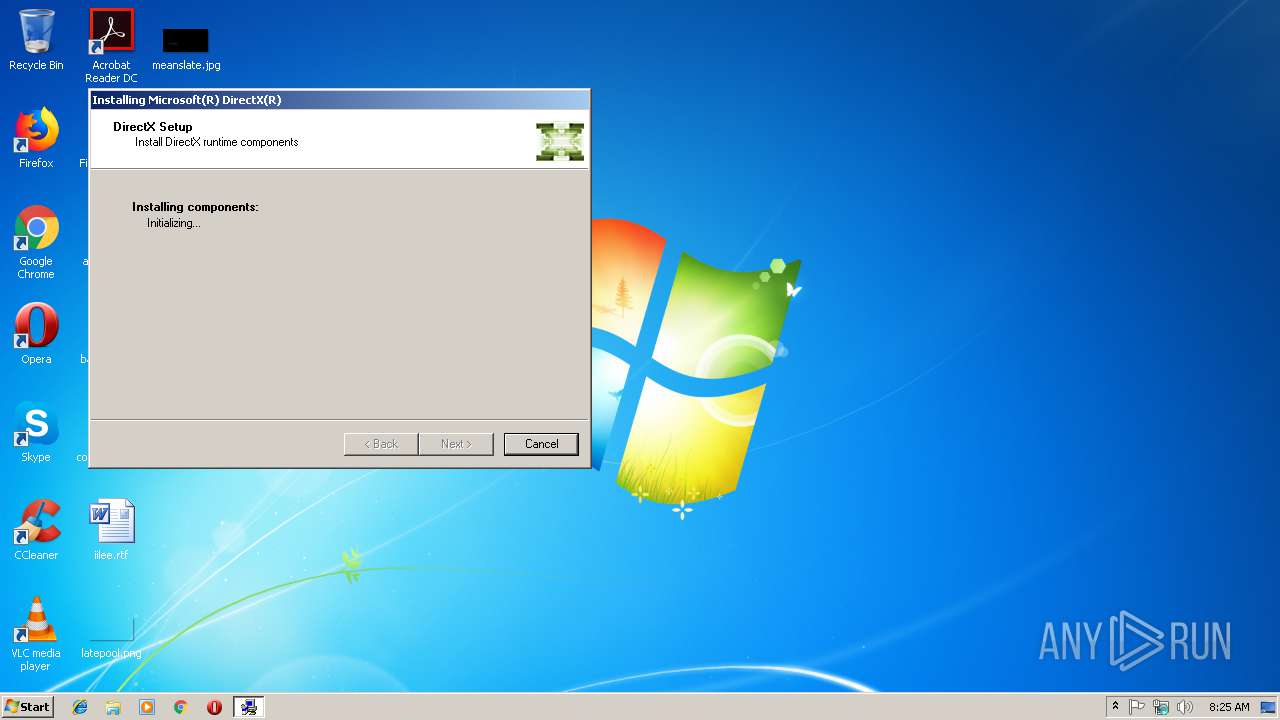
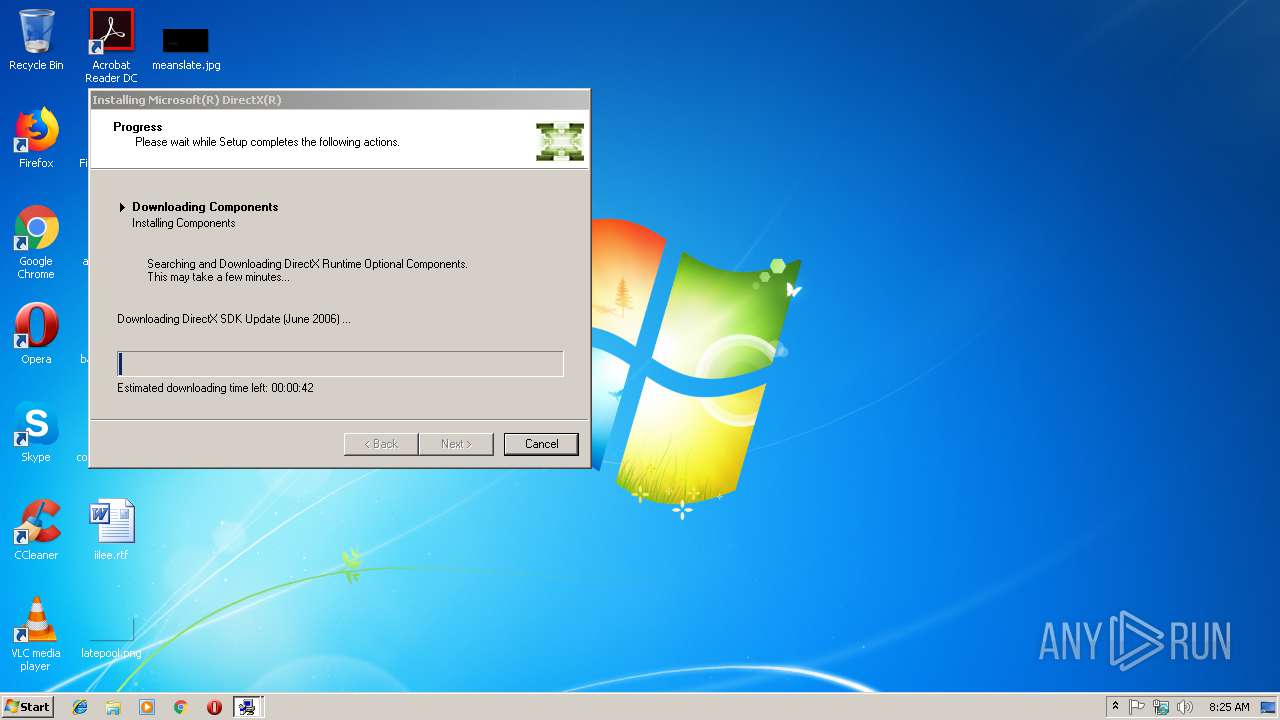
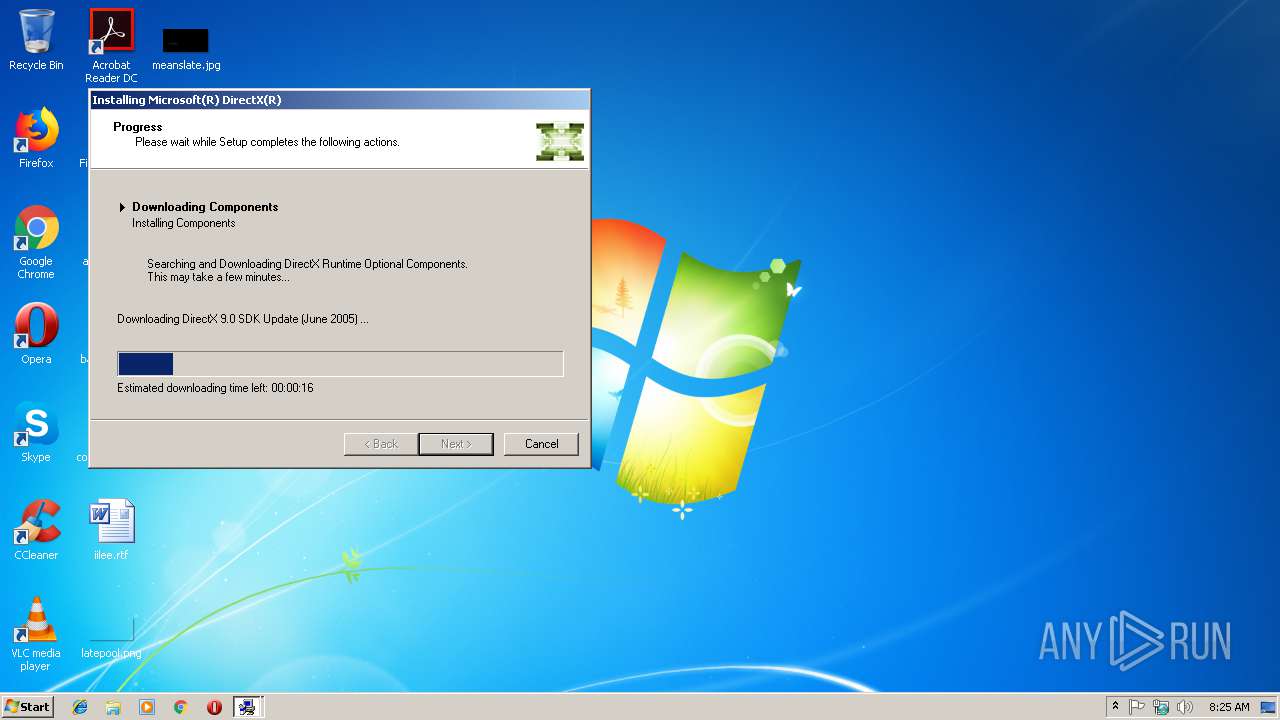
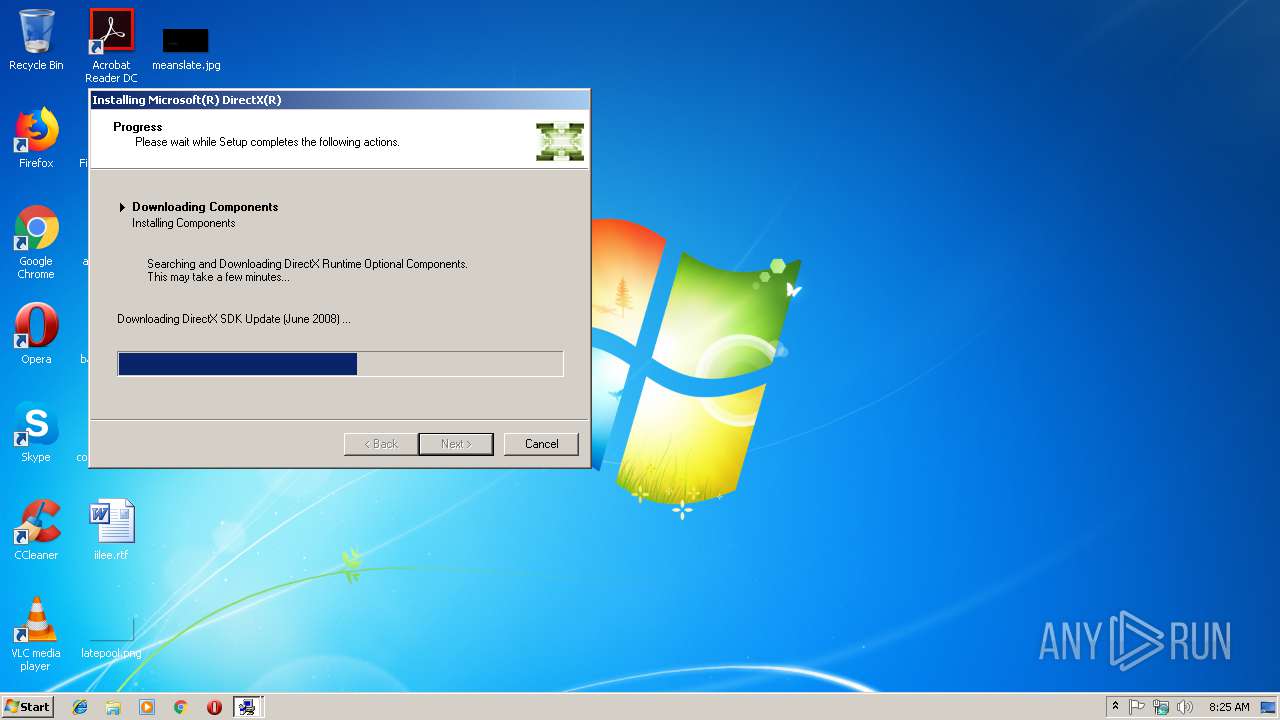
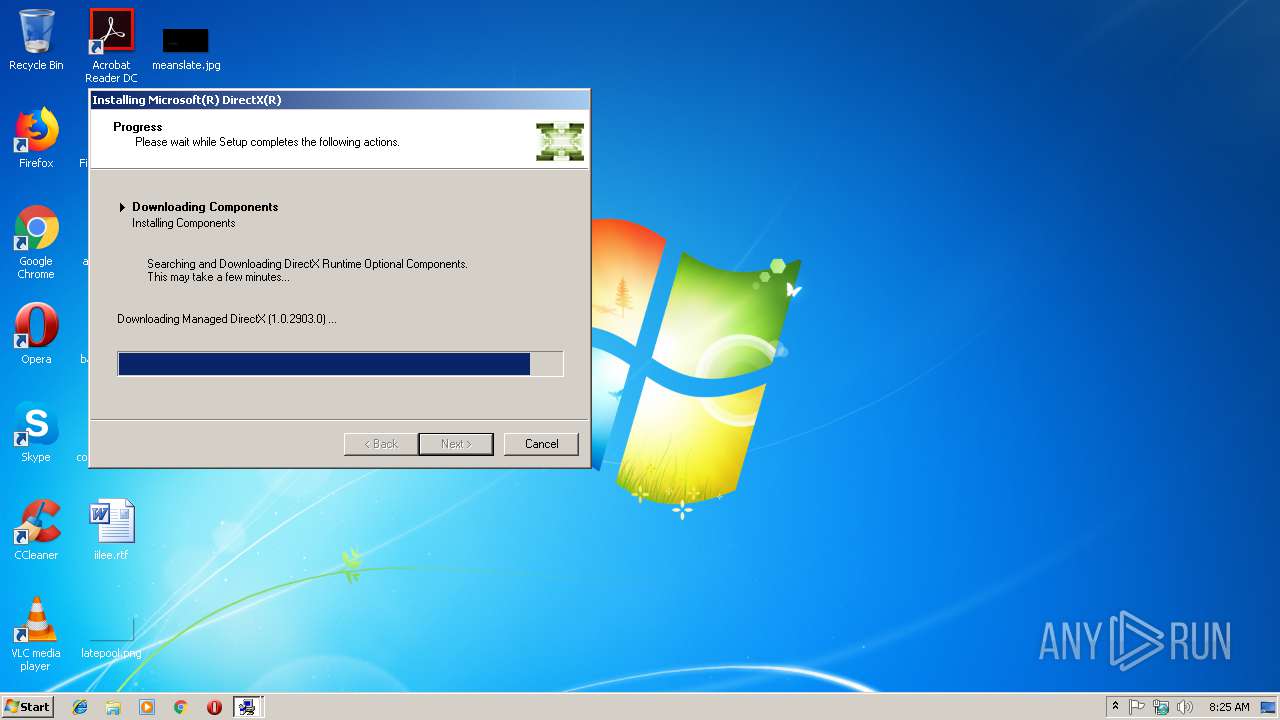
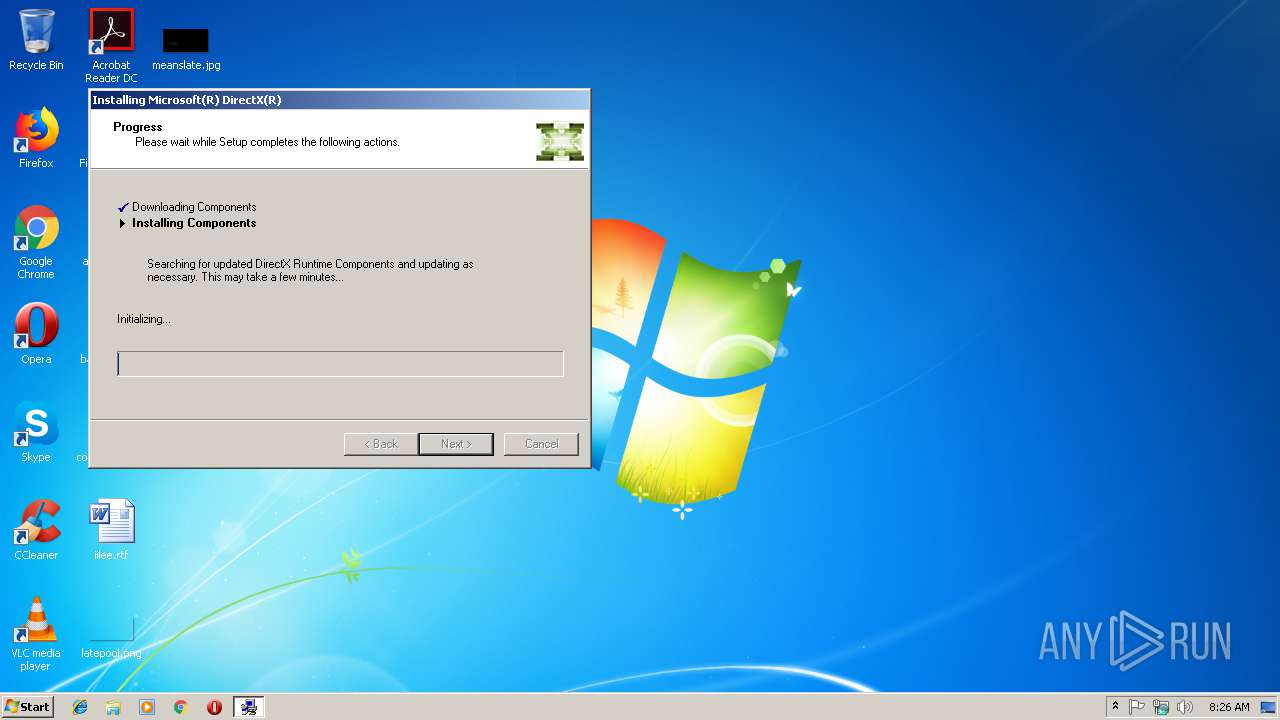
- dxwsetup.exe (PID: 2664)
- explorer.exe (PID: 284)
- 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe (PID: 3492)
- DllHost.exe (PID: 3892)
- dwm.exe (PID: 1988)
Application was dropped or rewritten from another process
- dxwsetup.exe (PID: 2664)
SUSPICIOUS
Executable content was dropped or overwritten
- 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe (PID: 3492)
- dxwsetup.exe (PID: 2664)
Searches for installed software
- dxwsetup.exe (PID: 2664)
- DllHost.exe (PID: 3892)
Creates COM task schedule object
- dxwsetup.exe (PID: 2664)
Removes files from Windows directory
- dxwsetup.exe (PID: 2664)
Creates files in the Windows directory
- dxwsetup.exe (PID: 2664)
INFO
Low-level read access rights to disk partition
- vssvc.exe (PID: 2892)
Reads settings of System Certificates
- dxwsetup.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:08:18 03:42:57+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7 |
| CodeSize: | 34816 |
| InitializedDataSize: | 246272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x48000 |
| OSVersion: | 5.1 |
| ImageVersion: | 5.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.0.2600.0 |
| ProductVersionNumber: | 6.0.2600.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | DirectX 9.0 Web setup |
| FileVersion: | 9.29.1962.0 |
| InternalName: | DXWebSetup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFileName: | dxwebsetup.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 9.29.1962.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Aug-2001 01:42:57 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | DirectX 9.0 Web setup |
| FileVersion: | 9.29.1962.0 |
| InternalName: | DXWebSetup |
| LegalCopyright: | Copyright (c) Microsoft Corporation. All rights reserved. |
| OriginalFilename: | dxwebsetup.exe |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 9.29.1962.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 18-Aug-2001 01:42:57 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000861A | 0x00008800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.55103 |
.data | 0x0000A000 | 0x00001BE4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18428 |
.rsrc | 0x0000C000 | 0x0003C000 | 0x0003BE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.82577 |
.mjg\x07 | 0x00048000 | 0x00001000 | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.96134 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.48538 | 884 | Latin 1 / Western European | English - United States | RT_VERSION |
2 | 3.53793 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
63 | 2.48958 | 140 | Latin 1 / Western European | English - United States | RT_STRING |
76 | 3.2674 | 1312 | Latin 1 / Western European | English - United States | RT_STRING |
77 | 3.29977 | 1484 | Latin 1 / Western European | English - United States | RT_STRING |
80 | 3.27174 | 1200 | Latin 1 / Western European | English - United States | RT_STRING |
83 | 3.2912 | 1098 | Latin 1 / Western European | English - United States | RT_STRING |
85 | 3.13591 | 974 | Latin 1 / Western European | English - United States | RT_STRING |
2001 | 3.35785 | 716 | Latin 1 / Western European | English - United States | RT_DIALOG |
2002 | 3.34986 | 394 | Latin 1 / Western European | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
VERSION.dll |
Total processes
39
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1988 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2664 | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.exe | 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
| 2892 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe" | C:\Users\admin\AppData\Local\Temp\5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DirectX 9.0 Web setup Exit code: 3221226540 Version: 9.29.1962.0 Modules
| |||||||||||||||
| 3492 | "C:\Users\admin\AppData\Local\Temp\5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe" | C:\Users\admin\AppData\Local\Temp\5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DirectX 9.0 Web setup Exit code: 0 Version: 9.29.1962.0 Modules
| |||||||||||||||
| 3840 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000003C0" "000005BC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3892 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\system32\DllHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
938
Read events
529
Write events
409
Delete events
0
Modification events
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.app.log |
Value: 4096 | |||
| (PID) Process: | (3492) 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | wextract_cleanup0 |
Value: rundll32.exe C:\Windows\system32\advpack.dll,DelNodeRunDLL32 "C:\Users\admin\AppData\Local\Temp\IXP000.TMP\" | |||
| (PID) Process: | (284) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | PINF |
Value: 0700433A5C55736572735C61646D696E5C417070446174615C4C6F63616C5C54656D705C697864454435322E746D7000 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2664) dxwsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dxwsetup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
23
Suspicious files
89
Text files
669
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | dxwsetup.exe | C:\Windows\system32\directx\websetup\SETEE0D.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\system32\directx\websetup\SETEE1E.tmp | — | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\dxupdate[1].cab | — | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\msdownld.tmp\AS21316F.tmp\dxupdate.cab | — | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\system32\DirectX\WebSetup\dxupdate.cab | compressed | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\INF\setupapi.app.log | text | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\system32\DirectX\WebSetup\filelist.dat | text | |
MD5:— | SHA256:— | |||
| 2664 | dxwsetup.exe | C:\Windows\Logs\DirectX.log | text | |
MD5:— | SHA256:— | |||
| 3492 | 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | C:\Users\admin\AppData\Local\Temp\IXP000.TMP\dxwsetup.inf | ini | |
MD5:AD8982EAA02C7AD4D7CDCBC248CAA941 | SHA256:D63C35E9B43EB0F28FFC28F61C9C9A306DA9C9DE3386770A7EB19FAA44DBFC00 | |||
| 3492 | 5e2b3771c665c2538cde7cbd4e5595793044adeaaad853ab5a8d9f4260b1460f.exe | C:\Users\admin\AppData\Local\Temp\ixdED52.tmp | executable | |
MD5:685F1CBD4AF30A1D0C25F252D399A666 | SHA256:0E478C95A7A07570A69E6061E7C1DA9001BCCAD9CC454F2ED4DA58824A13E0F4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
85
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/dxupdate.cab | unknown | compressed | 94.8 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Nov2007_xact_x86.cab | unknown | compressed | 145 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Mar2008_x3daudio_x86.cab | unknown | compressed | 22.3 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xinput_x86.cab | unknown | compressed | 45.9 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Feb2006_xact_x86.cab | unknown | compressed | 130 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Apr2006_xact_x86.cab | unknown | compressed | 130 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Jun2006_xact_x86.cab | unknown | compressed | 131 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xact_x86.cab | unknown | compressed | 135 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Dec2006_xact_x86.cab | unknown | compressed | 142 Kb | whitelisted |
2664 | dxwsetup.exe | GET | 200 | 2.18.233.19:80 | http://download.microsoft.com/download/1/7/1/1718CCC4-6315-4D8E-9543-8E28A4E18C4C/Aug2006_xinput_x86.cab | unknown | compressed | 45.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2664 | dxwsetup.exe | 2.18.233.19:80 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_DETACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |
dxwsetup.exe | DLL_PROCESS_ATTACH |