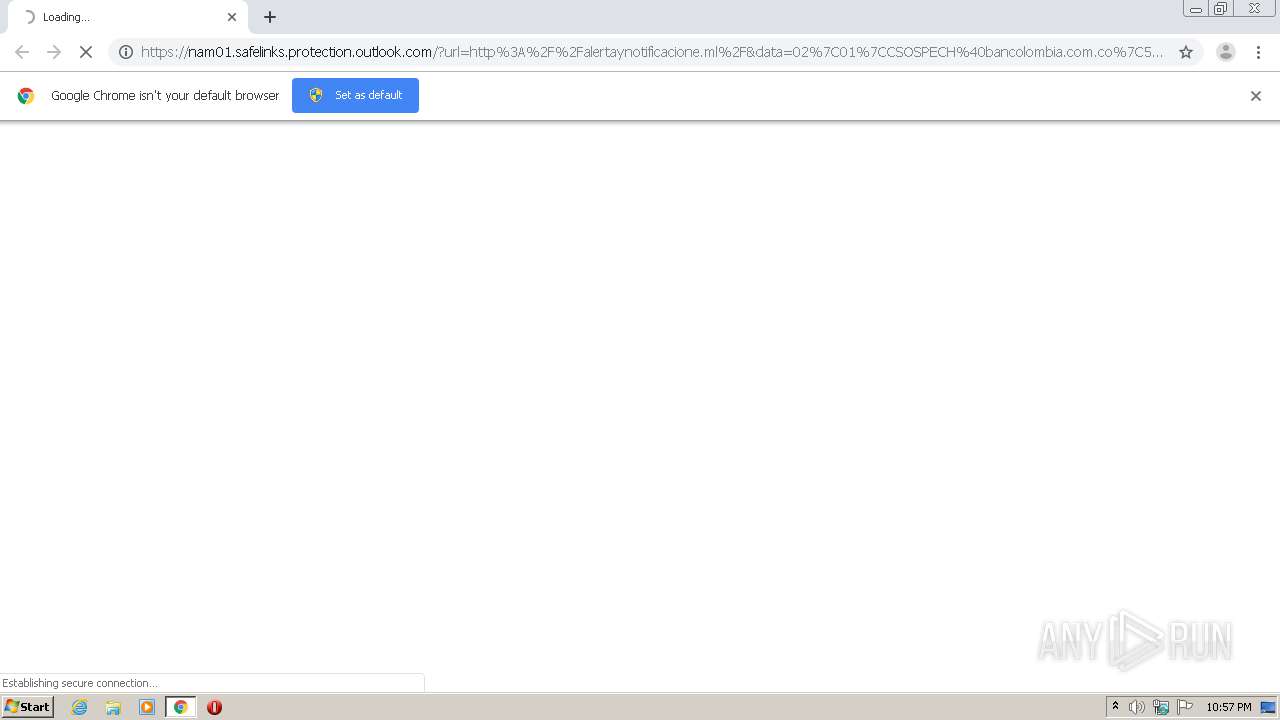
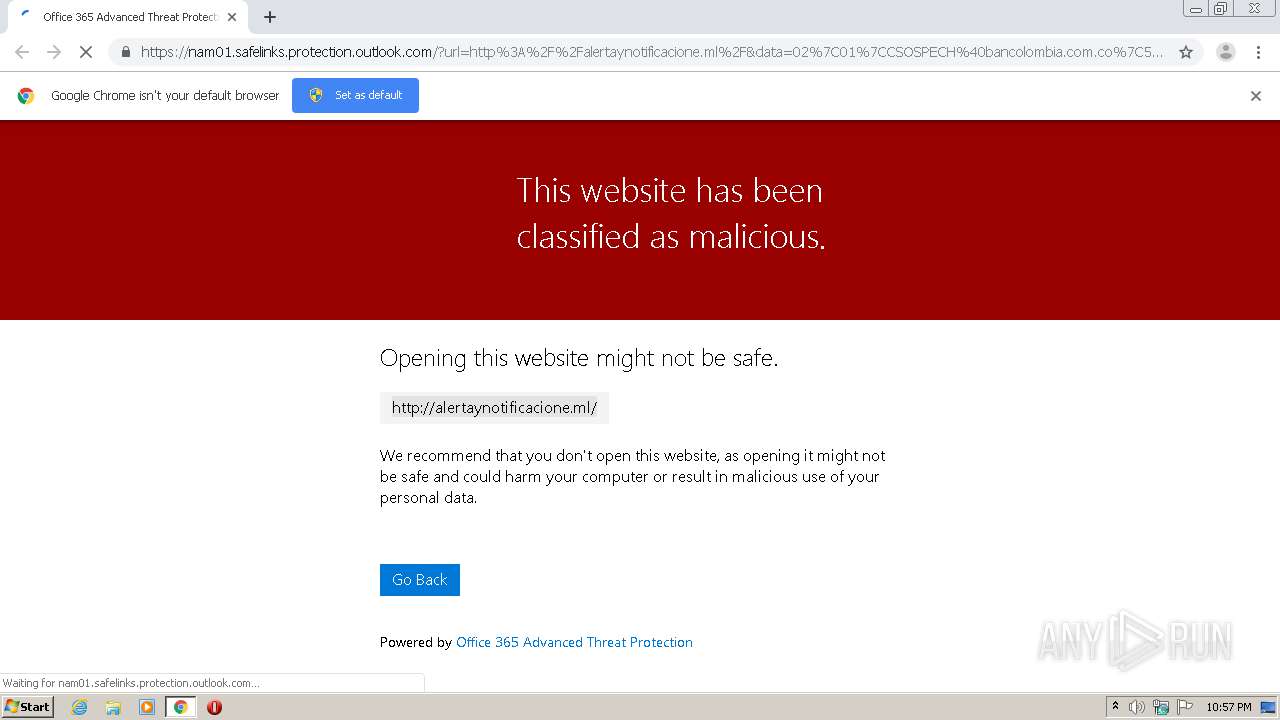
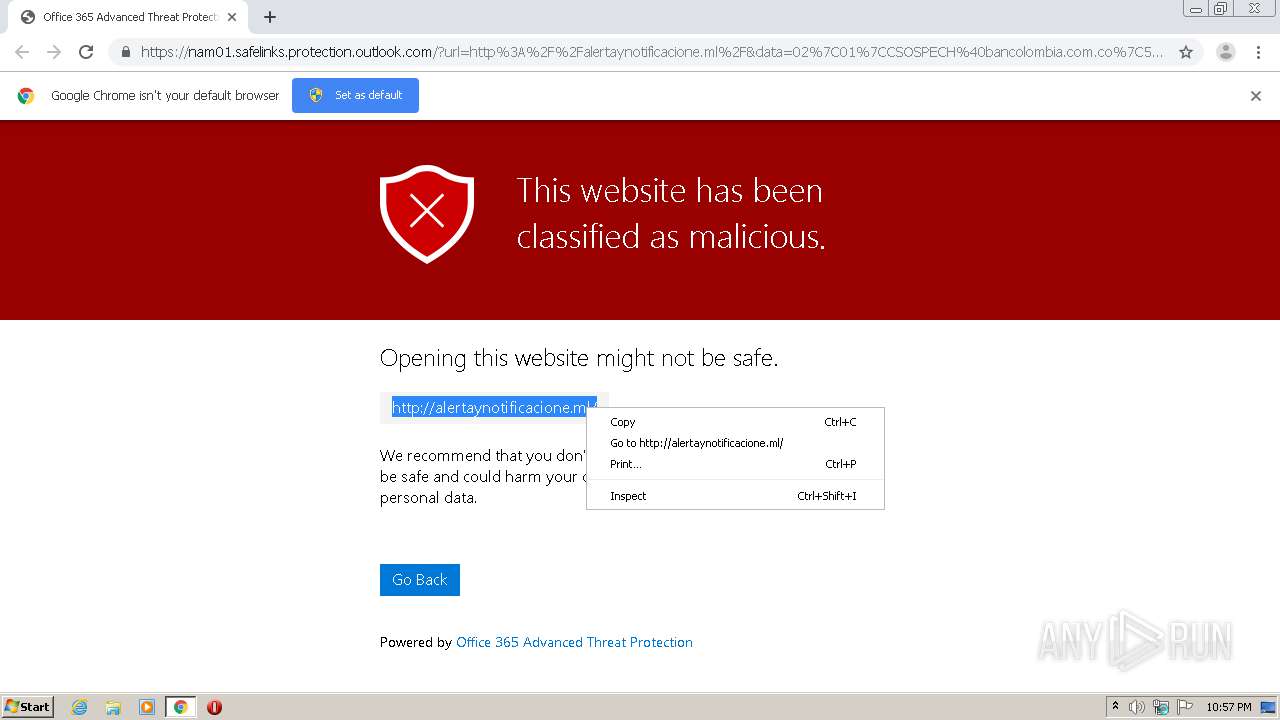
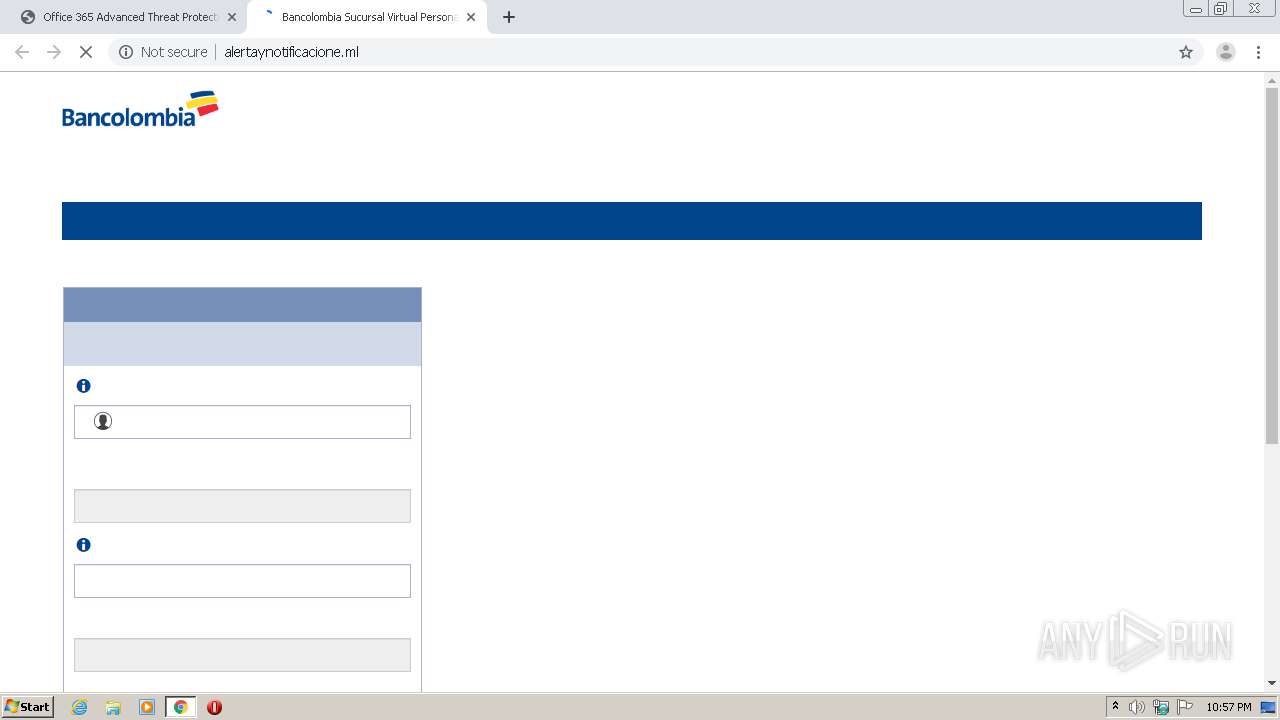
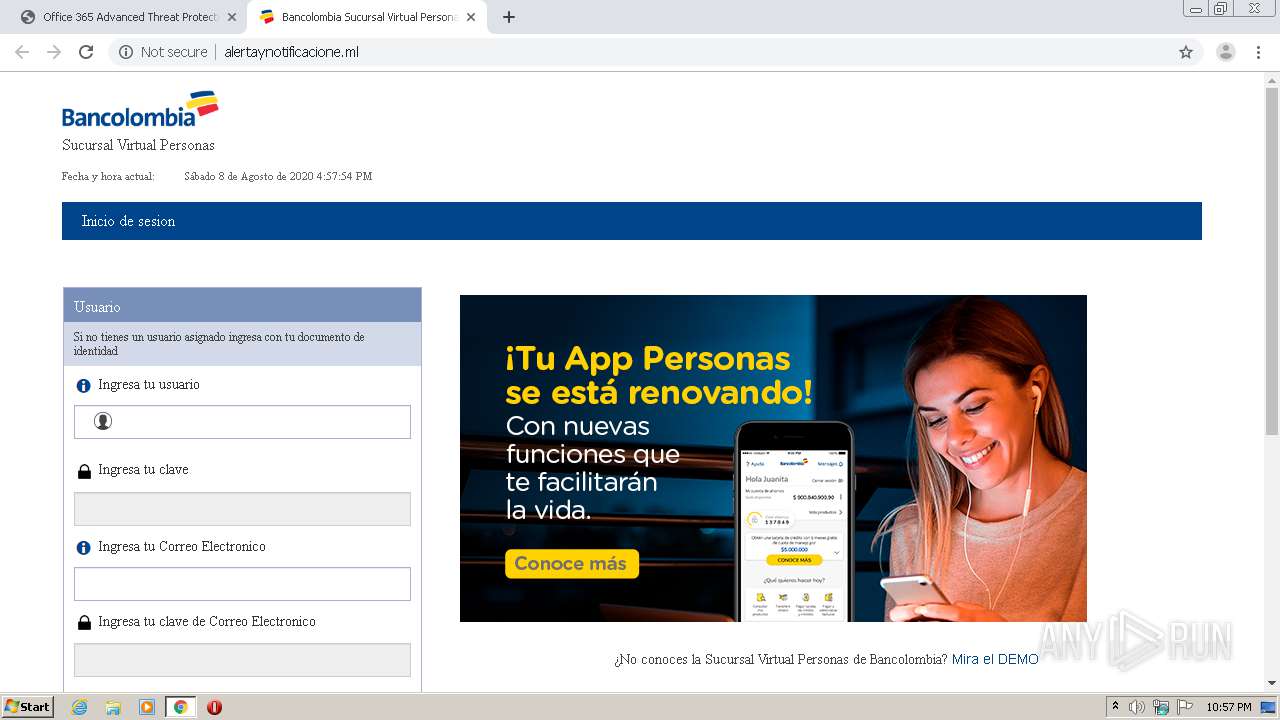
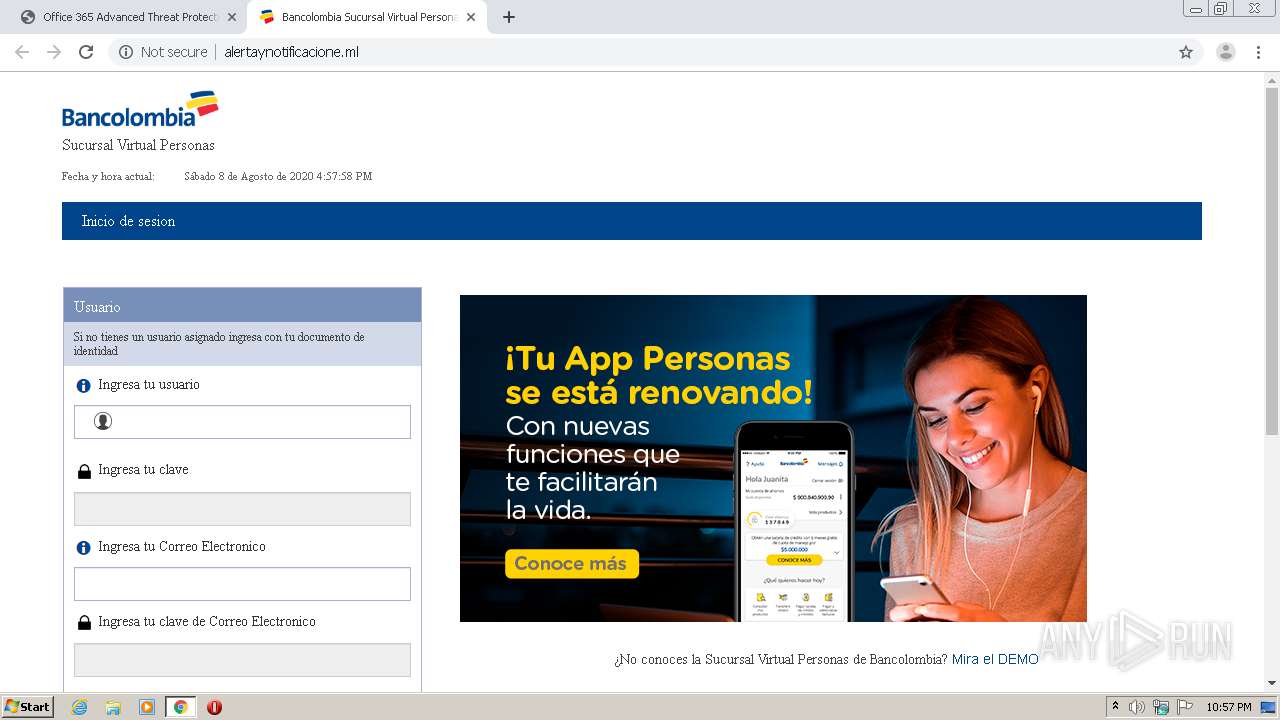
| URL: | https://nam01.safelinks.protection.outlook.com/?url=http%3A%2F%2Falertaynotificacione.ml%2F&data=02%7C01%7CCSOSPECH%40bancolombia.com.co%7C532af306f73b44d7337108d83bc57ea2%7Cb5e244bdc492495b8b1061bfd453e423%7C0%7C0%7C637325067147918140&sdata=eeZZIHz2D6O0OGZRSIwO3JnhdVB4iBdafkVvfel3fXU%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/1c852bfe-cbd4-4a19-b1c0-424682f21301 |
| Verdict: | Malicious activity |
| Analysis date: | August 08, 2020, 21:57:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B1E17C43F940CF108111E9AAD5113AD1 |
| SHA1: | 8E6C068BDE51D16FADBD6536A8EFB7412BD06DF0 |
| SHA256: | 5E292994B5E26EC29ECD65BCC5C270C5B1FECB444D6AE3DF56A967B6CF28E3A9 |
| SSDEEP: | 6:2u9V9iRXPNHszI0AXKTo319R9Hwn+2OWiiZoeQvQ:2u9qVs00Nollwn+rN2QI |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the hosts file
- chrome.exe (PID: 1260)
- chrome.exe (PID: 684)
Application launched itself
- chrome.exe (PID: 684)
Reads settings of System Certificates
- chrome.exe (PID: 1260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://nam01.safelinks.protection.outlook.com/?url=http%3A%2F%2Falertaynotificacione.ml%2F&data=02%7C01%7CCSOSPECH%40bancolombia.com.co%7C532af306f73b44d7337108d83bc57ea2%7Cb5e244bdc492495b8b1061bfd453e423%7C0%7C0%7C637325067147918140&sdata=eeZZIHz2D6O0OGZRSIwO3JnhdVB4iBdafkVvfel3fXU%3D&reserved=0" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3542731495644090168 --mojo-platform-channel-handle=1528 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4066252016439980165 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2252 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16825934197080448885 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1464 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4273683969839718189 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2496 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8012552419624718210 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=17920240879523459549 --mojo-platform-channel-handle=3404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2632 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13321525817359096715 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1028,145672727049277731,4986195442226811398,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1928523927613700857 --mojo-platform-channel-handle=3436 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
700
Read events
614
Write events
81
Delete events
5
Modification events
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2828) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 684-13241397454875000 |
Value: 259 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (684) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 684-13241397454875000 |
Value: 259 | |||
Executable files
0
Suspicious files
44
Text files
67
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\45f941c8-9bdd-44d9-a8af-a3f541db6e62.tmp | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFdb825.TMP | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdb825.TMP | text | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\AutofillStrikeDatabase\CURRENT | — | |
MD5:— | SHA256:— | |||
| 684 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
27
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/validations.js | US | text | 2.19 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/gtm_002.js | US | text | 28.0 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/jquery-validations.js | US | text | 286 b | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/jquery-ui.css | US | text | 7.09 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/blockKeys.js | US | text | 156 b | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/jquery-ui.js | US | text | 71.9 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/bootstrap.js | US | text | 9.84 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/jquery_002.js | US | text | 1.31 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/rsa.html | US | html | 2.93 Kb | shared |
1260 | chrome.exe | GET | 200 | 145.14.145.90:80 | http://alertaynotificacione.ml/Bancolombia%20Sucursal%20Virtual%20Personas_files/hashtable.html | US | html | 2.93 Kb | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1260 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1260 | chrome.exe | 104.47.32.28:443 | nam01.safelinks.protection.outlook.com | Microsoft Corporation | US | whitelisted |
1260 | chrome.exe | 172.217.21.195:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1260 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
1260 | chrome.exe | 145.14.145.90:80 | alertaynotificacione.ml | Hostinger International Limited | US | shared |
1260 | chrome.exe | 157.240.20.19:443 | connect.facebook.net | Facebook, Inc. | US | whitelisted |
1260 | chrome.exe | 172.217.22.78:443 | clients1.google.com | Google Inc. | US | whitelisted |
1260 | chrome.exe | 99.86.7.31:443 | api.omappapi.com | AT&T Services, Inc. | US | unknown |
1260 | chrome.exe | 172.217.21.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1260 | chrome.exe | 23.111.11.182:443 | a.opmnstr.com | netDNA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
nam01.safelinks.protection.outlook.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
clients2.google.com |
| whitelisted |
alertaynotificacione.ml |
| shared |
connect.facebook.net |
| whitelisted |
a.opmnstr.com |
| whitelisted |
cdn.000webhost.com |
| whitelisted |
monstat.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1048 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |